Conference:ACM SIGSOFT International Symposium on Software Testing and Analysis (ISSTA)
CCF level:CCF A
Categories:Software Engineering/System Software/Programming Languages
Year:2023
6
Title:
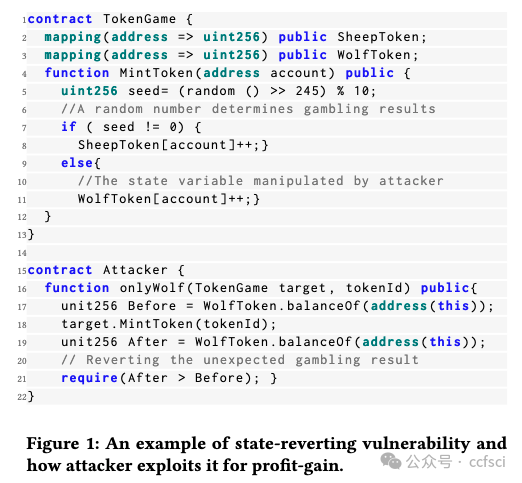
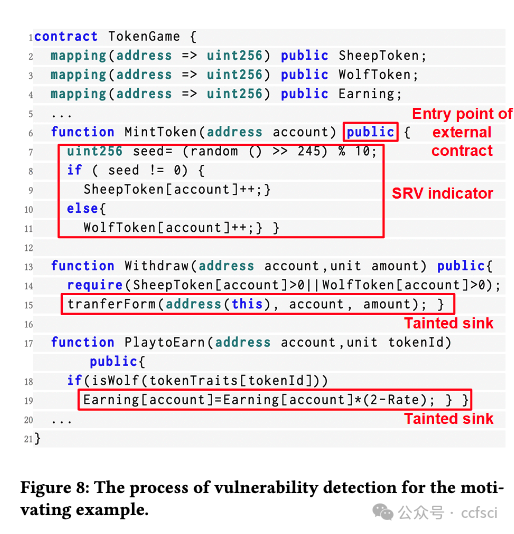
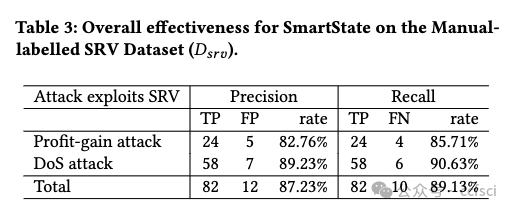
SmartState: Detecting State-Reverting Vulnerabilities in Smart Contracts via Fine-Grained State-Dependency Analysis
SmartState:通过细粒度状态依赖性分析检测智能合约中的状态恢复漏洞
Authors:****

Key words:
bug finding, smart contract, static analysis, state dependency
bug查找、智能合约、静态分析、状态依赖
Abstract:****
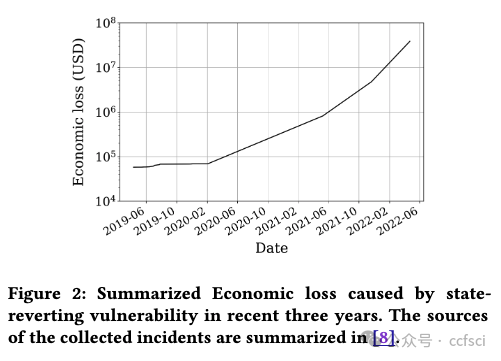
Smart contracts written in Solidity are widely used in different blockchain platforms such as Ethereum, TRON and BNB Chain. One of the unique designs in Solidity smart contracts is its statereverting mechanism for error handling and access control. Unfortunately, a number of recent security incidents showed that adversaries also utilize this mechanism to manipulate critical states of smart contracts, and hence, bring security consequences such as illegal profit-gain and Deny-of-Service (DoS). In this paper, we call such vulnerabilities as the State-reverting Vulnerability (SRV). Automatically identifying SRVs poses unique challenges, as it requires an in-depth analysis and understanding of the state-dependency relations in smart contracts. This paper presents SmartState, a new framework for detecting state-reverting vulnerability in Solidity smart contracts via finegrained state-dependency analysis. SmartState integrates a set of novel mechanisms to ensure its effectiveness. Particularly, Smart- State extracts state dependencies from both contract bytecode and historical transactions. Both of them are critical for inferring dependencies related to SRVs. Further, SmartState models the generic patterns of SRVs (i.e., profit-gain and DoS) as SRV indicators, and hence effectively identify SRVs based on the constructed statedependency graph. To evaluate SmartState, we manually annotated a ground-truth dataset which contains 91 SRVs in the real world. Evaluation results showed that SmartState achieves a precision of 87.23% and a recall of 89.13%. In addition, SmartState successfully identifies 406 new SRVs from 47,351 real-world smart contracts. 11 of these SRVs are from popular smart contracts with high transaction amounts (i.e., top 2000). In total, our reported SRVs affect a total amount of digital assets worth 428,600 USD.
用 Solidity 编写的智能合约广泛应用于以太坊、波场和 BNB Chain 等不同的区块链平台。Solidity 智能合约的独特设计之一是其用于错误处理和访问控制的状态恢复机制。不幸的是,最近的一些安全事件表明,攻击者还利用这种机制来操纵智能合约的关键状态,从而带来非法获利和拒绝服务 (DoS) 等安全后果。在本文中,我们将此类漏洞称为状态恢复漏洞 (SRV)。自动识别 SRV 带来了独特的挑战,因为它需要深入分析和理解智能合约中的状态依赖关系。本文介绍了 SmartState,这是一种通过细粒度状态依赖分析检测 Solidity 智能合约中状态恢复漏洞的新框架。SmartState 集成了一套新颖的机制来确保其有效性。特别是,Smart-State 从合约字节码和历史交易中提取状态依赖关系。它们两者对于推断与 SRV 相关的依赖关系都至关重要。此外,SmartState 将 SRV 的通用模式(即利润收益和 DoS)建模为 SRV 指标,从而根据构建的状态依赖图有效地识别 SRV。为了评估 SmartState,我们手动标注了一个包含现实世界中 91 个 SRV 的真实数据集。评估结果表明,SmartState 的准确率为 87.23%,召回率为 89.13%。此外,SmartState 还从 47,351 个现实世界智能合约中成功识别出 406 个新的 SRV。其中 11 个 SRV 来自交易金额较高的热门智能合约(即前 2000 个)。总的来说,我们报告的 SRV 影响了总价值 428,600 美元的数字资产。



assertion-related state dependency (ASD)
temporal order state dependency (TSD)
Pdf link:
https://dl.acm.org/doi/10.1145/3597926.3598111
7
Title:
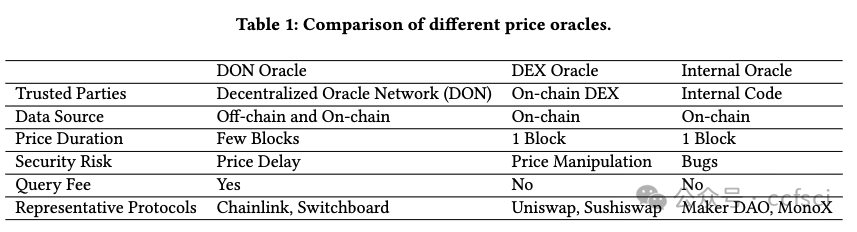
Toward Automated Detecting Unanticipated Price Feed in Smart Contract
在智能合约中自动检测意外价格馈送
Authors:****
Key words:
Smart Contract, Formal Verification, Price Oracle, DeFi
智能合约、形式化验证、价格预言机、DeFi
Abstract:****
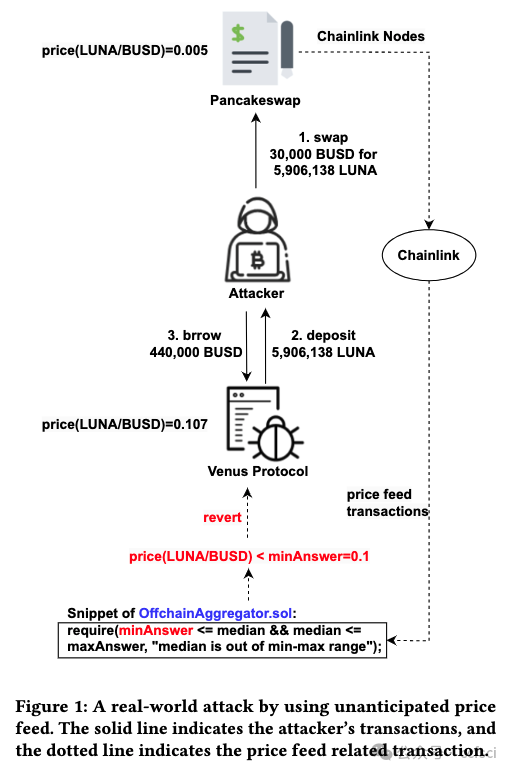
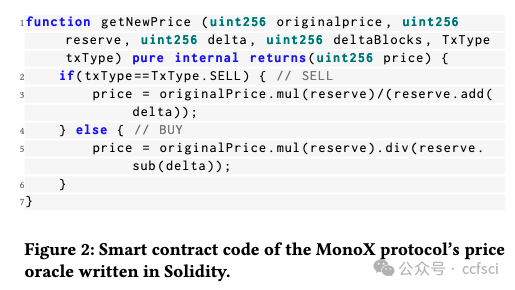
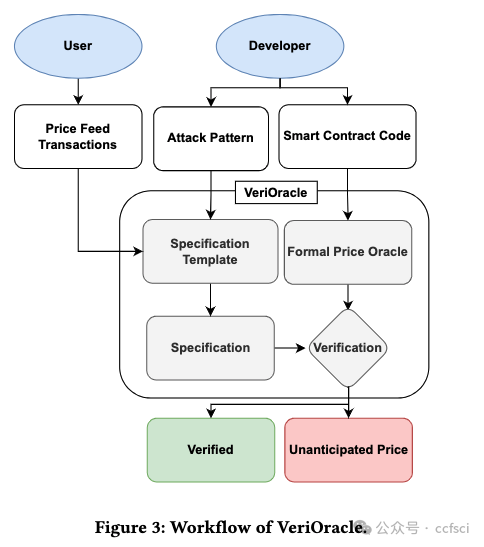
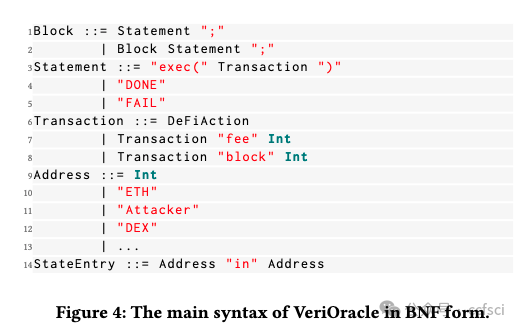
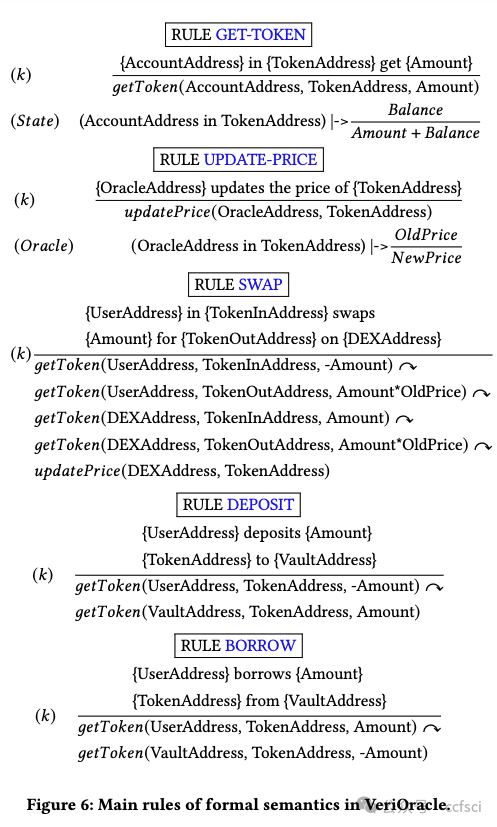
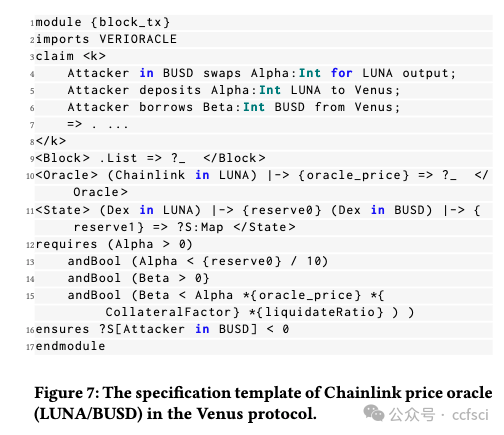
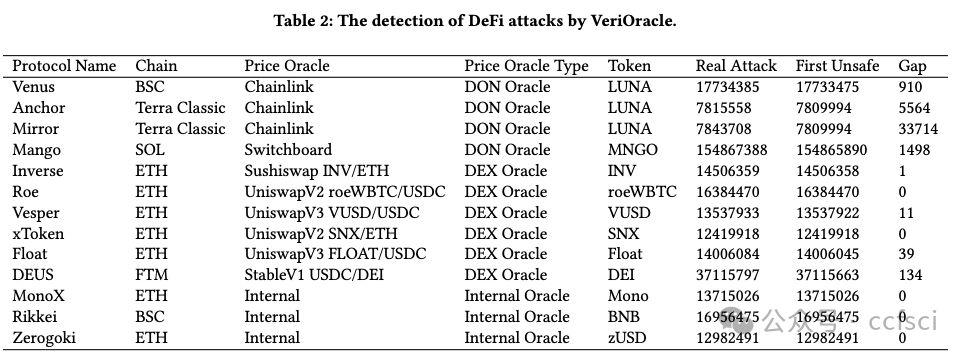
Decentralized finance (DeFi) based on smart contracts has reached a total value locked (TVL) of over USD 200 billion in 2022. In DeFi ecosystems, price oracles play a critical role in providing real-time price feeds for cryptocurrencies to ensure accurate asset pricing in smart contracts. However, the price oracle also faces security issues, including the possibility of unanticipated price feeds, which can lead to imbalances in debt and assets in the DeFi protocol. However, existing solutions cannot effectively combine transactions and code for real-time monitoring of price oracles. To address this limitation, we first categorize price oracles as either DON oracles, DEX oracles, or internal oracles based on trusted parties, and analyze their security risks, data sources, price duration, and query fees. Then, we propose VeriOracle, a formal verification framework for the automated detection of unanticipated price feeds in smart contracts. VeriOracle can deploy a formal semantic model of the price oracle on the blockchain to detect the status of smart contracts and identify unanticipated price feed transactions in real time. We apply VeriOracle to verify over 500,000 transactions of 13 vulnerable DeFi protocols in the real world. The experimental results show that (1) VeriOracle is effective and it can detect unanticipated price feeds before DeFi attacks (33,714 blocks ahead of the attacker in the best case); (2) VeriOracle is efficient in that its verification time (about 4s) is less than the block time of Ethereum (about 14s), which means VeriOracle can detect unsafe transactions in real time; and (3) VeriOracle is extendable for verifying defense strategies. Attacks using unanticipated price feeds can only succeed in particular smart contract states. VeriOracle can verify which smart contract states can defend against attacks.
基于智能合约的去中心化金融 (DeFi) 已在 2022 年达到超过 2000 亿美元的总锁定价值 (TVL)。在 DeFi 生态系统中,价格预言机在为加密货币提供实时价格信息以确保智能合约中资产定价准确方面发挥着关键作用。然而,价格预言机也面临安全问题,包括可能出现意外的价格信息,这可能导致 DeFi 协议中的债务和资产不平衡。然而,现有的解决方案无法有效地结合交易和代码来实时监控价格预言机。为了解决这一限制,我们首先根据可信方将价格预言机分类为 DON 预言机、DEX 预言机或内部预言机,并分析它们的安全风险、数据来源、价格持续时间和查询费用。然后,我们提出了 VeriOracle,这是一个用于自动检测智能合约中意外价格信息的形式化验证框架。VeriOracle 可以在区块链上部署价格预言机的形式化语义模型,以检测智能合约的状态并实时识别意外的价格馈送交易。我们应用 VeriOracle 验证了现实世界中 13 个易受攻击的 DeFi 协议的 500,000 多笔交易。实验结果表明:(1)VeriOracle 是有效的,它可以在 DeFi 攻击之前检测到意外的价格馈送(最好情况下比攻击者提前 33,714 个区块);(2)VeriOracle 的验证时间(约 4 秒)小于以太坊的出块时间(约 14 秒),这意味着 VeriOracle 可以实时检测不安全的交易;(3)VeriOracle 可扩展以验证防御策略。使用意外价格馈送的攻击只能在特定的智能合约状态下成功。VeriOracle 可以验证哪些智能合约状态可以抵御攻击。
decentralized exchanges (DEX)
Decentralized Oracle Networks (DONs)
Pdf link:
https://dl.acm.org/doi/10.1145/3597926.3598133
8
Title:
Detecting State Inconsistency Bugs in DApps via On-Chain Transaction Replay and Fuzzing
通过链上交易重放和模糊测试检测 DApp 中的状态不一致错误
Authors:****
Mingxi Ye,Sun Yat-sen University,China
Yuhong Nan,Sun Yat-sen University
Zibin Zheng,Sun Yat-sen University
Dongpeng Wu, Sun Yat-sen University
Huizhong Li, WeBank,China
Abstract:****
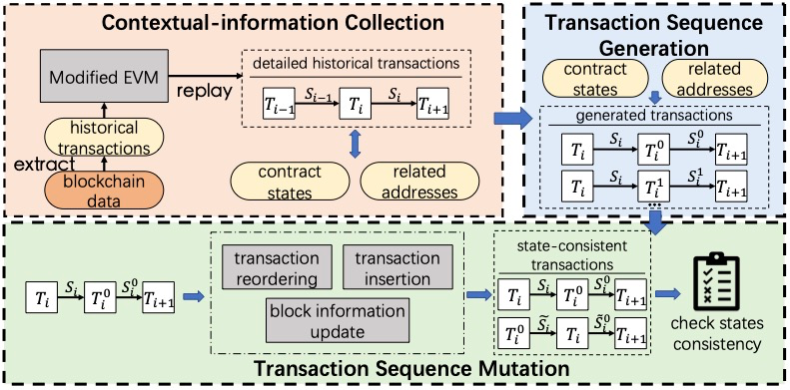
Decentralized applications (DApps) consist of multiple smart contracts running on Blockchain. With the increasing popularity of the DApp ecosystem, vulnerabilities in DApps could bring significant impacts such as financial losses. Identifying vulnerabilities in DApps is by no means trivial, as modern DApps consist of complex interactions across multiple contracts. Previous research suffers from either high false positives or false negatives, due to the lack of precise contextual information which is mandatory for confirming smart contract vulnerabilities when analyzing smart contracts. In this paper, we present IcyChecker, a new fuzzing-based framework to effectively identify State inconsistency (SI) Bugs -- a specific type of bugs that can cause vulnerabilities such as re-entrancy, front-running with complex patterns. Different from prior works, IcyChecker utilizes a set of accurate contextual information for contract fuzzing by replaying the on-chain historical transactions. Besides, instead of designing specific testing oracles which are required by other fuzzing approaches, IcyChecker implements novel mechanisms to mutate a set of fuzzing transaction sequences, and further identify SI bugs by observing their state differences. Evaluation of IcyChecker over the top 100 popular DApps showed it effectively identifies a total number of 277 SI bugs, with a precision of 87%. By comparing IcyChecker with other state-of-the-art tools (i.e., Smartian, Confuzzius, and Sailfish), we show IcyChecker not only identifies more SI bugs but also with much lower false positives, thanks to its integration of accurate on-chain data and unique fuzzing strategies. Our research sheds light on new ways of detecting smart contract vulnerabilities in DApps.
去中心化应用程序(DApps)由在区块链上运行的多个智能合约组成。随着 DApp 生态系统的日益普及,DApp 中的漏洞可能会带来重大影响,例如财务损失。识别 DApp 中的漏洞绝非易事,因为现代 DApp 包含跨多个合约的复杂交互。先前的研究存在高误报率或漏报率,这是因为缺乏精确的上下文信息,而这些信息在分析智能合约时对于确认智能合约漏洞是必不可少的。在本文中,我们提出了 IcyChecker,这是一个基于模糊测试的新框架,可有效识别状态不一致(SI)错误 - 这是一种特定类型的错误,可能导致诸如重入、具有复杂模式的抢先交易等漏洞。与之前的研究不同,IcyChecker 通过重放链上历史交易,利用一组准确的上下文信息进行合约模糊测试。此外,IcyChecker 无需设计其他模糊测试方法所需的特定测试预言机,而是实现了新颖的机制来改变一组模糊测试交易序列,并通过观察它们的状态差异进一步识别 SI 错误。对前 100 个流行 DApp 的 IcyChecker 评估表明,它有效识别了总共 277 个 SI 错误,准确率为 87%。通过将 IcyChecker 与其他最先进的工具(即 Smartian、Confuzzius 和 Sailfish)进行比较,我们发现 IcyChecker 不仅可以识别出更多的 SI 错误,而且由于其集成了准确的链上数据和独特的模糊测试策略,误报率也低得多。我们的研究为检测 DApp 中的智能合约漏洞的新方法提供了启示。
Pdf link:
https://dl.acm.org/doi/10.1145/3597926.3598057
9
Title:
DeFiTainter: Detecting Price Manipulation Vulnerabilities in DeFi Protocols
DeFiTainter:检测 DeFi 协议中的价格操纵漏洞
Authors:****
Key words:
vulnerability detection, smart contract, taint analysis
漏洞检测、智能合约、污点分析
Abstract:****
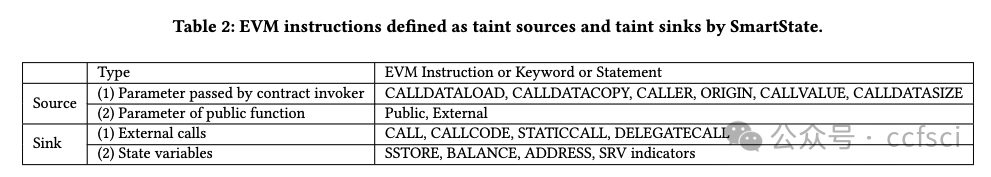
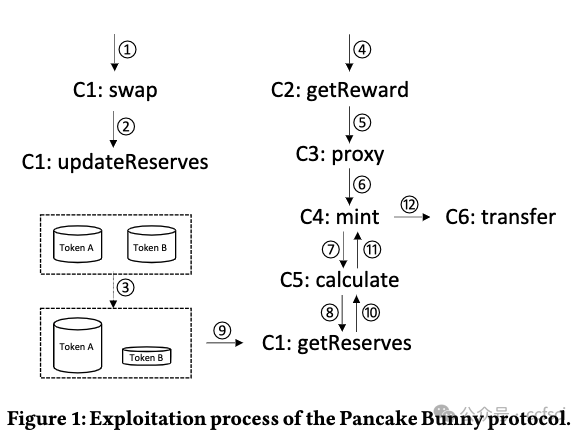
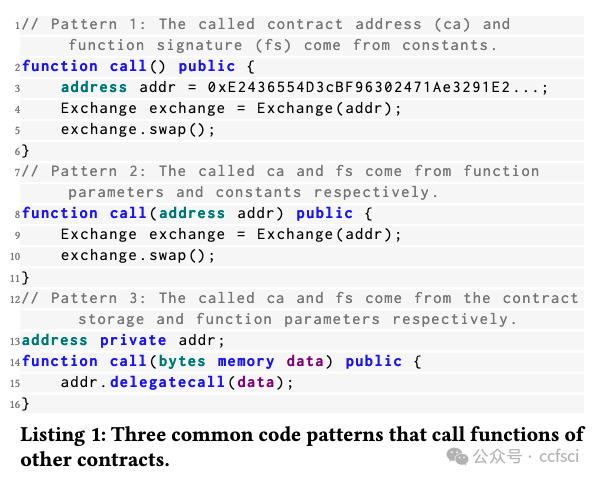
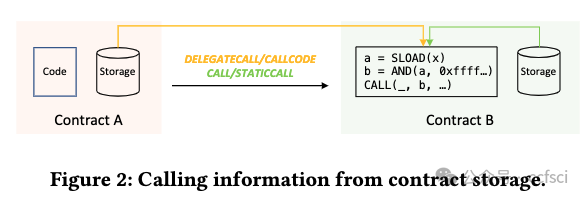
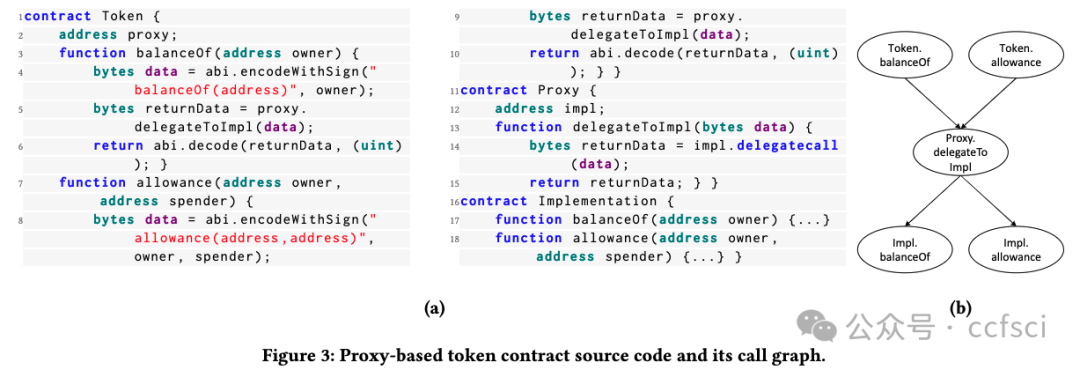
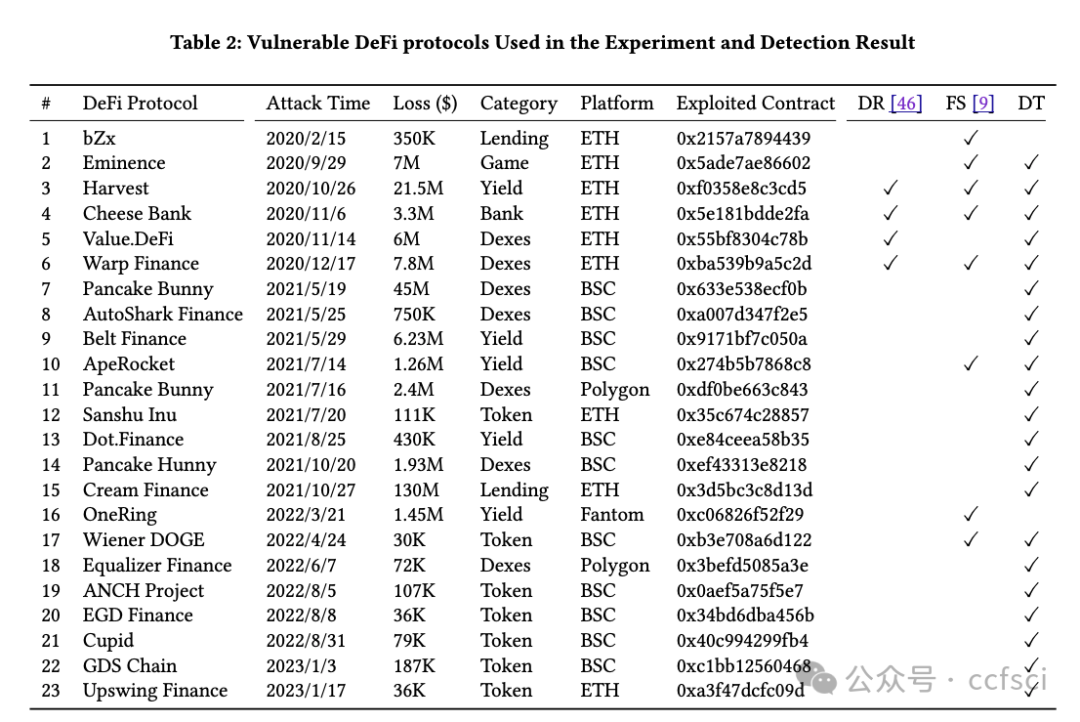
DeFi protocols are programs that manage high-value digital assets on blockchain. The price manipulation vulnerability is one of the common vulnerabilities in DeFi protocols, which allows attackers to gain excessive profits by manipulating token prices. In this paper, we propose DeFiTainter, an inter-contract taint analysis framework for detecting price manipulation vulnerabilities. DeFiTainter features two innovative mechanisms to ensure its effectiveness. The first mechanism is to construct a call graph for inter-contract taint analysis by restoring call information, not only from code constants but also from contract storage and function parameters. The second mechanism is a high-level semantic induction tailored for detecting price manipulation vulnerabilities, which accurately identifies taint sources and sinks and tracks taint data across contracts. Extensive evaluation of real-world incidents and high-value DeFi protocols shows that DeFiTainter outperforms existing approaches and achieves state-of-the-art performance with a precision of 96% and a recall of 91.3% in detecting price manipulation vulnerabilities. Furthermore, DeFiTainter uncovers three previously undisclosed price manipulation vulnerabilities.
DeFi 协议是管理区块链上高价值数字资产的程序。价格操纵漏洞是 DeFi 协议中常见的漏洞之一,攻击者可以通过操纵代币价格获取超额利润。本文提出了 DeFiTainter,一个用于检测价格操纵漏洞的合约间污点分析框架。DeFiTainter 具有两种创新机制来确保其有效性。第一种机制是通过恢复调用信息来构建合约间污点分析的调用图,不仅从代码常量,而且从合约存储和函数参数中恢复调用信息。第二种机制是专门为检测价格操纵漏洞而定制的高级语义归纳,它可以准确识别污点源和污点接收器并跟踪跨合约的污点数据。对现实世界事件和高价值 DeFi 协议的广泛评估表明,DeFiTainter 优于现有方法,在检测价格操纵漏洞方面以 96% 的准确率和 91.3% 的召回率实现了最先进的性能。此外,DeFiTainter 还发现了三个以前未披露的价格操纵漏洞。

Pdf link:
https://dl.acm.org/doi/10.1145/3597926.3598124

关注我们,持续接收区块链最新论文
洞察区块链技术发展趋势
Follow us to keep receiving the latest blockchain papers
Insight into Blockchain Technology Trends