华为eNSP网络实验之IPsec协议学习
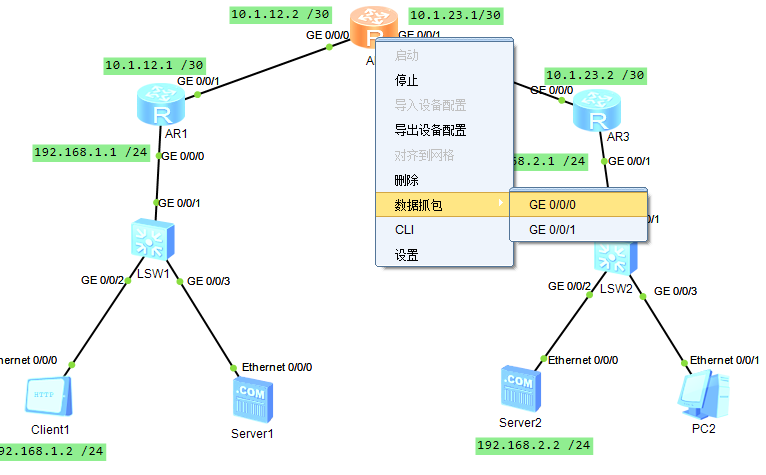
网络拓扑图如图所示:
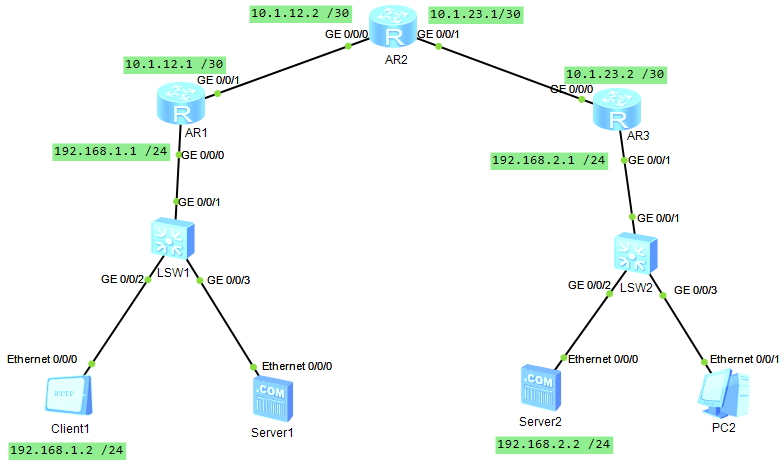
组网方案:
| 设备 | 接口 | IP地址/掩码 | 网关 | 所属区域 |
|---|---|---|---|---|
| Client1 | Ethernet 0/0/0 | 192.168.1.2/24 | 192.168.1.1 | 私网A |
| Server2 | Ethernet 0/0/0 | 192.168.2.2/24 | 192.168.2.1 | 私网B |
| AR1 | GE0/0/0 | 192.168.1.1/24 | - | 私网A网关 |
| GE0/0/1 | 10.1.12.1/30 | - | 公网 | |
| AR2 | GE0/0/0 | 10.1.12.2/30 | - | 公网 |
| GE0/0/1 | 10.1.23.1/30 | - | 公网 | |
| AR3 | GE0/0/0 | 10.1.23.2/30 | - | 公网 |
| GE0/0/1 | 192.168.2.1/24 | - | 私网B网关 | |
| LSW1, LSW2 | - | 无需配置 | - | 纯二层交换 |
实验要求:实现client1到sever2的ipsec通信。如client1通过httpclient的IP地址成功访问到server2。
1、该实验中,AR1 和 AR3 已经承担了网关角色,LSW1/LSW2 纯粹就是二层转发,所以无需配置。
2、本实验软件环境、版本:ensp 1.3.00,VirtualBox 5.2.22,wireshark3.0.0
(ps:不通软件版本的配置命令可能不同)
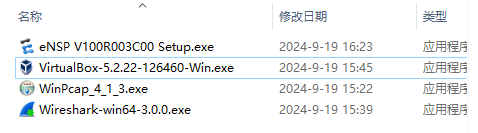
本实验同款环境:通过网盘分享的文件:计算机网络拓扑实验所需的配置软件
链接 : https://pan.baidu.com/s/1yHLcijdIQK8Ggl2r-l2Yqg?pwd=opop 提取码: opop)
一、基础连通性配置、测试。
1、client1与sever2配置。


2、AR1、AR2、AR3配置。
<Huawei>system-view
[Huawei]sysname AR1
[AR1]interface GigabitEthernet 0/0/0
[AR1-GigabitEthernet0/0/0]ip address 192.168.1.1 24
[AR1-GigabitEthernet0/0/0]quit
[AR1]interface GigabitEthernet 0/0/1
[AR1-GigabitEthernet0/0/1]ip address 10.1.12.1 30
[AR1-GigabitEthernet0/0/1]quit
<Huawei>system-view
[Huawei]sysname AR2
[AR2]interface GigabitEthernet 0/0/0
[AR2-GigabitEthernet0/0/0]ip address 10.1.12.2 30
[AR2-GigabitEthernet0/0/0]quit
[AR2]interface GigabitEthernet 0/0/1
[AR2-GigabitEthernet0/0/1]ip address 10.1.23.1 30
[AR2-GigabitEthernet0/0/1]quit
<Huawei>system-view
[Huawei]sysname AR3
[AR3]interface GigabitEthernet 0/0/0
[AR3-GigabitEthernet0/0/0]ip address 10.1.23.2 30
[AR3-GigabitEthernet0/0/0]quit
[AR3]interface GigabitEthernet 0/0/1
[AR3-GigabitEthernet0/0/1]ip address 192.168.2.1 24
[AR3-GigabitEthernet0/0/1]quit 3、内网联通性测试。
[AR1]ping 192.168.1.2 #client1和AR1连通性测试
PING 192.168.1.2: 56 data bytes, press CTRL_C to break
Reply from 192.168.1.2: bytes=56 Sequence=1 ttl=255 time=140 ms
Reply from 192.168.1.2: bytes=56 Sequence=2 ttl=255 time=30 ms
Reply from 192.168.1.2: bytes=56 Sequence=3 ttl=255 time=30 ms
Reply from 192.168.1.2: bytes=56 Sequence=4 ttl=255 time=20 ms
Reply from 192.168.1.2: bytes=56 Sequence=5 ttl=255 time=30 ms
--- 192.168.1.2 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 20/50/140 ms
[AR3]ping 192.168.2.2 #server21和AR3连通性测试
PING 192.168.2.2: 56 data bytes, press CTRL_C to break
Reply from 192.168.2.2: bytes=56 Sequence=1 ttl=255 time=120 ms
Reply from 192.168.2.2: bytes=56 Sequence=2 ttl=255 time=30 ms
Reply from 192.168.2.2: bytes=56 Sequence=3 ttl=255 time=30 ms
Reply from 192.168.2.2: bytes=56 Sequence=4 ttl=255 time=20 ms
Reply from 192.168.2.2: bytes=56 Sequence=5 ttl=255 time=40 ms
--- 192.168.2.2 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 20/48/120 msclient1和AR1连通性测试成功。server2和AR3的连通性测试成功。
4、公网路由配置、测试。
使用OSPF协议将AR1、AR2、AR3的公网接口联通,使它们能相互通信:
[AR1]ospf 1 router-id 1.1.1.1
[AR1-ospf-1]area 0.0.0.0
[AR1-ospf-1-area-0.0.0.0]network 10.1.12.1 0.0.0.3
[AR1-ospf-1-area-0.0.0.0]quit
[AR1-ospf-1]quit
[AR1]ip route-static 192.168.2.0 24 10.1.12.2 #保留私网指向静态路由
[AR2]ospf 1 router-id 2.2.2.2
[AR2-ospf-1]area 0.0.0.0
[AR2-ospf-1-area-0.0.0.0]network 10.1.12.2 0.0.0.3
[AR2-ospf-1-area-0.0.0.0]network 10.1.23.2 0.0.0.3
[AR2-ospf-1-area-0.0.0.0]quit
[AR2-ospf-1]quit #纯公网转发,无需私网静态路由
[AR3]ospf 1 router-id 3.3.3.3
[AR3-ospf-1]area 0.0.0.0
[AR3-ospf-1-area-0.0.0.0]network 10.1.23.0 0.0.0.3
[AR3-ospf-1-area-0.0.0.0]quit
[AR3-ospf-1]quit
[AR3]ip route-static 192.168.1.0 24 10.1.23.1公网联通性测试:
[AR1]ping -a 10.1.12.1 10.1.23.2
PING 10.1.23.3: 56 data bytes, press CTRL_C to break
Reply from 10.1.23.3: bytes=56 Sequence=1 ttl=255 time=30 ms
Reply from 10.1.23.3: bytes=56 Sequence=2 ttl=255 time=20 ms
Reply from 10.1.23.3: bytes=56 Sequence=3 ttl=255 time=20 ms
Reply from 10.1.23.3: bytes=56 Sequence=4 ttl=255 time=20 ms
Reply from 10.1.23.3: bytes=56 Sequence=5 ttl=255 time=20 ms
--- 10.1.23.3 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 20/22/30 msar1到ar3的公网路由打通成功。
[AR1]display ospf peer brief
OSPF Process 1 with Router ID 1.1.1.1
Peer Statistic Information
----------------------------------------------------------------------------
Area Id Interface Neighbor id State
0.0.0.0 GigabitEthernet0/0/1 2.2.2.2 Full
----------------------------------------------------------------------------
[AR1]display ip routing-table
Route Flags: R - relay, D - download to fib
------------------------------------------------------------------------------
Routing Tables: Public
Destinations : 11 Routes : 11
Destination/Mask Proto Pre Cost Flags NextHop Interface
10.1.12.0/30 Direct 0 0 D 10.1.12.1 GigabitEthernet
0/0/1
10.1.12.1/32 Direct 0 0 D 127.0.0.1 GigabitEthernet
0/0/1
10.1.12.3/32 Direct 0 0 D 127.0.0.1 GigabitEthernet
0/0/1
10.1.23.0/30 OSPF 10 2 D 10.1.12.2 GigabitEthernet
0/0/1
127.0.0.0/8 Direct 0 0 D 127.0.0.1 InLoopBack0
127.0.0.1/32 Direct 0 0 D 127.0.0.1 InLoopBack0
127.255.255.255/32 Direct 0 0 D 127.0.0.1 InLoopBack0
192.168.1.0/24 Direct 0 0 D 192.168.1.1 GigabitEthernet
0/0/0
192.168.1.1/32 Direct 0 0 D 127.0.0.1 GigabitEthernet
0/0/0
192.168.1.255/32 Direct 0 0 D 127.0.0.1 GigabitEthernet
0/0/0
255.255.255.255/32 Direct 0 0 D 127.0.0.1 InLoopBack0二、IPsec配置、测试。
计算机A和计算机B使用IPsec进行通信的流程:(IPsec是网络层协议)
(1)初始化。A发送数据包给B,发现未建立IPsec SA(security association),触发协商。
(2)IKE(互联网密钥交换)第一阶段:建立IKE SA。
A-----发出策略提议(如加密方式、认证方式等)------>B,B----发送策略接受-------------->A;
A-----发送DH公钥、随机数等------------------->B,B----发送DH公钥、随机数等-------->A;
结果:双方计算共享密钥,认证身份,成功建立IKE SA(即协商结果)。
(3)IKE(Internet key exchange)第二阶段:建立IPsec SA。
A-----(通过IKE SA加密)发起IPsec协商-------->B,B---(通过IKE SA加密)确认IPsec SA参数--->A;
(4)数据传输。
A-----使用IPsec SA发送加密的业务数据包---->B,B---使用IPsec SA发送加密的业务数据包--->A;
(5)IPsec生命周期结束或通信中断,隧道拆除。1、AR1上的配置:
(1)定义ACL。
[AR1]acl 3000 #(client1网段到sever2网段是需要加密的流量)
[AR1-acl-adv-3000]rule 5 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
[AR1-acl-adv-3000]quit (2)IKE第一阶段协商配置。
①配置IKE安全提议。
[AR1]ike proposal 1
[AR1-ike-proposal-1]encryption-algorithm aes-cbc-128 //AES128位对称加密算法
[AR1-ike-proposal-1]authentication-algorithm sha1 //SHA1算法验证数据的完整性和真实性
[AR1-ike-proposal-1]dh group14 #Diffie-Hellman (DH) 密钥交换算法是非对称的:
[AR1-ike-proposal-1]quit - AR1 和 AR3 用 DH 算法各自生成一对公私钥,互相交换公钥,然后各自算出 相同的对称密钥。即使有人在中间抓包,拿到公钥也算不出最终的对称密钥。
- 这就是 IPsec 的经典组合:
- DH (非对称):安全交换密钥。
- AES (对称):高效加密数据。
②配置ike对等体。
[AR1]ike peer AR3 v1
[AR1-ike-peer-AR3]pre-shared-key simple Huawei@123
[AR1-ike-peer-AR3]ike-proposal 1
[AR1-ike-peer-AR3]remote-address 10.1.23.2 #对端公网接口IP
[AR1-ike-peer-AR3]quit (3)IPsec第二阶段配置。
①配置IPsec安全提议。
[AR1]ipsec proposal trans1
[AR1-ipsec-proposal-trans1]encapsulation-mode tunnel #这里的传输模式是隧道模式
[AR1-ipsec-proposal-trans1]transform esp
[AR1-ipsec-proposal-trans1]esp encryption-algorithm aes-128
[AR1-ipsec-proposal-trans1]esp authentication-algorithm sha1
[AR1-ipsec-proposal-trans1]quit 这里设置的是隧道模式:加密了整个数据包,网络开销较高,但安全性也较高。
如果设置为传输模式AR1-ipsec-policy-isakmp-AR1-Policy-10 encapsulation-mode transport,则只加密有效载荷,网络开销较低,安全性也较低。
②创建IPsec策略。
[AR1]ipsec policy policy1 10 isakmp
[AR1-ipsec-policy-isakmp-policy1-10]security acl 3000
[AR1-ipsec-policy-isakmp-policy1-10]ike-peer AR3
[AR1-ipsec-policy-isakmp-policy1-10]proposal trans1
[AR1-ipsec-policy-isakmp-policy1-10]quit (4)应用策略到公网接口.
[AR1]interface GigabitEthernet 0/0/1
[AR1-GigabitEthernet0/0/1]ipsec policy policy1
[AR1-GigabitEthernet0/0/1]quit 2、AR3上的配置:
(1)定义ACL。
[AR3]acl 3000 #(和AR1相比:源地址和目的地址互换)
[AR3-acl-adv-3000]rule 5 permit ip source 192.168.2.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[AR3-acl-adv-3000]quit (2)IKE第一阶段协商配置。
①配置IKE安全提议。
[AR3]ike proposal 1 #(和AR1相比:完全相同)
[AR3-ike-proposal-1]encryption-algorithm aes-cbc-128
[AR3-ike-proposal-1]authentication-algorithm sha1
[AR3-ike-proposal-1]dh group14
[AR3-ike-proposal-1]quit ②配置ike对等体。
[AR3]ike peer AR1 v1 #(和AR1相比:peer名字和对端公网接口互换)
[AR3-ike-peer-AR1]pre-shared-key simple Huawei@123
[AR3-ike-peer-AR1]ike-proposal 1
[AR3-ike-peer-AR1]remote-address 10.1.12.1
[AR3-ike-peer-AR1]quit(3)IPsec第二阶段配置。
①配置IPsec安全提议。
[AR3]ipsec proposal trans1 #(和AR1相比:完全相同)
[AR3-ipsec-proposal-trans1]encapsulation-mode tunnel
[AR3-ipsec-proposal-trans1]transform esp
[AR3-ipsec-proposal-trans1]esp encryption-algorithm aes-128
[AR3-ipsec-proposal-trans1]esp authentication-algorithm sha1
[AR3-ipsec-proposal-trans1]quit②创建IPsec策略。
[AR3]ipsec policy policy1 10 isakmp #(和AR1相比:peer名字互换)
[AR3-ipsec-policy-isakmp-policy1-10]security acl 3000
[AR3-ipsec-policy-isakmp-policy1-10]ike-peer AR1
[AR3-ipsec-policy-isakmp-policy1-10]proposal trans1
[AR3-ipsec-policy-isakmp-policy1-10]quit(4)应用策略到公网接口
[AR3]interface GigabitEthernet 0/0/0 #(和AR1相比:公网接口是000)
[AR3-GigabitEthernet0/0/0]ipsec policy policy1
[AR3-GigabitEthernet0/0/0]quit 3、 配置测试。
(1)触发隧道建立
在 Client1 上执行 ping 192.168.2.2(需确保 Client1 支持命令行,否则用 AR1 的 ping -a 192.168.1.1 192.168.2.2 模拟触发)。
[AR1]ping -a 192.168.1.1 192.168.2.2
PING 192.168.2.2: 56 data bytes, press CTRL_C to break
Reply from 192.168.2.2: bytes=56 Sequence=1 ttl=255 time=90 ms
Reply from 192.168.2.2: bytes=56 Sequence=2 ttl=255 time=40 ms
Reply from 192.168.2.2: bytes=56 Sequence=3 ttl=255 time=40 ms
Reply from 192.168.2.2: bytes=56 Sequence=4 ttl=255 time=50 ms
Reply from 192.168.2.2: bytes=56 Sequence=5 ttl=255 time=30 ms
--- 192.168.2.2 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 30/50/90 ms(2)查看 IPsec 安全联盟
[AR1]display ipsec sa
===============================
Interface: GigabitEthernet0/0/1
Path MTU: 1500
===============================
-----------------------------
IPSec policy name: "policy1"
Sequence number : 10
Acl Group : 3000
Acl rule : 5
Mode : ISAKMP
-----------------------------
Connection ID : 13
Encapsulation mode: Tunnel
Tunnel local : 10.1.12.1
Tunnel remote : 10.1.23.2
Flow source : 192.168.1.0/255.255.255.0 0/0
Flow destination : 192.168.2.0/255.255.255.0 0/0
Qos pre-classify : Disable
[Outbound ESP SAs]
SPI: 3951477948 (0xeb86c4bc)
Proposal: ESP-ENCRYPT-AES-128 ESP-AUTH-SHA1
SA remaining key duration (bytes/sec): 1887329280/3488
Max sent sequence-number: 5
UDP encapsulation used for NAT traversal: N
[Inbound ESP SAs]
SPI: 87806325 (0x53bd175)
Proposal: ESP-ENCRYPT-AES-128 ESP-AUTH-SHA1
SA remaining key duration (bytes/sec): 1887436380/3488
Max received sequence-number: 5
Anti-replay window size: 32
UDP encapsulation used for NAT traversal: NIPsec隧道建立成功了。
-
存在有效的 SPI (安全参数索引):
- 出方向 SPI:
0xeb86c4bc - 入方向 SPI:
0x53bd175
这两个非零的 SPI 说明 IPsec 第二阶段协商已经完成,隧道建立成功。
- 出方向 SPI:
-
序列号在增加:
-
Max sent sequence-number: 5→ 已经发送了 5 个加密包 -
Max received sequence-number: 5→ 已经收到了 5 个加密包这说明数据已经在隧道中双向加密传输,隧道不仅建立,而且正在正常工作。
-
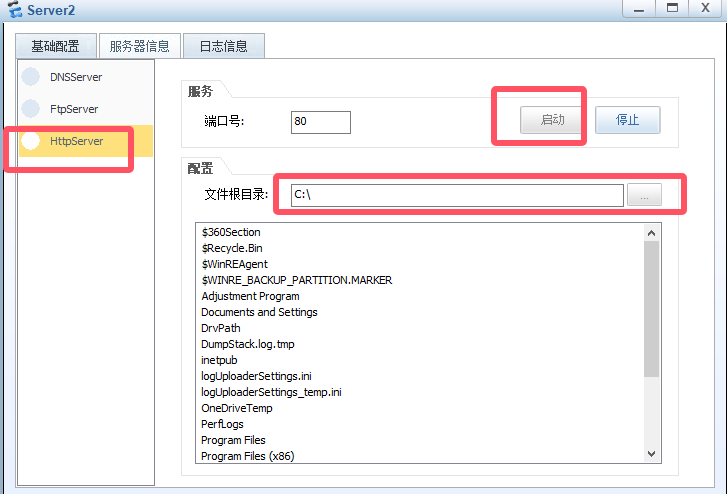
(3)Httpsever配置与测试
双击打开sever2设备-服务器信息-HttpSever-选择文件根目录为C盘-点击启动,如下图所示:
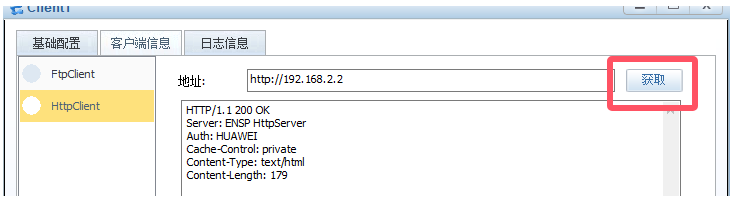
双击打开Client1-客户端信息-HttpClient-输入server2的IP地址http://192.168.2.2,成功获取文件
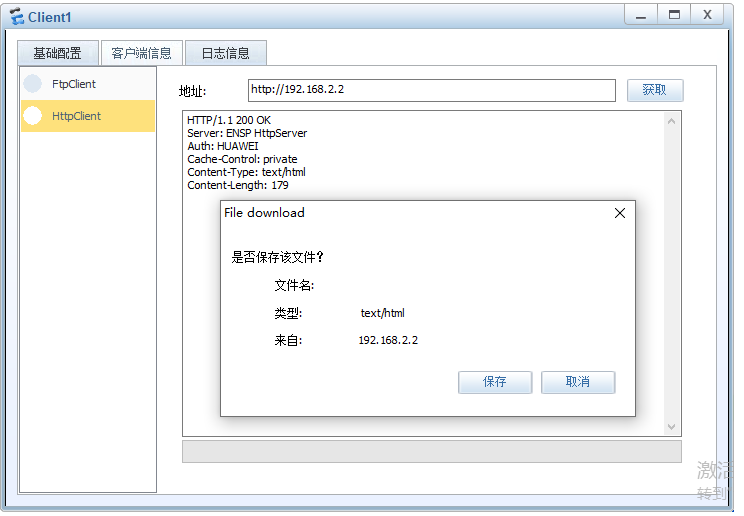
HTTP/1.1 200 OK 就是 HTTP 服务成功响应的标准状态码,这表示 Client1 已经通过 IPsec 加密隧道成功访问到了 Server2 上的网页服务,实验目标达成!
(4)Ftpsever配置与测试
在本地电脑的G盘新建一个"helloworld.txt"文件。

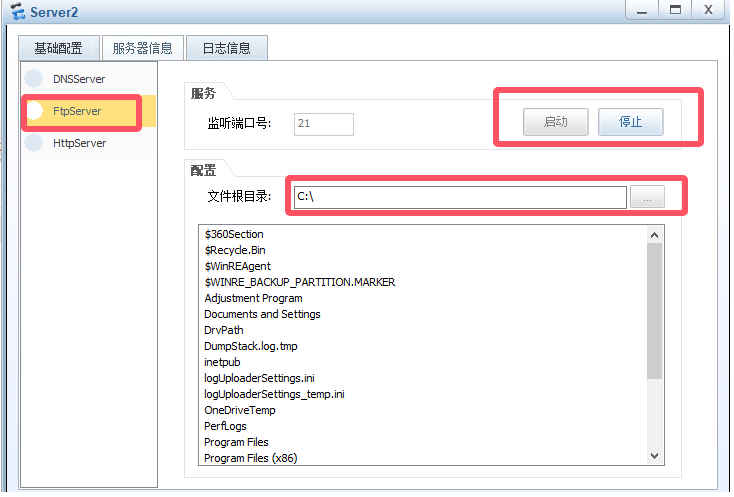
双击打开sever2-ftpsever-根目录选择c盘-启动监听端口:
双击打开client1-ftpclient-服务器地址192.168.2.2-点击登录-将G盘刚刚创建的文件helloworld.txt-点击大于号:
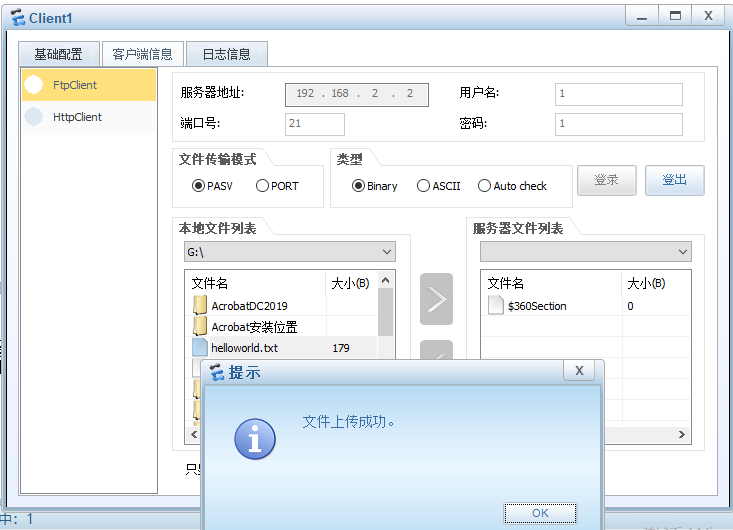
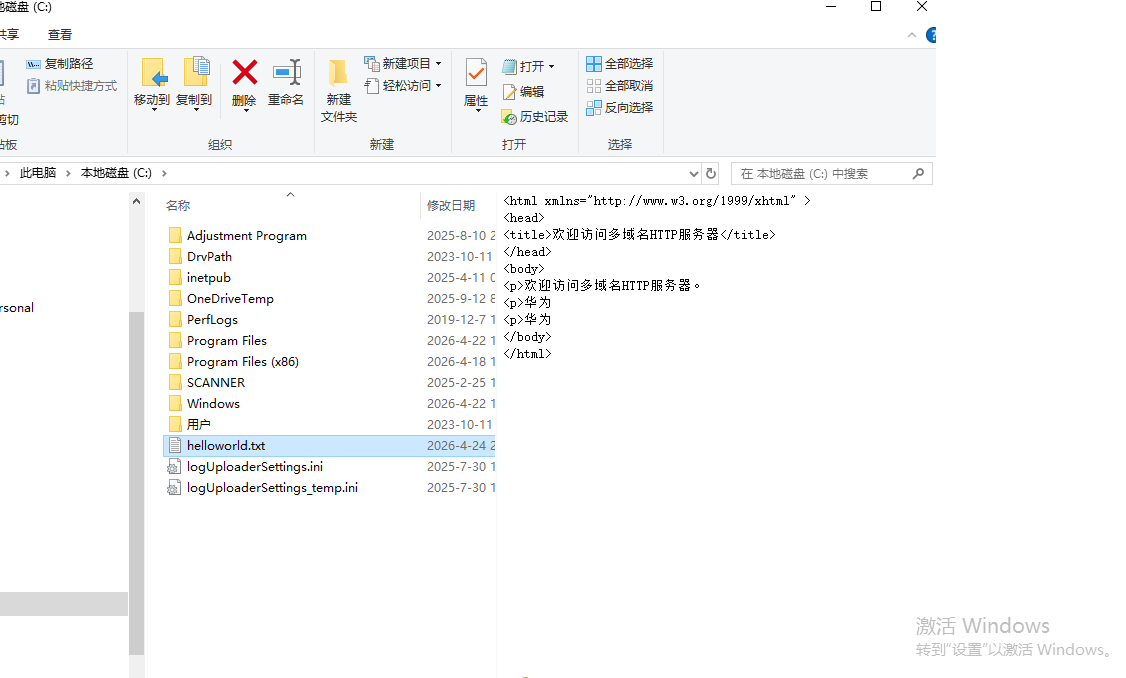
打开本地c盘发现刚刚创建好的helloworld.txt文件从G盘传过来了。
(5)通过抓包验证加密
①点击AR2,右键-数据抓包-0/0/0端口或者 0/0/1端口:
点击client1的HttpClient-获取,
在 Wireshark 的显示过滤器栏输入 esp,回车。
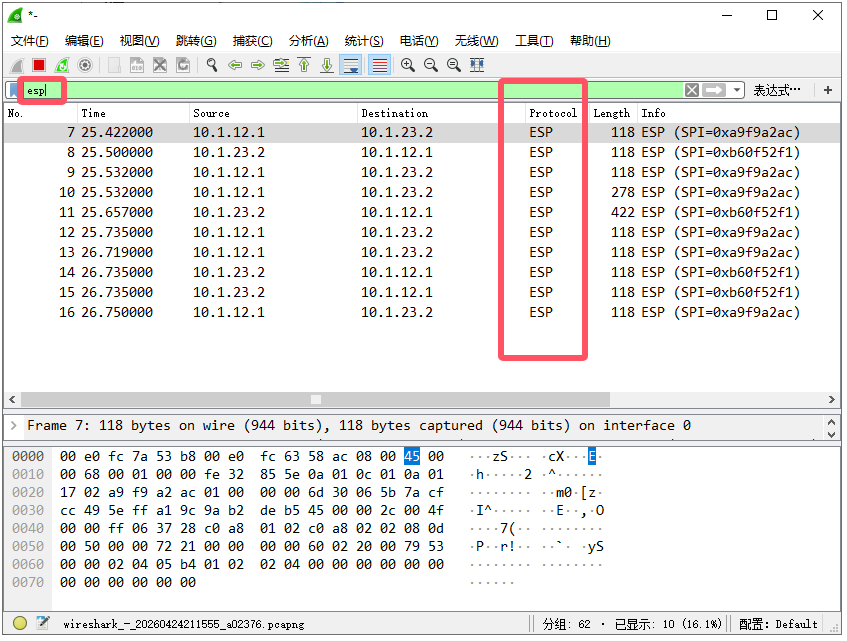
ESP 报文内部不会显示 任何 192.168.1.2、192.168.2.2 或 ICMP 的详细信息,因为这些内容已被加密并封装在 ESP 的加密载荷中。
在 AR2 的抓包,ICMP 报文应显示为 ESP 封装,看不到原始内层 IP 信息。这表示通信信息成功加密了。
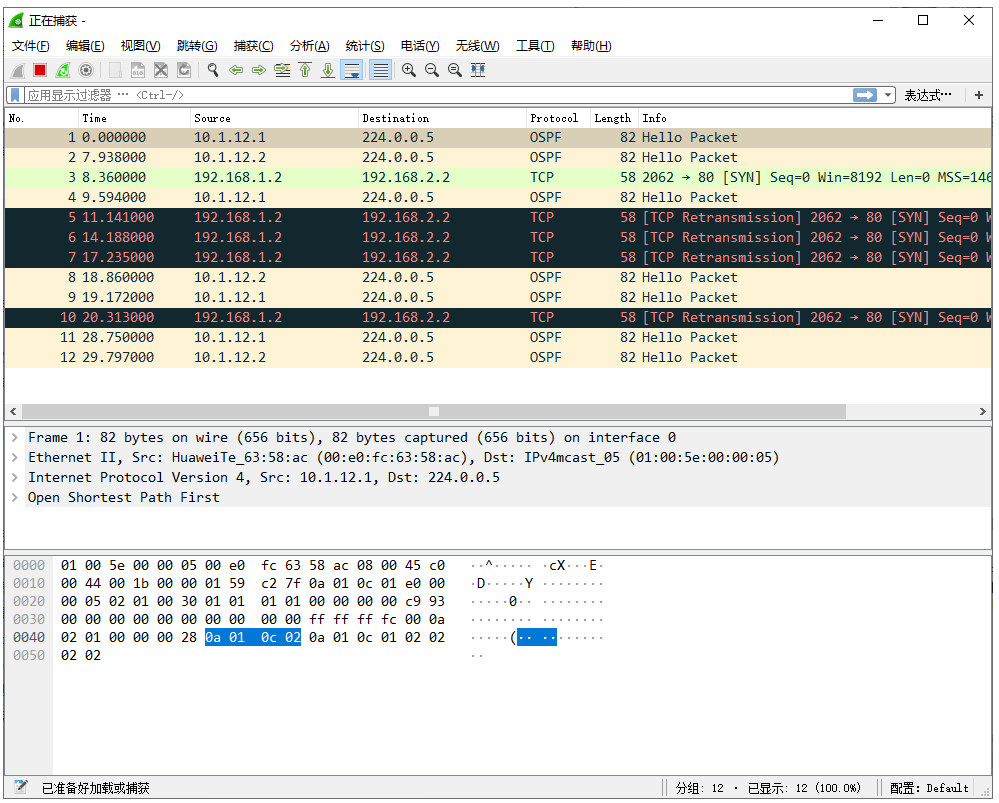
②对比非加密时的报文。暂时移除 IPsec 策略(undo ipsec policy):
[AR1] interface GigabitEthernet 0/0/1
[AR1-GigabitEthernet0/0/1] undo ipsec policy
[AR1-GigabitEthernet0/0/1] quit
[AR3] interface GigabitEthernet 0/0/0
[AR3-GigabitEthernet0/0/0] undo ipsec policy
[AR3-GigabitEthernet0/0/0] quit用相同方式抓包过滤 icmp,看到完整的 ICMP 请求/应答,里面直接包含内层源 IP 192.168.1.2 和目标 IP 192.168.2.2。
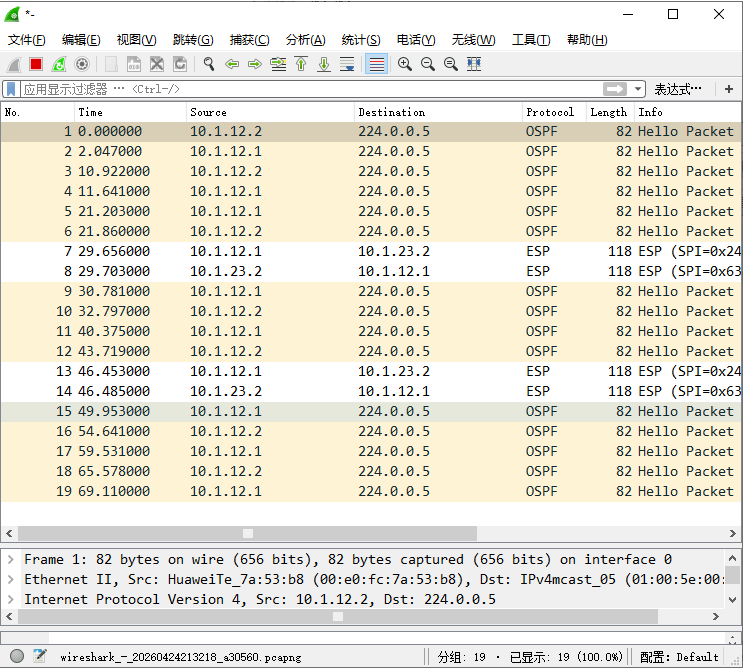
重新恢复 IPsec策略:
[AR1] interface GigabitEthernet 0/0/1
[AR1-GigabitEthernet0/0/1] ipsec policy policy1
[AR3] interface GigabitEthernet 0/0/0
[AR3-GigabitEthernet0/0/0] ipsec policy AR3-PolicyClient1再次通过HttpClient获取请求server2。可以看到这些内层 IP 就被 ESP 完全"吞没"了。
(6)别忘记保存本实验的配置哦。
<AR1>save
The current configuration will be written to the device.
Are you sure to continue? (y/n)[n]:y
It will take several minutes to save configuration file, please wait..........
Configuration file had been saved successfully
Note: The configuration file will take effect after being activated
<AR2>save
The current configuration will be written to the device.
Are you sure to continue? (y/n)[n]:y
It will take several minutes to save configuration file, please wait........
Configuration file had been saved successfully
Note: The configuration file will take effect after being activated
<AR3>save
The current configuration will be written to the device.
Are you sure to continue? (y/n)[n]:y
It will take several minutes to save configuration file, please wait........
Configuration file had been saved successfully
Note: The configuration file will take effect after being activated三、网工真题实战
有时间再写咯......