一,描述
Jenkins使用kubernetes插件主要用于完成两方面的工作:
一是用于在kubernetes集群内动态生成一个pod作为Jenkins 的slave节点,提供流水线执行的工作环境;
二是用于将应用代码持续部署到kubernetes集群中。
基于上面提到的这两方面的用途,下面介绍Jenkins与kubernetes的集成配置与使用方法。
1.1 插件的安装
在Jenkins里集成kubernetes也是依赖于插件的,所以在介绍如何配置与使用jenkins集成kubernetes之前需要先安装插件:
• Kubernetes plugin
• Kubernetes CLI
• Kubernetes Continous Deploy
如上列出的插件,第一个用于在kubernetes集群中动态生成jenkins slave节点,后两个插件用于通过不同的方式持续部署代码到kubernetes集群。无论哪种插件,使用前都要先保证jenkins能够连接到kubernetes集群,如下就不同环境(跨集群和同集群)下的jenkins连接kubernetes集群的配置开如。
二,配置Jenkins连接Kubernetes
Jenkins与kubernetes的集成,主要是通过调用Kubernetes的API去kubernetes集群中进行工作的。大多数的环境在安装kubernetes集群配置apiserver服务时使用了证书,所以在配置jenkins连接kubernetes集群时,需要根据kubernetes的配置文件生成一系列证书以及key,并将证书上传到Jenkins用来对apiserver进行认证。
部署在非kubernetes集群内的Jenkins连接kubernetes的方式配置
2.1 配置证书
下面针对部署在kubernetes集群环境下的Jenkins和非kubernetes集群环境下的jenkins连接kubernetes集群的配置进行详细介绍。
部署在非kubernetes集群内Jenkins连接kubernetes配置
安装好插件以后。
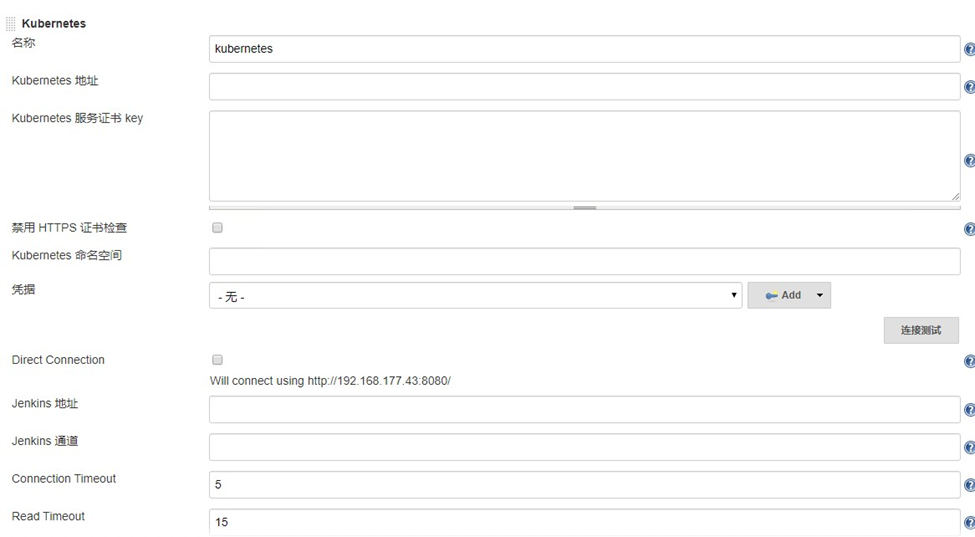
进入Jenkins首页,点击菜单"Manage Jenkins(系统管理)---> Configure System(系统设置)" 在跳转到的界面中,到最底部,点击" Add a new cloud(新建一个云)--> kubernetes"。
如下所示:
解释:
名称:这里用于填写要添加的这个云(cloud)的名称,默认为"kubernetes",如果不想用这个可以自定义。在编写pipeline的时候会用到。
kubernetes 地址:用于填写kubernetes集群的地址,做了多master集群高可用的环境直接写vip地址加端口;只有单个master的环境直接写master加端口地址即可。
Kubernetes 服务证书 key:用于填写与kubernetes集群认证的证书内容。
Kubernetes 命名空间:用于填写调用kubernetes时生成的pod工作的namespace。
Credentials(凭据):用于连接kubernetes的凭证。
Jenkins 地址:Jenkins的连接地址。
了解了基本配置的参数说明,下面主要说一下"Kubernetes 服务证书 key"和Credentials(凭据)配置。
kubernetes集群安装的时候生成了一系列证书以及key,并且在配置kubernetes中kubectl客户端命令权限的时候,根据这些证书以及key生成了一个kubeconfig文件,用于kubectl与集群通信,这个文件默认为/root/.kube/config文件,对集群有最高操作权限(如果给了cluster-admin权限)。
Jenkins需要根据这个文件生成的证书与集群通信,所以我们在生产环境配置Jenkins连接kubernetes集群的时候,需要注意一下kubeconfig文件绑定的用户的权限,最好从新生成一个低权限的kubeconfig文件,而不要用kubectl命令使用的文件。
为了测试方便,就先使用kubectl命令使用的kubeconfig文件
配置证书key
首先看一下config文件。
root@k8s-master01:~# cat /root/.kube/config
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURCVENDQWUyZ0F3SUJBZ0lJY3dUQ2tUUCtvZFl3RFFZSktvWklodmNOQVFFTEJRQXdGVEVUTUJFR0ExVUUKQXhNS2EzVmlaWEp1WlhSbGN6QWVGdzB5TkRBNE1ESXdPRFF3TkRWYUZ3MHpOREEzTXpFd09EUTFORFZhTUJVeApFekFSQmdOVkJBTVRDbXQxWW1WeWJtVjBaWE13Z2dFaU1BMEdDU3FHU0liM0RRRUJBUVVBQTRJQkR3QXdnZ0VLCkFvSUJBUURrRWxHUm9oTW1JeGtGa0pwbFd5RkRuYVp0YU9WMWMxYzhOUzUwMnlnU28zMkE1WGRXNHRFMFB0WlAKNTh2SlNYK3JKQnZvZERMTGlWcUQ5dVlmSXl4T051NHJGK2o0QzByRWlHWDFETWEwamRJSXcxYmU5YW1abkltVAp0YnZUV2tYMlpOYVVwc1VRT2NRVVd3WGRCT0hXQmw3WWVZK3F2R292dlNnV1Q2enJqSHBXNWM3eGptQUlMNXZmCkw2dHplYmJ1SnhPR1AxbTR5TzRRUnJua1E0M0V0OUV5NS9JOTB1SFFzZGpERE5TUGNMNnZ0Y1VvZ3lIb2xwTUQKUkNNd3J1c2xldFhHeVJxajkvWkhuNDJ2SU9xWFpkZG9mQmViMjdRWEhXb0VaMkRmeU0rWERFWnIxblkxdHFFbworQkVYekFiSmFBVmNNTCtSd2xEeTYyMnpxVnJkQWdNQkFBR2pXVEJYTUE0R0ExVWREd0VCL3dRRUF3SUNwREFQCkJnTlZIUk1CQWY4RUJUQURBUUgvTUIwR0ExVWREZ1FXQkJRUDVNdzFJbHJLL2xsUnRBYmNJcElxY2ZvV0FEQVYKQmdOVkhSRUVEakFNZ2dwcmRXSmxjbTVsZEdWek1BMEdDU3FHU0liM0RRRUJDd1VBQTRJQkFRQytDVWRUeVp5KwpkRVpRd0x1WTB6dVJzc2VWVXJ1RVozak1OQjFTZkswcXF1RW9jeWxwaGhGNnF6Mjk1STJuYmljY09yQW55MkNDCll4Z1lZUTU2TFRadFdTNG1DWTNobnc3aGozNFdHVzFzSzgvWjAvT09zakZ3KzVwYUJ6T0owNHgxdkRCWTU5OE4KR3Z5dSttRk4vNjA2Q281TkNxNW1EWEx1a3lnTGFGajR3Szl1cGJkNk5kMkJxUUFJSS83WFpmSlh6aUZKaUFBSgpkWjBYbXkreGQvcFRCTkVmM2NiZENOdHB5OTN4RVVHcXg4ampjM1pNQ0JuVkhraVhVY0lFSXJna2VqdmswbCtzCmtzK0dpZUdpUlBMOWtTZ09HSW8wQkhYUFZFQkdHK1pwNEFsemdmM2JNTG5qcU4weWlKVy94QUZsamdzWDZ6TnEKUXNtT29CVS9OSlZFCi0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K
server: https://192.168.2.63:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
user: kubernetes-admin
name: kubernetes-admin@kubernetes
current-context: kubernetes-admin@kubernetes
kind: Config
preferences: {}
users:
- name: kubernetes-admin
user:
client-certificate-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURLVENDQWhHZ0F3SUJBZ0lJV21XS2xxR0FOMG93RFFZSktvWklodmNOQVFFTEJRQXdGVEVUTUJFR0ExVUUKQXhNS2EzVmlaWEp1WlhSbGN6QWVGdzB5TkRBNE1ESXdPRFF3TkRWYUZ3MHlOVEE0TURJd09EUTFORGRhTUR3eApIekFkQmdOVkJBb1RGbXQxWW1WaFpHMDZZMngxYzNSbGNpMWhaRzFwYm5NeEdUQVhCZ05WQkFNVEVHdDFZbVZ5CmJtVjBaWE10WVdSdGFXNHdnZ0VpTUEwR0NTcUdTSWIzRFFFQkFRVUFBNElCRHdBd2dnRUtBb0lCQVFEUEIxWU8KVWpZTk45Q3FHSTc2U1RKc0k1bG9VeTdiam82NE1nU1FxeE9nM2ZLR3EydDg3bHFqZC9RRW1xSWlmWmZlYUt1cAoxUTFlTkI5OXFlNnF0WFhHY3k4alpHTy9aRkthZWJONGNmcDdOYXB1OW9lWG1aaTFjK1BMbWIyQjJvUUJrRDdCCjhMYUVmcFRWVkpGQkJZSEQ3blBFUDA1cVkybTI2aER2YVREeTN2VktQUTl3ODA5MUQ5Ym9MQmhTQkFDNHFBNFYKZnNWNS9XRjRkYzZIa3RlUkxEOVVLMXhJUFBBdEp5K0wrL2Z5clJLVjVmcDhjZmRWWHdXbTZTTFVBM1hxVzRIRworZDd5OTR4UERKYzlyazRzU0R6NFBZaEo0bHc3SFUzcXF6ekhhK0VvME51R2MyZUFtbDNNOHdNcnh0aFZyMlcrCk5GcVI2UUZhYTAxSHBpUXRBZ01CQUFHalZqQlVNQTRHQTFVZER3RUIvd1FFQXdJRm9EQVRCZ05WSFNVRUREQUsKQmdnckJnRUZCUWNEQWpBTUJnTlZIUk1CQWY4RUFqQUFNQjhHQTFVZEl3UVlNQmFBRkEva3pEVWlXc3IrV1ZHMApCdHdpa2lweCtoWUFNQTBHQ1NxR1NJYjNEUUVCQ3dVQUE0SUJBUUFocnNoT0t2bjNmSDlkTWJrdzF4QW1KcGo4CmxERjNWTVdWQ3lFdVRrVzlvYklUcjdhOHdab3Y5LzhYcnJqdTkvblBqb0hyRHBXK2dVQ0lFU29ORGZvWEluS3kKaWU4SlplbGNETzRtUk5HTUtZVkhIdzNqSEtjSHQ2OWVoTHVOWHNTOHJSRUxCZEM4ZXZ2c2hmNVR1QUQxZlNoUQpWbFpRUWdIdFlzeXRqNmhGQnpwZ1pjeGxTMTgyYWxrVkxtNFVybE9lY0N4Vldrb3V3eVdGSm1qVzVmS2VUSCtqCkp6c3RtYk5VdzlVUXpPSGhIK3ZKaTNlck1pR3pyOTl0VE92YnZ4bXY1bkw2ZXFqZzlDNXovQ2FZcU9iYXJCL0IKb2N6eFVyMzlPRUtJSVJmVk9tbFN2bmhQVXhFTmwzRERrY1R2dDdJcGdLYmtDd1FBRlh4cTQvZ0FuRERYCi0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K
client-key-data: LS0tLS1CRUdJTiBSU0EgUFJJVkFURSBLRVktLS0tLQpNSUlFcEFJQkFBS0NBUUVBendkV0RsSTJEVGZRcWhpTytra3liQ09aYUZNdTI0Nk91RElFa0tzVG9OM3locXRyCmZPNWFvM2YwQkpxaUluMlgzbWlycWRVTlhqUWZmYW51cXJWMXhuTXZJMlJqdjJSU21ubXplSEg2ZXpXcWJ2YUgKbDVtWXRYUGp5NW05Z2RxRUFaQSt3ZkMyaEg2VTFWU1JRUVdCdys1enhEOU9hbU5wdHVvUTcya3c4dDcxU2owUApjUE5QZFEvVzZDd1lVZ1FBdUtnT0ZYN0ZlZjFoZUhYT2g1TFhrU3cvVkN0Y1NEendMU2N2aS92MzhxMFNsZVg2CmZISDNWVjhGcHVraTFBTjE2bHVCeHZuZTh2ZU1Ud3lYUGE1T0xFZzgrRDJJU2VKY094MU42cXM4eDJ2aEtORGIKaG5ObmdKcGR6UE1ESzhiWVZhOWx2alJha2VrQldtdE5SNllrTFFJREFRQUJBb0lCQVFDM09RWG5YTWpyZjlkVApncktmUGNLN1EvSlVDekp3SzhXUnJPcXZZa2pYMlRYNEM2UHdpRDU5Wi83MVNDbHdIdmtXWkVwdzN0YWE1Y1J0CkFjVHhIZkdpOVhQbGZjWnRyNHNQbmQvQkhCYVRqcFpNNkRCdWNnaGRwcmdYQy9SVkJTQkpCZkVVMFVXbkV5UUQKZlhta013eDZiQUhXMERSRkljQ0FtcnpzTll1VmxUZXBnblVKcHB5QVNDSUpPYnFWbS8xOFJnZVU1TlpUVDgzeAo0Sk42dEpMSWhKeTFVOVV5SW4rbGVnQUoxWnAxajFRVjJ6dVp0WC9VOXNBaUFMTGRoeUcrMVZuWFl1UGVzRGlFCjdJMUdTRTRQcTJ3ajlWb3FGN1Z2RHdxVlZiYm0wNy9rd3VXeCtpc2VBc2JnU3ZQR1ZaUkFCQzJJeElrZ3VDLzQKSERTdTRRUmRBb0dCQU9Ga1ZwMU5GWmNzeUlpS0tDSkdVTVYxOFp0cmVGaTErMThLVlRBZlMreEc2N2JDZGdBawpiTzV1UVQwZHFHR2dsVWswWWdWVnk5b3pYYnRyRGwzbzVjSGFXU05jTmhjYU5oc0U5aVFVL0VxQTh6S0lUY0NHCnluOUxpS1JIVDdQU3dKREpsM3cyWDVjRGJDcWZvNC9DSHRmR29SSFFpK3lwQy9yRGQyc0RZRjRqQW9HQkFPc2sKbXZibmU4dmttS3JNTjl2Q3NkaGNmSXlsNXAwK3liNEhIaWVEaUJBN2dpNmVMZURwMlRrL2tHWG5RbkJJVkttRgptdUtHZk9hSm13dTVNakFZZ0paS3k0MUlkbWxXYjVKVFQrSjVRSUZZZG1lblBRUHlFSVp0azdYN1M0NW9vTDZNCm9RSkFDTDF2SmxTc0lXUzFtTnhOU2ltRVpqZzVkZndHdlBUQVB4RnZBb0dBYjVLMTlhUkUvZExqYWdQS0hqMWsKbW5ycUlSK3dNV25VaDVXYjJmaUVJdkJ3bXNYa2wrbHdLdzlWS0NYWVJvdXhtczFkZ0hxYU1PZWdqTGhRSWxpNQo4NTVjNWM0dDBIM2ZMcnprQTdTSHQzSGg4YS9ibldTY05TdDA5cTErWE93RSt5ZHYzOE1peXFTZEZQUjFpU0oxCkZpZHpjRmdtQy84YXVRV3R4Y0drSUxVQ2dZQUU5V0tuTGo1NEVEdi83Z3FIZ2RXS1FIa0g1aiswdFN3LzY1cUIKTHM3aHVMK0lDQ0hqaWtyZ1lDekZXVmtYVVE4bisvOUdJNXZpcUtneVdSZHIyRGh0OHVuVDh1RThXMnhDNDZyZApsYno4ZlVjUjdIN201R1hnejlLN2xhOEVNOFNnQUFzdEp2aUlOaDNTejBacy96OVg5ZkZJYXRoVSt6RTN2VlNpCnZLTVgxUUtCZ1FDVVlaS2F6ZVJwalNXSlV1eU5nMjVMU3BSM2FLMUwxWlRhVy9sSHBWc1BYYVMyU2tHc05YT0kKU1dCdFRaVjVSbnY3cUc4V3dkOGJxeUt5UTV0M0svVlV4ZlRJcUxjQXkrNnZyQnZNSXBWRGpSQTF5NURqSkxiaApNUW5BckQ1ZkcvYTFtdGVyd08zUkVlZmRPNW53b1I3YWRaU3dHRzIvS3pWT2E0cXFWenNnZ1E9PQotLS0tLUVORCBSU0EgUFJJVkFURSBLRVktLS0tLQo=获取文件中certificate-authority-data的内容并转化成base64 encoded文件
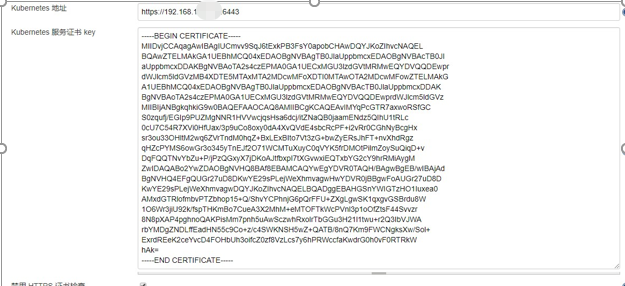
echo LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURLVENDQWhHZ0F3SUJBZ0lJV21XS2xxR0FOMG93RFFZSktvWklodmNOQVFFTEJRQXdGVEVUTUJFR0ExVUUKQXhNS2EzVmlaWEp1WlhSbGN6QWVGdzB5TkRBNE1ESXdPRFF3TkRWYUZ3MHlOVEE0TURJd09EUTFORGRhTUR3eApIekFkQmdOVkJBb1RGbXQxWW1WaFpHMDZZMngxYzNSbGNpMWhaRzFwYm5NeEdUQVhCZ05WQkFNVEVHdDFZbVZ5CmJtVjBaWE10WVdSdGFXNHdnZ0VpTUEwR0NTcUdTSWIzRFFFQkFRVUFBNElCRHdBd2dnRUtBb0lCQVFEUEIxWU8KVWpZTk45Q3FHSTc2U1RKc0k1bG9VeTdiam82NE1nU1FxeE9nM2ZLR3EydDg3bHFqZC9RRW1xSWlmWmZlYUt1cAoxUTFlTkI5OXFlNnF0WFhHY3k4alpHTy9aRkthZWJONGNmcDdOYXB1OW9lWG1aaTFjK1BMbWIyQjJvUUJrRDdCCjhMYUVmcFRWVkpGQkJZSEQ3blBFUDA1cVkybTI2aER2YVREeTN2VktQUTl3ODA5MUQ5Ym9MQmhTQkFDNHFBNFYKZnNWNS9XRjRkYzZIa3RlUkxEOVVLMXhJUFBBdEp5K0wrL2Z5clJLVjVmcDhjZmRWWHdXbTZTTFVBM1hxVzRIRworZDd5OTR4UERKYzlyazRzU0R6NFBZaEo0bHc3SFUzcXF6ekhhK0VvME51R2MyZUFtbDNNOHdNcnh0aFZyMlcrCk5GcVI2UUZhYTAxSHBpUXRBZ01CQUFHalZqQlVNQTRHQTFVZER3RUIvd1FFQXdJRm9EQVRCZ05WSFNVRUREQUsKQmdnckJnRUZCUWNEQWpBTUJnTlZIUk1CQWY4RUFqQUFNQjhHQTFVZEl3UVlNQmFBRkEva3pEVWlXc3IrV1ZHMApCdHdpa2lweCtoWUFNQTBHQ1NxR1NJYjNEUUVCQ3dVQUE0SUJBUUFocnNoT0t2bjNmSDlkTWJrdzF4QW1KcGo4CmxERjNWTVdWQ3lFdVRrVzlvYklUcjdhOHdab3Y5LzhYcnJqdTkvblBqb0hyRHBXK2dVQ0lFU29ORGZvWEluS3kKaWU4SlplbGNETzRtUk5HTUtZVkhIdzNqSEtjSHQ2OWVoTHVOWHNTOHJSRUxCZEM4ZXZ2c2hmNVR1QUQxZlNoUQpWbFpRUWdIdFlzeXRqNmhGQnpwZ1pjeGxTMTgyYWxrVkxtNFVybE9lY0N4Vldrb3V3eVdGSm1qVzVmS2VUSCtqCkp6c3RtYk5VdzlVUXpPSGhIK3ZKaTNlck1pR3pyOTl0VE92YnZ4bXY1bkw2ZXFqZzlDNXovQ2FZcU9iYXJCL0IKb2N6eFVyMzlPRUtJSVJmVk9tbFN2bmhQVXhFTmwzRERrY1R2dDdJcGdLYmtDd1FBRlh4cTQvZ0FuRERYCi0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K |base64 -d > ca.crt将ca.crt的内容粘贴到kubernetes server certificate key(Kubernetes 服务证书 key)框里,如下图所示:
2.2 配置凭据
获取/root/.kube/config文件中client-certificate-data和client-key-data的内容并转化成base64 encoded文件
echo LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURLVENDQWhHZ0F3SUJBZ0lJV21XS2xxR0FOMG93RFFZSktvWklodmNOQVFFTEJRQXdGVEVUTUJFR0ExVUUKQXhNS2EzVmlaWEp1WlhSbGN6QWVGdzB5TkRBNE1ESXdPRFF3TkRWYUZ3MHlOVEE0TURJd09EUTFORGRhTUR3eApIekFkQmdOVkJBb1RGbXQxWW1WaFpHMDZZMngxYzNSbGNpMWhaRzFwYm5NeEdUQVhCZ05WQkFNVEVHdDFZbVZ5CmJtVjBaWE10WVdSdGFXNHdnZ0VpTUEwR0NTcUdTSWIzRFFFQkFRVUFBNElCRHdBd2dnRUtBb0lCQVFEUEIxWU8KVWpZTk45Q3FHSTc2U1RKc0k1bG9VeTdiam82NE1nU1FxeE9nM2ZLR3EydDg3bHFqZC9RRW1xSWlmWmZlYUt1cAoxUTFlTkI5OXFlNnF0WFhHY3k4alpHTy9aRkthZWJONGNmcDdOYXB1OW9lWG1aaTFjK1BMbWIyQjJvUUJrRDdCCjhMYUVmcFRWVkpGQkJZSEQ3blBFUDA1cVkybTI2aER2YVREeTN2VktQUTl3ODA5MUQ5Ym9MQmhTQkFDNHFBNFYKZnNWNS9XRjRkYzZIa3RlUkxEOVVLMXhJUFBBdEp5K0wrL2Z5clJLVjVmcDhjZmRWWHdXbTZTTFVBM1hxVzRIRworZDd5OTR4UERKYzlyazRzU0R6NFBZaEo0bHc3SFUzcXF6ekhhK0VvME51R2MyZUFtbDNNOHdNcnh0aFZyMlcrCk5GcVI2UUZhYTAxSHBpUXRBZ01CQUFHalZqQlVNQTRHQTFVZER3RUIvd1FFQXdJRm9EQVRCZ05WSFNVRUREQUsKQmdnckJnRUZCUWNEQWpBTUJnTlZIUk1CQWY4RUFqQUFNQjhHQTFVZEl3UVlNQmFBRkEva3pEVWlXc3IrV1ZHMApCdHdpa2lweCtoWUFNQTBHQ1NxR1NJYjNEUUVCQ3dVQUE0SUJBUUFocnNoT0t2bjNmSDlkTWJrdzF4QW1KcGo4CmxERjNWTVdWQ3lFdVRrVzlvYklUcjdhOHdab3Y5LzhYcnJqdTkvblBqb0hyRHBXK2dVQ0lFU29ORGZvWEluS3kKaWU4SlplbGNETzRtUk5HTUtZVkhIdzNqSEtjSHQ2OWVoTHVOWHNTOHJSRUxCZEM4ZXZ2c2hmNVR1QUQxZlNoUQpWbFpRUWdIdFlzeXRqNmhGQnpwZ1pjeGxTMTgyYWxrVkxtNFVybE9lY0N4Vldrb3V3eVdGSm1qVzVmS2VUSCtqCkp6c3RtYk5VdzlVUXpPSGhIK3ZKaTNlck1pR3pyOTl0VE92YnZ4bXY1bkw2ZXFqZzlDNXovQ2FZcU9iYXJCL0IKb2N6eFVyMzlPRUtJSVJmVk9tbFN2bmhQVXhFTmwzRERrY1R2dDdJcGdLYmtDd1FBRlh4cTQvZ0FuRERYCi0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K |base64 -d >client.crt生成key
echo LS0tLS1CRUdJTiBSU0EgUFJJVkFURSBLRVktLS0tLQpNSUlFcEFJQkFBS0NBUUVBendkV0RsSTJEVGZRcWhpTytra3liQ09aYUZNdTI0Nk91RElFa0tzVG9OM3locXRyCmZPNWFvM2YwQkpxaUluMlgzbWlycWRVTlhqUWZmYW51cXJWMXhuTXZJMlJqdjJSU21ubXplSEg2ZXpXcWJ2YUgKbDVtWXRYUGp5NW05Z2RxRUFaQSt3ZkMyaEg2VTFWU1JRUVdCdys1enhEOU9hbU5wdHVvUTcya3c4dDcxU2owUApjUE5QZFEvVzZDd1lVZ1FBdUtnT0ZYN0ZlZjFoZUhYT2g1TFhrU3cvVkN0Y1NEendMU2N2aS92MzhxMFNsZVg2CmZISDNWVjhGcHVraTFBTjE2bHVCeHZuZTh2ZU1Ud3lYUGE1T0xFZzgrRDJJU2VKY094MU42cXM4eDJ2aEtORGIKaG5ObmdKcGR6UE1ESzhiWVZhOWx2alJha2VrQldtdE5SNllrTFFJREFRQUJBb0lCQVFDM09RWG5YTWpyZjlkVApncktmUGNLN1EvSlVDekp3SzhXUnJPcXZZa2pYMlRYNEM2UHdpRDU5Wi83MVNDbHdIdmtXWkVwdzN0YWE1Y1J0CkFjVHhIZkdpOVhQbGZjWnRyNHNQbmQvQkhCYVRqcFpNNkRCdWNnaGRwcmdYQy9SVkJTQkpCZkVVMFVXbkV5UUQKZlhta013eDZiQUhXMERSRkljQ0FtcnpzTll1VmxUZXBnblVKcHB5QVNDSUpPYnFWbS8xOFJnZVU1TlpUVDgzeAo0Sk42dEpMSWhKeTFVOVV5SW4rbGVnQUoxWnAxajFRVjJ6dVp0WC9VOXNBaUFMTGRoeUcrMVZuWFl1UGVzRGlFCjdJMUdTRTRQcTJ3ajlWb3FGN1Z2RHdxVlZiYm0wNy9rd3VXeCtpc2VBc2JnU3ZQR1ZaUkFCQzJJeElrZ3VDLzQKSERTdTRRUmRBb0dCQU9Ga1ZwMU5GWmNzeUlpS0tDSkdVTVYxOFp0cmVGaTErMThLVlRBZlMreEc2N2JDZGdBawpiTzV1UVQwZHFHR2dsVWswWWdWVnk5b3pYYnRyRGwzbzVjSGFXU05jTmhjYU5oc0U5aVFVL0VxQTh6S0lUY0NHCnluOUxpS1JIVDdQU3dKREpsM3cyWDVjRGJDcWZvNC9DSHRmR29SSFFpK3lwQy9yRGQyc0RZRjRqQW9HQkFPc2sKbXZibmU4dmttS3JNTjl2Q3NkaGNmSXlsNXAwK3liNEhIaWVEaUJBN2dpNmVMZURwMlRrL2tHWG5RbkJJVkttRgptdUtHZk9hSm13dTVNakFZZ0paS3k0MUlkbWxXYjVKVFQrSjVRSUZZZG1lblBRUHlFSVp0azdYN1M0NW9vTDZNCm9RSkFDTDF2SmxTc0lXUzFtTnhOU2ltRVpqZzVkZndHdlBUQVB4RnZBb0dBYjVLMTlhUkUvZExqYWdQS0hqMWsKbW5ycUlSK3dNV25VaDVXYjJmaUVJdkJ3bXNYa2wrbHdLdzlWS0NYWVJvdXhtczFkZ0hxYU1PZWdqTGhRSWxpNQo4NTVjNWM0dDBIM2ZMcnprQTdTSHQzSGg4YS9ibldTY05TdDA5cTErWE93RSt5ZHYzOE1peXFTZEZQUjFpU0oxCkZpZHpjRmdtQy84YXVRV3R4Y0drSUxVQ2dZQUU5V0tuTGo1NEVEdi83Z3FIZ2RXS1FIa0g1aiswdFN3LzY1cUIKTHM3aHVMK0lDQ0hqaWtyZ1lDekZXVmtYVVE4bisvOUdJNXZpcUtneVdSZHIyRGh0OHVuVDh1RThXMnhDNDZyZApsYno4ZlVjUjdIN201R1hnejlLN2xhOEVNOFNnQUFzdEp2aUlOaDNTejBacy96OVg5ZkZJYXRoVSt6RTN2VlNpCnZLTVgxUUtCZ1FDVVlaS2F6ZVJwalNXSlV1eU5nMjVMU3BSM2FLMUwxWlRhVy9sSHBWc1BYYVMyU2tHc05YT0kKU1dCdFRaVjVSbnY3cUc4V3dkOGJxeUt5UTV0M0svVlV4ZlRJcUxjQXkrNnZyQnZNSXBWRGpSQTF5NURqSkxiaApNUW5BckQ1ZkcvYTFtdGVyd08zUkVlZmRPNW53b1I3YWRaU3dHRzIvS3pWT2E0cXFWenNnZ1E9PQotLS0tLUVORCBSU0EgUFJJVkFURSBLRVktLS0tLQo= | base64 -d >client.key生成Client P12认证文件cert.pfx,并下载至本地
openssl pkcs12 -export -out cert.pfx -inkey client.key -in client.crt -certfile ca.crt
Enter Export Password: //密码自定义,jenkins导入证书的时候需要用到
Verifying - Enter Export Password:
2.3 在jenkins凭据菜单添加凭据
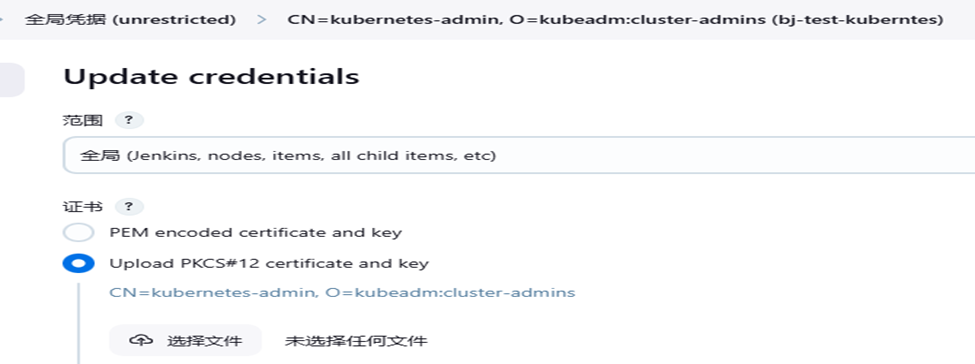
如上图所指示,凭据类型为"Certiticate",password为生成证书时的设置的密码。
添加完成后如下图所示,点击连接测试
连接成功如下所示:
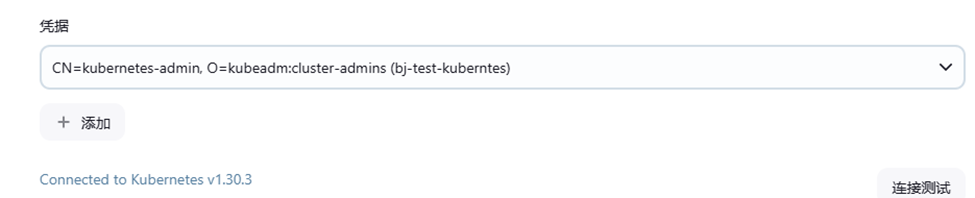
至此,部署在非kubernetes集群内的Jenkins连接kubernetes配置就完成了。
第二种部署在kubernetes集群内jenkins连接kubernetes配置
1、如何在kubernetes集群中部署jenkins。
1.1 在kubernetes集群部署jenkins
需先创建一个服务账户(ServiceAccount),用来绑定对某一个命名空间的一系列kubernetes资源对象的操作权限。
如 jenkins-rbac.yaml文件:
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: jenkins
namespace: jenkins
---
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
name: jenkins
namespace: jenkins
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["create", "delete", "get", "list", "patch", "update", "watch"]
- apiGroups: [""]
resources: ["pods/exec"]
verbs: ["create", "delete", "get", "list", "patch", "update", "watch"]
- apiGroups: [""]
resources: ["pods/log"]
verbs: ["get", "list", "watch"]
- apiGroups: [""]
resources: ["secrets"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: jenkins
namespace: jenkins
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: jenkins
subjects:
- kind: ServiceAccount
name: jenkins
namespace: jenkins然后创建deployment资源对象文件,描述jenkins的一些基本配置信息,比如开放的端口,启动参数,使用的镜像等。
编辑yaml文件
vim jenkins-deployment.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: jenkins
labels:
app-name: jenkins
namespace: jenkins
spec:
replicas: 1
strategy:
type: RollingUpdate
rollingUpdate:
maxSurge: 1
maxUnavailable: 0
selector:
matchLabels:
app-name: jenkins # Ensure this matches the label below
template:
metadata:
labels:
app-name: jenkins # This label should match the selector
spec:
serviceAccount: "jenkins"
containers:
- name: jenkins
image: docker.io/jenkins:latest
imagePullPolicy: IfNotPresent
ports:
- containerPort: 8080
name: web
protocol: TCP
- containerPort: 50000
name: agent
protocol: TCP
volumeMounts:
- name: jenkins-home
mountPath: /var/jenkins_home
env:
- name: JAVA_OPTS
value: "-Duser.timezone=Asia/Shanghai -XX:+UnlockExperimentalVMOptions -XX:+UseCGroupMemoryLimitForHeap -XX:MaxRAMFraction=1 -Dhudson.slaves.NodeProvisioner.MARGIN=50 -Dhudson.slaves.NodeProvisioner.MARGIN0=0.85"
volumes:
- name: jenkins-home
persistentVolumeClaim:
claimName: jenkins-public-pvc在资源对象的定义中使用了pv和pvc做持久化volume,所以还需要创建这两种资源对象定义的文件。
vim jenkins-pv-pvc.yaml
kind: PersistentVolume
apiVersion: v1
metadata:
labels:
name: jenkins-public-pv
name: jenkins-public-pv
namespace: jenkins
spec:
capacity:
storage: 30Gi
accessModes:
- ReadWriteMany
persistentVolumeReclaimPolicy: Retain
nfs:
path: /data/jenkins
server: 192.168.2.200
---
kind: PersistentVolumeClaim
apiVersion: v1
metadata:
name: jenkins-public-pvc
namespace: jenkins
spec:
accessModes:
- ReadWriteMany
resources:
requests:
storage: 30Gi
selector:
matchLabels:
name: jenkins-public-pv使用nfs作为共享存储,创建pvc使用pv,在生产环境中,一般使用storageclass替代pv作为动态存储。也可以用挂载nfs目录的方式
部署service资源对象,相当于给运行jenkins服务的pod加了一个代理。
vim jenkins-service.yaml
kind: Service
apiVersion: v1
metadata:
labels:
app-name: jenkins
name: jenkins
namespace: kube-system
spec:
ports:
- port: 8080
targetPort: 8080
name: web
- port: 50000
targetPort: 50000
name: agent
selector:
app-name: jenkins部署ingress服务,直接跳过service接管service代理的pod。
vim jenkins-ingress.yaml:
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: jenkins
namespace: kube-system
spec:
rules:
- host: jenkins.cctbb.com
http:
paths:
- path: /
backend:
serviceName: jenkins
servicePort: 8080配置本地hosts文件做解析。
或不配置ingress 直接用nodePort方式
部署完成后如下所示:
root@ops-test-021:~# kubectl get pods,ingress,svc,deploy -n kube-system |grep jenkins
pod/jenkins-78f658b5d6-25qgl 1/1 Running 0 163d
ingress.extensions/jenkins k8s-jenkins.com 80 10m
service/jenkins ClusterIP 10.254.179.172 <none> 8080/TCP,50000/TCP 198d
deployment.extensions/jenkins 1/1 1 1 198d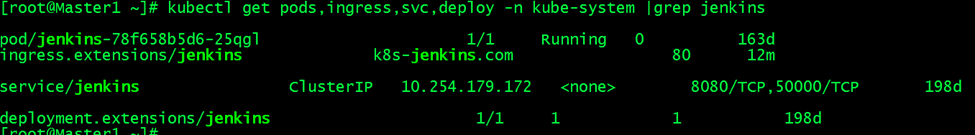
1.2、配置jenkins连接kubernetes
部署在kubernetes集群内的jenkins配置连接kubernetes相对较简单,同样在系统配置页进行配置,不用生成第一种方式中的系列证书,kubernetes的地址直接写kubernetes的FQDN即可。
如下图:
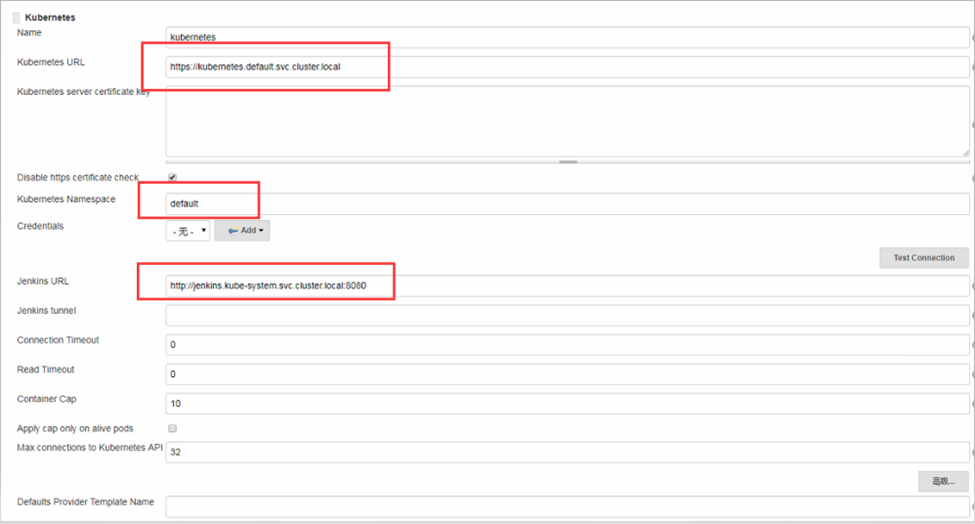
解释
Name 处默认为 kubernetes,也可以修改为其他名称
Kubernetes URL 处可以填写 https://kubernetes.default ,为Kubernetes Service 对应的 DNS 记录,通过该DNS记录可以解析成该 Service 的 Cluster IP。注意:这里也可以填写 https://kubernetes.default.svc.cluster.local 完整 DNS 记录,因为它要符合 service_name.namespace_name.svc.cluster_domain的命名方式。
也可以直接填写外部 Kubernetes 的地址 https://ClusterIP:Ports (不推荐)。
Jenkins URL 处应该填写Jenkins的service地址和端口。比如我的:http://jenkins.kube-system.svc.cluster.local:8080 也可以写成http://jenkins.kube-system:8080, 表示jenkins的service名称和所在的namespace名称,
同kubernetes url设置类似,也是使用Jenkins Service 对应的 DNS 记录以及端口。
如果暴露服务的方式为nodeport,也可以用http://NodeIP:NodePort(本示例没配置)的方式,根据自己实际情况修改即可。
Credentials :同属于一个集群环境,对于集群认证的过程就不需要了,认证凭证也就不用填写了。
Jenkins虽然能连接kubernetes了,但是通过kubernetes还不能生成动态的slave代理,因为slave agent(jnlp-agent)在启动的时候会通过50000(默认)端口与jenkins master进行通信。Jenkins这个端口默认是关闭的,需要开启这个端口。
Manage Jenkins(系统管理)--->(Configure global Security)全局安全配置---> Agents(代理)
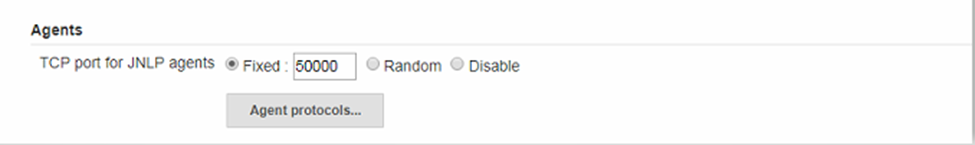
解释
如上指定的端口是jnlp-agent连接jenkins-master使用的端口。
如果Jenkins-master只是在Docker容器(没有使用容器编排系统)中启动的一定要记得将这个端口暴露到外部,不然jenkins-master会不知道slave是否已经启动,会反复去创建pod直到到超过重试次数。
该端口的默认值是50000,如果要修改为其他端口,需要修改在创建jenkins"云"时对应的Jenkins Tunnel(通道)参数的配置,如果使用50000端口,这里可以不用填写,如果换成别的端口,这里需要单独设定,最好是jenkins_url:port的形式。
如果不开启代理端口,Jenkins通过kubernetes动态生成slave节点的时候,jenkins后台会报如下错误,并且pod会不断的生成和删除。
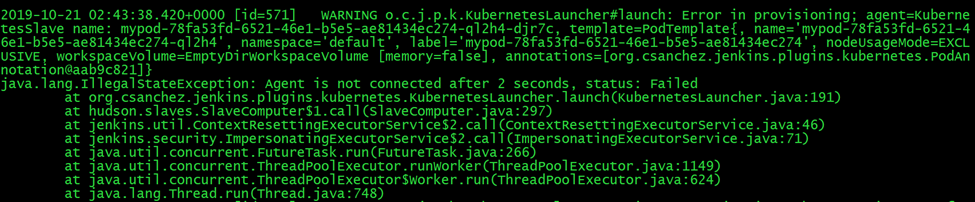
至此,jenkins与kubernetes的集成就完成了
默认情况下,agent代理连Jenkins的接超时时间为100秒。在特殊情况下,如果想设置一个不同的值,可以将system属性设置org.csanchez.jenkins.plugins.kubernetes.PodTemplate.connectionTimeout为一个不同的值。但是100s的话其实够用了,如果超过100s还没生成代理pod,就需要根据jenkins日志去排查问题了。如果jenkins连接kubernetes配置成功了,大多数情况下的错误一般就是配置podtemplate出现了问题。