
Conference:ACM CCS 2025
CCF level:CCF A
Year:2025
Conference time:October 13-17, 2025
1
Title:
Accountable Liveness
可验证的活跃性
Authors:****
Key words:
BFT Protocols; Blockchain; Accountability; Forensics
BFT 协议;区块链;问责制;取证
Abstract:****
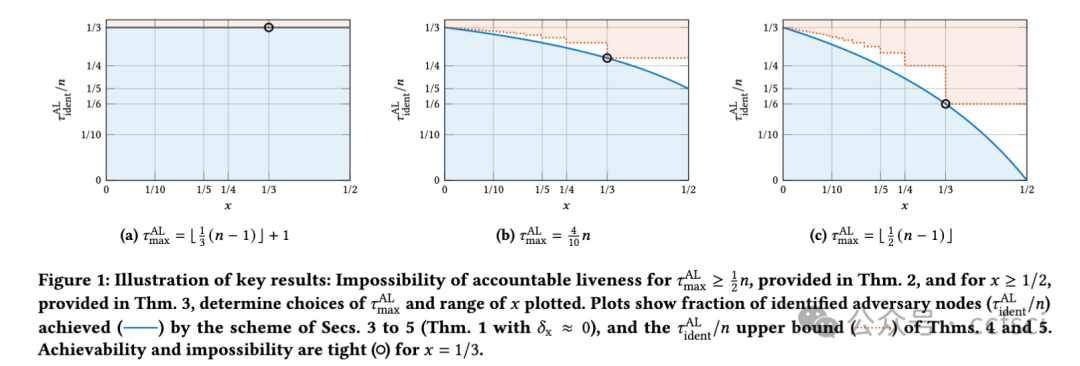
Safety and liveness are the two classical security properties of consensus protocols. Recent works have strengthened safety with accountability: should any safety violation occur, a sizable fraction of adversary nodes can be proven to be protocol violators. This paper studies to what extent analogous accountability guarantees are achievable for liveness. To reveal the full complexity of this question, we introduce an interpolation between the classical synchronous and partially-synchronous models that we call the x-partially-synchronous network model in which, intuitively, at most an x fraction of the time steps in any sufficiently long interval are asynchronous (and, as with a partially-synchronous network, all time steps are synchronous following the passage of an unknown ''global stablization time''). We prove a precise characterization of the parameter regime in which accountable liveness is achievable: if and only if x < 1/2 and ƒ < n/2, where n denotes the number of nodes and ƒ the number of nodes controlled by an adversary. We further refine the problem statement and our analysis by parameterizing by the number of violating nodes identified following a liveness violation, and provide evidence that the guarantees achieved by our protocol are near-optimal (as a function of x and ƒ). Our results provide rigorous foundations for liveness-accountability heuristics such as the ''inactivity leaks'' employed in Ethereum.
安全性和活性是共识协议的两个经典安全属性。近期研究通过引入问责机制来增强安全性:一旦发生任何安全违规,即可证明相当一部分攻击者节点是协议违规者。本文探讨了在活性方面,类似的问责保证在多大程度上能够实现。为了全面揭示该问题的复杂性, 我们引入了经典同步模型与部分同步模型之间的插值模型,即所谓的 x-部分同步网络模型。直观而言,在该模型中,任何足够长的区间内,最多 x 比例的时间步是异步的(且与部分同步网络类似,经过一个未知的"全局稳定化时间"后,所有时间步均变为同步)。我们证明了可问责活性可实现的参数区域具有精确特征:当且仅当 x < 1/2 且 ƒ < n/2 时,其中 n 表示节点数,ƒ 表示由攻击者控制的节点数。我们进一步通过将问题陈述和分析参数化为"活体性违规"发生后被识别出的违规节点数量,从而对问题陈述和分析进行了细化,并提供了证据表明,我们的协议所实现的保证是近乎最优的(作为 x 和 ƒ 的函数)。我们的结果为以太坊中采用的"非活动泄漏"等活体性问责启发式方法提供了严谨的理论基础。
Pdf下载链接:
https://dl.acm.org/doi/10.1145/3719027.3765032
2
Title:
Efficient Constant-Size Linkable Ring Signatures for Ad-Hoc Rings via Pairing-Based Set Membership Arguments
基于配对的集合成员论证实现的、适用于自组织环的高效恒定大小可链接环签名
Authors:****
Key words:
Linkable Ring Signatures, Ad-hoc Rings, Set Membership Arguments, Blockchain
可链接环签名、临时环、集合成员论、区块链
Abstract:****
Linkable Ring Signatures (LRS) allow users to anonymously sign messages on behalf of ad-hoc rings, while ensuring that multiple signatures from the same user can be linked. This feature makes LRS widely used in privacy-preserving applications like e-voting and e-cash. To scale to systems with large user groups, efficient schemes with short signatures and fast verification are essential. Recent works, such as DualDory (ESORICS'22) and LLRing (ESORICS'24), improve verification efficiency through offline precomputations but rely on static rings, limiting their applicability in ad-hoc ring scenarios. Similarly, constant-size ring signature schemes based on accumulators face the same limitation.
In this paper, we propose a framework for constructing constant-size LRS suitable for large ad-hoc rings. We introduce a novel pairing-based Set Membership Argument (SMA) with a proof size of only three group elements. By leveraging KZG polynomial commitments, we optimize the verification to require only constant group exponentiations and pairings, as well as linear field multiplications. Utilizing the SMA, our framework achieves constant-size signatures with verification dominated by linear field operations, outperforming existing schemes that require linear group exponentiations in ad-hoc ring settings. Moreover, it exhibits strong scalability: (i) compatibility with any PKI-based cryptosystem and (ii) scoped linkability, enabling flexible definitions of linking scope.
We instantiate our framework using a discrete logarithm public key structure. On the BN254 curve, our signature size is fixed at 687 bytes, which to our best knowledge is the shortest LRS for ring sizes larger than 32. For a ring size of 1024, our verification cost is only 10.4 ms, achieving 48.6×, 2.6×--467×, 7.9×--13.2×, and 2.2×--102.5× improvements over Omniring (CCS'19), DualDory (with and without precomputation), LLRing-DL (with and without precomputation), and LLRing-P (with and without precomputation), respectively. Moreover, this performance gap continues to grow as the ring size increases.
可链接环签名(LRS)允许用户代表ad-hoc环匿名签署消息,同时确保来自同一用户的多个签名可以链接。这一特性使得LRS在电子投票和电子现金等隐私保护应用中得到了广泛应用。为了扩展到具有大型用户组的系统,具有短签名和快速验证的高效方案至关重要。最近的工作,如DualDory(ESORICS'22)和LLRing(ESORICS'24),通过离线预计算提高了验证效率,但依赖于静态环,限制了它们在ad-hoc环场景中的适用性。同样,基于累加器的恒定大小环签名方案也面临着同样的限制。
本文提出了一种适用于大型ad-hoc环的恒定大小LRS构建框架。我们引入了一种新的基于配对的集成员参数(SMA),其证明大小仅为三个组元素。通过利用KZG多项式承诺,我们优化了验证,只需要常数群指数和配对,以及线性域乘法。利用SMA,我们的框架通过线性字段操作主导的验证实现了恒定大小的签名,优于在ad-hoc环设置中需要线性群指数的现有方案。此外,它还具有很强的可扩展性:(i)与任何基于PKI的密码系统兼容,(ii)范围链接能力,能够灵活定义链接范围。
我们使用离散对数公钥结构实例化我们的框架。在BN254曲线上,我们的签名大小固定为687字节,据我们所知,这是大于32的环大小的最短LRS。对于1024的环大小,我们的验证成本仅为10.4毫秒,分别比Omniring(CCS'19)、DualDory(有和没有预计算)、LLR-computing DL(有和不有预计算)和LLR-P(有和无预计算)提高了48.6×、2.6×-467×、7.9×-13.2×和2.2×-102.5×。此外,随着环尺寸的增加,这种性能差距继续扩大。
Pdf下载链接:
https://dl.acm.org/doi/10.1145/3719027.3744830
3
Title:
Forking the RANDAO: Manipulating Ethereum's Distributed Randomness Beacon
RANDAO 分叉:操纵以太坊的分布式随机性信标
Authors:****
Key words:
Ethereum, blockchain, proof-of-stake, unpredictability, manipula-bility, distributed randomness beacon, RANDAO
以太坊、区块链、权益证明、不可预测性、可操纵性、分布式随机信标、RANDAO
Abstract:****
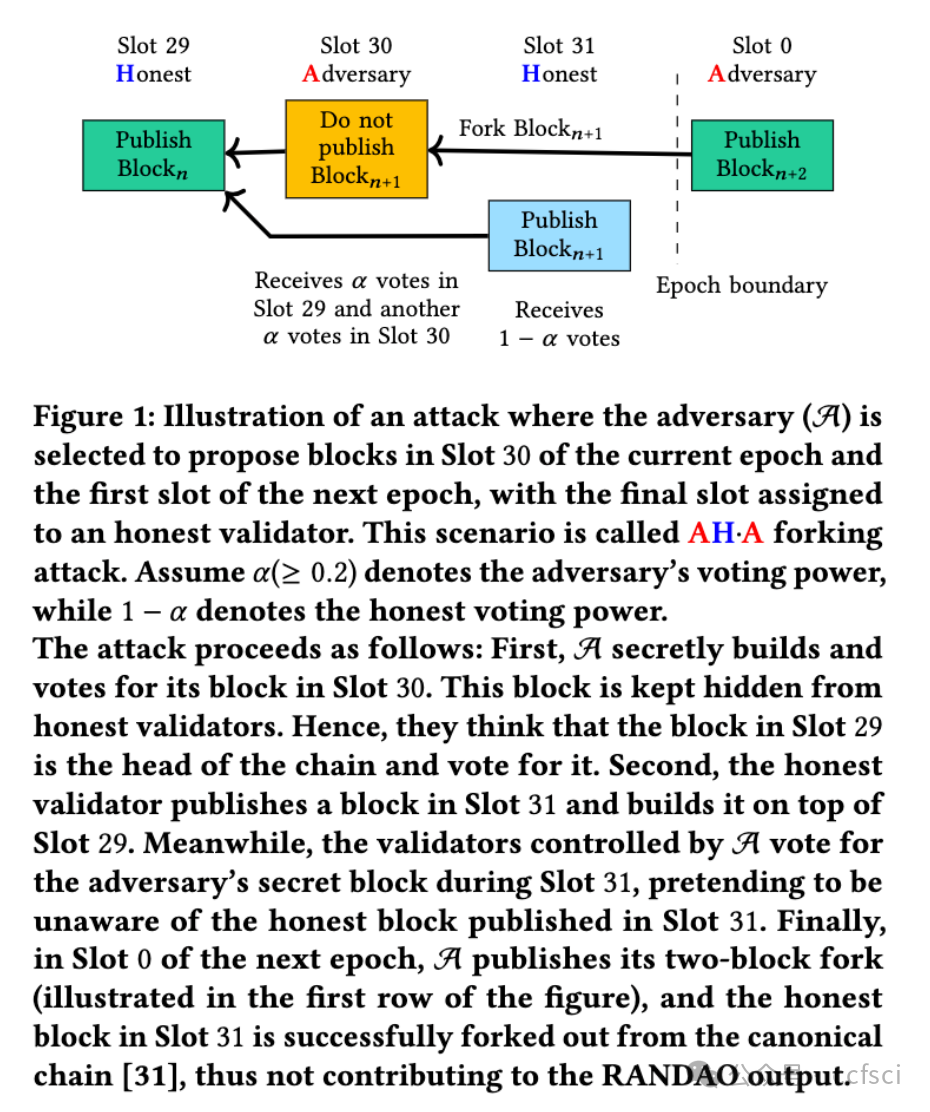
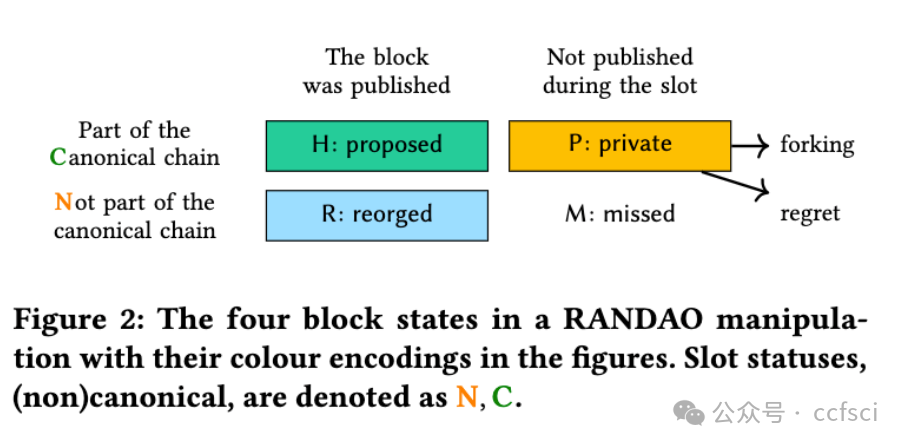
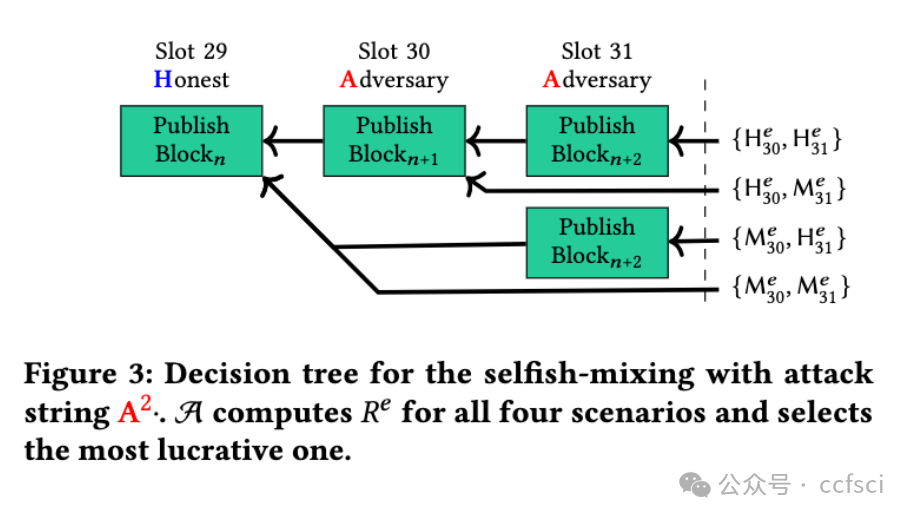
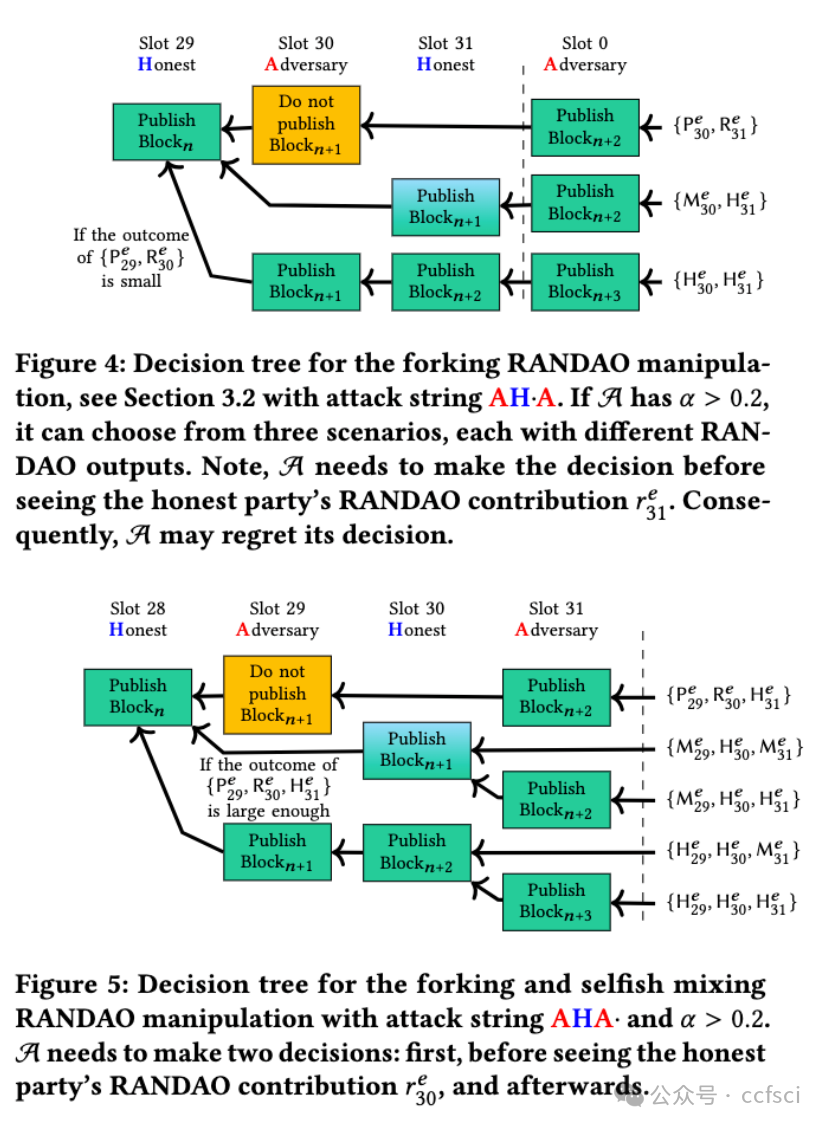
Proof-of-stake consensus protocols often rely on distributed randomness beacons (DRBs) to generate randomness for leader selection. This work analyses the manipulability of Ethereum's DRB implementation, RANDAO, in its current consensus mechanism. Even with its efficiency, RANDAO remains vulnerable to manipulation through the deliberate omission of blocks from the canonical chain. Previous research has shown that economically rational players can withhold blocks known as a block withholding attack or selfish mixing when the manipulated RANDAO outcome yields greater financial rewards.
We introduce and evaluate a new manipulation strategy, the RANDAO forking attack. Unlike block withholding, whereby validators opt to hide a block, this strategy relies on selectively forking out an honest proposer's block to maximise transaction fee revenues and block rewards. In this paper, we draw attention to the fact that the forking attack is significantly more harmful than selfish mixing for two reasons. Firstly, it exacerbates the unfairness among validators. More importantly, it significantly undermines the reliability of the blockchain for the average user by frequently causing already published blocks to be forked out. By doing so, the attacker can fork the chain without losing slots, and we demonstrate that these are later fully compensated for. Our empirical measurements, investigating such manipulations on Ethereum mainnet, revealed no statistically significant traces of these attacks to date.
权益证明共识协议通常依赖分布式随机信标(DRB)来生成用于领导者选出的随机数。本研究分析了以太坊当前共识机制中DRB实现方案RANDAO的可操纵性。尽管RANDAO效率较高,但它仍然容易受到通过故意从规范链中省略区块而进行的操纵。先前研究表明,当操纵RANDAO的结果能带来更高经济回报时,经济理性行为者可能会隐匿区块,这种行为被称为区块隐匿攻击或自私混币。
我们提出并评估了一种新的操纵策略------RANDAO分叉攻击。与验证者选择隐藏区块的区块保留不同,该策略依赖于有选择地将诚实提议者的区块分叉出去,以最大化交易手续费收入和区块奖励。本文指出,分叉攻击比自私混币危害更大,原因有二。首先,它加剧了验证者之间的不公平。更重要的是,它会频繁导致已发布的区块被分叉,从而严重削弱了区块链对普通用户的可靠性。通过这种方式,攻击者可以在不损失槽位的情况下分叉链,且我们证明这些损失随后会得到全额补偿。我们在以太坊主网上针对此类操纵行为进行的实证测量显示,迄今为止尚未发现这些攻击的统计学上显著的痕迹。
Pdf下载链接:
https://dl.acm.org/doi/10.1145/3719027.3744852
4
Title:
Mining in Logarithmic Space with Variable Difficulty
在难度可变的对数空间中进行挖矿
Authors:****
Abstract:****
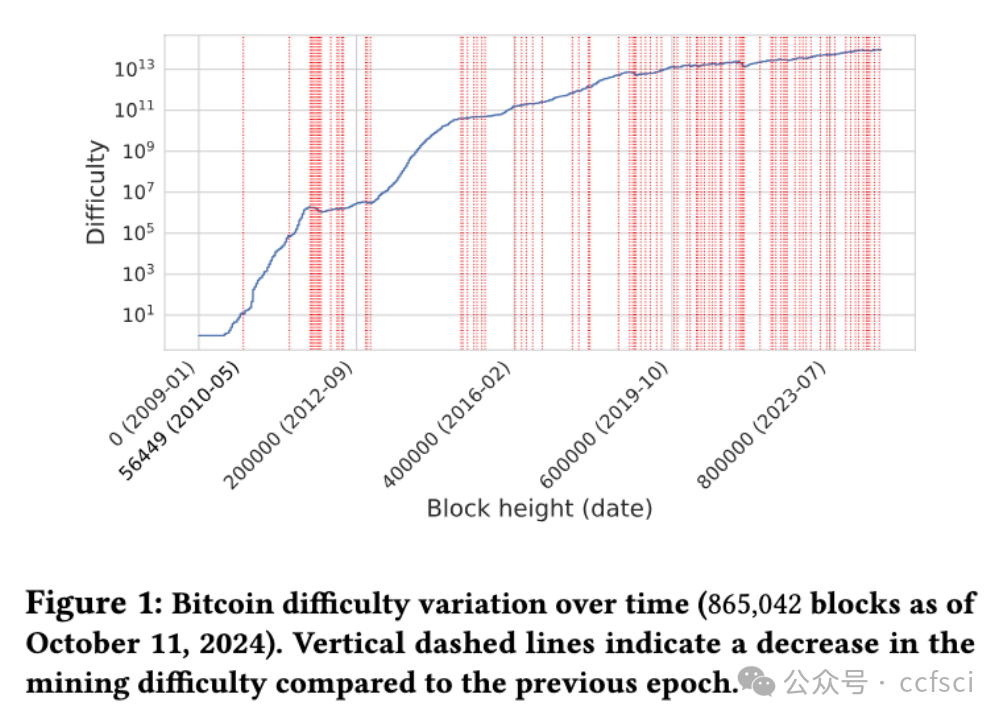
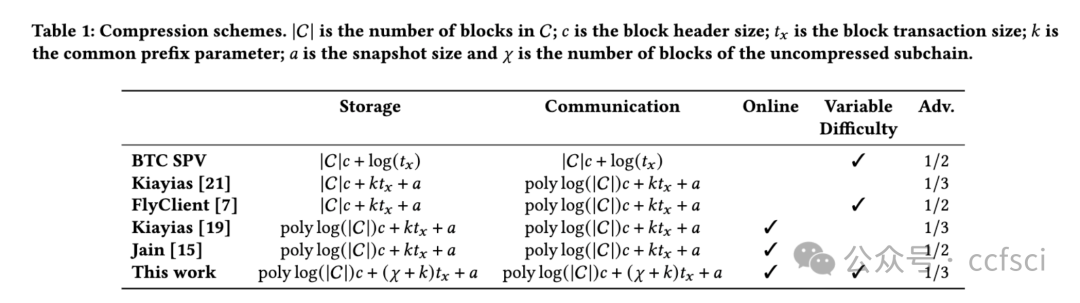
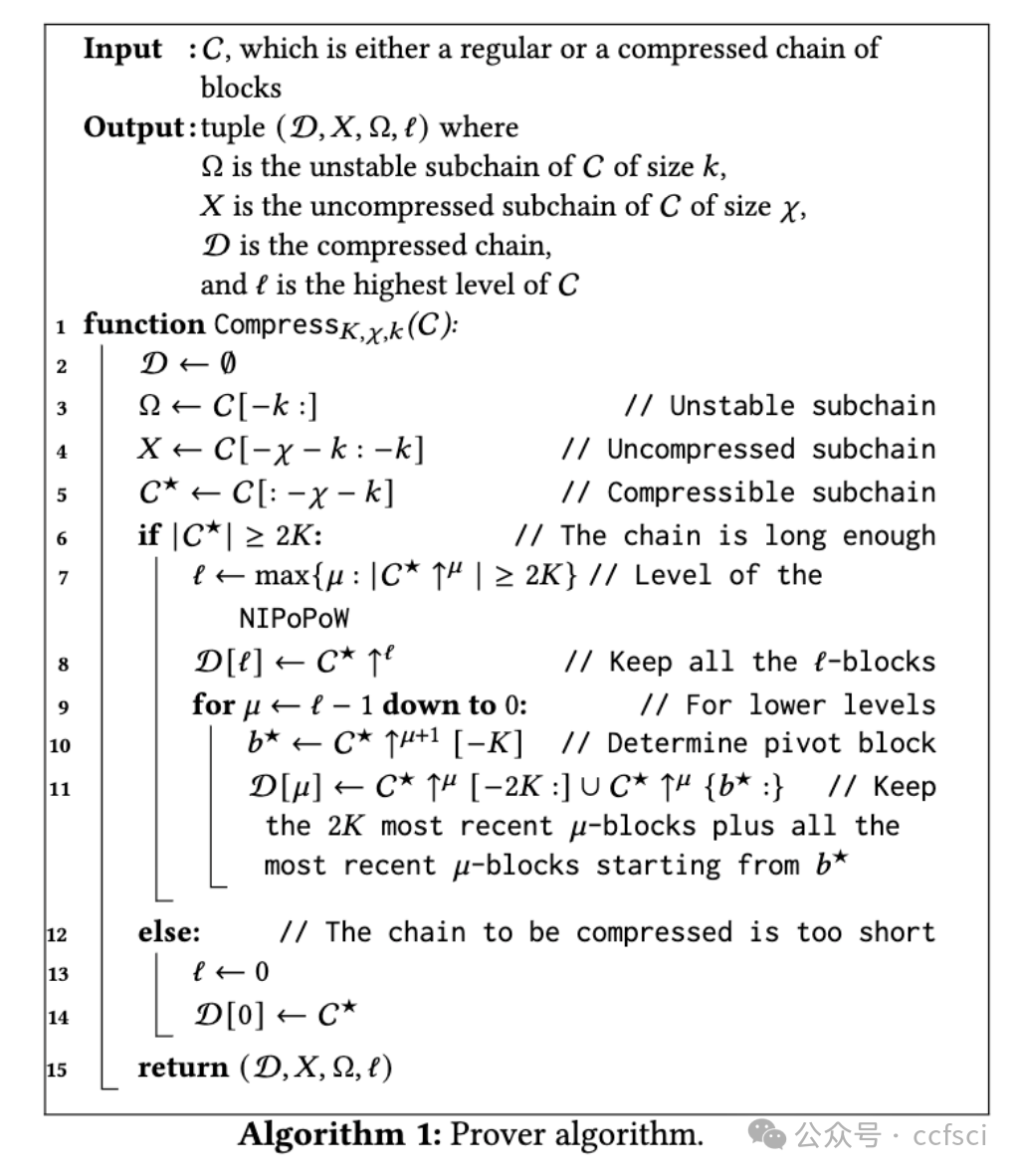
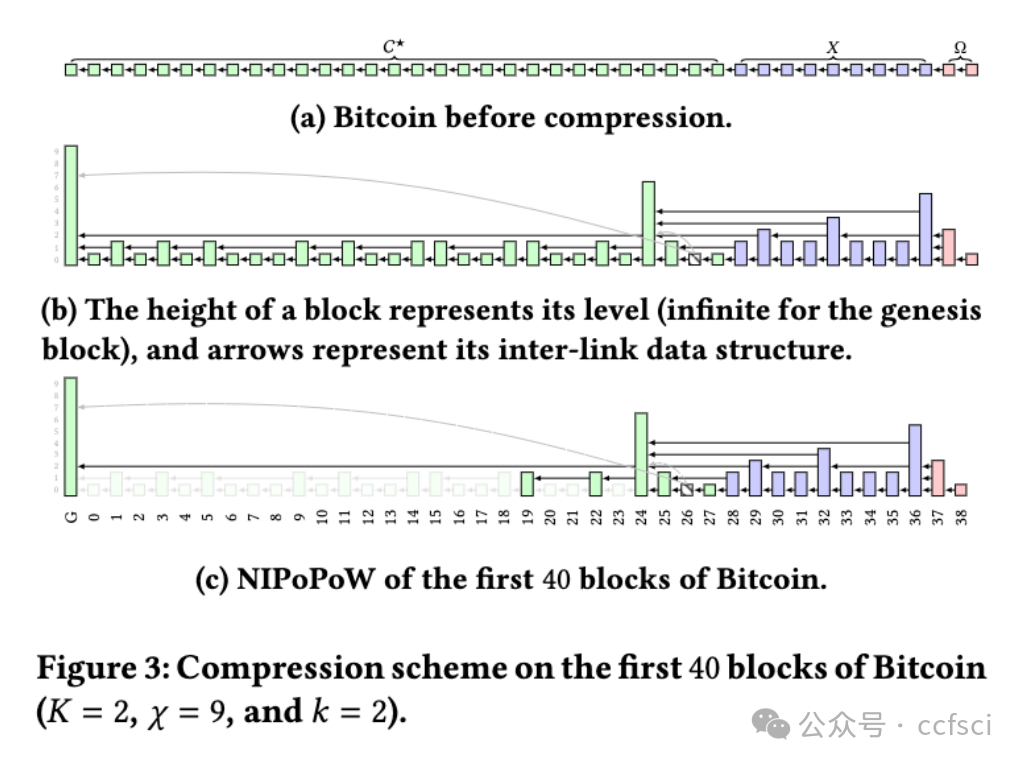
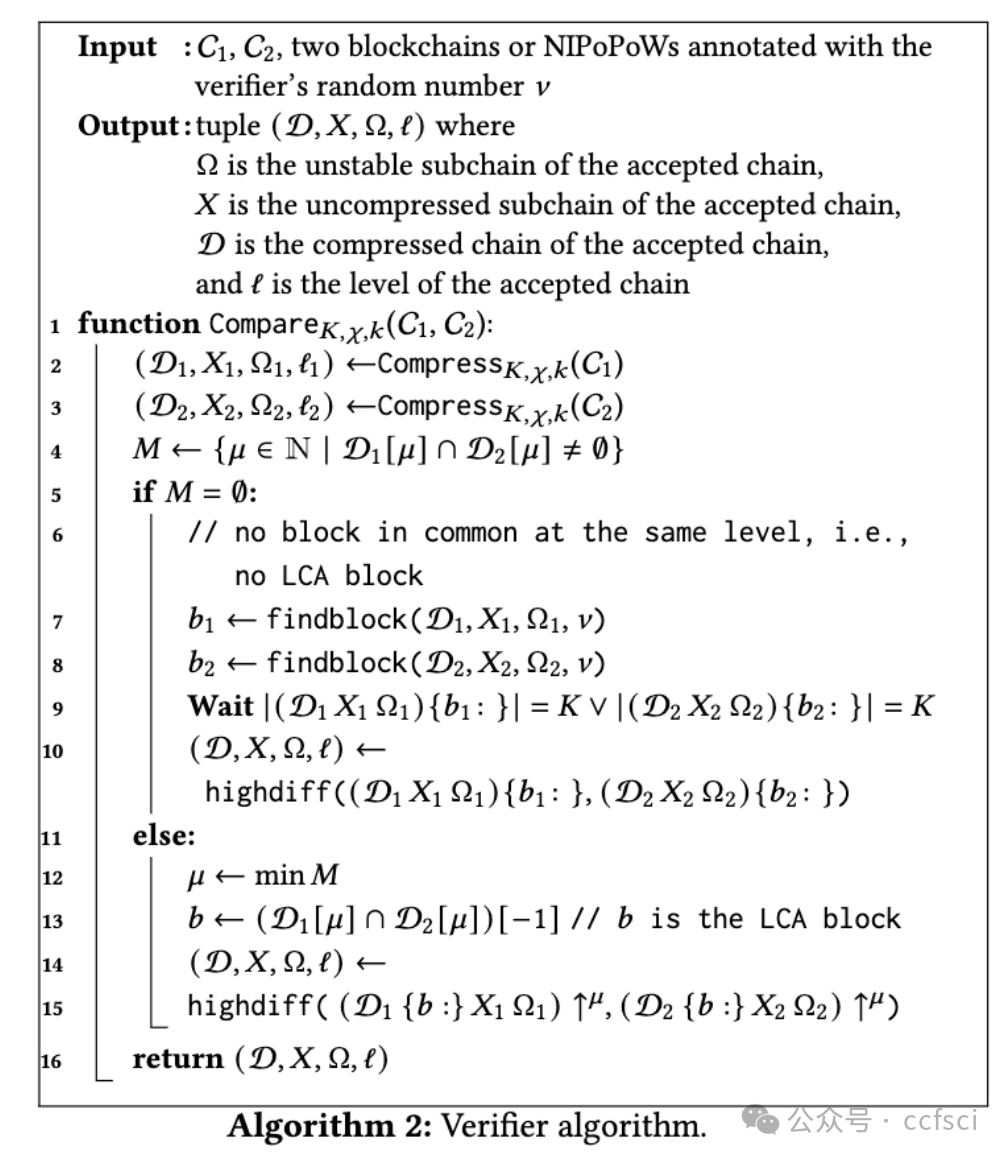
This paper presents the first non-interactive, succinct, and secure representation of a PoW-based blockchain that operates under variable mining difficulty while satisfying both completeness and onlineness properties. Completeness ensures that provers can update an existing NIPoPoW by incorporating a newly mined block, whereas onlineness ensures that miners can extend the chain directly from a NIPoPoW. The time complexity for both the prover (to update a NIPoPoW with a new block) and the verifier is logarithmic in the number of blocks of the underlying PoW blockchain. The communication complexity required for synchronization is polylogarithmic in the length of the blockchain. We prove the correctness of our scheme in the presence of a 1/3-bounded PPT adversary.
本文提出了一种基于工作量证明(PoW)的区块链的首个非交互式、紧凑且安全的表示方法,该方法在挖矿难度可变的情况下运行,同时满足完备性和在线性属性。完备性确保证明者能够通过纳入新挖出的区块来更新现有的NIPoPoW,而在线性则确保矿工能够直接从NIPoPoW延伸区块链。对于证明者(将新区块整合到NIPoPoW中)和验证者而言,其时间复杂度均为底层PoW区块链区块数的对数级。同步所需的通信复杂度为区块链长度的多对数级。我们证明了本方案在面对1/3界限的PPT攻击者时具有正确性。
Pdf下载链接:
https://dl.acm.org/doi/10.1145/3719027.3744874
5
Title:
Bitcoin Under Volatile Block Rewards: How Mempool Statistics Can Influence Bitcoin Mining
波动块奖励下的比特币:Mempool统计数据如何影响比特币挖矿
Authors:****
Key words:
Bitcoin, Selfish mining, Transaction fee, Undercutting, Reinforce-ment learning, A3C
比特币、自私挖矿、交易费、削减、强化学习、A3C
Abstract:****
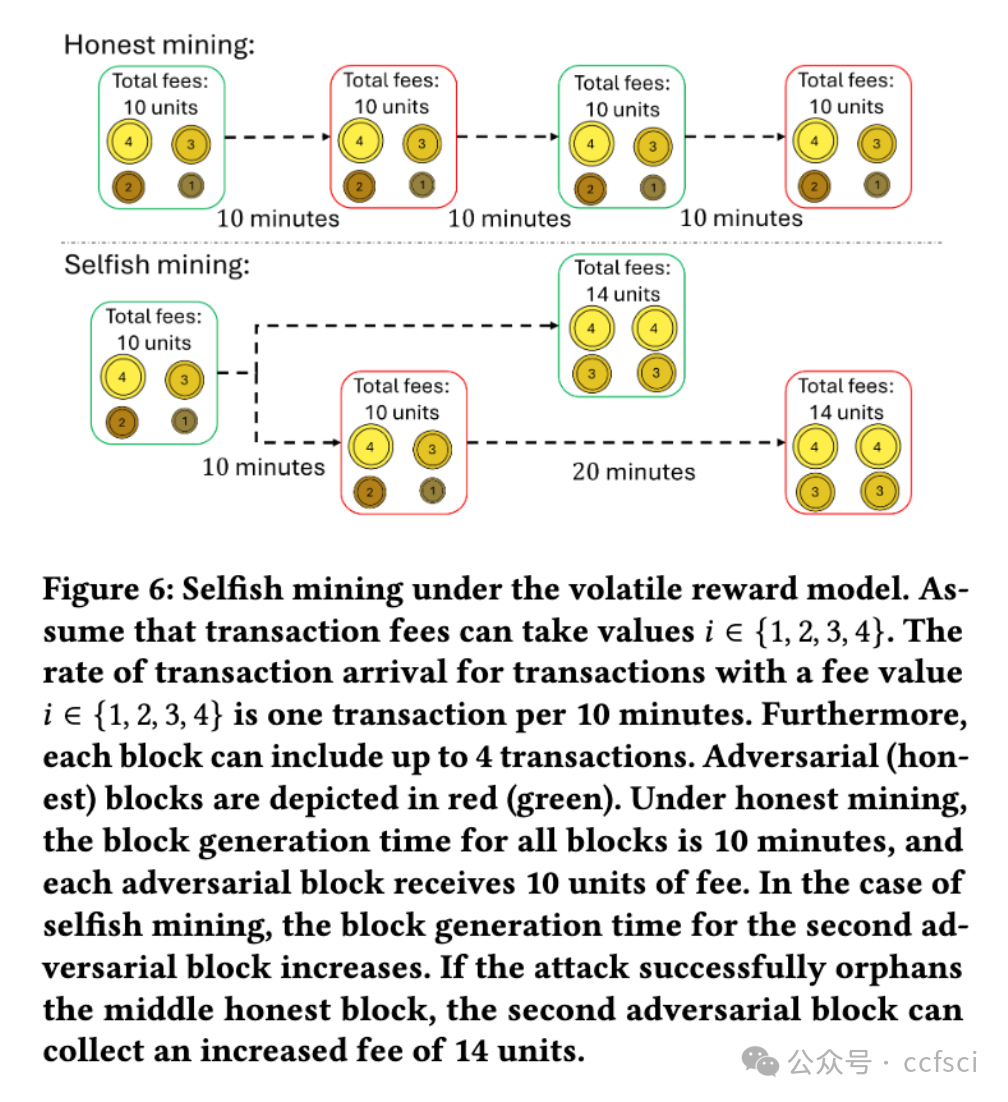
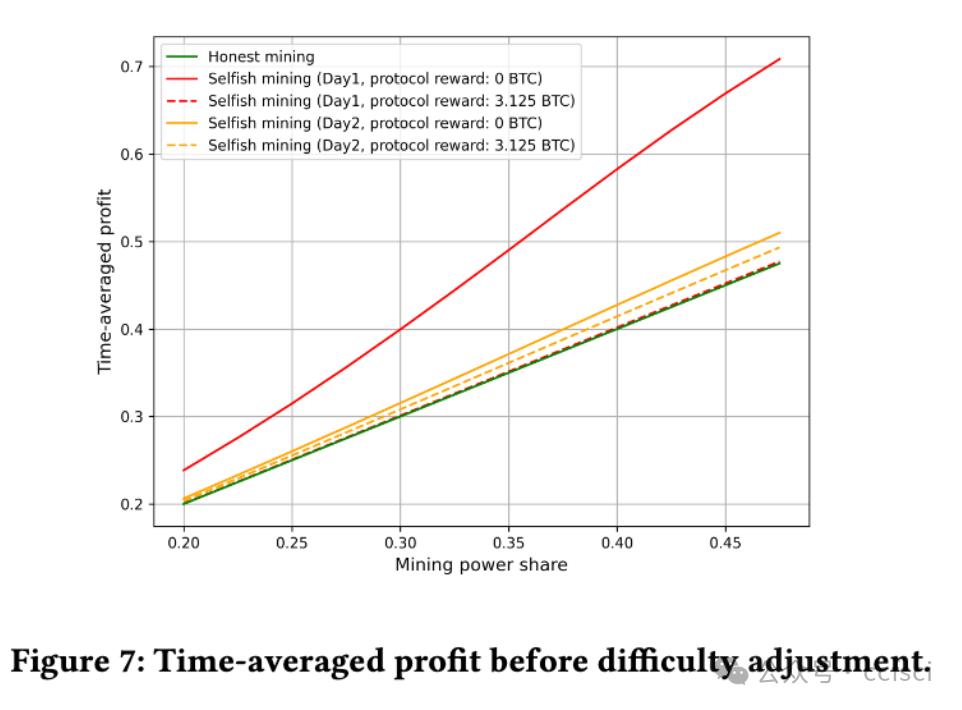
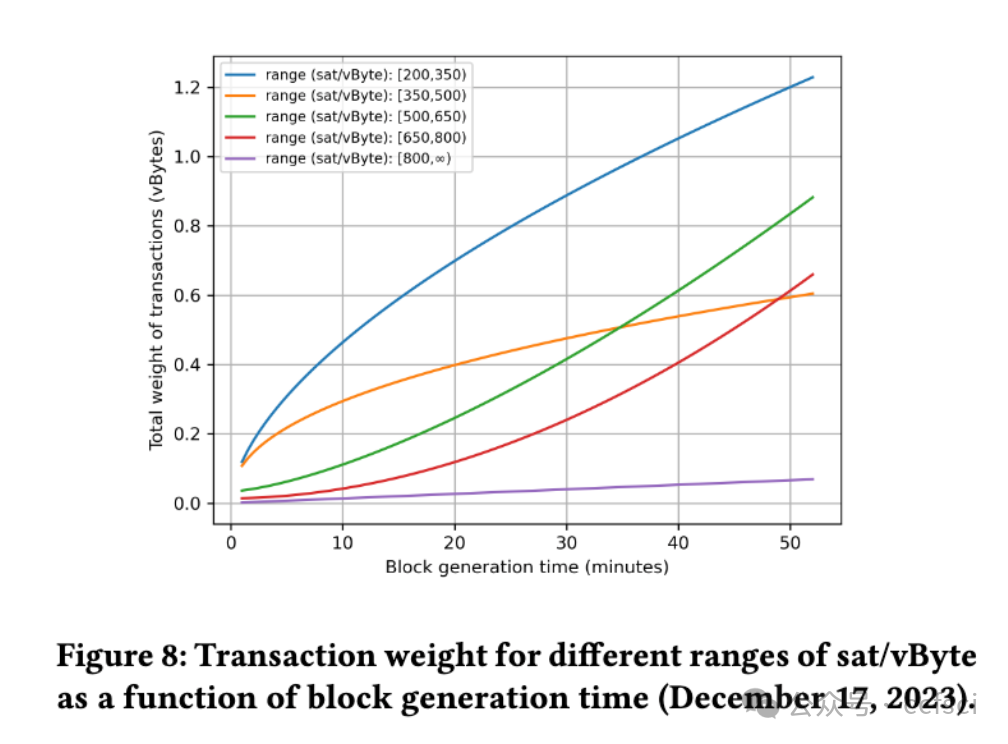
The security of Bitcoin protocols is deeply dependent on the incentives provided to miners, which come from a combination of block rewards and transaction fees. As Bitcoin experiences more halving events, the protocol reward converges to zero, making transaction fees the primary source of miner rewards. This shift in Bitcoin's incentivization mechanism, which introduces volatility into block rewards, leads to the emergence of new security threats or intensifies existing ones. Previous security analyses of Bitcoin have either considered a fixed block reward model or a highly simplified volatile model, overlooking the complexities of Bitcoin's mempool behavior.
In this paper, we present a reinforcement learning-based tool for analyzing mining strategies under a more realistic volatile reward model. The tool leverages the Asynchronous Advantage Actor-Critic (A3C) algorithm to derive near-optimal strategies while interacting with an environment that simulates the behavior of the Bitcoin mempool during any specified period, enabling analysis based on actual historical patterns. It supports the evaluation of adversarial mining strategies, such as selfish mining and undercutting, both before and after the difficulty adjustment, offering insights into the effects of mining attacks in both the short and long term.
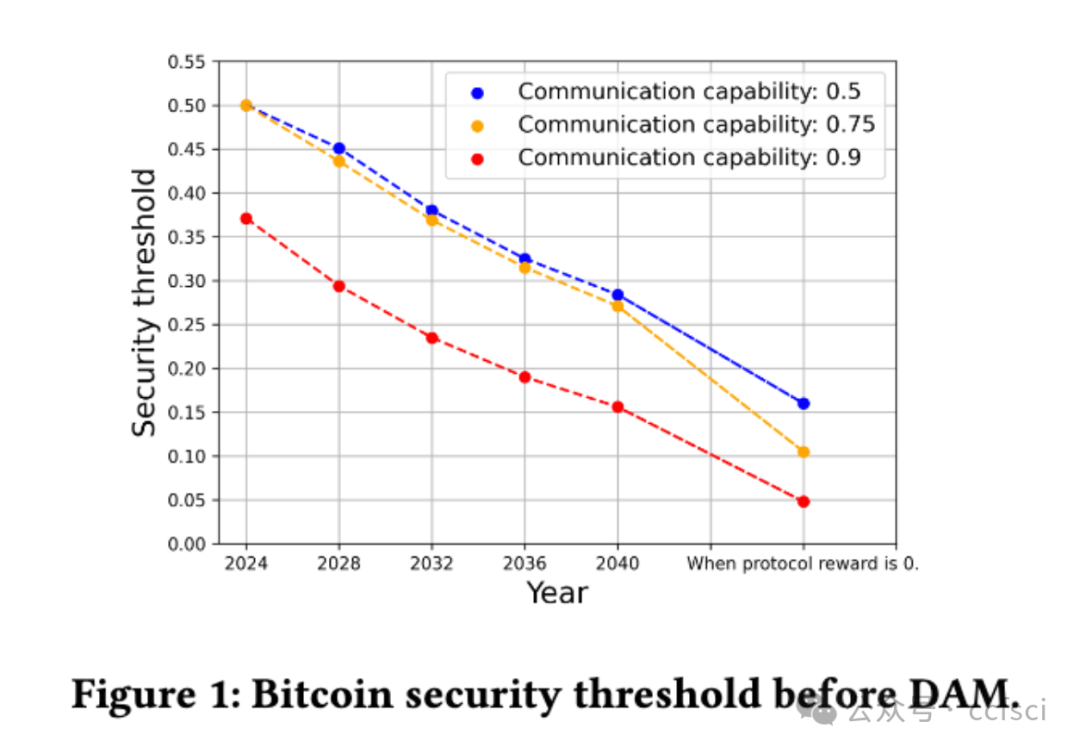
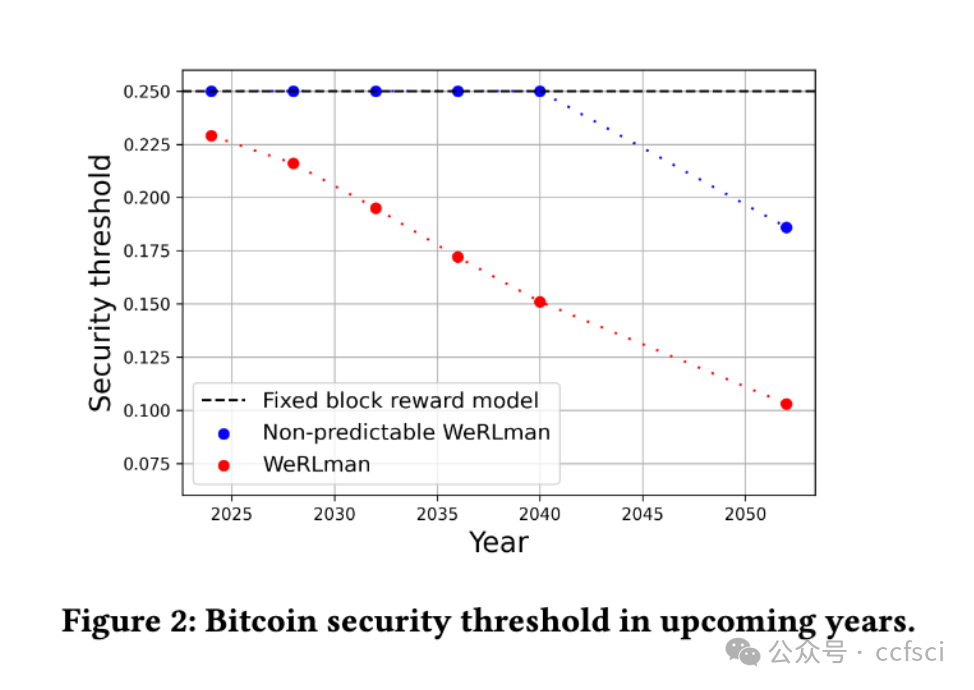
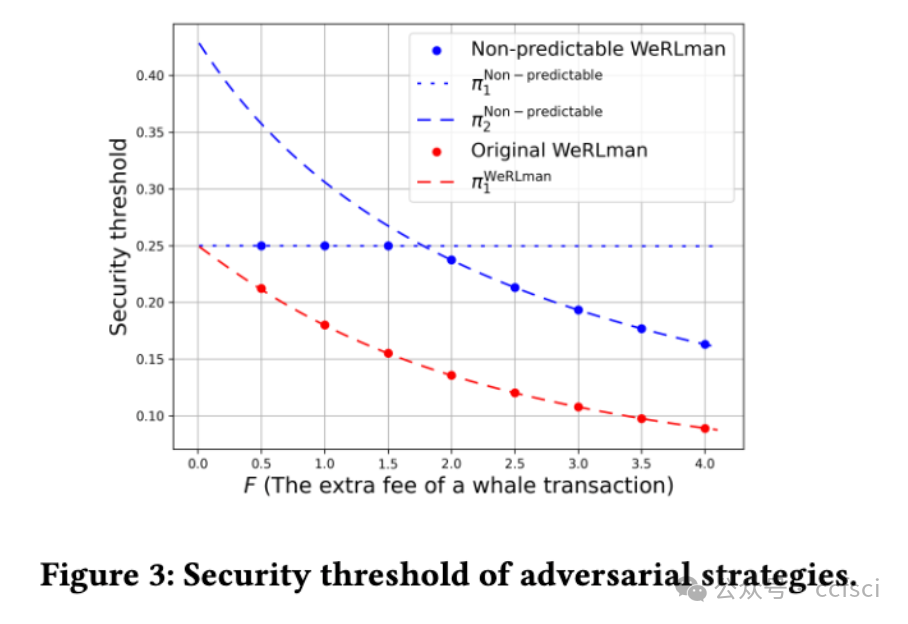
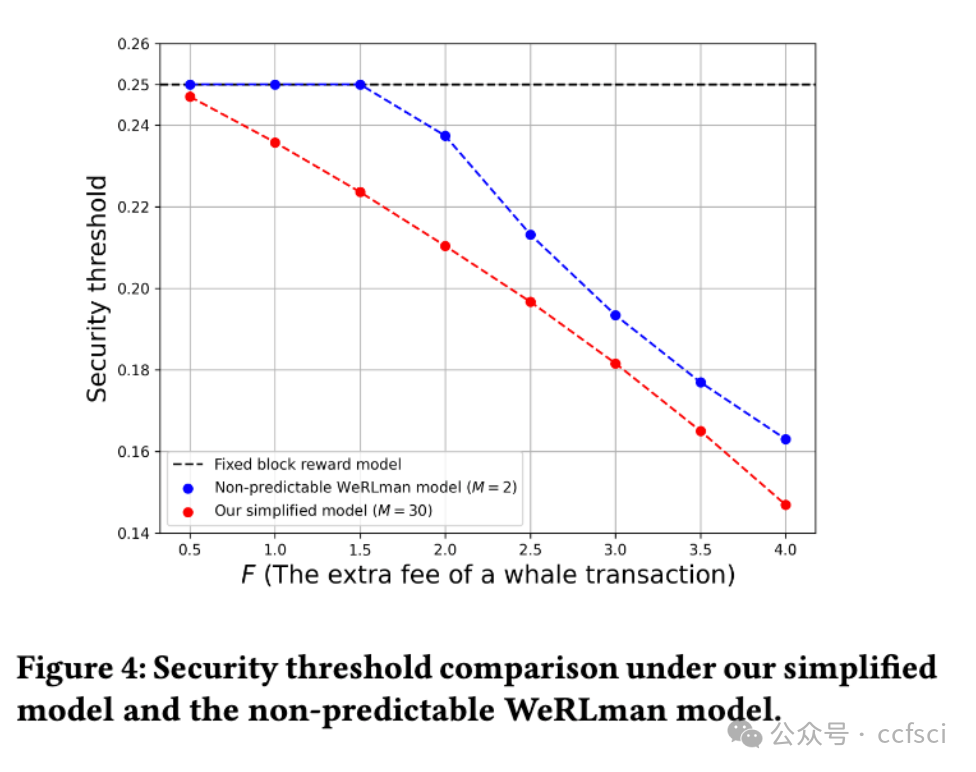
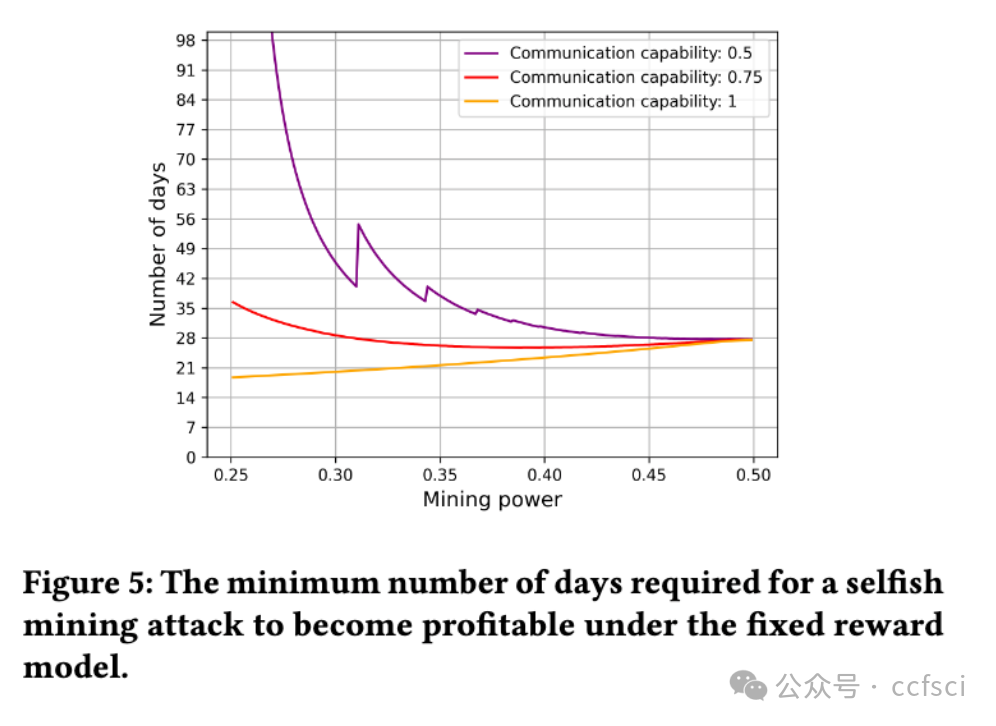
We revisit the Bitcoin security threshold presented in the WeRLman paper and demonstrate that the implicit predictability of valuable transaction arrivals in this model leads to an underestimation of the reported threshold. Additionally, we show that, while adversarial strategies like selfish mining under the fixed reward model incur an initial loss period of at least two weeks, the transition toward a transaction-fee era incentivizes mining pools to abandon honest mining for immediate profits. This incentive is expected to become more significant as the protocol reward approaches zero in the future.
比特币协议的安全性在很大程度上取决于向矿工提供的激励,这些激励来自区块奖励和交易费用的组合。随着比特币经历更多减半事件,协议奖励趋近于零,使交易费用成为矿工奖励的主要来源。比特币激励机制的这种转变,将波动性引入区块奖励,导致新的安全威胁的出现或加剧了现有的安全威胁。之前对比特币的安全分析要么考虑了固定块奖励模型,要么考虑了高度简化的波动模型,忽视了比特币内存池行为的复杂性。
在本文中,我们提出了一种基于强化学习的工具,用于在更现实的波动奖励模型下分析挖掘策略。该工具利用异步优势参与者批判(A3C)算法,在与模拟比特币内存池在任何指定时期行为的环境交互时,得出接近最优的策略,从而能够基于实际历史模式进行分析。它支持在难度调整前后评估对抗性挖矿策略,如自私挖矿和底切,从而深入了解挖矿攻击的短期和长期影响。
我们重新审视了WeRLman论文中提出的比特币安全阈值,并证明该模型中有价值交易到达的隐含可预测性导致对报告阈值的低估。此外,我们发现,虽然在固定奖励模型下自私挖矿等对抗性策略会导致至少两周的初始损失期,但向交易费时代的过渡会激励矿池放弃诚实挖矿以获得即时利润。随着协议奖励在未来接近零,这种激励预计将变得更加重要。
Pdf下载链接: