一、实验要求与目的
1) 学习AES密码算法原理
2) 学习AES密码算法编程实现
二、实验内容与步骤记录(只记录关键步骤与结果,可截图,但注意排版与图片大小)
字符串加解密
运行python程序,输入密文,即可在第一个框格中输入密文,即可得到加密字符串。
重要步骤:自顶向下,逐步求精,设计好AES每一个操作。
重要的操作有密钥产生、字节代换、行移位及其逆变换、列混合及其逆变换、轮密钥加五项,分别为AES加密的五个函数板块。
同时,写查询函数:
这样可以得出查询结果,以便更好控制中间过程量,例如加密helloworld:
三、源代码记录(关键代码需备注)
python
# S盒
S_BOX = [
0x63, 0x7c, 0x77, 0x7b, 0xf2, 0x6b, 0x6f, 0xc5, 0x30, 0x01, 0x67, 0x2b, 0xfe, 0xd7, 0xab, 0x76,
0xca, 0x82, 0xc9, 0x7d, 0xfa, 0x59, 0x47, 0xf0, 0xad, 0xd4, 0xa2, 0xaf, 0x9c, 0xa4, 0x72, 0xc0,
0xb7, 0xfd, 0x93, 0x26, 0x36, 0x3f, 0xf7, 0xcc, 0x34, 0xa5, 0xe5, 0xf1, 0x71, 0xd8, 0x31, 0x15,
0x04, 0xc7, 0x23, 0xc3, 0x18, 0x96, 0x05, 0x9a, 0x07, 0x12, 0x80, 0xe2, 0xeb, 0x27, 0xb2, 0x75,
0x09, 0x83, 0x2c, 0x1a, 0x1b, 0x6e, 0x5a, 0xa0, 0x52, 0x3b, 0xd6, 0xb3, 0x29, 0xe3, 0x2f, 0x84,
0x53, 0xd1, 0x00, 0xed, 0x20, 0xfc, 0xb1, 0x5b, 0x6a, 0xcb, 0xbe, 0x39, 0x4a, 0x4c, 0x58, 0xcf,
0xd0, 0xef, 0xaa, 0xfb, 0x43, 0x4d, 0x33, 0x85, 0x45, 0xf9, 0x02, 0x7f, 0x50, 0x3c, 0x9f, 0xa8,
0x51, 0xa3, 0x40, 0x8f, 0x92, 0x9d, 0x38, 0xf5, 0xbc, 0xb6, 0xda, 0x21, 0x10, 0xff, 0xf3, 0xd2,
0xcd, 0x0c, 0x13, 0xec, 0x5f, 0x97, 0x44, 0x17, 0xc4, 0xa7, 0x7e, 0x3d, 0x64, 0x5d, 0x19, 0x73,
0x60, 0x81, 0x4f, 0xdc, 0x22, 0x2a, 0x90, 0x88, 0x46, 0xee, 0xb8, 0x14, 0xde, 0x5e, 0x0b, 0xdb,
0xe0, 0x32, 0x3a, 0x0a, 0x49, 0x06, 0x24, 0x5c, 0xc2, 0xd3, 0xac, 0x62, 0x91, 0x95, 0xe4, 0x79,
0xe7, 0xc8, 0x37, 0x6d, 0x8d, 0xd5, 0x4e, 0xa9, 0x6c, 0x56, 0xf4, 0xea, 0x65, 0x7a, 0xae, 0x08,
0xba, 0x78, 0x25, 0x2e, 0x1c, 0xa6, 0xb4, 0xc6, 0xe8, 0xdd, 0x74, 0x1f, 0x4b, 0xbd, 0x8b, 0x8a,
0x70, 0x3e, 0xb5, 0x66, 0x48, 0x03, 0xf6, 0x0e, 0x61, 0x35, 0x57, 0xb9, 0x86, 0xc1, 0x1d, 0x9e,
0xe1, 0xf8, 0x98, 0x11, 0x69, 0xd9, 0x8e, 0x94, 0x9b, 0x1e, 0x87, 0xe9, 0xce, 0x55, 0x28, 0xdf,
0x8c, 0xa1, 0x89, 0x0d, 0xbf, 0xe6, 0x42, 0x68, 0x41, 0x99, 0x2d, 0x0f, 0xb0, 0x54, 0xbb, 0x16,
]
# 常量轮 (Rcon)
R_CON = [0x00,0x01,0x02,0x04,0x08,0x10,0x20,0x40,0x80,0x1B,0x36]
# 将16字节明文转4x4矩阵
def bytes_to_matrix(text):
return [list(text[i:i+4]) for i in range(0, len(text), 4)]
# 将矩阵转回16字节
def matrix_to_bytes(matrix):
return bytes(sum(matrix, []))
#------------密钥扩展-----------
def key_expansion(key):
key = [ord(c) for c in key]
if len(key) < 16:
key += [0x00] * (16 - len(key))
elif len(key) > 16:
key = key[:16]
key_schedule = [key[i:i+4] for i in range(0, 16, 4)]
for i in range(4, 44):
temp = key_schedule[i-1]
if i % 4 == 0:
temp = [
S_BOX[temp[1]] ^ R_CON[i//4],
S_BOX[temp[2]],
S_BOX[temp[3]],
S_BOX[temp[0]],
]
word = [a ^ b for a, b in zip(key_schedule[i-4], temp)]
key_schedule.append(word)
return [key_schedule[4*i:4*(i+1)] for i in range(11)]
#------------密钥扩展-----------
#------------字节代换-----------
def sub_bytes(state):
for i in range(4):
for j in range(4):
state[i][j] = S_BOX[state[i][j]]
return state
#------------字节代换-----------
#-------------行移位------------
def shift_rows(state):
for i in range(1, 4):
state[i] = state[i][i:] + state[i][:i]
return state
#-------------行移位------------
# Galois乘法
def galois_multiply(a, b):
p = 0
for i in range(8):
if b & 1:
p ^= a
high_bit_set = a & 0x80
a <<= 1
if high_bit_set:
a ^= 0x1b
a &= 0xFF
b >>= 1
return p % 256
#-------------列混合------------
def mix_columns(state):
for i in range(4):
a = state[0][i]
b = state[1][i]
c = state[2][i]
d = state[3][i]
state[0][i] = galois_multiply(a,2) ^ galois_multiply(b,3) ^ c ^ d
state[1][i] = a ^ galois_multiply(b,2) ^ galois_multiply(c,3) ^ d
state[2][i] = a ^ b ^ galois_multiply(c,2) ^ galois_multiply(d,3)
state[3][i] = galois_multiply(a,3) ^ b ^ c ^ galois_multiply(d,2)
return state
#-------------列混合------------
#------------轮密钥加-----------
def add_round_key(state, round_key):
for i in range(4):
for j in range(4):
state[i][j] ^= round_key[i][j]
return state
#------------轮密钥加-----------
#------------------------AES加密函数----------------------
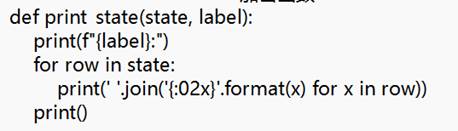
def print_state(state, label):
print(f"{label}:")
for row in state:
print(' '.join('{:02x}'.format(x) for x in row))
print()
def aes_encrypt(plaintext, key="0123456789ABCDEF"):
if len(plaintext) < 16:
plaintext = plaintext.ljust(16, '\0') # 补齐16字节
state = bytes_to_matrix(plaintext.encode('utf-8'))
round_keys = key_expansion(key)
print("初始状态:")
print_state(state, "初始输入")
# -------初始轮密钥加-------
state = add_round_key(state, round_keys[0])
print_state(state, "初始轮密钥加")
for i in range(1, 10):
print(f"-------第{i}轮开始-------")
# -------字节代换-------
state = sub_bytes(state)
print_state(state, f"第{i}轮 字节代换后")
# -------行移位-------
state = shift_rows(state)
print_state(state, f"第{i}轮 行移位后")
# -------列混合-------
state = mix_columns(state)
print_state(state, f"第{i}轮 列混合后")
# -------轮密钥加-------
state = add_round_key(state, round_keys[i])
print_state(state, f"第{i}轮 轮密钥加后")
# 最后一轮没有列混合
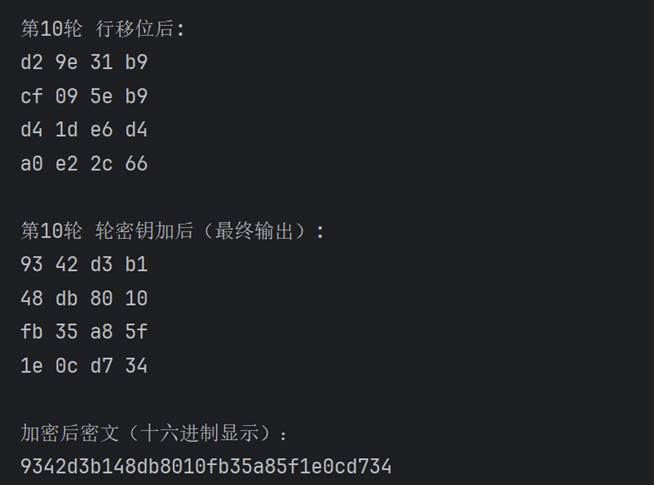
print(f"-------第10轮开始-------")
state = sub_bytes(state)
print_state(state, "第10轮 字节代换后")
state = shift_rows(state)
print_state(state, "第10轮 行移位后")
state = add_round_key(state, round_keys[10])
print_state(state, "第10轮 轮密钥加后(最终输出)")
return matrix_to_bytes(state)
#------------------------AES加密函数----------------------
# 主程序
def main():
plaintext = input("请输入明文:")
ciphertext = aes_encrypt(plaintext)
print("加密后密文(十六进制显示):")
print(''.join('{:02x}'.format(b) for b in ciphertext))
if __name__ == "__main__":
main()四、实验思考
- AES的解密过程是怎样的?
答:AES解密基本上就是加密过程的逆操作,顺序也反过来了,但每步需要用逆运算。具体是:首先将密文与最后一轮的轮密钥进行异或操作(AddRoundKey),随后依次进行多轮逆变换。每一轮解密操作包括四个步骤:①首先进行逆行移位(Inverse ShiftRows),将各行的数据按一定规则向右循环移动;②接着执行逆字节代换(Inverse SubBytes),使用逆S盒还原每个字节;③然后再次进行轮密钥加(AddRoundKey),将数据与对应的轮密钥异或;④在前九轮,还需进行逆列混合(Inverse MixColumns),通过特定的逆矩阵运算还原列间关系。最后一轮解密不再进行逆列混合。整体上,AES解密是加密过程的逆序执行,且每步使用相应的逆操作,从而逐步还原出明文。
