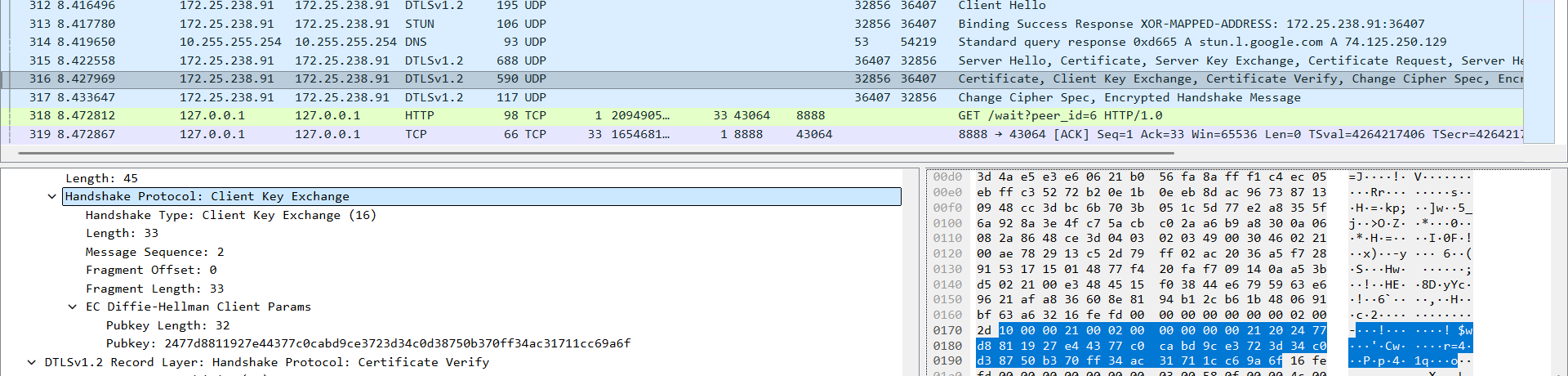
1.1.计算共享密钥:
from cryptography.hazmat.primitives.asymmetric import x25519
from cryptography.hazmat.backends import default_backend
import binascii
private_key_bytes = binascii.unhexlify("7f6fb1acf6fcee90c8090859a6c1a64d90d49b65002ccc880e53b1a409227085")
public_key_bytes = binascii.unhexlify("2477d8811927e44377c0cabd9ce3723d34c0d38750b370ff34ac31711cc69a6f")
priv_key = x25519.X25519PrivateKey.from_private_bytes(private_key_bytes)
pub_key = x25519.X25519PublicKey.from_public_bytes(public_key_bytes)
计算共享密钥
shared = priv_key.exchange(pub_key)
输出
print("共享密钥:", binascii.hexlify(shared).decode())
premaster_secret (32 bytes): 062d2be5a1adafc05422439468f38ec20f64c34ffc0259916b6408821d5dcc4c
1.2.计算EMS REAL SEED
ref:rfc5246
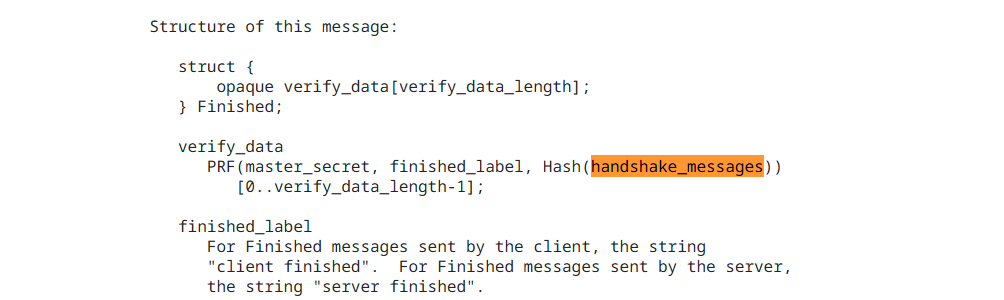
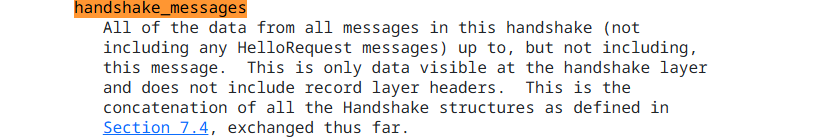
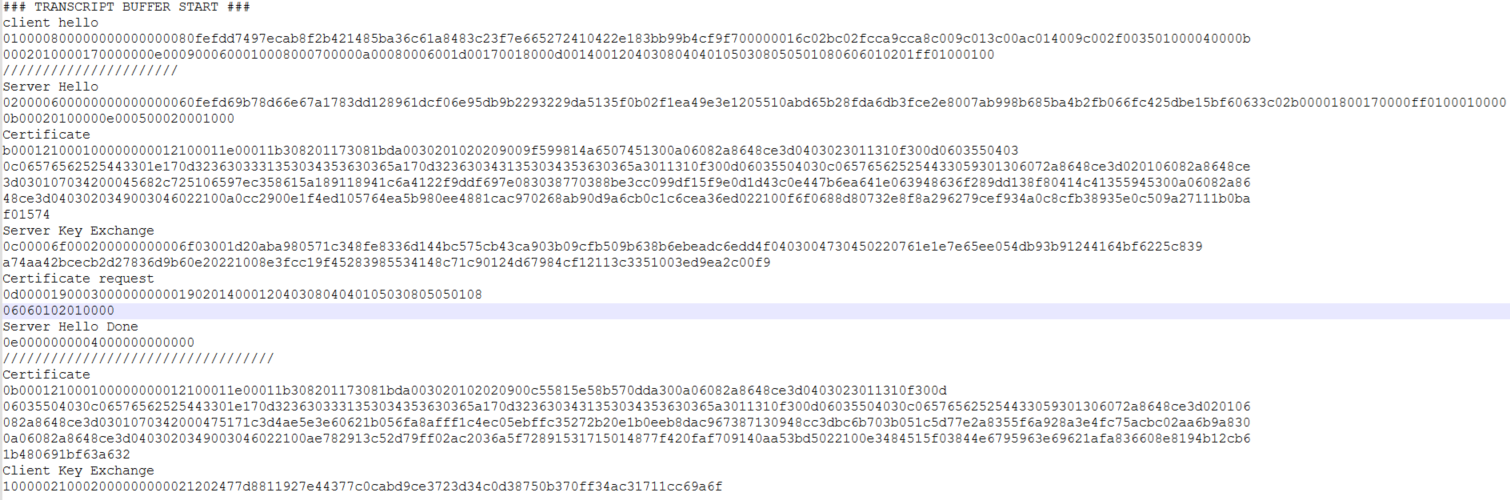
EMS REAL SEED (32 bytes): 624eae1953f714909e5a78e8a45faaad82b0f80e4f964f0a021114f446db07f6
1.3. USE D LABEL: extended master secret
1.4 有了上面3 个参数 就可以计算master secret了
计算session->secret
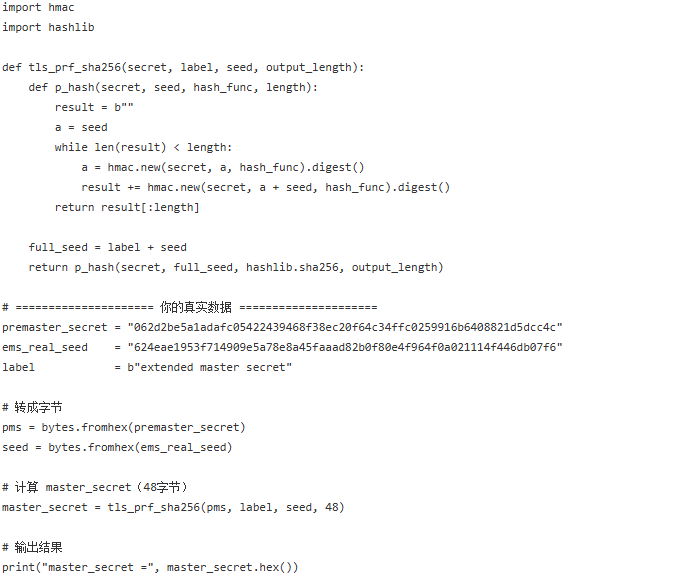 session->secret (48 bytes): 7726416b5c12ca53a5e023bd7c731f74034d2b6c8e702cee0770891e2f03848713d7ec9e58f7a7461cdc98863ab69bcc
session->secret (48 bytes): 7726416b5c12ca53a5e023bd7c731f74034d2b6c8e702cee0770891e2f03848713d7ec9e58f7a7461cdc98863ab69bcc
1.5 计算EX TRACTOR-dtls_srtp
输入master secret key : 7726416b5c12ca53a5e023bd7c731f74034d2b6c8e702cee0770891e2f03848713d7ec9e58f7a7461cdc98863ab69bcc
输入 prf label: EXTRACTOR-dtls_srtp
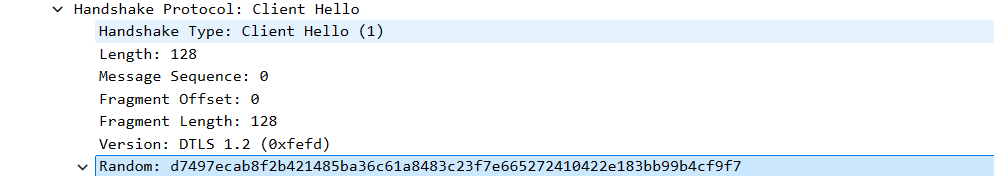
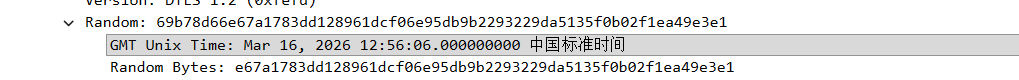
输入 clientRandom+serverRandom seed d7497ecab8f2b421485ba36c61a8483c23f7e665272410422e183bb99b4cf9f769b78d66e67a1783dd128961dcf06e95db9b2293229da5135f0b02f1ea49e3e1
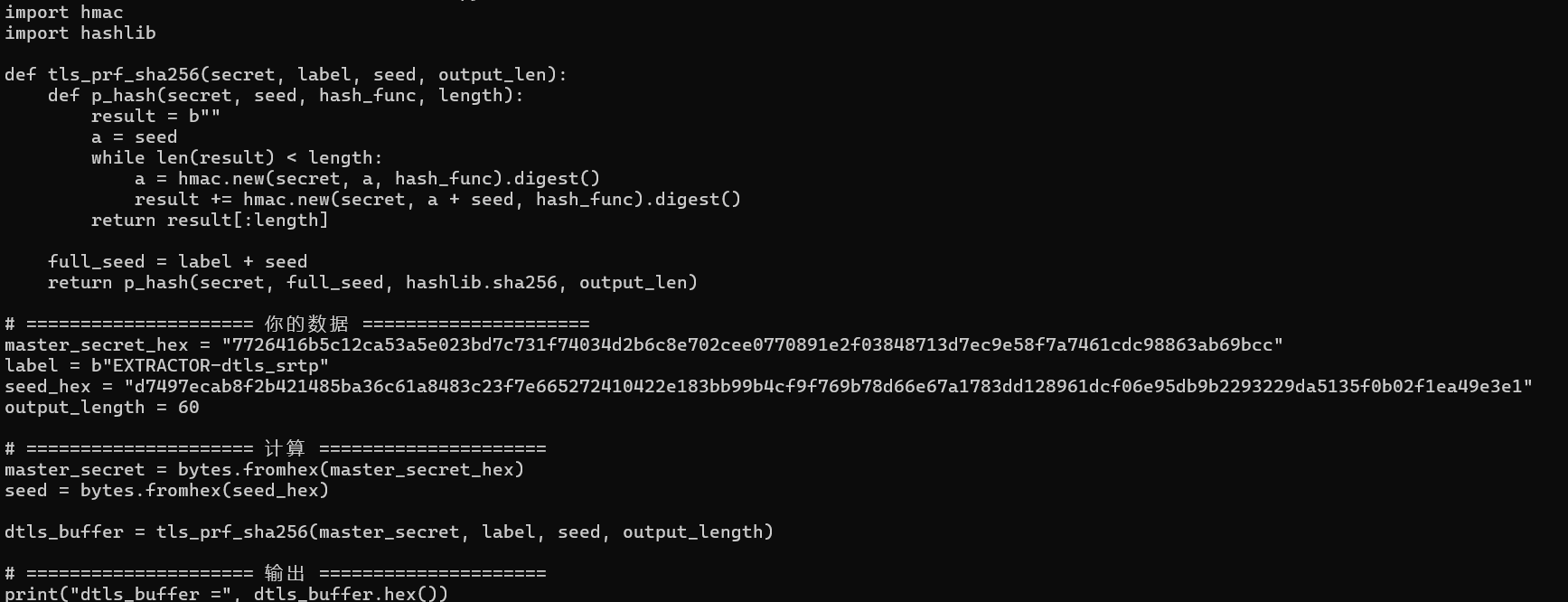 output length (dtls_buffer): 60 bytes
output length (dtls_buffer): 60 bytes
dtls_buffer: b4201281f6ed36230a448b6558aa1355ccf19e8b20d501950827514f37ace2422706d67c762cd9a61bcd79b0e5f26abe51e34e1b61cab1c10059468d
/////////////////////////////////////////////
client_write_key = b4201281f6ed36230a448b6558aa1355 server_write_key = ccf19e8b20d501950827514f37ace242 client_salt = 2706d67c762cd9a61bcd79b0e5f2 server_salt = 6abe51e34e1b61cab1c10059468d
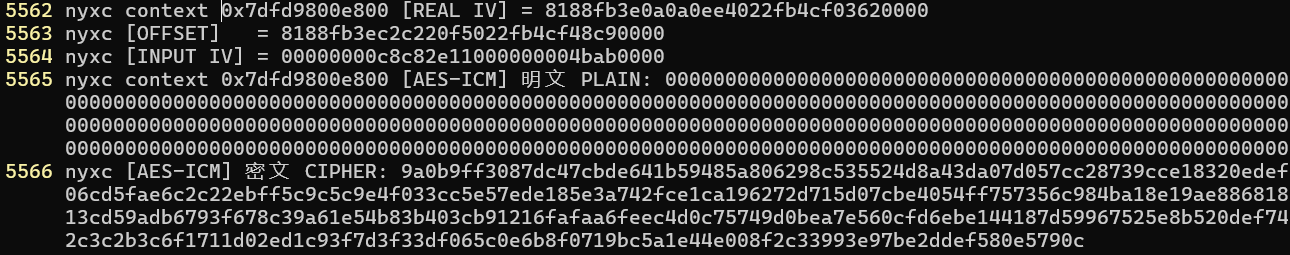
IV 6abe51e34e1b61cab1c10059468d0000
用ccf19e8b20d501950827514f37ace242
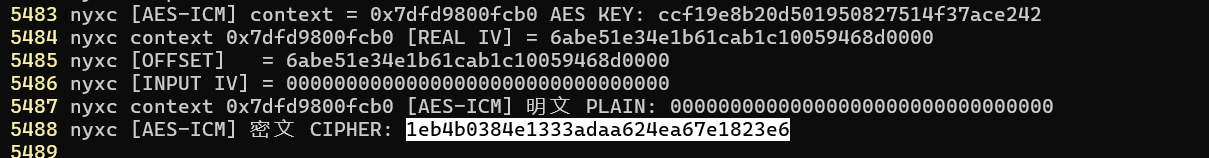
的到用于加密srtp的密钥流
//////////////////////////////////////////
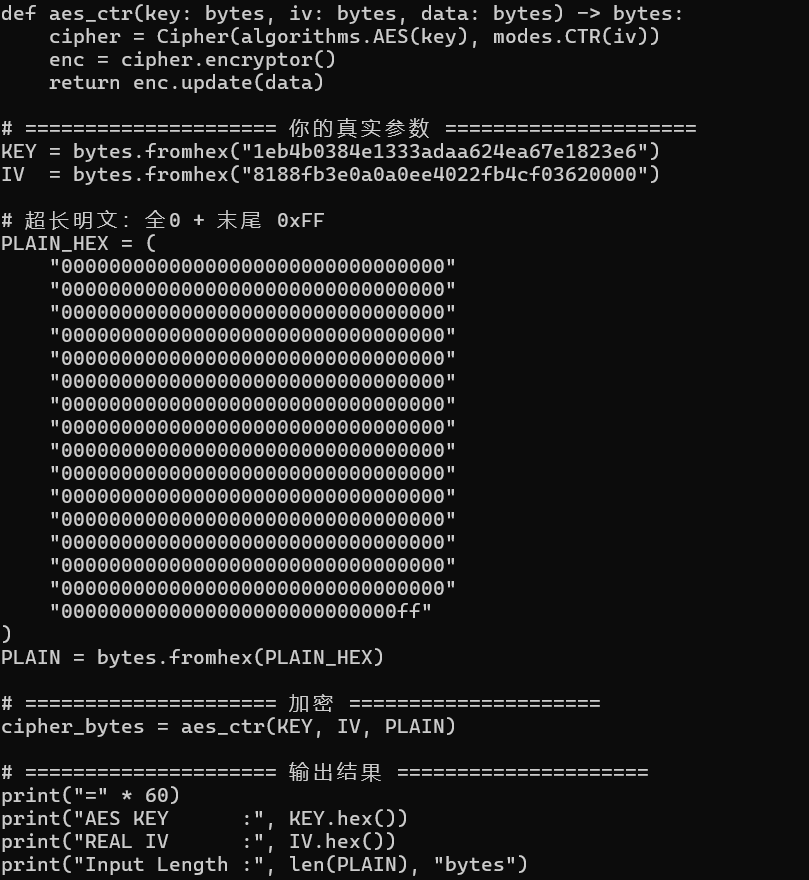
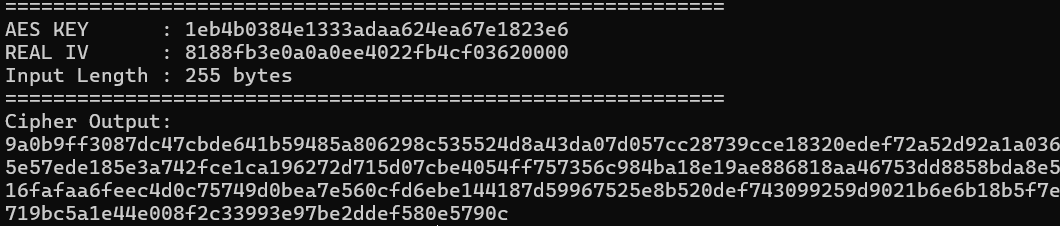
对比源码的打印nyxc AES-ICM context = 0x7dfd9800e800 AES KEY: 1eb4b0384e1333adaa624ea67e1823e6