安装EFS相关插件
bash
[root@ip-172-31-26-146 ~]# helm repo add aws-efs-csi-driver https://kubernetes-sigs.github.io/aws-efs-csi-driver/
"aws-efs-csi-driver" has been added to your repositories
[root@ip-172-31-26-146 ~]# helm repo update aws-efs-csi-driver
Hang tight while we grab the latest from your chart repositories...
...Successfully got an update from the "aws-efs-csi-driver" chart repository
Update Complete. ⎈Happy Helming!⎈- 出现servcesaccount报错
bash
[root@ip-172-31-26-146 ~]# helm upgrade --install aws-efs-csi-driver --namespace kube-system aws-efs-csi-driver/aws-efs-csi-driver
Release "aws-efs-csi-driver" does not exist. Installing it now.
Error: Unable to continue with install: ServiceAccount "efs-csi-controller-sa" in namespace "kube-system" exists and cannot be imported into the current release: invalid ownership metadata; label validation error: key "app.kubernetes.io/managed-by" must equal "Helm": current value is "eksctl"; annotation validation error: missing key "meta.helm.sh/release-name": must be set to "aws-efs-csi-driver"; annotation validation error: missing key "meta.helm.sh/release-namespace": must be set to "kube-system"- 解决办法,跳过servicesaccount创建,指定现有的
bash
[root@ip-172-31-26-146 ~]# kubectl create serviceaccount efs-csi-node-sa -n kube-system
[root@ip-172-31-26-146 ~]# helm upgrade --install aws-efs-csi-driver aws-efs-csi-driver/aws-efs-csi-driver \
--namespace kube-system \
--set controller.serviceAccount.create=false \
--set controller.serviceAccount.name=efs-csi-controller-sa \
--set node.serviceAccount.create=false \
--set node.serviceAccount.name=efs-csi-node-sa
Release "aws-efs-csi-driver" does not exist. Installing it now.
NAME: aws-efs-csi-driver
LAST DEPLOYED: Fri Apr 24 13:49:46 2026
NAMESPACE: kube-system
STATUS: deployed
REVISION: 1
TEST SUITE: None
NOTES:
To verify that aws-efs-csi-driver has started, run:
kubectl get pod -n kube-system -l "app.kubernetes.io/name=aws-efs-csi-driver,app.kubernetes.io/instance=aws-efs-csi-driver"创建存储类
yaml文件内容
yaml
kind: StorageClass
apiVersion: storage.k8s.io/v1
metadata:
name: cfs # 这是你在 values.yaml 中要填写的名字
provisioner: efs.csi.aws.com
parameters:
provisioningMode: efs-ap
fileSystemId: fs-xxxxxxxxxxxxxxxxx # 【关键】替换成你在 AWS 控制台创建的 EFS ID
directoryPerms: "700"
gidRangeStart: "1000" # 可选
gidRangeEnd: "2000" # 可选
basePath: "/dynamic_provisioning" # 可选
[root@ip-172-31-26-146 yaml]# kubectl apply -f cfs-sc.yaml
storageclass.storage.k8s.io/efs-sc created
[root@ip-172-31-26-146 yaml]# kubectl get sc
NAME PROVISIONER RECLAIMPOLICY VOLUMEBINDINGMODE ALLOWVOLUMEEXPANSION AGE
efs-sc efs.csi.aws.com Delete Immediate false 23s- 出现报错
efs-csi-node起不来
bash
[root@ip-172-31-26-146 multifect-server]# kubectl get ds efs-csi-node -n kube-system
NAME DESIRED CURRENT READY UP-TO-DATE AVAILABLE NODE SELECTOR AGE
efs-csi-node 4 0 0 0 0 kubernetes.io/os=linux 27m授权
bash
[root@ip-172-31-26-146 charts]# kubectl get sa efs-csi-controller-sa -n kube-system -o yaml | grep role-arn
eks.amazonaws.com/role-arn: arn:aws:iam::xxxxx:role/EKS_EFS_CSI_Driver检查 IAM 权限策略
请去 AWS 控制台确认该角色(EKS_EFS_CSI_Driver)是否关联了 AmazonEFSCSIDriverPolicy。
这个驱动程序需要执行 elasticfilesystem:CreateAccessPoint 等操作。如果角色虽然挂载了,但里面是空的或者权限不足,就会报错。

这个驱动程序需要执行 elasticfilesystem:CreateAccessPoint 等操作。如果角色虽然挂载了,但里面是空的或者权限不足,就会报错。
检查 OIDC 信任关系 (最隐蔽的原因)
即使角色有权限,如果它"不信任"你的 EKS 集群,AWS 也会拒绝授权。
核对步骤:
获取集群 OIDC ID:
bash
aws eks describe-cluster --name <你的集群名> --query "cluster.identity.oidc.issuer" --output text
# 输出结果类似:https://oidc.eks.us-east-2.amazonaws.com/id/EXAMPLEDOCUMENT123检查 IAM 角色信任关系:
在 IAM 控制台找到 EKS_EFS_CSI_Driver 角色,点击 Trust relationships(信任关系)页签。
对比 ID:
确认 JSON 中的 Federated 字段里的 ID 与你上面查到的 ID 完全一致。
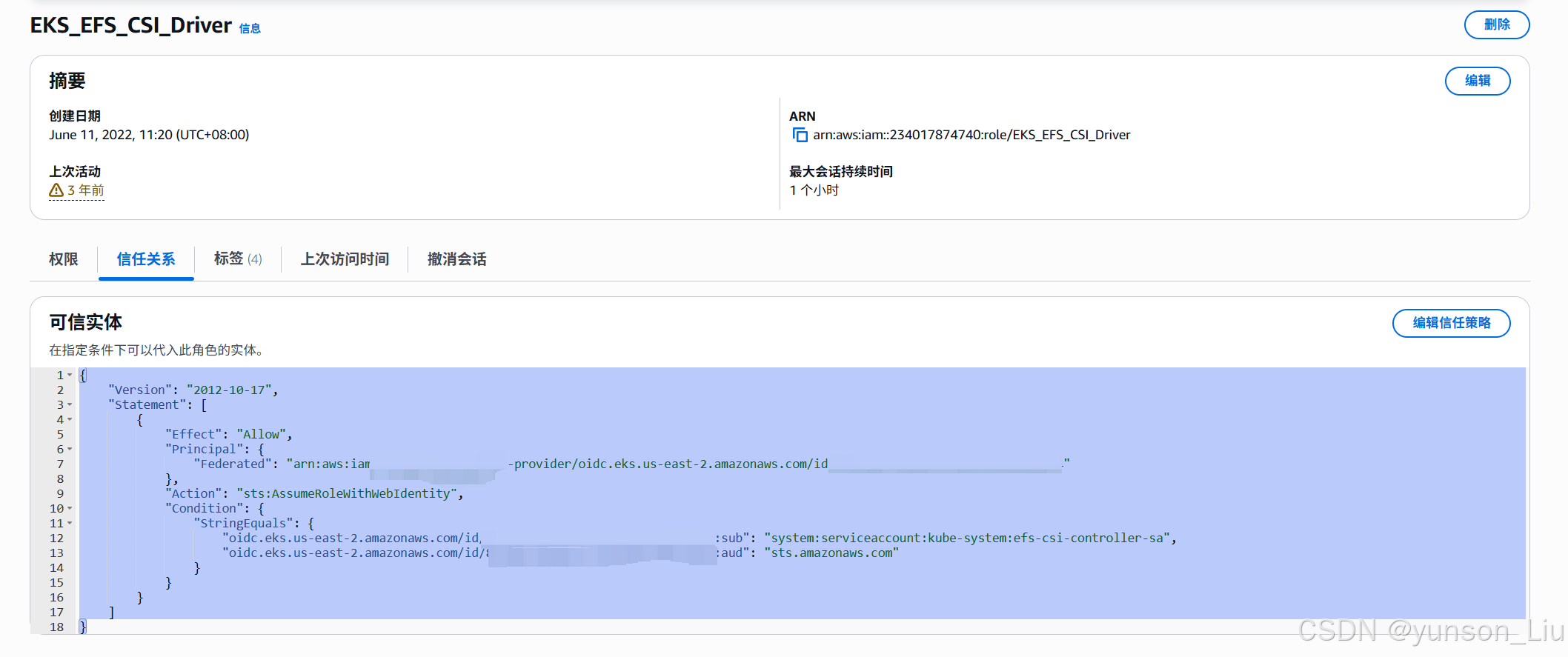
json
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"Federated": "arn:aws:iam::xxxx:oidc-provider/oidc.eks.us-east-2.amazonaws.com/id/xxxxxx"
},
"Action": "sts:AssumeRoleWithWebIdentity",
"Condition": {
"StringEquals": {
"oidc.eks.us-east-2.amazonaws.com/id/xxxx:sub": "system:serviceaccount:kube-system:efs-csi-controller-sa",
"oidc.eks.us-east-2.amazonaws.com/id/xxxxx:aud": "sts.amazonaws.com"
}
}
}
]
}注意
创建efs对已经的pvc的时候要注意指定sc、开启sc的安全组2049端口