Kubernetes创建只读权限的kubeconfig
背景:由于openclaw和其他智能体的兴起,使k8s集群的运维巡检效率都得到了提升,但是风险也会提升,因此需要给智能体提供只读权限的kubeconfig配置文件,保证不会私自篡改集群配置
注:由于k8s集群自带具有只读权限的名为 view 的clusterrole,因此我们创建 serviceaccount,并创建 clusterrolebinding 将 view 和我们新建的serviceaccount绑定到一块
特:由于 view 具备的权限有限,不具备查询 ClusterRole 和 ClusterRoleBinding、Role 和 RoleBinding、Secrets 和 Nodes 权限,如果需要这些权限,需要创建更多权限的 clusterrole 来和 serviceaccount 绑定。
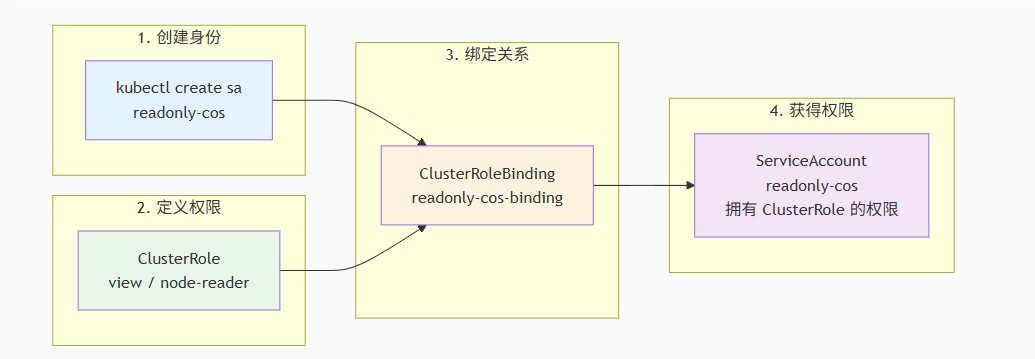
ServiceAccount、ClusterRole、clusterRolebinding关系图如下:
1、创建 ServiceAccount
bash
kubectl create sa readonly-cos -n kube-system2、创建clusterrolebinding,将view与sa绑定到一起
yaml
# readonly-clusterrolebinding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: readonly-sa-binding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: view
subjects:
- kind: ServiceAccount
name: readonly-cos
namespace: kube-system
bash
kubectl apply -f eadonly-clusterrolebinding.yaml3、创建 ServiceAccount 的长期 Token
yaml
# sa-secret.yaml
apiVersion: v1
kind: Secret
metadata:
name: readonly-cos-secret
namespace: kube-system
annotations:
kubernetes.io/service-account.name: readonly-cos
type: kubernetes.io/service-account-token
bash
kubectl apply -f sa-secret.yaml
TOKEN=$(kubectl get secret readonly-cos-secret -n kube-system -o jsonpath='{.data.token}' | base64 -d)
echo $TOKEN4、生成kubeconfig文件
4.1、获取集群信息
bash
CLUSTER_NAME=$(kubectl config current-context)
API_SERVER=$(kubectl config view --minify -o jsonpath='{.clusters[0].cluster.server}')
CA_DATA=$(kubectl config view --raw -o jsonpath='{.clusters[0].cluster.certificate-authority-data}')4.2、生成配置文件
bash
kubectl config set-cluster cluster-readonly-cos \
--server=$API_SERVER \
--certificate-authority=<(echo $CA_DATA | base64 -d) \
--embed-certs=true \
--kubeconfig=readonly-kubeconfig
会在当前目录下生成名为readonly-kubeconfig的配置文件4.3、设置用户凭证
bash
kubectl config set-credentials user-readonly-cos \
--token=$TOKEN \
--kubeconfig=readonly-kubeconfig
会在配置文件readonly-kubeconfig添加token配置4.4、设置上下文
bash
kubectl config set-context context-readonly-cos \
--cluster=cluster-readonly-cos \
--user=user-readonly-cos \
--kubeconfig=readonly-kubeconfig
会在配置文件readonly-kubeconfig配置上下文信息
kubectl config use-context context-readonly-cos --kubeconfig=/zq/readonly/readonly-kubeconfig
输出:Switched to context "context-readonly-cos".
kubectl config current-context --kubeconfig=/zq/readonly/readonly-kubeconfig
输出:context-readonly-cos4.5、验证
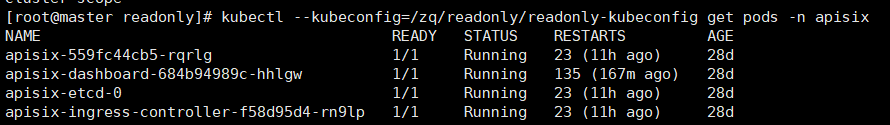
当编辑资源时会提示拒绝
bash
[root@master readonly]# kubectl --kubeconfig=/zq/readonly/readonly-kubeconfig edit deploy apisix-dashboard -n apisix
error: deployments.apps "apisix-dashboard" could not be patched: deployments.apps "apisix-dashboard" is forbidden: User "system:serviceaccount:kube-system:readonly-cos" cannot patch resource "deployments" in API group "apps" in the namespace "apisix"
You can run `kubectl replace -f /tmp/kubectl-edit-864880171.yaml` to try this update again.
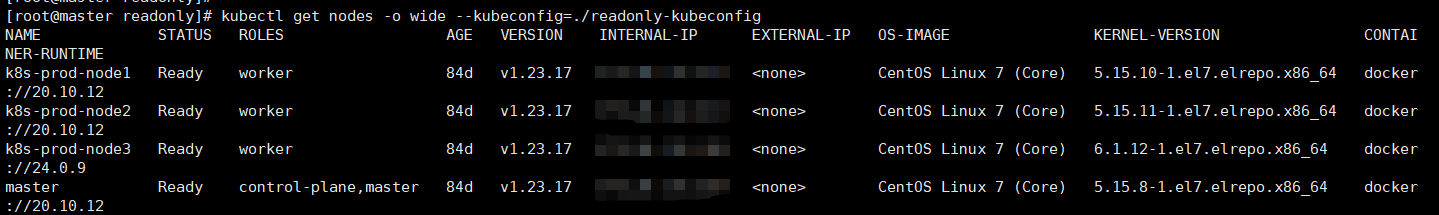
[root@master readonly]# 5、添加 node 权限
默认的 view 不带集群节点的权限,因此使用上述生成的kubeconfig查询时会提示拒绝
bash
[root@master readonly]# kubectl --kubeconfig=/zq/readonly/readonly-kubeconfig get nodes
Error from server (Forbidden): nodes is forbidden: User "system:serviceaccount:kube-system:readonly-cos" cannot list resource "nodes" in API group "" at the cluster scope需新建一个clusterrole,并将这个具备node权限的clusterrole也帮到ServiceAccount上
yaml
# node-readonly-cos.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: node-readonly-cos
rules:
- apiGroups: [""]
resources: ["nodes"]
verbs: ["get", "list", "watch"]
bash
kubectl apply -f node-readonly-cos.yaml创建clusterrolebinding绑定
bash
kubectl create clusterrolebinding nodes-readonly-cos \
--clusterrole=node-readonly-cos \
--serviceaccount=kube-system:readonly-cos再次查询node信息就可以了
6、更大权限的clusterrole
yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: all-readonly
rules:
- apiGroups: ["*"]
resources: ["*"]
verbs: ["get", "list", "watch"]将此clusterrole绑定到ServiceAccount上,可获得更大的权限:
bash
kubectl create clusterrolebinding all-readonly-cos \
--clusterrole=all-readonly \
--serviceaccount=kube-system:readonly-cos