背景 :
zsteg是基于Ruby开发的一款检测PNG与BMP中隐写数据的工具,其工作原理是它通过读取像素颜色的二进制最后一位来提取隐藏信息(LSB隐写),这种方法要求图像数据是无损或准无损的,因此基于有损压缩算法DCT得到的JPG中的隐写信息提取则不能用Zsteg。目前最稳定的方法是通RubyGems(Ruby的包管理器)进行安装。
操作 :
Step1。安装Ruby依赖环境
Kali-linux中一般自带Ruby,但为确保所有必要库都已经具备,执行下面这两条指令进行环境更新。(更新过程中需打开VPN以顺利连接Ruby官网,此外过程中可能出现图1所示的提示系统重启界面,属于正常现象,按下Tab键盘然后Enter一下OK,接下来Enter一下Yes即可)
bash
sudo apt update
sudo apt install ruby ruby-dev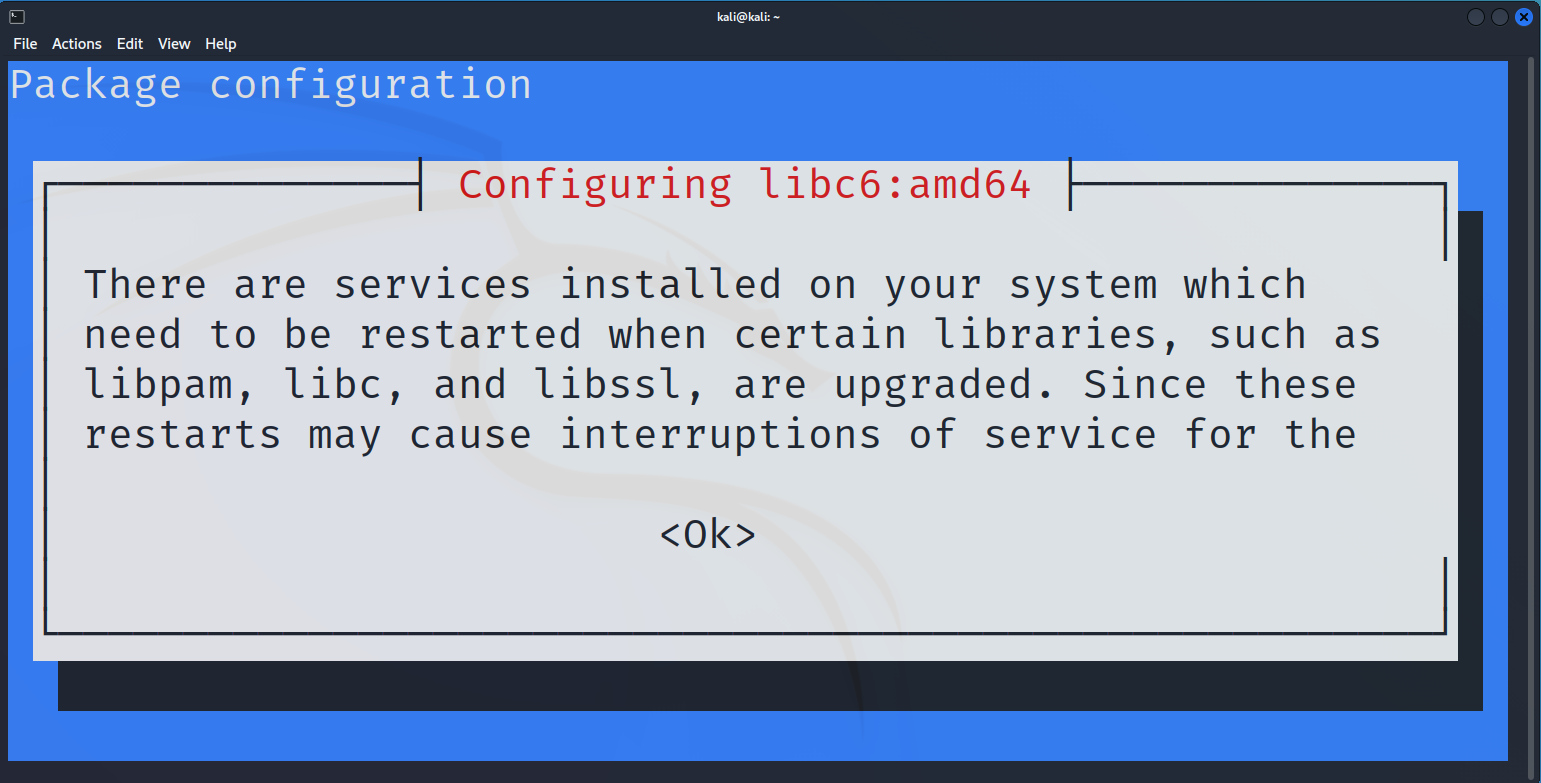
(图1)
Step2。使用Gem安装zsteg。过程中打开Vpn
bash
sudo gem install zstegStep3。验证安装已成功。输入bash指令,可看到图2界面,说明zsteg被安装在/usr/lcoal/bin/zsteg这个路径下(科普,放在这个路径下说明安装的非常成功,因为在kali-linux中这个路径一般用来专门存放第三方包,而/bin与/usr/bin一般是存放系统的核心命令)
bash
which zsteg
(图2)
Step4。用zsteg提取png隐写数据。使用的测试图片
test.png放在本文开头的资源连接中,从提取出来的隐写数据(extradata)中可知答案为flag{haobachang_huanying_nin_123782934789372459}
bash
┌──(kali㉿kali)-[~/tmp]
└─$ zsteg test.png
[?] 64 bytes of extra data after image end (IEND), offset = 0x13925
extradata:0 ..
00000000: 00 ff 00 54 45 58 54 5f 53 54 41 52 54 00 ff 00 |...TEXT_START...|
00000010: 66 6c 61 67 7b 68 61 6f 62 61 63 68 61 6e 67 5f |flag{haobachang_|
00000020: 68 75 61 6e 79 69 6e 67 5f 6e 69 6e 5f 31 32 33 |huanying_nin_123|
00000030: 37 38 32 39 33 34 37 38 39 33 37 32 34 35 39 7d |782934789372459}|
imagedata .. file: mc68k executable (shared demand paged)
b1,bgr,lsb,xy .. <wbStego size=0x49d2 ext="\x00\x00\t" data="$\xDB\xFF\xFF\xFE\xDB{m\xB6\xC9"... even=false hdr=ni l enc=nil mix=nil controlbyte=nil>
b2,r,lsb,xy .. file: SoftQuad DESC or font file binary
b2,r,msb,xy .. file: VISX image file
b2,g,msb,xy .. text: ["U" repeated 10 times]
b2,rgb,lsb,xy .. file: OpenPGP Secret Key
b2,bgr,msb,xy .. file: OpenPGP Public Key
b4,r,lsb,xy .. text: "\"\"\"\"\"\"\"\"!"
b4,r,msb,xy .. text: "HDDDDDDDD"
b4,g,lsb,xy .. text: "wwwwwwwwwwwwwwwwwwwwwfffffffffffffffffffffeUUUUUUUUUUTDDUUUUUUUTDDDDDDDDDDC3334DDDDDC333333333333\"\"\"#333333\"\"\"\"\"\"\"\"\"\"\""
b4,g,msb,xy .. text: ";333333333"
b4,b,lsb,xy .. text: "wwwwwwvffffeUUUUUTEUUUUTDDDDC333333\"\"\"\"\"\"\"\"\"\"\"\"!"
b4,b,msb,xy .. text: ["D" repeated 12 times]
b4,rgb,msb,xy .. text: "4C34C34C34C38"
b4,bgr,msb,xy .. text: "C34C34C34C34C38"