提示:本文原创作品,良心制作,干货为主,简洁清晰,一看就会
文章目录
- 前言
- 一、RBAC基础知识
-
- [1.1 什么是RBAC](#1.1 什么是RBAC)
- [1.2 RBAC核心工作流程](#1.2 RBAC核心工作流程)
- 二、RBAC实例
-
- [2.1 Role-RoleBinding](#2.1 Role-RoleBinding)
- [2.2 ClusterRole-ClusterRoleBinding](#2.2 ClusterRole-ClusterRoleBinding)
- [2.3 Dashboard账号配置](#2.3 Dashboard账号配置)
前言
随着Kubernetes集群规模与业务接入量不断扩大,多用户、多服务账号共存已成常态,集群资源权限管控愈发关键。RBAC作为K8s核心授权机制,可实现基于角色的细粒度资源访问控制,规避权限泛滥与误操作风险。本文将详解K8s RBAC核心概念、资源绑定规则及实战配置,助力搭建规范安全的集群权限体系
一、RBAC基础知识
1.1 什么是RBAC
RBAC 全称 基于角色的访问控制(Role-Based Access Control),是 Kubernetes 内置的权限授权机制
核心逻辑:不给用户直接赋权限,先把权限打包给角色,再把角色绑定给用户/服务账号
实现谁、能对哪些资源、做什么操作的精细化管控,精准限制集群资源访问权限,避免权限过大、误操作、越权访问,保障多团队、多服务共用K8s集群的安全性
1.2 RBAC核心工作流程
RBAC核心工作流程如下:先定义好"能对什么资源做什么操作"的规则,把规则打包成角色,再通过角色绑定,把角色分配给用户/服务账号,就完成了精细化的权限控制
K8s RBAC的本质,就是通过角色绑定 ,把"权限定义"和"使用者"连接起来,完成授权
完整链路是:
资源 + 操作 → 规则 → 角色 → 角色绑定 → 主体(用户/服务账号)
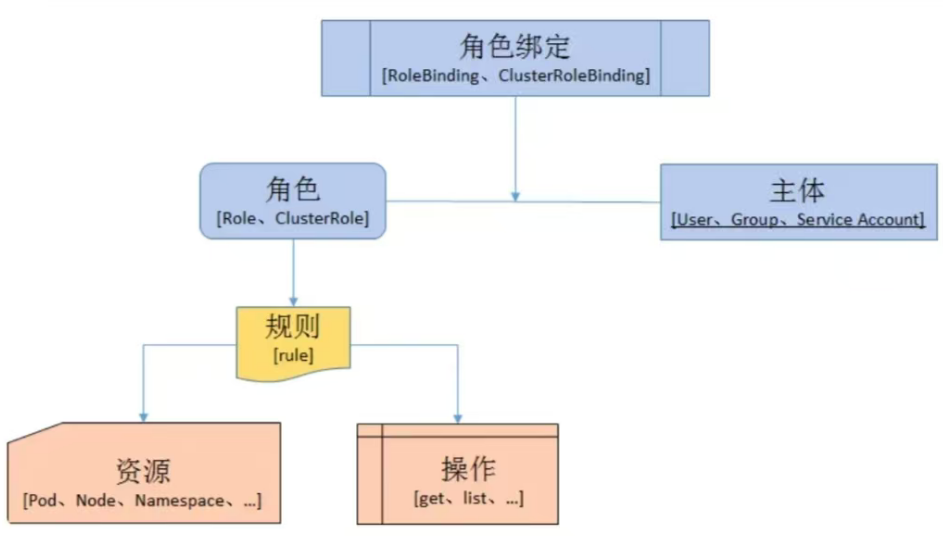
权限的基础单元:规则(Rule),它是权限的最小组成单位 ,回答两个问题:
对什么资源?(比如 Pod、Deployment、Namespace、Node 等)
做什么操作?(比如 get、list、create、update、delete 等)
权限的打包载体:角色(Role / ClusterRole),把多条「规则」打包在一起,就成了角色,用来给"一类权限"做统一管理,分为两种:
Role:命名空间级 角色,权限只在指定 Namespace 内生效
ClusterRole:集群级角色,权限对整个集群(包括所有 Namespace、集群资源如 Node)生效
权限的使用者:主体(Subject), 就是"谁要被授权",分为三类:
User:普通用户(人)
Group:用户组(批量管理用户)
ServiceAccount:服务账号(给集群内的应用/服务用)
权限的连接桥梁:角色绑定(RoleBinding / ClusterRoleBinding),它的作用只有一个:把「角色」绑定到「主体」,让主体获得角色定义的所有权限,对应角色也分两种:
RoleBinding:绑定Role,权限仅在指定 Namespace 内生效
ClusterRoleBinding:绑定ClusterRole,权限在整个集群生效;也可以用RoleBinding绑定ClusterRole,让集群级角色的权限"缩小"到某个 Namespace 内使用
二、RBAC实例
2.1 Role-RoleBinding
例:创建一个账号给开发人员 只能看自己命名空间 下的 Pod、Deployment、日志
yaml
## 1. 创建命名空间
root@k8s-master1:~# kubectl create ns dev-ns
## 在这个命名空间下创建Pod方便待会测试使用
root@k8s-master1:~# kubectl get pod -n dev-ns -o wide
NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES
deploy-nginx-pod-57445b8986-ldx97 1/1 Running 0 3m49s 10.244.169.159 k8s-node2 <none> <none>
deploy-nginx-pod-57445b8986-x467w 1/1 Running 0 3m49s 10.244.36.83 k8s-node1 <none> <none>
## 2. 创建开发专用 SA
root@k8s-master1:~# kubectl create sa dev-user-sa -n dev-ns
## 3. 创建Role,RoleBinding
root@k8s-master1:~# vim dev-user-role-rolebinding.yaml
---
## 创建Role,定义权限:只有查询操作
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: dev-user-role
namespace: dev-ns
rules:
# 允许查看 Pod、日志
- apiGroups: [""]
resources: ["pods","pods/log"]
verbs: ["get","list","watch"]
# 允许查看 Deployment
- apiGroups: ["apps"]
resources: ["deployments"]
verbs: ["get","list","watch"]
---
## RoleBinding 把角色绑定给账号
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: dev-user-rolebinding
namespace: dev-ns
subjects:
- kind: ServiceAccount
name: dev-user-sa
namespace: dev-ns
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: dev-user-role
root@k8s-master1:~# kubectl apply -f dev-user-role-rolebinding.yaml
yaml
## 4. 切换成开发账号
## 生成dev-user-sa 临时token
root@k8s-master1:~# kubectl create token dev-user-sa -n dev-ns --duration=1h
eyJhbGciOiJSUzI1NiIsImtpZCI6I...
## 给kubectl临时配置这个账号身份
root@k8s-master1:~# kubectl config set-credentials dev-test --token="eyJhbGciOiJSUzI1NiIsImtpZCI6I..."
## 新建上下文
root@k8s-master1:~# kubectl config set-context dev-test-ctx --cluster=kubernetes --user=dev-test --namespace=dev-ns
## 看完整 kubeconfig 配置
root@k8s-master1:~# kubectl config view
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: DATA+OMITTED
server: https://192.168.13.100:16443
name: kubernetes
contexts:
- context:
cluster: kubernetes
namespace: dev-ns
user: dev-test
name: dev-test-ctx
- context:
cluster: kubernetes
user: kubernetes-admin
name: kubernetes-admin@kubernetes
current-context: kubernetes-admin@kubernetes
kind: Config
preferences: {}
users:
- name: dev-test
user:
token: REDACTED
- name: kubernetes-admin
user:
client-certificate-data: DATA+OMITTED
client-key-data: DATA+OMITTED
## 5. 切换上下文,测试
root@k8s-master1:~# kubectl config use-context dev-test-ctx
root@k8s-master1:~# kubectl get pod
NAME READY STATUS RESTARTS AGE
deploy-nginx-pod-57445b8986-ldx97 1/1 Running 0 29m
deploy-nginx-pod-57445b8986-x467w 1/1 Running 0 29m
root@k8s-master1:~# kubectl apply -f nginx2.yaml # 不能创建pod
Error from server (Forbidden): error when creating "nginx2.yaml": deployments.apps is forbidden: User "system:serviceaccount:dev-ns:dev-user-sa" cannot create resource "deployments" in API group "apps" in the namespace "dev-ns"
root@k8s-master1:~# kubectl delete pod deploy-nginx-pod-57445b8986-x467w # 不能删除pod
Error from server (Forbidden): pods "deploy-nginx-pod-57445b8986-x467w" is forbidden: User "system:serviceaccount:dev-ns:dev-user-sa" cannot delete resource "pods" in API group "" in the namespace "dev-ns"
root@k8s-master1:~# kubectl get pod -n default # 不能查看其他命名空间下的资源对象
Error from server (Forbidden): pods is forbidden: User "system:serviceaccount:dev-ns:dev-user-sa" cannot list resource "pods" in API group "" in the namespace "default"
root@k8s-master1:~# kubectl config use-context kubernetes-admin@kubernetes # 切换回来
root@k8s-master1:~# kubectl get pod -n dev-ns
NAME READY STATUS RESTARTS AGE
deploy-nginx-pod-57445b8986-ldx97 1/1 Running 0 32m
deploy-nginx-pod-57445b8986-x467w 1/1 Running 0 32m
root@k8s-master1:~# kubectl delete pod deploy-nginx-pod-57445b8986-x467w -n dev-ns # kubernetes-admin可以删除
pod "deploy-nginx-pod-57445b8986-x467w" deleted2.2 ClusterRole-ClusterRoleBinding
例:创建一个账号,授予全集群节点、存储、命名空间、PV 全局查看权限
yaml
## 1. 创建ClusterRole,ClusterRoleBinding
root@k8s-master1:~# vim clusterrole.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: clusterrole-test
rules:
# 同一组(核心组)资源合并在一起
- apiGroups: [""]
resources: ["nodes","namespaces","persistentvolumes","persistentvolumeclaims","pods","services","configmaps"]
verbs: ["get", "list", "watch"]
# apps 组资源
- apiGroups: ["apps"]
resources: ["deployments","statefulsets"]
verbs: ["get", "list", "watch"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: clusterrolebinding-test
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: clusterrole-test
subjects:
# 就绑刚才创建好的 dev-user-sa,真实存在,马上能测
- kind: ServiceAccount
name: dev-user-sa
namespace: dev-ns
root@k8s-master1:~# kubectl apply -f clusterrole.yaml
yaml
## 2. 切换上下文测试权限
root@k8s-master1:~# kubectl config use-context dev-test-ctx
root@k8s-master1:~# kubectl get pod
NAME READY STATUS RESTARTS AGE
deploy-nginx-pod-57445b8986-hwllj 1/1 Running 0 40m
deploy-nginx-pod-57445b8986-k2v65 1/1 Running 0 40m
root@k8s-master1:~# kubectl get ns
NAME STATUS AGE
calico-apiserver Active 34d
calico-system Active 34d
default Active 34d
dev-ns Active 176m
kube-node-lease Active 34d
kube-public Active 34d
kube-system Active 34d
kubernetes-dashboard Active 33d
tigera-operator Active 34d
root@k8s-master1:~# kubectl get pod -n default # 可以查看其他命名空间下的资源对象
NAME READY STATUS RESTARTS AGE
deploy-nginx2-pod-57445b8986-8vzgj 1/1 Running 0 41m
deploy-nginx2-pod-57445b8986-d48jm 1/1 Running 0 41m
root@k8s-master1:~# kubectl delete pod deploy-nginx-pod-57445b8986-hwllj # 依旧做删除操作
Error from server (Forbidden): pods "deploy-nginx-pod-57445b8986-hwllj" is forbidden: User "system:serviceaccount:dev-ns:dev-user-sa" cannot delete resource "pods" in API group "" in the namespace "dev-ns"
root@k8s-master1:~# kubectl config use-context kubernetes-admin@kubernetes
Switched to context "kubernetes-admin@kubernetes".
root@k8s-master1:~# 2.3 Dashboard账号配置
RBAC权限划分另有Dashboard页面账号配置 实战案例,可参考下文第七小节自行配置Dashboard访问账号,此处不再展开赘述
https://blog.csdn.net/m0_63756214/article/details/159942750?spm=1001.2014.3001.5501
注:
文中若有疏漏,欢迎大家指正赐教。
本文为100%原创,转载请务必标注原创作者,尊重劳动成果。
求赞、求关注、求评论!你的支持是我更新的最大动力,评论区等你~