闲着没事把大三的实验发一下 这里用的技术和老师要求的略有不同但大体相同
1. RSA 算法简介
公钥密码体制中,解密和加密密钥不同,解密和加密可分离,通信双方无须事先交换密钥就可建立起保密通信,较好地解决了传统密码体制在网络通信中出现的问题.另外,随着电子商务的发展,网络上资金的电子交换日益频繁,如何防止信息的伪造和欺骗也成为非常重要的问题.数字签名可以起到身份认证,核准数据完整性的作用.目前关于数字签名的研究主要集中基于公钥密码体制的数字签名.
公钥密码体制的特点是:为每个用户产生一对密钥(PK和SK);PK公开,SK保密;从PK推出SK是很困难的;A,B双方通信时,A通过任何途径取得B的公钥,用B的公钥加密信息.加密后的信息可通过任何不安全信道发送.B收到密文信息后,用自己私钥解密恢复出明文.
RSA公钥密码体制到目前为止还是一种认可为安全的体制. RSA算法和用RSA算法实现数字签名的理论,以及它们在实际应用中
2. RSA 数字签名算法的理论描述
关于数字签名,先了解下何为数字签名。数字签名,就是只有信息的发送者才能产生的别人无法伪造的一段数字串,这段数字串同时也是对信息的发送者发送信息真实性的一个有效证明。数字签名是非对称密钥加密技术与数字摘要技术的应用。简单地说,所谓数字签名就是附加在数据单元上的一些数据,或是对数据单元所作的密码变换。这种数据或变换允许数据单元的接收者用以确认数据单元的来源和数据单元的完整性并保护数据,防止被人(例如接收者)进行伪造。
RSA数字签名算法的过程为:A对明文m用解密变换作: s Dk (m)=m^d mod n,其中d,n为A的私人密钥,只有A才知道它;B收到A的签名后,用A的公钥和加密变换得到明文,因: Ek(s)= Ek(Dk (m))= (m^d)^e mod n,又 de1 mod (n)即de=l(n)+1,根据欧拉定理m(n)=1 mod n,所以Ek(s)=ml(n)+1=m(n)em=m mod n.若明文m和签名s一起送给用户B,B可以确信信息确实是A发送的.同时A也不能否认送给这个信息,因为除了A本人外,其他任何人都无法由明文m产生s.因此RSA数字签名方案是可行的.
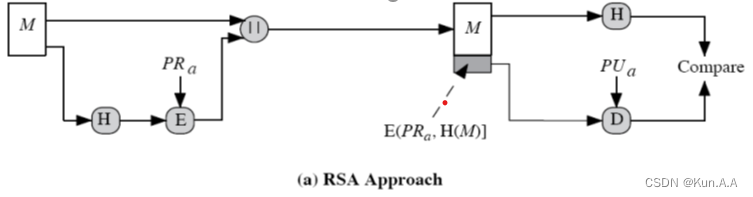
但是RSA数字签名算法存在着因计算方法本身同构造成签名易被伪造和计算时间长的弱点,因此实际对文件签名前,需要对消息做SHA--512变换. SHA--512函数是一种单向散列函数,它将任意长度的消息压缩成512位的消息摘要.应用SHA--512的单向性(即给定散列值,计算消息很难)和抗碰撞性(即给定消息M,要找到另一消息M' 并满足两者的散列值很难),可以实现信息的完整性检验.另外该函数的设计不基于任何假设和密码体制而直接构造,执行的速度快,是一种被广泛认可的单向散列算法.
3. RSA 数字签名算法的实现
RSA数字签名算法,包括签名算法和验证签名算法.首先用SHA--512算法对
信息作散列计算.签名的过程需用户的私钥,验证过程需用户的公钥.A用签名算法将字符串形式的消息处理成签名;B用验证签名算法验证签名是否是A对消息的签名,确认是A发送的消息;消息没有被攥改过;A一定发送过消息.
(1)签名算法
签名算法包括三步:消息摘要、计算、RSA加密.
消息摘要计算. 消息在签名前首先通过SHA--512计算,生成512位的消息摘要,对摘要作RSA计算. 用加密算法,采用签名者的私钥加密消息摘要,得到加密后的字符串.加密算法中使用的加密块为01类型.
(2)验证签名算法
验证签名算法包括两步:RSA解密得签名者的消息摘要,验证者对原消息计算摘要,比较两个消息摘要.验证签名的过程输入为:消息、签名者的公钥、签名;输出为:验证的结果,即是否是正确的签名.
RSA解密. 签名实际是加密的字符串.采用签名者的公钥对这个加密的字符串解密.解密的结果应为512位的消息摘要.在解密过程中,若出现得到的加密块的类型不是01,则解密失败.签名不正确.
消息摘要计算和比较. 验证者对消息用SHA--512算法重新计算,得到验证者自己的消息摘要.验证者比较解密得到的消息摘要和自己的消息摘要,如果两者相同,则验证成功,可以确认消息的完整性及签名确实为签名者的;否则,验证失败.
- 实验内容和步骤
实验内容 :
-
- 理解数字签名的原理和步骤。
- 学会使用RSA算法, 在此基础上对各项功能按步骤进行综合,实现RSA数字签名功能。
实验步骤 :
同学们需要制作可视化界面,包括:签名生成界面、签名验证界面,可以做静态html+JavaScript(推荐),也可以做B/S。以下步骤针对(html+JavaScript):
1.实验需要RSA和SHA-512的js包,来完成基本的公私钥生成、加密解密、hash运算功能,同学们可以在网上自行下载,学习使用方法。
也可以使用整理的两个js包。
RSA Encrypt包使用方法:
数据加密:
var hashed; //
var encrypt = new JSEncrypt();
encrypt.setPrivateKey(PU);
var encrypted= encrypt.encrypt(hashed);
数据解密:
var sign;
var decrypt = new JSEncrypt();
decrypt.setPrivateKey(PR);
var uncrypted = decrypt.decrypt(sign);
SHA-512:
hashed =hex_sha512(message);
感觉后面都是废话直接贴代码了
前端html代码
html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta http-equiv="X-UA-Compatible" content="IE=edge">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<link crossorigin="anonymous" href="https://cdn.bootcdn.net/ajax/libs/twitter-bootstrap/5.2.2/css/bootstrap.min.css" rel="stylesheet">
<title>信息安全实验</title>
</head>
<body>
<div style="display: flex;flex-direction: row; margin-left: 240px; margin-right: 240px;">
<div class="container" style="display: flex;flex-direction: column;align-items: flex-start;justify-items: start;margin-top: 80px; " >
<h1>签名生成</h1>
<li>输入Message</li>
<input id="input_Message" placeholder="输入消息" style="width:400px ;">
<br><button id="sha-512" class="btn btn-primary" onclick="sha512ToHash()">SHA-512</button>
<li>HASH值</li>
<input id="hash_Result" placeholder="散列结果"style="width:400px ;">
<br><button id = "private_Key" type="button" class="btn btn-warning" onclick="getSignature()">私钥签名</button>
<li>签名</li>
<input id="encrypt" placeholder="加密结果"style="width:400px ;">
</div>
<div class="container" style="display: flex;flex-direction: column;align-items: flex-start;justify-items: start;margin-top: 50px; ">
<h1>签名验证</h1>
1.验证者已获取到签名、公钥、Messgae
<li>Message:</li><input id="Message" style="width:400px ;">
<li>签名:</li><input id="sign" style="width:400px ;">
<li>公钥:</li><input id="public_key" style="width:400px ;">
<button id="get_Data"class="btn btn-success" onclick="setValue()">获取数据</button>
<br>2.使用公钥解析签名
<button class="btn btn-danger" onclick="decrypt()">公钥解签</button>
<li>HASH I:</li><input id="hash_Result1" placeholder="通过公钥解析签名后得到" style="width:400px ;">
<br>3.SHA-512散列Message
<button id="sha-512-2" class="btn btn-warning" onclick="setSHA512()">SHA-512</button>
<li>HASH II:</li><input id="hash_Result2" placeholder="通过SHA-512散列M后得到" style="width:400px ;">
<br>4.比较HASH I 与HASH II
<input id="cmp_Result" placeholder="将结果进行对比" style="width:400px ;height: 40px;">
<button id="cmp" class="btn btn-success btn-lg" onclick="judge()">对比结果</button>
</div>
</div>
<script src="./sha512.js" type="text/javascript"></script>
<script src="https://passport.cnblogs.com/scripts/jsencrypt.min.js"></script>
<script>
function sha512ToHash(){
let m = document.getElementById('input_Message').value;
var hashed;
if(m.length === 0){
hashed = "数据空无法计算";
}else{
hashed = hex_sha512(m);
hashed = hashed.slice(0, 60);
}
document.getElementById("hash_Result").value = hashed;
};
function getSignature(){
var PRIVATE_KEY = "-----BEGIN PRIVATE KEY-----MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQC90B6j6w6V6eHXyBNK9CMqTUHNjg1gqbJem8pBOkB15yEvbeMRCzHNwmKKI08Vm2EozMB2w8m9NwCtR2LQMxmhjMsrwOM+hcVzpD6fI6pXY+XPW6IEL6FGdNViG3lWFDe8R4EQ3jZWdOC8ZkeOmyC6+VbWrH3snlmRlbzOvDcHG2JlN553mA58g41q2AFCQlMjy6JfldDuLORJ9M2rJAux3WbAUhsdd4Q+0iGu5fXKqxcYqFnuIyqQM6VPMLh/qN7eXf38l2v+DY5aAnb+ZsAaRnpCcjfjmRGnJAMLXgcjesFJ8xlA1e6LyH6J3tlHGBdewlo3gnocBIBug9+0LO/tAgMBAAECggEADooOjsfGij0sC3dL4wXoW6knTTOAWtMk0pJkX7KylVVq+VMVfYy59+TX33Ts7d7FBncIlxBQN6oq5xr8uq3vXKyIM4XG4lck1MLT+SSmO6NvSv7d3iw30knIvocUOD+8NTPU8xHSX7T8MfIzsPy4+Rl4SWFVE/bdLYWmvL82B9kzQ+oQa5x2lwg/vlM/FVM+1GyuR/f15UCd2Us/+yPnRc3ukQUFRnhlDqImssx926C5W1w2RnBhTQuce4leq/wu3wBCAxBnMbYdBJkaMqkHfRQUMc5ewvp/J6IulGXUp0yfEVHZ2JnqZ5G0oysIE+OE7yglu+AayZdz7g13tJ/8EQKBgQDumoHdegdsRT20ZiJwOS10njacMf1T0KQeKvAXzsofcKjBZ0hfvCC97wg1+ZmOgf9nscxIqyuepIFVRTuxWH8NFX1Zd7LhZTOQiephBscTkvLIxp0oBQ+LRxhUupTCNBj5Nw9lcD5Rt6GKoEfyafMSDFv9Jq2HE9BjeY7pooaaXwKBgQDLpvHpf3UwArRD+o/B9mZ0d4g9OH8ZgmDWwBwagcnJfYYEQP0sAWGcIvPfn+visCmydQ765GMPNrdVlwUHsiKIzMwxTX1qDkeYf53Bu+VTsCVS8WZ5QqEUCRSLGUgYAD9kOgHvQMut4z3J2OEwwtnppcYwzM+2xS67YC5lIjAxMwKBgC6QrMOCayxwHuiz/giUwBBASDwXbW8MCttwWcbrrnqQS/7inzc/ycwHeDzAZ31uVV/xTQLplOuzAyKXDl0//huZlAr/10MxsuyEXd9tqTBiv0r7p/QFeNEfoNn4R8vWywDoA/MyApeEFNyvBxuCHdPp4ZH4GGmCLmsbcA6cj1RVAoGBAKrZmte+Y0zs59ij61jY42lQIo7hx9dZxu5C6xDd07DjSrxk3UC+w+nedOQl4Rojmkep5vBbDDPmPnZipQiozEoiLigqj02bPztTzMCMZr8H5rgn50VRvZr2ZzKu+gmQo53tAFR88qMmIl8lQP7MaU6YEaY9HQGDeUofTazwuqd7AoGBAIvAY8BnyI1OSjB2dv1lpNDqXkfbEJTCWn0fDku0p/Z19aRriLWn4oBDZL52V6fp8v3mFvxe6TzI1pl+SiBMuCkbycc1AgNoGMEJ94C1R03nc+AmqVc1ZQ5nrZDnBxnEJ1lTiEf2uoXrdiJsSDj/P2emVvz/RyGwWRoX2yaSL81G-----END PRIVATE KEY-----";
let hashed = document.getElementById('hash_Result').value;
var encrypt = new JSEncrypt();
encrypt.setPrivateKey(PRIVATE_KEY);
var encrypted;
if(hashed.length === 0){
encrypt="数据空无法签名";
}else{
encrypted = encrypt.encrypt(hashed);
}
document.getElementById('encrypt').value = encrypted;
}
function setValue(){
document.getElementById('Message').value = document.getElementById('input_Message').value;
document.getElementById('sign').value = document.getElementById('encrypt').value;
PUBLIC_KEY = "MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAvdAeo+sOlenh18gTSvQjKk1BzY4NYKmyXpvKQTpAdechL23jEQsxzcJiiiNPFZthKMzAdsPJvTcArUdi0DMZoYzLK8DjPoXFc6Q+nyOqV2Plz1uiBC+hRnTVYht5VhQ3vEeBEN42VnTgvGZHjpsguvlW1qx97J5ZkZW8zrw3BxtiZTeed5gOfIONatgBQkJTI8uiX5XQ7izkSfTNqyQLsd1mwFIbHXeEPtIhruX1yqsXGKhZ7iMqkDOlTzC4f6je3l39/Jdr/g2OWgJ2/mbAGkZ6QnI345kRpyQDC14HI3rBSfMZQNXui8h+id7ZRxgXXsJaN4J6HASAboPftCzv7QIDAQAB";
document.getElementById('public_key').value = PUBLIC_KEY;
}
function decrypt(){
var PRIVATE_KEY = "-----BEGIN PRIVATE KEY-----MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQC90B6j6w6V6eHXyBNK9CMqTUHNjg1gqbJem8pBOkB15yEvbeMRCzHNwmKKI08Vm2EozMB2w8m9NwCtR2LQMxmhjMsrwOM+hcVzpD6fI6pXY+XPW6IEL6FGdNViG3lWFDe8R4EQ3jZWdOC8ZkeOmyC6+VbWrH3snlmRlbzOvDcHG2JlN553mA58g41q2AFCQlMjy6JfldDuLORJ9M2rJAux3WbAUhsdd4Q+0iGu5fXKqxcYqFnuIyqQM6VPMLh/qN7eXf38l2v+DY5aAnb+ZsAaRnpCcjfjmRGnJAMLXgcjesFJ8xlA1e6LyH6J3tlHGBdewlo3gnocBIBug9+0LO/tAgMBAAECggEADooOjsfGij0sC3dL4wXoW6knTTOAWtMk0pJkX7KylVVq+VMVfYy59+TX33Ts7d7FBncIlxBQN6oq5xr8uq3vXKyIM4XG4lck1MLT+SSmO6NvSv7d3iw30knIvocUOD+8NTPU8xHSX7T8MfIzsPy4+Rl4SWFVE/bdLYWmvL82B9kzQ+oQa5x2lwg/vlM/FVM+1GyuR/f15UCd2Us/+yPnRc3ukQUFRnhlDqImssx926C5W1w2RnBhTQuce4leq/wu3wBCAxBnMbYdBJkaMqkHfRQUMc5ewvp/J6IulGXUp0yfEVHZ2JnqZ5G0oysIE+OE7yglu+AayZdz7g13tJ/8EQKBgQDumoHdegdsRT20ZiJwOS10njacMf1T0KQeKvAXzsofcKjBZ0hfvCC97wg1+ZmOgf9nscxIqyuepIFVRTuxWH8NFX1Zd7LhZTOQiephBscTkvLIxp0oBQ+LRxhUupTCNBj5Nw9lcD5Rt6GKoEfyafMSDFv9Jq2HE9BjeY7pooaaXwKBgQDLpvHpf3UwArRD+o/B9mZ0d4g9OH8ZgmDWwBwagcnJfYYEQP0sAWGcIvPfn+visCmydQ765GMPNrdVlwUHsiKIzMwxTX1qDkeYf53Bu+VTsCVS8WZ5QqEUCRSLGUgYAD9kOgHvQMut4z3J2OEwwtnppcYwzM+2xS67YC5lIjAxMwKBgC6QrMOCayxwHuiz/giUwBBASDwXbW8MCttwWcbrrnqQS/7inzc/ycwHeDzAZ31uVV/xTQLplOuzAyKXDl0//huZlAr/10MxsuyEXd9tqTBiv0r7p/QFeNEfoNn4R8vWywDoA/MyApeEFNyvBxuCHdPp4ZH4GGmCLmsbcA6cj1RVAoGBAKrZmte+Y0zs59ij61jY42lQIo7hx9dZxu5C6xDd07DjSrxk3UC+w+nedOQl4Rojmkep5vBbDDPmPnZipQiozEoiLigqj02bPztTzMCMZr8H5rgn50VRvZr2ZzKu+gmQo53tAFR88qMmIl8lQP7MaU6YEaY9HQGDeUofTazwuqd7AoGBAIvAY8BnyI1OSjB2dv1lpNDqXkfbEJTCWn0fDku0p/Z19aRriLWn4oBDZL52V6fp8v3mFvxe6TzI1pl+SiBMuCkbycc1AgNoGMEJ94C1R03nc+AmqVc1ZQ5nrZDnBxnEJ1lTiEf2uoXrdiJsSDj/P2emVvz/RyGwWRoX2yaSL81G-----END PRIVATE KEY-----";
var PUBLIC_KEY = "-----BEGIN PUBLIC KEY-----MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAvdAeo+sOlenh18gTSvQjKk1BzY4NYKmyXpvKQTpAdechL23jEQsxzcJiiiNPFZthKMzAdsPJvTcArUdi0DMZoYzLK8DjPoXFc6Q+nyOqV2Plz1uiBC+hRnTVYht5VhQ3vEeBEN42VnTgvGZHjpsguvlW1qx97J5ZkZW8zrw3BxtiZTeed5gOfIONatgBQkJTI8uiX5XQ7izkSfTNqyQLsd1mwFIbHXeEPtIhruX1yqsXGKhZ7iMqkDOlTzC4f6je3l39/Jdr/g2OWgJ2/mbAGkZ6QnI345kRpyQDC14HI3rBSfMZQNXui8h+id7ZRxgXXsJaN4J6HASAboPftCzv7QIDAQAB-----END PUBLIC KEY-----";
let sign = document.getElementById('sign').value;
var decrypt = new JSEncrypt();
decrypt.setPublicKey(PUBLIC_KEY);
decrypt.setPrivateKey(PRIVATE_KEY);
var undecrypt = decrypt.decrypt(sign);
// console.log('undecrypt :>> ', undecrypt);
if(undecrypt === false){
undecrypt = "解密失败";
}else if(undecrypt === null){
undecrypt = "解密失败"
}
document.getElementById('hash_Result1').value = undecrypt;
}
function setSHA512(){
let m = document.getElementById('Message').value;
var hashed;
if(m.length === 0){
hashed = "数据空无法计算";
}else{
hashed = hex_sha512(m);
hashed = hashed.slice(0, 60);
}
document.getElementById("hash_Result2").value = hashed;
}
function judge(){
var I = document.getElementById('hash_Result1').value;
var II = document.getElementById('hash_Result2').value;
if(I === II){
document.getElementById('cmp_Result').value = "解密成功√";
}else{
document.getElementById('cmp_Result').value = "解密失败X";
}
}
</script>
</body>
</html>RSA.js代码
javascript
// import {jsencrypt} from 'https://passport.cnblogs.com/scripts/jsencrypt.min.js';
// import {} from './sha512.js';
const btnsha512 = document.getElementById('sha-512');
btnsha512.onclick = function sha512ToHash(){
let m = document.getElementById('input_Message');
var hashed;
if(m.length){
hashed == "数据空无法计算";
}else{
hashed = hex_sha512(m);
hashed = hashed.slice(0,60);
}
document.getElementById('hash_Result').vlaue = hashed;
}SHA512.js代码
国外大神写的SHA512的JS代码
javascript
/*
* A JavaScript implementation of the Secure Hash Algorithm, SHA-512, as defined
* in FIPS 180-2
* Version 2.2 Copyright Anonymous Contributor, Paul Johnston 2000 - 2009.
* Other contributors: Greg Holt, Andrew Kepert, Ydnar, Lostinet
* Distributed under the BSD License
* See http://pajhome.org.uk/crypt/md5 for details.
*/
/*
* Configurable variables. You may need to tweak these to be compatible with
* the server-side, but the defaults work in most cases.
*/
var hexcase = 0; /* hex output format. 0 - lowercase; 1 - uppercase */
var b64pad = ""; /* base-64 pad character. "=" for strict RFC compliance */
/*
* These are the functions you'll usually want to call
* They take string arguments and return either hex or base-64 encoded strings
*/
function hex_sha512(s) { return rstr2hex(rstr_sha512(str2rstr_utf8(s))); }
function b64_sha512(s) { return rstr2b64(rstr_sha512(str2rstr_utf8(s))); }
function any_sha512(s, e) { return rstr2any(rstr_sha512(str2rstr_utf8(s)), e);}
function hex_hmac_sha512(k, d)
{ return rstr2hex(rstr_hmac_sha512(str2rstr_utf8(k), str2rstr_utf8(d))); }
function b64_hmac_sha512(k, d)
{ return rstr2b64(rstr_hmac_sha512(str2rstr_utf8(k), str2rstr_utf8(d))); }
function any_hmac_sha512(k, d, e)
{ return rstr2any(rstr_hmac_sha512(str2rstr_utf8(k), str2rstr_utf8(d)), e);}
/*
* Perform a simple self-test to see if the VM is working
*/
function sha512_vm_test()
{
return hex_sha512("abc").toLowerCase() ==
"ddaf35a193617abacc417349ae20413112e6fa4e89a97ea20a9eeee64b55d39a" +
"2192992a274fc1a836ba3c23a3feebbd454d4423643ce80e2a9ac94fa54ca49f";
}
/*
* Calculate the SHA-512 of a raw string
*/
function rstr_sha512(s)
{
return binb2rstr(binb_sha512(rstr2binb(s), s.length * 8));
}
/*
* Calculate the HMAC-SHA-512 of a key and some data (raw strings)
*/
function rstr_hmac_sha512(key, data)
{
var bkey = rstr2binb(key);
if(bkey.length > 32) bkey = binb_sha512(bkey, key.length * 8);
var ipad = Array(32), opad = Array(32);
for(var i = 0; i < 32; i++)
{
ipad[i] = bkey[i] ^ 0x36363636;
opad[i] = bkey[i] ^ 0x5C5C5C5C;
}
var hash = binb_sha512(ipad.concat(rstr2binb(data)), 1024 + data.length * 8);
return binb2rstr(binb_sha512(opad.concat(hash), 1024 + 512));
}
/*
* Convert a raw string to a hex string
*/
function rstr2hex(input)
{
try { hexcase } catch(e) { hexcase=0; }
var hex_tab = hexcase ? "0123456789ABCDEF" : "0123456789abcdef";
var output = "";
var x;
for(var i = 0; i < input.length; i++)
{
x = input.charCodeAt(i);
output += hex_tab.charAt((x >>> 4) & 0x0F)
+ hex_tab.charAt( x & 0x0F);
}
return output;
}
/*
* Convert a raw string to a base-64 string
*/
function rstr2b64(input)
{
try { b64pad } catch(e) { b64pad=''; }
var tab = "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/";
var output = "";
var len = input.length;
for(var i = 0; i < len; i += 3)
{
var triplet = (input.charCodeAt(i) << 16)
| (i + 1 < len ? input.charCodeAt(i+1) << 8 : 0)
| (i + 2 < len ? input.charCodeAt(i+2) : 0);
for(var j = 0; j < 4; j++)
{
if(i * 8 + j * 6 > input.length * 8) output += b64pad;
else output += tab.charAt((triplet >>> 6*(3-j)) & 0x3F);
}
}
return output;
}
/*
* Convert a raw string to an arbitrary string encoding
*/
function rstr2any(input, encoding)
{
var divisor = encoding.length;
var i, j, q, x, quotient;
/* Convert to an array of 16-bit big-endian values, forming the dividend */
var dividend = Array(Math.ceil(input.length / 2));
for(i = 0; i < dividend.length; i++)
{
dividend[i] = (input.charCodeAt(i * 2) << 8) | input.charCodeAt(i * 2 + 1);
}
/*
* Repeatedly perform a long division. The binary array forms the dividend,
* the length of the encoding is the divisor. Once computed, the quotient
* forms the dividend for the next step. All remainders are stored for later
* use.
*/
var full_length = Math.ceil(input.length * 8 /
(Math.log(encoding.length) / Math.log(2)));
var remainders = Array(full_length);
for(j = 0; j < full_length; j++)
{
quotient = Array();
x = 0;
for(i = 0; i < dividend.length; i++)
{
x = (x << 16) + dividend[i];
q = Math.floor(x / divisor);
x -= q * divisor;
if(quotient.length > 0 || q > 0)
quotient[quotient.length] = q;
}
remainders[j] = x;
dividend = quotient;
}
/* Convert the remainders to the output string */
var output = "";
for(i = remainders.length - 1; i >= 0; i--)
output += encoding.charAt(remainders[i]);
return output;
}
/*
* Encode a string as utf-8.
* For efficiency, this assumes the input is valid utf-16.
*/
function str2rstr_utf8(input)
{
var output = "";
var i = -1;
var x, y;
while(++i < input.length)
{
/* Decode utf-16 surrogate pairs */
x = input.charCodeAt(i);
y = i + 1 < input.length ? input.charCodeAt(i + 1) : 0;
if(0xD800 <= x && x <= 0xDBFF && 0xDC00 <= y && y <= 0xDFFF)
{
x = 0x10000 + ((x & 0x03FF) << 10) + (y & 0x03FF);
i++;
}
/* Encode output as utf-8 */
if(x <= 0x7F)
output += String.fromCharCode(x);
else if(x <= 0x7FF)
output += String.fromCharCode(0xC0 | ((x >>> 6 ) & 0x1F),
0x80 | ( x & 0x3F));
else if(x <= 0xFFFF)
output += String.fromCharCode(0xE0 | ((x >>> 12) & 0x0F),
0x80 | ((x >>> 6 ) & 0x3F),
0x80 | ( x & 0x3F));
else if(x <= 0x1FFFFF)
output += String.fromCharCode(0xF0 | ((x >>> 18) & 0x07),
0x80 | ((x >>> 12) & 0x3F),
0x80 | ((x >>> 6 ) & 0x3F),
0x80 | ( x & 0x3F));
}
return output;
}
/*
* Encode a string as utf-16
*/
function str2rstr_utf16le(input)
{
var output = "";
for(var i = 0; i < input.length; i++)
output += String.fromCharCode( input.charCodeAt(i) & 0xFF,
(input.charCodeAt(i) >>> 8) & 0xFF);
return output;
}
function str2rstr_utf16be(input)
{
var output = "";
for(var i = 0; i < input.length; i++)
output += String.fromCharCode((input.charCodeAt(i) >>> 8) & 0xFF,
input.charCodeAt(i) & 0xFF);
return output;
}
/*
* Convert a raw string to an array of big-endian words
* Characters >255 have their high-byte silently ignored.
*/
function rstr2binb(input)
{
var output = Array(input.length >> 2);
for(var i = 0; i < output.length; i++)
output[i] = 0;
for(var i = 0; i < input.length * 8; i += 8)
output[i>>5] |= (input.charCodeAt(i / 8) & 0xFF) << (24 - i % 32);
return output;
}
/*
* Convert an array of big-endian words to a string
*/
function binb2rstr(input)
{
var output = "";
for(var i = 0; i < input.length * 32; i += 8)
output += String.fromCharCode((input[i>>5] >>> (24 - i % 32)) & 0xFF);
return output;
}
/*
* Calculate the SHA-512 of an array of big-endian dwords, and a bit length
*/
var sha512_k;
function binb_sha512(x, len)
{
if(sha512_k == undefined)
{
//SHA512 constants
sha512_k = new Array(
new int64(0x428a2f98, -685199838), new int64(0x71374491, 0x23ef65cd),
new int64(-1245643825, -330482897), new int64(-373957723, -2121671748),
new int64(0x3956c25b, -213338824), new int64(0x59f111f1, -1241133031),
new int64(-1841331548, -1357295717), new int64(-1424204075, -630357736),
new int64(-670586216, -1560083902), new int64(0x12835b01, 0x45706fbe),
new int64(0x243185be, 0x4ee4b28c), new int64(0x550c7dc3, -704662302),
new int64(0x72be5d74, -226784913), new int64(-2132889090, 0x3b1696b1),
new int64(-1680079193, 0x25c71235), new int64(-1046744716, -815192428),
new int64(-459576895, -1628353838), new int64(-272742522, 0x384f25e3),
new int64(0xfc19dc6, -1953704523), new int64(0x240ca1cc, 0x77ac9c65),
new int64(0x2de92c6f, 0x592b0275), new int64(0x4a7484aa, 0x6ea6e483),
new int64(0x5cb0a9dc, -1119749164), new int64(0x76f988da, -2096016459),
new int64(-1740746414, -295247957), new int64(-1473132947, 0x2db43210),
new int64(-1341970488, -1728372417), new int64(-1084653625, -1091629340),
new int64(-958395405, 0x3da88fc2), new int64(-710438585, -1828018395),
new int64(0x6ca6351, -536640913), new int64(0x14292967, 0xa0e6e70),
new int64(0x27b70a85, 0x46d22ffc), new int64(0x2e1b2138, 0x5c26c926),
new int64(0x4d2c6dfc, 0x5ac42aed), new int64(0x53380d13, -1651133473),
new int64(0x650a7354, -1951439906), new int64(0x766a0abb, 0x3c77b2a8),
new int64(-2117940946, 0x47edaee6), new int64(-1838011259, 0x1482353b),
new int64(-1564481375, 0x4cf10364), new int64(-1474664885, -1136513023),
new int64(-1035236496, -789014639), new int64(-949202525, 0x654be30),
new int64(-778901479, -688958952), new int64(-694614492, 0x5565a910),
new int64(-200395387, 0x5771202a), new int64(0x106aa070, 0x32bbd1b8),
new int64(0x19a4c116, -1194143544), new int64(0x1e376c08, 0x5141ab53),
new int64(0x2748774c, -544281703), new int64(0x34b0bcb5, -509917016),
new int64(0x391c0cb3, -976659869), new int64(0x4ed8aa4a, -482243893),
new int64(0x5b9cca4f, 0x7763e373), new int64(0x682e6ff3, -692930397),
new int64(0x748f82ee, 0x5defb2fc), new int64(0x78a5636f, 0x43172f60),
new int64(-2067236844, -1578062990), new int64(-1933114872, 0x1a6439ec),
new int64(-1866530822, 0x23631e28), new int64(-1538233109, -561857047),
new int64(-1090935817, -1295615723), new int64(-965641998, -479046869),
new int64(-903397682, -366583396), new int64(-779700025, 0x21c0c207),
new int64(-354779690, -840897762), new int64(-176337025, -294727304),
new int64(0x6f067aa, 0x72176fba), new int64(0xa637dc5, -1563912026),
new int64(0x113f9804, -1090974290), new int64(0x1b710b35, 0x131c471b),
new int64(0x28db77f5, 0x23047d84), new int64(0x32caab7b, 0x40c72493),
new int64(0x3c9ebe0a, 0x15c9bebc), new int64(0x431d67c4, -1676669620),
new int64(0x4cc5d4be, -885112138), new int64(0x597f299c, -60457430),
new int64(0x5fcb6fab, 0x3ad6faec), new int64(0x6c44198c, 0x4a475817));
}
//Initial hash values
var H = new Array(
new int64(0x6a09e667, -205731576),
new int64(-1150833019, -2067093701),
new int64(0x3c6ef372, -23791573),
new int64(-1521486534, 0x5f1d36f1),
new int64(0x510e527f, -1377402159),
new int64(-1694144372, 0x2b3e6c1f),
new int64(0x1f83d9ab, -79577749),
new int64(0x5be0cd19, 0x137e2179));
var T1 = new int64(0, 0),
T2 = new int64(0, 0),
a = new int64(0,0),
b = new int64(0,0),
c = new int64(0,0),
d = new int64(0,0),
e = new int64(0,0),
f = new int64(0,0),
g = new int64(0,0),
h = new int64(0,0),
//Temporary variables not specified by the document
s0 = new int64(0, 0),
s1 = new int64(0, 0),
Ch = new int64(0, 0),
Maj = new int64(0, 0),
r1 = new int64(0, 0),
r2 = new int64(0, 0),
r3 = new int64(0, 0);
var j, i;
var W = new Array(80);
for(i=0; i<80; i++)
W[i] = new int64(0, 0);
// append padding to the source string. The format is described in the FIPS.
x[len >> 5] |= 0x80 << (24 - (len & 0x1f));
x[((len + 128 >> 10)<< 5) + 31] = len;
for(i = 0; i<x.length; i+=32) //32 dwords is the block size
{
int64copy(a, H[0]);
int64copy(b, H[1]);
int64copy(c, H[2]);
int64copy(d, H[3]);
int64copy(e, H[4]);
int64copy(f, H[5]);
int64copy(g, H[6]);
int64copy(h, H[7]);
for(j=0; j<16; j++)
{
W[j].h = x[i + 2*j];
W[j].l = x[i + 2*j + 1];
}
for(j=16; j<80; j++)
{
//sigma1
int64rrot(r1, W[j-2], 19);
int64revrrot(r2, W[j-2], 29);
int64shr(r3, W[j-2], 6);
s1.l = r1.l ^ r2.l ^ r3.l;
s1.h = r1.h ^ r2.h ^ r3.h;
//sigma0
int64rrot(r1, W[j-15], 1);
int64rrot(r2, W[j-15], 8);
int64shr(r3, W[j-15], 7);
s0.l = r1.l ^ r2.l ^ r3.l;
s0.h = r1.h ^ r2.h ^ r3.h;
int64add4(W[j], s1, W[j-7], s0, W[j-16]);
}
for(j = 0; j < 80; j++)
{
//Ch
Ch.l = (e.l & f.l) ^ (~e.l & g.l);
Ch.h = (e.h & f.h) ^ (~e.h & g.h);
//Sigma1
int64rrot(r1, e, 14);
int64rrot(r2, e, 18);
int64revrrot(r3, e, 9);
s1.l = r1.l ^ r2.l ^ r3.l;
s1.h = r1.h ^ r2.h ^ r3.h;
//Sigma0
int64rrot(r1, a, 28);
int64revrrot(r2, a, 2);
int64revrrot(r3, a, 7);
s0.l = r1.l ^ r2.l ^ r3.l;
s0.h = r1.h ^ r2.h ^ r3.h;
//Maj
Maj.l = (a.l & b.l) ^ (a.l & c.l) ^ (b.l & c.l);
Maj.h = (a.h & b.h) ^ (a.h & c.h) ^ (b.h & c.h);
int64add5(T1, h, s1, Ch, sha512_k[j], W[j]);
int64add(T2, s0, Maj);
int64copy(h, g);
int64copy(g, f);
int64copy(f, e);
int64add(e, d, T1);
int64copy(d, c);
int64copy(c, b);
int64copy(b, a);
int64add(a, T1, T2);
}
int64add(H[0], H[0], a);
int64add(H[1], H[1], b);
int64add(H[2], H[2], c);
int64add(H[3], H[3], d);
int64add(H[4], H[4], e);
int64add(H[5], H[5], f);
int64add(H[6], H[6], g);
int64add(H[7], H[7], h);
}
//represent the hash as an array of 32-bit dwords
var hash = new Array(16);
for(i=0; i<8; i++)
{
hash[2*i] = H[i].h;
hash[2*i + 1] = H[i].l;
}
return hash;
}
//A constructor for 64-bit numbers
function int64(h, l)
{
this.h = h;
this.l = l;
//this.toString = int64toString;
}
//Copies src into dst, assuming both are 64-bit numbers
function int64copy(dst, src)
{
dst.h = src.h;
dst.l = src.l;
}
//Right-rotates a 64-bit number by shift
//Won't handle cases of shift>=32
//The function revrrot() is for that
function int64rrot(dst, x, shift)
{
dst.l = (x.l >>> shift) | (x.h << (32-shift));
dst.h = (x.h >>> shift) | (x.l << (32-shift));
}
//Reverses the dwords of the source and then rotates right by shift.
//This is equivalent to rotation by 32+shift
function int64revrrot(dst, x, shift)
{
dst.l = (x.h >>> shift) | (x.l << (32-shift));
dst.h = (x.l >>> shift) | (x.h << (32-shift));
}
//Bitwise-shifts right a 64-bit number by shift
//Won't handle shift>=32, but it's never needed in SHA512
function int64shr(dst, x, shift)
{
dst.l = (x.l >>> shift) | (x.h << (32-shift));
dst.h = (x.h >>> shift);
}
//Adds two 64-bit numbers
//Like the original implementation, does not rely on 32-bit operations
function int64add(dst, x, y)
{
var w0 = (x.l & 0xffff) + (y.l & 0xffff);
var w1 = (x.l >>> 16) + (y.l >>> 16) + (w0 >>> 16);
var w2 = (x.h & 0xffff) + (y.h & 0xffff) + (w1 >>> 16);
var w3 = (x.h >>> 16) + (y.h >>> 16) + (w2 >>> 16);
dst.l = (w0 & 0xffff) | (w1 << 16);
dst.h = (w2 & 0xffff) | (w3 << 16);
}
//Same, except with 4 addends. Works faster than adding them one by one.
function int64add4(dst, a, b, c, d)
{
var w0 = (a.l & 0xffff) + (b.l & 0xffff) + (c.l & 0xffff) + (d.l & 0xffff);
var w1 = (a.l >>> 16) + (b.l >>> 16) + (c.l >>> 16) + (d.l >>> 16) + (w0 >>> 16);
var w2 = (a.h & 0xffff) + (b.h & 0xffff) + (c.h & 0xffff) + (d.h & 0xffff) + (w1 >>> 16);
var w3 = (a.h >>> 16) + (b.h >>> 16) + (c.h >>> 16) + (d.h >>> 16) + (w2 >>> 16);
dst.l = (w0 & 0xffff) | (w1 << 16);
dst.h = (w2 & 0xffff) | (w3 << 16);
}
//Same, except with 5 addends
function int64add5(dst, a, b, c, d, e)
{
var w0 = (a.l & 0xffff) + (b.l & 0xffff) + (c.l & 0xffff) + (d.l & 0xffff) + (e.l & 0xffff);
var w1 = (a.l >>> 16) + (b.l >>> 16) + (c.l >>> 16) + (d.l >>> 16) + (e.l >>> 16) + (w0 >>> 16);
var w2 = (a.h & 0xffff) + (b.h & 0xffff) + (c.h & 0xffff) + (d.h & 0xffff) + (e.h & 0xffff) + (w1 >>> 16);
var w3 = (a.h >>> 16) + (b.h >>> 16) + (c.h >>> 16) + (d.h >>> 16) + (e.h >>> 16) + (w2 >>> 16);
dst.l = (w0 & 0xffff) | (w1 << 16);
dst.h = (w2 & 0xffff) | (w3 << 16);
}界面
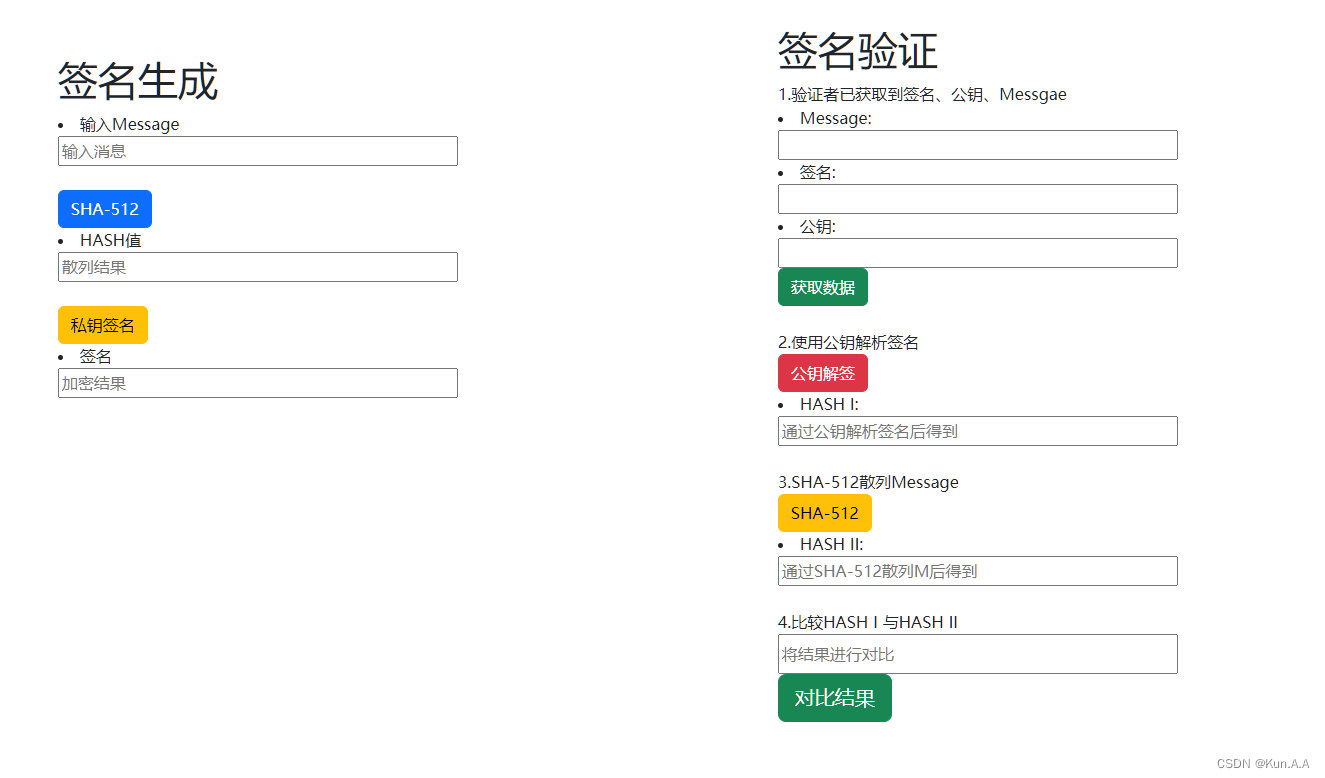
使用方法
书上有公钥秘钥生成顺序,课上应该也会讲,不会的地方评论或者私信吧