定义
在CTF中,如果存在对密码的提示,如压缩包密码以"abc"开头且总长度为7,我们就会优先采用字典破解的方式。
这里我们用会用到在Kali中用到的工具crunch
如:
bash
crunch 10 10 -t abc%%%%%%% -o abc_7digit.txtcrunch 10 10:固定生成 10 位 字符串
-t abc%%%%%%%:模板参数
abc:固定开头
%:代表数字 0-9,写 7 个就是 7 位数字
@:小写字母 a-z
,:大写字母 A-Z
^:特殊符号
-o abc_7digit.txt:把字典保存到文件里
-z gzip:压缩输出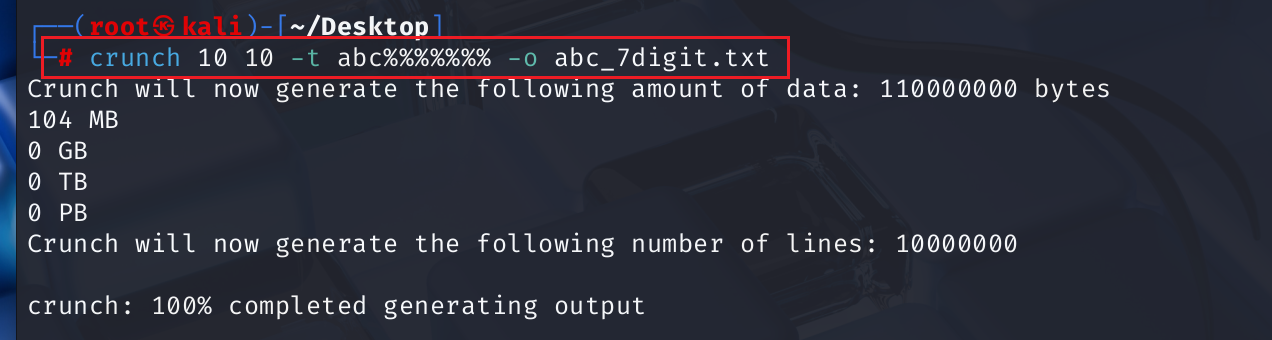
实战:[第八章][8.2.3 字典破解]字典破解

这道题,《CTF实战:从入门到提升》这本书里没有给一点提示,所以就得把能想到的所有CTF常用字典,Top1000字典搞来,暴力破解一遍。这里我问了Workbuddy,生成了一个字典脚本.py,字典脚本脚本如下:
python
import zipfile
import itertools
import string
# ============================================================
# CTF 字典破解 ZIP
# 字典来源:
# 1. CTF 高频密码(比赛中出现最多的)
# 2. 常见数字组合
# 3. 键盘走位
# 4. 常见英文弱密码
# 5. ctf/flag 相关变体
# ============================================================
ZIP_PATH = r'c:\Users\lenovo\WorkBuddy\Claw\字典破解.zip'
# --- CTF & 通用高频密码字典 ---
CTF_WORDLIST = [
# CTF 专用
"flag", "ctf", "ctf123", "flag123", "ctfctf", "passwd", "password",
"p@ssw0rd", "p@ssword", "passw0rd", "admin", "admin123", "administrator",
"root", "root123", "toor", "test", "test123", "guest", "guest123",
# 数字序列
"123456", "1234567", "12345678", "123456789", "1234567890",
"111111", "222222", "333333", "666666", "888888", "000000",
"123123", "321321", "112233", "123321", "1q2w3e", "1q2w3e4r",
"1q2w3e4r5t", "qwerty", "qwerty123", "qwertyuiop",
# 常见英文弱密码
"password", "password1", "password123", "iloveyou", "sunshine",
"princess", "monkey", "dragon", "master", "letmein", "welcome",
"login", "hello", "hello123", "abc123", "abcd1234", "baseball",
"football", "shadow", "superman", "batman", "trustno1",
# 键盘走位
"qazwsx", "zxcvbnm", "asdfgh", "asdfghjkl", "1234qwer",
# 年份/日期
"2020", "2021", "2022", "2023", "2024", "2025",
"20200101", "20210101", "20221212", "19891231",
# 中文拼音常见
"woaini", "woshini", "nihaoma", "zhongguo", "beijing",
# CTF 平台常见
"hack", "hacker", "hacking", "exploit", "shell", "pwn", "pwned",
"reverse", "crypto", "web", "misc", "binary",
# 空密码
"",
# 其他
"pass", "123", "1234", "12345", "654321", "7654321",
"a123456", "a12345678", "aa123456",
"abc", "abcdef", "abcdefg", "abcdefgh",
"111", "1111", "11111", "000", "0000", "00000",
"9999", "99999", "8888", "88888", "7777", "6666", "5555",
"4321", "4444", "3333", "2222", "1111", "3141592",
"123qwe", "123abc", "a1b2c3", "aaa111",
"success", "game", "love", "god", "sex", "god123",
"michael", "jessica", "charlie", "thomas", "robert",
"pokemon", "starwars", "matrix", "linux", "windows",
]
# --- 生成额外的数字组合 (4-8位纯数字) ---
extra = []
# 4位
for n in range(0, 10000):
extra.append(f"{n:04d}")
# 6位常见
for n in [100000,110000,111111,112233,121212,123321,123456,
123654,132456,147258,159357,159753,192168,200000,
202020,210987,212121,246810,258369,314159,321654,
456789,519519,520520,521521,654321,666666,696969,
741852,741963,753951,789456,852456,852963,963852,
987654,999999]:
extra.append(str(n))
wordlist = CTF_WORDLIST + extra
print(f"[*] 字典总词条数: {len(wordlist)}")
print(f"[*] 开始破解: {ZIP_PATH}")
print()
found = False
count = 0
try:
zf = zipfile.ZipFile(ZIP_PATH)
for pwd in wordlist:
count += 1
if count % 500 == 0:
print(f" [~] 已尝试 {count}/{len(wordlist)} ... 当前: {repr(pwd)}")
try:
zf.extractall(
path=r'c:\Users\lenovo\WorkBuddy\Claw\cracked_output',
pwd=pwd.encode('utf-8')
)
print(f"\n[+] 破解成功!密码是: {repr(pwd)}")
found = True
break
except (RuntimeError, zipfile.BadZipFile):
continue
except Exception:
# 尝试 latin-1 编码
try:
zf.extractall(
path=r'c:\Users\lenovo\WorkBuddy\Claw\cracked_output',
pwd=pwd.encode('latin-1')
)
print(f"\n[+] 破解成功!密码是: {repr(pwd)}")
found = True
break
except Exception:
continue
except Exception as e:
print(f"[-] 打开ZIP出错: {e}")
if not found:
print(f"\n[-] 字典破解失败,已尝试 {count} 个密码,未找到匹配项")
print(" 建议:尝试更大字典(如 rockyou.txt)或暴力破解")
else:
import os
out_dir = r'c:\Users\lenovo\WorkBuddy\Claw\cracked_output'
for f in os.listdir(out_dir):
fpath = os.path.join(out_dir, f)
print(f"[*] 解压文件: {fpath}")
try:
content = open(fpath, 'rb').read()
print(f"[*] 内容: {content}")
except Exception:
pass最后拿到密码是:p@ssw0rd。
成功破解压缩包。