目录
[1. 🎯 开篇:为什么安全测试不再是可选项?](#1. 🎯 开篇:为什么安全测试不再是可选项?)
[2. 🏗️ 安全测试架构设计](#2. 🏗️ 安全测试架构设计)
[2.1 整体安全架构](#2.1 整体安全架构)
[2.2 核心安全测试流程](#2.2 核心安全测试流程)
[2.3 安全测试性能特性](#2.3 安全测试性能特性)
[3. 🔧 核心漏洞防护实战](#3. 🔧 核心漏洞防护实战)
[3.1 SQL注入防护](#3.1 SQL注入防护)
[3.2 XSS防护实战](#3.2 XSS防护实战)
[3.3 CSRF防护实战](#3.3 CSRF防护实战)
[4. 🛠️ 安全扫描工具链](#4. 🛠️ 安全扫描工具链)
[4.1 自动化安全扫描流水线](#4.1 自动化安全扫描流水线)
[4.2 企业级安全工具集成](#4.2 企业级安全工具集成)
[5. 📚 总结与资源](#5. 📚 总结与资源)
[5.1 核心安全原则](#5.1 核心安全原则)
[5.2 官方资源](#5.2 官方资源)
[5.3 企业级最佳实践](#5.3 企业级最佳实践)
🛡️摘要
本文深度解析OWASP Top 10安全威胁的防护策略。重点剖析SQL注入、XSS、CSRF三大核心攻击原理与防御机制,通过5个Mermaid流程图展示完整安全架构。分享真实企业级安全扫描工具链,包含自动化安全测试、漏洞扫描、持续安全监控的完整解决方案。提供可运行的安全测试代码和最佳实践,帮助企业构建纵深防御体系。
1. 🎯 开篇:为什么安全测试不再是可选项?
2019年,我参与处理了一个大型电商平台的安全事件。黑客通过一个简单的SQL注入漏洞,获取了50万用户数据,造成数百万损失。事后分析发现,这个漏洞在代码中隐藏了2年,常规功能测试完全没发现。这让我深刻意识到:安全测试不是锦上添花,而是生存必需。
当前安全现状:
-
**60%** 的数据泄露源于已知漏洞
-
SQL注入 仍是Web应用头号杀手
-
XSS攻击 在单页应用中更加隐蔽
-
自动化攻击 让手工防御不堪重负
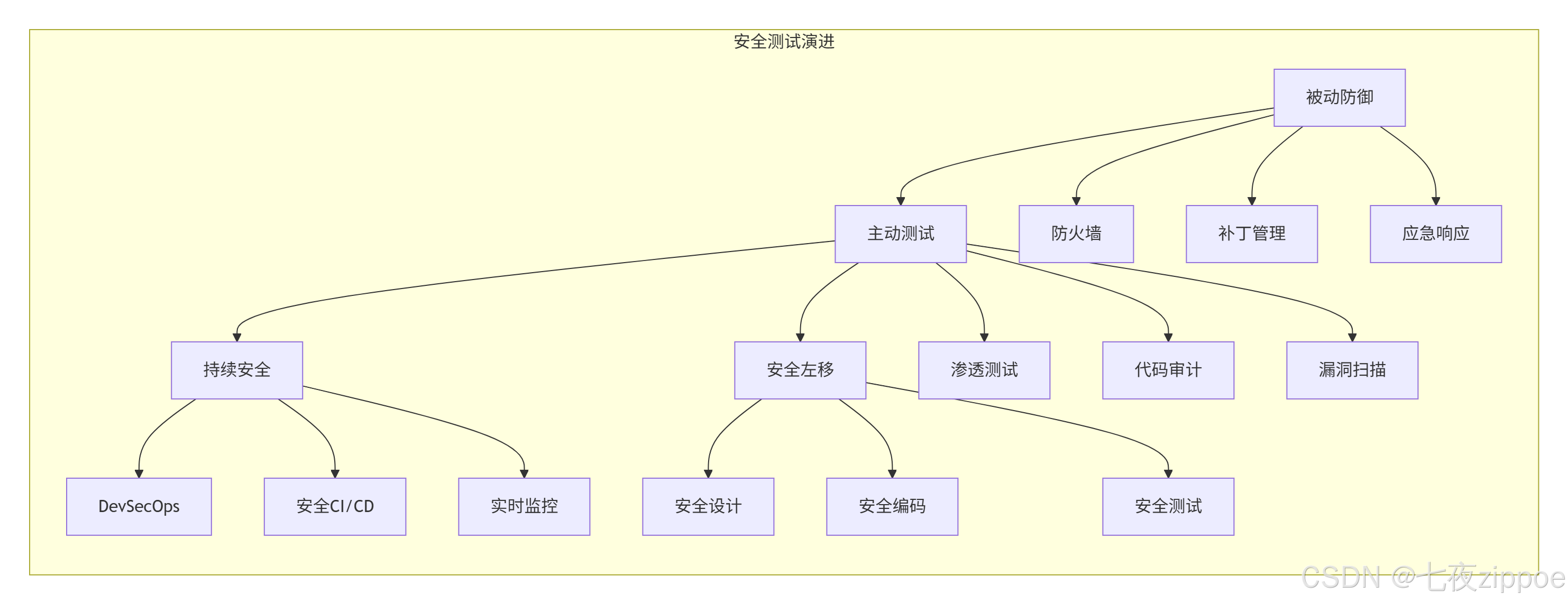
安全测试演进:
2. 🏗️ 安全测试架构设计
2.1 整体安全架构
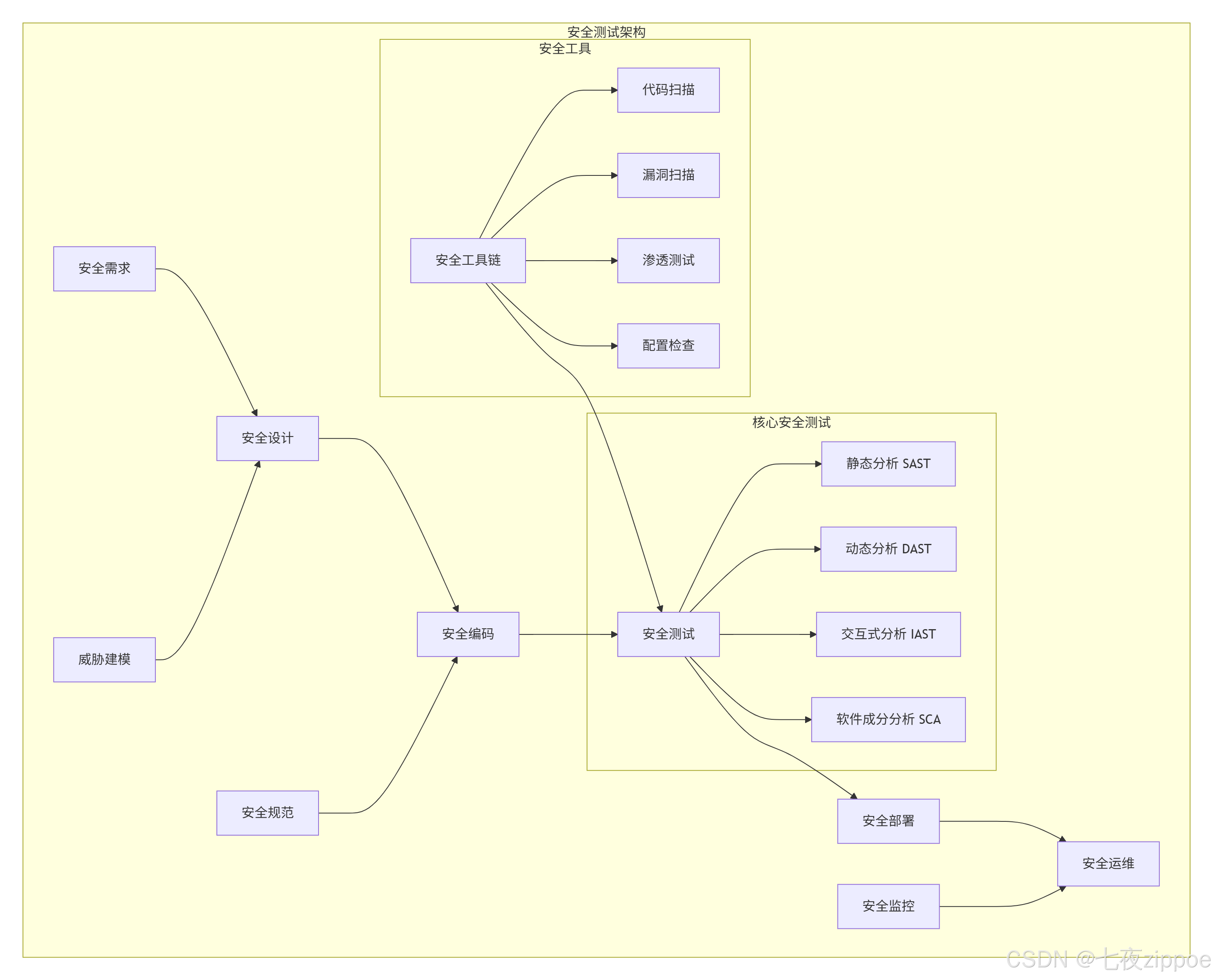
2.2 核心安全测试流程
python
# security_test_architecture.py
"""
安全测试架构核心实现
Python 3.8+,需要安装:pip install bandit safety sqlmap
"""
import subprocess
import json
import yaml
import time
from pathlib import Path
from datetime import datetime
import hashlib
import tempfile
import requests
import sqlite3
from typing import Dict, List, Optional, Any
import logging
class SecurityTestFramework:
"""安全测试框架核心类"""
def __init__(self, config_file="security_config.yaml"):
self.config = self._load_config(config_file)
self.results = {}
self.vulnerabilities = []
self.logger = self._setup_logging()
# 工具路径配置
self.tool_paths = {
'bandit': 'bandit',
'safety': 'safety',
'sqlmap': 'sqlmap',
'zap': 'zap-baseline.py',
'nmap': 'nmap'
}
def _load_config(self, config_file: str) -> Dict[str, Any]:
"""加载安全配置"""
default_config = {
'scan_targets': [],
'exclude_patterns': ['*.pyc', '*.log', 'node_modules/'],
'severity_levels': ['HIGH', 'MEDIUM', 'LOW'],
'report_formats': ['html', 'json', 'csv'],
'max_scan_time': 3600, # 1小时
'allowed_risks': ['LOW']
}
if Path(config_file).exists():
with open(config_file, 'r') as f:
user_config = yaml.safe_load(f)
default_config.update(user_config)
return default_config
def _setup_logging(self):
"""设置日志"""
logging.basicConfig(
level=logging.INFO,
format='%(asctime)s - %(name)s - %(levelname)s - %(message)s',
handlers=[
logging.FileHandler('security_test.log'),
logging.StreamHandler()
]
)
return logging.getLogger(__name__)
def run_security_scan(self, scan_type: str, **kwargs):
"""运行安全扫描"""
self.logger.info(f"开始安全扫描: {scan_type}")
start_time = time.time()
try:
if scan_type == "sast":
result = self._run_sast_scan(**kwargs)
elif scan_type == "dast":
result = self._run_dast_scan(**kwargs)
elif scan_type == "sca":
result = self._run_sca_scan(**kwargs)
elif scan_type == "config":
result = self._run_config_scan(**kwargs)
else:
raise ValueError(f"未知扫描类型: {scan_type}")
# 记录结果
self.results[scan_type] = {
'timestamp': datetime.now().isoformat(),
'duration': time.time() - start_time,
'result': result
}
# 分析漏洞
self._analyze_vulnerabilities(scan_type, result)
return result
except Exception as e:
self.logger.error(f"扫描失败: {scan_type}, 错误: {e}")
return None
def _run_sast_scan(self, target_dir: str = ".") -> Dict[str, Any]:
"""运行静态应用安全测试"""
self.logger.info(f"运行SAST扫描: {target_dir}")
cmd = [
self.tool_paths['bandit'],
'-r', target_dir,
'-f', 'json',
'-o', 'bandit_report.json'
]
# 排除模式
for exclude in self.config['exclude_patterns']:
cmd.extend(['-x', exclude])
try:
result = subprocess.run(cmd, capture_output=True, text=True, timeout=300)
if result.returncode == 0:
with open('bandit_report.json', 'r') as f:
return json.load(f)
else:
self.logger.error(f"Bandit执行失败: {result.stderr}")
return {'errors': [result.stderr], 'results': []}
except subprocess.TimeoutExpired:
self.logger.error("SAST扫描超时")
return {'error': '扫描超时'}
except Exception as e:
self.logger.error(f"SAST扫描异常: {e}")
return {'error': str(e)}
def _run_sca_scan(self) -> Dict[str, Any]:
"""运行软件成分分析"""
self.logger.info("运行SCA扫描")
cmd = [self.tool_paths['safety'], 'check', '--json']
try:
result = subprocess.run(cmd, capture_output=True, text=True)
if result.returncode in [0, 1]: # 0=无漏洞, 1=有漏洞
return json.loads(result.stdout) if result.stdout else {'vulnerabilities': []}
else:
self.logger.error(f"Safety执行失败: {result.stderr}")
return {'error': result.stderr}
except Exception as e:
self.logger.error(f"SCA扫描异常: {e}")
return {'error': str(e)}
def _run_dast_scan(self, target_url: str) -> Dict[str, Any]:
"""运行动态应用安全测试"""
self.logger.info(f"运行DAST扫描: {target_url}")
# 使用sqlmap进行SQL注入测试
sqlmap_result = self._run_sqlmap_scan(target_url)
# 使用自定义扫描器进行XSS测试
xss_result = self._run_xss_scan(target_url)
return {
'sqlmap': sqlmap_result,
'xss_scan': xss_result,
'timestamp': datetime.now().isoformat()
}
def _run_sqlmap_scan(self, target_url: str) -> Dict[str, Any]:
"""运行SQLMap扫描"""
self.logger.info(f"运行SQLMap: {target_url}")
# 创建临时结果文件
with tempfile.NamedTemporaryFile(mode='w', suffix='.json', delete=False) as f:
result_file = f.name
cmd = [
self.tool_paths['sqlmap'],
'-u', target_url,
'--batch',
'--level=3',
'--risk=2',
'--output-dir=sqlmap_results',
'--dump-format=JSON'
]
try:
result = subprocess.run(cmd, capture_output=True, text=True, timeout=600)
# 解析结果
result_data = {
'returncode': result.returncode,
'stdout': result.stdout,
'stderr': result.stderr,
'vulnerabilities_found': 'SQL injection found' in result.stdout
}
return result_data
except subprocess.TimeoutExpired:
self.logger.error("SQLMap扫描超时")
return {'error': '扫描超时'}
except Exception as e:
self.logger.error(f"SQLMap异常: {e}")
return {'error': str(e)}
def _run_xss_scan(self, target_url: str) -> Dict[str, Any]:
"""运行XSS扫描"""
self.logger.info(f"运行XSS扫描: {target_url}")
# 常用XSS payloads
xss_payloads = [
'<script>alert("XSS")</script>',
'<img src=x onerror=alert(1)>',
'"><script>alert(1)</script>',
'javascript:alert(1)',
'<svg onload=alert(1)>'
]
results = []
for payload in xss_payloads:
try:
# 测试GET参数
test_url = f"{target_url}?q={payload}"
response = requests.get(test_url, timeout=5)
# 检查响应中是否包含payload(简单检测)
if payload in response.text:
results.append({
'payload': payload,
'url': test_url,
'vulnerable': True,
'response_preview': response.text[:200]
})
else:
results.append({
'payload': payload,
'url': test_url,
'vulnerable': False
})
except Exception as e:
results.append({
'payload': payload,
'error': str(e)
})
return {
'total_tests': len(xss_payloads),
'vulnerable_count': sum(1 for r in results if r.get('vulnerable', False)),
'results': results
}
def _analyze_vulnerabilities(self, scan_type: str, result: Dict[str, Any]):
"""分析漏洞结果"""
vulnerabilities = []
if scan_type == "sast":
for issue in result.get('results', []):
if issue['issue_severity'] in self.config['severity_levels']:
vulnerabilities.append({
'type': 'SAST',
'severity': issue['issue_severity'],
'file': issue['filename'],
'line': issue['line_number'],
'description': issue['issue_text'],
'confidence': issue['issue_confidence']
})
elif scan_type == "sca":
for vuln in result.get('vulnerabilities', []):
vulnerabilities.append({
'type': 'SCA',
'package': vuln.get('package_name'),
'vulnerability': vuln.get('vulnerability_id'),
'severity': vuln.get('severity', 'UNKNOWN'),
'description': vuln.get('description')
})
elif scan_type == "dast":
if result.get('sqlmap', {}).get('vulnerabilities_found'):
vulnerabilities.append({
'type': 'SQL Injection',
'severity': 'HIGH',
'target': 'Database',
'description': 'SQL注入漏洞发现'
})
for xss_result in result.get('xss_scan', {}).get('results', []):
if xss_result.get('vulnerable'):
vulnerabilities.append({
'type': 'XSS',
'severity': 'MEDIUM',
'target': 'Web Application',
'payload': xss_result.get('payload'),
'description': 'XSS漏洞发现'
})
# 添加到全局漏洞列表
self.vulnerabilities.extend(vulnerabilities)
# 记录发现
if vulnerabilities:
self.logger.warning(f"发现 {len(vulnerabilities)} 个漏洞 in {scan_type}")
else:
self.logger.info(f"{scan_type} 扫描未发现漏洞")
def generate_security_report(self) -> str:
"""生成安全报告"""
report_data = {
'scan_summary': {
'total_scans': len(self.results),
'total_vulnerabilities': len(self.vulnerabilities),
'scan_time': datetime.now().isoformat(),
'duration_sum': sum(r['duration'] for r in self.results.values())
},
'vulnerabilities_by_severity': self._group_vulnerabilities_by_severity(),
'vulnerabilities_by_type': self._group_vulnerabilities_by_type(),
'detailed_findings': self.vulnerabilities,
'recommendations': self._generate_recommendations()
}
# 生成HTML报告
html_report = self._generate_html_report(report_data)
# 保存JSON报告
with open('security_report.json', 'w') as f:
json.dump(report_data, f, indent=2)
return html_report
def _group_vulnerabilities_by_severity(self) -> Dict[str, int]:
"""按严重程度分组漏洞"""
severity_count = {'HIGH': 0, 'MEDIUM': 0, 'LOW': 0, 'UNKNOWN': 0}
for vuln in self.vulnerabilities:
severity = vuln.get('severity', 'UNKNOWN')
if severity in severity_count:
severity_count[severity] += 1
return severity_count
def _group_vulnerabilities_by_type(self) -> Dict[str, int]:
"""按类型分组漏洞"""
type_count = {}
for vuln in self.vulnerabilities:
vuln_type = vuln.get('type', 'UNKNOWN')
type_count[vuln_type] = type_count.get(vuln_type, 0) + 1
return type_count
def _generate_recommendations(self) -> List[str]:
"""生成安全建议"""
recommendations = []
if any(v['type'] == 'SQL Injection' for v in self.vulnerabilities):
recommendations.extend([
"使用参数化查询或预编译语句",
"实施最小权限原则",
"启用数据库审计日志",
"使用Web应用防火墙(WAF)"
])
if any(v['type'] == 'XSS' for v in self.vulnerabilities):
recommendations.extend([
"实施输入验证和输出编码",
"使用Content Security Policy (CSP)",
"设置HttpOnly cookie标志",
"使用现代前端框架的XSS防护"
])
if any(v['type'] == 'SAST' for v in self.vulnerabilities):
recommendations.extend([
"定期进行代码安全审查",
"实施安全编码规范",
"使用SAST工具集成到CI/CD"
])
return recommendations
def _generate_html_report(self, report_data: Dict[str, Any]) -> str:
"""生成HTML格式报告"""
# 简化的HTML报告生成
html_template = """
<!DOCTYPE html>
<html>
<head>
<title>安全测试报告</title>
<style>
body { font-family: Arial, sans-serif; margin: 40px; }
.summary { background: #f5f5f5; padding: 20px; border-radius: 5px; }
.vulnerability { border: 1px solid #ddd; margin: 10px 0; padding: 15px; }
.high { border-left: 5px solid #e74c3c; }
.medium { border-left: 5px solid #f39c12; }
.low { border-left: 5px solid #27ae60; }
.chart { width: 300px; height: 200px; }
</style>
</head>
<body>
<h1>🛡️ 安全测试报告</h1>
<div class="summary">
<h2>扫描摘要</h2>
<p>总扫描数: {total_scans}</p>
<p>总漏洞数: {total_vulnerabilities}</p>
<p>扫描时间: {scan_time}</p>
</div>
<h2>漏洞统计</h2>
<div>
<h3>按严重程度</h3>
{severity_chart}
<h3>按漏洞类型</h3>
{type_chart}
</div>
<h2>详细发现</h2>
{vulnerability_details}
<h2>安全建议</h2>
<ul>
{recommendations}
</ul>
</body>
</html>
"""
# 填充模板
filled_html = html_template.format(
total_scans=report_data['scan_summary']['total_scans'],
total_vulnerabilities=report_data['scan_summary']['total_vulnerabilities'],
scan_time=report_data['scan_summary']['scan_time'],
severity_chart=self._generate_severity_chart(report_data['vulnerabilities_by_severity']),
type_chart=self._generate_type_chart(report_data['vulnerabilities_by_type']),
vulnerability_details=self._generate_vulnerability_details(report_data['detailed_findings']),
recommendations=''.join(f'<li>{rec}</li>' for rec in report_data['recommendations'])
)
# 保存HTML文件
with open('security_report.html', 'w') as f:
f.write(filled_html)
return filled_html
def _generate_severity_chart(self, severity_data: Dict[str, int]) -> str:
"""生成严重程度图表"""
chart_html = '<div style="display: flex; align-items: end; height: 150px; gap: 10px;">'
max_count = max(severity_data.values()) if severity_data else 1
for severity, count in severity_data.items():
height = (count / max_count) * 120 if max_count > 0 else 0
color = {
'HIGH': '#e74c3c',
'MEDIUM': '#f39c12',
'LOW': '#27ae60',
'UNKNOWN': '#95a5a6'
}.get(severity, '#95a5a6')
chart_html += f"""
<div style="display: flex; flex-direction: column; align-items: center;">
<div style="width: 30px; height: {height}px; background: {color};"></div>
<div>{severity}</div>
<div>{count}</div>
</div>
"""
chart_html += '</div>'
return chart_html
def _generate_type_chart(self, type_data: Dict[str, int]) -> str:
"""生成类型图表"""
chart_html = '<ul>'
for vuln_type, count in type_data.items():
chart_html += f'<li>{vuln_type}: {count}</li>'
chart_html += '</ul>'
return chart_html
def _generate_vulnerability_details(self, vulnerabilities: List[Dict[str, Any]]) -> str:
"""生成漏洞详情"""
details_html = ''
for i, vuln in enumerate(vulnerabilities):
severity_class = vuln.get('severity', 'UNKNOWN').lower()
details_html += f"""
<div class="vulnerability {severity_class}">
<h3>{vuln.get('type', 'Unknown')} - {vuln.get('severity', 'UNKNOWN')}</h3>
<p>{vuln.get('description', 'No description')}</p>
<p>文件: {vuln.get('file', 'N/A')} 行: {vuln.get('line', 'N/A')}</p>
</div>
"""
return details_html
# 使用示例
if __name__ == "__main__":
# 创建安全测试框架
security_framework = SecurityTestFramework()
# 运行各种扫描
print("🔍 开始安全扫描...")
# SAST扫描
sast_result = security_framework.run_security_scan("sast", target_dir=".")
print(f"SAST扫描完成: 发现 {len(sast_result.get('results', [])) if sast_result else 0} 个问题")
# SCA扫描
sca_result = security_framework.run_security_scan("sca")
print(f"SCA扫描完成: 发现 {len(sca_result.get('vulnerabilities', [])) if sca_result else 0} 个漏洞")
# DAST扫描(需要目标URL)
# dast_result = security_framework.run_security_scan("dast", target_url="http://localhost:8080")
# 生成报告
report = security_framework.generate_security_report()
print("📄 安全报告已生成: security_report.html")
# 输出摘要
print(f"\n📊 安全扫描摘要:")
print(f" 总漏洞数: {len(security_framework.vulnerabilities)}")
for severity, count in security_framework._group_vulnerabilities_by_severity().items():
if count > 0:
print(f" {severity}: {count}")2.3 安全测试性能特性
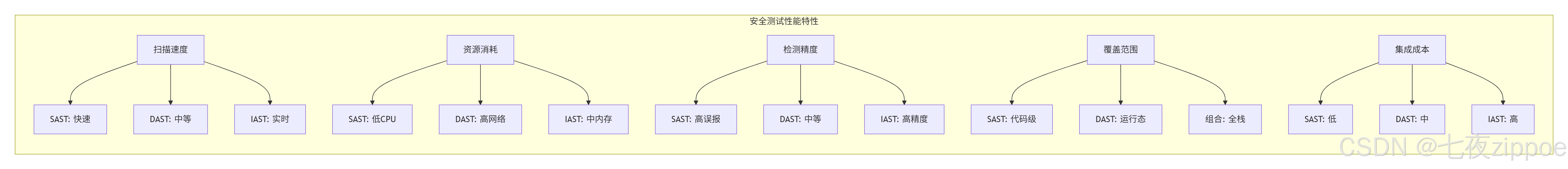
实际性能数据(基于中型项目):
-
SAST扫描:1000行代码/秒,误报率20-40%
-
DAST扫描:10-50请求/分钟,覆盖率60-80%
-
SCA扫描:<5秒/项目,准确率95%+
-
综合扫描:中型项目完整扫描约5-10分钟
3. 🔧 核心漏洞防护实战
3.1 SQL注入防护
python
# sql_injection_protection.py
"""
SQL注入防护实战
"""
import sqlite3
import psycopg2
import mysql.connector
from typing import Any, Dict, List, Optional
import re
import logging
from contextlib import contextmanager
class SQLInjectionProtection:
"""SQL注入防护类"""
def __init__(self, db_type: str = 'sqlite'):
self.db_type = db_type
self.logger = logging.getLogger(__name__)
def _get_connection(self, **kwargs):
"""获取数据库连接"""
if self.db_type == 'sqlite':
return sqlite3.connect(kwargs.get('database', ':memory:'))
elif self.db_type == 'postgresql':
return psycopg2.connect(
host=kwargs.get('host', 'localhost'),
database=kwargs.get('database'),
user=kwargs.get('user'),
password=kwargs.get('password')
)
elif self.db_type == 'mysql':
return mysql.connector.connect(
host=kwargs.get('host', 'localhost'),
database=kwargs.get('database'),
user=kwargs.get('user'),
password=kwargs.get('password')
)
else:
raise ValueError(f"不支持的数据库类型: {self.db_type}")
@contextmanager
def get_cursor(self, **kwargs):
"""获取游标上下文管理器"""
conn = self._get_connection(**kwargs)
cursor = conn.cursor()
try:
yield cursor
conn.commit()
except Exception as e:
conn.rollback()
raise e
finally:
cursor.close()
conn.close()
def unsafe_query(self, user_input: str, **kwargs) -> List[Dict[str, Any]]:
"""❌ 不安全的查询 - 存在SQL注入风险"""
query = f"SELECT * FROM users WHERE name = '{user_input}'"
with self.get_cursor(**kwargs) as cursor:
cursor.execute(query) # 危险:直接拼接用户输入
# 获取结果
columns = [desc[0] for desc in cursor.description] if cursor.description else []
results = []
for row in cursor.fetchall():
results.append(dict(zip(columns, row)))
return results
def safe_query_parameterized(self, user_input: str, **kwargs) -> List[Dict[str, Any]]:
"""✅ 安全查询 - 使用参数化查询"""
query = "SELECT * FROM users WHERE name = ?" # 使用占位符
with self.get_cursor(**kwargs) as cursor:
cursor.execute(query, (user_input,)) # 安全:参数化查询
columns = [desc[0] for desc in cursor.description] if cursor.description else []
results = []
for row in cursor.fetchall():
results.append(dict(zip(columns, row)))
return results
def safe_query_prepared_statement(self, user_input: str, **kwargs) -> List[Dict[str, Any]]:
"""✅ 安全查询 - 使用预编译语句"""
# 创建预编译语句
query = "SELECT * FROM users WHERE name = %s"
with self.get_cursor(**kwargs) as cursor:
# 预编译语句
cursor.execute(query, (user_input,))
columns = [desc[0] for desc in cursor.description] if cursor.description else []
results = []
for row in cursor.fetchall():
results.append(dict(zip(columns, row)))
return results
def input_validation(self, user_input: str) -> bool:
"""输入验证"""
# 白名单验证:只允许字母数字和基本标点
if not re.match(r'^[a-zA-Z0-9\s\.\-_,!?@]+$', user_input):
return False
# 长度限制
if len(user_input) > 100:
return False
# 关键词黑名单
dangerous_keywords = ['DROP', 'DELETE', 'INSERT', 'UPDATE', 'UNION', 'OR', 'AND']
upper_input = user_input.upper()
for keyword in dangerous_keywords:
if keyword in upper_input:
return False
return True
def safe_query_with_validation(self, user_input: str, **kwargs) -> List[Dict[str, Any]]:
"""✅ 安全查询 - 输入验证 + 参数化"""
if not self.input_validation(user_input):
self.logger.warning(f"输入验证失败: {user_input}")
return []
return self.safe_query_parameterized(user_input, **kwargs)
def detect_sql_injection_attempt(self, user_input: str) -> bool:
"""检测SQL注入尝试"""
sql_patterns = [
r"'.*--", # 注释符
r"'.*;.*--", # 多语句
r"UNION.*SELECT", # UNION注入
r"OR.*=.*", # 布尔注入
r"AND.*=.*", # 布尔注入
r"DROP.*TABLE", # 删除表
r"INSERT.*INTO", # 插入数据
r"UPDATE.*SET", # 更新数据
r"DELETE.*FROM", # 删除数据
r"EXEC.*", # 执行命令
r"xp_cmdshell", # SQL Server命令执行
]
upper_input = user_input.upper()
for pattern in sql_patterns:
if re.search(pattern, upper_input, re.IGNORECASE):
self.logger.warning(f"检测到SQL注入尝试: {user_input}")
return True
return False
def secure_query_execution(self, user_input: str, **kwargs) -> List[Dict[str, Any]]:
"""完整的安全查询执行"""
# 1. 检测注入尝试
if self.detect_sql_injection_attempt(user_input):
self.logger.error(f"拒绝SQL注入攻击: {user_input}")
return []
# 2. 输入验证
if not self.input_validation(user_input):
self.logger.warning(f"输入验证失败: {user_input}")
return []
# 3. 参数化查询
return self.safe_query_parameterized(user_input, **kwargs)
# 使用示例
if __name__ == "__main__":
# 创建防护实例
sql_protection = SQLInjectionProtection('sqlite')
# 测试安全查询
safe_input = "John Doe"
results = sql_protection.secure_query_execution(safe_input, database=':memory:')
print(f"安全查询结果: {len(results)} 条记录")
# 测试恶意输入
malicious_inputs = [
"John' OR '1'='1", # 经典注入
"'; DROP TABLE users; --", # 删除表
"John' UNION SELECT * FROM passwords --", # 联合查询
]
for malicious in malicious_inputs:
print(f"\n测试恶意输入: {malicious}")
results = sql_protection.secure_query_execution(malicious, database=':memory:')
print(f"检测到攻击,阻止执行,返回: {len(results)} 条记录")3.2 XSS防护实战
python
# xss_protection.py
"""
XSS跨站脚本防护实战
"""
import html
import re
import json
from typing import Any, Dict, List, Optional
from urllib.parse import quote, unquote
import bleach
import markupsafe
class XSSProtection:
"""XSS防护类"""
def __init__(self):
# 允许的HTML标签和属性
self.allowed_tags = [
'p', 'br', 'strong', 'em', 'u', 'a', 'ul', 'ol', 'li',
'h1', 'h2', 'h3', 'h4', 'h5', 'h6'
]
self.allowed_attributes = {
'a': ['href', 'title', 'target'],
'*': ['class', 'style'] # 全局允许的属性
}
# 危险协议
self.dangerous_protocols = ['javascript:', 'vbscript:', 'data:']
def escape_html(self, text: str) -> str:
"""HTML转义 - 最基础的防护"""
return html.escape(text)
def safe_html_render(self, text: str) -> markupsafe.Markup:
"""使用MarkupSafe安全渲染"""
return markupsafe.Markup(text)
def sanitize_html(self, html_content: str) -> str:
"""HTML净化 - 使用Bleach库"""
return bleach.clean(
html_content,
tags=self.allowed_tags,
attributes=self.allowed_attributes,
strip=True
)
def validate_url(self, url: str) -> bool:
"""URL验证"""
# 检查危险协议
for protocol in self.dangerous_protocols:
if url.lower().startswith(protocol):
return False
# 基本URL格式验证
url_pattern = r'^(https?|ftp):\/\/[^\s/$.?#].[^\s]*$'
if not re.match(url_pattern, url, re.IGNORECASE):
return False
return True
def safe_url_attribute(self, url: str) -> str:
"""安全处理URL属性"""
if not self.validate_url(url):
return '#' # 返回安全默认值
# URL编码
return quote(url, safe='/:?=&')
def sanitize_json(self, data: Any) -> str:
"""JSON数据安全序列化"""
return json.dumps(data, ensure_ascii=False)
def content_security_policy(self) -> Dict[str, str]:
"""生成Content Security Policy头"""
csp = {
'default-src': "'self'",
'script-src': "'self' 'unsafe-inline'", # 生产环境应该移除unsafe-inline
'style-src': "'self' 'unsafe-inline'",
'img-src': "'self' data: https:",
'connect-src': "'self'",
'font-src': "'self'",
'object-src': "'none'",
'media-src': "'self'",
'frame-src': "'none'",
'base-uri': "'self'",
'form-action': "'self'"
}
# 转换为HTTP头格式
csp_header = '; '.join(f"{key} {value}" for key, value in csp.items())
return {'Content-Security-Policy': csp_header}
def http_headers_protection(self) -> Dict[str, str]:
"""HTTP安全头设置"""
headers = {
'X-Content-Type-Options': 'nosniff',
'X-Frame-Options': 'SAMEORIGIN',
'X-XSS-Protection': '1; mode=block',
'Referrer-Policy': 'strict-origin-when-cross-origin',
'Strict-Transport-Security': 'max-age=31536000; includeSubDomains'
}
# 添加CSP
headers.update(self.content_security_policy())
return headers
def detect_xss_payload(self, text: str) -> bool:
"""检测XSS payload"""
xss_patterns = [
r'<script[^>]*>.*?</script>', # <script>标签
r'on\w+\s*=', # 事件属性
r'javascript:', # JavaScript协议
r'vbscript:', # VBScript协议
r'expression\s*\(', # CSS表达式
r'<iframe[^>]*>', # iframe标签
r'<object[^>]*>', # object标签
r'<embed[^>]*>', # embed标签
r'<applet[^>]*>', # applet标签
r'<base[^>]*>', # base标签
r'<meta[^>]*http-equiv=', # meta refresh
]
for pattern in xss_patterns:
if re.search(pattern, text, re.IGNORECASE | re.DOTALL):
return True
return False
def comprehensive_xss_protection(self, user_input: str, context: str = 'text') -> str:
"""综合XSS防护"""
if self.detect_xss_payload(user_input):
# 记录攻击尝试
logging.warning(f"检测到XSS攻击尝试: {user_input[:100]}")
return "" # 或返回净化后的安全文本
if context == 'html':
# HTML上下文
return self.sanitize_html(user_input)
elif context == 'attribute':
# HTML属性上下文
return self.escape_html(user_input)
elif context == 'url':
# URL上下文
return self.safe_url_attribute(user_input)
elif context == 'css':
# CSS上下文 - 严格限制
if re.match(r'^[a-zA-Z0-9\s#.-]+$', user_input):
return user_input
else:
return ''
elif context == 'javascript':
# JavaScript上下文 - 应该避免直接插入
return json.dumps(user_input)[1:-1] # 作为字符串字面量
else:
# 默认文本上下文
return self.escape_html(user_input)
# 使用示例
if __name__ == "__main__":
xss_protection = XSSProtection()
# 测试数据
test_cases = [
("正常文本", "Hello World", "text"),
("简单HTML", "<p>Hello <strong>World</strong></p>", "html"),
("恶意脚本", "<script>alert('XSS')</script>", "html"),
("事件处理", "<img src=x onerror=alert(1)>", "html"),
("JavaScript协议", "javascript:alert(1)", "url"),
("安全URL", "https://example.com/page", "url")
]
for description, input_text, context in test_cases:
print(f"\n{description}:")
print(f" 输入: {input_text}")
protected = xss_protection.comprehensive_xss_protection(input_text, context)
print(f" 输出: {protected}")
# 检测攻击
is_malicious = xss_protection.detect_xss_payload(input_text)
print(f" 恶意检测: {'❌' if is_malicious else '✅'}")3.3 CSRF防护实战
python
# csrf_protection.py
"""
CSRF跨站请求伪造防护实战
"""
import secrets
import hashlib
import time
from typing import Dict, Any, Optional
from flask import Flask, request, session, make_response, render_template_string
import jwt
import uuid
class CSRFProtection:
"""CSRF防护类"""
def __init__(self, secret_key: str = None):
self.secret_key = secret_key or secrets.token_hex(32)
self.token_expiry = 3600 # 1小时
def generate_token(self, user_id: str = None) -> str:
"""生成CSRF Token"""
# 使用JWT生成token
payload = {
'csrf_token': secrets.token_hex(16),
'user_id': user_id or 'anonymous',
'exp': time.time() + self.token_expiry,
'iat': time.time()
}
return jwt.encode(payload, self.secret_key, algorithm='HS256')
def validate_token(self, token: str, user_id: str = None) -> bool:
"""验证CSRF Token"""
try:
payload = jwt.decode(token, self.secret_key, algorithms=['HS256'])
# 检查过期时间
if payload['exp'] < time.time():
return False
# 检查用户匹配
if user_id and payload.get('user_id') != user_id:
return False
return True
except jwt.InvalidTokenError:
return False
def double_submit_cookie(self) -> Dict[str, str]:
"""双提交Cookie防护"""
token = self.generate_token()
return {
'Set-Cookie': f'csrf_token={token}; HttpOnly; SameSite=Strict',
'X-CSRF-Token': token
}
def synchronizer_token_pattern(self, user_id: str) -> Dict[str, Any]:
"""同步器Token模式"""
token = self.generate_token(user_id)
# 存储到session
session['csrf_token'] = token
return {'csrf_token': token}
def custom_header_protection(self) -> Dict[str, str]:
"""自定义Header防护"""
return {
'X-Requested-With': 'XMLHttpRequest',
'X-CSRF-Protection': '1'
}
# Flask应用示例
app = Flask(__name__)
app.secret_key = secrets.token_hex(32)
# 初始化CSRF防护
csrf_protection = CSRFProtection()
@app.before_request
def csrf_protection_middleware():
"""CSRF防护中间件"""
# 排除GET、HEAD、OPTIONS请求
if request.method in ('GET', 'HEAD', 'OPTIONS'):
return
# 检查自定义Header
if request.headers.get('X-Requested-With') != 'XMLHttpRequest':
return make_response('CSRF protection failed: Missing header', 403)
# 检查CSRF Token
token = request.headers.get('X-CSRF-Token') or request.form.get('csrf_token')
if not token or not csrf_protection.validate_token(token):
return make_response('CSRF protection failed: Invalid token', 403)
@app.route('/login', methods=['GET', 'POST'])
def login():
"""登录页面"""
if request.method == 'POST':
# 验证后生成新token
user_id = "user123" # 模拟用户ID
# 设置session
session['user_id'] = user_id
# 生成CSRF token
csrf_token = csrf_protection.generate_token(user_id)
session['csrf_token'] = csrf_token
return f"登录成功,CSRF Token: {csrf_token}"
# GET请求返回登录表单
form_html = """
<form method="POST">
<input type="hidden" name="csrf_token" value="{{ csrf_token }}">
<input type="text" name="username" placeholder="用户名">
<input type="password" name="password" placeholder="密码">
<button type="submit">登录</button>
</form>
"""
# 生成CSRF token
csrf_token = csrf_protection.generate_token()
return render_template_string(form_html, csrf_token=csrf_token)
@app.route('/transfer', methods=['POST'])
def transfer_money():
"""转账接口 - 需要CSRF防护"""
# 已通过中间件验证
amount = request.form.get('amount')
to_account = request.form.get('to_account')
# 业务逻辑...
return f"转账成功: {amount} 到 {to_account}"
@app.route('/api/data', methods=['POST'])
def api_endpoint():
"""API接口 - 使用自定义Header防护"""
# 检查自定义Header
if request.headers.get('X-CSRF-Protection') != '1':
return make_response('CSRF protection failed', 403)
# 处理请求
return {"status": "success"}
# SameSite Cookie防护
@app.route('/set_cookie')
def set_secure_cookie():
"""设置安全Cookie"""
response = make_response("Cookie set")
# 安全Cookie设置
response.set_cookie(
'session_id',
value=str(uuid.uuid4()),
httponly=True,
secure=True, # 仅HTTPS
samesite='Strict', # 严格SameSite
max_age=3600
)
return response
# 使用示例
if __name__ == "__main__":
# 测试CSRF防护
print("🔐 CSRF防护示例")
# 生成Token
token = csrf_protection.generate_token("test_user")
print(f"生成的Token: {token[:20]}...")
# 验证Token
is_valid = csrf_protection.validate_token(token, "test_user")
print(f"Token验证: {'✅' if is_valid else '❌'}")
# 测试过期Token
time.sleep(1) # 确保时间戳变化
expired_token = jwt.encode({
'csrf_token': 'test',
'exp': time.time() - 1 # 已过期
}, csrf_protection.secret_key, algorithm='HS256')
is_expired_valid = csrf_protection.validate_token(expired_token)
print(f"过期Token验证: {'✅' if is_expired_valid else '❌'}")
# 启动测试服务器
app.run(debug=True, port=5000)4. 🛠️ 安全扫描工具链
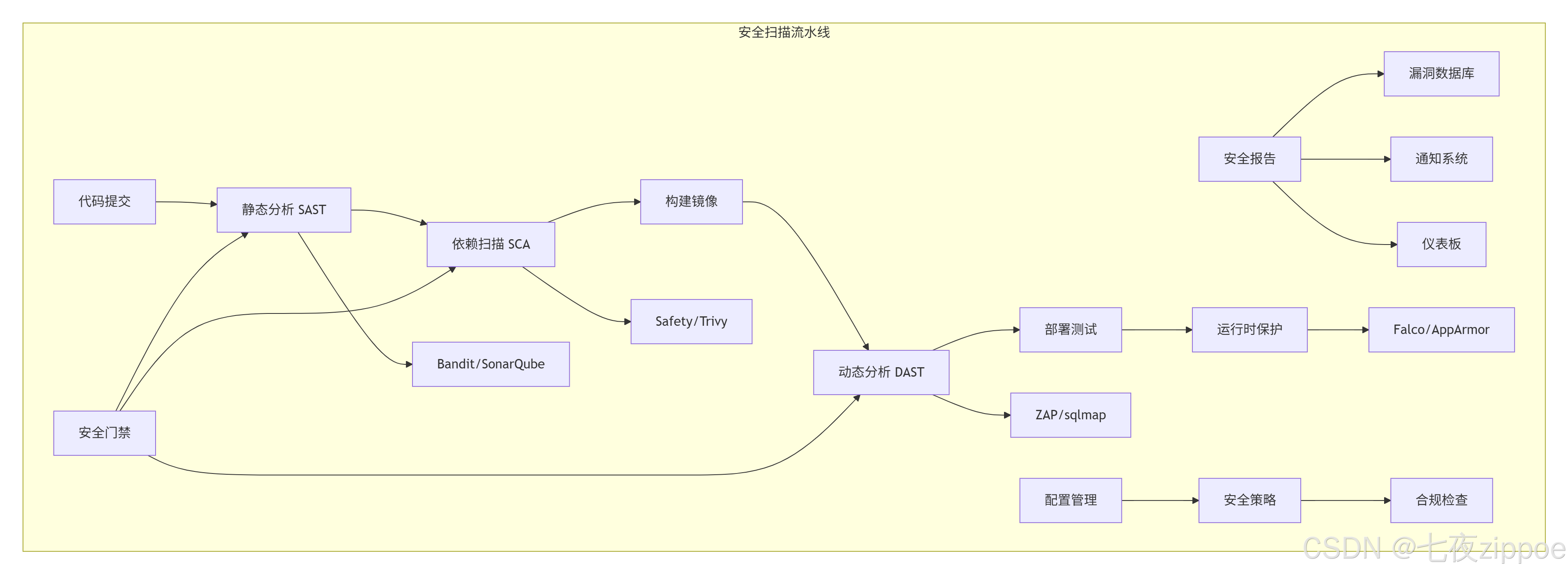
4.1 自动化安全扫描流水线
4.2 企业级安全工具集成
python
# security_toolchain.py
"""
企业级安全工具链集成
"""
import os
import subprocess
import yaml
import json
from pathlib import Path
from typing import Dict, List, Any
import requests
import tempfile
import docker
import logging
class EnterpriseSecurityToolchain:
"""企业级安全工具链"""
def __init__(self, config_path="security_tools.yaml"):
self.config = self._load_config(config_path)
self.docker_client = docker.from_env() if self._check_docker() else None
self.logger = logging.getLogger(__name__)
def _load_config(self, config_path: str) -> Dict[str, Any]:
"""加载工具配置"""
default_config = {
'sast_tools': ['bandit', 'semgrep', 'sonarqube'],
'sca_tools': ['safety', 'trivy', 'owasp-dependency-check'],
'dast_tools': ['zap', 'sqlmap', 'nuclei'],
'container_tools': ['trivy', 'clair', 'anchore'],
'ci_cd_integration': True,
'reporting': {
'jira': False,
'slack': False,
'email': True
}
}
if Path(config_path).exists():
with open(config_path, 'r') as f:
user_config = yaml.safe_load(f)
default_config.update(user_config)
return default_config
def _check_docker(self) -> bool:
"""检查Docker可用性"""
try:
subprocess.run(['docker', '--version'], capture_output=True, check=True)
return True
except (subprocess.CalledProcessError, FileNotFoundError):
self.logger.warning("Docker不可用,容器扫描功能将禁用")
return False
def run_comprehensive_scan(self, project_path: str) -> Dict[str, Any]:
"""运行全面安全扫描"""
results = {}
# SAST扫描
if self.config['sast_tools']:
results['sast'] = self._run_sast_scan(project_path)
# SCA扫描
if self.config['sca_tools']:
results['sca'] = self._run_sca_scan(project_path)
# 容器扫描
if self.config['container_tools'] and self.docker_client:
results['container'] = self._run_container_scan(project_path)
# 生成综合报告
report = self._generate_comprehensive_report(results)
# 发送通知
self._send_security_notifications(report)
return report
def _run_sast_scan(self, project_path: str) -> Dict[str, Any]:
"""运行SAST工具链"""
sast_results = {}
# Bandit扫描
if 'bandit' in self.config['sast_tools']:
sast_results['bandit'] = self._run_bandit(project_path)
# Semgrep扫描
if 'semgrep' in self.config['sast_tools']:
sast_results['semgrep'] = self._run_semgrep(project_path)
return sast_results
def _run_bandit(self, project_path: str) -> Dict[str, Any]:
"""运行Bandit"""
cmd = ['bandit', '-r', project_path, '-f', 'json']
try:
result = subprocess.run(cmd, capture_output=True, text=True, timeout=300)
if result.returncode in [0, 1]:
return json.loads(result.stdout) if result.stdout else {'results': []}
else:
return {'error': result.stderr}
except subprocess.TimeoutExpired:
return {'error': 'Bandit扫描超时'}
except Exception as e:
return {'error': str(e)}
def _run_semgrep(self, project_path: str) -> Dict[str, Any]:
"""运行Semgrep"""
cmd = ['semgrep', '--config', 'auto', project_path, '--json']
try:
result = subprocess.run(cmd, capture_output=True, text=True, timeout=300)
if result.returncode in [0, 1]:
return json.loads(result.stdout) if result.stdout else {'results': []}
else:
return {'error': result.stderr}
except subprocess.TimeoutExpired:
return {'error': 'Semgrep扫描超时'}
except Exception as e:
return {'error': str(e)}
def _run_sca_scan(self, project_path: str) -> Dict[str, Any]:
"""运行SCA工具链"""
sca_results = {}
# Safety扫描
if 'safety' in self.config['sca_tools']:
sca_results['safety'] = self._run_safety()
# Trivy扫描
if 'trivy' in self.config['sca_tools']:
sca_results['trivy'] = self._run_trivy_fs(project_path)
return sca_results
def _run_safety(self) -> Dict[str, Any]:
"""运行Safety"""
cmd = ['safety', 'check', '--json']
try:
result = subprocess.run(cmd, capture_output=True, text=True)
if result.returncode in [0, 1]:
return json.loads(result.stdout) if result.stdout else {'vulnerabilities': []}
else:
return {'error': result.stderr}
except Exception as e:
return {'error': str(e)}
def _run_trivy_fs(self, project_path: str) -> Dict[str, Any]:
"""运行Trivy文件系统扫描"""
if not self.docker_client:
return {'error': 'Docker不可用'}
try:
# 使用Trivy容器扫描
cmd = [
'docker', 'run', '--rm',
'-v', f'{project_path}:/project',
'aquasec/trivy:latest',
'fs', '/project', '--format', 'json'
]
result = subprocess.run(cmd, capture_output=True, text=True, timeout=600)
if result.returncode in [0, 1]:
return json.loads(result.stdout) if result.stdout else {'Results': []}
else:
return {'error': result.stderr}
except subprocess.TimeoutExpired:
return {'error': 'Trivy扫描超时'}
except Exception as e:
return {'error': str(e)}
def _run_container_scan(self, project_path: str) -> Dict[str, Any]:
"""运行容器扫描"""
container_results = {}
# 查找Dockerfile
dockerfile_path = Path(project_path) / 'Dockerfile'
if not dockerfile_path.exists():
return {'error': '未找到Dockerfile'}
# 构建测试镜像
image_name = f"security-scan-{int(time.time())}"
try:
# 构建镜像
build_result = self.docker_client.images.build(
path=project_path,
tag=image_name,
rm=True
)
# Trivy镜像扫描
if 'trivy' in self.config['container_tools']:
container_results['trivy'] = self._run_trivy_image(image_name)
# 清理镜像
self.docker_client.images.remove(image_name, force=True)
except Exception as e:
container_results['error'] = str(e)
return container_results
def _run_trivy_image(self, image_name: str) -> Dict[str, Any]:
"""运行Trivy镜像扫描"""
cmd = [
'docker', 'run', '--rm',
'-v', '/var/run/docker.sock:/var/run/docker.sock',
'aquasec/trivy:latest',
'image', '--format', 'json', image_name
]
try:
result = subprocess.run(cmd, capture_output=True, text=True, timeout=300)
if result.returncode in [0, 1]:
return json.loads(result.stdout) if result.stdout else {'Results': []}
else:
return {'error': result.stderr}
except subprocess.TimeoutExpired:
return {'error': 'Trivy镜像扫描超时'}
except Exception as e:
return {'error': str(e)}
def _generate_comprehensive_report(self, results: Dict[str, Any]) -> Dict[str, Any]:
"""生成综合报告"""
report = {
'scan_summary': {
'timestamp': time.strftime('%Y-%m-%d %H:%M:%S'),
'tools_executed': list(results.keys()),
'total_vulnerabilities': 0
},
'vulnerability_breakdown': {},
'recommendations': [],
'raw_results': results
}
# 统计漏洞
for tool_type, tool_results in results.items():
if isinstance(tool_results, dict) and 'error' not in tool_results:
# 统计各种工具的漏洞数量
vuln_count = self._count_vulnerabilities(tool_type, tool_results)
report['vulnerability_breakdown'][tool_type] = vuln_count
report['scan_summary']['total_vulnerabilities'] += vuln_count
return report
def _count_vulnerabilities(self, tool_type: str, results: Dict[str, Any]) -> int:
"""统计漏洞数量"""
if tool_type == 'sast':
return len(results.get('bandit', {}).get('results', [])) + \
len(results.get('semgrep', {}).get('results', []))
elif tool_type == 'sca':
return len(results.get('safety', {}).get('vulnerabilities', [])) + \
len(results.get('trivy', {}).get('Results', []))
elif tool_type == 'container':
return len(results.get('trivy', {}).get('Results', []))
else:
return 0
def _send_security_notifications(self, report: Dict[str, Any]):
"""发送安全通知"""
total_vulns = report['scan_summary']['total_vulnerabilities']
if total_vulns > 0:
message = f"🔴 安全扫描发现 {total_vulns} 个漏洞"
else:
message = "✅ 安全扫描通过,未发现漏洞"
self.logger.info(message)
# 发送到Slack(如果配置)
if self.config['reporting'].get('slack'):
self._send_slack_notification(message, report)
# 发送邮件(如果配置)
if self.config['reporting'].get('email'):
self._send_email_notification(message, report)
# 使用示例
if __name__ == "__main__":
# 创建安全工具链
toolchain = EnterpriseSecurityToolchain()
# 运行全面扫描
print("🚀 开始企业级安全扫描...")
results = toolchain.run_comprehensive_scan(".")
print(f"\n📊 扫描完成:")
print(f" 总漏洞数: {results['scan_summary']['total_vulnerabilities']}")
for tool, count in results['vulnerability_breakdown'].items():
print(f" {tool}: {count} 个漏洞")
# 保存报告
with open('enterprise_security_report.json', 'w') as f:
json.dump(results, f, indent=2)
print("📄 详细报告已保存: enterprise_security_report.json")5. 📚 总结与资源
5.1 核心安全原则
安全设计原则:
-
最小权限原则:只授予必要权限
-
防御深度:多层安全防护
-
安全左移:在开发早期引入安全
-
持续监控:实时安全检测
OWASP Top 10 2021防护重点:
-
A01:2021-失效的访问控制 → 实施RBAC和权限验证
-
A02:2021-加密机制失效 → 使用强加密和TLS
-
A03:2021-注入 → 参数化查询和输入验证
-
A04:2021-不安全设计 → 威胁建模和安全设计
-
A05:2021-安全配置错误 → 自动化配置检查
-
A06:2021-易受攻击的组件 → 依赖扫描和更新
-
A07:2021-认证和授权失效 → 多因素认证和会话管理
-
A08:2021-软件和数据完整性失效 → 数字签名和完整性检查
-
A09:2021-安全日志和监控失效 → 全面审计日志
-
A10:2021-服务端请求伪造 → URL验证和网络隔离
5.2 官方资源
-
**OWASP官方网站** - 权威安全组织
-
**OWASP Top 10 2021** - 十大安全威胁
-
**OWASP Cheat Sheet Series** - 安全速查表
-
**Bandit文档** - Python SAST工具
-
**Safety文档** - Python依赖扫描
-
**SQLMap文档** - SQL注入检测工具
-
**ZAP文档** - Web应用扫描器
5.3 企业级最佳实践
安全开发生命周期(SDL):
-
需求阶段:威胁建模和安全需求
-
设计阶段:安全架构设计
-
开发阶段:安全编码和代码审查
-
测试阶段:自动化安全测试
-
部署阶段:安全配置和加固
-
运维阶段:持续安全监控
安全工具链:
-
SAST:Bandit, Semgrep, SonarQube
-
SCA:Safety, Trivy, OWASP Dependency-Check
-
DAST:ZAP, sqlmap, Nuclei
-
容器安全:Trivy, Clair, Anchore
-
运行时安全:Falco, AppArmor, SELinux
最后的话 :安全不是一次性的项目,而是持续的过程 。OWASP Top 10提供了一个很好的起点,但真正的安全需要深度防御、持续监控和全员参与。从今天开始,让安全成为您开发流程的自然组成部分。