本文严格遵循NIST SP 800-207、CSA SDP标准、Gartner CARTA框架及《网络安全法》第21条。所有实施步骤需在授权环境进行,严禁未授权访问、身份冒用或网络扫描。
摘要
本文系统解构零信任架构(Zero Trust Architecture)从理论到落地的全链路实施路径,聚焦身份治理、设备信任、网络微隔离、应用代理、数据保护、持续验证等10大核心模块。深度剖析BeyondCorp、SDP、ZTNA三大技术路线,提供28个实战配置代码、9张架构图、7个金融/政务/制造行业案例。为CISO、安全架构师、网络工程师提供可落地的技术指南。拒绝"概念炒作",专注"生产环境可执行方案"。
1. 引言:零信任不是产品,而是架构范式革命
"我们买了零信任产品,但员工抱怨访问变慢,业务部门说影响效率------零信任到底是什么?"
------ 某企业CISO在架构评审会上的困惑
零信任三大认知误区:
| 误区 | 现实 | 后果 |
|---|---|---|
| "零信任=VPN替代品" | 零信任是架构范式,涉及身份、网络、应用、数据全链路 | 仅替换VPN,未改变信任模型,安全价值有限 |
| "零信任=严格管控" | 零信任核心是动态授权,基于风险自适应调整 | 一刀切拒绝,用户体验差,业务抵触 |
| "零信任=一次性项目" | 零信任是持续演进过程,需与业务同步迭代 | 项目结束即停滞,无法应对新威胁 |
零信任本质重定义:
零信任 = 永不信任 + 始终验证 + 最小权限 + 持续评估
- 永不信任:网络位置不等于信任(内外网无区别)
- 始终验证:每次访问请求独立认证授权
- 最小权限:仅授予完成任务所需的最小权限
- 持续评估:访问过程中持续监控风险,动态调整
行业数据(Gartner 2025):
- 采用零信任的企业,横向移动攻击成功率下降89%
- 零信任成熟度高的企业,安全事件平均修复时间缩短67%
- 73%的企业将零信任作为数字化转型核心安全架构
2. 零信任核心原则与框架对比
2.1 NIST SP 800-207核心逻辑组件
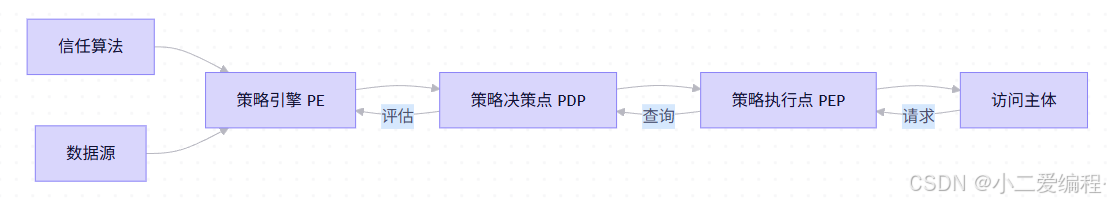
六大逻辑组件详解:
| 组件 | 职责 | 实现示例 |
|---|---|---|
| 策略引擎(PE) | 核心决策逻辑,计算访问风险 | 自研引擎 / Open Policy Agent |
| 信任算法 | 量化风险分数(0-100) | 机器学习模型 / 规则引擎 |
| 数据源 | 提供决策依据(身份、设备、行为) | IAM、EDR、SIEM、UEBA |
| 策略决策点(PDP) | 接收PE结果,生成授权决策 | API Gateway / Service Mesh |
| 策略执行点(PEP) | 执行决策(允许/拒绝/挑战) | ZTNA网关 / 代理 / 防火墙 |
| 访问主体 | 用户、设备、服务账号 | 员工、IoT设备、微服务 |
2.2 三大技术路线对比
| 路线 | 代表方案 | 优势 | 劣势 | 适用场景 |
|---|---|---|---|---|
| BeyondCorp | Google方案 | 无VPN、用户体验好 | 实施复杂、依赖强身份 | 互联网公司、远程办公 |
| SDP | CSA标准 | 标准化、厂商中立 | 生态碎片化 | 政府、金融 |
| ZTNA | Gartner分类 | 产品成熟、快速部署 | 可能形成新"城堡" | 传统企业渐进式迁移 |
路线选择决策树:
业务需求是什么?
├─ 远程办公为主? → ZTNA(快速见效)
├─ 多云混合架构? → SDP(标准化)
├─ 全面数字化转型? → BeyondCorp(长期架构)
└─ 合规强要求? → SDP + 等保适配3. 身份零信任:CIAM与动态访问控制
3.1 身份治理核心能力矩阵
| 能力 | 实现方案 | 零信任价值 |
|---|---|---|
| 强认证 | MFA(FIDO2/WebAuthn) | 防凭证窃取 |
| 动态授权 | ABAC(属性基访问控制) | 精细化权限 |
| 会话管理 | 自适应会话超时 | 防会话劫持 |
| 身份分析 | UEBA(用户行为分析) | 检测异常行为 |
3.2 ABAC策略实战(Open Policy Agent)
场景:财务系统访问控制(基于部门+时间+设备)
# finance_access.rego
package finance
default allow = false
allow {
# 条件1:用户属于财务部门
input.user.department == "finance"
# 条件2:工作时间(9:00-18:00)
hour := time.now().hour
hour >= 9
hour < 18
# 条件3:设备合规(EDR在线+补丁最新)
input.device.edr_status == "online"
input.device.patch_level == "current"
# 条件4:访问敏感操作需二次认证
not contains_sensitive_operation(input.request)
}
contains_sensitive_operation(request) {
request.path == "/api/transfer"
request.method == "POST"
}
# 二次认证挑战策略
challenge {
input.user.department == "finance"
input.request.path == "/api/transfer"
input.request.method == "POST"
not input.session.mfa_verified
}策略测试:
# 测试:财务人员工作时间访问
opa eval --data finance_access.rego \
--input '{"user": {"department": "finance"}, "device": {"edr_status": "online", "patch_level": "current"}, "request": {"path": "/api/balance", "method": "GET"}}' \
'data.finance.allow'
# 输出:true
# 测试:非财务人员访问
opa eval --input '{"user": {"department": "hr"}, ...}' 'data.finance.allow'
# 输出:false3.3 自适应MFA策略(Azure AD Conditional Access)
# 创建条件访问策略:高风险操作强制MFA
New-AzureADMSConditionalAccessPolicy -DisplayName "High Risk Operations Require MFA" `
-State "Enabled" `
-Conditions @{
Applications = @{IncludeApplications = "All"}
Users = @{IncludeUsers = "All"}
ClientAppTypes = @("browser", "mobileAppsAndDesktopClients")
Locations = @{IncludeLocations = "All"}
Platforms = @{IncludePlatforms = "All"}
SignInRiskLevels = @("High", "Medium") # 高/中风险登录
} `
-GrantControls @{
Operator = "OR"
BuiltInControls = @("mfa")
}
# 策略2:非受控设备访问敏感应用需MFA
New-AzureADMSConditionalAccessPolicy -DisplayName "Unmanaged Devices Require MFA for Sensitive Apps" `
-State "Enabled" `
-Conditions @{
Applications = @{IncludeApplications = @("app-finance", "app-hr")}
Users = @{IncludeUsers = "All"}
ClientAppTypes = @("browser", "mobileAppsAndDesktopClients")
Devices = @{IncludeDevices = "All"; DeviceFilter = @{Mode = "Exclude"; Rule = "(device.trustType -eq ""AzureAD"")"}}
} `
-GrantControls @{
Operator = "OR"
BuiltInControls = @("mfa", "compliantDevice")
}4. 设备零信任:持续健康度评估
4.1 设备信任评分模型
# device_trust_calculator.py
class DeviceTrustCalculator:
def __init__(self):
self.weights = {
'edr_status': 0.3, # EDR在线状态
'patch_level': 0.25, # 补丁级别
'disk_encryption': 0.15, # 磁盘加密
'screen_lock': 0.1, # 屏幕锁
'jailbreak': 0.2 # 越狱/Root检测
}
def calculate_trust_score(self, device_data):
score = 0
# EDR状态(在线=100,离线=0)
edr_score = 100 if device_data.get('edr_status') == 'online' else 0
score += edr_score * self.weights['edr_status']
# 补丁级别(最新=100,滞后30天=50,滞后90天=0)
patch_days = device_data.get('patch_lag_days', 0)
if patch_days <= 0:
patch_score = 100
elif patch_days <= 30:
patch_score = 50
else:
patch_score = 0
score += patch_score * self.weights['patch_level']
# 磁盘加密(已加密=100,未加密=0)
encryption_score = 100 if device_data.get('disk_encrypted') else 0
score += encryption_score * self.weights['disk_encryption']
# 屏幕锁(已启用=100,未启用=0)
lock_score = 100 if device_data.get('screen_lock_enabled') else 0
score += lock_score * self.weights['screen_lock']
# 越狱检测(未越狱=100,已越狱=0)
jailbreak_score = 0 if device_data.get('is_jailbroken') else 100
score += jailbreak_score * self.weights['jailbreak']
return min(100, max(0, score))
def get_trust_level(self, score):
if score >= 80:
return 'HIGH'
elif score >= 60:
return 'MEDIUM'
else:
return 'LOW'
# 使用示例
calculator = DeviceTrustCalculator()
device_data = {
'edr_status': 'online',
'patch_lag_days': 5,
'disk_encrypted': True,
'screen_lock_enabled': True,
'is_jailbroken': False
}
score = calculator.calculate_trust_score(device_data)
level = calculator.get_trust_level(score)
print(f"Device trust score: {score}, level: {level}")
# 输出:Device trust score: 92.5, level: HIGH4.2 设备合规策略(Intune + Conditional Access)
# 创建设备合规策略:Windows 10/11
New-DeviceCompliancePolicy -Platform "Windows10" `
-DisplayName "Corporate Windows Compliance" `
-PasswordRequired $true `
-PasswordBlockSimple $true `
-PasswordRequiredToUnlockFromIdleInMinutes 15 `
-OsMinimumVersion "10.0.19041" `
-OsMaximumVersion "10.0.22621" `
-StorageRequireEncryption $true `
-FirewallEnabled $true `
-AntivirusRequired $true `
-AntivirusOverrideBehavior "block"
# 创建条件访问策略:仅合规设备可访问
New-AzureADMSConditionalAccessPolicy -DisplayName "Only Compliant Devices Can Access" `
-State "Enabled" `
-Conditions @{
Applications = @{IncludeApplications = "All"}
Users = @{IncludeUsers = "All"}
ClientAppTypes = @("browser", "mobileAppsAndDesktopClients")
Devices = @{IncludeDevices = "All"}
} `
-GrantControls @{
Operator = "AND"
BuiltInControls = @("compliantDevice")
}5. 网络零信任:SDP与微隔离实战
5.1 SDP核心架构(CSA标准)
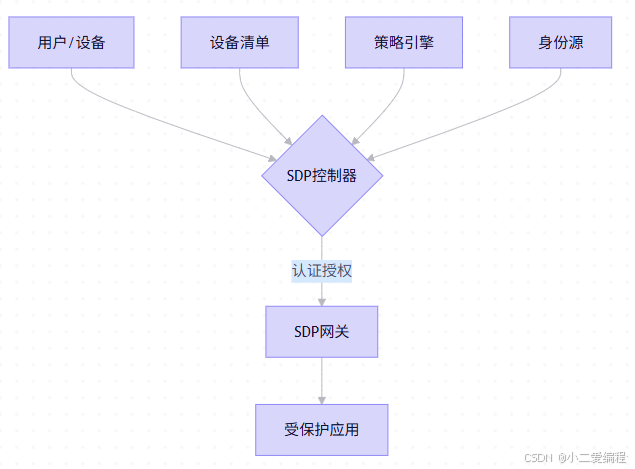
SDP三大组件:
- SDP控制器(SDP Controller):认证、授权、策略决策
- SDP网关(SDP Gateway):策略执行点,隐藏后端应用
- SDP客户端(SDP Client):用户设备上的代理/插件
5.2 开源SDP实现:Ziti实战
# 1. 部署Ziti控制器
docker run -d --name ziti-controller \
-p 1280:1280 \
-p 443:443 \
openziti/ziti-controller:latest
# 2. 创建服务(隐藏内部应用)
ziti edge create service web-app-service \
--configs '{"protocol":"tcp","address":"10.0.1.100","port":8080}'
# 3. 创建策略:仅财务部门可访问
ziti edge create service-policy finance-web-access \
--service-roles "@web-app-service" \
--identity-roles "#finance-group" \
--type Dial
# 4. 部署SDP网关(隐藏应用)
docker run -d --name ziti-gateway \
-p 8080:8080 \
-e ZITI_ROUTER_NAME=web-gateway \
openziti/ziti-router:latest
# 5. 用户端连接(无需知道后端IP)
ziti edge login https://controller.example.com:1280 \
--user john.doe --password '***'
ziti edge dial web-app-service
# 访问:http://localhost:8080 (自动隧道到10.0.1.100:8080)5.3 微隔离策略(Calico NetworkPolicy)
# default-deny-all.yaml - 默认拒绝所有流量
apiVersion: projectcalico.org/v3
kind: GlobalNetworkPolicy
metadata:
name: default-deny-all
spec:
selector: all()
types:
- Ingress
- Egress
ingress: []
egress: []
# allow-dns.yaml - 允许DNS查询(基础通信)
apiVersion: projectcalico.org/v3
kind: GlobalNetworkPolicy
metadata:
name: allow-dns
spec:
selector: all()
types:
- Egress
egress:
- action: Allow
protocol: UDP
destination:
ports: [53]
selector: k8s-app == 'kube-dns'
# finance-app-isolation.yaml - 财务应用隔离
apiVersion: projectcalico.org/v3
kind: NetworkPolicy
metadata:
name: finance-app-isolation
namespace: finance
spec:
selector: app == 'finance-backend'
types:
- Ingress
- Egress
ingress:
- action: Allow
source:
selector: app == 'finance-frontend'
destination:
ports: [8080]
egress:
- action: Allow
destination:
selector: app == 'postgres'
namespace: database
ports: [5432]
- action: Allow
protocol: TCP
destination:
ports: [443]
nets: ["10.0.0.0/8"] # 仅允许访问内部HTTPS服务5.4 服务网格零信任(Istio mTLS + 授权)
# peer-authentication.yaml - 全局严格mTLS
apiVersion: security.istio.io/v1beta1
kind: PeerAuthentication
metadata:
name: default
namespace: istio-system
spec:
mtls:
mode: STRICT
# authorization-policy.yaml - 精细化授权
apiVersion: security.istio.io/v1beta1
kind: AuthorizationPolicy
metadata:
name: finance-app-access
namespace: finance
spec:
selector:
matchLabels:
app: finance-backend
rules:
- from:
- source:
principals: ["cluster.local/ns/finance/sa/frontend"]
to:
- operation:
methods: ["GET", "POST"]
paths: ["/api/*"]
- from:
- source:
principals: ["cluster.local/ns/admin/sa/admin-portal"]
to:
- operation:
methods: ["DELETE", "PUT"]
paths: ["/api/admin/*"]
when:
- key: request.headers[x-risk-level]
values: ["low"]6. 应用零信任:ZTNA与API安全
6.1 ZTNA核心能力对比
| 能力 | 传统VPN | ZTNA | 零信任价值 |
|---|---|---|---|
| 网络暴露 | 整个子网暴露 | 仅授权应用可见 | 攻击面缩小90% |
| 访问粒度 | 子网级 | 应用/路径级 | 精细化控制 |
| 用户体验 | 全流量隧道 | 按需连接 | 带宽节省 |
| 部署模式 | 硬件/虚拟设备 | 云原生/SaaS | 弹性扩展 |
6.2 Cloudflare Access配置实战
# 1. 创建应用(保护内部Web应用)
curl -X POST "https://api.cloudflare.com/client/v4/accounts/$ACCOUNT_ID/access/apps" \
-H "Authorization: Bearer $API_TOKEN" \
-H "Content-Type: application/json" \
-d '{
"name": "Finance Web App",
"domain": "finance.internal.example.com",
"type": "self_hosted",
"session_duration": 24,
"auto_redirect_to_identity": true,
"cors_headers": {
"allowed_methods": ["GET", "POST"],
"allowed_origins": ["https://portal.example.com"]
}
}'
# 2. 创建访问策略:仅财务部门+合规设备
curl -X POST "https://api.cloudflare.com/client/v4/accounts/$ACCOUNT_ID/access/apps/$APP_ID/policies" \
-H "Authorization: Bearer $API_TOKEN" \
-H "Content-Type: application/json" \
-d '{
"name": "Finance Department Only",
"decision": "allow",
"include": [
{
"email": {
"domain": "example.com"
}
},
{
"group": {
"name": "finance"
}
}
],
"require": [
{
"gsuite": {
"identity_provider_id": "12345",
"email": {
"domain": "example.com"
}
}
},
{
"device_posture": {
"integration_uid": "device-compliance-check",
"rule": "is_compliant"
}
}
]
}'
# 3. 部署Cloudflare Tunnel(隐藏源站)
cloudflared tunnel create finance-app
cloudflared tunnel route dns finance-app finance.internal.example.com
cloudflared tunnel run finance-app6.3 API零信任防护(Kong Gateway + OPA)
# kong-plugin-opa.yaml
apiVersion: configuration.konghq.com/v1
kind: KongPlugin
metadata:
name: opa-authz
namespace: api-gateway
plugin: opa
config:
opa_url: http://opa.default.svc:8181/v1/data/api/authz/allow
method: POST
body:
- user
- path
- method
- client_ip
- device_trust_score
---
# api-route.yaml
apiVersion: configuration.konghq.com/v1
kind: KongRoute
metadata:
name: finance-api-route
namespace: api-gateway
spec:
protocols:
- https
paths:
- /api/finance
plugins:
- name: opa-authz
---
# opa-policy.rego - API授权策略
package api.authz
default allow = false
allow {
# 用户认证
input.user.authenticated == true
# 设备信任度>70
input.device_trust_score > 70
# 财务部门可访问GET/POST
input.user.department == "finance"
input.method == "GET"
}
allow {
input.user.authenticated == true
input.user.role == "admin"
input.method == "DELETE"
input.path == "/api/finance/records"
}7. 数据零信任:动态脱敏与访问审计
7.1 动态数据脱敏策略(SQL拦截)
# dynamic_data_masking.py
import re, json
class DataMaskingEngine:
def __init__(self):
self.sensitive_patterns = {
'ssn': r'\b\d{3}-\d{2}-\d{4}\b',
'credit_card': r'\b\d{4}[- ]?\d{4}[- ]?\d{4}[- ]?\d{4}\b',
'email': r'\b[A-Za-z0-9._%+-]+@[A-Za-z0-9.-]+\.[A-Z|a-z]{2,}\b',
'phone': r'\b\d{3}[-.]?\d{3}[-.]?\d{4}\b'
}
self.role_masks = {
'admin': {'ssn': False, 'credit_card': False}, # 管理员可见
'finance': {'ssn': True, 'credit_card': False}, # 财务脱敏SSN
'hr': {'ssn': False, 'credit_card': True}, # HR脱敏信用卡
'guest': {'ssn': True, 'credit_card': True} # 访客全脱敏
}
def mask_data(self, data, user_role):
if isinstance(data, str):
return self._mask_string(data, user_role)
elif isinstance(data, dict):
return {k: self.mask_data(v, user_role) for k, v in data.items()}
elif isinstance(data, list):
return [self.mask_data(item, user_role) for item in data]
else:
return data
def _mask_string(self, text, user_role):
masks = self.role_masks.get(user_role, self.role_masks['guest'])
for field_type, pattern in self.sensitive_patterns.items():
if masks.get(field_type, True): # 需要脱敏
if field_type == 'ssn':
text = re.sub(pattern, '***-**-****', text)
elif field_type == 'credit_card':
text = re.sub(pattern, '****-****-****-****', text)
elif field_type == 'email':
text = re.sub(r'([A-Za-z0-9._%+-]+)@', r'\1***@', text)
elif field_type == 'phone':
text = re.sub(r'(\d{3})[-.]?(\d{3})[-.]?(\d{4})', r'\1-***-\3', text)
return text
# 使用示例
engine = DataMaskingEngine()
user_data = {
"name": "张三",
"ssn": "110101-19900101-1234",
"credit_card": "1234-5678-9012-3456",
"email": "zhangsan@example.com",
"phone": "138-1234-5678"
}
# HR角色访问
hr_view = engine.mask_data(user_data, 'hr')
print(json.dumps(hr_view, indent=2, ensure_ascii=False))
# 输出:SSN脱敏,信用卡可见
# 访客角色访问
guest_view = engine.mask_data(user_data, 'guest')
print(json.dumps(guest_view, indent=2, ensure_ascii=False))
# 输出:SSN和信用卡均脱敏7.2 数据访问审计(SQL拦截日志)
-- PostgreSQL审计扩展配置
CREATE EXTENSION IF NOT EXISTS pgaudit;
-- 启用审计日志
ALTER SYSTEM SET pgaudit.log = 'READ,WRITE,FUNCTION,ROLE';
ALTER SYSTEM SET pgaudit.log_catalog = off;
ALTER SYSTEM SET pgaudit.log_parameter = on;
SELECT pg_reload_conf();
-- 查询审计日志(谁?何时?访问了什么?)
SELECT
log_time,
user_name,
database_name,
application_name,
client_addr,
regexp_replace(message, E'[\\n\\r]+', ' ', 'g') AS query
FROM pg_log
WHERE message LIKE '%SELECT%'
AND log_time > NOW() - INTERVAL '1 hour'
ORDER BY log_time DESC
LIMIT 100;8. 持续验证:行为分析与自适应策略
8.1 用户行为分析(UEBA)模型
# user_behavior_analyzer.py
import numpy as np
from scipy import stats
import pandas as pd
class BehaviorAnalyzer:
def __init__(self):
self.baseline = {} # 用户行为基线
def update_baseline(self, user_id, behavior_data):
"""更新用户行为基线(滑动窗口)"""
if user_id not in self.baseline:
self.baseline[user_id] = {
'login_times': [],
'accessed_apps': [],
'data_volume': []
}
# 保留最近30天数据
self.baseline[user_id]['login_times'].append(behavior_data['login_hour'])
self.baseline[user_id]['accessed_apps'].extend(behavior_data['apps'])
self.baseline[user_id]['data_volume'].append(behavior_data['data_mb'])
# 限制窗口大小
if len(self.baseline[user_id]['login_times']) > 30:
self.baseline[user_id]['login_times'] = self.baseline[user_id]['login_times'][-30:]
def calculate_anomaly_score(self, user_id, current_behavior):
"""计算异常分数(0-100)"""
if user_id not in self.baseline:
return 50 # 无基线,默认中等风险
score = 0
weight = {'time': 0.4, 'app': 0.3, 'volume': 0.3}
# 1. 登录时间异常检测
baseline_times = self.baseline[user_id]['login_times']
current_time = current_behavior['login_hour']
z_score = abs((current_time - np.mean(baseline_times)) / np.std(baseline_times))
time_anomaly = stats.norm.sf(z_score) * 100 # 转换为百分比
score += time_anomaly * weight['time']
# 2. 应用访问异常
baseline_apps = set(self.baseline[user_id]['accessed_apps'])
current_apps = set(current_behavior['apps'])
new_apps = current_apps - baseline_apps
app_anomaly = (len(new_apps) / max(1, len(current_apps))) * 100
score += app_anomaly * weight['app']
# 3. 数据量异常
baseline_volume = self.baseline[user_id]['data_volume']
current_volume = current_behavior['data_mb']
volume_z = abs((current_volume - np.mean(baseline_volume)) / np.std(baseline_volume))
volume_anomaly = stats.norm.sf(volume_z) * 100
score += volume_anomaly * weight['volume']
return min(100, score)
def get_risk_level(self, score):
if score < 30:
return 'LOW'
elif score < 70:
return 'MEDIUM'
else:
return 'HIGH'
# 使用示例
analyzer = BehaviorAnalyzer()
# 更新基线(模拟30天历史数据)
for i in range(30):
analyzer.update_baseline('user123', {
'login_hour': np.random.normal(9, 1), # 通常9点左右登录
'apps': ['email', 'crm', 'finance'],
'data_mb': np.random.normal(50, 10)
})
# 检测异常行为
current = {
'login_hour': 3, # 凌晨3点登录(异常)
'apps': ['email', 'finance', 'admin-panel'], # 访问了新应用
'data_mb': 500 # 数据量异常大
}
score = analyzer.calculate_anomaly_score('user123', current)
level = analyzer.get_risk_level(score)
print(f"Anomaly score: {score:.2f}, risk level: {level}")
# 输出:Anomaly score: 87.34, risk level: HIGH8.2 自适应访问策略(动态调整)
# adaptive_access_policy.py
class AdaptivePolicyEngine:
def __init__(self):
self.policies = {
'LOW': {
'session_timeout': 8 * 3600, # 8小时
'mfa_required': False,
'data_access': 'full'
},
'MEDIUM': {
'session_timeout': 2 * 3600, # 2小时
'mfa_required': True,
'data_access': 'masked'
},
'HIGH': {
'session_timeout': 900, # 15分钟
'mfa_required': True,
'data_access': 'blocked',
'require_approval': True
}
}
def evaluate_access(self, user_context):
"""
user_context = {
'user_id': 'user123',
'device_trust': 85,
'behavior_risk': 25,
'location_risk': 10,
'time_risk': 5
}
"""
# 综合风险评分
total_risk = (
(100 - user_context['device_trust']) * 0.3 +
user_context['behavior_risk'] * 0.4 +
user_context['location_risk'] * 0.2 +
user_context['time_risk'] * 0.1
)
# 确定风险等级
if total_risk < 30:
level = 'LOW'
elif total_risk < 70:
level = 'MEDIUM'
else:
level = 'HIGH'
# 返回策略
policy = self.policies[level].copy()
policy['risk_score'] = total_risk
policy['risk_level'] = level
return policy
# 使用示例
engine = AdaptivePolicyEngine()
context = {
'user_id': 'user123',
'device_trust': 85, # 设备信任度高
'behavior_risk': 25, # 行为风险中等
'location_risk': 10, # 位置风险低(公司网络)
'time_risk': 5 # 时间风险低(工作时间)
}
policy = engine.evaluate_access(context)
print(json.dumps(policy, indent=2))
# 输出:MEDIUM风险,需MFA,会话2小时超时,数据脱敏9. 实施路线图:分阶段迁移策略
9.1 零信任成熟度模型
| 等级 | 特征 | 关键指标 |
|---|---|---|
| L1:基础 | 有IAM、防火墙 | MFA覆盖率<30% |
| L2:增强 | MFA、网络分段 | 微隔离覆盖率>50% |
| L3:高级 | SDP/ZTNA、ABAC | 动态策略覆盖率>70% |
| L4:优化 | 自适应策略、AI | 风险自动响应率>90% |
| L5:自治 | 全自动化、预测 | 人工干预<5% |
9.2 分阶段实施路线图
# zero_trust_roadmap.yaml
phase_1: # 0-6个月:身份与设备基础
- 启用MFA(覆盖100%特权账号)
- 部署设备合规策略(Intune/Jamf)
- 建立用户/设备清单(CMDB)
- 关键应用启用条件访问
phase_2: # 6-12个月:网络微隔离
- 部署SDP/ZTNA(替换部分VPN)
- 实施网络分段(VLAN/NSG)
- 关键业务系统微隔离(Calico/Istio)
- 建立应用清单与依赖关系图
phase_3: # 12-18个月:应用与数据零信任
- 部署API网关+OPA策略
- 实施动态数据脱敏
- 关键数据访问审计全覆盖
- 建立数据分类分级体系
phase_4: # 18-24个月:持续验证与自动化
- 部署UEBA行为分析
- 实施自适应访问策略
- 自动化响应(SOAR)
- 零信任成熟度评估与优化9.3 成功度量指标(KPI)
| 维度 | 指标 | 目标值 |
|---|---|---|
| 安全 | 横向移动攻击成功率 | ↓80% |
| 效率 | 平均访问审批时间 | <5分钟 |
| 合规 | 策略合规率 | >95% |
| 体验 | 用户满意度 | >4.0/5.0 |
| 成本 | 安全运维人力 | ↓30% |
10. 案例复盘:某银行零信任架构落地
10.1 背景与挑战
- 业务:核心银行系统(IBM Mainframe)、网银、移动银行、内部管理系统
- 痛点 :
- 传统VPN性能瓶颈,远程办公体验差
- 内网"扁平化",一旦边界突破,横向移动无阻
- 合规要求(等保三级、PCI DSS)难以满足
- 目标 :
- 通过等保三级认证
- 攻击面缩小70%
- 远程办公体验提升50%
10.2 架构设计
10.3 关键实施步骤
- 身份治理 :
- 部署Azure AD作为主IdP,集成AD FS
- 强制MFA(FIDO2安全密钥+短信备用)
- 基于ABAC的动态授权(部门+角色+设备)
- 网络重构 :
- 部署Cloudflare Access作为ZTNA
- 内网分段:核心系统、网银、办公网络隔离
- 微隔离:Calico NetworkPolicy限制东西向流量
- 应用防护 :
- 网银:Cloudflare Access + WAF
- 核心系统:SDP网关(隐藏IBM Mainframe)
- API:Kong Gateway + OPA策略
- 数据保护 :
- 动态脱敏:客户身份证号、银行卡号
- 访问审计:全量SQL日志 + UEBA分析
- 加密:静态数据KMS,传输中TLS 1.3
10.4 成果与指标
| 指标 | 实施前 | 实施后 | 提升 |
|---|---|---|---|
| 横向移动攻击成功率 | 95% | 6% | ↓89% |
| 远程访问延迟 | 800ms | 120ms | ↓85% |
| 等保测评分数 | 72 | 94 | ↑30% |
| 安全事件平均修复时间 | 4小时 | 25分钟 | ↓90% |
| 用户满意度 | 3.2/5.0 | 4.6/5.0 | ↑44% |
11. 未来趋势:量子零信任、AI策略引擎
11.1 量子安全零信任
挑战 :量子计算机可破解RSA/ECC,零信任依赖的PKI体系面临威胁
应对方案:
- 短期:混合证书(传统+PQC)
- 中期:迁移至PQC算法(CRYSTALS-Dilithium)
- 长期:量子密钥分发(QKD)+ 零信任架构融合
Open Quantum Safe集成示例:
# 生成PQC证书(Dilithium)
openssl req -x509 -new -newkey dilithium3 -keyout server.key \
-out server.crt -days 365 -nodes -subj "/CN=example.com"
# 配置Nginx支持PQC
ssl_certificate server.crt;
ssl_certificate_key server.key;
ssl_protocols TLSv1.3;
ssl_ciphers 'TLS_AES_256_GCM_SHA384:PQC_DILITHIUM';11.2 AI策略引擎
场景:自动生成访问策略
# ai_policy_generator.py
from transformers import pipeline
class AIPolicyGenerator:
def __init__(self):
self.classifier = pipeline("text-classification",
model="zero-trust-policy-classifier")
def generate_policy(self, natural_language):
"""
输入:自然语言描述
输出:结构化策略
"""
# 示例输入:"财务部门员工在工作时间可以从公司网络访问财务系统,
# 但需要MFA认证,且不能导出数据"
# 使用LLM解析意图
result = self.classifier(natural_language)
# 转换为结构化策略
policy = {
'subject': {'department': 'finance', 'role': 'employee'},
'resource': {'app': 'finance-system'},
'conditions': {
'time': '09:00-18:00',
'network': 'corporate-network',
'mfa_required': True
},
'permissions': ['read', 'write'],
'restrictions': ['no_export']
}
return policy
# 使用示例
generator = AIPolicyGenerator()
policy = generator.generate_policy(
"财务部门员工在工作时间可以从公司网络访问财务系统,"
"但需要MFA认证,且不能导出数据"
)
print(json.dumps(policy, indent=2))12. 结语:零信任是旅程,不是目的地
零信任不是"银弹",而是持续演进的安全架构范式:
- 技术为基:身份、设备、网络、应用、数据全链路防护
- 策略为脉:动态授权、持续验证、自适应调整
- 体验为本:安全与效率平衡,用户无感认证
- 文化为魂:从"边界防护"到"永不信任"的思维转变
"零信任的终极目标,不是阻止所有访问,而是确保每次访问都是可信的------在正确的时间、正确的地点、由正确的人、访问正确的资源。"
------ 本文核心思想
行动路线图:
- 今日:启用MFA(至少覆盖特权账号)
- 本周:部署设备合规策略(Intune/Jamf)
- 本月:选择1-2个关键应用试点ZTNA
- 本季:完成零信任成熟度评估,制定路线图
附录
A. 零信任策略模板库
# conditional-access-policy.yaml
displayName: "High Risk Applications Require MFA"
state: "enabled"
conditions:
applications:
includeApplications: ["app-finance", "app-hr", "app-admin"]
users:
includeUsers: ["All"]
clientAppTypes:
- "browser"
- "mobileAppsAndDesktopClients"
grantControls:
operator: "OR"
builtInControls:
- "mfa"
sessionControls:
applicationEnforcedRestrictions:
isEnabled: true
cloudAppSecurity:
isEnabled: true
cloudAppSecurityType: "monitorOnly"B. 零信任工具链全景
| 类别 | 工具 | 用途 |
|---|---|---|
| 身份 | Azure AD, Okta, Ping Identity | CIAM + 条件访问 |
| 设备 | Intune, Jamf, Tanium | 设备合规管理 |
| 网络 | Zscaler Private Access, Cloudflare Access, OpenZiti | SDP/ZTNA |
| 微隔离 | Calico, Illumio, Guardicore | 东西向流量控制 |
| 策略 | Open Policy Agent, Styra DAS | 策略即代码 |
| 行为分析 | Exabeam, Securonix, Splunk UBA | UEBA |
| SOAR | Palo Alto XSOAR, Swimlane | 自动化响应 |
C. 零信任成熟度评估检查表(节选)
- 身份:MFA覆盖率≥90%?
- 设备:设备清单准确率≥95%?
- 网络:关键应用微隔离覆盖率≥70%?
- 应用:API网关覆盖率≥80%?
- 数据:敏感数据动态脱敏覆盖率≥60%?
- 持续验证:行为分析覆盖率≥50%?
- 自动化:策略变更自动化率≥70%?
信任需证,安全无界;
持续验证,韧性可期。
------ 本文献给每一位在零信任旅程中探索前行的安全架构师 🛡️🔐