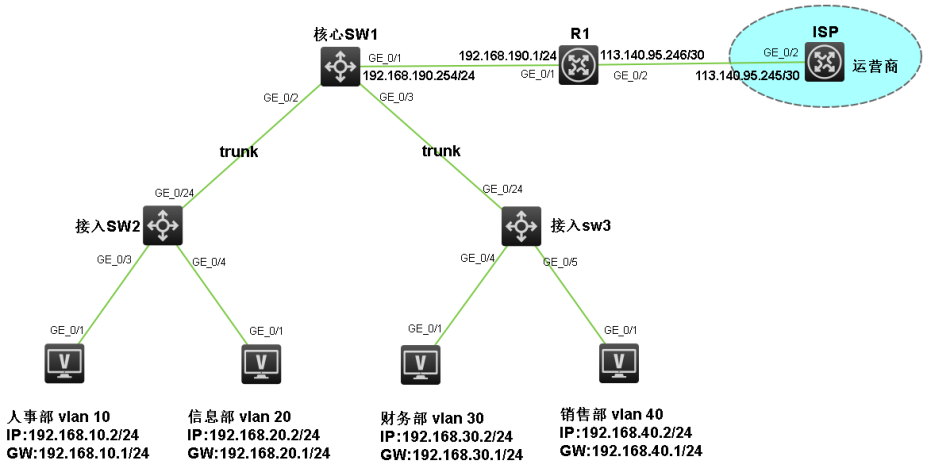
1. 组网拓扑
某企业内部共划分 4 个业务部门,为实现部门间网络隔离与安全访问控制,分别规划独立网段:192.168.10.0/24、192.168.20.0/24、192.168.30.0/24、192.168.40.0/24。核心交换机作为三层网关,配置各网段 VLANIF 接口地址;全网采用 DHCP 服务器为终端动态分配 IP 地址、子网掩码、网关及 DNS 信息。接入交换机负责下联 PC、打印机等终端设备,上联核心交换机实现数据转发。
出口路由器通过运营商提供的固定公网 IP 地址接入互联网,配置静态路由与 NAT 策略,在满足内网用户正常上网的同时,提升网络出口带宽利用率与整体访问速度,保障企业办公业务稳定、高效、安全运行。
2. 配置思路
中小型企业二层组网,配置思路如下:
-
vlan trunk配置
-
VLANIF用户网关配置
-
DHCP服务器配置
-
物理接口IP配置
-
静态路由配置
-
NAT地址转换配置
-
SSH远程登录配置
3. 配置步骤
步骤① vlan trunk配置
-
核心交换机vlan trunk配置。
vlan 10
vlan 20
vlan 30
vlan 40
vlan 200interface GigabitEthernet1/0/2
port link-type trunk
undo port trunk permit vlan 1
port trunk permit vlan 10 20 200interface GigabitEthernet1/0/3
port link-type trunk
undo port trunk permit vlan 1
port trunk permit vlan 30 40 200 -
接入交换机1vlan trunk配置。
vlan 10
vlan 20
vlan 200interface GigabitEthernet1/0/24
port link-type trunk
undo port trunk permit vlan 1
port trunk permit vlan 10 20 200interface GigabitEthernet1/0/3
port access vlan 10
interface GigabitEthernet1/0/4
port access vlan 20 -
接入交换机3 vlan trunk配置。
vlan 30
vlan 40
vlan 200interface GigabitEthernet1/0/24
port link-type trunk
undo port trunk permit vlan 1
port trunk permit vlan 30 40 200interface GigabitEthernet1/0/4
port access vlan 30
interface GigabitEthernet1/0/5
port access vlan 40
步骤②VLANIF用户网关配置
-
核心交换机VLANIF用户网关配置。
interface Vlan-interface10
ip address 192.168.10.1 24interface Vlan-interface20
ip address 192.168.20.1 24interface Vlan-interface30
ip address 192.168.30.1 24interface Vlan-interface40
ip address 192.168.40.1 24interface Vlan-interface200
ip address 192.168.200.1 24
步骤③DHCP服务器配置
-
核心交换机DHCP服务器地址池配置。
dhcp enable
dhcp server ip-pool vlan10
gateway-list 192.168.10.1
network 192.168.10.0 24
dns-list 114.114.114.114 223.5.5.5
expired day 3dhcp server ip-pool vlan20
gateway-list 192.168.20.1
network 192.168.20.0 24
dns-list 114.114.114.114 223.5.5.5
expired day 3dhcp server ip-pool vlan30
gateway-list 192.168.30.1
network 192.168.30.0 24
dns-list 114.114.114.114 223.5.5.5
expired day 3dhcp server ip-pool vlan40
gateway-list 192.168.40.1
network 192.168.40.0 24
dns-list 114.114.114.114 223.5.5.5
expired day 3
步骤④ 物理接口IP配置
-
出口路由器接口IP地址配置。
interface GigabitEthernet0/2
ip address 113.140.95.246 30interface GigabitEthernet0/1
ip address 192.168.190.1 24 -
核心交换机互联出口路由器地址配置。
interface GigabitEthernet1/0/1
port link-mode route
ip address 192.168.190.254 24
步骤⑤ 静态路由配置
-
出口路由器指向核心交换机的静态路由和指向公网的缺省路由配置。
ip route-static 0.0.0.0 0 0 113.140.95.245
ip route-static 192.168.10.0 24 192.168.190.254
ip route-static 192.168.20.0 24 192.168.190.254
ip route-static 192.168.30.0 24 192.168.190.254
ip route-static 192.168.40.0 24 192.168.190.254
ip route-static 192.168.200.0 24 192.168.190.254 -
核心交换机指向出口路由器的缺省路由配置。
ip route-static 0.0.0.0 0 192.168.190.1
步骤⑥ NAT地址转换配置
-
出口路由器ACL 策略配置。
acl basic 2000
rule 0 permit source 192.168.10.0 0.0.0.255
rule 0 permit source 192.168.20.0 0.0.0.255
rule 0 permit source 192.168.30.0 0.0.0.255
rule 0 permit source 192.168.40.0 0.0.0.255
rule 0 permit source 192.168.190.0 0.0.0.255
rule 0 permit source 192.168.200.0 0.0.0.255 -
在出口路由器出接口调用NAT 策略,使内网正常访问互联网。
interface GigabitEthernet0/2
nat outbound 2000
步骤⑦ SSH远程登录配置
-
两台接入交换机管理地址配置(核心交换机管理地址VLANIF接口已经配置过,这里不用再配置)。
interface Vlan-interface 200
ip add 192.168.200.2 24ip route-static 0.0.0.0 0 192.168.200.1
interface Vlan-interface 200
ip add 192.168.200.3 24ip route-static 0.0.0.0 0 192.168.200.1
-
出口路由器、核心交换机、接入交换机SSH远程登录配置。
public-key local create rsa
public-key local create dsassh server enable
ssh server authentication-retries 5
ssh user admin service-type stelnet authentication-type passwordlocal-user admin
password simple admin@123
service-type ssh
authorization-attribute user-role level-15user-interface vty 0 4
authentication-mode scheme
protocol inbound ssh
说明: 其他设备SSH远程登录配置类似,这里不做演示。