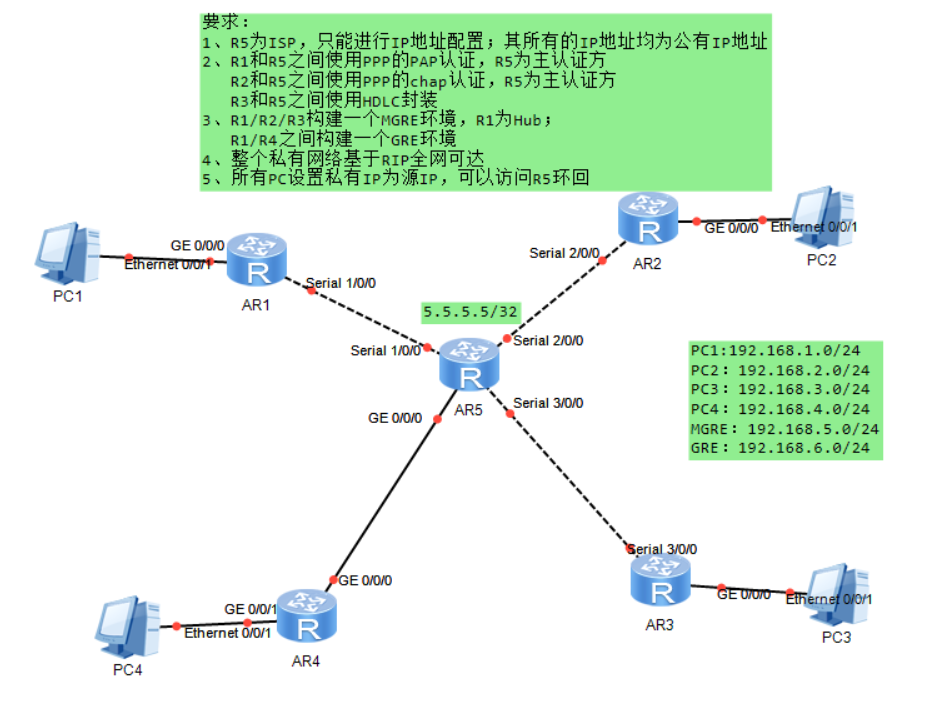
要求:
1、R5 为 ISP,只能进行 IP 地址配置;其所有的 IP 地址均为公有 IP 地址
2、R1 和 R5 之间使用 PPP 的 PAP 认证,R5 为主认证方 R2 和 R5 之间使用 PPP 的 chap 认证,R5 为主认证方 R3 和 R5 之间使用 HDLC 封装
3、R1/R2/R3 构建一个 MGRE 环境,R1 为 Hub; R1/R4 之间构建一个 GRE 环境
4、整个私有网络基于 RIP 全网可达5、所有 PC 设置私有 IP 为源 IP,可以访问 R5 环回
代码实现
1.先给IP地址
AR1 ---AR5 15.0.0.0 24
AR2 ---AR5 25.0.0.0 24
AR3 ---AR5 35.0.0.0 24
AR4 ---AR5 45.0.0.0 24
bash
//AR1
[AR1]interface Serial 1/0/0
[AR1-Serial1/0/0]ip address 15.0.0.1 24
[AR1-Serial1/0/0]int g 0/0/0
[AR1-GigabitEthernet0/0/0]ip address 192.168.1.1 24
//AR2
[AR2]INT GigabitEthernet 0/0/0
[AR2-GigabitEthernet0/0/0]IP address 192.168.2.1 24
[AR2-GigabitEthernet0/0/0]int s 2/0/0
[AR2-Serial2/0/0]ip address 25.0.0.1 24
//AR3
[AR3]int Serial 3/0/0
[AR3-Serial3/0/0]ip address 35.0.0.1 24
[AR3]INT G 0/0/0
[AR3-GigabitEthernet0/0/0]ip address 192.168.3.1 24
//AR4
[AR4]int g 0/0/0
[AR4-GigabitEthernet0/0/0]ip address 45.0.0.1 24
[AR4]int GigabitEthernet 0/0/1
[AR4-GigabitEthernet0/0/1]ip address 192.168.4.1 24
//AR5
[AR5]int s 1/0/0
[AR5-Serial1/0/0]ip address 15.0.0.2 24
[AR5-Serial1/0/0]int s 2/0/0
[AR5-Serial2/0/0]ip address 25.0.0.2 24
[AR5-Serial2/0/0]int s 3/0/0
[AR5-Serial3/0/0]ip address 35.0.0.2 24
[AR5-Serial3/0/0]int g 0/0/0
[AR5-GigabitEthernet0/0/0]ip address 45.0.0.2 24
[AR5-GigabitEthernet0/0/0]q
[AR5]int LoopBack 0
[AR5-LoopBack0]ip address 5.5.5.5 322.配认证
bash
//AR5
[AR5]aaa
[AR5-aaa]local-user AR1 P
[AR5-aaa]local-user AR1 password cipher 123456
Info: Add a new user.
[AR5-aaa]local-user AR1 service-type ppp
[AR5-aaa]q
[AR5]int s 1/0/0
[AR5-Serial1/0/0]ppp authentication-mode pap
[AR5-Serial1/0/0]q
[AR5-aaa]local-user AR2 password cipher 123456
Info: Add a new user.
[AR5-aaa]local-user AR2 service-type ppp
[AR5-aaa]q
[AR5]int s 2/0/0
[AR5-Serial2/0/0]ppp authentication-mode chap
[AR5]int s 3/0/0
[AR5-Serial3/0/0]link-protocol hdlc
Warning: The encapsulation protocol of the link will be changed. Continue? [Y/N]
:y
May 11 2026 19:02:39-08:00 AR5 %%01IFNET/4/CHANGE_ENCAP(l)[4]:The user performed
the configuration that will change the encapsulation protocol of the link and t
hen selected Y.
//AR2
[AR2]int Serial 2/0/0
[AR2-Serial2/0/0]ppp chap user AR2
[AR2-Serial2/0/0]PPP chap password cipher 123456
//AR1
[AR1]int s 1/0/0
[AR1-Serial1/0/0]ppp pap local-user AR1 password cipher 123456
//AR3
[AR3]int Serial 3/0/0
[AR3-Serial3/0/0]link-protocol hdlc 3.构建MERE环境
bash
///MGRE配置
//AR1
[AR1]interface Tunnel 0/0/0
[AR1-Tunnel0/0/0]ip address 192.168.5.1 24
[AR1-Tunnel0/0/0]tunnel-protocol gre p2mp
[AR1-Tunnel0/0/0]source 15.0.0.1
[AR1]rip
[AR1-rip-1]rip 1
[AR1-rip-1]version 2
[AR1-rip-1]network 192.168.1.0
[AR1-rip-1]network 192.168.5.0
[AR1-rip-1]q
[AR1]interface Tunnel 0/0/0
[AR1-Tunnel0/0/0]nhrp entry multicast dynamic
[AR1-Tunnel0/0/0]undo rip split-horizon
//AR3
[AR3]interface Tunnel 0/0/0
[AR3-Tunnel0/0/0]ip address 192.168.5.3 24
[AR3-Tunnel0/0/0]tunnel-protocol gre p2mp
[AR3-Tunnel0/0/0]source Serial 3/0/0
[AR3-Tunnel0/0/0]nhrp entry 192.168.5.1 15.0.0.1 register
[AR3]rip 1
[AR3-rip-1]version 2
[AR3-rip-1]network 192.168.3.0
[AR3-rip-1]network 192.168.5.0
//AR2
[AR2]interface Tunnel 0/0/0
[AR2-Tunnel0/0/0]ip address 192.168.5.2 24
[AR2-Tunnel0/0/0]tunnel-protocol gre p2mp
[AR2-Tunnel0/0/0]source Serial 2/0/0
May 11 2026 19:24:49-08:00 AR2 %%01IFNET/4/LINK_STATE(l)[0]:The line protocol IP
on the interface Tunnel0/0/0 has entered the UP state.
[AR2-Tunnel0/0/0]nhrp entry 192.168.5.1 15.0.0.1 register
[AR2-Tunnel0/0/0]q
[AR2]rip 1
[AR2-rip-1]version 2
[AR2-rip-1]network 192.168.2.0
[AR2-rip-1]network 192.168.5.0
[AR2-rip-1]q
///GRE配置
//AR1
[AR1]interface Tunnel 0/0/1
[AR1-Tunnel0/0/1]ip add 192.168.6.1 24
[AR1-Tunnel0/0/1]tunnel-protocol gre
[AR1-Tunnel0/0/1]source 15.0.0.1
[AR1-Tunnel0/0/1]destination 45.0.0.1
May 11 2026 19:41:39-08:00 AR1 %%01IFNET/4/LINK_STATE(l)[0]:The line protocol IP
on the interface Tunnel0/0/1 has entered the UP state.
[AR1-Tunnel0/0/1]rip 1
[AR1-rip-1]network 192.168.6.0
//AR4
[AR4]interface Tunnel 0/0/1
[AR4-Tunnel0/0/1]ip add 192.168.6.2 24
[AR4-Tunnel0/0/1]tunnel-protocol gre
[AR4-Tunnel0/0/1]source 45.0.0.1
[AR4-Tunnel0/0/1]destination 15.0.0.1
May 11 2026 19:42:32-08:00 AR4 %%01IFNET/4/LINK_STATE(l)[0]:The line protocol IP
on the interface Tunnel0/0/1 has entered the UP state.
[AR4-Tunnel0/0/1]rip 1
[AR4-rip-1]version 2
[AR4-rip-1]network 192.168.6.0
[AR4-rip-1]network 192.168.4.0路由方面 与 nat
bash
指向AR5
[AR1]ip route-static 0.0.0.0 0 15.0.0.2
[AR2]ip route-static 0.0.0.0 0 25.0.0.2
[AR3]ip route-static 0.0.0.0 0 35.0.0.2
[AR4]ip route-static 0.0.0.0 0 45.0.0.2
回路由 这边做了子网汇总
[AR5]ip route-static 192.168.0.0 255.255.0.0 15.0.0.1 # 回 R1 私网
[AR5]ip route-static 192.168.0.0 255.255.0.0 25.0.0.1 # 回 R2 私网
[AR5]ip route-static 192.168.0.0 255.255.0.0 35.0.0.1 # 回 R3 私网
[AR5]ip route-static 192.168.0.0 255.255.0.0 45.0.0.1 # 回 R4 私网
nat
//AR1
[AR1]acl number 2000
[AR1-acl-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[AR1-acl-basic-2000] rule permit source 192.168.5.0 0.0.0.255
[AR1-acl-basic-2000] rule permit source 192.168.6.0 0.0.0.255
[AR1-acl-basic-2000]
[AR1-acl-basic-2000]interface Serial1/0/0
[AR1-Serial1/0/0] nat outbound 2000
//AR2
[AR2]acl number 2000
[AR2-acl-basic-2000]
[AR2-acl-basic-2000] rule permit source 192.168.2.0 0.0.0.255
[AR2-acl-basic-2000]
[AR2-acl-basic-2000] rule permit source 192.168.5.0 0.0.0.255
[AR2-acl-basic-2000]
[AR2-acl-basic-2000]
[AR2-acl-basic-2000]
[AR2-acl-basic-2000]interface Serial2/0/0
[AR2-Serial2/0/0]
[AR2-Serial2/0/0] nat outbound 2000
[AR2-Serial2/0/0]
//AR3
[AR3]acl number 2000
[AR3-acl-basic-2000] rule permit source 192.168.3.0 0.0.0.255
[AR3-acl-basic-2000] rule permit source 192.168.5.0 0.0.0.255
[AR3-acl-basic-2000]
[AR3-acl-basic-2000]interface Serial3/0/0
[AR3-Serial3/0/0] nat outbound 2000
[AR3-Serial3/0/0]
//AR4
[AR4]acl number 2000
[AR4-acl-basic-2000] rule permit source 192.168.4.0 0.0.0.255
[AR4-acl-basic-2000] rule permit source 192.168.6.0 0.0.0.255
[AR4-acl-basic-2000]
[AR4-acl-basic-2000]interface GigabitEthernet0/0/1
[AR4-GigabitEthernet0/0/1] nat outbound 2000
[AR4-GigabitEthernet0/0/1]给pc配置静态IP地址

pc2 192.168.2.2 24
pc3 192.168.3.2 24
pc4192.168.4.2 24
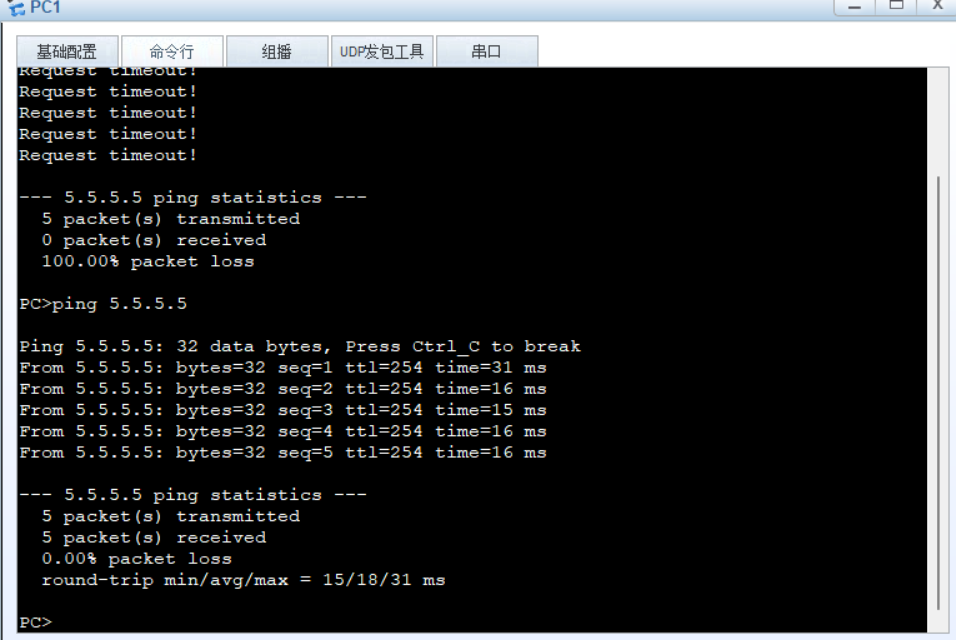
验证
pc2可以ping通pc1
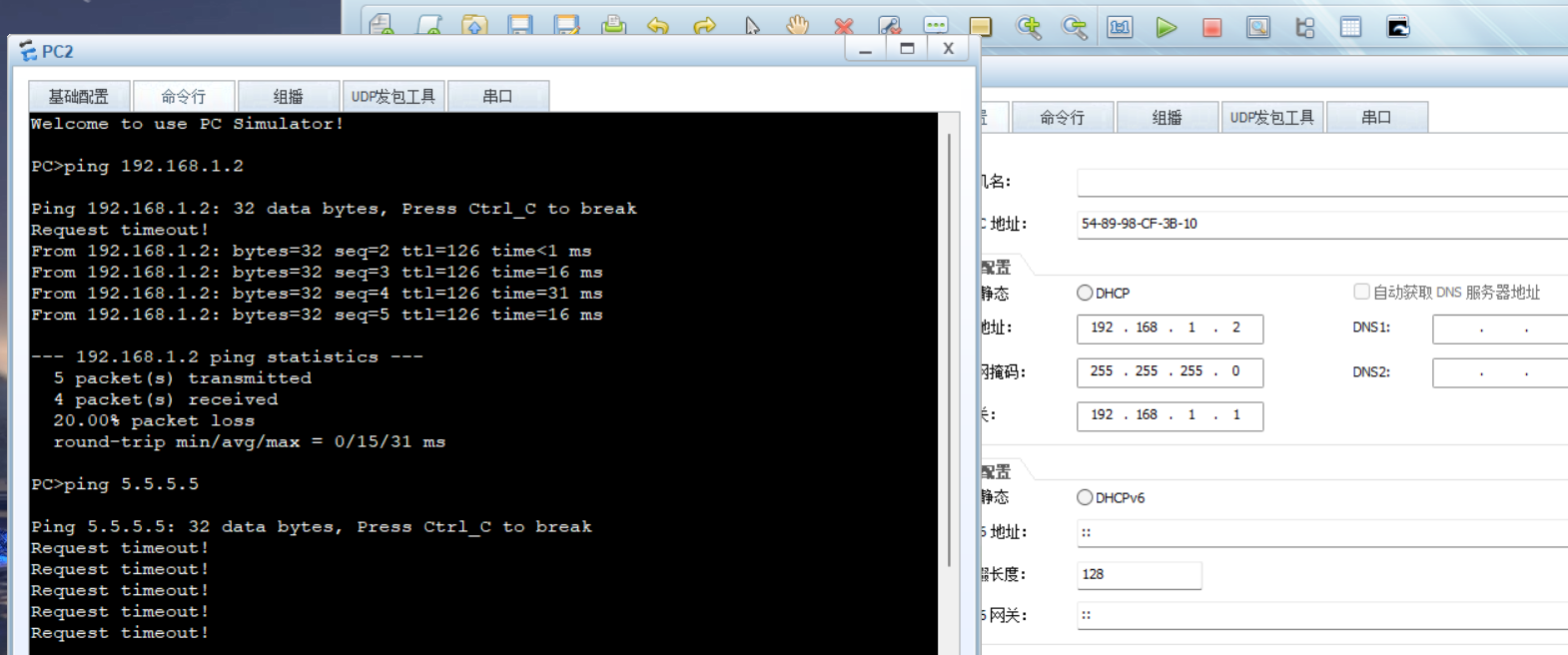
pc1 可以ping通环回5.5.5.5